CMSC 313 Assembly Language and Computer Organization Topics
CMSC 313 Assembly Language and Computer Organization Topics: n n Theme Great realities of computer systems How this fits within CS curriculum Logistical issues
Course Theme n Abstraction is good, but don’t forget reality! Most CS courses emphasize abstraction n n Abstract data types Asymptotic analysis These abstractions have limits n n Especially in the presence of bugs Need to understand underlying implementations Useful outcomes n Become more effective programmers l Able to find and eliminate bugs efficiently l Able to tune program performance n Prepare for later “systems” classes in CS & ECE l Compilers, Operating Systems, Networks, Computer – 2– Architecture, Embedded Systems CMSC 313, F ‘ 09
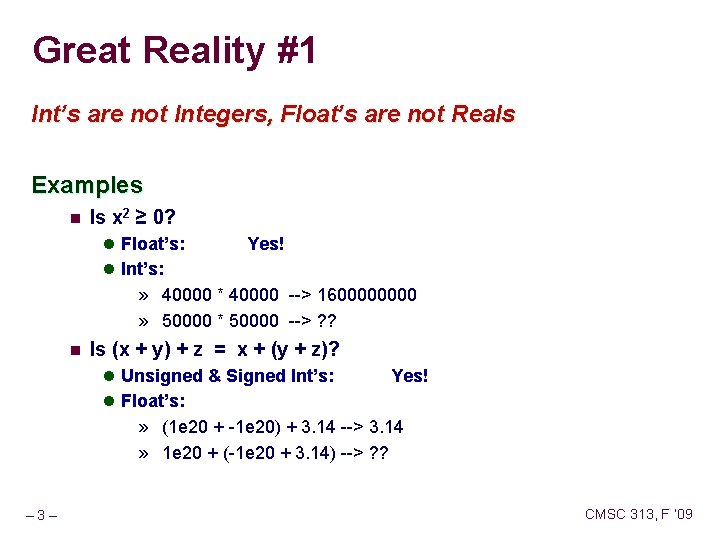
Great Reality #1 Int’s are not Integers, Float’s are not Reals Examples n Is x 2 ≥ 0? l Float’s: Yes! l Int’s: » 40000 * 40000 --> 160000 » 50000 * 50000 --> ? ? n Is (x + y) + z = x + (y + z)? l Unsigned & Signed Int’s: Yes! l Float’s: » (1 e 20 + -1 e 20) + 3. 14 --> 3. 14 » 1 e 20 + (-1 e 20 + 3. 14) --> ? ? – 3– CMSC 313, F ‘ 09
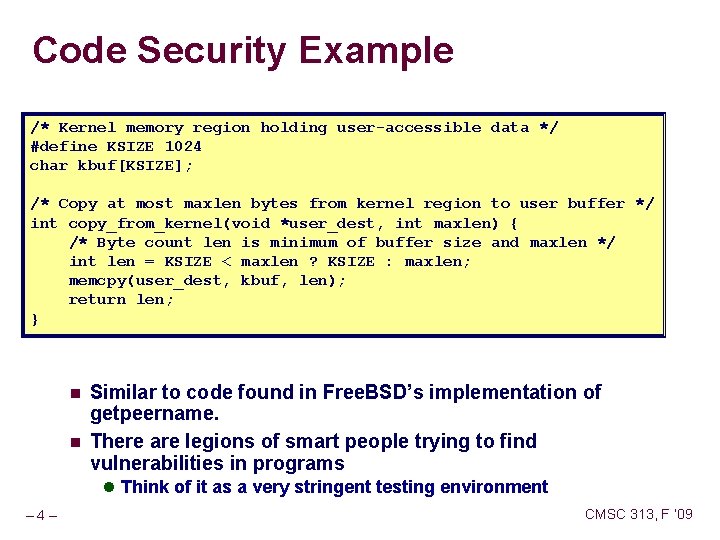
Code Security Example /* Kernel memory region holding user-accessible data */ #define KSIZE 1024 char kbuf[KSIZE]; /* Copy at most maxlen bytes from kernel region to user buffer */ int copy_from_kernel(void *user_dest, int maxlen) { /* Byte count len is minimum of buffer size and maxlen */ int len = KSIZE < maxlen ? KSIZE : maxlen; memcpy(user_dest, kbuf, len); return len; } n n Similar to code found in Free. BSD’s implementation of getpeername. There are legions of smart people trying to find vulnerabilities in programs l Think of it as a very stringent testing environment – 4– CMSC 313, F ‘ 09
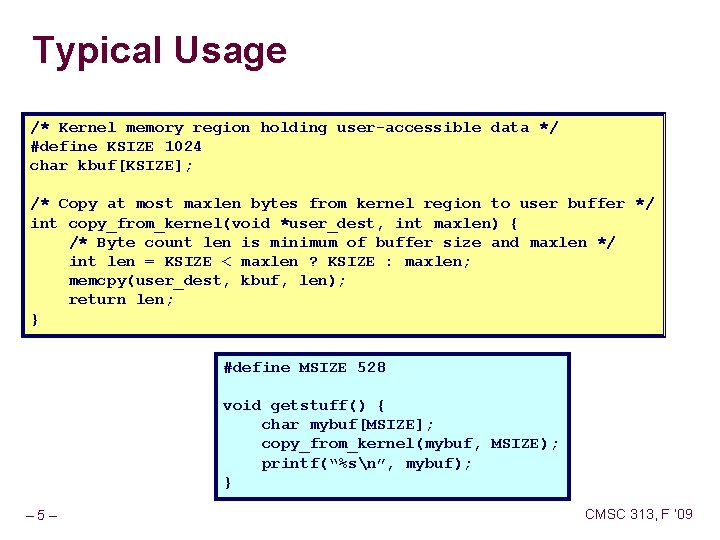
Typical Usage /* Kernel memory region holding user-accessible data */ #define KSIZE 1024 char kbuf[KSIZE]; /* Copy at most maxlen bytes from kernel region to user buffer */ int copy_from_kernel(void *user_dest, int maxlen) { /* Byte count len is minimum of buffer size and maxlen */ int len = KSIZE < maxlen ? KSIZE : maxlen; memcpy(user_dest, kbuf, len); return len; } #define MSIZE 528 void getstuff() { char mybuf[MSIZE]; copy_from_kernel(mybuf, MSIZE); printf(“%sn”, mybuf); } – 5– CMSC 313, F ‘ 09
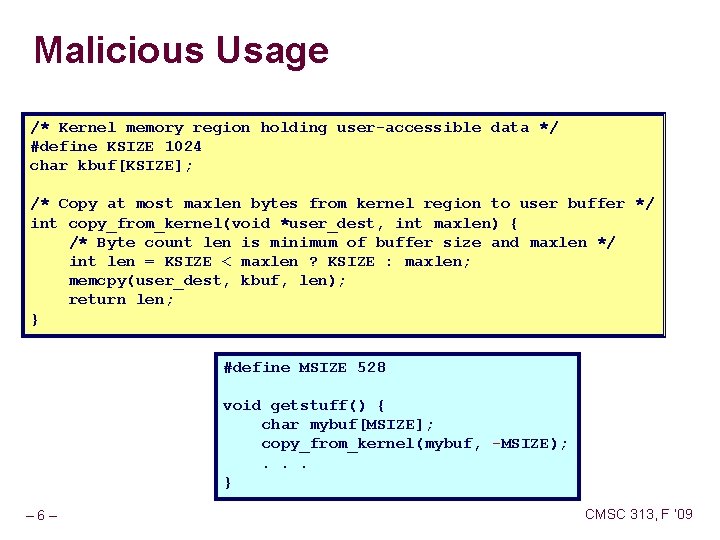
Malicious Usage /* Kernel memory region holding user-accessible data */ #define KSIZE 1024 char kbuf[KSIZE]; /* Copy at most maxlen bytes from kernel region to user buffer */ int copy_from_kernel(void *user_dest, int maxlen) { /* Byte count len is minimum of buffer size and maxlen */ int len = KSIZE < maxlen ? KSIZE : maxlen; memcpy(user_dest, kbuf, len); return len; } #define MSIZE 528 void getstuff() { char mybuf[MSIZE]; copy_from_kernel(mybuf, -MSIZE); . . . } – 6– CMSC 313, F ‘ 09
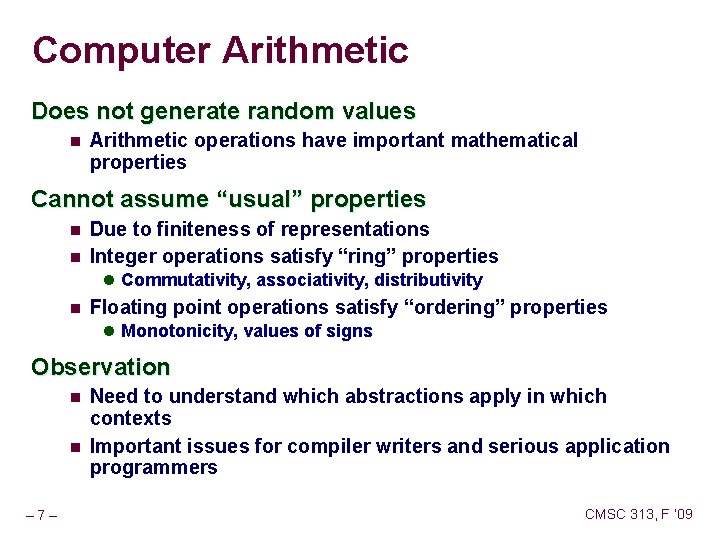
Computer Arithmetic Does not generate random values n Arithmetic operations have important mathematical properties Cannot assume “usual” properties n n Due to finiteness of representations Integer operations satisfy “ring” properties l Commutativity, associativity, distributivity n Floating point operations satisfy “ordering” properties l Monotonicity, values of signs Observation n n – 7– Need to understand which abstractions apply in which contexts Important issues for compiler writers and serious application programmers CMSC 313, F ‘ 09
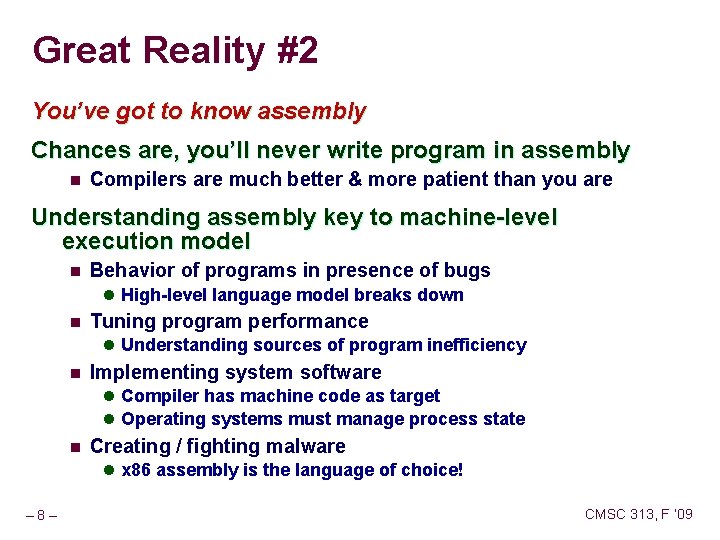
Great Reality #2 You’ve got to know assembly Chances are, you’ll never write program in assembly n Compilers are much better & more patient than you are Understanding assembly key to machine-level execution model n Behavior of programs in presence of bugs l High-level language model breaks down n Tuning program performance l Understanding sources of program inefficiency n Implementing system software l Compiler has machine code as target l Operating systems must manage process state n Creating / fighting malware l x 86 assembly is the language of choice! – 8– CMSC 313, F ‘ 09
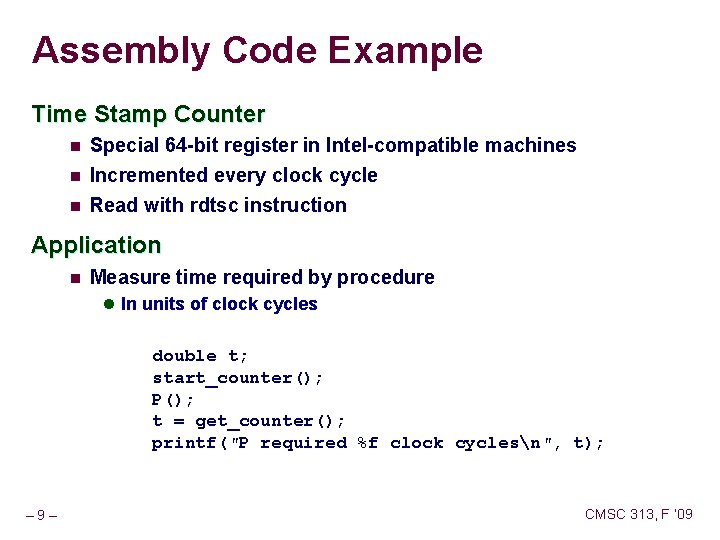
Assembly Code Example Time Stamp Counter n Special 64 -bit register in Intel-compatible machines n Incremented every clock cycle Read with rdtsc instruction n Application n Measure time required by procedure l In units of clock cycles double t; start_counter(); P(); t = get_counter(); printf("P required %f clock cyclesn", t); – 9– CMSC 313, F ‘ 09
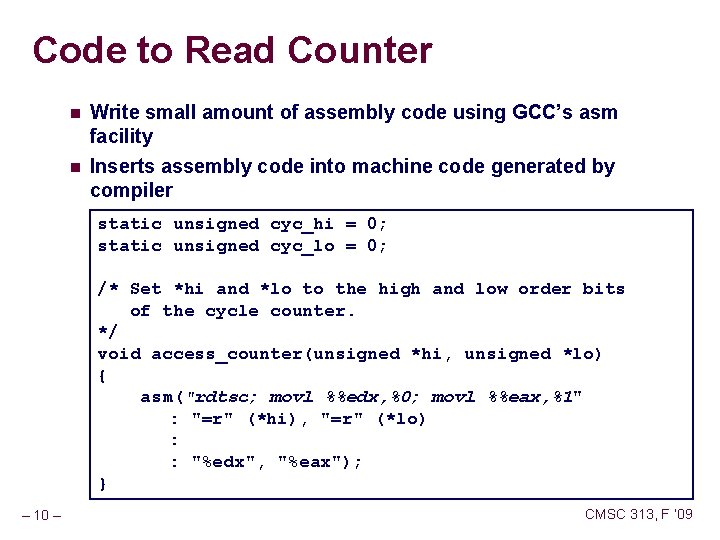
Code to Read Counter n Write small amount of assembly code using GCC’s asm facility n Inserts assembly code into machine code generated by compiler static unsigned cyc_hi = 0; static unsigned cyc_lo = 0; /* Set *hi and *lo to the high and low order bits of the cycle counter. */ void access_counter(unsigned *hi, unsigned *lo) { asm("rdtsc; movl %%edx, %0; movl %%eax, %1" : "=r" (*hi), "=r" (*lo) : : "%edx", "%eax"); } – 10 – CMSC 313, F ‘ 09
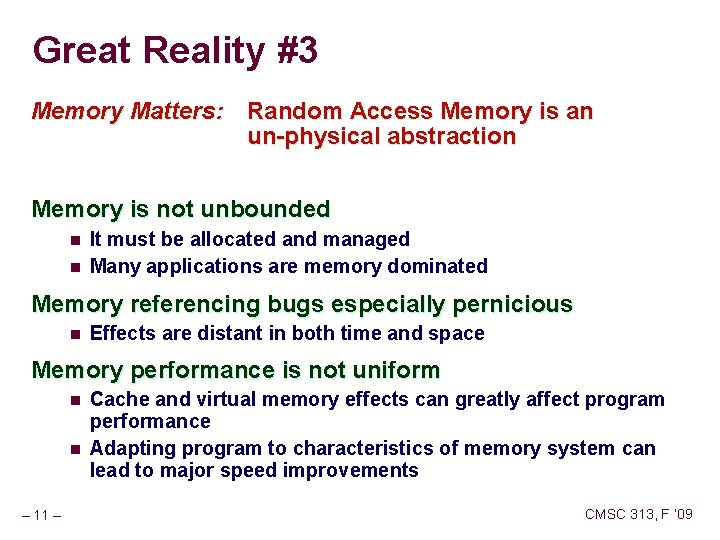
Great Reality #3 Memory Matters: Random Access Memory is an un-physical abstraction Memory is not unbounded n n It must be allocated and managed Many applications are memory dominated Memory referencing bugs especially pernicious n Effects are distant in both time and space Memory performance is not uniform n n – 11 – Cache and virtual memory effects can greatly affect program performance Adapting program to characteristics of memory system can lead to major speed improvements CMSC 313, F ‘ 09
![Memory Referencing Bug Example double fun(int i) { double d[1] = {3. 14}; long Memory Referencing Bug Example double fun(int i) { double d[1] = {3. 14}; long](http://slidetodoc.com/presentation_image_h/307bef778d3f6a23610a7b09a944118b/image-12.jpg)
Memory Referencing Bug Example double fun(int i) { double d[1] = {3. 14}; long int a[2]; a[i] = 1073741824; /* Possibly out of bounds */ return d[0]; } fun(0) fun(1) fun(2) fun(3) fun(4) – 12 – –> –> –> 3. 14 3. 1399998664856 2. 00000061035156 3. 14, then segmentation fault CMSC 313, F ‘ 09
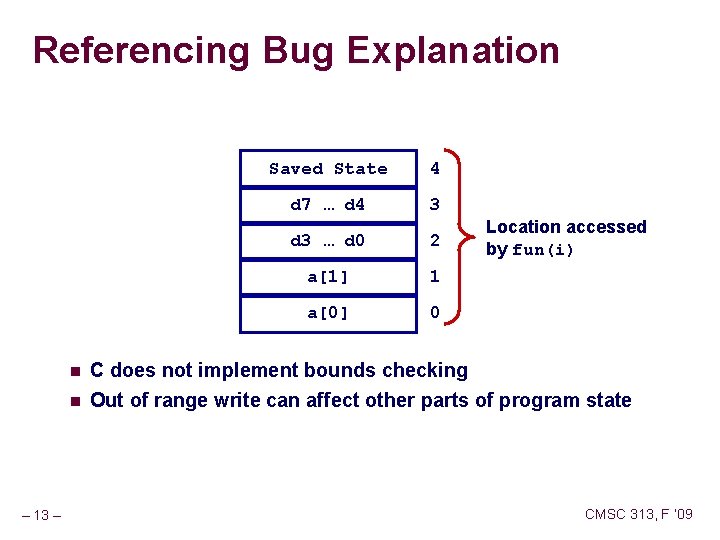
Referencing Bug Explanation n n – 13 – Saved State 4 d 7 … d 4 3 d 3 … d 0 2 a[1] 1 a[0] 0 Location accessed by fun(i) C does not implement bounds checking Out of range write can affect other parts of program state CMSC 313, F ‘ 09
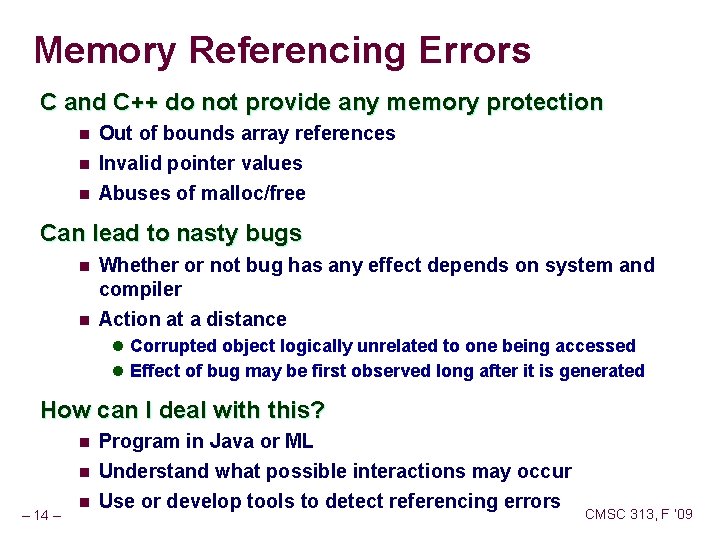
Memory Referencing Errors C and C++ do not provide any memory protection n Out of bounds array references n Invalid pointer values Abuses of malloc/free n Can lead to nasty bugs n n Whether or not bug has any effect depends on system and compiler Action at a distance l Corrupted object logically unrelated to one being accessed l Effect of bug may be first observed long after it is generated How can I deal with this? n n – 14 – n Program in Java or ML Understand what possible interactions may occur Use or develop tools to detect referencing errors CMSC 313, F ‘ 09
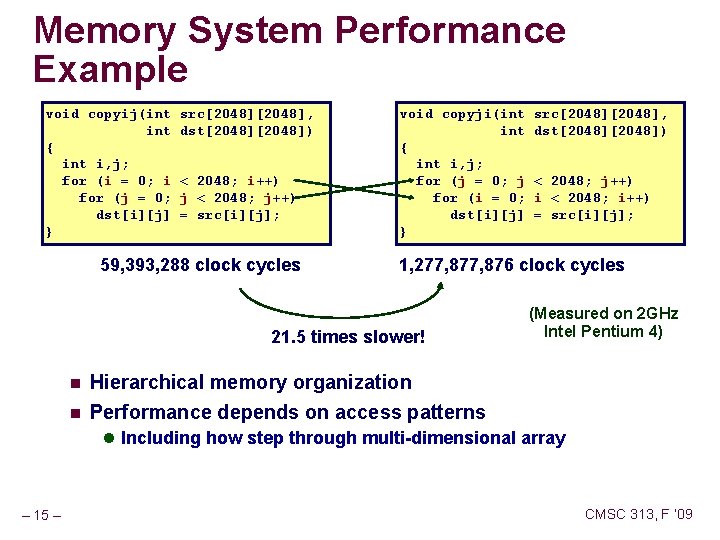
Memory System Performance Example void copyij(int { int i, j; for (i = 0; i for (j = 0; dst[i][j] } src[2048], dst[2048]) < 2048; i++) j < 2048; j++) = src[i][j]; 59, 393, 288 clock cycles void copyji(int { int i, j; for (j = 0; j for (i = 0; dst[i][j] } n < 2048; j++) i < 2048; i++) = src[i][j]; 1, 277, 876 clock cycles 21. 5 times slower! n src[2048], dst[2048]) (Measured on 2 GHz Intel Pentium 4) Hierarchical memory organization Performance depends on access patterns l Including how step through multi-dimensional array – 15 – CMSC 313, F ‘ 09
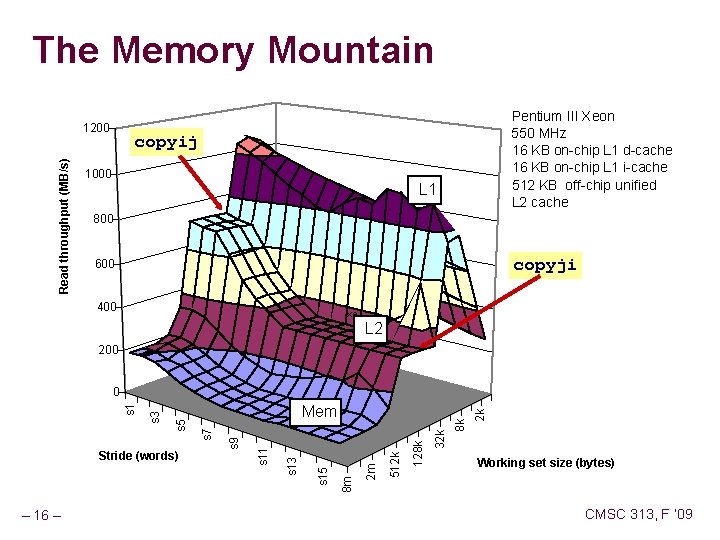
The Memory Mountain Read throughput (MB/s) 1200 Pentium III Xeon 550 MHz 16 KB on-chip L 1 d-cache 16 KB on-chip L 1 i-cache 512 KB off-chip unified L 2 cache copyij 1000 L 1 800 copyji 600 400 xe L 2 200 – 16 – 2 k 8 k 32 k 128 k 512 k 2 m 8 m s 15 s 13 s 11 s 9 Stride (words) Mem s 7 s 5 s 3 s 1 0 Working set size (bytes) CMSC 313, F ‘ 09
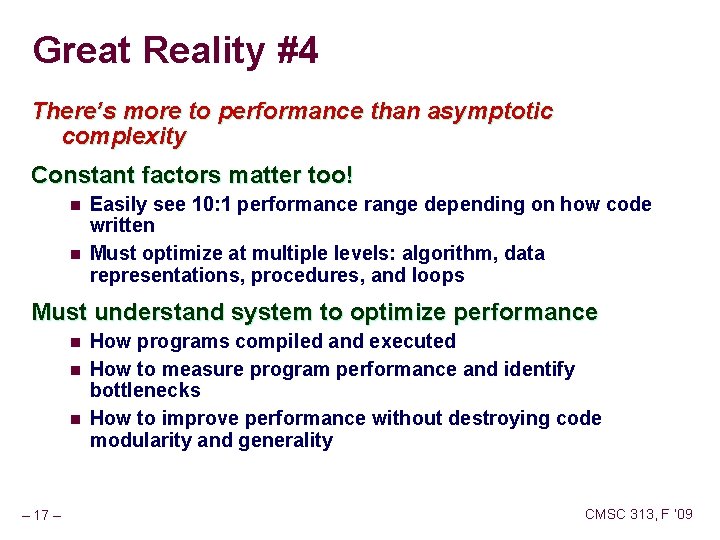
Great Reality #4 There’s more to performance than asymptotic complexity Constant factors matter too! n n Easily see 10: 1 performance range depending on how code written Must optimize at multiple levels: algorithm, data representations, procedures, and loops Must understand system to optimize performance n n n – 17 – How programs compiled and executed How to measure program performance and identify bottlenecks How to improve performance without destroying code modularity and generality CMSC 313, F ‘ 09
![Code Performance Example /* Compute product of array elements */ double product(double d[], int Code Performance Example /* Compute product of array elements */ double product(double d[], int](http://slidetodoc.com/presentation_image_h/307bef778d3f6a23610a7b09a944118b/image-18.jpg)
Code Performance Example /* Compute product of array elements */ double product(double d[], int n) { double result = 1; int i; for (i = 0; i < n; i++) result = result * d[i]; return result; } Multiply all elements of array n Performance on class machines: ~7. 0 clock cycles per element n l Latency of floating-point multiplier – 18 – CMSC 313, F ‘ 09
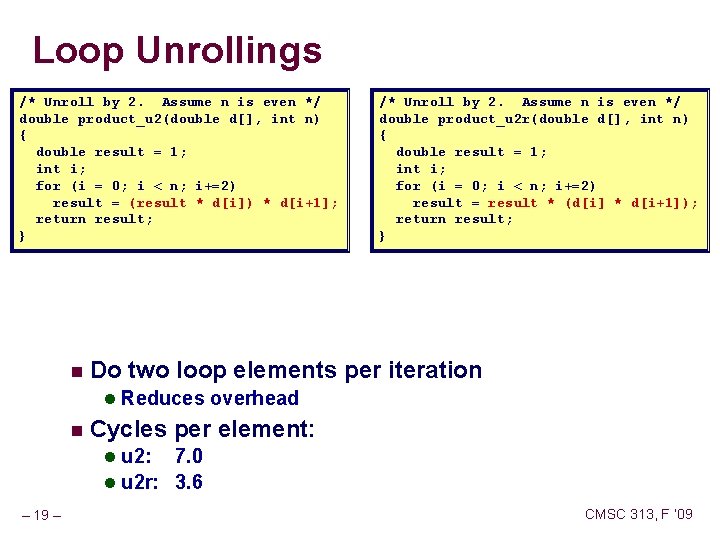
Loop Unrollings /* Unroll by 2. Assume n is even */ double product_u 2(double d[], int n) { double result = 1; int i; for (i = 0; i < n; i+=2) result = (result * d[i]) * d[i+1]; return result; } n /* Unroll by 2. Assume n is even */ double product_u 2 r(double d[], int n) { double result = 1; int i; for (i = 0; i < n; i+=2) result = result * (d[i] * d[i+1]); return result; } Do two loop elements per iteration l Reduces overhead n Cycles per element: l u 2: 7. 0 l u 2 r: 3. 6 – 19 – CMSC 313, F ‘ 09
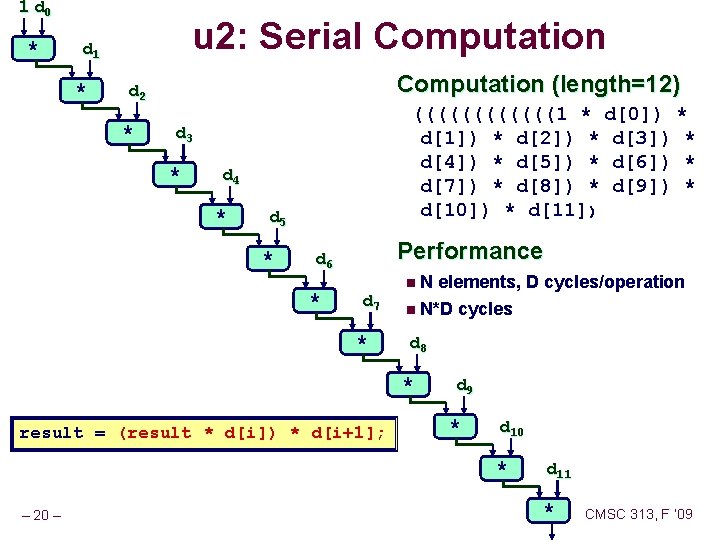
1 d 0 * u 2: Serial Computation d 1 * Computation (length=12) d 2 * ((((((1 * d[0]) * d[1]) * d[2]) * d[3]) * d[4]) * d[5]) * d[6]) * d[7]) * d[8]) * d[9]) * d[10]) * d[11]) d 3 * d 4 * d 5 * Performance d 6 * d 7 * n. N elements, D cycles/operation n N*D cycles d 8 * result = (result * d[i]) * d[i+1]; d 9 * d 10 * – 20 – d 11 * CMSC 313, F ‘ 09
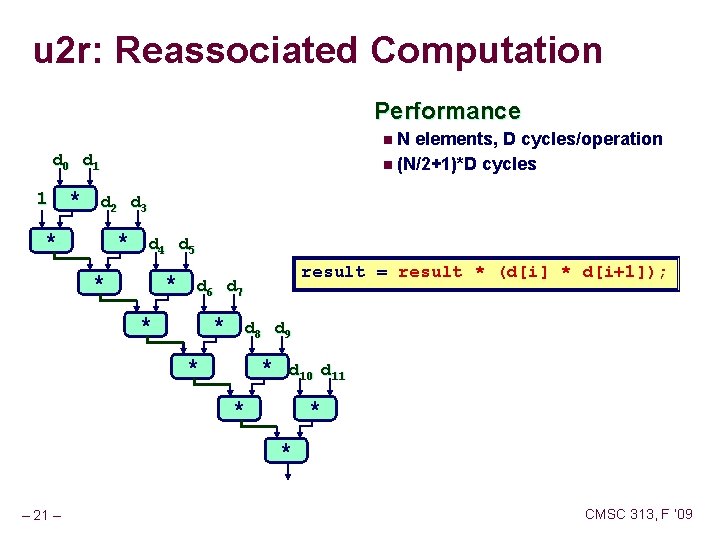
u 2 r: Reassociated Computation Performance n. N elements, D cycles/operation n (N/2+1)*D cycles d 0 d 1 1 * d 2 d 3 * * d 4 d 5 * result = result * (d[i] * d[i+1]); * d 6 d 7 * d 8 d 9 * * * d 10 d 11 * * * – 21 – CMSC 313, F ‘ 09
Great Reality #5 Computers do more than execute programs They need to get data in and out n I/O system critical to program reliability and performance They communicate with each other over networks n Many system-level issues arise in presence of network l Concurrent operations by autonomous processes l Coping with unreliable media l Cross platform compatibility l Complex performance issues – 22 – CMSC 313, F ‘ 09
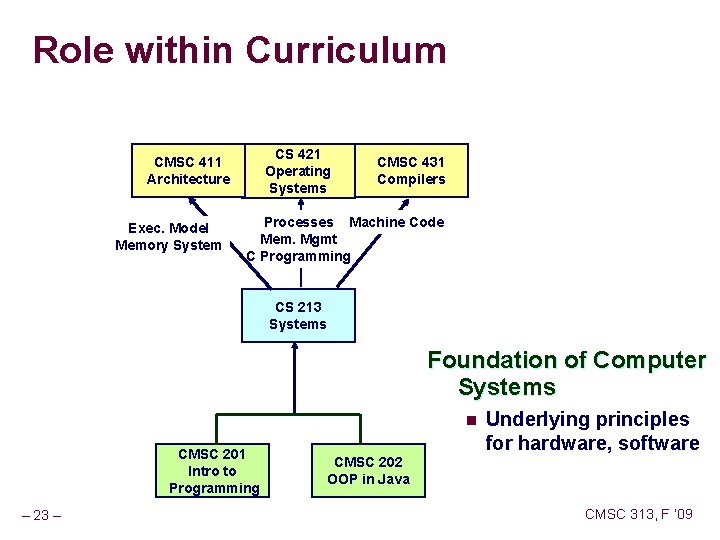
Role within Curriculum CS 421 Operating Systems CMSC 411 Architecture Exec. Model Memory System CMSC 431 Compilers Processes Machine Code Mem. Mgmt C Programming CS 213 Systems Foundation of Computer Systems n CMSC 201 Intro to Programming – 23 – Underlying principles for hardware, software CMSC 202 OOP in Java CMSC 313, F ‘ 09
Course Perspective Most Systems Courses are Builder-Centric n Computer Architecture l Design pipelined processor in Verilog n Operating Systems l Implement large portions of operating system n Compilers l Write compiler for simple language n Networking l Implement and simulate network protocols – 24 – CMSC 313, F ‘ 09
Course Perspective (Cont. ) Our Course is Programmer-Centric n Purpose is to show by knowing more about the underlying system, one can be more effective as a programmer n Enable you to l Write programs that are more reliable and efficient l Incorporate features that require hooks into OS » E. g. , concurrency, signal handlers n Not just a course for dedicated hackers l We bring out the hidden hacker in everyone n – 25 – Cover material in this course that you won’t see elsewhere CMSC 313, F ‘ 09
Textbooks Randal E. Bryant and David R. O’Hallaron, n n n “Computer Systems: A Programmer’s Perspective”, Prentice Hall 2003. http: //csapp. cs. cmu. edu This book really matters for the course! l How to solve labs l Practice problems typical of exam problems Brian Kernighan and Dennis Ritchie, n n – 26 – “The C Programming Language, Second Edition”, Prentice Hall, 1988 The “C” bible CMSC 313, F ‘ 09
Course Components Lectures n Higher level concepts Projects n n The heart of the course 2 or 3 weeks Provide in-depth understanding of an aspect of systems Programming and measurement Exams n Test your understanding of concepts & mathematical principles l Critical component of grade – 27 – CMSC 313, F ‘ 09
Getting Help Class Web Page n n n http: //www. cs. umbc. edu/courses/undergraduate/313/fall 09 Copies of lectures, assignments, exams, solutions Clarifications to assignments Black. Board n n n http: //blackboard. umbc. edu Clarifications to assignments, general discussion The only board your instructors will be monitoring Email n – 28 – frey@cs. umbc. edu CMSC 313, F ‘ 09
Policies: Assignments Work groups n Some projects are team of two Handins n n Assignment due time/date specified in project description Electronic handins Appealing grades n Within 7 days of completion of grading. l Following procedure described in syllabus n n – 29 – Projects: Talk to your TA Exams: Talk to your instructor CMSC 313, F ‘ 09
Timeliness Grace Days n 4 for the course Covers scheduling crunch, out-of-town trips, illnesses, minor setbacks n Save them until late in the term! n Lateness Penalties n n Once grace days used up, get penalized 15% / day Typically shut off all handins 2— 3 days after due date Catastrophic Events n n Major illness, death in family, … Work with your academic advisor to formulate plan for getting back on track Advice n – 30 – Once you start running late, it’s really hard to catch up CMSC 313, F ‘ 09
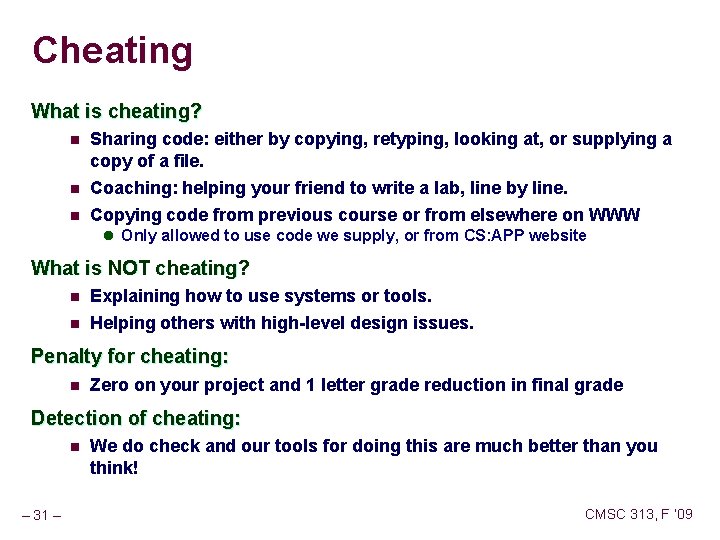
Cheating What is cheating? n Sharing code: either by copying, retyping, looking at, or supplying a copy of a file. n Coaching: helping your friend to write a lab, line by line. n Copying code from previous course or from elsewhere on WWW l Only allowed to use code we supply, or from CS: APP website What is NOT cheating? n n Explaining how to use systems or tools. Helping others with high-level design issues. Penalty for cheating: n Zero on your project and 1 letter grade reduction in final grade Detection of cheating: n – 31 – We do check and our tools for doing this are much better than you think! CMSC 313, F ‘ 09
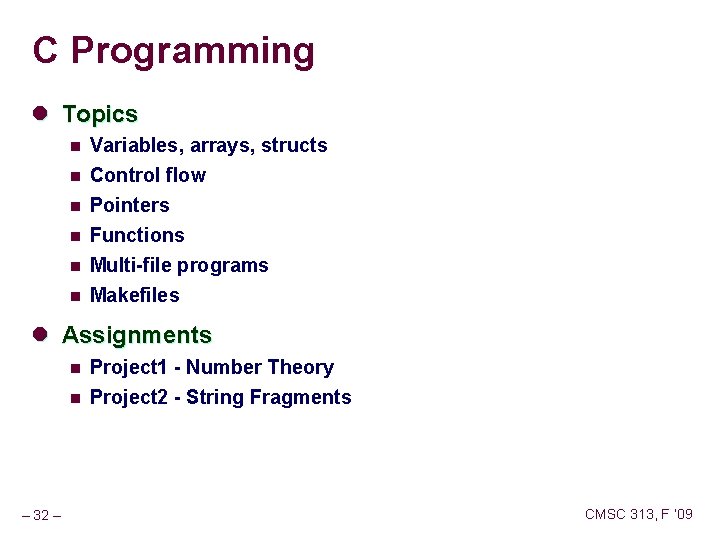
C Programming l Topics n Variables, arrays, structs n Control flow Pointers n n Functions Multi-file programs Makefiles l Assignments n n – 32 – Project 1 - Number Theory Project 2 - String Fragments CMSC 313, F ‘ 09
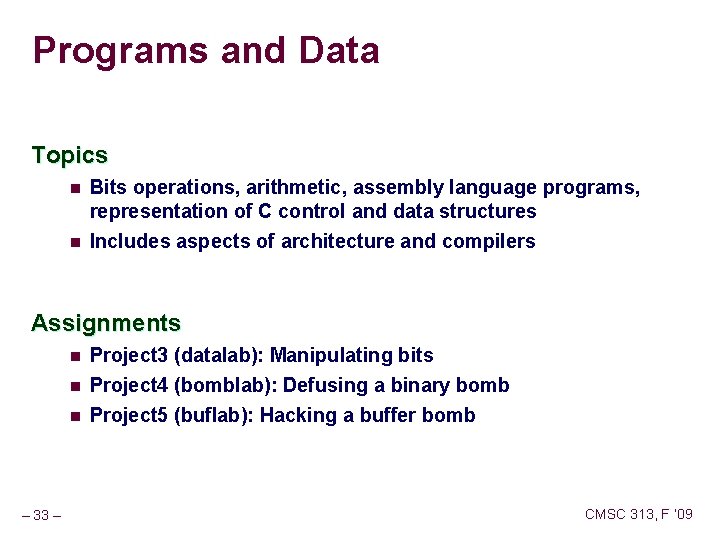
Programs and Data Topics n n Bits operations, arithmetic, assembly language programs, representation of C control and data structures Includes aspects of architecture and compilers Assignments n n n – 33 – Project 3 (datalab): Manipulating bits Project 4 (bomblab): Defusing a binary bomb Project 5 (buflab): Hacking a buffer bomb CMSC 313, F ‘ 09
The Memory Hierarchy Topics n n Memory technology, memory hierarchy, caches, disks, locality Includes aspects of architecture and OS. Assignments – 34 – CMSC 313, F ‘ 09
Exceptional Control Flow (3) Topics n n Hardware exceptions, processes, process control, Unix signals, nonlocal jumps Includes aspects of compilers, OS, and architecture Assignments – 35 – CMSC 313, F ‘ 09
Virtual Memory Topics n n Virtual memory, address translation, dynamic storage allocation Includes aspects of architecture and OS Assignments n Project 6 (malloclab): Writing your own malloc package l Get a real feel for systems programming – 36 – CMSC 313, F ‘ 09
Project Rationale Each project should have a well-defined goal such as solving a puzzle or winning a contest. Doing a project should result in new skills and concepts We try to use competition in a fun and healthy way. n n – 37 – Set a reasonable threshold for full credit. Post intermediate results (anonymized) on Web page for glory! CMSC 313, F ‘ 09
Good Luck! – 38 – CMSC 313, F ‘ 09
- Slides: 38