Coin Flipping Protocol CS 303 Alg Number Theory
Coin Flipping Protocol CS 303 Alg. Number Theory & Cryptography Jeremy Johnson Manuel Blum, Coin Flipping by Telephone: A Protocol for Solving Impossible Problems, ACM SIGACT, Vol. 15, No. 1, 1983, pp. 23 -27.
Outline Coin flipping protocol n Completely secure vs. normally secure one-way functions n Some protocols that do not work n Blum Protocol n Goldwasser-Micali Probabilistic Encryption n 12/10/2008 Goldwasser 1
Coin Tossing Protocol n Want to flip a coin over the telephone Fair and verifiable n Not subject to cheating n 2
Public Key Cryptography n Let M be a message and let C be the encrypted message (ciphertext). A public key cryptosystem has a separate method E() for encrypting and D() decrypting. n n n D(E(M)) = M Both E() and D() are easy to compute Publicly revealing E() does not make it easy to determine D() E(D(M)) = M - needed for signatures The collection of E()’s are made publicly available but the D()’s remain secret. Called a one-way trap-door function (hard to invert, but easy if you have the secret information) 3
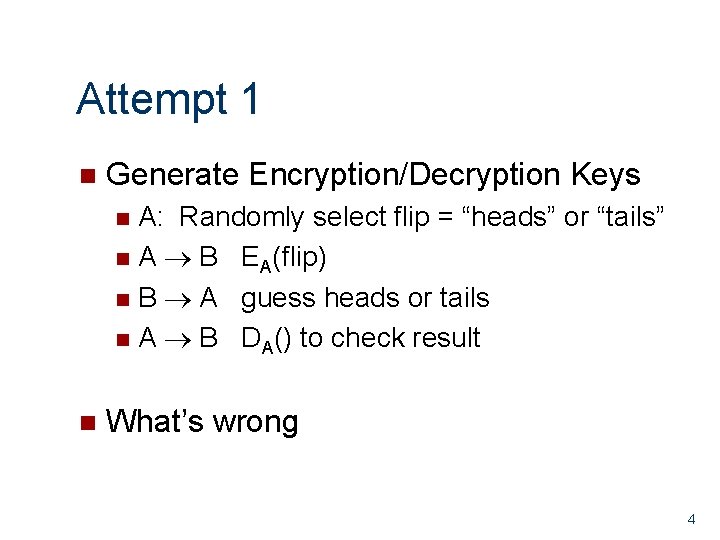
Attempt 1 n Generate Encryption/Decryption Keys A: Randomly select flip = “heads” or “tails” n A B EA(flip) n B A guess heads or tails n A B DA() to check result n n What’s wrong 4
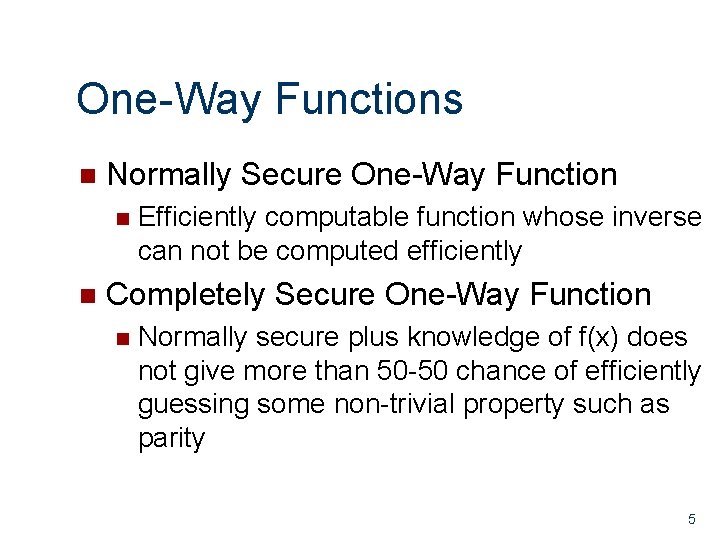
One-Way Functions n Normally Secure One-Way Function n n Efficiently computable function whose inverse can not be computed efficiently Completely Secure One-Way Function n Normally secure plus knowledge of f(x) does not give more than 50 -50 chance of efficiently guessing some non-trivial property such as parity 5
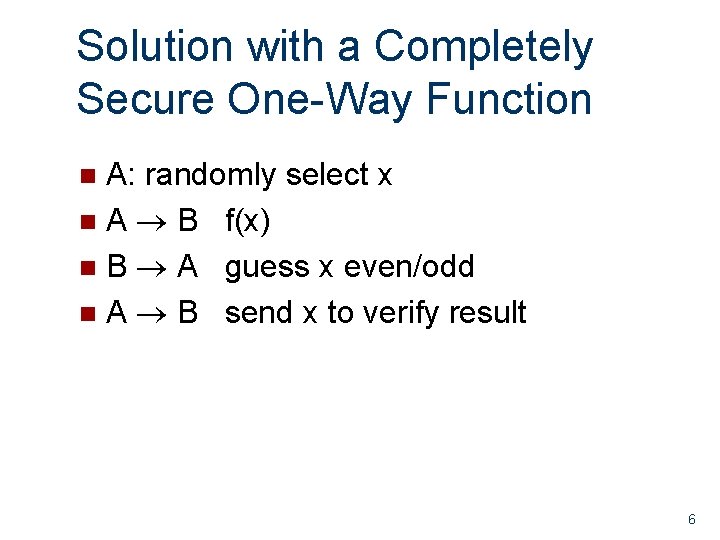
Solution with a Completely Secure One-Way Function A: randomly select x n A B f(x) n B A guess x even/odd n A B send x to verify result n 6
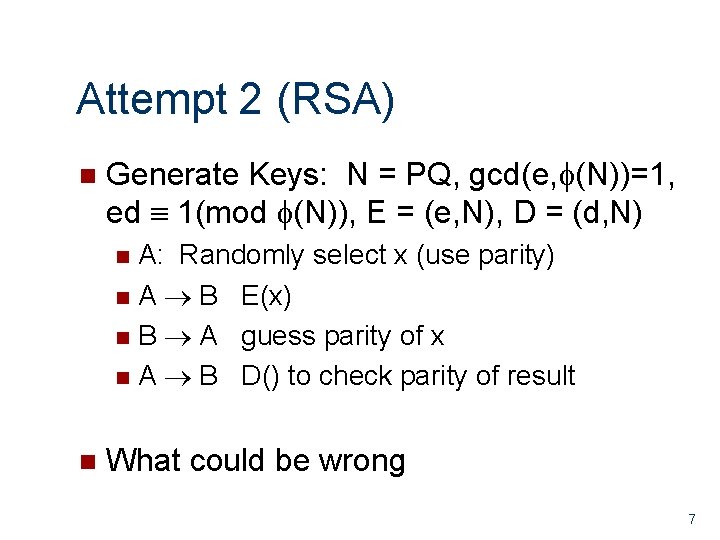
Attempt 2 (RSA) n Generate Keys: N = PQ, gcd(e, (N))=1, ed 1(mod (N)), E = (e, N), D = (d, N) A: Randomly select x (use parity) n A B E(x) n B A guess parity of x n A B D() to check parity of result n n What could be wrong 7
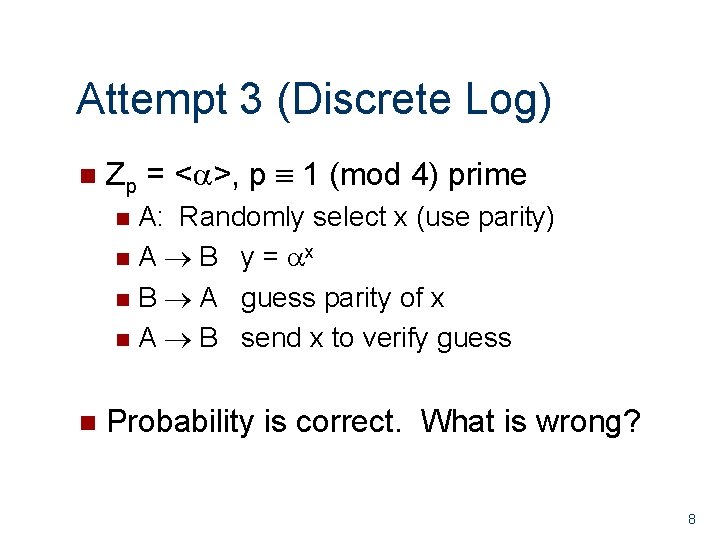
Attempt 3 (Discrete Log) n Zp = < >, p 1 (mod 4) prime A: Randomly select x (use parity) n A B y = x n B A guess parity of x n A B send x to verify guess n n Probability is correct. What is wrong? 8
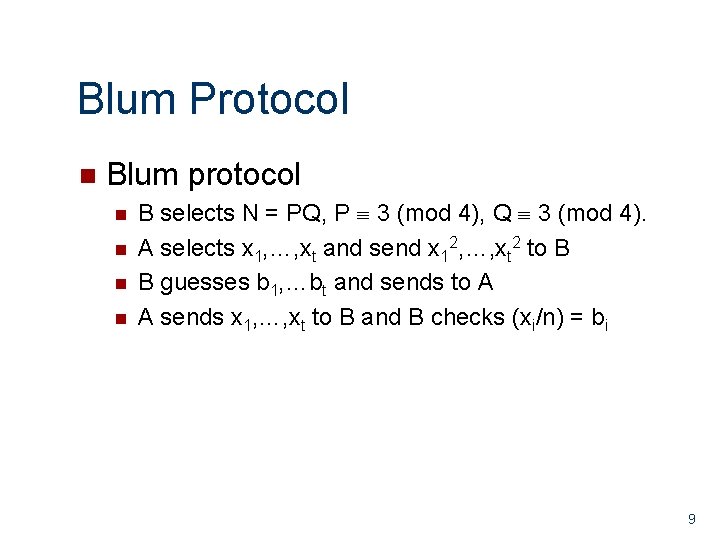
Blum Protocol n Blum protocol n n B selects N = PQ, P 3 (mod 4), Q 3 (mod 4). A selects x 1, …, xt and send x 12, …, xt 2 to B B guesses b 1, …bt and sends to A A sends x 1, …, xt to B and B checks (xi/n) = bi 9
![Correctness of Blum Protocol n Four solutions x 2 a (mod N) [use CRT] Correctness of Blum Protocol n Four solutions x 2 a (mod N) [use CRT]](http://slidetodoc.com/presentation_image_h2/14bc879d3c78ecb70ebe01f0400dec50/image-11.jpg)
Correctness of Blum Protocol n Four solutions x 2 a (mod N) [use CRT] n n P Q 3 (mod 4) J(-1, P) =J(-1, Q) = -1 § n (±b)2 a (mod P), (±c)2 a (mod Q) Half with J(x, N) = 1, half with J(x, N)= -1 Knowing ±b and ±c gives P and Q n b c (mod P) b = c (mod Q) gcd(b-c, N)=Q 10
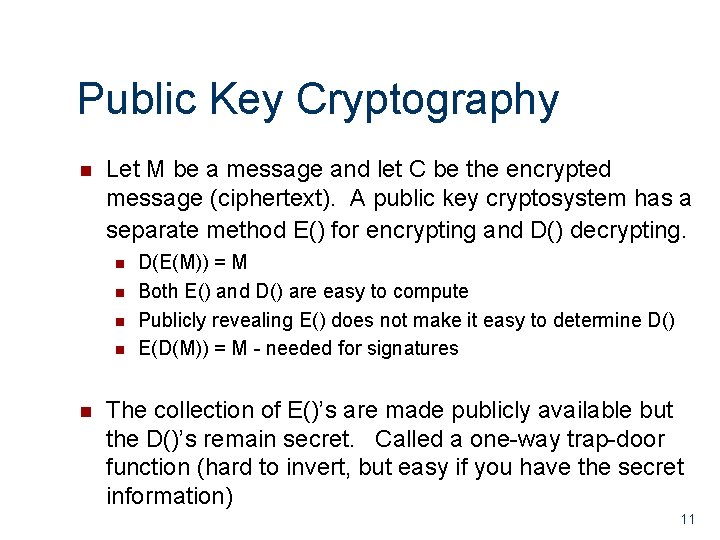
Public Key Cryptography n Let M be a message and let C be the encrypted message (ciphertext). A public key cryptosystem has a separate method E() for encrypting and D() decrypting. n n n D(E(M)) = M Both E() and D() are easy to compute Publicly revealing E() does not make it easy to determine D() E(D(M)) = M - needed for signatures The collection of E()’s are made publicly available but the D()’s remain secret. Called a one-way trap-door function (hard to invert, but easy if you have the secret information) 11
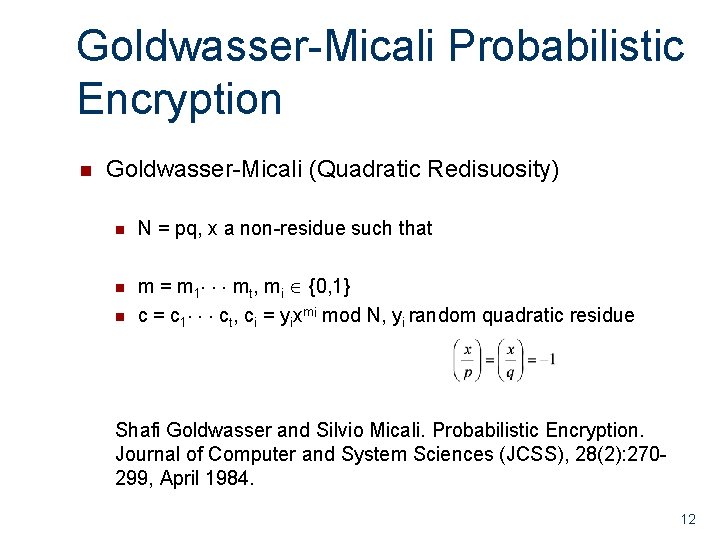
Goldwasser-Micali Probabilistic Encryption n Goldwasser-Micali (Quadratic Redisuosity) n N = pq, x a non-residue such that n m = m 1 mt, mi {0, 1} c = c 1 ct, ci = yixmi mod N, yi random quadratic residue n Shafi Goldwasser and Silvio Micali. Probabilistic Encryption. Journal of Computer and System Sciences (JCSS), 28(2): 270299, April 1984. 12
- Slides: 13