Class 36 Public Key Crypto CS 150 Computer
Class 36: Public Key Crypto CS 150: Computer Science University of Virginia Computer Science David Evans http: //www. cs. virginia. edu/evans
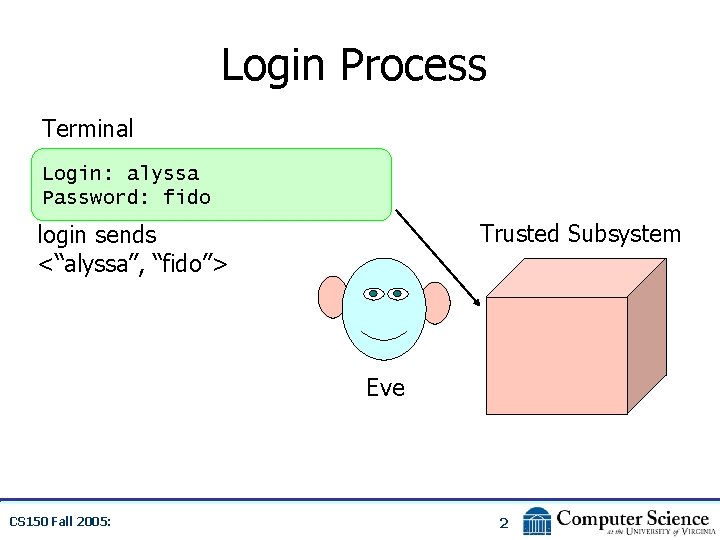
Login Process Terminal Login: alyssa Password: fido Trusted Subsystem login sends <“alyssa”, “fido”> Eve CS 150 Fall 2005: 2
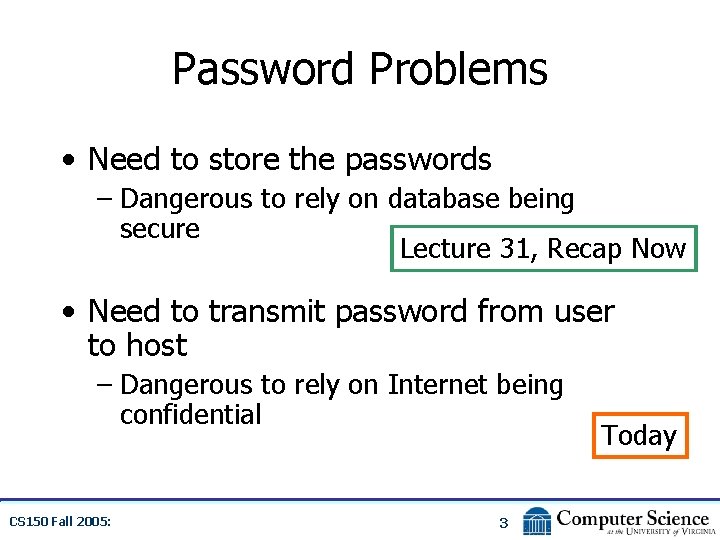
Password Problems • Need to store the passwords – Dangerous to rely on database being secure Lecture 31, Recap Now • Need to transmit password from user to host – Dangerous to rely on Internet being confidential CS 150 Fall 2005: 3 Today
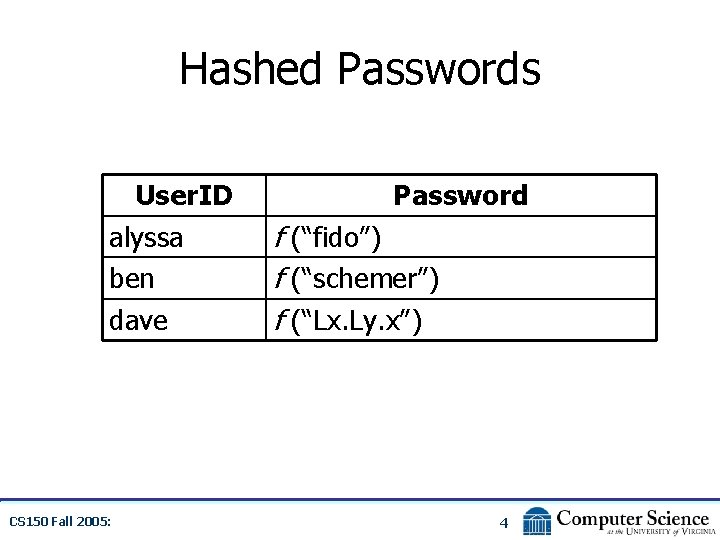
Hashed Passwords User. ID alyssa ben dave CS 150 Fall 2005: Password f (“fido”) f (“schemer”) f (“Lx. Ly. x”) 4
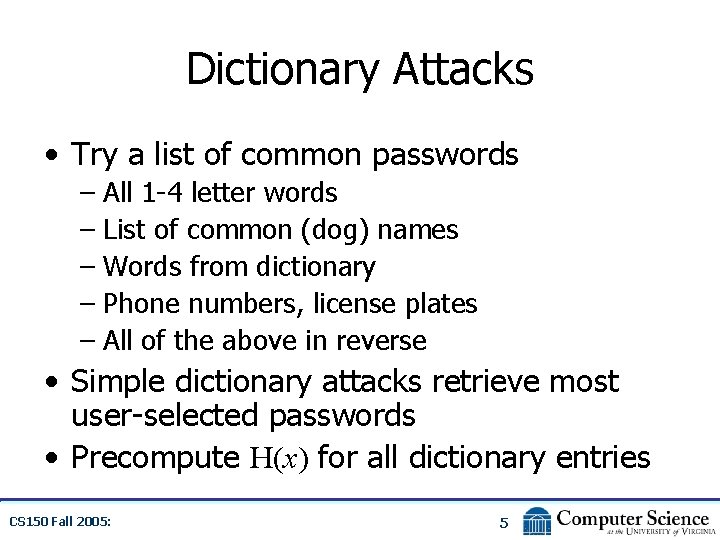
Dictionary Attacks • Try a list of common passwords – All 1 -4 letter words – List of common (dog) names – Words from dictionary – Phone numbers, license plates – All of the above in reverse • Simple dictionary attacks retrieve most user-selected passwords • Precompute H(x) for all dictionary entries CS 150 Fall 2005: 5
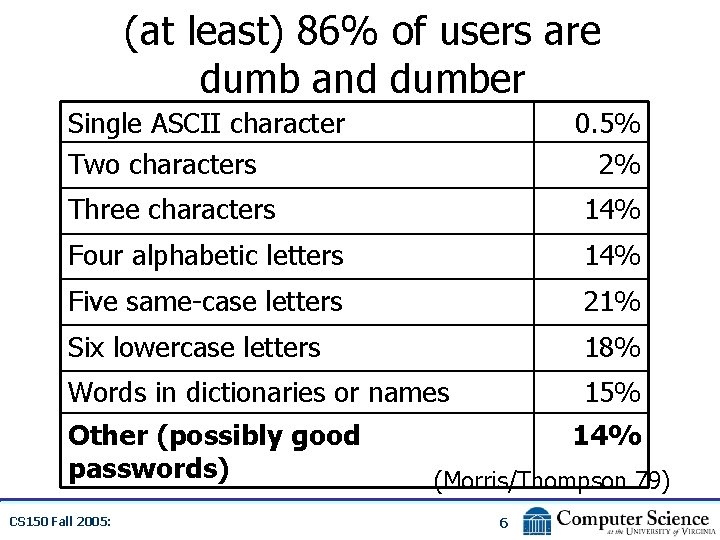
(at least) 86% of users are dumb and dumber Single ASCII character Two characters 0. 5% 2% Three characters 14% Four alphabetic letters 14% Five same-case letters 21% Six lowercase letters 18% Words in dictionaries or names 15% Other (possibly good passwords) CS 150 Fall 2005: 14% (Morris/Thompson 79) 6
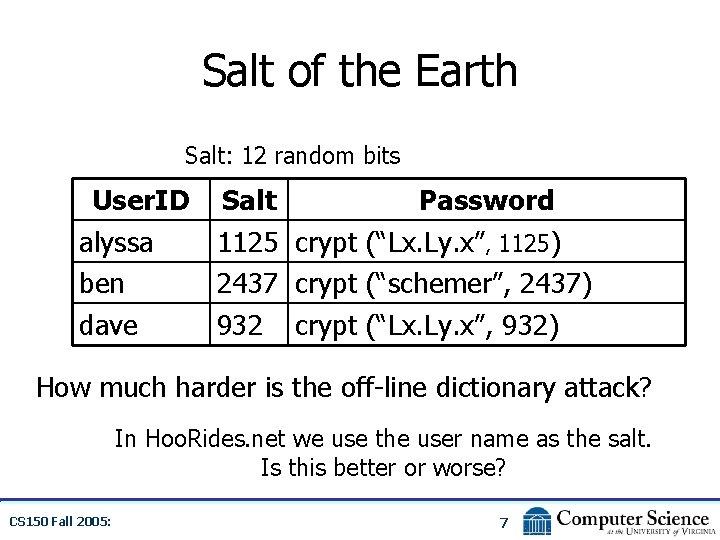
Salt of the Earth Salt: 12 random bits User. ID Salt Password alyssa 1125 crypt (“Lx. Ly. x”, 1125) ben 2437 crypt (“schemer”, 2437) dave 932 crypt (“Lx. Ly. x”, 932) How much harder is the off-line dictionary attack? In Hoo. Rides. net we use the user name as the salt. Is this better or worse? CS 150 Fall 2005: 7
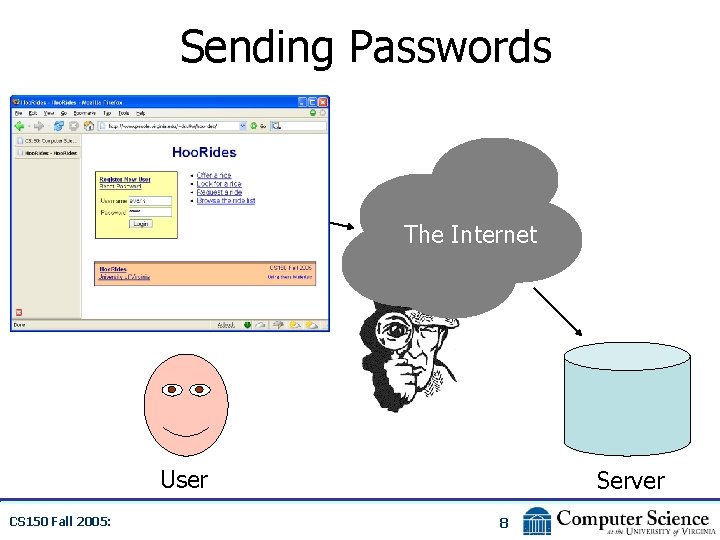
Sending Passwords Encrypt The Internet User CS 150 Fall 2005: Server 8
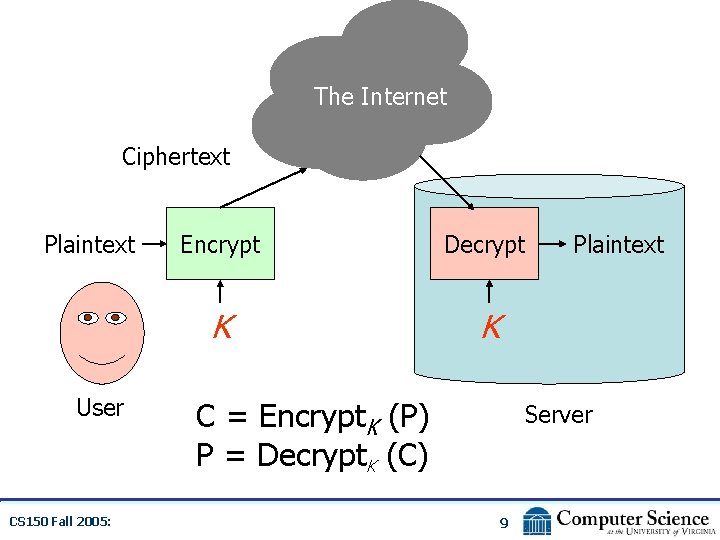
The Internet Ciphertext Plaintext User CS 150 Fall 2005: Encrypt Decrypt K K C = Encrypt. K (P) P = Decrypt. K (C) Plaintext Server 9
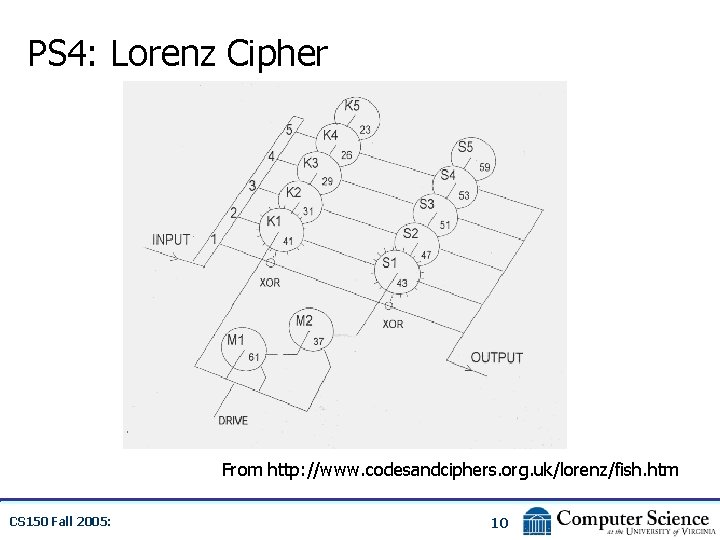
PS 4: Lorenz Cipher From http: //www. codesandciphers. org. uk/lorenz/fish. htm CS 150 Fall 2005: 10

Modern Symmetric Ciphers A billion is a large number, but it's not that large a number. Whitfield Diffie • Same idea but: – Use digital logic instead of mechanical rotors – Larger keys (random bits, not rotor alignments) • PS 4 = 53; Lorenz 512 < 109 • Modern 128 bits > 1037 – Encrypt blocks of letters at a time CS 150 Fall 2005: 11
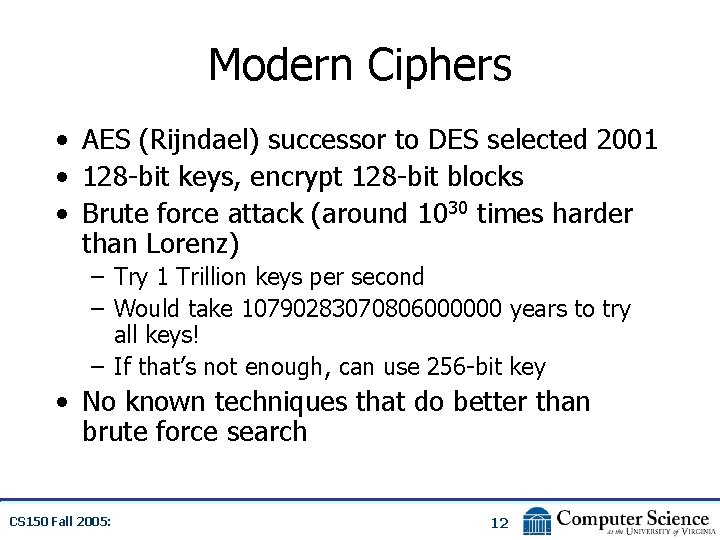
Modern Ciphers • AES (Rijndael) successor to DES selected 2001 • 128 -bit keys, encrypt 128 -bit blocks • Brute force attack (around 1030 times harder than Lorenz) – Try 1 Trillion keys per second – Would take 10790283070806000000 years to try all keys! – If that’s not enough, can use 256 -bit key • No known techniques that do better than brute force search CS 150 Fall 2005: 12
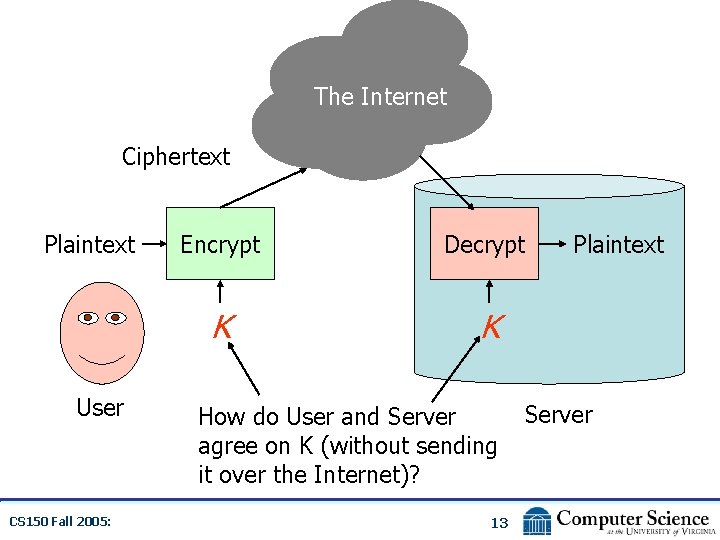
The Internet Ciphertext Plaintext User CS 150 Fall 2005: Encrypt Decrypt K K How do User and Server agree on K (without sending it over the Internet)? 13 Plaintext Server
Key Agreement Demo (Animated version at end of slides. ) CS 150 Fall 2005: 14
Asymmetric Cryptosystems • Need a hard problem (like symmetric cryptosystems) • With a trap door: if you know a secret, the hard problem becomes easy CS 150 Fall 2005: 15
One-Way Functions • Easy to compute, hard to invert • Trap-door one way function: – D (E (M)) = M – E and D are easy to compute. – Revealing E doesn’t reveal an easy way to compute D. – Hence, anyone who knows E can encrypt, but only someone who knows D can decrypt CS 150 Fall 2005: 16
![RSA [Rivest, Shamir, Adelman 78] One-way function: multiplication is easy, factoring is hard Trap-door: RSA [Rivest, Shamir, Adelman 78] One-way function: multiplication is easy, factoring is hard Trap-door:](http://slidetodoc.com/presentation_image_h2/0c04b861252f58a6ee6797da2314786f/image-17.jpg)
RSA [Rivest, Shamir, Adelman 78] One-way function: multiplication is easy, factoring is hard Trap-door: number theory (Euler and Fermat) CS 150 Fall 2005: 17
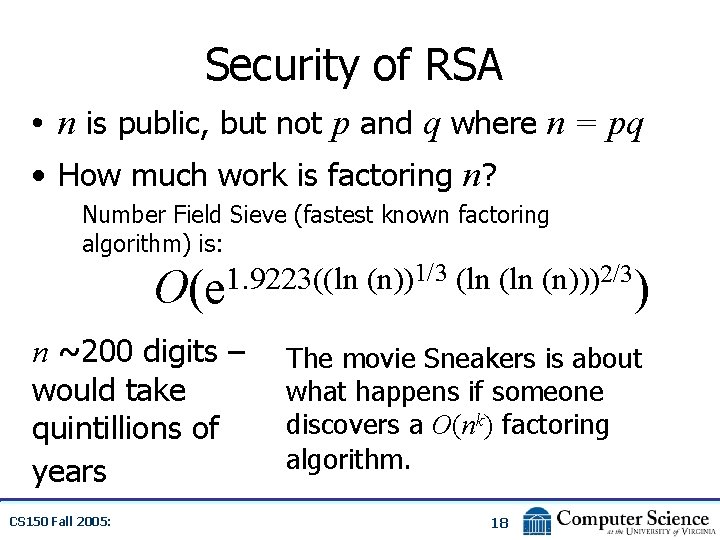
Security of RSA • n is public, but not p and q where n = pq • How much work is factoring n? Number Field Sieve (fastest known factoring algorithm) is: 1/3 (ln (n)))2/3 1. 9223((ln (n)) O(e ) n ~200 digits – would take quintillions of years CS 150 Fall 2005: The movie Sneakers is about what happens if someone discovers a O(nk) factoring algorithm. 18

Asymmetric Cryptosystems • Encryption and Decryption are done with different keys • Keep one of the keys secret, reveal the other EKRA (EKUA (M)) = M Alice’s Public Key: KUA Alice’s Private Key: KRA CS 150 Fall 2005: Only KRA can decrypt a message encrypted using KUA. 19

Public-Key Applications: Privacy Bob Alice Plaintext Encrypt Ciphertext Bob’s Public Key Decrypt Plaintext Bob’s Private Key • Alice encrypts message to Bob using Bob’s Private Key • Only Bob knows Bob’s Private Key only Bob can decrypt message CS 150 Fall 2005: 20
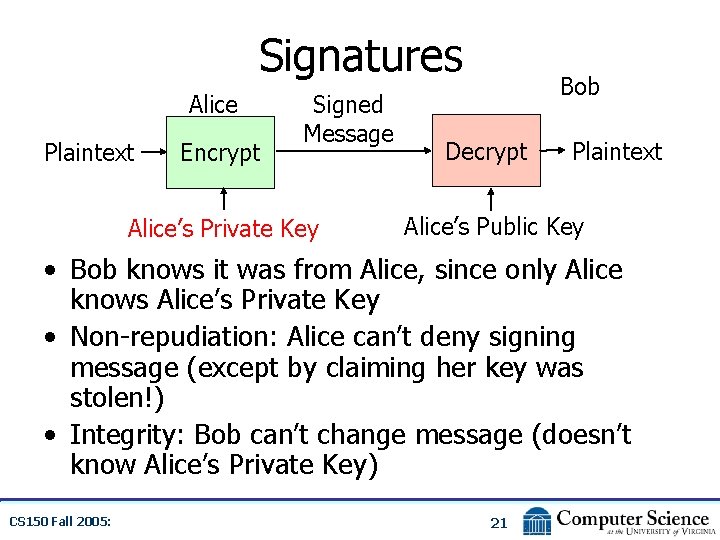
Signatures Alice Plaintext Encrypt Signed Message Alice’s Private Key Bob Decrypt Plaintext Alice’s Public Key • Bob knows it was from Alice, since only Alice knows Alice’s Private Key • Non-repudiation: Alice can’t deny signing message (except by claiming her key was stolen!) • Integrity: Bob can’t change message (doesn’t know Alice’s Private Key) CS 150 Fall 2005: 21
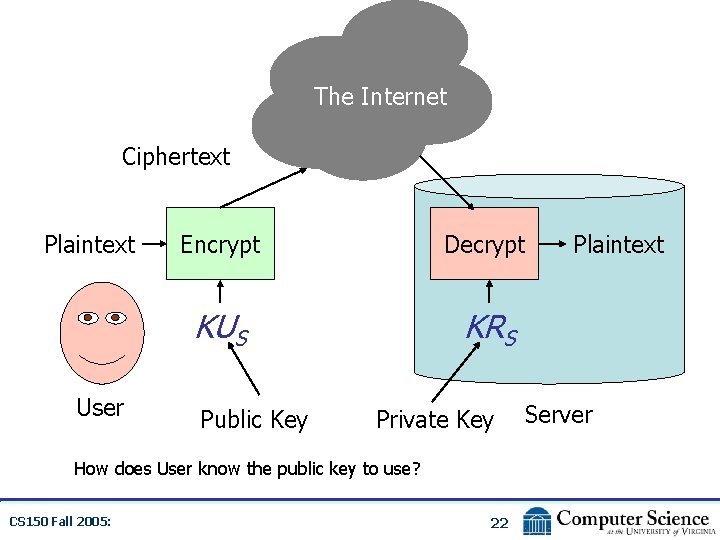
The Internet Ciphertext Plaintext User Encrypt Decrypt KUS KRS Public Key Private Key How does User know the public key to use? CS 150 Fall 2005: 22 Plaintext Server
Key Management CS 150 Fall 2005: 23
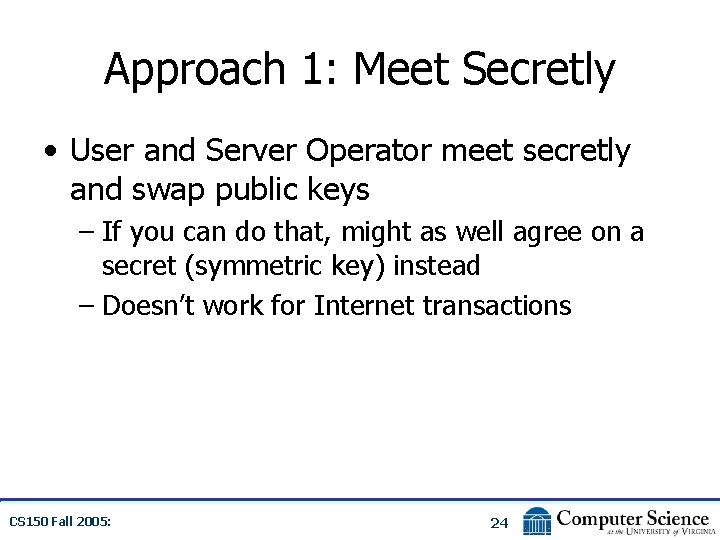
Approach 1: Meet Secretly • User and Server Operator meet secretly and swap public keys – If you can do that, might as well agree on a secret (symmetric key) instead – Doesn’t work for Internet transactions CS 150 Fall 2005: 24

Approach 2: Public Announcement • Publish public keys in a public forum – Append to email messages – Post on web site – New York Time classifieds • Easy for rogue to pretend to be someone else – Forge email, alter web site, lie to New York Times CS 150 Fall 2005: 25

Approach 3: Public Directory • Trusted authority maintains directory mapping names to public keys • Entities register public keys with authority in some secure way • Authority publishes directory – Print using watermarked paper, special fonts, etc. – Allow secure electronic access • Depends on secure distribution of directory’s key CS 150 Fall 2005: 26
![Approach 4: Certificates Veri. Sign KUS $$$$ CS = EKRVeri. Sign[“Server”, KUS] Request CS Approach 4: Certificates Veri. Sign KUS $$$$ CS = EKRVeri. Sign[“Server”, KUS] Request CS](http://slidetodoc.com/presentation_image_h2/0c04b861252f58a6ee6797da2314786f/image-27.jpg)
Approach 4: Certificates Veri. Sign KUS $$$$ CS = EKRVeri. Sign[“Server”, KUS] Request CS User EKUVeri. Sign (CS) = [“Server”, KUS] CS 150 Fall 2005: Server Knows KRS 27
![SSL (Secure Sockets Layer) Browser Server Hello KRCA[Server Identity, KUS] Check Certificate using KUCA SSL (Secure Sockets Layer) Browser Server Hello KRCA[Server Identity, KUS] Check Certificate using KUCA](http://slidetodoc.com/presentation_image_h2/0c04b861252f58a6ee6797da2314786f/image-28.jpg)
SSL (Secure Sockets Layer) Browser Server Hello KRCA[Server Identity, KUS] Check Certificate using KUCA Pick random K Note: This is slightly simplified from the actual SSL protocol. This version is vulnerable to a person-inthe-middle attack! CS 150 Fall 2005: KUS[K] Find K using KRS Secure channel using K 28

Data encrypted using secret key exchanged using some public key associated with some certificate. CS 150 Fall 2005: 29

CS 150 Fall 2005: 30
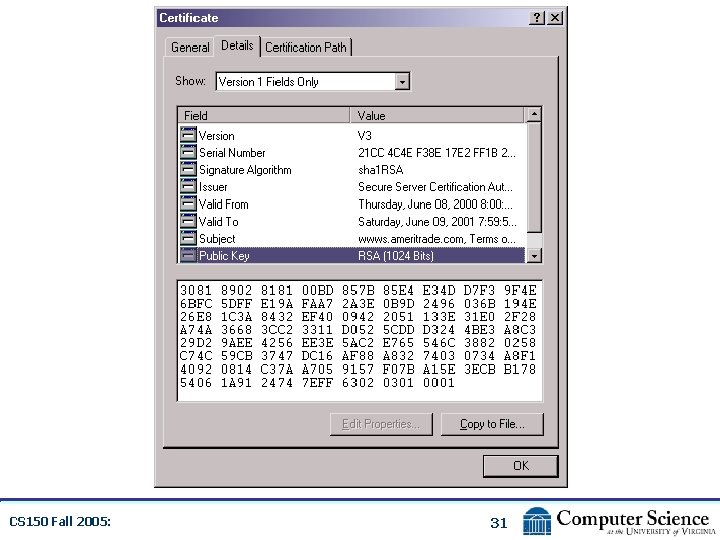
CS 150 Fall 2005: 31
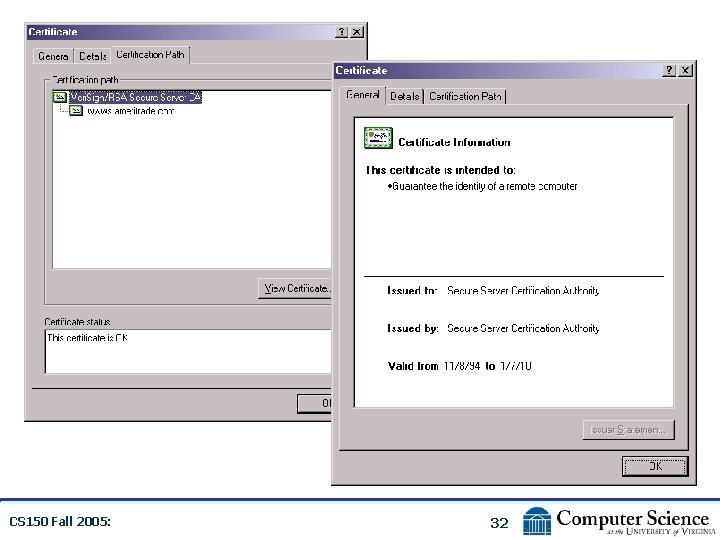
CS 150 Fall 2005: 32

How do you make your web site password form encrypt its input? http: // CS 150 Fall 2005: https: // 33
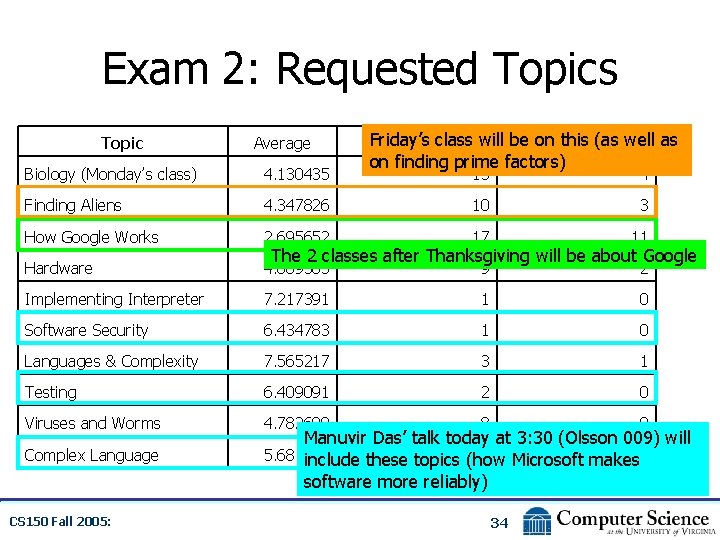
Exam 2: Requested Topics Topic Average Biology (Monday’s class) 4. 130435 Finding Aliens Friday’s this (as well as <=3 class will be on <=1 on finding prime factors) 13 4 4. 347826 10 3 How Google Works 2. 695652 17 11 Hardware 4. 869565 9 2 Implementing Interpreter 7. 217391 1 0 Software Security 6. 434783 1 0 Languages & Complexity 7. 565217 3 1 Testing 6. 409091 2 0 Viruses and Worms 4. 782609 8 0 Complex Language CS 150 Fall 2005: The 2 classes after Thanksgiving will be about Google Manuvir Das’ talk today at 3: 30 (Olsson 009) will 5. 681818 7 Microsoft makes 1 include these topics (how software more reliably) 34
Charge • Project Meetings today, tomorrow and Friday • Exam 2: return now – Comments will be posted on web site tonight CS 150 Fall 2005: 35
Animated version of Asymmetric Cryptography Demo CS 150 Fall 2005: 36
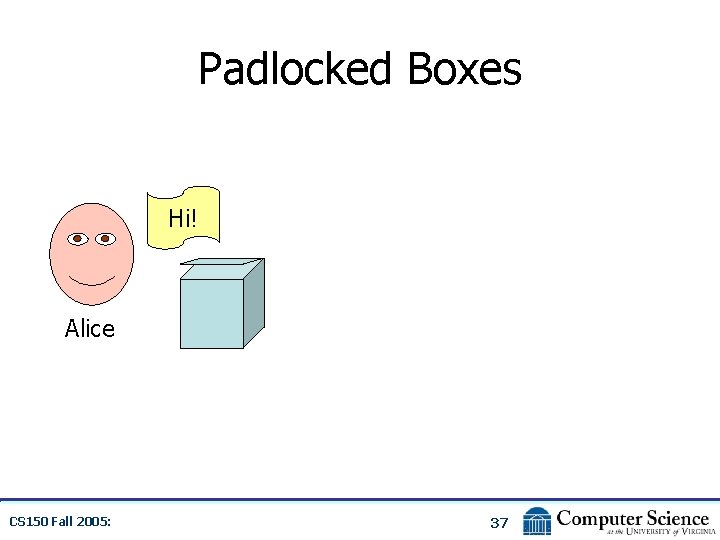
Padlocked Boxes Hi! Alice CS 150 Fall 2005: 37

Padlocked Boxes Alice Hi! Alice’s Padlock Key CS 150 Fall 2005: 38

Padlocked Boxes Alice Shady Sammy’s Slimy Shipping Service Alice’s Padlock Key CS 150 Fall 2005: 39
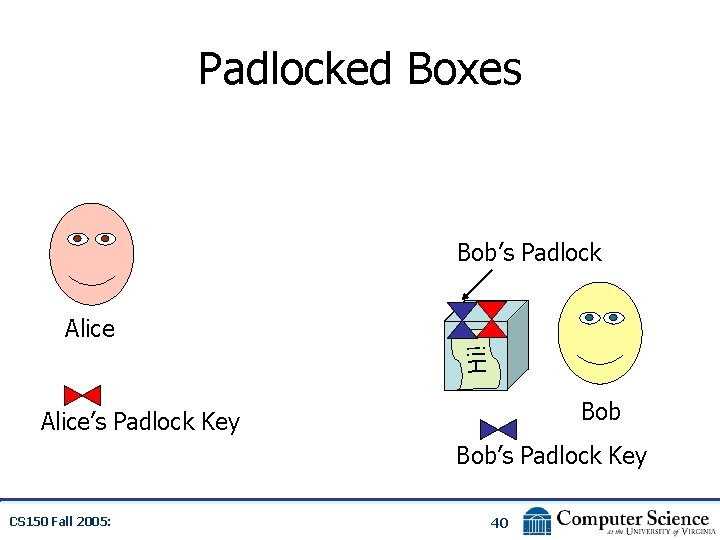
Padlocked Boxes Bob’s Padlock Hi! Alice Bob Alice’s Padlock Key Bob’s Padlock Key CS 150 Fall 2005: 40
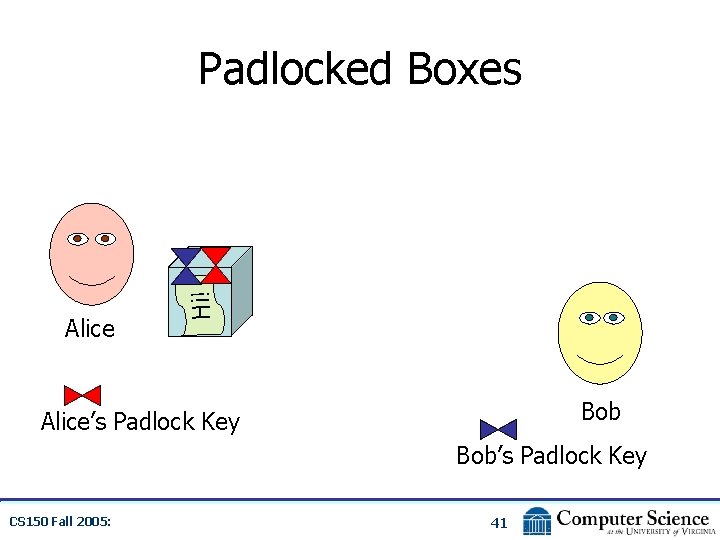
Alice Hi! Padlocked Boxes Bob Alice’s Padlock Key Bob’s Padlock Key CS 150 Fall 2005: 41
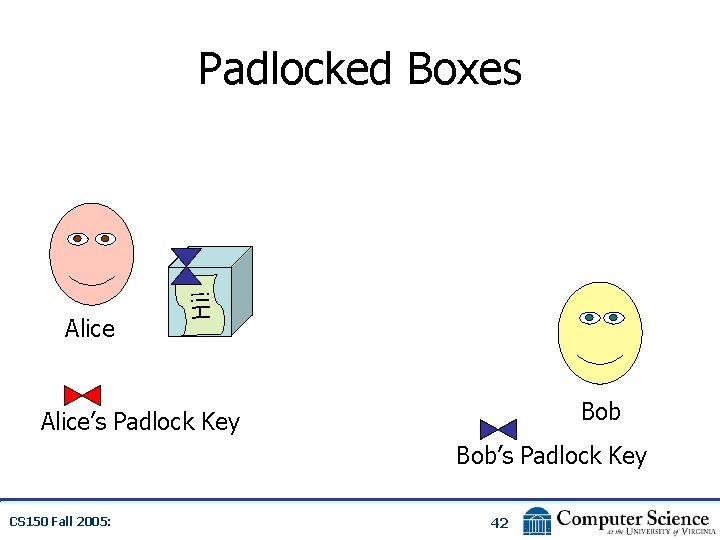
Alice Hi! Padlocked Boxes Bob Alice’s Padlock Key Bob’s Padlock Key CS 150 Fall 2005: 42
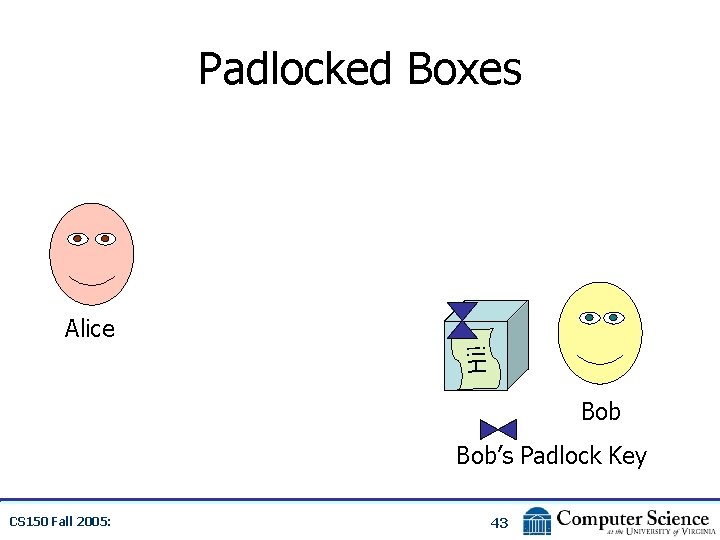
Padlocked Boxes Hi! Alice Bob’s Padlock Key CS 150 Fall 2005: 43
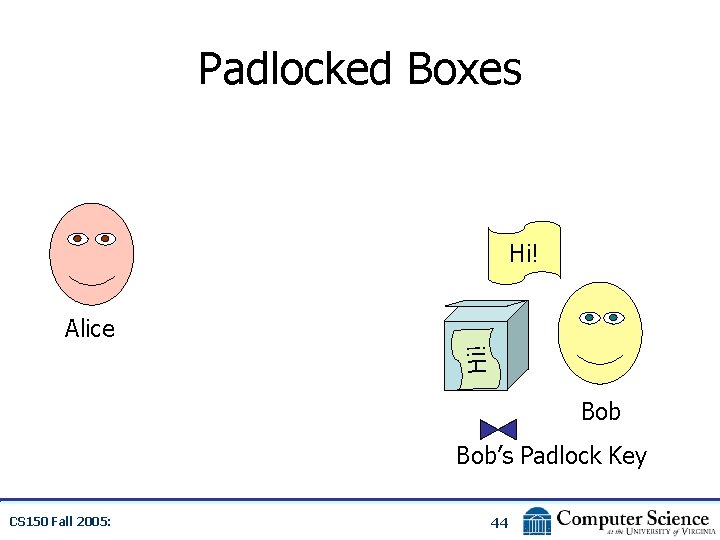
Padlocked Boxes Hi! Alice Bob’s Padlock Key CS 150 Fall 2005: 44
- Slides: 44