Civil Subpoenas and User Anonymity Matt Zimmerman Senior
Civil Subpoenas and User Anonymity Matt Zimmerman Senior Staff Attorney EFF Bootcamp May 11, 2009
Congratulations: You’re Now a Subpoena Magnet!
Overview: Navigating Legal Process o Law enforcement inquiries o DMCA notices o Civil Subpoenas o Other
Potentially Anonymity-Piercing Info In Your Possession o Registration info (e. g. name) o E-mail address o IP logs o Communication content
Why Protect Anonymity?
A Few Good Reasons Mc. Intyre v. Ohio Elections Comm’n 514 U. S. 334 (1995) “Anonymity is a shield from the tyranny of the majority. . . [that] exemplifies the purpose [of the First Amendment] to protect unpopular individuals from retaliation … at the hand of an intolerant society. ”
A Few Good Reasons Mc. Intyre v. Ohio Elections Comm’n, 514 U. S. 334 (1995) “[A]n author’s decision to remain anonymous, like other decisions concerning omissions or additions to the content of a publication, is an aspect of the freedom of speech protected by the First Amendment. ”
A Few Good Reasons Gibson v. Fla. Legislative Investigative Comm’n, 372 U. S. 539 (1963) “[I]t is. . . clear that [free speech guarantees]. . . encompass[] protection of privacy association …”
A Few Good Reasons Talley v. California, 362 U. S. 60 (1960) Finding a municipal ordinance requiring identification on hand-bills unconstitutional, and noting that “[a]nonymous pamphlets, leaflets, brochures and even books have played an important role in the progress of mankind. ”
A Few Good Reasons Doe v. 2 the. Mart. com, 140 F. Supp. 2 d 1088 (W. D. Wash. 2001) “The right to speak anonymously extends to speech via the Internet anonymity facilitates the rich, diverse, and far ranging exchange of ideas. ”
First Amendment Limitations on Civil Subpoenas Seeking Identity Information
Party Subpoenas: The Dendrite Standard Dendrite Int'l v. Doe No. 3, 342 N. J. Super. 134 (App. Div. 2001)
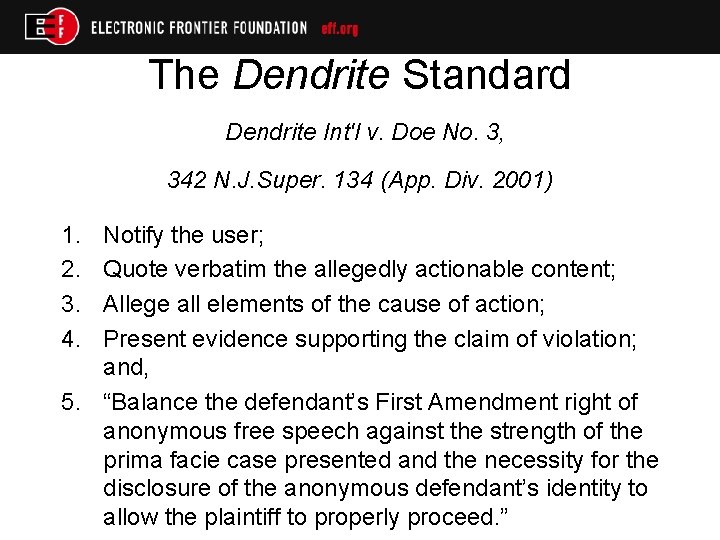
The Dendrite Standard Dendrite Int'l v. Doe No. 3, 342 N. J. Super. 134 (App. Div. 2001) 1. 2. 3. 4. Notify the user; Quote verbatim the allegedly actionable content; Allege all elements of the cause of action; Present evidence supporting the claim of violation; and, 5. “Balance the defendant’s First Amendment right of anonymous free speech against the strength of the prima facie case presented and the necessity for the disclosure of the anonymous defendant’s identity to allow the plaintiff to properly proceed. ”
Non-Party Subpoenas: The 2 the. Mart Factors Doe v. 2 the. Mart. com, 140 F. Supp. 2 d 1088 (W. D. Wash. 2001)
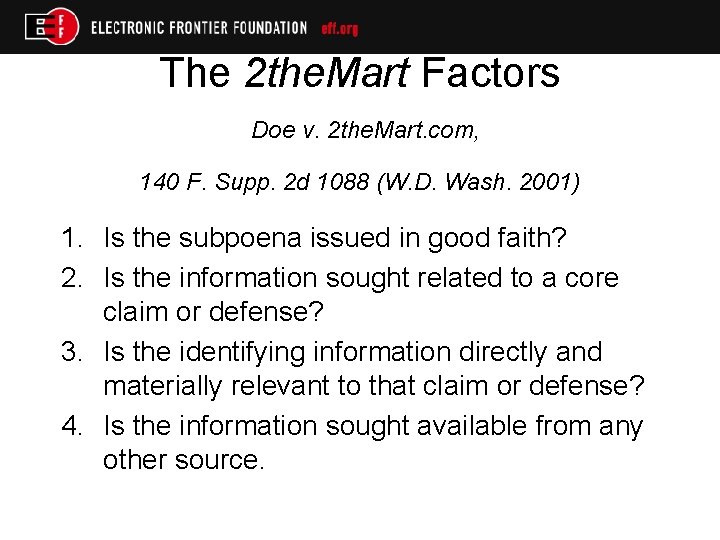
The 2 the. Mart Factors Doe v. 2 the. Mart. com, 140 F. Supp. 2 d 1088 (W. D. Wash. 2001) 1. Is the subpoena issued in good faith? 2. Is the information sought related to a core claim or defense? 3. Is the identifying information directly and materially relevant to that claim or defense? 4. Is the information sought available from any other source.
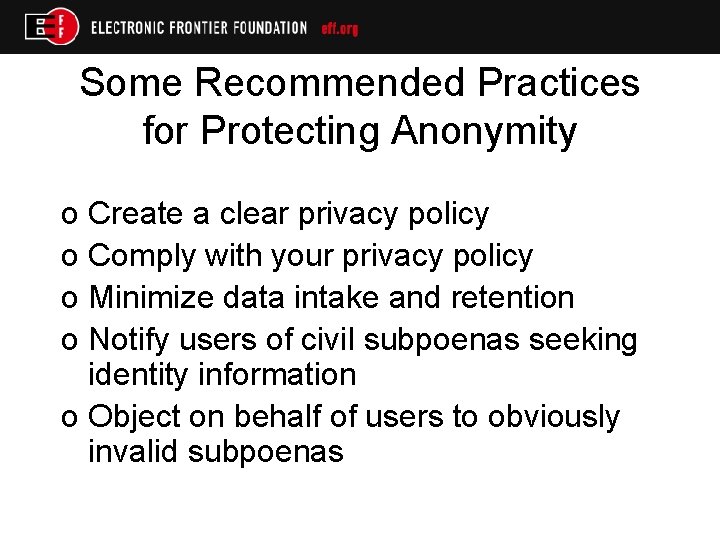
Some Recommended Practices for Protecting Anonymity o Create a clear privacy policy o Comply with your privacy policy o Minimize data intake and retention o Notify users of civil subpoenas seeking identity information o Object on behalf of users to obviously invalid subpoenas
A Few Examples, Good and Bad o Manalapan v. Moskovitz o Burd v. Cole o Fix Wilson Yard v. Chicago o Autoadmit o Lesher v. John Doe
For more information EFF’s Legal Guide For Bloggers http: //www. eff. org/issues/bloggers/legal Matt Zimmerman, Senior Staff Attorney Electronic Frontier Foundation mattz@eff. org http: //www. eff. org
- Slides: 18