Claimsbased Identity Beyond Identity Silos 1 st European
Claims-based Identity Beyond Identity Silos 1 st European Identity Conference 2007 Don Schmidt Principal Program Manager Architect, Microsoft Corp http: //identity-des. com Copyright © 2007 Microsoft Corporation. All Rights Reserved.
Agenda • Identity Silos – Summary of problems and costs • Claims-based Identity – Identity Federation – Claim Transformation – User Selection • Rx for Identity Silos – Enterprise Directory to Identity Metasystem Copyright © 2007 Microsoft Corporation. All Rights Reserved.
e. Commerce System Snapshot • Network de-perimeterization – Organizational boundaries dissolving • Service oriented application architecture – Reusable, “legonic” web services • Isolated, inflexible Identity silos – Local identity system is the only source of truth • Authenticates all users directly • Manages authoritative version of all user attributes Copyright © 2007 Microsoft Corporation. All Rights Reserved.
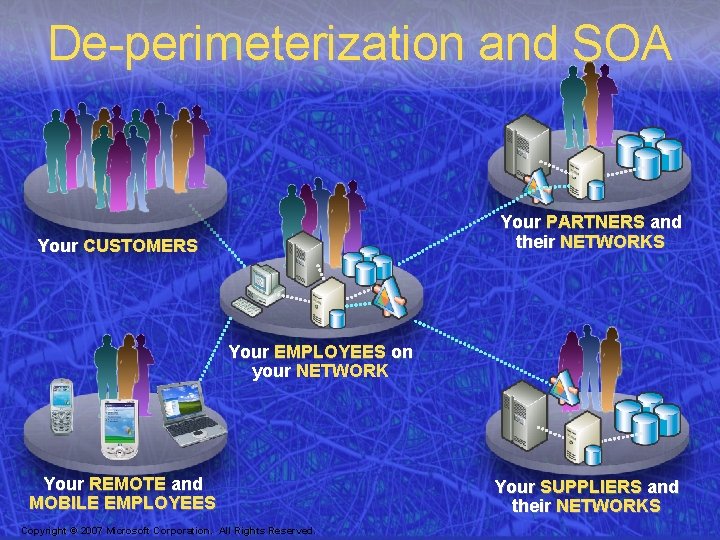
De-perimeterization and SOA Your PARTNERS and their NETWORKS Your CUSTOMERS Your EMPLOYEES on your NETWORK Your REMOTE and MOBILE EMPLOYEES Copyright © 2007 Microsoft Corporation. All Rights Reserved. Your SUPPLIERS and their NETWORKS
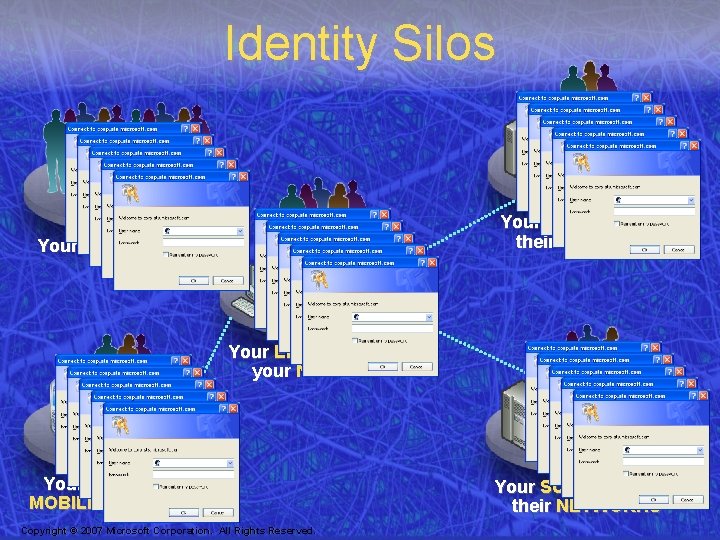
Identity Silos Your PARTNERS and their NETWORKS Your CUSTOMERS Your EMPLOYEES on your NETWORK Your REMOTE and MOBILE EMPLOYEES Copyright © 2007 Microsoft Corporation. All Rights Reserved. Your SUPPLIERS and their NETWORKS
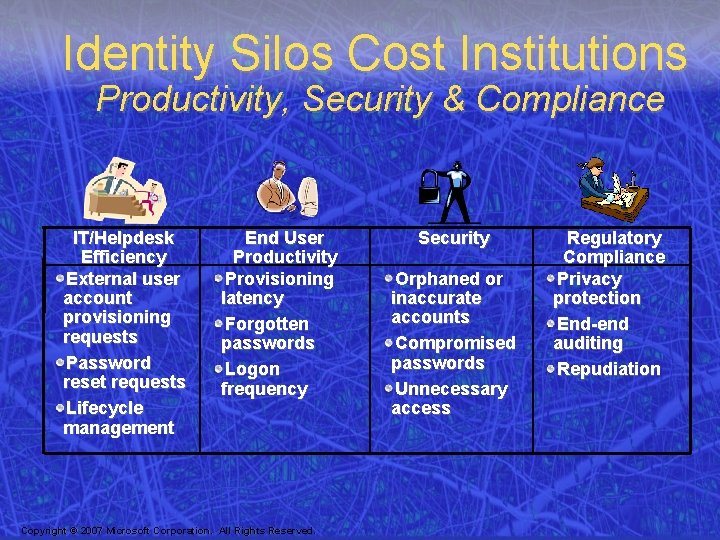
Identity Silos Cost Institutions Productivity, Security & Compliance IT/Helpdesk Efficiency External user account provisioning requests Password reset requests Lifecycle management End User Productivity Provisioning latency Forgotten passwords Logon frequency Copyright © 2007 Microsoft Corporation. All Rights Reserved. Security Orphaned or inaccurate accounts Compromised passwords Unnecessary access Regulatory Compliance Privacy protection End-end auditing Repudiation
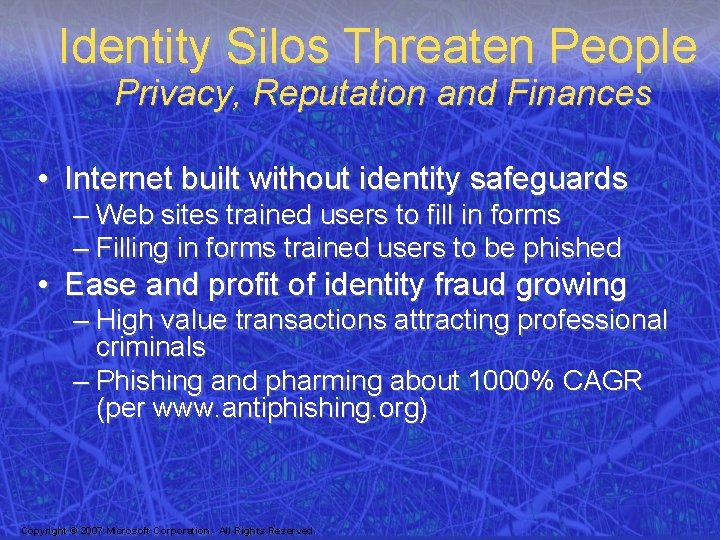
Identity Silos Threaten People Privacy, Reputation and Finances • Internet built without identity safeguards – Web sites trained users to fill in forms – Filling in forms trained users to be phished • Ease and profit of identity fraud growing – High value transactions attracting professional criminals – Phishing and pharming about 1000% CAGR (per www. antiphishing. org) Copyright © 2007 Microsoft Corporation. All Rights Reserved.
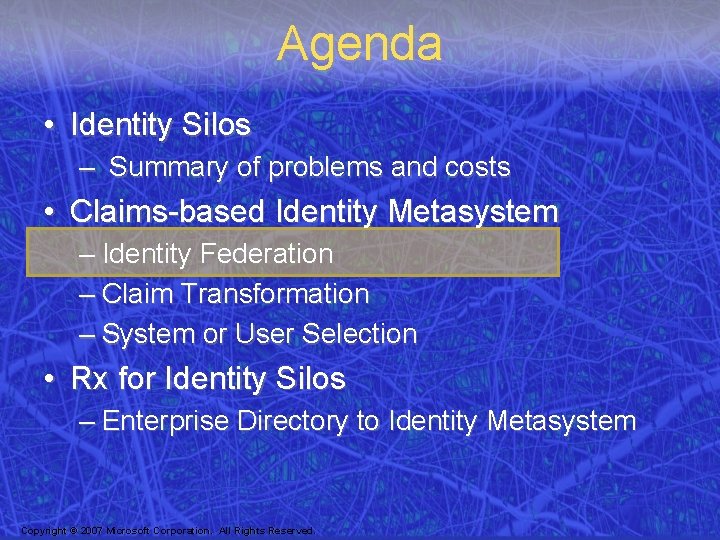
Agenda • Identity Silos – Summary of problems and costs • Claims-based Identity Metasystem – Identity Federation – Claim Transformation – System or User Selection • Rx for Identity Silos – Enterprise Directory to Identity Metasystem Copyright © 2007 Microsoft Corporation. All Rights Reserved.
Digital Identity • Set of claims about a subject – Asserted by subject or third party – Uniquely identify subject, describe attributes, both • Possibly many IDs for many purposes – Use may require proving ownership • Parallels physical world • Common model for access technology Copyright © 2007 Microsoft Corporation. All Rights Reserved.
Identity Federation • Relying Party does not mange identity • RP depends on external Identity Providers – Authenticate a subject – Provide accurate digital identity • RP determines “it’s truth” based on: – IP with closest relationship to subject, or – How IP authenticated subject, or – Average of multiple IPs, or … Copyright © 2007 Microsoft Corporation. All Rights Reserved.
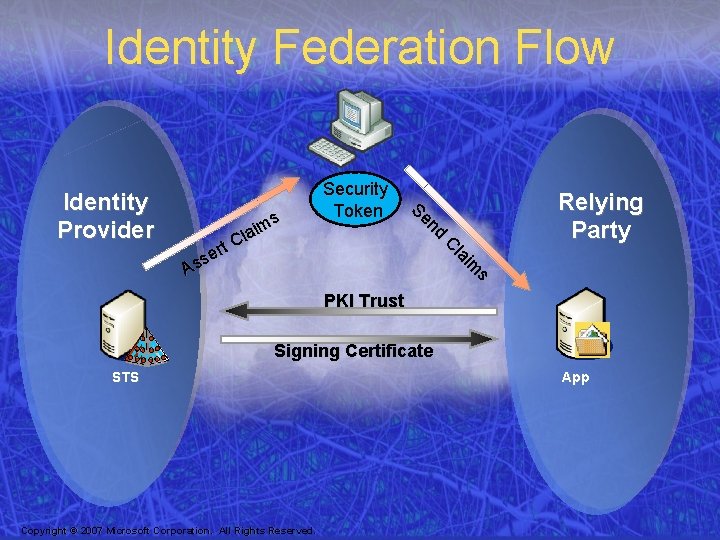
Identity Federation Flow s im la C ms i a l C t r se s A nd Se Identity Provider Security Token Relying Party PKI Trust Signing Certificate STS Copyright © 2007 Microsoft Corporation. All Rights Reserved. App
Agenda • Identity Silos – Summary of problems and costs • Claims-based Identity Metasystem – Identity Federation – Claim Transformation – System or User Selection • Rx for Identity Silos – Enterprise Directory to Identity Metasystem Copyright © 2007 Microsoft Corporation. All Rights Reserved.
Claim Transformation • Claims can be transformed by Security Token Services before RP consumes them • Provides impedance matching between RP, IP and subject – IP may not store claim values in same data type as RP requires – IP may not issue claims with same syntax as RP requires – User may want to send derived claims (e. g. >21) rather than stored claim value Copyright © 2007 Microsoft Corporation. All Rights Reserved.
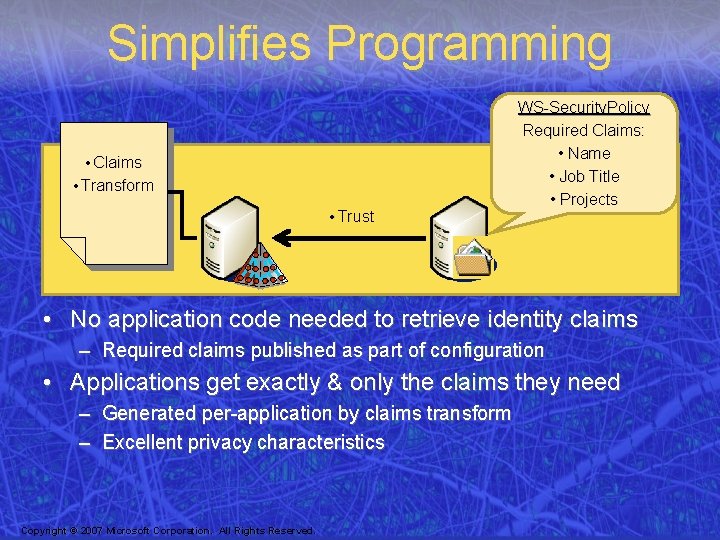
Simplifies Programming • Claims • Transform • Trust WS-Security. Policy Required Claims: • Name • Job Title • Projects • No application code needed to retrieve identity claims – Required claims published as part of configuration • Applications get exactly & only the claims they need – Generated per-application by claims transform – Excellent privacy characteristics Copyright © 2007 Microsoft Corporation. All Rights Reserved.
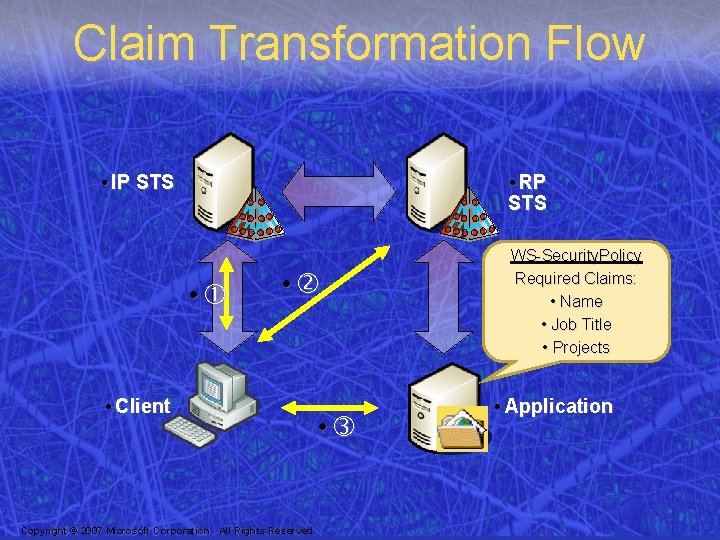
Claim Transformation Flow • IP STS • RP STS • • • Client Copyright © 2007 Microsoft Corporation. All Rights Reserved. • WS-Security. Policy Required Claims: • Name • Job Title • Projects • Application
Agenda • Identity Silos – Summary of problems and costs • Claims-based Identity Metasystem – Identity Federation – Claim Transformation – System or User Selection • Rx for Identity Silos – Enterprise Directory to Identity Metasystem Copyright © 2007 Microsoft Corporation. All Rights Reserved.

Laws of Identity Established through industry dialog 1. User control and consent 2. Minimal disclosure for a defined use 3. Justifiable parties 4. Directional identity 5. Pluralism of operators and technologies 6. Human integration 7. Consistent experience across contexts Copyright © 2007 Microsoft Corporation. All Rights Reserved.
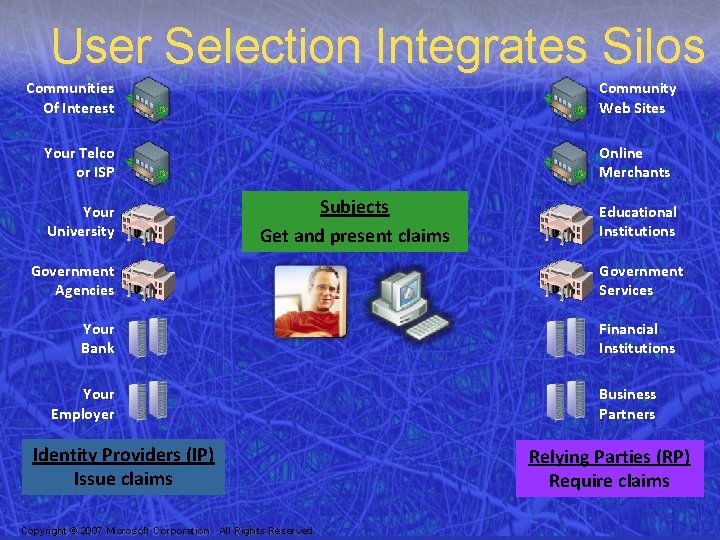
User Selection Integrates Silos Community Web Sites Communities Of Interest Online Merchants Your Telco or ISP Your University Subjects Get and present claims Government Agencies Your Bank Your Employer Identity Providers (IP) Issue claims Copyright © 2007 Microsoft Corporation. All Rights Reserved. Educational Institutions Government Services Financial Institutions Business Partners Relying Parties (RP) Require claims
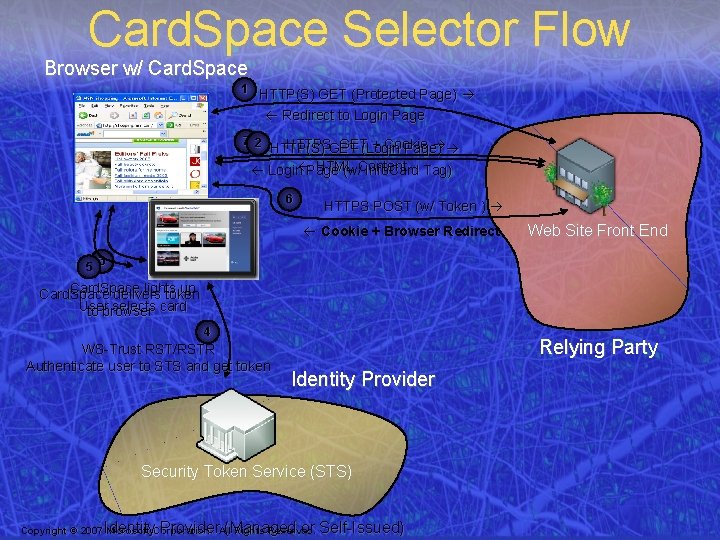
Card. Space Selector Flow Browser w/ Card. Space 1 HTTP(S) GET (Protected Page) Redirect to Login Page 7 2 HTTPSGET GET(Login + Cookie HTTP(S) Page) HTML Login Page (w/Content Info. Card Tag) 6 HTTPS POST (w/ Token ) Cookie + Browser Redirect Web Site Front End 5 3 Card. Space lights up Card. Space delivers token User selects card to browser 4 WS-Trust RST/RSTR Authenticate user to STS and get token Relying Party Identity Provider Security Token Service (STS) Identity Provider (Managed or Self-Issued) Copyright © 2007 Microsoft Corporation. All Rights Reserved.
Agenda • Identity Silos – Summary of problems and costs • Claims-based Identity Metasystem – Identity Federation – Claim Transformation – System or User Selection • Rx for Identity Silos – Enterprise Directory to Identity Metasystem Copyright © 2007 Microsoft Corporation. All Rights Reserved.
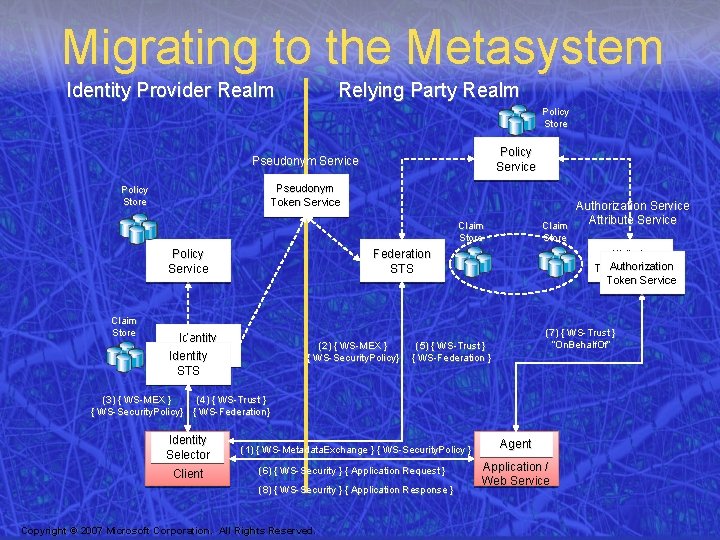
Migrating to the Metasystem Identity Provider Realm Relying Party Realm Policy Store Policy Service Pseudonym Token Service Policy Store Authorization Service Attribute Service Claim Store Policy Service Claim Store Federation STS Identity STS (2) { WS-MEX } { WS-Security. Policy} Attribute Authorization Token Service (7) { WS-Trust } “On. Behalf. Of” (5) { WS-Trust } { WS-Federation } (3) { WS-MEX } (4) { WS-Trust } { WS-Security. Policy} { WS-Federation} Identity Selector Client (1) { WS-Metadata. Exchange } { WS-Security. Policy } (6) { WS-Security } { Application Request } (8) { WS-Security } { Application Response } Copyright © 2007 Microsoft Corporation. All Rights Reserved. Agent Application / Web Service
Microsoft Open Specification Promise (OSP) • Perpetual legal promise that Microsoft will never bring legal action against anyone for using the protocols listed – Includes all the protocols underlying Card. Space • Issued September 2006 • http: //www. microsoft. com/interop/osp/ Copyright © 2007 Microsoft Corporation. All Rights Reserved.
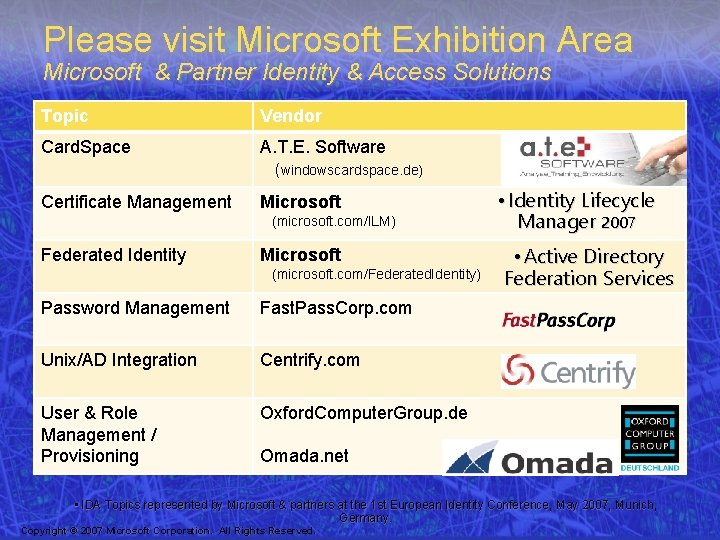
Please visit Microsoft Exhibition Area Microsoft & Partner Identity & Access Solutions Topic Vendor Card. Space A. T. E. Software (windowscardspace. de) Certificate Management Microsoft (microsoft. com/ILM) Federated Identity Microsoft (microsoft. com/Federated. Identity) Password Management Fast. Pass. Corp. com Unix/AD Integration Centrify. com User & Role Management / Provisioning Oxford. Computer. Group. de • Identity Lifecycle Manager 2007 • Active Directory Federation Services Omada. net • IDA Topics represented by Microsoft & partners at the 1 st European Identity Conference, May 2007, Munich, Germany. Copyright © 2007 Microsoft Corporation. All Rights Reserved.
Microsoft, Windows Vista and other product names are or may be registered trademarks and/or trademarks in the U. S. and/or other countries. The information herein is for informational purposes only and represents the current view of Microsoft Corporation as of the date of this presentation. Because Microsoft must respond to changing market conditions, it should not be interpreted to be a commitment on the part of Microsoft, and Microsoft cannot guarantee the accuracy of any information provided after the date of this presentation. MICROSOFT MAKES NO WARRANTIES, EXPRESS, IMPLIED OR STATUTORY, AS TO THE INFORMATION IN THIS PRESENTATION. Copyright © 2007 Microsoft Corporation. All Rights Reserved.
- Slides: 24