CIT 485 Advanced Cybersecurity Cybercrime CIT 485 Advanced
CIT 485: Advanced Cybersecurity Cybercrime CIT 485: Advanced Cybersecurity Slide #1
Topics 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. 11. What is cybercrime? Spam, Phishing, and Fraud Intrusions Extortion (ransomware and more) Data Breaches Identity Theft Intellectual Property Theft Cyberbullying and cyberstalking Cyberterrorism and cyberwarfare Cybercrime Laws Government Partners CIT 485: Advanced Cybersecurity Slide #2
Cybercrime includes crimes in which �the computer is the target of a crime, such as denial of service or installation of malware, �the computer is incidentally used to commit traditional crimes, such as fraud, sometimes called cyber-assisted crimes. �the computer is used to more effectively commit crimes, such as sexual exploitation (child pornography, solicitation of minors), also called cyber-exacerbated crimes. �the computer is an accessory or a device that contains data incidental to the crime, such as location data. There are many different types of cybercrime. CIT 485: Advanced Cybersecurity Slide #3
Spam is the use of electronic messaging systems to send unsolicited bulk messages, especially advertising, indiscriminately. �Types: E-mail, IM, wiki, comment spam. Used to deliver other attacks �Malware �Phishing and other fraud enticements Slide #4
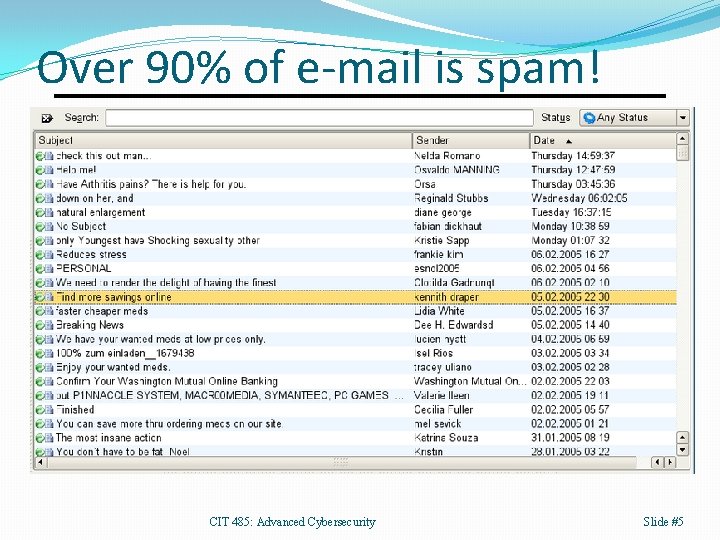
Over 90% of e-mail is spam! CIT 485: Advanced Cybersecurity Slide #5
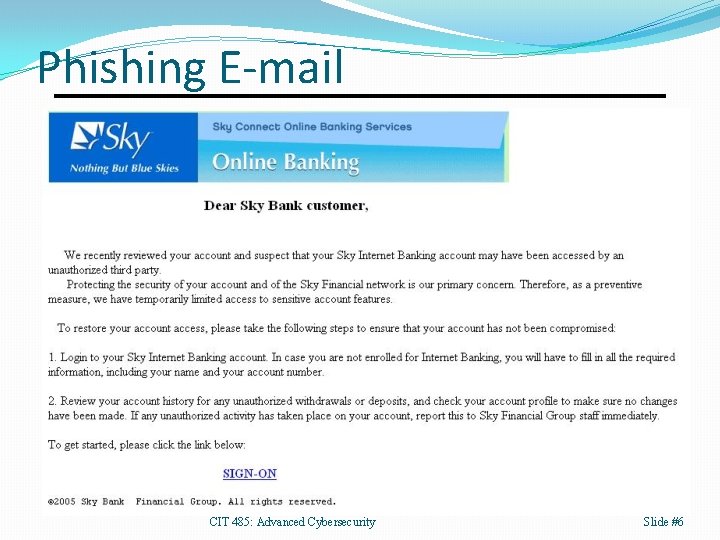
Phishing E-mail CIT 485: Advanced Cybersecurity Slide #6
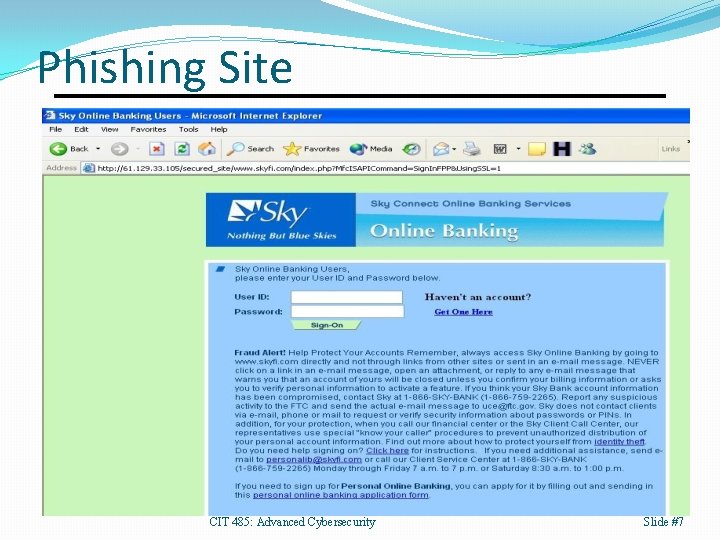
Phishing Site CIT 485: Advanced Cybersecurity Slide #7
Fraud is any misrepresentation of fact that lets another do something or refrain from doing something that causes loss. Example: Advance-fee scam �AKA: 419 scam or Nigerian Prince scam �Promises victim a share of a large sum of money in return for a small up front payment. �Dates back to 18 th century. CIT 485: Advanced Cybersecurity Slide #8
Fraud Examples �Carding �Purchase items with stolen card numbers. �Create copies of cards, then use quickly to withdraw maximum funds from ATMs or cash advances. �Identity theft �Steal SSNs and other identity information, then �Take out loans, get credit cards, etc. in person’s name. �File fraudulent tax forms to claim refunds �Obtain SSNs from big data breaches, or �Hack tax preparers who have everything needed. �Obtain business credentials to wire money. CIT 485: Advanced Cybersecurity Slide #9
Identity Theft Identity theft is deliberate use of someone else’s identity to obtain money or harass the victim. Motives for identity theft include �Financial: bank accounts, credit cards, tax refunds, taking out loans, using victim’s insurance, etc. �Hiding from debts or law enforcement. Identity information includes a person’s name, date of birth, SSN, fingerprints driver’s license, bank account number, health or tax records, etc. �Can be obtained on an individual basis, or �Large data breaches can leak identity of millions. CIT 485: Advanced Cybersecurity Slide #10
Intrusions �Criminals intrude into networks and systems to �Obtain information to sell or use in another scheme. �Obtain computing resources to use for tasks like cryptocurrency mining. �Intrusions often result in the installation of malware on the victim’s system(s). CIT 485: Advanced Cybersecurity Slide #11
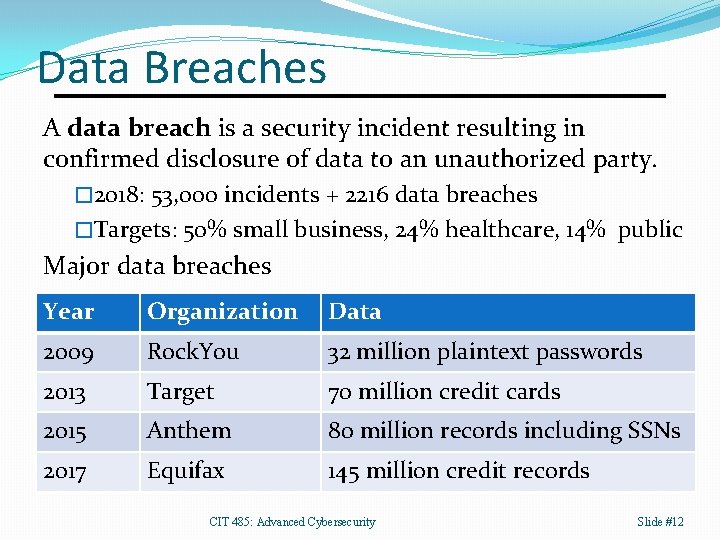
Data Breaches A data breach is a security incident resulting in confirmed disclosure of data to an unauthorized party. � 2018: 53, 000 incidents + 2216 data breaches �Targets: 50% small business, 24% healthcare, 14% public Major data breaches Year Organization Data 2009 Rock. You 32 million plaintext passwords 2013 Target 70 million credit cards 2015 Anthem 80 million records including SSNs 2017 Equifax 145 million credit records CIT 485: Advanced Cybersecurity Slide #12
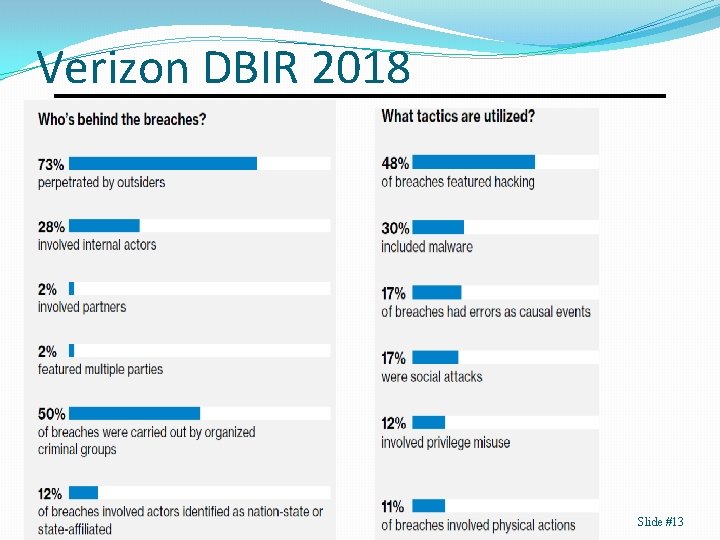
Verizon DBIR 2018 Slide #13
Extortion Criminals contact victims to demand money in order for the criminal to take or not take an action, such as �Providing the key to decrypt the victim’s data, which the criminal secretly encrypted using ransomware. �Not releasing private data of a person or company that was obtained by a previous intrusion. �Not performing a denial of service attack against an organization. CIT 485: Advanced Cybersecurity Slide #14
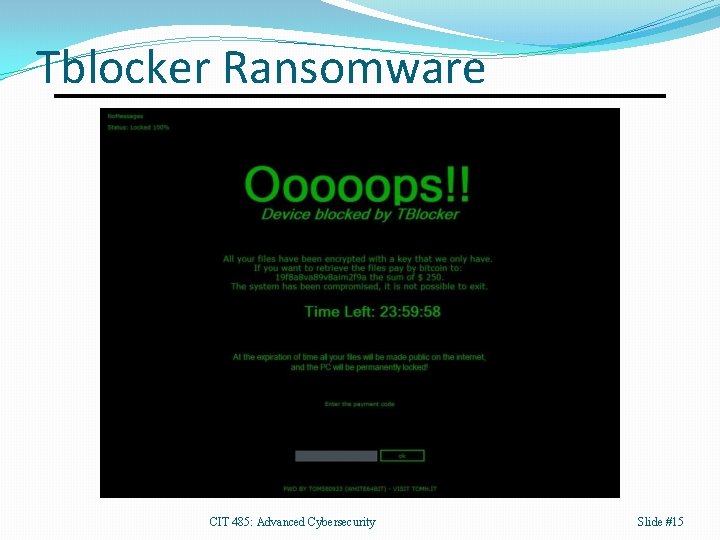
Tblocker Ransomware CIT 485: Advanced Cybersecurity Slide #15
Intellectual Property Criminals want to obtain information assets, such as �Copyrighted software, music, or other media. �Patented inventions. �Corporate secrets, such as plans for a new product. IP “theft” is different from actual theft in the real world �Victim usually still has the “stolen” information, so �Without good logging and audit processes, an organization may not detect such a “theft” until a competitor produces their own version of the product. �Cyberespionage frequently targets military and other high tech products. CIT 485: Advanced Cybersecurity Slide #16

Windows 10 source code CIT 485: Advanced Cybersecurity Slide #17
Cybercrime Organization Sponsors �Governments, corporations, activists, organized crime. Cybercrime Boss �Plans crime, recruits tech providers and money mules. Technology Providers �Deployment providers �Malware authors �Botnet masters Money Mules �Ship stolen goods, use fake cards, wire transfers. �Cybercrime limited by the number of mules available. CIT 485: Advanced Cybersecurity Slide #18
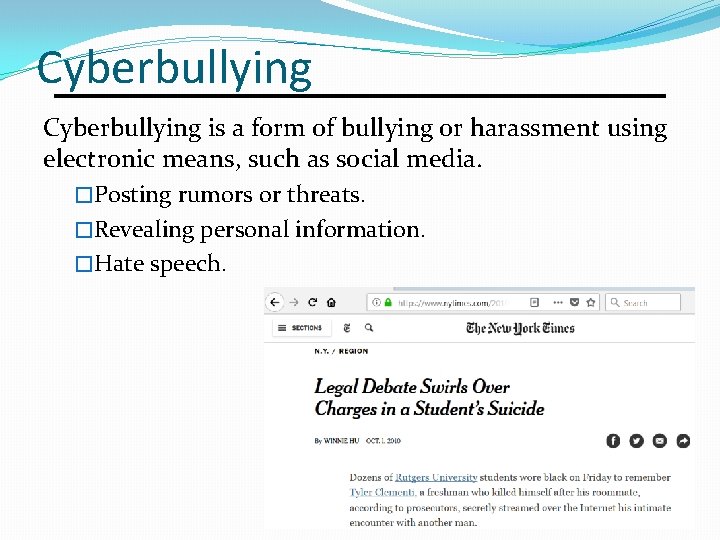
Cyberbullying is a form of bullying or harassment using electronic means, such as social media. �Posting rumors or threats. �Revealing personal information. �Hate speech. Slide #19
Cyberstalking is the use of information resources to stalk or harass an individual or organization. It is a form of cyberbullying. �A criminal offense under various state laws. �Often accompanied by real world stalking. �Often performed by predators who enjoy harassing either friends/romantic partners or random people. �Includes monitoring target’s online activities through social media and open sites, obtaining the victim’s password, and installing spyware to help monitor the victim. CIT 485: Advanced Cybersecurity Slide #20

Remote Access Trojans CIT 485: Advanced Cybersecurity Slide #21

RAT User Interface Slide #22
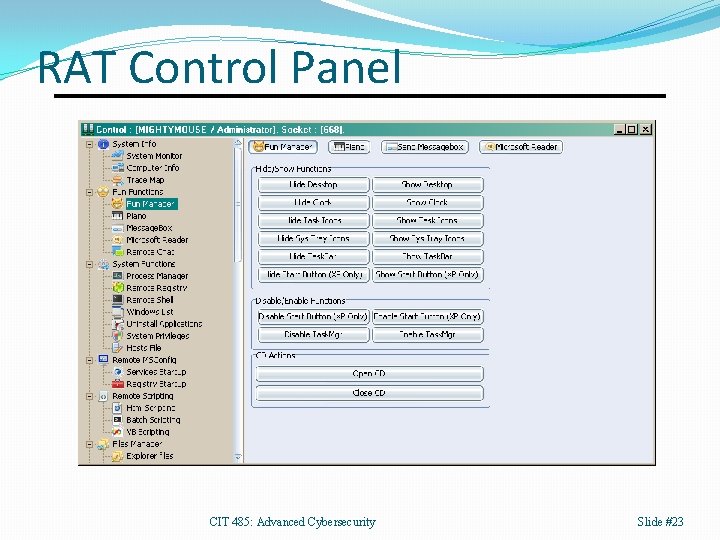
RAT Control Panel CIT 485: Advanced Cybersecurity Slide #23
Doxing is the practice of broadcasting private or identifiable information about an individual or organization for a variety of motives including �Political activism (hacktivism). �Cyberbullying or cyberstalking. �Extortion. Examples �In the 1990 s, anti-abortion activists posted home addresses and photos of doctors as a hit list. �After the 2013 Boston Marathon bombing, vigilantes on reddit misidentified several people as suspects. CIT 485: Advanced Cybersecurity Slide #24
The U. S. Code �Ethical hacking must be done in accordance with all applicable laws, otherwise criminal prosecution and / or civil litigation could result �The U. S. Code is an organized collection of every law ever created by the Legislative branch of the United States �It is organized into 53 titles covering all aspects of government from observed holidays (Title 36) to voting and elections (Title 52) to taxes (Title 26) �Title 18: Crimes and Criminal Procedures, contains most of the laws for which a person can be charged with a federal crime and tried in a court of law (more on state laws later)
Title 18 Cyber-Related Crimes �Even if a person does something that seems like it should be illegal, without reference to a law “on the books” no criminal prosecution can occur �Furthermore, whatever law is used to charge an individual with a crime must be specific enough to “stick” – lawyers are masters of arguing about the strict definitions of terms �Crimes involving computer technology have necessitated the creation of new laws so that the law could better fit the crime �The main federal cybercrime laws are the following: � Title 18, Section 1030: The Computer Fraud and Abuse Act (CFAA) � Title 18, Sections 2510 -2522 : The Electronic Communications Privacy Act � Title 18, Sections 2701 -2712: The Stored Communications Act � Title 18, Sections 1831 -1832: The Economic Espionage Acts
Computer Fraud & Abuse Act �Passed in 1986, the CFAA is the umbrella “anti-hacking” law �It is very broad and is used to prosecute a huge variety of cases, and sometimes this means the charges do not stick � U. S. v. Drew is a famous cyberbullying case where the CFAA didn’t stick � Since then states have passed cyberbullying-specific laws �The first successful conviction was in 1990 in U. S. v. Morris � Robert Tappan Morris unleashed the first Internet worm (the Morris Worm) � He had just graduated from Harvard; now he is a professor at MIT �Punishment can be minor (i. e. , a misdemeanor conviction) such as a fine or major (i. e. , a felony conviction) such as 5 years in prison �Civil action can also be taken – civil lawsuits are where one private party sues another party for causing harm (in this case, in connection with violating the CFAA)
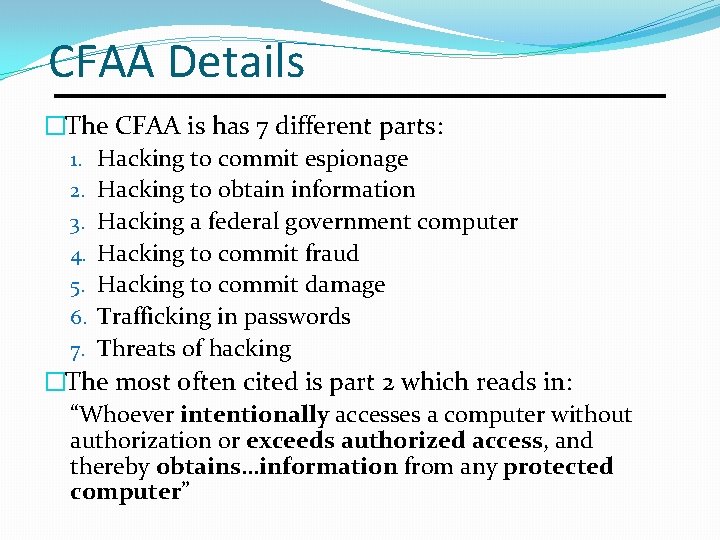
CFAA Details �The CFAA is has 7 different parts: 1. Hacking to commit espionage 2. Hacking to obtain information 3. Hacking a federal government computer 4. Hacking to commit fraud 5. Hacking to commit damage 6. Trafficking in passwords 7. Threats of hacking �The most often cited is part 2 which reads in: “Whoever intentionally accesses a computer without authorization or exceeds authorized access, and thereby obtains…information from any protected computer”
Example: Video Poker Bug Let’s practice trying a CFAA case together as a class, using the story of a couple of guys who got rich exploiting a bug in a video poker machine: Is exploiting a video poker software bug to multiply winnings a violation of the Computer Fraud and Abuse Act? Here are the relevant facts of the case: • Using an elaborate sequence of screen clicks the defendants were able to cause video poker machines to pay out 10 times the correct amount of winnings; therefore, they knowingly defrauded casinos • The defendants did not tamper with the hardware or the software of the video poker machines in any way • A video poker machine is not connected to the Internet
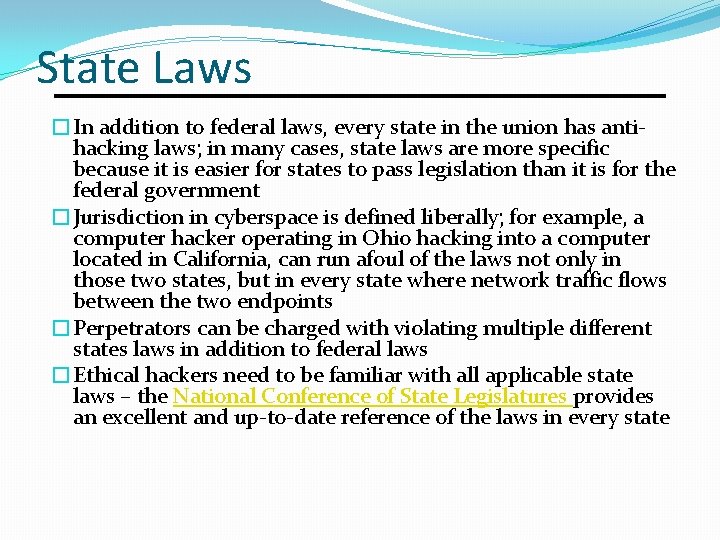
State Laws �In addition to federal laws, every state in the union has antihacking laws; in many cases, state laws are more specific because it is easier for states to pass legislation than it is for the federal government �Jurisdiction in cyberspace is defined liberally; for example, a computer hacker operating in Ohio hacking into a computer located in California, can run afoul of the laws not only in those two states, but in every state where network traffic flows between the two endpoints �Perpetrators can be charged with violating multiple different states laws in addition to federal laws �Ethical hackers need to be familiar with all applicable state laws – the National Conference of State Legislatures provides an excellent and up-to-date reference of the laws in every state
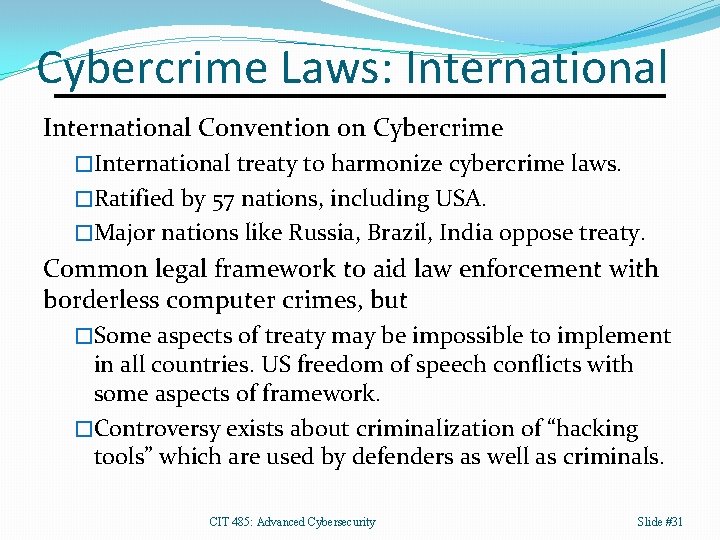
Cybercrime Laws: International Convention on Cybercrime �International treaty to harmonize cybercrime laws. �Ratified by 57 nations, including USA. �Major nations like Russia, Brazil, India oppose treaty. Common legal framework to aid law enforcement with borderless computer crimes, but �Some aspects of treaty may be impossible to implement in all countries. US freedom of speech conflicts with some aspects of framework. �Controversy exists about criminalization of “hacking tools” which are used by defenders as well as criminals. CIT 485: Advanced Cybersecurity Slide #31
Cyberespionage CIT 485: Advanced Cybersecurity Slide #32
Cyberterrorism is the use of electronic resources to conduct violent acts in order to achieve political goals through intimidation. �Large-scale long term denial of service attacks or denial of service attacks focused on emergency services like 911. �Erasure of all computer’s storage systems in an organization. �Usurping control of SCADA (Supervisory Control And Data Acquisition) systems to destroy controlled hardware. �Shutting down a country’s power grid. CIT 485: Advanced Cybersecurity Slide #33
USA PATRIOT Act (2001) Broadens law enforcement powers, including �Expands scope and availability of surveillance. �Anti-money-laundering provisions. �Expanded immigration powers, including indefinite detention. �Increased ability of agencies to share information about terrorism. �Prohibits cyberextortion, exacerbates punishments for computer crimes. �National Security Letters: permanent gag order, cannot be contended before a judge. CIT 485: Advanced Cybersecurity Slide #34
Cyberwarfare CIT 485: Advanced Cybersecurity Slide #35
Stuxnet Malware that targeted SCADA systems in Iran that operated centrifuges used to refine Uranium. �Spread via network and USB drives, so it could reach airgapped networks. �Altered centrifuge rotational frequency rapidly from over 1 k. Hz to 2 Hz and back, wearing out motors to gradually destroy centrifuges. �Accidentally discovered when infecting systems outside of Iran. CIT 485: Advanced Cybersecurity Slide #36
Government Partners: Federal �FBI �Has a mission to investigate cybercrime. �FBI Cyber Division handles intrusions. �Infragard. �FBI partnership with industry to share information and help protect important infrastructure and industries. �Internet Crime Complaint Center (IC 3) �Clearinghouse for cybercrime (fraud) complaints. �NIST �Publishes cybersecurity standards, such as the NIST Cybersecurity Framework and SP 800 -53. CIT 485: Advanced Cybersecurity Slide #37
Government Partners: State �Attorney General’s Office �Provides expert criminal investigative services for cybercrimes in many states. �Cyber Fusion/Operation Centers �Collect reports of cyber crimes. �Watch critical infrastructure, provide training, &c. �National Guard �Most states have cybersecurity units. �Support DHS, FBI, NSA on protecting infrastructure. CIT 485: Advanced Cybersecurity Slide #38
References 1. Nate Anderson. Meet the men who spy on women through their webcams: The Remote Administration Tool is the revolver of the Internet's Wild West. Ars Technica, http: //arstechnica. com/techpolicy/2013/03/rat-breeders-meet-the-men-who-spy-on-womenthrough-their-webcams/, 2013. 2. Will Gragido and John Pirc. Cybercrime and Espionage: An Analysis of Subversive Multi-Vector Threats. Syngress. 2011. 3. Seth Hammon. Intro to Cyber Law and Ethics Module. CLARK. 2018. 4. Honeynet Project. Know Your Enemy, 2 nd edition, Addison-Wesley, 2004. 5. IBM X-Force Threat Intelligence Index 2018. 6. Verizon. 2018 Data Breach Investigation Report. 2018. 7. Michael E. Whitman and Herbert J. Mattord. Principles of Information Security, 6 th Edition. Course Technology. 2017. CIT 485: Advanced Cybersecurity Slide #39
Released under CC BY-SA 3. 0 § All slides in this presentation unless otherwise noted are released under the Creative Commons Attribution. Share. Alike 3. 0 Unported (CC BY-SA 3. 0) license § You are free: § to Share — to copy and redistribute the material in any medium § to Adapt— to remix, build, and transform upon the material § to use part or all of this presentation in your own classes § Under the following conditions: § Attribution — You must attribute the work to James Walden, but cannot do so in a way that suggests that he endorses you or your use of these materials. § Share Alike — If you remix, transform, or build upon this material, you must distribute the resulting work under this or a similar open license. § Details and full text of the license can be found at https: //creativecommons. org/licenses/by-nc-sa/3. 0/ CIT 485: Advanced Cybersecurity Slide #40
- Slides: 40