Columbia Verizon Research Security SIP Application Layer Gateway
Columbia Verizon Research Security: SIP Application Layer Gateway Eilon Yardeni Columbia University Gaston Ormazabal Verizon Labs May 23, 2006
Agenda Team l Project Overview l – Background Ø What is the Problem – Goals l Technical Overview – – l Hardware Platform Software Developed at Columbia Integrated Testing and Analysis Tool Large Scale Testing Environment Conclusions May 23, 2006 2
Team Verizon Stu Elby, VP Architecture l Jim Sylvester, VP Systems Integration and Testing l – Gaston Ormazabal Columbia l Prof. Henning Schulzrinne – Jonathan Lennox – Kundan Singh – Eilon Yardeni May 23, 2006 3
Background Columbia likes to work in real life problems and analyze large data sets with the goal of improving generic architectures and testing methodologies l Columbia has world-renowned expertise in SIP l Verizon needs to solve a perimeter protection problem for security of Vo. IP Services l – Protocol Aware Application Layer Gateway l Verizon needs to build a high powered test tool to verify performance and scalability of these security solutions at carrier class rates – Security and Performance are a zero sum game May 23, 2006 4
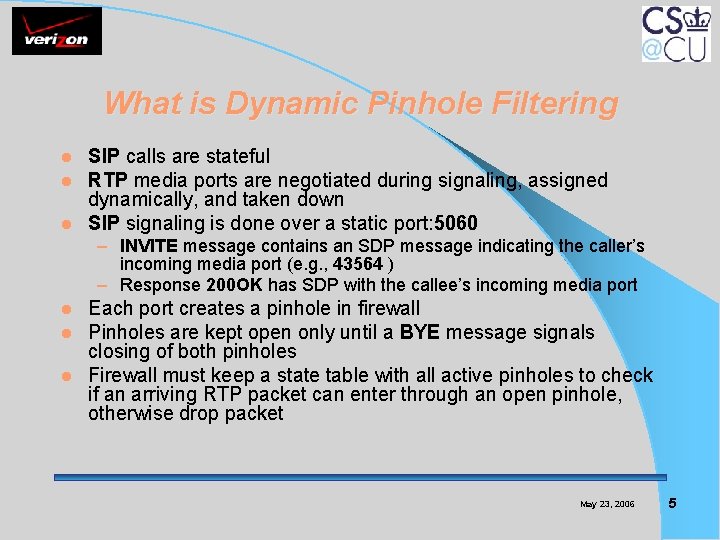
What is Dynamic Pinhole Filtering SIP calls are stateful RTP media ports are negotiated during signaling, assigned dynamically, and taken down l SIP signaling is done over a static port: 5060 l l – INVITE message contains an SDP message indicating the caller’s incoming media port (e. g. , 43564 ) – Response 200 OK has SDP with the callee’s incoming media port Each port creates a pinhole in firewall Pinholes are kept open only until a BYE message signals closing of both pinholes l Firewall must keep a state table with all active pinholes to check if an arriving RTP packet can enter through an open pinhole, otherwise drop packet l l May 23, 2006 5
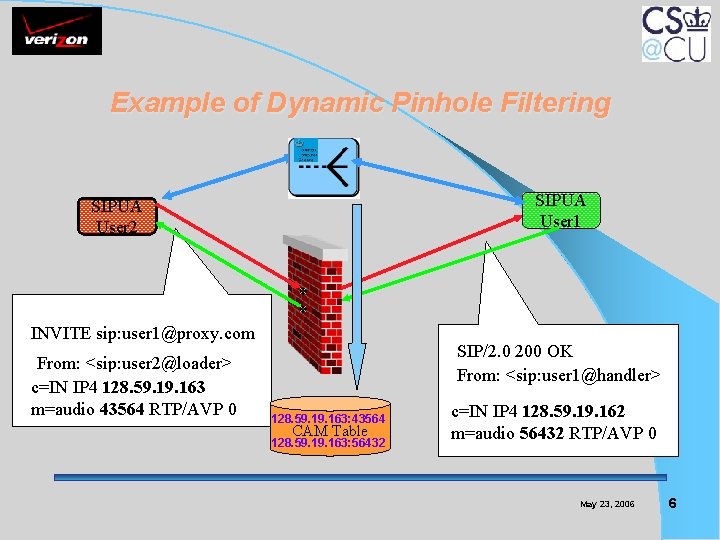
Example of Dynamic Pinhole Filtering SIPUA User 1 SIPUA User 2 INVITE sip: user 1@proxy. com From: <sip: user 2@loader> c=IN IP 4 128. 59. 163 m=audio 43564 RTP/AVP 0 SIP/2. 0 200 OK From: <sip: user 1@handler> 128. 59. 163: 43564 CAM Table 128. 59. 163: 56432 c=IN IP 4 128. 59. 162 m=audio 56432 RTP/AVP 0 May 23, 2006 6
Project Goals Program SIP based dynamic pinhole filtering in a parallel processing hardware platform l Build an integrated testing and analysis tool that will validate functionality and performance of above device at carrier-class rates l – Tool will provide automation of testing (script based) Apply testing tool to evaluate several Session Border Controllers on behalf of Verizon l Perform comparative analysis of architectural models and develop architectural improvements l Generalize testing methodology l May 23, 2006 7
Applicability to Columbia l Hands on experience with SIP Application Layer Gateways – Experience some SIP security related challenges – Experiment with carrier class traffic and scale models Hands on experience with a state-of-the-art programmable packet processing hardware l Enhance Columbia’s SIP Proxy with Firewall Control Proxy capabilities l Formalize security benchmarking methodology for SIP ALGs l May 23, 2006 8
Applicability to Verizon l Verizon needs this functionality to perform at high rates for use: – In the protection of highly valued network assets Ø Session Border Controllers for Packet Telephony – In the provision of security services to Enterprise customers for revenue Ø VADS (SIP Application Layer Gateway) l Verizon needs to verify in the lab the performance and scalability of this technology prior to introduction in the network May 23, 2006 9
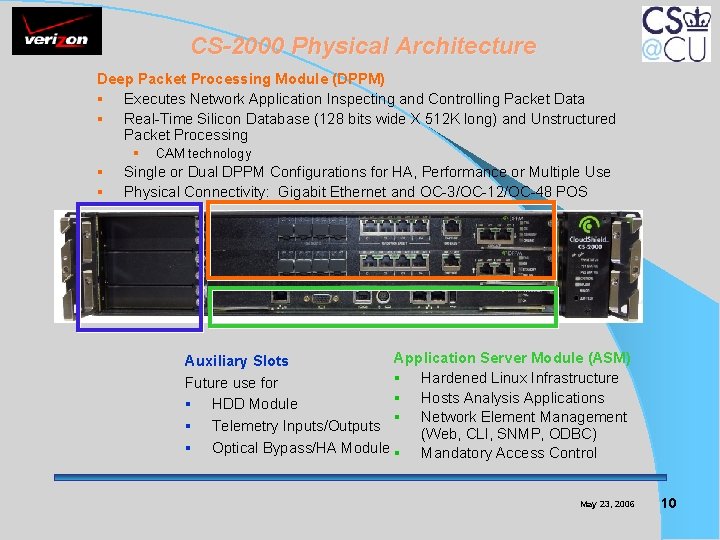
CS-2000 Physical Architecture Deep Packet Processing Module (DPPM) § Executes Network Application Inspecting and Controlling Packet Data § Real-Time Silicon Database (128 bits wide X 512 K long) and Unstructured Packet Processing § § § CAM technology Single or Dual DPPM Configurations for HA, Performance or Multiple Use Physical Connectivity: Gigabit Ethernet and OC-3/OC-12/OC-48 POS Application Server Module (ASM) Auxiliary Slots § Hardened Linux Infrastructure Future use for § Hosts Analysis Applications § HDD Module § Network Element Management § Telemetry Inputs/Outputs (Web, CLI, SNMP, ODBC) § Optical Bypass/HA Module § Mandatory Access Control May 23, 2006 10
Cloud. Shield Application Platform l l Applications written in RAVE and “pushed” to DPPM Dynamic Pinhole Implementation – RAVE based Ø Complex logic such as SIP call processing is difficult to implement in Regular Expressions (Regex) Ø Support only a “thin” SIP functionality – SIP Proxy controlling the DPPM (Midcom-like solution) Ø Introduce SIP Proxy - DDPM data exchange problem Ø Solved by using a Firewall Control Protocol l Columbia developed a breakthrough solution that allowed to use SIP Proxy with performance equal to the “thin” SIP-RAVE – Maximized the use of RAVE – Use full SIP proxy functionality May 23, 2006 11
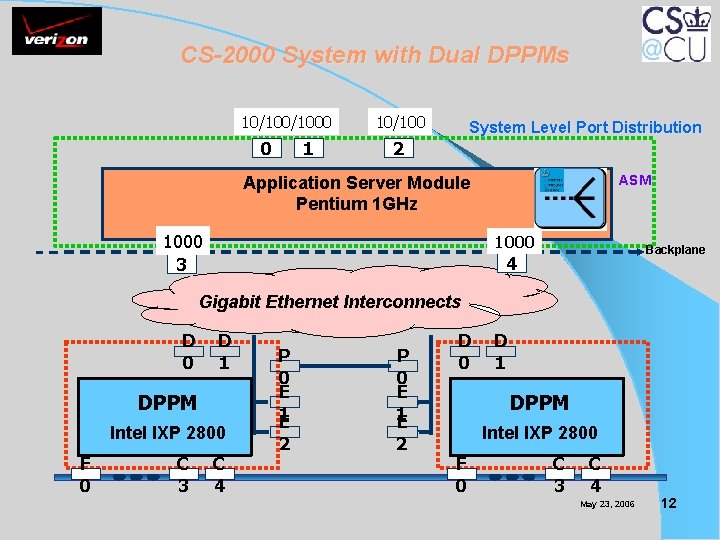
CS-2000 System with Dual DPPMs 10/1000 0 1 10/100 System Level Port Distribution 2 Application Server Module Pentium 1 GHz 1000 3 ASM 1000 Backplane 4 Gigabit Ethernet Interconnects D 0 D 1 DPPM Intel IXP 2800 F 0 C 3 C 4 P 0 E 1 E 2 D 0 D 1 DPPM Intel IXP 2800 F 0 C 3 C 4 May 23, 2006 12
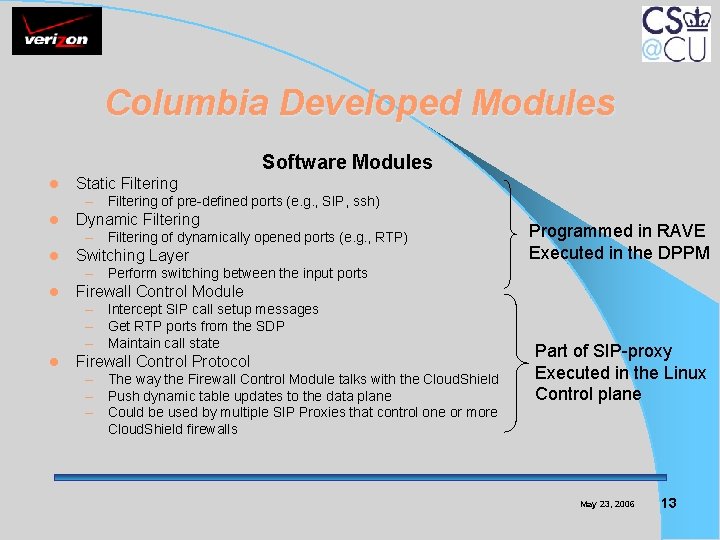
Columbia Developed Modules Software Modules l Static Filtering – Filtering of pre-defined ports (e. g. , SIP, ssh) l Dynamic Filtering – Filtering of dynamically opened ports (e. g. , RTP) l Switching Layer Programmed in RAVE Executed in the DPPM – Perform switching between the input ports l Firewall Control Module – Intercept SIP call setup messages – Get RTP ports from the SDP – Maintain call state l Firewall Control Protocol – The way the Firewall Control Module talks with the Cloud. Shield – Push dynamic table updates to the data plane – Could be used by multiple SIP Proxies that control one or more Cloud. Shield firewalls Part of SIP-proxy Executed in the Linux Control plane May 23, 2006 13
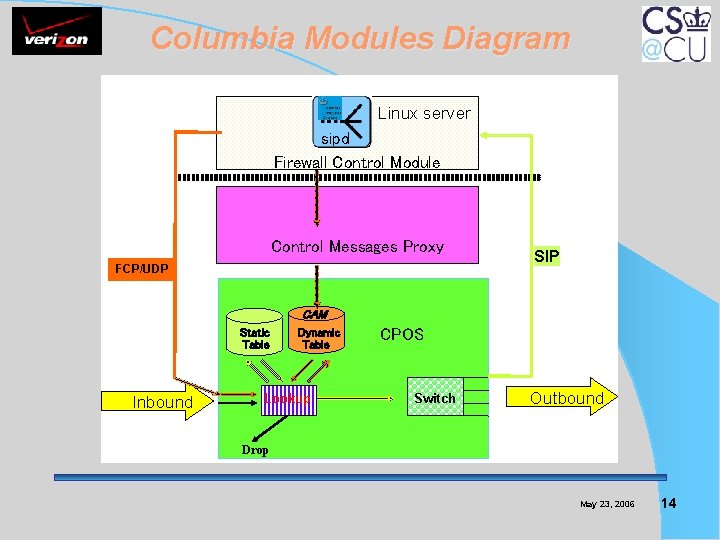
Columbia Modules Diagram Linux server sipd Firewall Control Module Control Messages Proxy FCP/UDP SIP CAM Static Table Inbound Dynamic Table Lookup CPOS Switch Outbound Drop May 23, 2006 14
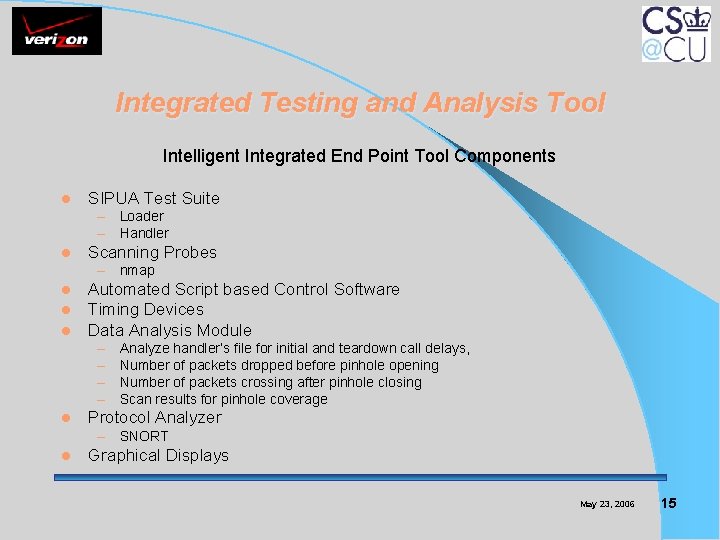
Integrated Testing and Analysis Tool Intelligent Integrated End Point Tool Components l SIPUA Test Suite – Loader – Handler l Scanning Probes – nmap l l l Automated Script based Control Software Timing Devices Data Analysis Module – – l Analyze handler’s file for initial and teardown call delays, Number of packets dropped before pinhole opening Number of packets crossing after pinhole closing Scan results for pinhole coverage Protocol Analyzer – SNORT l Graphical Displays May 23, 2006 15
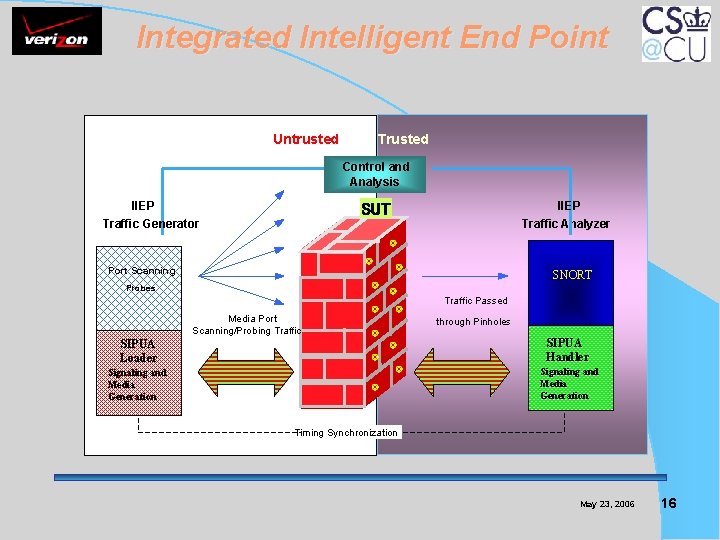
Integrated Intelligent End Point Untrusted Trusted Control and Analysis IIEP Traffic Generator IIEP Traffic Analyzer SUT Port Scanning SNORT Probes Traffic Passed Media Port Scanning/Probing Traffic through Pinholes 4 SIPUA Loader SIPUA Handler Signaling and Media Generation Timing Synchronization May 23, 2006 16
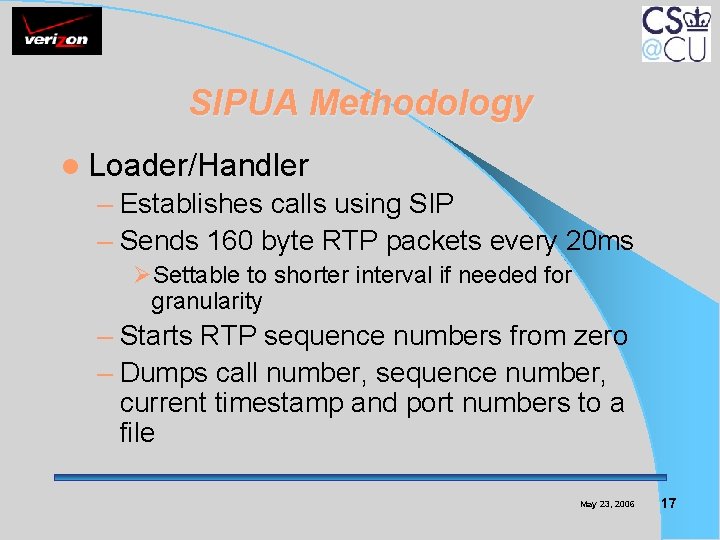
SIPUA Methodology l Loader/Handler – Establishes calls using SIP – Sends 160 byte RTP packets every 20 ms ØSettable to shorter interval if needed for granularity – Starts RTP sequence numbers from zero – Dumps call number, sequence number, current timestamp and port numbers to a file May 23, 2006 17
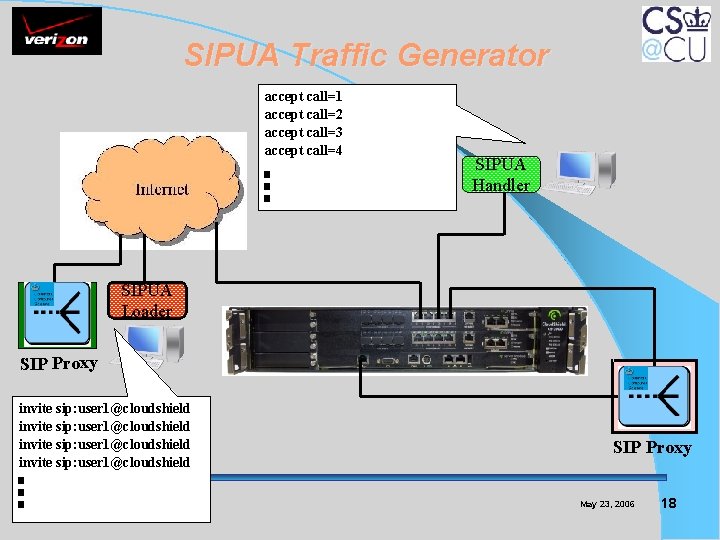
SIPUA Traffic Generator accept call=1 accept call=2 accept call=3 accept call=4 SIPUA Handler SIPUA Loader SIP Proxy invite sip: user 1@cloudshield SIP Proxy May 23, 2006 18
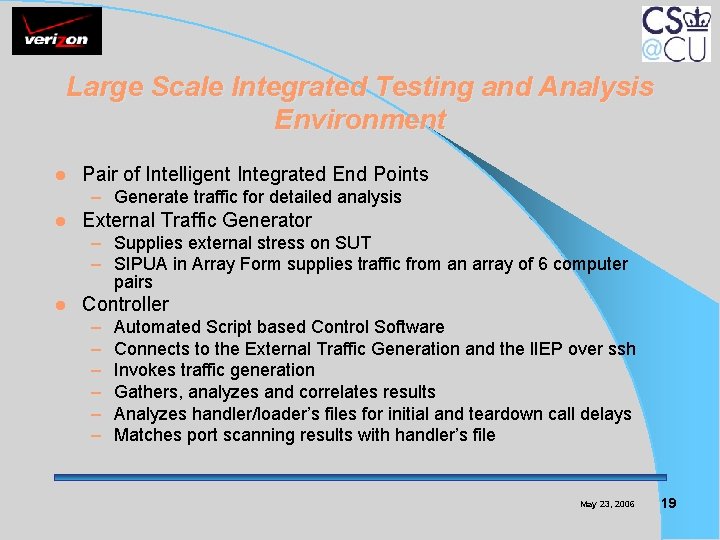
Large Scale Integrated Testing and Analysis Environment l Pair of Intelligent Integrated End Points – Generate traffic for detailed analysis l External Traffic Generator – Supplies external stress on SUT – SIPUA in Array Form supplies traffic from an array of 6 computer pairs l Controller – – – Automated Script based Control Software Connects to the External Traffic Generation and the IIEP over ssh Invokes traffic generation Gathers, analyzes and correlates results Analyzes handler/loader’s files for initial and teardown call delays Matches port scanning results with handler’s file May 23, 2006 19
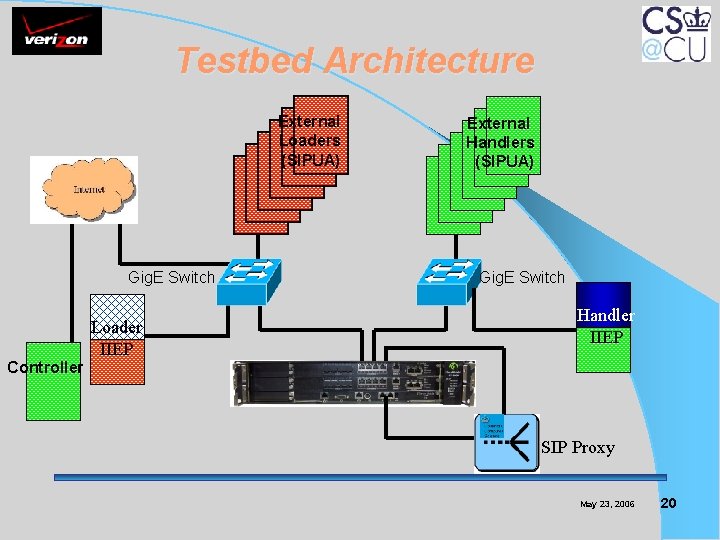
Testbed Architecture External Loaders (SIPUA) Gig. E Switch Loader IIEP External Handlers (SIPUA) Gig. E Switch Handler IIEP Controller SIP Proxy May 23, 2006 20
Problem Definition l Problem parameterized along two independent vectors – Call Rate (calls/sec) ØRelated to performance of SIP Proxy in Pentium – Concurrent Calls ØRelated to performance of table lookup in IXP 2800 May 23, 2006 21
Testing And Analysis Methodology l Generate external load on the firewall – – SIPUA Loader/Handler in external load mode Generates thousands of concurrent RTP sessions For 30 K concurrent calls have 120 K open pinholes CAM table length is 120 K entries Ø Search algorithm finds match in one cycle l When external load is established, run the IIEP analysis – SIPUA Loader/Handler in internal load mode – Port scanning and Protocol analyzer – Increment calls/sec rate l Measure pinhole opening and closing delays – Opening delay data provided in units of 20 ms packets – Closing delay data provided in units of 10 ms packets l Detect pinholes extraneously open May 23, 2006 22
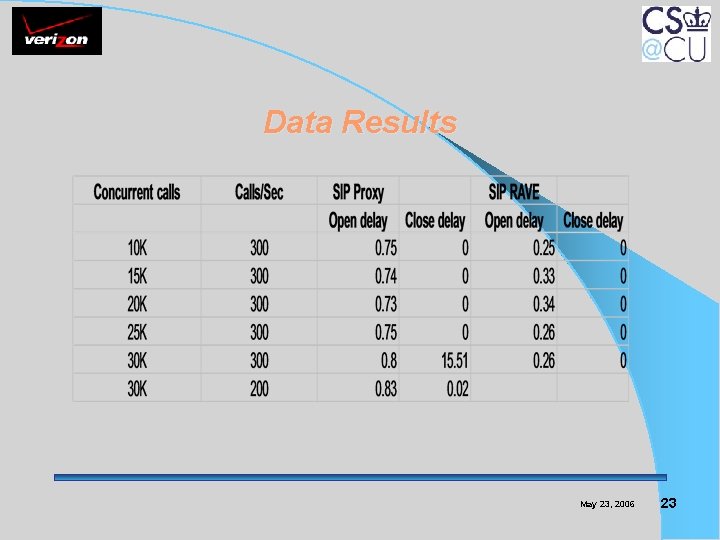
Data Results May 23, 2006 23
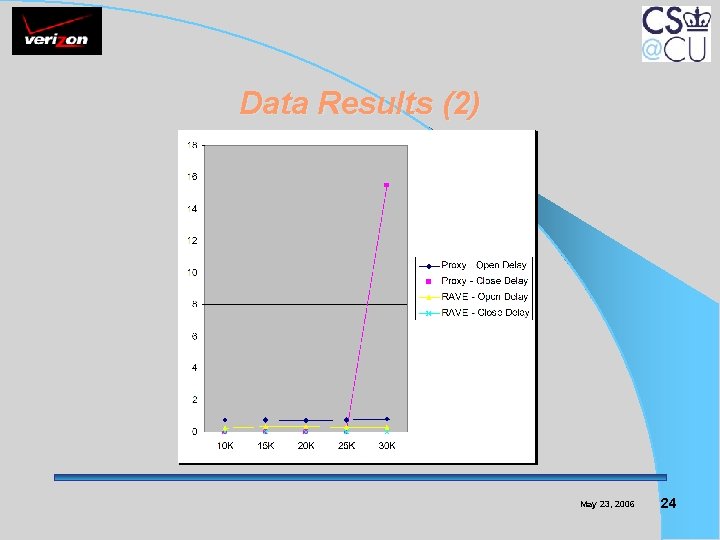
Data Results (2) May 23, 2006 24
Benefits to Verizon and Columbia l Technology Transfer to Verizon Labs – Set up a replica of Columbia testbed in Silver Spring Vo. IP lab for rapid SBC evaluation l Licensing Agreement with Cloud. Shield – Currently negotiating a Royalty Agreement to take technology to market l Intellectual Property – Patents and Publications May 23, 2006 25
Technology Transfer l Silver Spring Vo. IP Lab testbed – Have 12 computer in parallel running SIPUA, SNORT, nmap, protocol analyzers – Set up Controller software – Interoperability testing with local SIP proxy (Broadsoft) – SIPUA can be used for other SIP performance testing with modifications May 23, 2006 26
Intellectual Property l Pending Patent Applications – “Fine Granularity Scalability and Performance of SIP Aware Border Gateways: Methodology and Architecture for Measurements” Ø Inventors: Henning Schulzrinne, Kundan Singh, Eilon Yardeni (Columbia), Gaston Ormazabal (Verizon) – “Architectural Design of a High Performance SIP-aware Application Layer Gateway” Ø Inventors: Henning Schulzrinne, Jonathan Lennox, Eilon Yardeni (Columbia), Gaston Ormazabal (Verizon) l Paper submitted to MASCOTS 2006 – “Large Scale SIP-aware Application Layer Firewall”. Ø Authors: Henning Schulzrinne, Eilon Yardeni (Columbia), Gaston Ormazabal (Verizon) May 23, 2006 27
Conclusions l Have implemented for the first time a SIP ALG that scales up to 30 K concurrent calls with 300 calls/sec – This performance should satisfy Verizon “carrier-class” requirements at a reasonable cost Have proved hypothesis that cpu exhaustion will limit scalability because of degradation in performance l Have constructed a SIP Proxy based model that will permit modularization, l – Hence increasing scalability of future architectures l Have built a one of a kind high-powered “black box” testing environment – Will permit Verizon verify this technology for other vendors May 23, 2006 28
Back up slides May 23, 2006
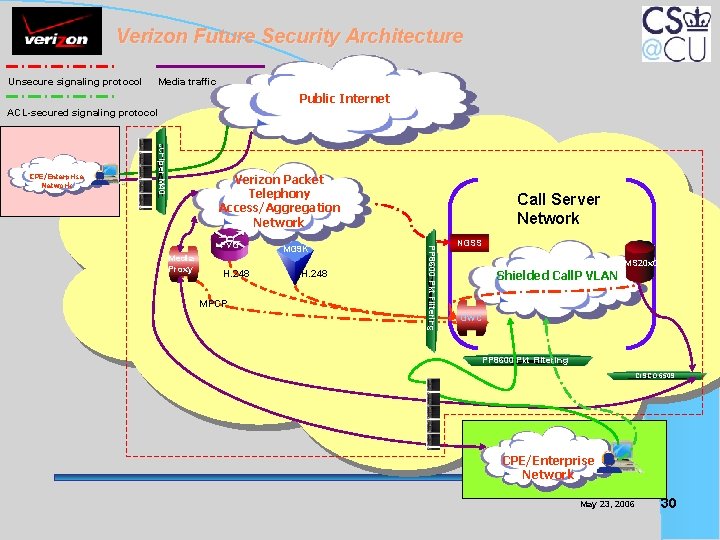
Verizon Future Security Architecture Unsecure signaling protocol Media traffic Public Internet ACL-secured signaling protocol Juniper M 40 CPE/Enterprise Network Verizon Packet Telephony SIP Access/Aggregation Network Media Proxy H. 248 MPCP MG 9 K H. 248 PP 8600 Pkt Filtering PVG Call Server Network NGSS Shielded Call. P VLAN MS 20 x 0 GWC PP 8600 Pkt Filtering CISCO 6509 CPE/Enterprise Network May 23, 2006 30
- Slides: 30