Combating Online Identity Theft Spoofguard Pwd Hash Spyware
Combating Online Identity Theft Spoofguard, Pwd. Hash, Spyware, Botnets John Mitchell (Stanford) TRUST, Washington, D. C. Meeting January 9– 10, 2006
Problem: Online Identity Theft l Password phishing – – l Password theft – l Keyloggers steal passwords, product activation codes, etc. Botnets – l Criminals break into servers and steal password files Spyware – l Forged email and fake web sites steal passwords Passwords used to withdraw money, degrade trust Networks of compromised end-user machines spread SPAM, launch attacks, collect and share stolen information Magnitude – – $$$ Hundreds of millions in direct loss per year Significant Indirect loss in brand erosion l l Loss of confidence in online transactions Inconvenience of restoring credit rating, identity Online identity theft, J. C. Mitchell TRUST, Washington, D. C. Meeting January 9– 10, 2006 2
TRUST team l l l Stanford – D Boneh, J Mitchell, D Dill, Jennifer Granick (Law School) – A Bortz, N Chou, C Jackson, N Miyake, R Ledesma, B Ross, E Stinson, Y Teraguchi, … Berkeley – D Tygar, R Dhamija, , – Deidre Mulligan (UC Berkeley Law), … CMU – A Perrig, D Song – B Parno, C Kuo Partners and collaborators – US Secret Service, DHS/SRI Id Theft Tech Council, RSA Securities, … – R Rodriguez, D Maughan, … And growing … Online identity theft, J. C. Mitchell TRUST, Washington, D. C. Meeting January 9– 10, 2006 3
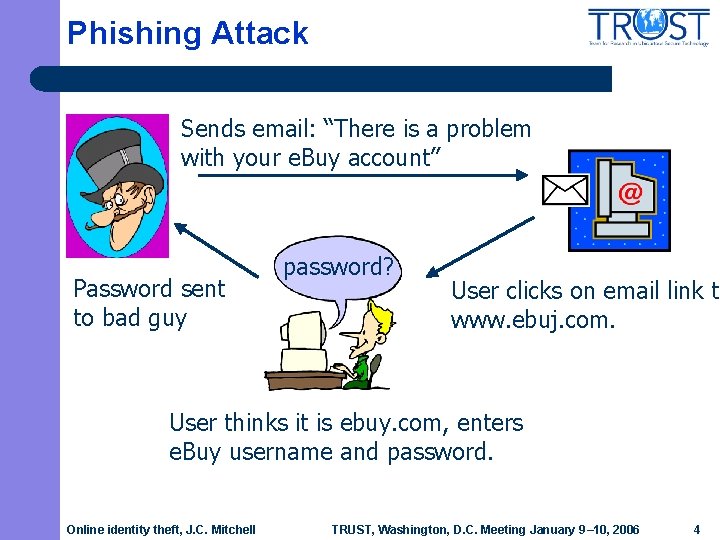
Phishing Attack Sends email: “There is a problem with your e. Buy account” Password sent to bad guy password? User clicks on email link to www. ebuj. com. User thinks it is ebuy. com, enters e. Buy username and password. Online identity theft, J. C. Mitchell TRUST, Washington, D. C. Meeting January 9– 10, 2006 4

Sample phishing email Online identity theft, J. C. Mitchell TRUST, Washington, D. C. Meeting January 9– 10, 2006 5
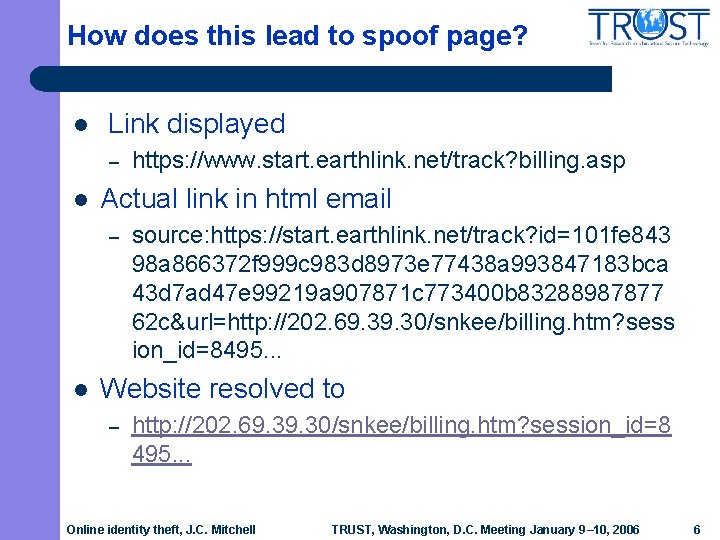
How does this lead to spoof page? l Link displayed – l Actual link in html email – l https: //www. start. earthlink. net/track? billing. asp source: https: //start. earthlink. net/track? id=101 fe 843 98 a 866372 f 999 c 983 d 8973 e 77438 a 993847183 bca 43 d 7 ad 47 e 99219 a 907871 c 773400 b 83288987877 62 c&url=http: //202. 69. 30/snkee/billing. htm? sess ion_id=8495. . . Website resolved to – http: //202. 69. 30/snkee/billing. htm? session_id=8 495. . . Online identity theft, J. C. Mitchell TRUST, Washington, D. C. Meeting January 9– 10, 2006 6
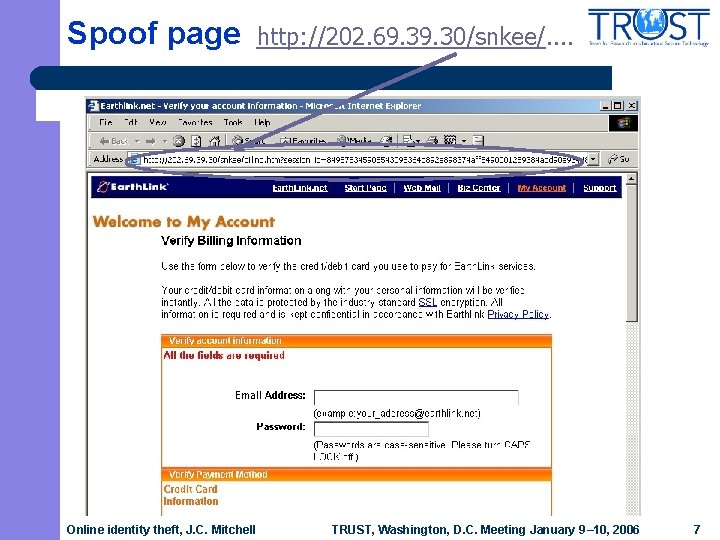
Spoof page Online identity theft, J. C. Mitchell http: //202. 69. 30/snkee/. . TRUST, Washington, D. C. Meeting January 9– 10, 2006 7
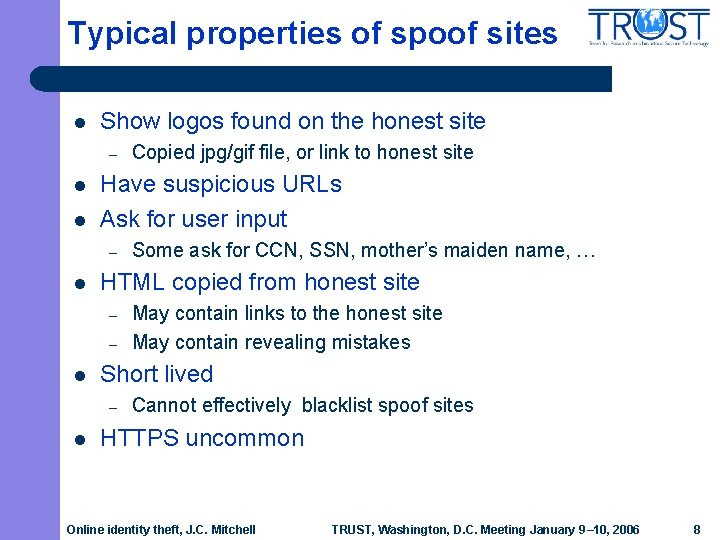
Typical properties of spoof sites l Show logos found on the honest site – l l Have suspicious URLs Ask for user input – l – May contain links to the honest site May contain revealing mistakes Short lived – l Some ask for CCN, SSN, mother’s maiden name, … HTML copied from honest site – l Copied jpg/gif file, or link to honest site Cannot effectively blacklist spoof sites HTTPS uncommon Online identity theft, J. C. Mitchell TRUST, Washington, D. C. Meeting January 9– 10, 2006 8
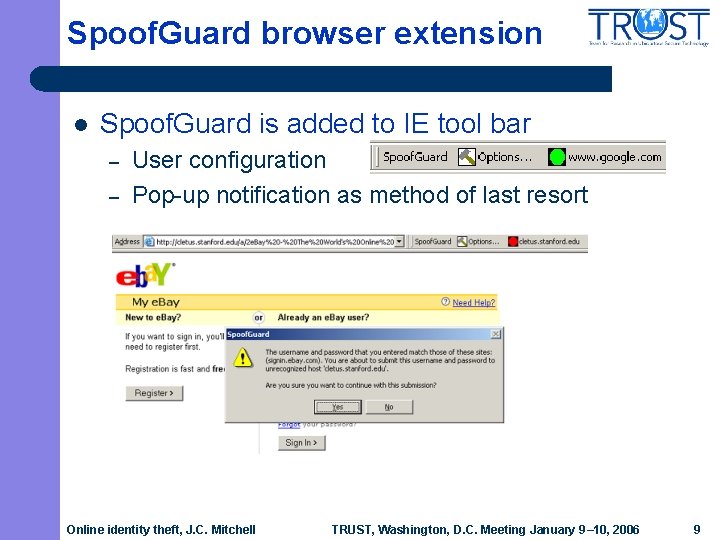
Spoof. Guard browser extension l Spoof. Guard is added to IE tool bar – – User configuration Pop-up notification as method of last resort Online identity theft, J. C. Mitchell TRUST, Washington, D. C. Meeting January 9– 10, 2006 9
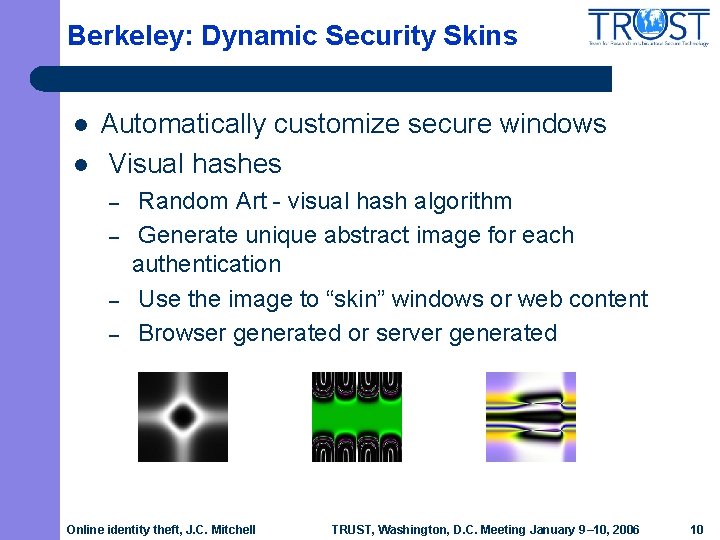
Berkeley: Dynamic Security Skins l l Automatically customize secure windows Visual hashes – – Random Art - visual hash algorithm Generate unique abstract image for each authentication Use the image to “skin” windows or web content Browser generated or server generated Online identity theft, J. C. Mitchell TRUST, Washington, D. C. Meeting January 9– 10, 2006 10
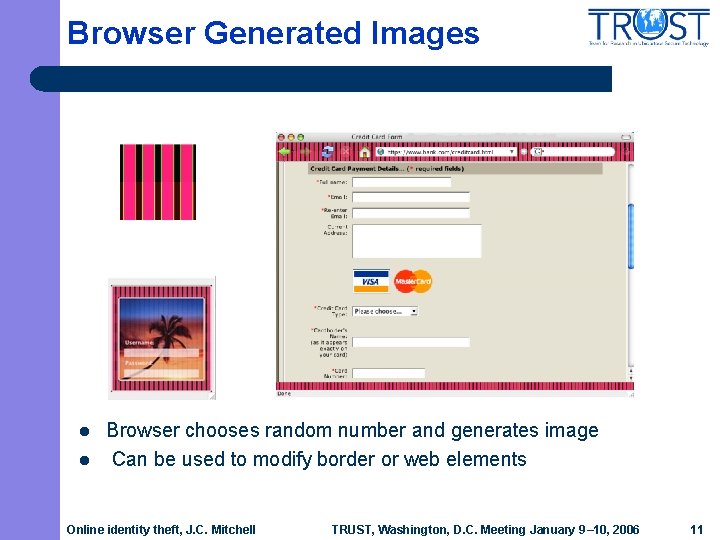
Browser Generated Images l l Browser chooses random number and generates image Can be used to modify border or web elements Online identity theft, J. C. Mitchell TRUST, Washington, D. C. Meeting January 9– 10, 2006 11
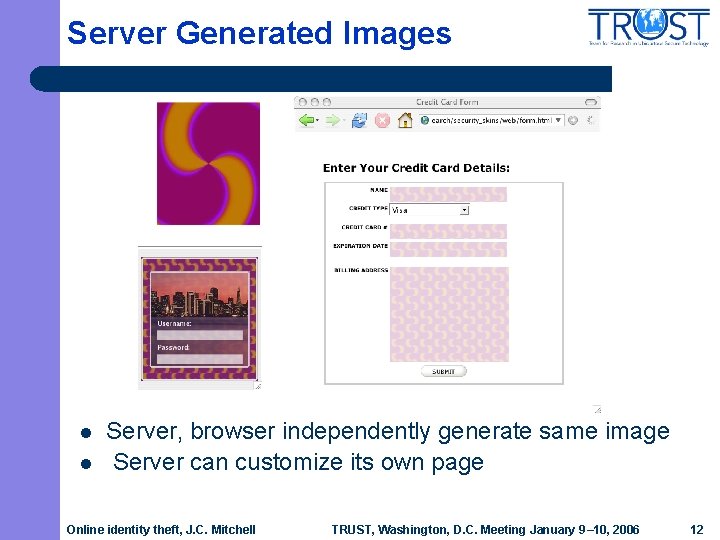
Server Generated Images l l Server, browser independently generate same image Server can customize its own page Online identity theft, J. C. Mitchell TRUST, Washington, D. C. Meeting January 9– 10, 2006 12
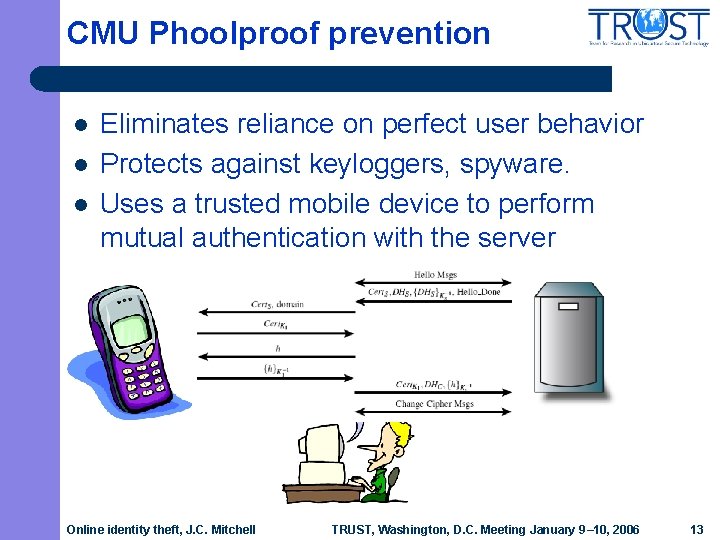
CMU Phoolproof prevention l l l Eliminates reliance on perfect user behavior Protects against keyloggers, spyware. Uses a trusted mobile device to perform mutual authentication with the server password? Online identity theft, J. C. Mitchell TRUST, Washington, D. C. Meeting January 9– 10, 2006 13
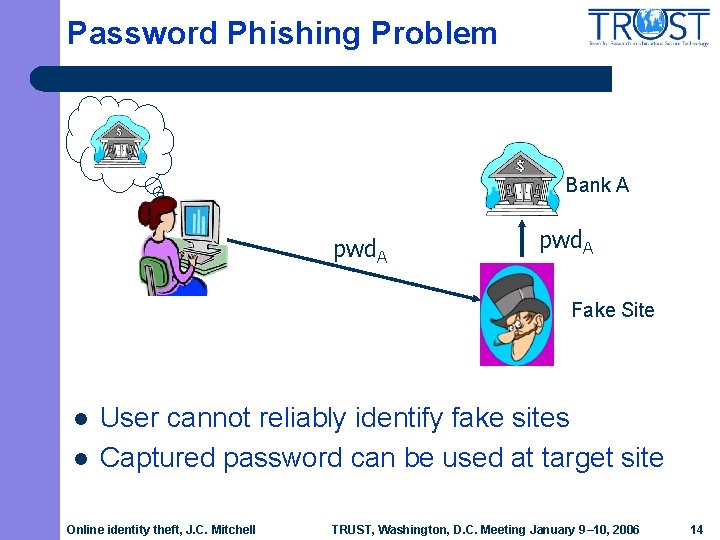
Password Phishing Problem Bank A pwd. A Fake Site l l User cannot reliably identify fake sites Captured password can be used at target site Online identity theft, J. C. Mitchell TRUST, Washington, D. C. Meeting January 9– 10, 2006 14
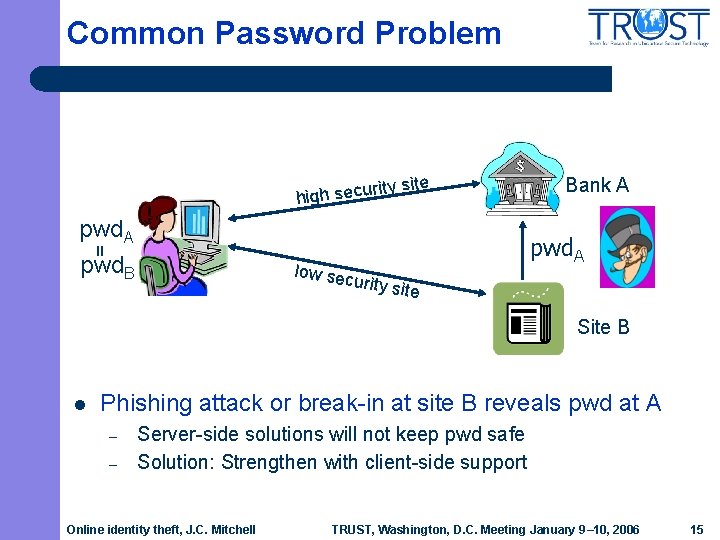
Common Password Problem rit high secu y site pwd. A = pwd. B Bank A low sec urity si te Site B l Phishing attack or break-in at site B reveals pwd at A – – Server-side solutions will not keep pwd safe Solution: Strengthen with client-side support Online identity theft, J. C. Mitchell TRUST, Washington, D. C. Meeting January 9– 10, 2006 15
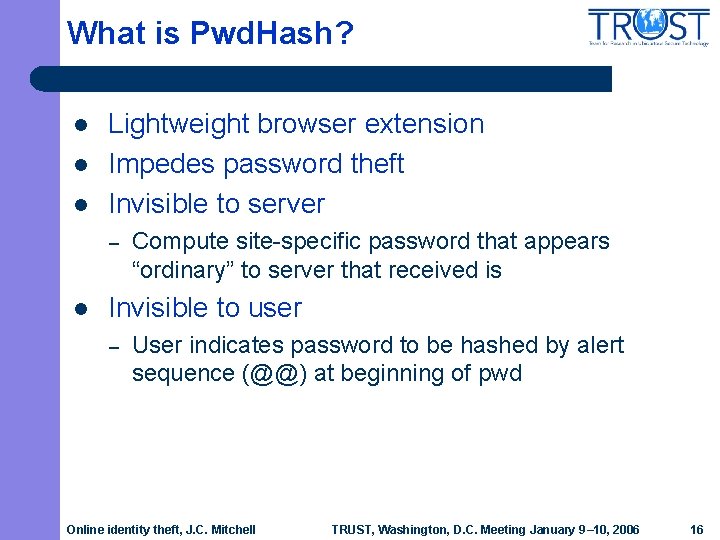
What is Pwd. Hash? l l l Lightweight browser extension Impedes password theft Invisible to server – l Compute site-specific password that appears “ordinary” to server that received is Invisible to user – User indicates password to be hashed by alert sequence (@@) at beginning of pwd Online identity theft, J. C. Mitchell TRUST, Washington, D. C. Meeting January 9– 10, 2006 16

Password Hashing k. A ) n a B , d hash(pw A = pwd. A pwd. B Bank A l wd , S B ite. B) Site B Generate a unique password per site – – l hash(p HMACfido: 123(banka. com) Q 7 a+0 ek. EXb HMACfido: 123(siteb. com) Oz. X 2+ICiqc Hashed password is not usable at any other site – – Protects against password phishing Protects against common password problem Online identity theft, J. C. Mitchell TRUST, Washington, D. C. Meeting January 9– 10, 2006 17

Many additional issues l Malicious javascript in browser – l l Implement keystroke logger, keep scripts from reading user password entry Password reset problem Internet café Dictionary attacks (defense: added salt) Try it! http: //crypto. stanford. edu/Spoof. Guard/ http: //crypto. stanford. edu/Pwd. Hash/ Online identity theft, J. C. Mitchell TRUST, Washington, D. C. Meeting January 9– 10, 2006 18

Tech Transfer l Spoof. Guard – – l Some Spoof. Guard heuristics now used in e. Bay toolbar and Earthlink Scam. Blocker. Very effective against basic phishing attacks. Pwd. Hash – Collaboration with RSA Security to implement Pwd. Hash on one-time RSA Secur. ID passwords. l l l RSA Secur. ID passwords vulnerable to online phishing Pwd. Hash helps strengthen Secur. ID passwords New browser extensions for privacy – Safe. Cache and Safe. History Online identity theft, J. C. Mitchell TRUST, Washington, D. C. Meeting January 9– 10, 2006 19
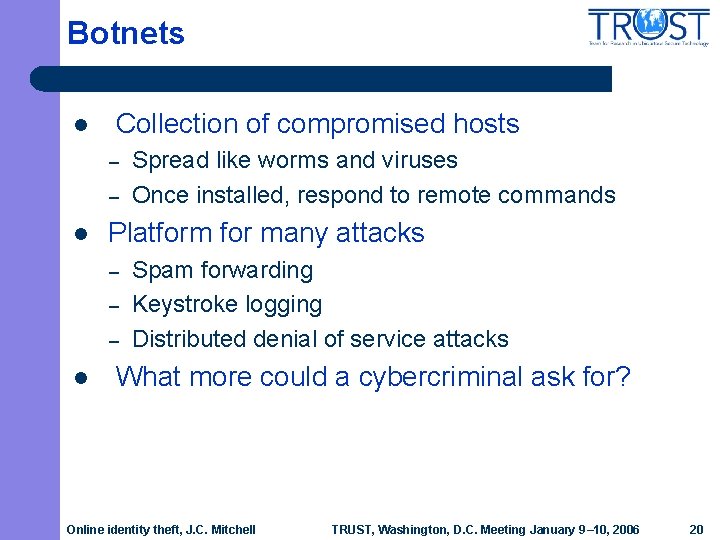
Botnets l Collection of compromised hosts – – l Platform for many attacks – – – l Spread like worms and viruses Once installed, respond to remote commands Spam forwarding Keystroke logging Distributed denial of service attacks What more could a cybercriminal ask for? Online identity theft, J. C. Mitchell TRUST, Washington, D. C. Meeting January 9– 10, 2006 20

Botnet facts l Platforms – – l Example bot software: – l Most bots are compromised Windows machines Most controllers are compromised Unix hosts running ircd Korgobot, Spy. Bot, Optix Pro, r. Bot, SDBot, Agobot, Phatbot. Versatile launching point for many attacks – – – 70% of spam from bots (Message. Labs, October 2004). Most worms and viruses used to propagate bot software Most denial of service attacks are orchestrated using bots Botnets are the primary infrastructure of criminal activity on the Internet, used most heavily for spamming, phishing, and creating more bots. – Jim Lippard, Director, Information Security Operations, Global Crossing Online identity theft, J. C. Mitchell TRUST, Washington, D. C. Meeting January 9– 10, 2006 21
GLBC: malware-infected hosts Online identity theft, J. C. Mitchell TRUST, Washington, D. C. Meeting January 9– 10, 2006 22
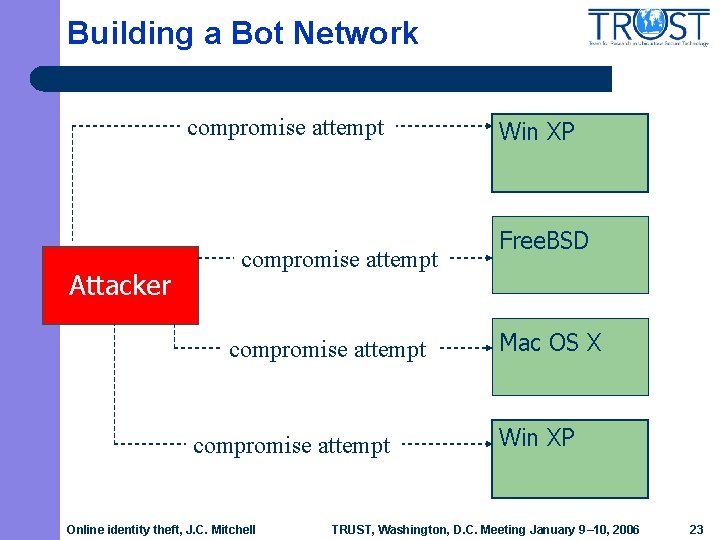
Building a Bot Network compromise attempt Attacker compromise attempt Online identity theft, J. C. Mitchell Win XP Free. BSD Mac OS X Win XP TRUST, Washington, D. C. Meeting January 9– 10, 2006 23

Building a Bot Network compromise attempt install bot software Attacker compromise attempt install bot software Online identity theft, J. C. Mitchell Win XP compromised Free. BSD Mac OS X Win XP compromised TRUST, Washington, D. C. Meeting January 9– 10, 2006 24
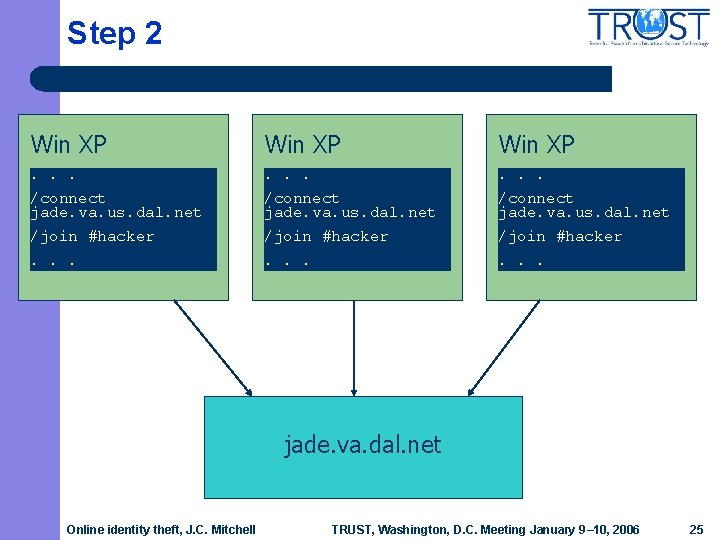
Step 2 Win XP . . /connect jade. va. us. dal. net /join #hacker. . . jade. va. dal. net Online identity theft, J. C. Mitchell TRUST, Washington, D. C. Meeting January 9– 10, 2006 25
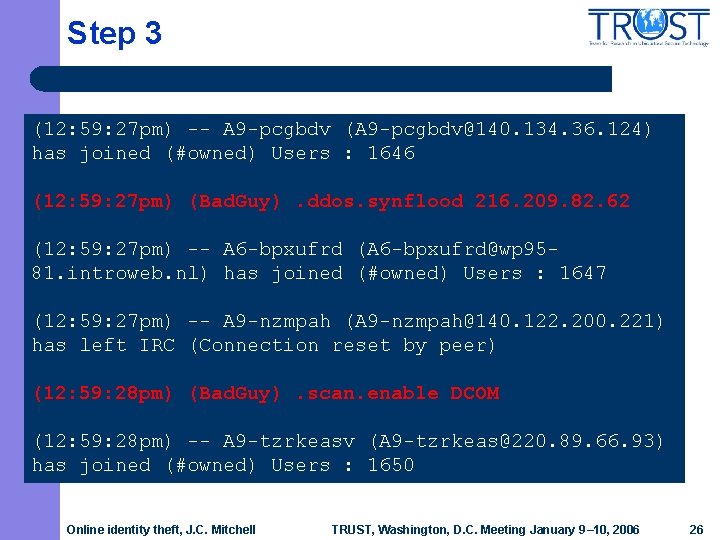
Step 3 (12: 59: 27 pm) -- A 9 -pcgbdv (A 9 -pcgbdv@140. 134. 36. 124) has joined (#owned) Users : 1646 (12: 59: 27 pm) (Bad. Guy). ddos. synflood 216. 209. 82. 62 (12: 59: 27 pm) -- A 6 -bpxufrd (A 6 -bpxufrd@wp 9581. introweb. nl) has joined (#owned) Users : 1647 (12: 59: 27 pm) -- A 9 -nzmpah (A 9 -nzmpah@140. 122. 200. 221) has left IRC (Connection reset by peer) (12: 59: 28 pm) (Bad. Guy). scan. enable DCOM (12: 59: 28 pm) -- A 9 -tzrkeasv (A 9 -tzrkeas@220. 89. 66. 93) has joined (#owned) Users : 1650 Online identity theft, J. C. Mitchell TRUST, Washington, D. C. Meeting January 9– 10, 2006 26
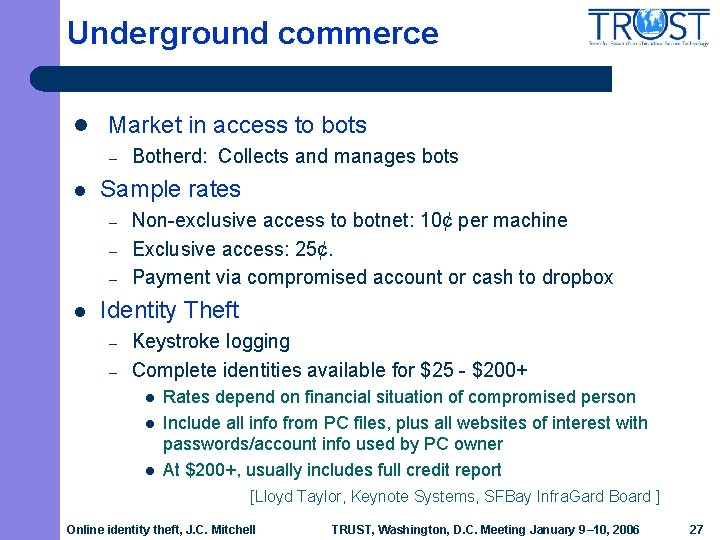
Underground commerce l Market in access to bots – l Sample rates – – – l Botherd: Collects and manages bots Non-exclusive access to botnet: 10¢ per machine Exclusive access: 25¢. Payment via compromised account or cash to dropbox Identity Theft – – Keystroke logging Complete identities available for $25 - $200+ l l l Rates depend on financial situation of compromised person Include all info from PC files, plus all websites of interest with passwords/account info used by PC owner At $200+, usually includes full credit report [Lloyd Taylor, Keynote Systems, SFBay Infra. Gard Board ] Online identity theft, J. C. Mitchell TRUST, Washington, D. C. Meeting January 9– 10, 2006 27
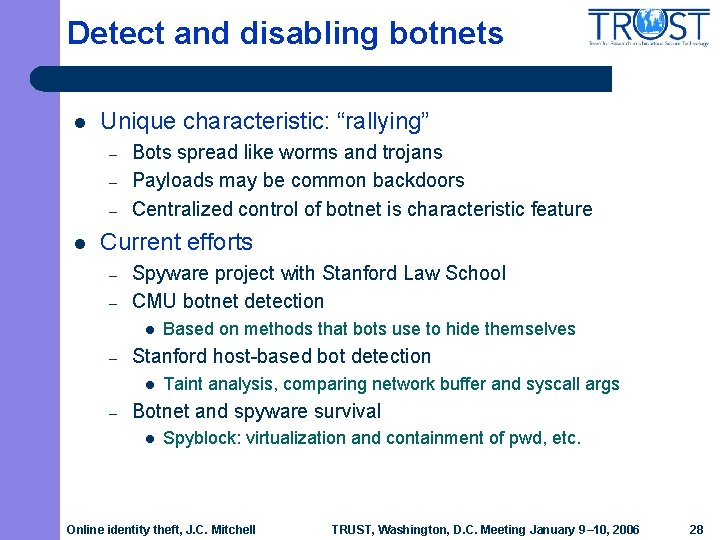
Detect and disabling botnets l Unique characteristic: “rallying” – – – l Bots spread like worms and trojans Payloads may be common backdoors Centralized control of botnet is characteristic feature Current efforts – – Spyware project with Stanford Law School CMU botnet detection l – Stanford host-based bot detection l – Based on methods that bots use to hide themselves Taint analysis, comparing network buffer and syscall args Botnet and spyware survival l Spyblock: virtualization and containment of pwd, etc. Online identity theft, J. C. Mitchell TRUST, Washington, D. C. Meeting January 9– 10, 2006 28

Future challenges l Criminals become increasingly sophisticated – l Increasing interest at server side – l Basic science can be applied to solve problem: challengeresponse, two-factor auth, … Social awareness, legal issues, and human factors – l Protect assets from crimeware Need improved web authentication – l Losses are significant Need improved platform security – l “In 25 years of law enforcement, this is the closest thing I’ve seen to the perfect crime” – Don Wilborn Studies with Law Clinics; user studies Technology transfer – More free software, RSA Security, … Online identity theft, J. C. Mitchell TRUST, Washington, D. C. Meeting January 9– 10, 2006 29
- Slides: 29