COEN 252 Computer Forensics Data Analysis Techniques for

- Slides: 111
COEN 252 Computer Forensics Data Analysis Techniques for Hard Drives
Data Analysis Techniques n Create forensic duplicate. Protect original as best evidence. n Review image file (with tools). n n n Report. Testify.
Data Analysis Techniques n Need collaboration between forensics investigators and case workers.
Data Analysis Techniques n Sources of Evidence n n n Existing Files Deleted Files Logs Special system files (registry, cron) Email archives, printer spools Administrative settings
Data Analysis Techniques n File restoration techniques n FAT, NTFS By hand with a hexeditor n Specialty tools like Norton undelete n Forensics software like encase, FTK n Mount drive on UNIX system and use UNIX tools (Fatback) n
Data Analysis Techniques n Unix system n n With a hex editor edit the link count in inodes, file will then be linked to Lost&Found debugfs to relink a file to Lost&Found in ext 2
Data Analysis Techniques Deleted files are overwritten if n Drive is wiped (e. g. part of PGP suite) n New files are created on the partition n New software is installed on the partition n Applications running may update the partition
Data Analysis Techniques Deleted files are overwritten if n The partition stores the %systemroot% directory and Windows modifies it for internal housekeeping. n If the partition contains the web browser cache n If the volume contains the TEMP directory
Data Analysis Techniques Deleted files are overwritten n At system shutdown / startup
Data Analysis Techniques Free, slack and unallocated space n Use a hex-editor n Use a specialty tool that generates a file by appending all slack and free space n Use a forensics tool Free: Outside of a partition. Slack: Allocated, but unused overhang in the last cluster of a file Unallocated: Not assigned to a current file.
Data Analysis Techniques First Task: n Generate database of all files n n Full path. MAC-dates & -times. Logical size of file. MD 5 hash (to counteract evidence deterioration).
Data Analysis Techniques n Generate database of all files n Use MD 5 hash to exclude well-known files from investigation.
Data Analysis Techniques n Prepare drive for string searches. n n Forensics tools do this automatically. Need to deal with proprietary formats. Compressed files need to be uncompressed. Encrypted files need to be unencrypted.
Data Analysis Techniques n Perform string searches n n On UNIX, use grep. Forensics tools preprocess forensic duplicates.
Data Analysis Techniques n Perform String Searches n n The “How” is easier than the “What”. Investigator and analyst need to work together: n n “What are we looking for? ” “What information do we need? ”
Data Analysis Techniques Example: The hard drive of a robbery suspect contains numerous references to his “little excursions”. To tie the suspect to the computer, establish usage by suspect alone by: n n n Finding personal pictures (look for jpg). Restore old emails. Restore chat sessions. http: //www. signonsandiego. com/news/metro/santana/200103129999_1 n 12 compute. html
Data Analysis Techniques What to look for Email n Primary Source of Evidence. n Email in transit is protected by the EPCA and other statutes. n Checking email after transition is treated similar to searches of files.
Data Analysis Techniques What to look for n Print Spooler Files. n n Typically deleted right after printing. Might not be overwritten.
Data Analysis Techniques What to look for n Web Cache Evidence n n n All web browsers cache. Some delete files after session closes. Ex. : United States v. Tucker: The government introduced Internet conversations taken from Tucker's computer which showed that while he was looking for pictures he stated that he was into "young action" and would "like to start trading (3)27" and introduced a listing of Internet conversations documenting Tucker's trading of such images. United States Court of Appeals, Eleventh Circuit. No. 97 -2767
Data Analysis Techniques What to look for n Swap Files / Virtual Memory Files n n n Can be very large. Use Forensics Tools like Encase Alternatively: Hex Editors, Norton Disk Commander (under Windows)
Windows Data Analysis n n n Perform keyword searches. Review Logs. Review Registry. Review swap files. Review special application files: n n Internet Cache Recycle Bin Printer Spool Email Files
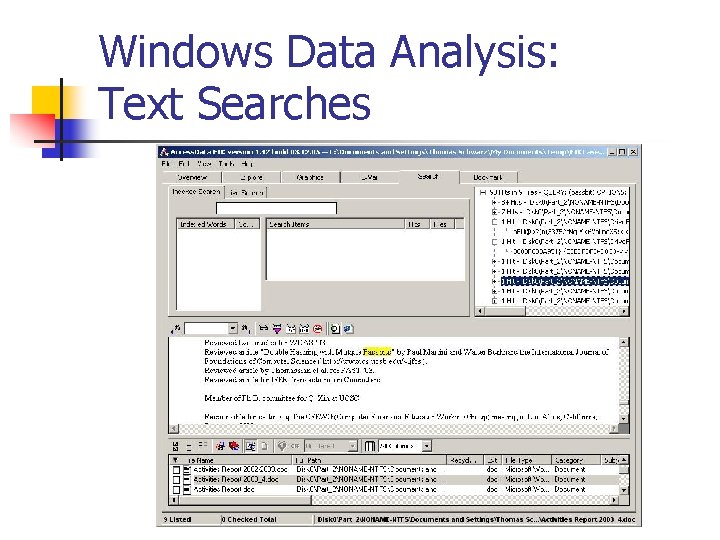
Windows Data Analysis: Text Searches n Raw Data Level n n Bin. Text (Foundstone) Disk Investigator (K. Soloway) Sector. Spy. XP (Mc. Camy, Lexun Freeware) Forensics Tools n n n Encase FTK Mareswares
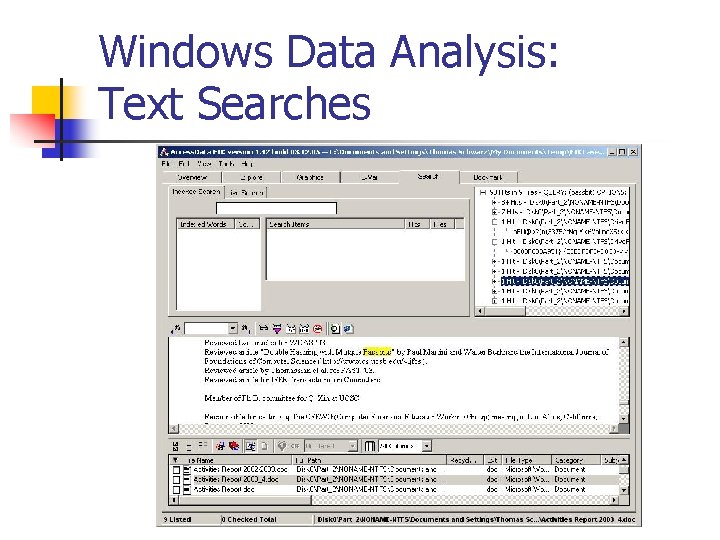
Windows Data Analysis: Text Searches
Windows Data Analysis Logs Windows NT, 2000, XP maintain log files n System Log n Application Log n Security Log
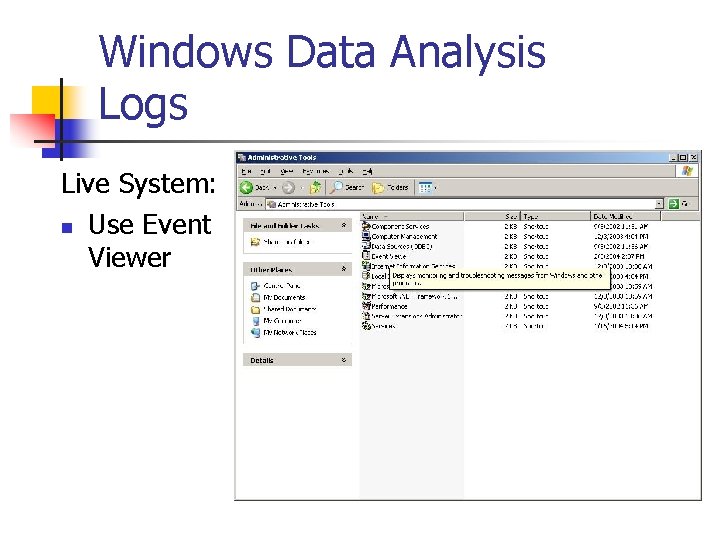
Windows Data Analysis Logs Live System: n Use Event Viewer
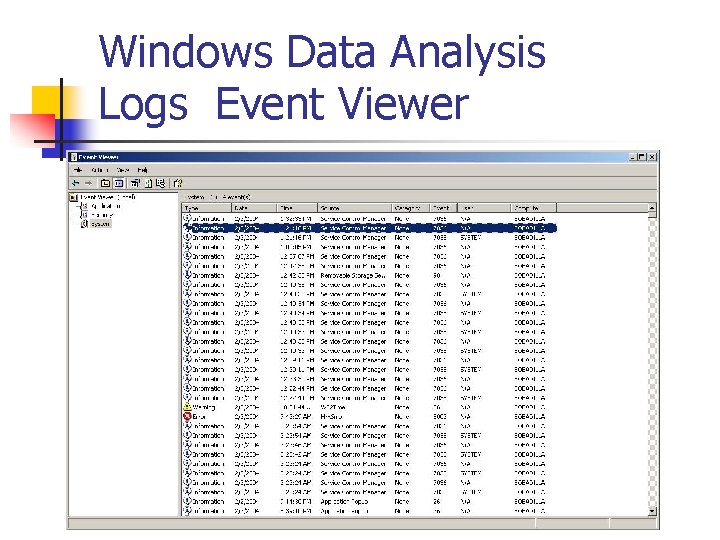
Windows Data Analysis Logs Event Viewer n Event Viewer
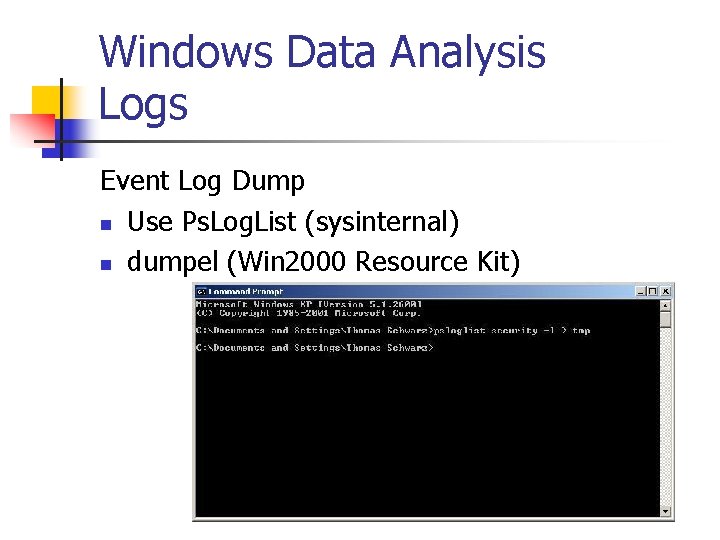
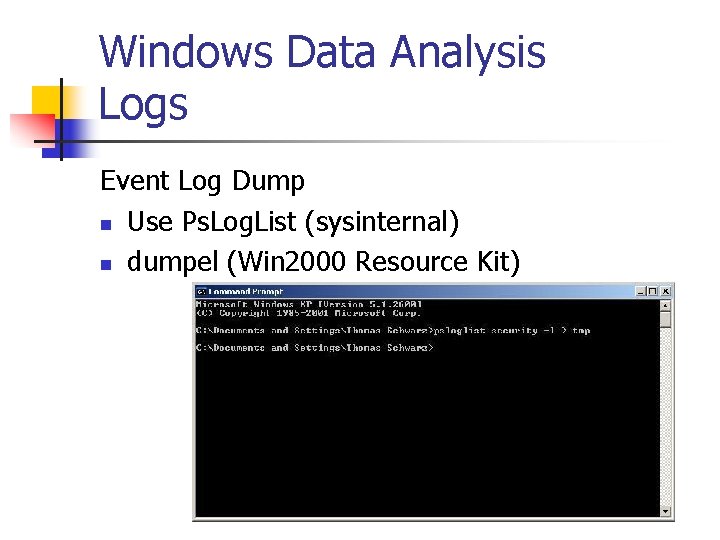
Windows Data Analysis Logs Event Log Dump n Use Ps. Log. List (sysinternal) n dumpel (Win 2000 Resource Kit)
Windows Data Analysis Logs From forensics duplicate n secevent. evt n appevent. evt n sysevent. evt
Windows Data Analysis Logs Drawbacks n Default security logging is “no logging”. n Do not record IP addresses n Application log uses localized settings. (Forensics workstation will not interpret these. )
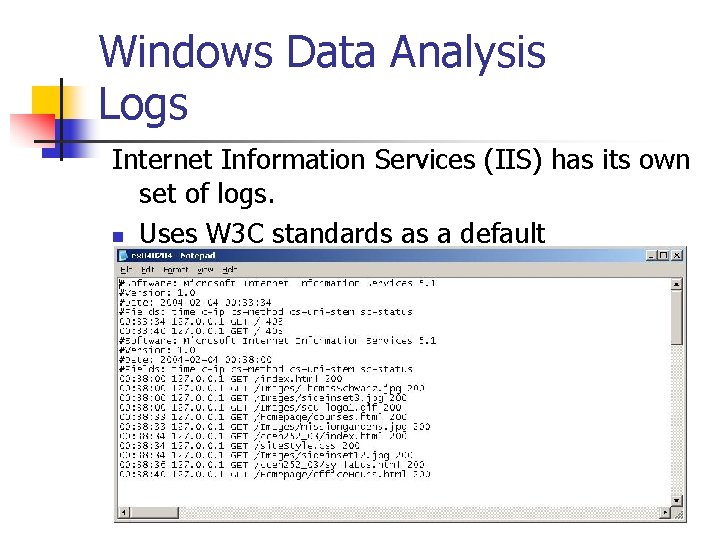
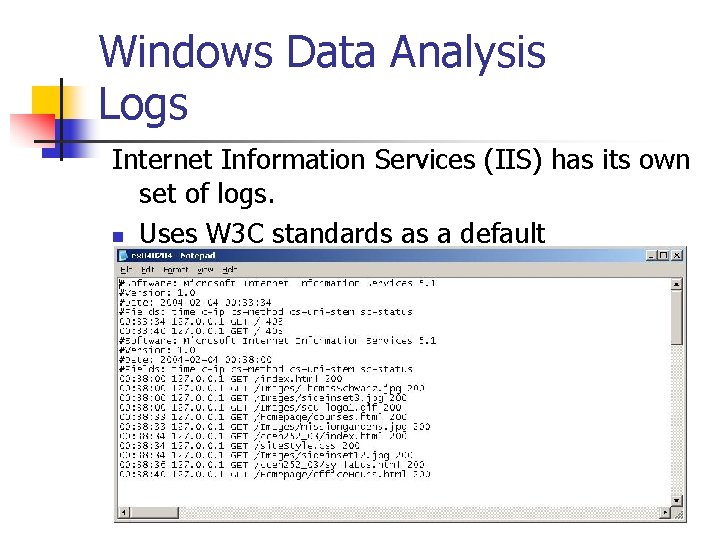
Windows Data Analysis Logs Internet Information Services (IIS) has its own set of logs. n Uses W 3 C standards as a default
Windows Data Analysis Logs n n n Need to be enabled. More important for incidence response than for law enforcement. Get HTTP status codes.
Windows Data Analysis Logs n Many other applications log: n n Internal firewalls. Create your own log from the timestamp of files around critical times. n File. List (www. forensics-intl. com) will do this for you.
Windows Data Analysis Reviewing Relevant Files n Recycle Bin n Date and Time of Deletion in n Folder Recycled in Win 95/98. Folder Recycler in Win. NT/2000/XP. System file INFO in Win 95 System file INFO 2 in Win 98 Information available in Win 2000, Win. XP
Windows Data Analysis Reviewing Relevant Files n n n Windows moves deleted file into the recycle bin. It deletes from there. Thus, files can be retrieved from deleted recycle bin entries.
Windows Data Analysis Reviewing Relevant Files n n $Logfile entry in the MFT contains the log of all file system transactions Deletion of a file leaves several entries in $Logfile Not unusual to find files that are no longer on the disk Shows that file was used by the system
Windows Data Analysis Reviewing Relevant Files n n Shortcuts can contain relevant information. Stored in the desktop folder. A special agent of the Illinois Attorney General’s Office investigated a case involving child pornography. The agent located a shortcut file in the Windows/Desktop folder whose target was a screensaver program. Upon examining the screensaver program, the agent found that it caused 30 images depicting child pornography to be displayed on the computer’s monitor when the shortcut was activated. Casey, p. 153
Windows Data Analysis Reviewing Relevant Files n Thumbs. db (System file) n n n Contains thumbs pictures for folder. Not perfectly synchronized with folder. Deleted images might still be available.
Windows Data Analysis Reviewing Relevant Files n Temporary files n n n Emails with large attachments: n n Files with extension tmp Created by many applications Attachments are probably stored as temp files. (Depends on email system. ) Look for file extensions. tmp.
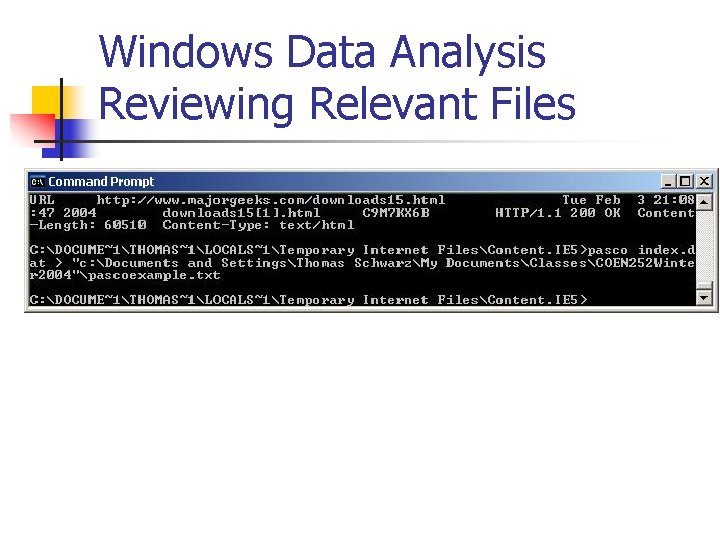
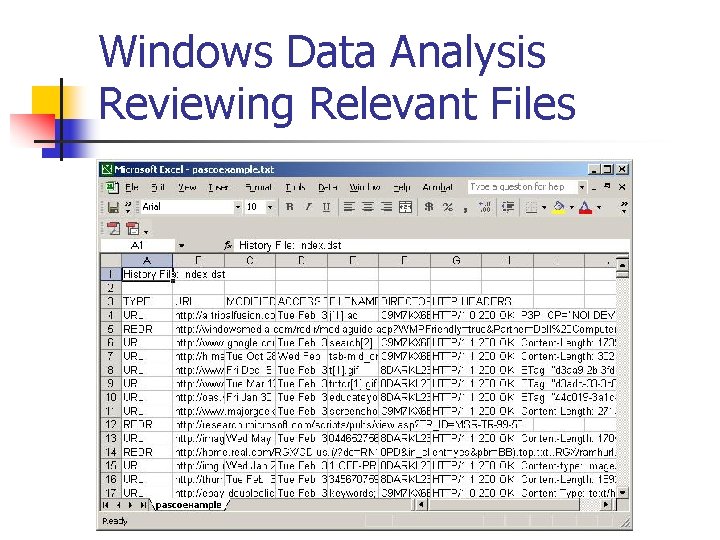
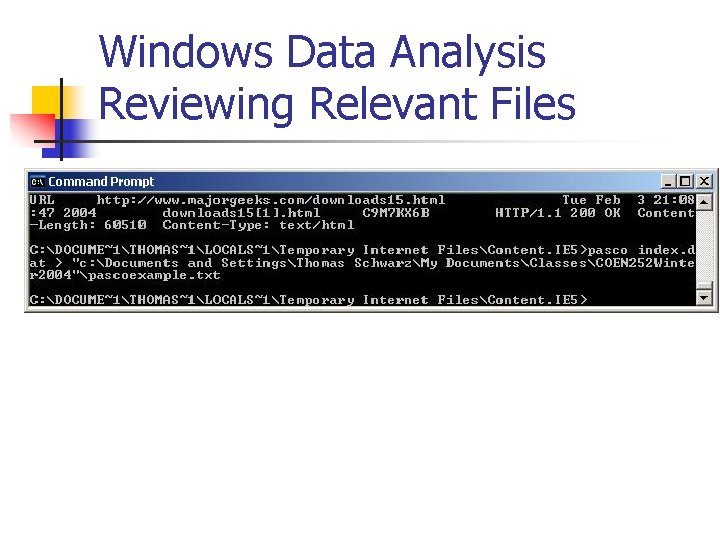
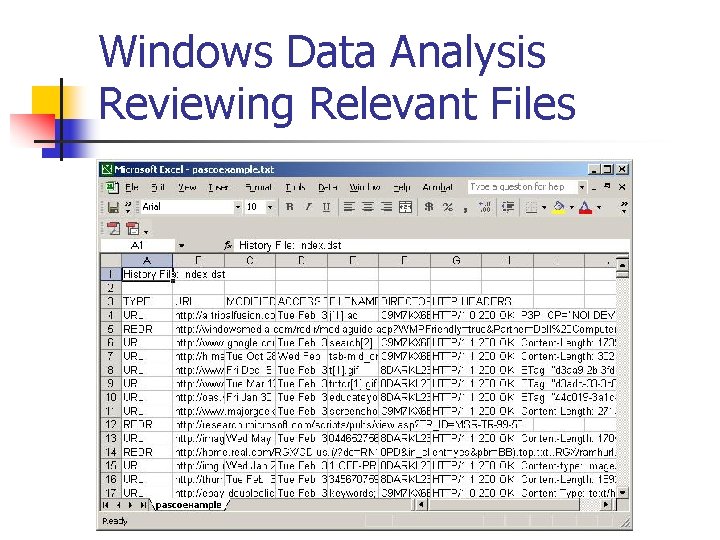
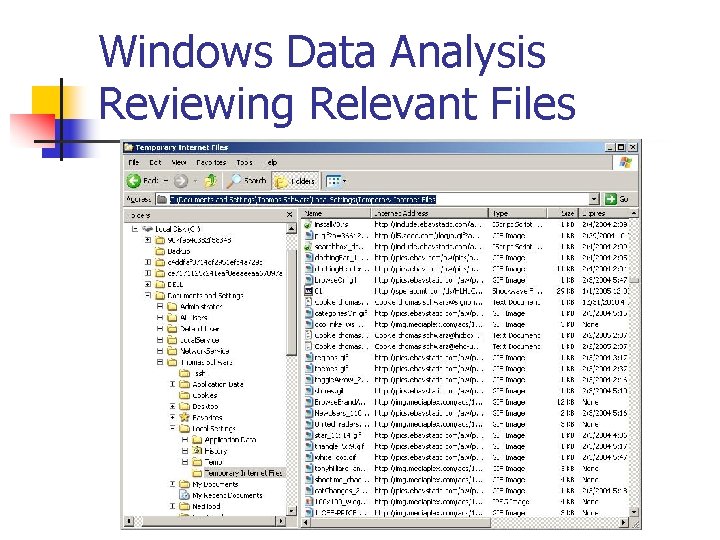
Windows Data Analysis Reviewing Relevant Files n n Internet Explorer (as well as other browsers) use a cache. index. dat contains internet explorer cached websites. Written in binary. Use Pasco from Foundstone.
Windows Data Analysis Reviewing Relevant Files
Windows Data Analysis Reviewing Relevant Files
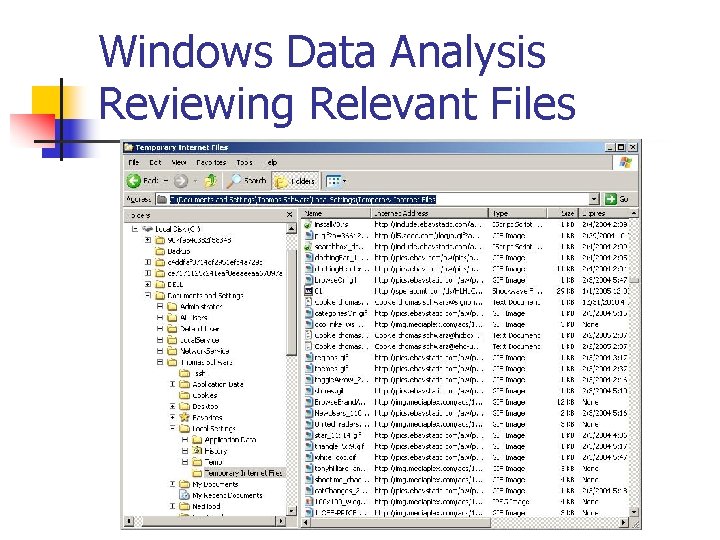
Windows Data Analysis Reviewing Relevant Files n Browser Cache C: Documents and Settings Username Local SettingsTemporary Internet Files Or n C: Program FilesNetscapeUsers UsernameCache n
Windows Data Analysis Reviewing Relevant Files
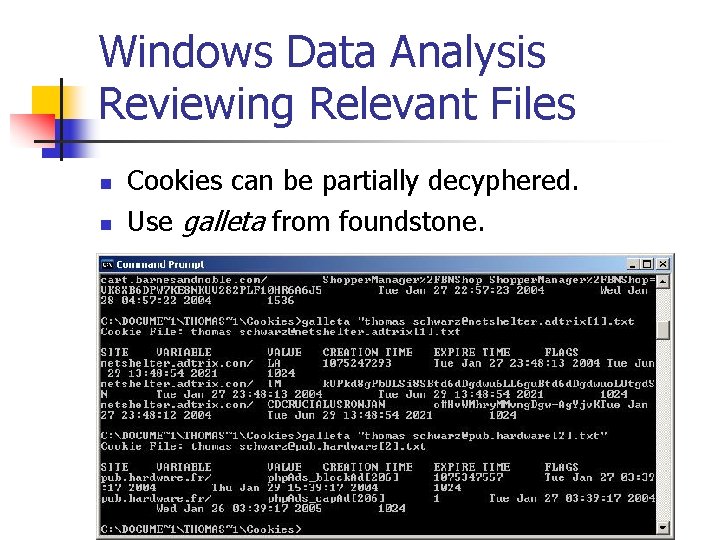
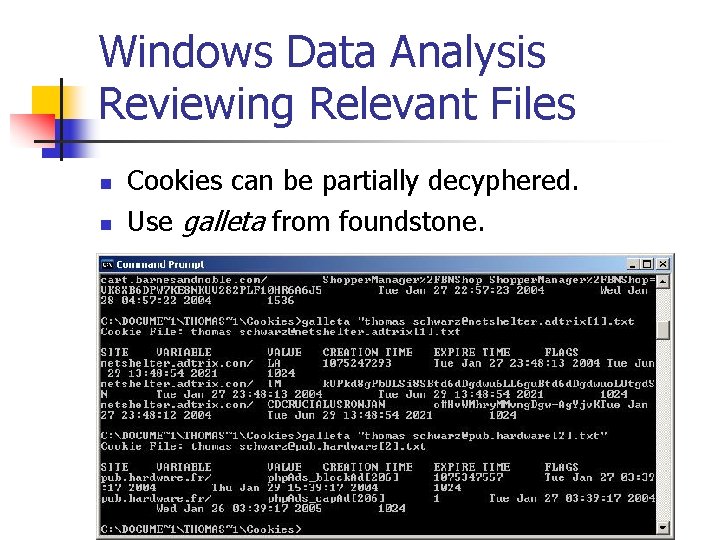
Windows Data Analysis Reviewing Relevant Files n n Cookies can be partially decyphered. Use galleta from foundstone.
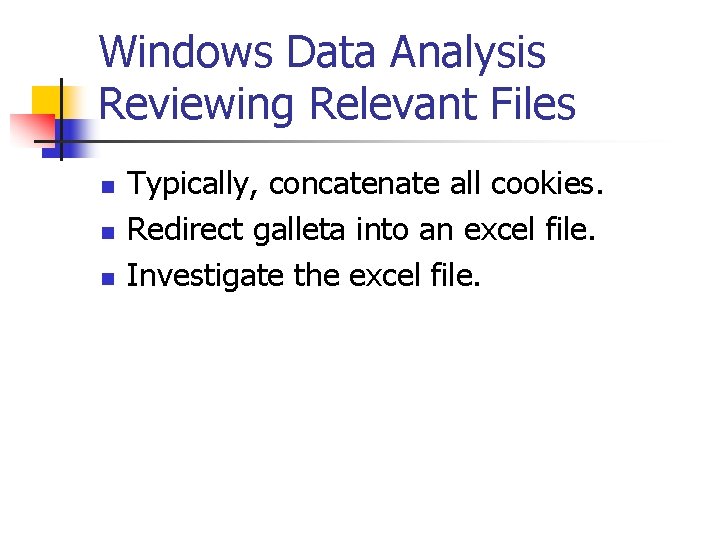
Windows Data Analysis Reviewing Relevant Files n n n Typically, concatenate all cookies. Redirect galleta into an excel file. Investigate the excel file.
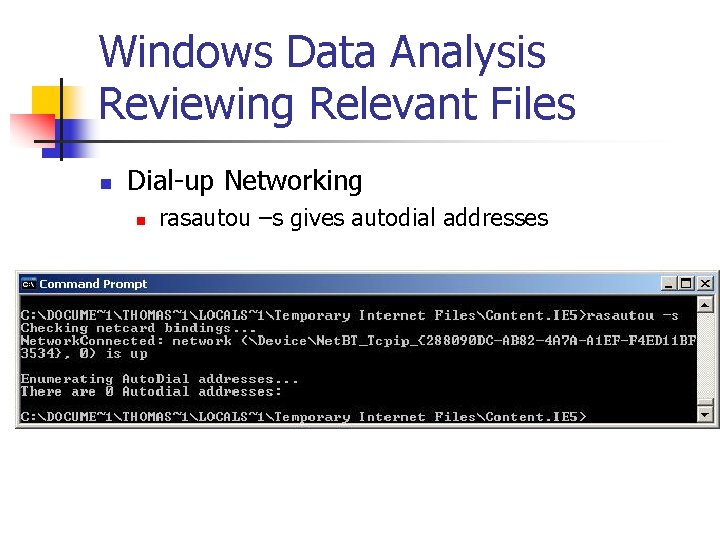
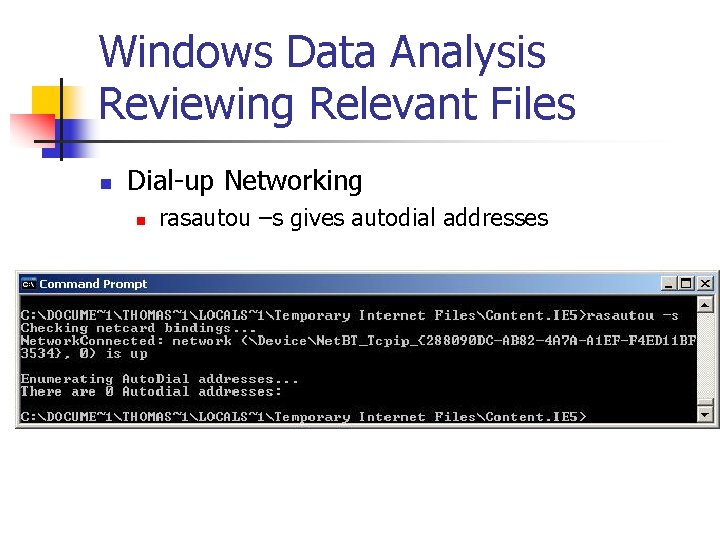
Windows Data Analysis Reviewing Relevant Files n Dial-up Networking n rasautou –s gives autodial addresses
Windows Data Analysis Registry n n Database that stores settings and options for 32 b MSWin OS Contains information and setting for n n Hardware Software Users Preferences
Windows Data Analysis Registry Win 95, Win 98 n USER. DAT, SYSTEM. DAT in Windows Win. ME n USER. DAT, SYSTEM. DAT, CLASSES. DAT Win. NT, 2000, XP n In %System. Root%System 32Config
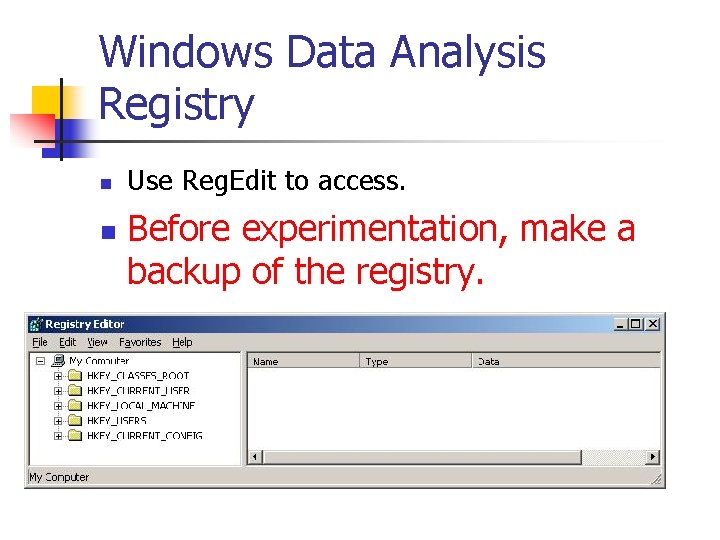
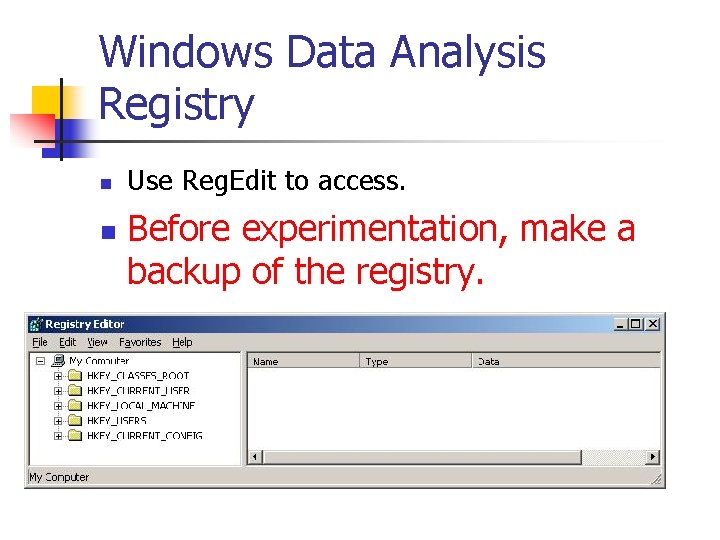
Windows Data Analysis Registry n n Use Reg. Edit to access. Before experimentation, make a backup of the registry.
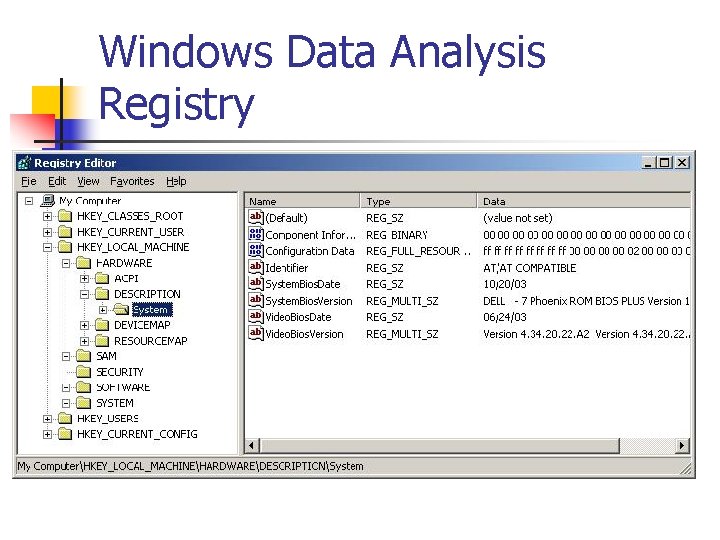
Windows Data Analysis Registry n n Hierarchical structure Main branches are Hives contain keys. Keys can contain subkeys and values
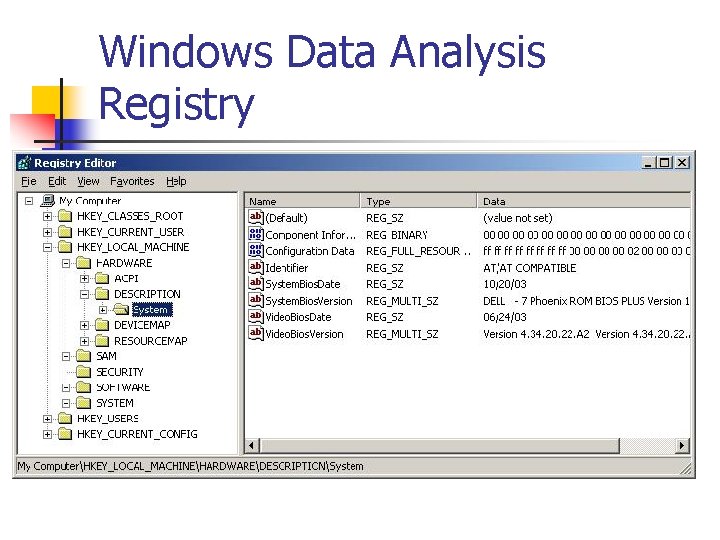
Windows Data Analysis Registry
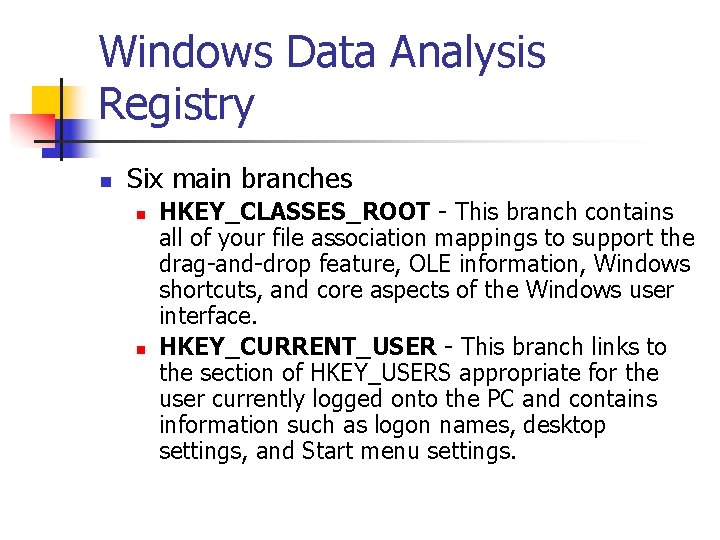
Windows Data Analysis Registry n Six main branches n n HKEY_CLASSES_ROOT - This branch contains all of your file association mappings to support the drag-and-drop feature, OLE information, Windows shortcuts, and core aspects of the Windows user interface. HKEY_CURRENT_USER - This branch links to the section of HKEY_USERS appropriate for the user currently logged onto the PC and contains information such as logon names, desktop settings, and Start menu settings.
Windows Data Analysis Registry n n HKEY_LOCAL_MACHINE - This branch contains computer specific information about the type of hardware, software, and other preferences on a given PC, this information is used for all users who log onto this computer. HKEY_USERS - This branch contains individual preferences for each user of the computer, each user is represented by a SID sub-key located under the main branch.
Windows Data Analysis Registry n n HKEY_CURRENT_CONFIG - links to the section of HKEY_LOCAL_MACHINE appropriate for the current hardware configuration. HKEY_DYN_DATA - points to the part of HKEY_LOCAL_MACHINE, for use with the Plug-&-Play features of Windows, this section is dynamic and will change as devices are added and removed from the system.
Windows Data Analysis Registry n n n Registry Editor can import and export registry settings to / from a text file. Copy registry hive files from the forensic duplicate to your forensic work station. Import them into regedit. IF YOU MESS UP THE REGISTRY, YOU NEED TO REBUILD YOUR SYSTEM.
Windows Data Analysis Registry In a recent investigation by the Los Angeles County Sheriff’s Computer Crime Unit, a detective investigated an employee suspected of misappropriating confidential computer information stored by his company. When the detective examined one of the workplace computers, he found remnants of a key-trapping program in the registry. During an interview, the suspect admitted to having installed, used, and deleted the key-trapping program for the purposes of obtaining user names and passwords of coworkers.
Windows Data Analysis Registry n Use the registry to n n Find installed software (such as L 0 phtcrack). Manually deleted software. Use backups of the registry to trace the installation and uninstallation of software. Find data on user accounts
Windows Data Analysis Registry n Use the registry to n n obtain listing of applications that are set to run automatically obtain registry entries that have been modified lately n Registry keys have Last. Write time n n 64 b value representing 100 nanoseconds since January 1, 1601. User accounts
Windows Data Analysis MS Word files n Word documents contain a revision log. n n n Used by Richard M. Smith to investigate a press release by PM Blair. Turned out that press released was mainly a copy of an Middle East Review of International Affairs article. . pdf, . html, … files generated from. doc files do not have this revision history.
Windows Data Analysis. pfd files n . pdf files also contain meta-data n Accessible in Adobe Reader
Windows Data Analysis Unusual or Hidden Files n n n NTSF uses a feature from Mac Hierarchical File System to store multiple entry under one file entry. “Data Streams” Allow us to hide a file cp nc. exe logo. jpg: nc. exe Now nc. exe is hidden. Use SFind (foundstone) to find stremed files.
Windows Data Analysis Print Spooler Files n n Print Spooler Files. (EMF under Win). EMF files are deleted after printing. n n n “Gap-Toothed Bandit”, Micheal Craig Dickman, used proceeds from bank robberies to support his struggling biotech start-up. Arrested after a heist in La Jolla, 1999. SD RCFL found the demand notes as a deleted EMF file on his laptop.
Data Analysis Techniques What to look for n Print Spooling uses temporary files. n n n contain data to be printed. data on the print job. Two methods, RAW and EMF n n n Shadow file. SHD info on print job. SPL contains data to be printed (RAW). SPL contains file name, method, list of files with print data EMF****. TMP
Data Analysis Techniques What to look for Department of Consumer Affairs in Orange County, CA, arrested a suspect for selling counterfeit state license certificates and seized his computer. Although the examiners had seized some of the counterfeit certificates from victims, they were unable to locate evidence on the computer. When the examiners requested a second review from the California Department of Insurance, Fraud Division, the Computer Forensics Team identified several deleted enhanced metafiles that exactly matched the paper copies that had been seized during the investigation. The only evidence present on the drive were the enhanced metafiles. The defendant was convicted at trial. Casey, p. 163
Windows Data Analysis Rogue Processes To find rogue processes on a duplicate image n Restore the file system. n Run a virus software. n Disable writing to restored volume.
Windows Data Analysis Find Hidden Doors n Schedule an event remote /s “cmd. exe” mysystem n Remote command from NT Resource Kit remote /c “cmd. exe” mysystem n n Allows to connect with a command prompt from outside the system Schedule this with the at or the soon utility
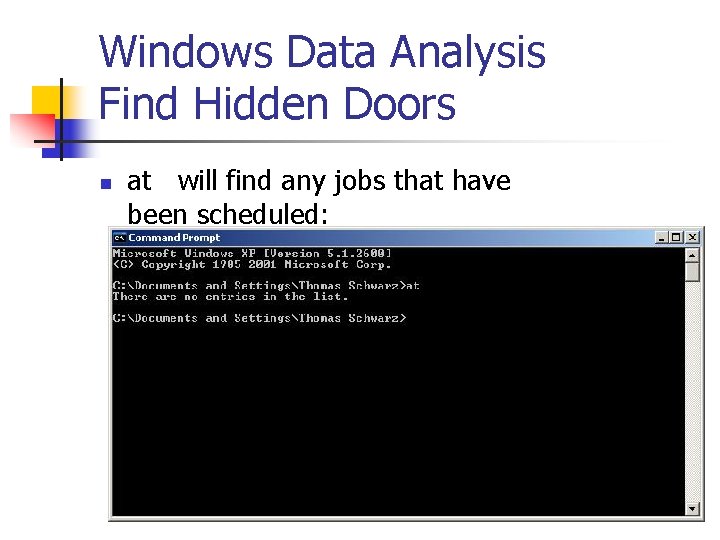
Windows Data Analysis Find Hidden Doors n at will find any jobs that have been scheduled:
Windows Data Analysis Review last searches n n Use AFind (foundstone) to look for the last few files accessed. Look at the Find scrollbox.
UNIX Data Analysis n n n n Review all pertinent logs Perform keyword searches Review relevant files Identify unauthorized user accounts or groups Identify rogue processes Check for unauthorized access points Analyze trust relationships Check for kernel module rootkits
Unix Data Analysis Logs n n Unix maintains a variety of logs. A hacker could change the logs. But you need to look at them. Placed in directories depending on UNIX flavor n n n /var/log usr/adm Var/adm
UNIX Data Analysis Logs n n syslog Controlled by /etc/syslog. conf Uses syslogd Can be used to log remotely
Unix Data Analysis Logs n n Look at the syslog. conf Three fields: n n n Facility field: subsystem that produced the log (e. g. mail) Priority field: debug, info, notice, warning, err, crit, alert, emerg Action field: how is the log recorded, typically name of log field (or IP address)
Unix Data Analysis Logs n Log entries n n n In ASCII Usually world-readable Only writable by root
Unix Data Analysis Logs Remote Syslog Server logs n Attackers with root privileges can change the logs n Use a remote syslog server for safety n Attacker can add spurious entries to the remote syslog n Harden remote syslog server
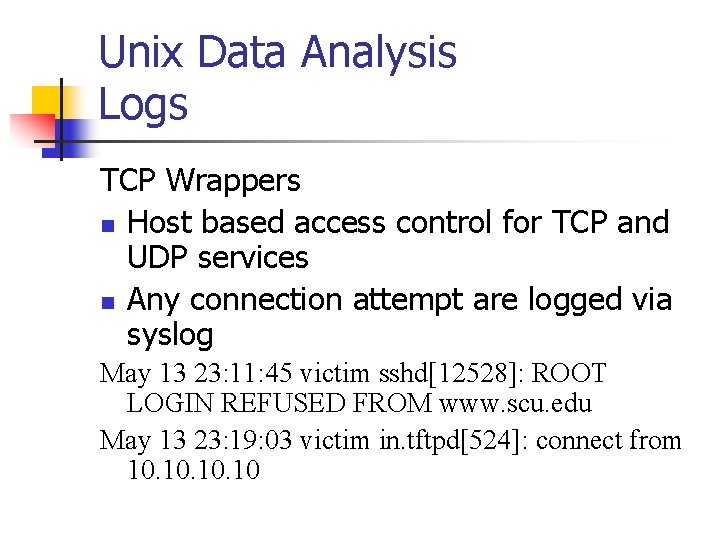
Unix Data Analysis Logs TCP Wrappers n Host based access control for TCP and UDP services n Any connection attempt are logged via syslog May 13 23: 11: 45 victim sshd[12528]: ROOT LOGIN REFUSED FROM www. scu. edu May 13 23: 19: 03 victim in. tftpd[524]: connect from 10. 10. 10
Unix Data Analysis Logs Other network logs n Server specific logs, e. g. for FTP
Unix Data Analysis Host Logging n su command logs n n n Part of syslog Stored in var/log/messages Currently logged in users n n n Stored in utmp or wtmp Use w, who, finger, last to read Modified by many hacker tools
Unix Data Analysis Host Logging Logon attempt logs n Recorded on most UNIX machines n /var/messages in LINUX
Unix Data Analysis Host Logging cron n Allows users to schedule programs for future execution n Often used for attacks n Logged, typically in /var/cron/log
Unix Data Analysis User Activity Logging n n Every command by every user can be logged Shells store history files for each user
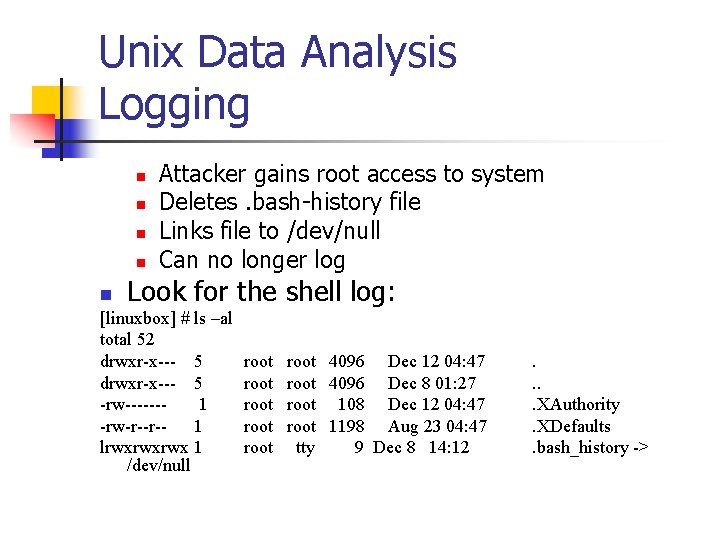
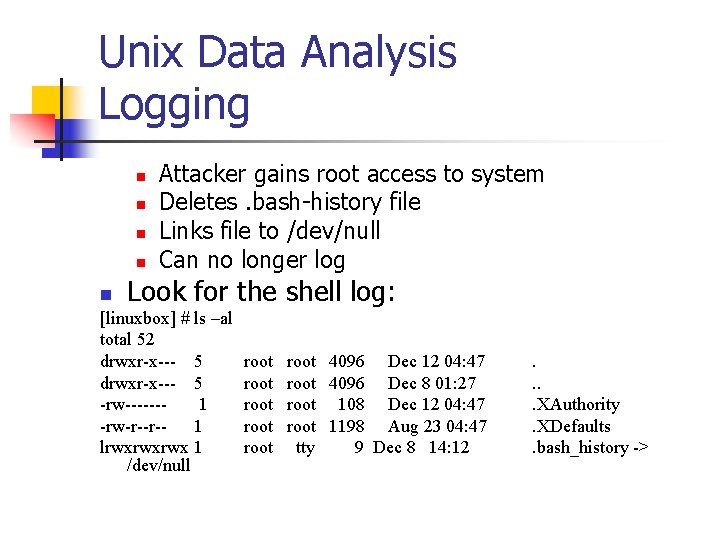
Unix Data Analysis Logging n n Attacker gains root access to system Deletes. bash-history file Links file to /dev/null Can no longer log Look for the shell log: n [linuxbox] # ls –al total 52 drwxr-x--- 5 -rw------1 -rw-r--r-1 lrwxrwxrwx 1 /dev/null root root 4096 Dec 12 04: 47 root 4096 Dec 8 01: 27 root 108 Dec 12 04: 47 root 1198 Aug 23 04: 47 tty 9 Dec 8 14: 12 . . XAuthority. XDefaults. bash_history ->
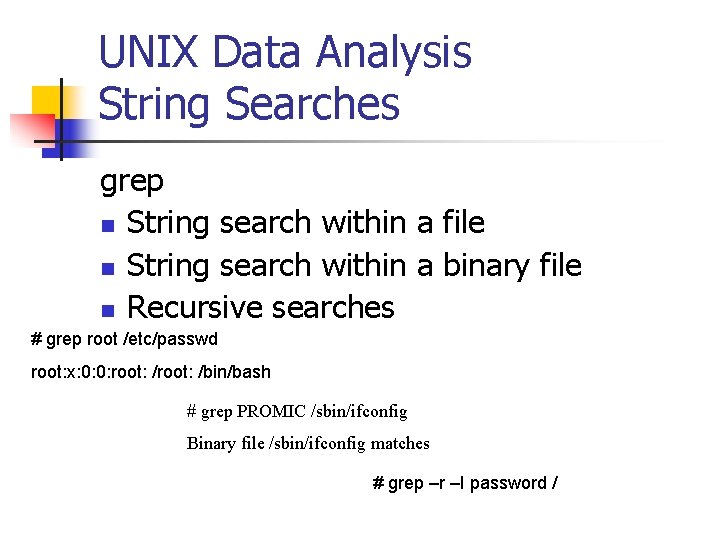
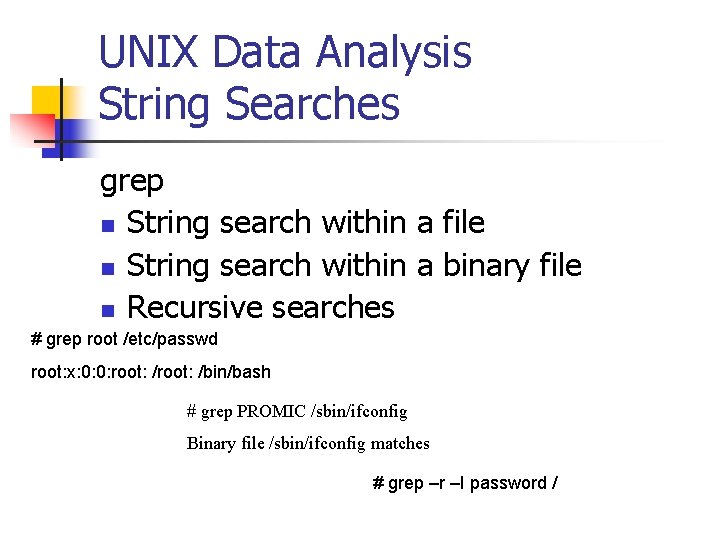
UNIX Data Analysis String Searches grep n String search within a file n String search within a binary file n Recursive searches # grep root /etc/passwd root: x: 0: 0: root: /bin/bash # grep PROMIC /sbin/ifconfig Binary file /sbin/ifconfig matches # grep –r –I password /
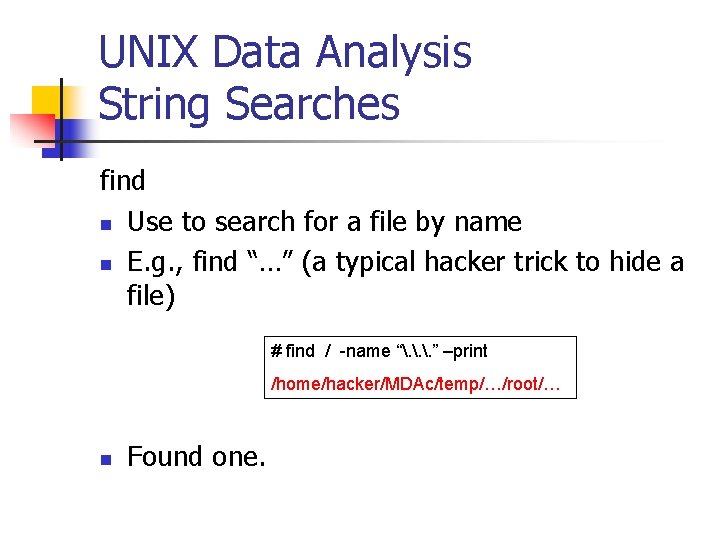
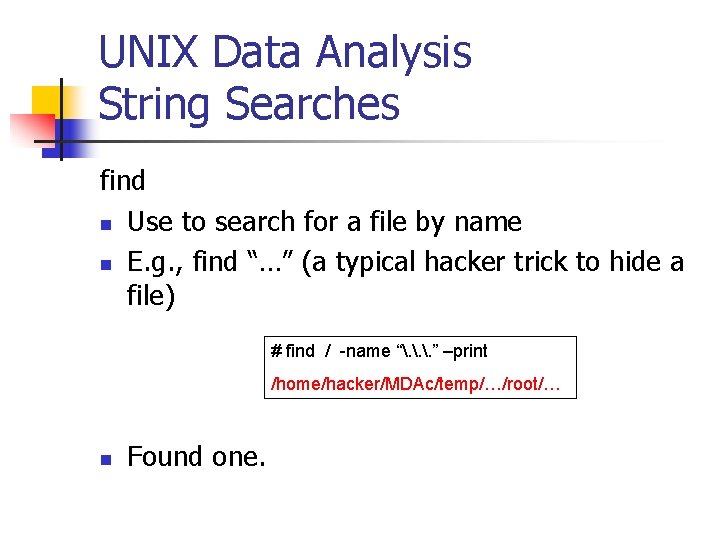
UNIX Data Analysis String Searches find n Use to search for a file by name n E. g. , find “…” (a typical hacker trick to hide a file) # find / -name “. . . ” –print /home/hacker/MDAc/temp/…/root/… n Found one.
UNIX Data Analysis Relevant Files n n n Finding relevant files after an incident is an art. Careful about destroying evidence by running system commands that will change times. Mount evidence drive read-only or better, duplicate.
UNIX Data Analysis Relevant Files n n n Identify the time of the incident. Look for files accessed, created or modified around that time. Use find with –atime, -ctime, -mtime option
UNIX Data Analysis Relevant Files: SUID Programs n n n UNIX allows applications to set the userid (SUID) and set the group-id (SGID). Programs runs with privileges of owner, typically root. Programs are source of most privilege escalation attacks.
UNIX Data Analysis Relevant Files: SUID Programs n n n Sometimes unprivileged users need to accomplish tasks that require high privileges. For example, passwd needs to access the password file in /etc/passwd But users should not be given access to /etc/passwd
UNIX Data Analysis Relevant Files: SUID Programs n n User invokes passwd changes its UID (with SUID) passwd now runs with root UID passwd can now access the password file.
UNIX Data Analysis Relevant Files: SUID Programs n n You recognize these programs with ls –l File permission have an s instead of an x n n -rwsr-xr-- SUID program -rwxr-sr-- SGID program
UNIX Data Analysis Relevant Files: SUID Programs SECURITY INCIDENT EXAMPLE n Superuser is logged on as root and leaves terminal unattended # cp /bin/sh /tmp/break-acct #chmod 4755 /tmp/break-acct n n Creates SUID shell. Anyone invoking /tmp/break-account gets root privileges.
UNIX Data Analysis Relevant Files: SUID Programs Old Break-in n n /usr/lib/preserve is used by vi and ex editors to make an automatic backup of a file that is edited when the users suddenly disconnects. preserve writes file changes to a temp file in a special directory
UNIX Data Analysis Relevant Files: SUID Programs n n n preserve uses /bin/mail to send the user a notification that the file has been saved. This temp file should not be accessible by world. Thus, preserve needs root privileges
UNIX Data Analysis Relevant Files: SUID Programs n n preserve was installed as SUID root. preserve ran /bin/mail as root. preserve executed the mail program with the system function call. system uses sh to parse the string that it executes.
UNIX Data Analysis Relevant Files: SUID Programs Problem: n Shell variable IFS tells sh how to interpret the white spaces. n Normally sets white spaces to be space, tab, enter, etc. n Attacker sets white spaces to “/”
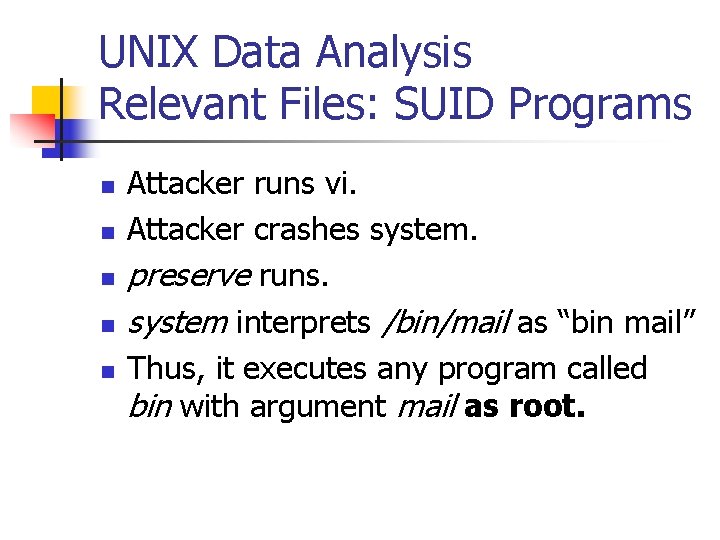
UNIX Data Analysis Relevant Files: SUID Programs n n n Attacker runs vi. Attacker crashes system. preserve runs. system interprets /bin/mail as “bin mail” Thus, it executes any program called bin with argument mail as root.

UNIX Data Analysis Relevant Files: SUID Programs n Find all SUID SGID with the following command: # find / ( -perm -00400 –o –perm -002000 ) –type f -print n n n find starts in / Looks for files with permission 002000 (SGID) or 004000 (SUID) Know what to expect.
UNIX Data Analysis Relevant Files: Hidden Files Hide “bad” files n By giving them innocuous names n By giving a name similar to a reasonable name “ syslog” vs. “syslog” n Calling a directory “…” (“. ” current directory, “. . ” parent directory)
UNIX Data Analysis Relevant Files: Configuration Files n n n Primary target to keep access for a hacker. etc/hosts. allow etc/hosts. deny determine access policy. /etc/inetd. conf controls network services
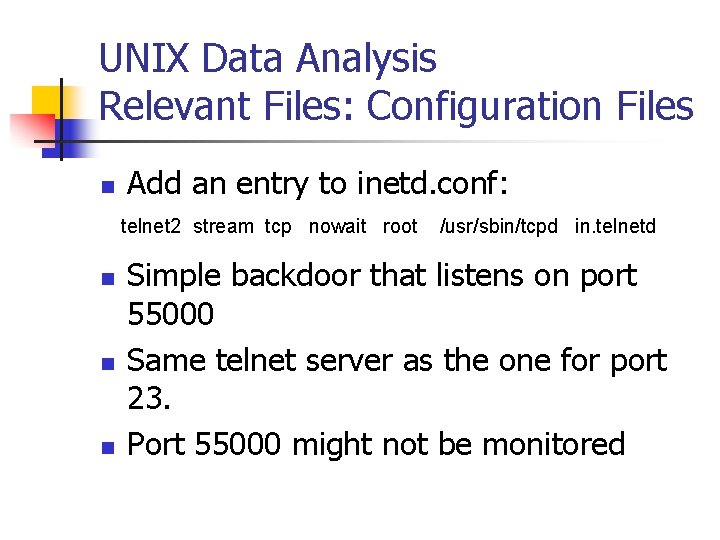
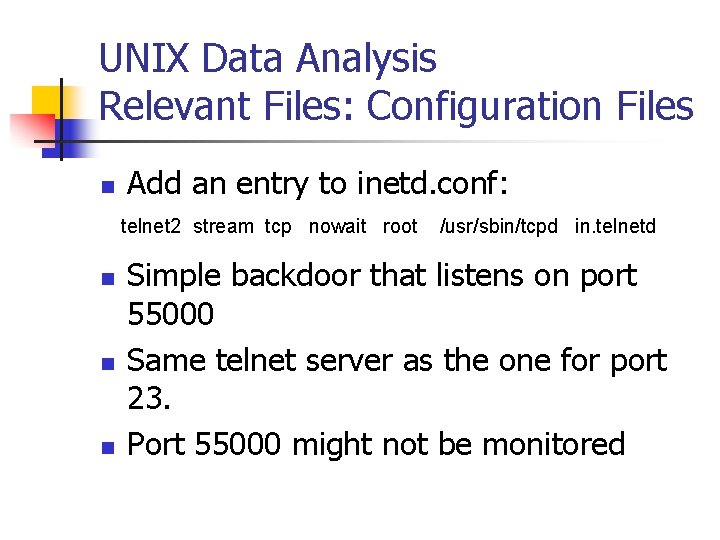
UNIX Data Analysis Relevant Files: Configuration Files n Add an entry to inetd. conf: telnet 2 stream tcp nowait root n n n /usr/sbin/tcpd in. telnetd Simple backdoor that listens on port 55000 Same telnet server as the one for port 23. Port 55000 might not be monitored
UNIX Data Analysis Relevant Files: cron n n cron facility used to schedule future executions of programs /var/spool/cron /usr/spool/cron stores cron jobs /etc/rc. d contains a listing of programs that start when UNIX boots. Check all startup scripts for trojans.
UNIX Data Analysis Phone Home n n n Outgoing traffic is usually not monitored. Compromised system uses cron to initiate a connection to an outside system. Outside system can control the compromised system.
UNIX Data Analysis Relevant Files: Startup n n User home directory contain startup files. . login. profile. cshrc
UNIX Data Analysis Relevant Files: /tmp n n Only world-writable file system on a typical UNIX system. Hangout for nefarious tools.
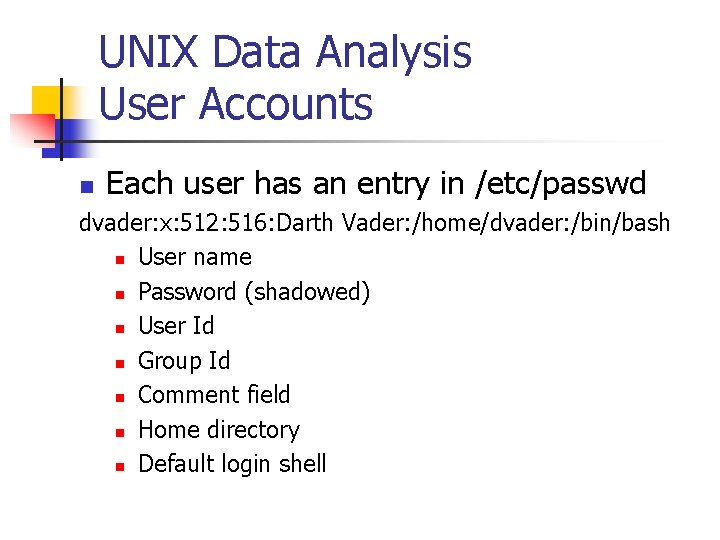
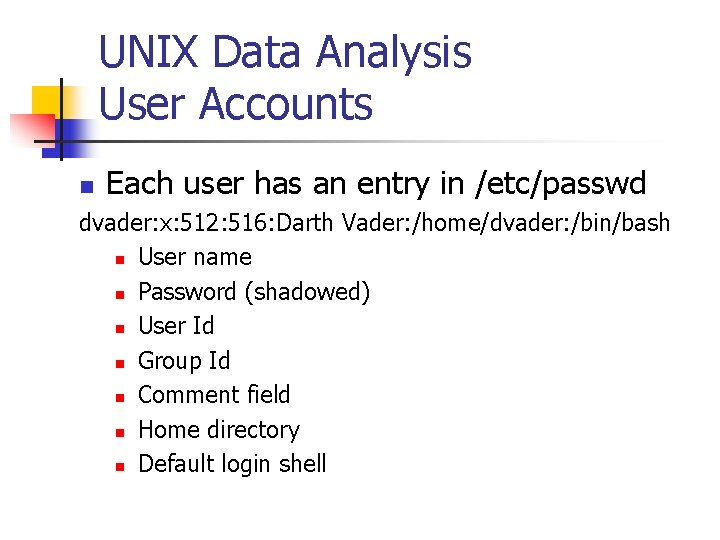
UNIX Data Analysis User Accounts n Each user has an entry in /etc/passwd dvader: x: 512: 516: Darth Vader: /home/dvader: /bin/bash n User name n Password (shadowed) n User Id n Group Id n Comment field n Home directory n Default login shell
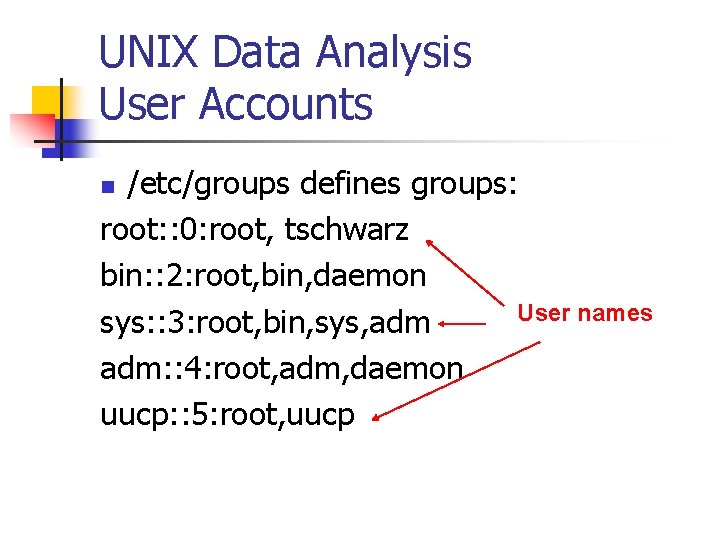
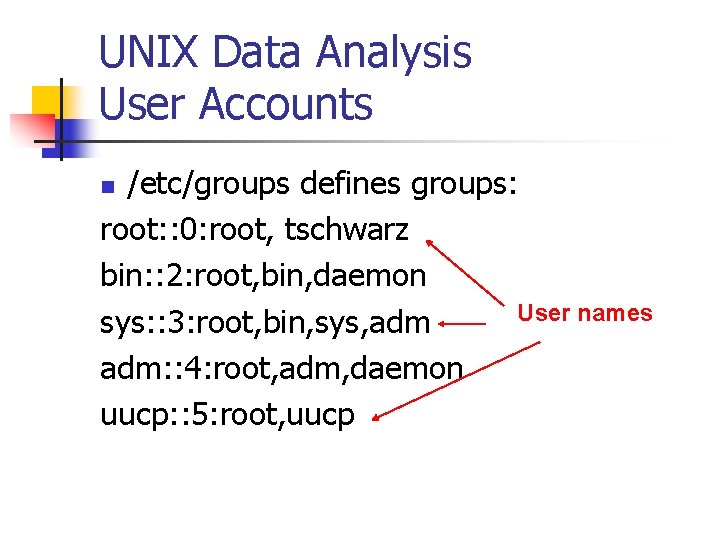
UNIX Data Analysis User Accounts /etc/groups defines groups: root: : 0: root, tschwarz bin: : 2: root, bin, daemon User names sys: : 3: root, bin, sys, adm: : 4: root, adm, daemon uucp: : 5: root, uucp n
UNIX Data Analysis User Accounts n If suspicious of compromise, investigate user accounts and group accounts.
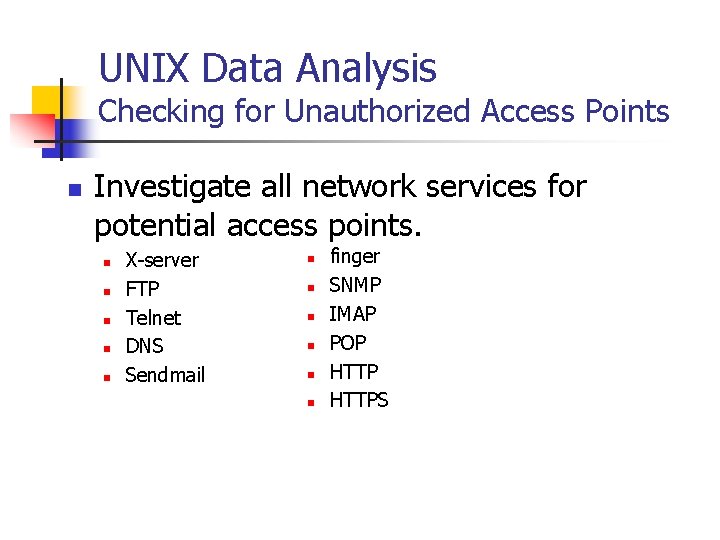
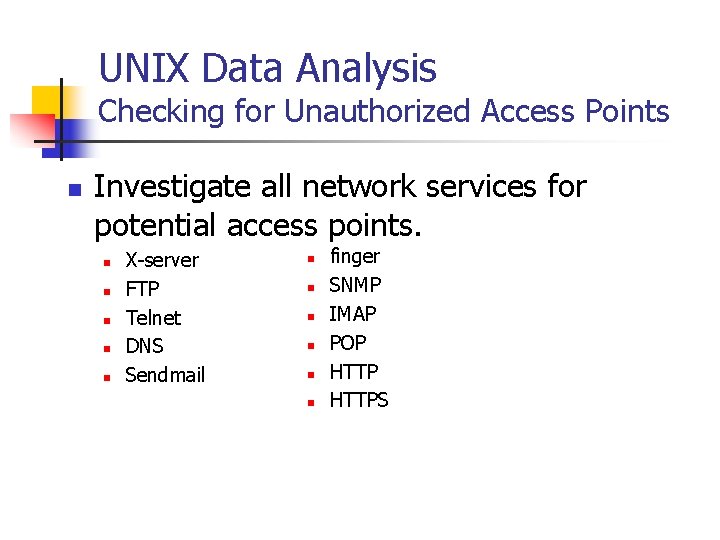
UNIX Data Analysis Checking for Unauthorized Access Points n Investigate all network services for potential access points. n n n X-server FTP Telnet DNS Sendmail n n n finger SNMP IMAP POP HTTPS
UNIX Data Analysis Analyzing Trust Relationships n n If machine A trusts machine B, then anyone on machine B can access services on machine A. Don’t set up trust relationships. n n They allow an attacker to escalate privileges to other machines Check files such as /etc/hosts. equiv or. rhosts
UNIX Data Analysis Analyzing Trust Relationships n n n Network topology routes data through other computers. Sniffing (esp. for passwords). Even possible in a switched environment: arpredirect in dsniff
UNIX Data Analysis Loadable Kernel Modules n n n LKM can by dynamically loaded with root-level access. Used to let a hacker maintain access. Adore, Knark, Itf
UNIX Data Analysis Loadable Kernel Modules n n n Trojan system utilities used to detect them. Look for discrepancies between internal and external scans. Detection tools are available.