CIT 480 Securing Computer Systems Security Fundamentals About
CIT 480: Securing Computer Systems Security Fundamentals
About Me James Walden – Associate Professor of Computer Science – waldenj@nku. edu – http: //faculty. cs. nku. edu/~waldenj – Interests: • Software Security • Mobile Application Security • Web Application Security • Empirical Software Engineering
Topics 1. What is Security? 2. Security Concepts 1. Confidentiality 2. Integrity 3. Availability 3. States of Information 4. Policies and Principles 5. Security Controls
What is Security? Security is the prevention of certain types of intentional actions from occurring in a system. – The actors who might attack a system are threats. – Threats carry out attacks to compromise a system. – Objects of attacks are assets.
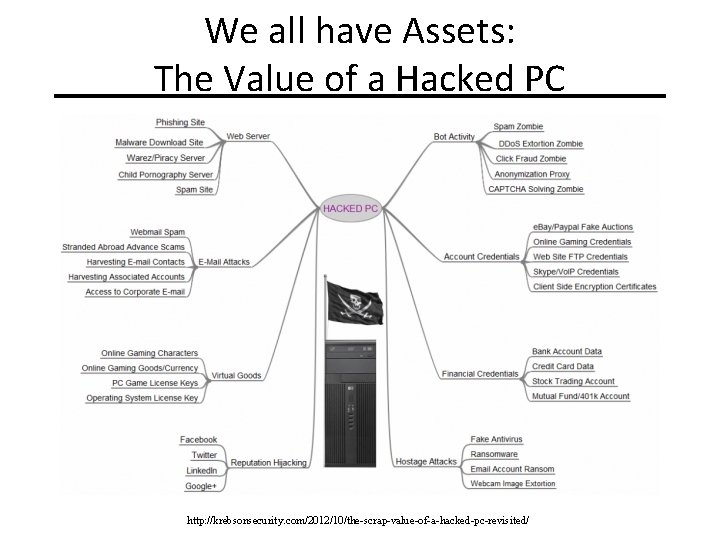
We all have Assets: The Value of a Hacked PC http: //krebsonsecurity. com/2012/10/the-scrap-value-of-a-hacked-pc-revisited/
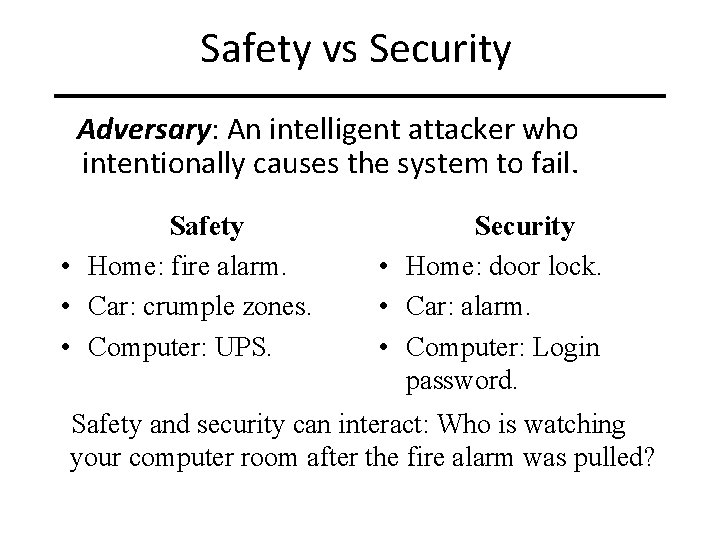
Safety vs Security Adversary: An intelligent attacker who intentionally causes the system to fail. Safety • Home: fire alarm. • Car: crumple zones. • Computer: UPS. Security • Home: door lock. • Car: alarm. • Computer: Login password. Safety and security can interact: Who is watching your computer room after the fire alarm was pulled?
Components of Security Integrity Confidentiality Availability
Confidentiality is the avoidance of the unauthorized disclosure of information. Examples where confidentiality is critical: – Personal information – Trade secrets – Military plans
Security Controls for Confidentiality Access Control: rules and policies that limit access to certain people and/or systems. – File permissions (which users can access) – Firewall settings (which IP addresses can access) Encryption: transforming information so that it can only be read using a secret key. – AES – SSL
Integrity is the property that information has not be altered in an unauthorized way. Examples where integrity is critical: – Operating system files – Software updates and downloads – Bank account records
Security Controls for Integrity • Backups: periodic archiving of data. • Checksums: the computation of a function that maps the contents of a file to a numerical value. • Intrusion detection: systems that look for signatures of attacks or that verify that all system software matches correct checksums.
Availability is the property that information is accessible and modifiable in a timely fashion by those authorized to do so. Examples where availability is critical: – E-commerce site – Authentication server for your network – Current stock quotes
Security Controls for Availability Physical protections: infrastructure meant to keep information available even in the event of physical challenges. – Backup generators – Disaster recovery site Computational redundancies: computers and storage devices that serve as fallbacks in the case of failures. – Backup tapes – RAID
Other Security Components Authenticity Anonymity Assurance
States of Information 1. Storage: information in permanent storage (disk or tape) that is not currently being accessed. 2. Processing: information in memory (RAM or cache) that is currently being used by a program. 3. Transmission: information in transit between one node and another on a network.
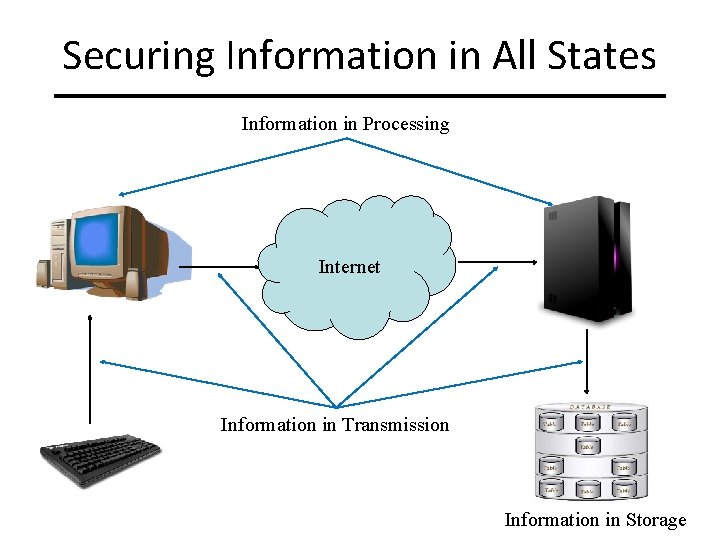
Securing Information in All States Information in Processing Internet Information in Transmission Information in Storage
Security Policies A security policy is a definition of what it means to be secure for a system or organization. – Security controls are used to enforce security policies. – Security policies hold even in the absence of a control to protect a system, e. g. you can commit a crime by entering someone’s house even if they didn’t lock the door. Examples: http: //oit. nku. edu/security/policies-and-guidelines. html • • Acceptable Use Policy Antivirus Policy Security Policy LISTSERV and Mass Email Policy
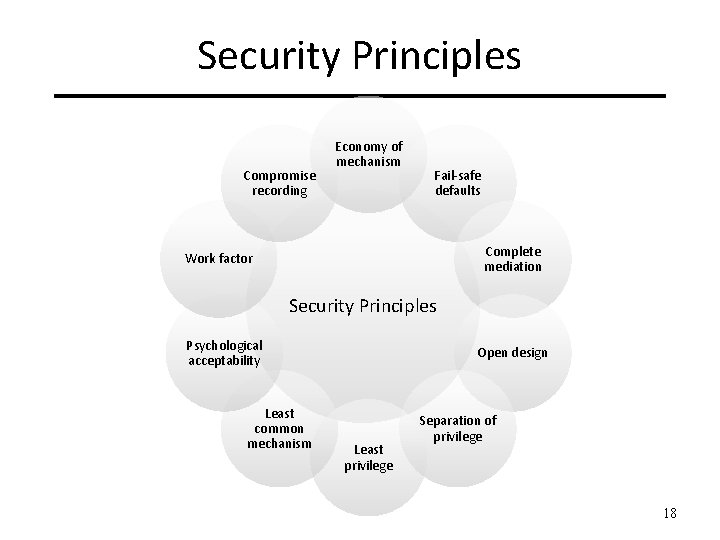
Security Principles Compromise recording Economy of mechanism Fail-safe defaults Complete mediation Work factor Security Principles Psychological acceptability Least common mechanism Open design Least privilege Separation of privilege 18
Security Controls Security controls are policies, technologies, or human factors that avoid, reduce, or counteract security risks. Controls act in three main ways: – Prevention: prevent attackers from violating security policy. Ex: firewall. – Detection: detect attackers’ violation of security policy. Ex: anti-virus. – Recovery: stop attack, assess and repair damage. Ex: backups.
Types of Security Controls Technologies – Hardware/software used to ensure confidentiality, integrity, or availability. Policy and practice. – Security requirements and activities. Education, training, and awareness. – Understanding of threats and vulnerabilities and how to protect against them.
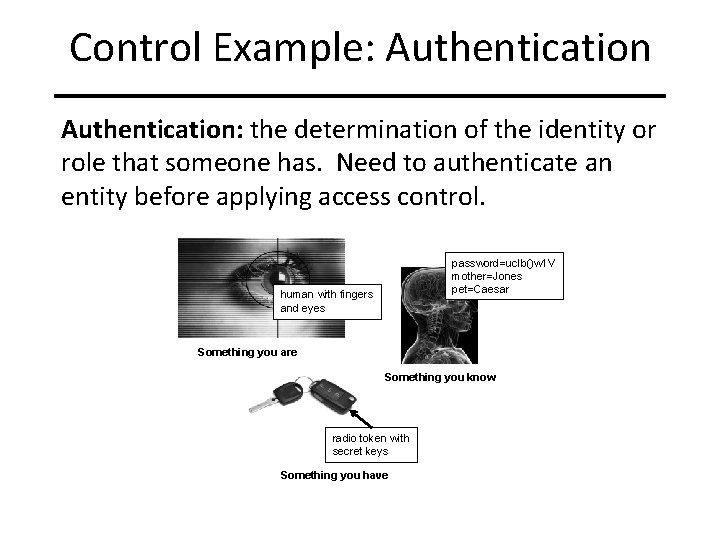
Control Example: Authentication: the determination of the identity or role that someone has. Need to authenticate an entity before applying access control. password=uc. Ib()w 1 V mother=Jones pet=Caesar human with fingers and eyes Something you are Something you know radio token with secret keys Something you have
How to evaluate security controls? 1. What assets are you trying to protect? 2. What are the risks to those assets? 3. How well does the security control mitigate those risks? 4. What other risks does the security control cause? 5. What costs and trade-offs does the security control impose?
Example: Password Vault 1. Asset: passwords. 2. Risks: use of passwords by someone else to gain access to private email, bank, health information. 3. Mitigate: encrypted storage prevents use of passwords without vault key. 4. Other risks: lose access to all passwords if you forget the vault key. 5. Costs/tradeoffs: if vault is on PC, lose access elsewhere. If vault is networked, passwords may not be encrypted in transit, will be accessible to attackers who don’t have access to your PC.
Security is a matter of Trade-offs Security is only one of many system goals: • Functionality • Usability • Efficiency • Time to market • Cost • Security
Aspects of Risks To evaluate a risk, we need to evaluate both: – Probability of risk occurring. – Cost incurred by risk if it occurs. Minimize product of probability and cost. Risks are impacted by environment. – Building a house in a flood plain incurs additional risks beyond that of house itself. – Similarly, installation and configuration options impact risk of software systems.
Cost-Benefit Analysis Is it cheaper to prevent violation or recover? – Cost of good network security: • Money, time, reduced functionality, annoyed users. • Large and ongoing. – Risks of bad network security: • Angry customers, bad press, network downtime. • Small and temporary.
Security: Laws and Customs Are desired security measures illegal? – cryptography export before 2000 – is it legal to monitor security breakins? – international commerce Will users circumvent them? – writing down passwords – removing file ACLs
Security Liability Product liability: – Tires: Continental recalled Ford SUV tires in 2002 due to wire and vibration problems. – Software: Manufacturer not liable for security flaws. Since Microsoft isn’t liable for Windows security failures, why would they want to sacrifice money, time, functionality, and ease of use for security?
Assumptions Security rests on assumptions specific to type of security required and environment. Example: – TCP/IP designed for pre-commercial Internet. • Assumed only legitimate admins had root access. • Trusted IP addresses, since only root can set IP addr. • What happens to network when everyone has personal devices with administrative (root) access?
What do you trust? Your vendor’s software – “Yet another picture frame malware incident” – http: //blog. trendmicro. com/trendlabs-security-intelligence/yetanother-digital-picture-frame-malware-incident/ Your encryption libraries – RSA warns customers to stop using BSAFE lib – http: //rt. com/usa/nsa-weak-cryptography-rsa-110/ Your ISP – ISP hijacks DNS and adds affiliates to URLs – http: //erichelgeson. github. io/blog/2013/12/31/i-fought-my-ispsbad-behavior-and-won/
Can you trust your compiler? Ken Thompson’s compiler hack from “Reflections on Trusting Trust. ” – Modified C compiler does two things: • If compiling a compiler, inserts the self-replicating code into the executable of the new compiler. • If compiling login, inserts code to allow a backdoor password. – After recompiling and installing old C compiler: • Source code for Trojan horse does not appear anywhere in login or C compiler. • Only method of finding Trojan is analyzing binary.
Key Points 1. Definitions Security, security policy, security control, threat, attack, asset. 2. Components of security Confidentiality, Integrity, Availability 3. Protect CIA in all states of information: Storage, Processing, Transmission 4. Security Controls Technology, policy, education 5. Cost-Benefit Analysis Probability × cost of the risk 6. Policy and Principles
References 1. Anderson, Security Engineering 2 nd Edition, Wiley, 2008. 2. Bishop, Computer Security: Art and Science, Addison-Wesley, 2002. 3. Goodrich and Tammasia, Introduction to Computer Security, Pearson, 2011.
- Slides: 33