CIT 380 Securing Computer Systems Cryptography Basics CIT
CIT 380: Securing Computer Systems Cryptography Basics CIT 380: Securing Computer Systems Slide #1
Topics 1. 2. 3. 4. 5. 6. Cryptographic Concepts History of Cryptography Symmetric Encryption Public Key Encryption Digital Signatures Message Authentication Codes CIT 380: Securing Computer Systems Slide #2
Cryptographic Concepts Encryption: a means to allow two parties to establish confidential communication over an insecure channel that is subject to eavesdropping. Alice Bob Eve 3
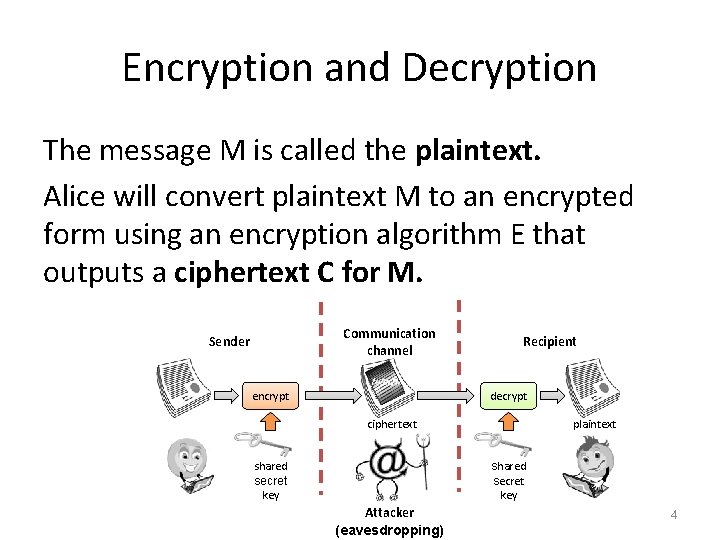
Encryption and Decryption The message M is called the plaintext. Alice will convert plaintext M to an encrypted form using an encryption algorithm E that outputs a ciphertext C for M. Communication channel Sender encrypt Recipient decrypt ciphertext plaintext shared secret key Attacker (eavesdropping) 4
Encryption and Decryption As equations: C = E(M) M = D(C) The encryption and decryption algorithms are chosen so that it is infeasible for someone other than Alice and Bob to determine plaintext M from ciphertext C. Thus, ciphertext C can be transmitted over an insecure channel that can be eavesdropped by an adversary. 5
Cryptosystem 1. 2. 3. 4. 5. The set of possible plaintexts The set of possible ciphertexts The set of encryption keys The set of decryption keys The correspondence between encryption keys and decryption keys 6. The encryption algorithm to use 7. The decryption algorithm to use 6
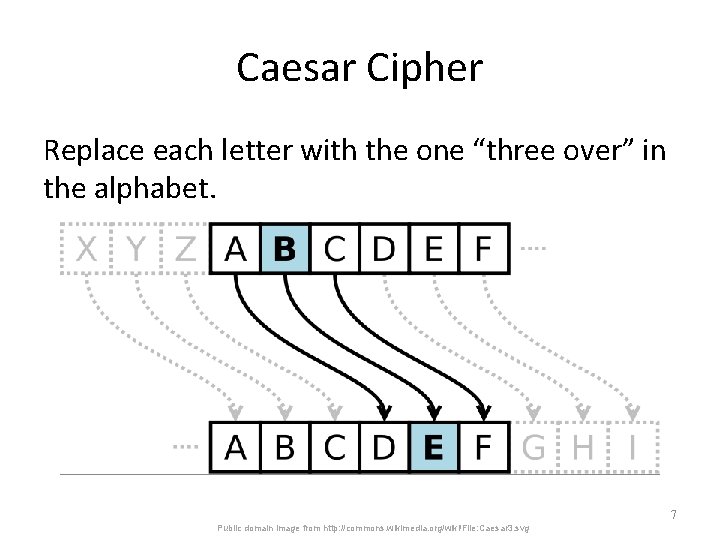
Caesar Cipher Replace each letter with the one “three over” in the alphabet. 7 Public domain image from http: //commons. wikimedia. org/wiki/File: Caesar 3. svg
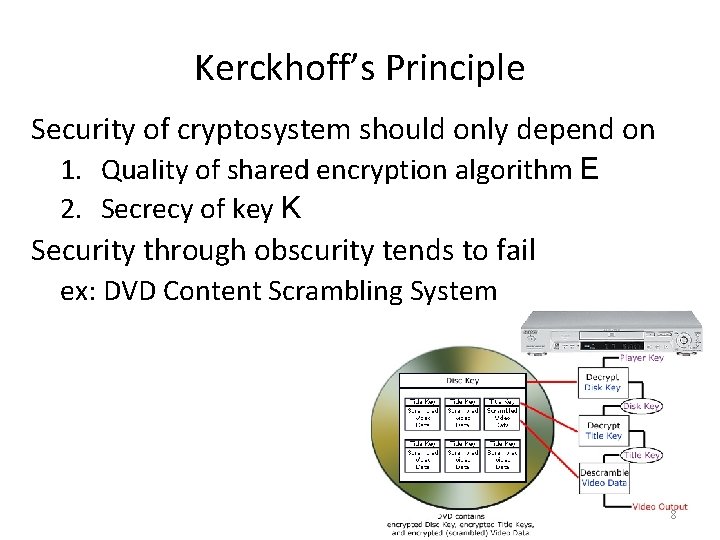
Kerckhoff’s Principle Security of cryptosystem should only depend on 1. Quality of shared encryption algorithm E 2. Secrecy of key K Security through obscurity tends to fail ex: DVD Content Scrambling System 8
Early Cryptography Egyptian hieroglyphics ~ 2000 B. C. E. – Cryptic tomb enscriptions for regality. Spartan skytale cipher ~ 500 B. C. E. – Wrapped thin sheet of papyrus around staff. – Messages written down length of staff. – Decrypted by wrapped around = diameter staff. Cæsar cipher ~ 50 B. C. E. – Simple alphabetic substitution cipher. al-Kindi ~ 850 C. E. – Cryptanalysis using letter frequencies. 9
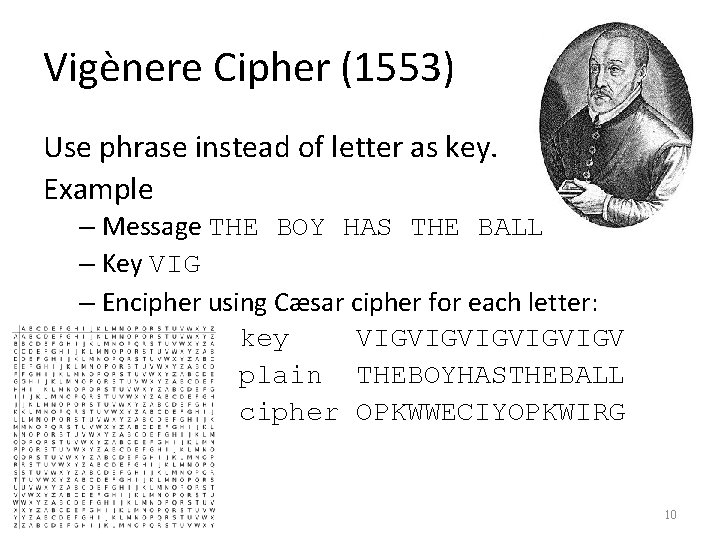
Vigènere Cipher (1553) Use phrase instead of letter as key. Example – Message THE BOY HAS THE BALL – Key VIG – Encipher using Cæsar cipher for each letter: key VIGVIGVIGV plain THEBOYHASTHEBALL cipher OPKWWECIYOPKWIRG 10
The World Wars Decryption of Zimmerman telegram 1917 – Leads US into World War I Japanese Purple Machine cracked 1937 – US breaks rotor machine for highest secrets. German Enigma machine cracked 1933 -45 – Initially broken by Polish mathematician – Variants broken at Bletchley Park in UK – Colossus, world’s 1 st electronic computer. 11
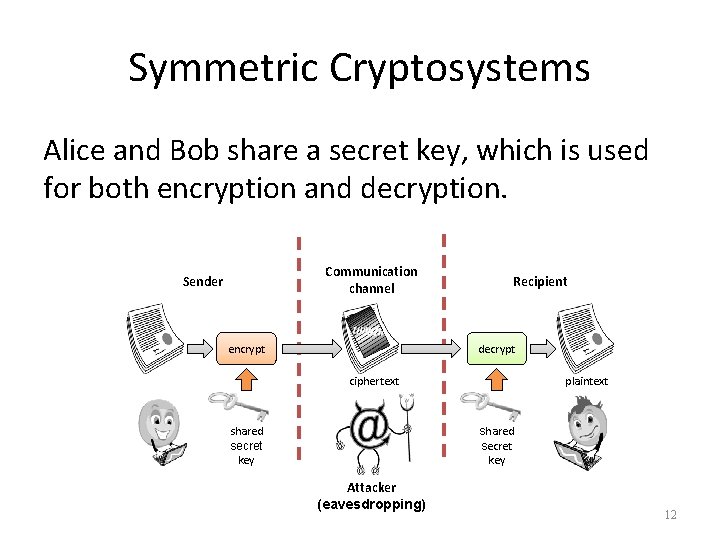
Symmetric Cryptosystems Alice and Bob share a secret key, which is used for both encryption and decryption. Communication channel Sender encrypt Recipient decrypt ciphertext plaintext shared secret key Attacker (eavesdropping) 12
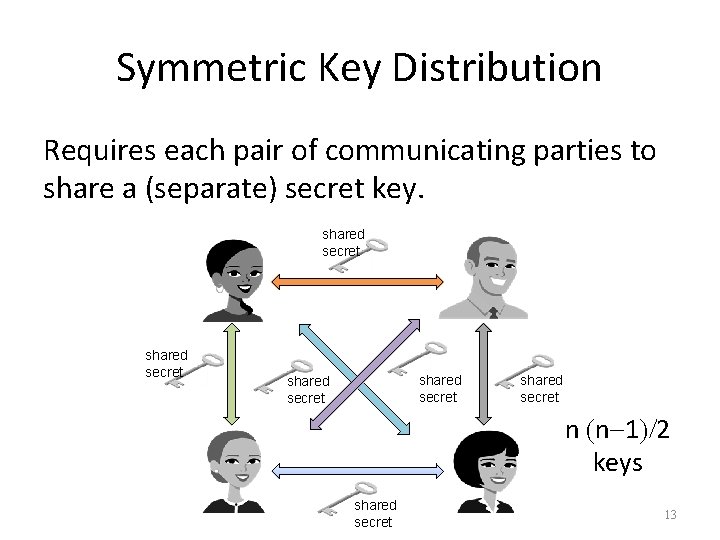
Symmetric Key Distribution Requires each pair of communicating parties to share a (separate) secret key. shared secret shared secret n (n-1)/2 keys shared secret 13
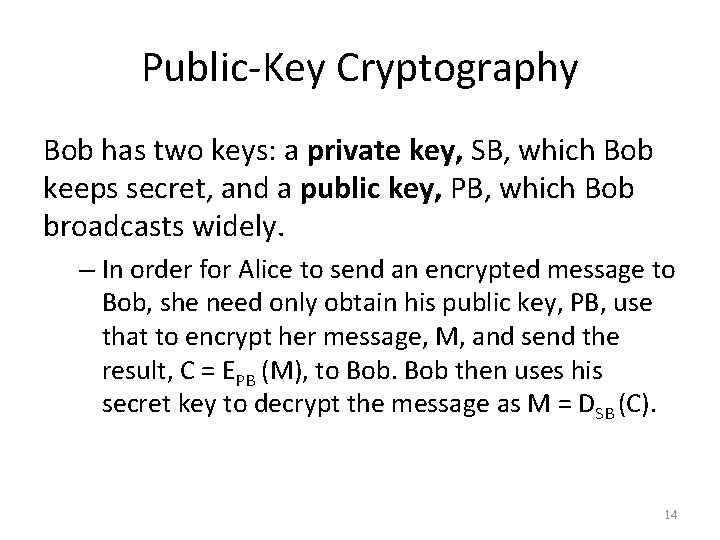
Public-Key Cryptography Bob has two keys: a private key, SB, which Bob keeps secret, and a public key, PB, which Bob broadcasts widely. – In order for Alice to send an encrypted message to Bob, she need only obtain his public key, PB, use that to encrypt her message, M, and send the result, C = EPB (M), to Bob then uses his secret key to decrypt the message as M = DSB (C). 14
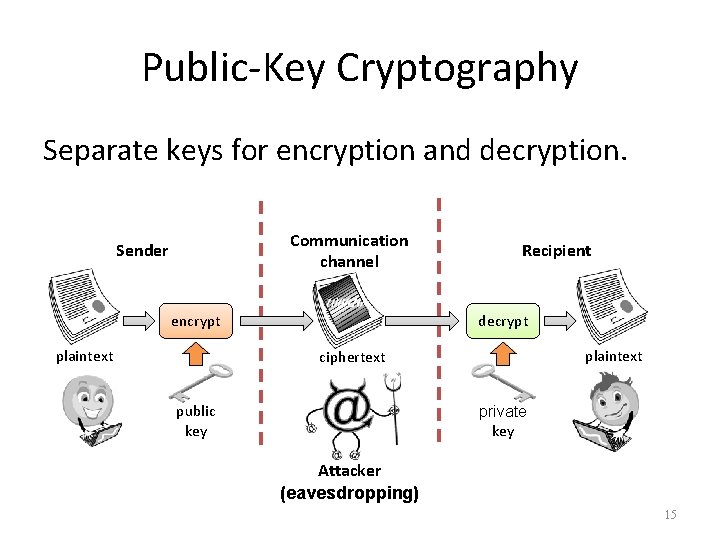
Public-Key Cryptography Separate keys for encryption and decryption. Communication channel Sender encrypt plaintext Recipient decrypt plaintext ciphertext plaintext public key private key Attacker (eavesdropping) 15
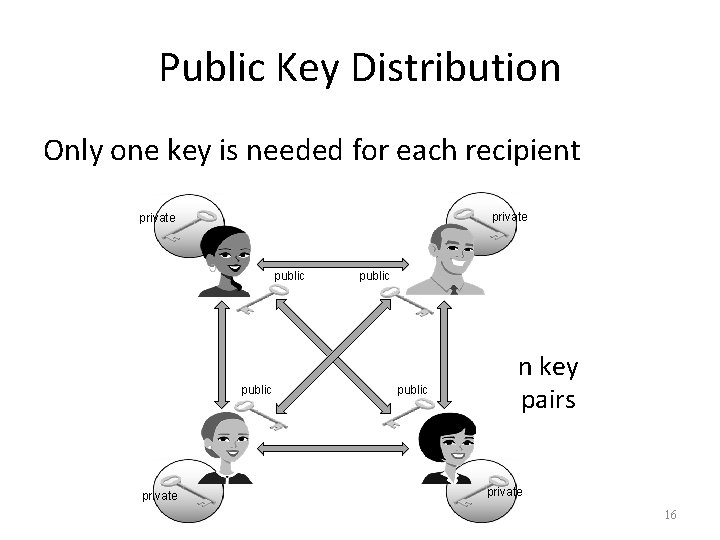
Public Key Distribution Only one key is needed for each recipient private public n key pairs private 16
Why Johnny Can’t Encrypt Usability evaluation of PGP 5. 0 – Pretty Good Privacy – Encrypts data – Plugins for e-mail clients Results of study of 12 users – 3 users sent e-mail without encryption (2 of 3 realized) – 7 users used public key instead of private key to encrypt – Only 2 users could decrypt without problems 17
Digital Signatures • Public-key encryption provides a method for doing digital signatures • To sign a message, M, Alice just encrypts it with her private key, SA, creating C = ESA(M). • Anyone can decrypt this message using Alice’s public key, as M’ = DPA(C), and compare that to the message M. 18
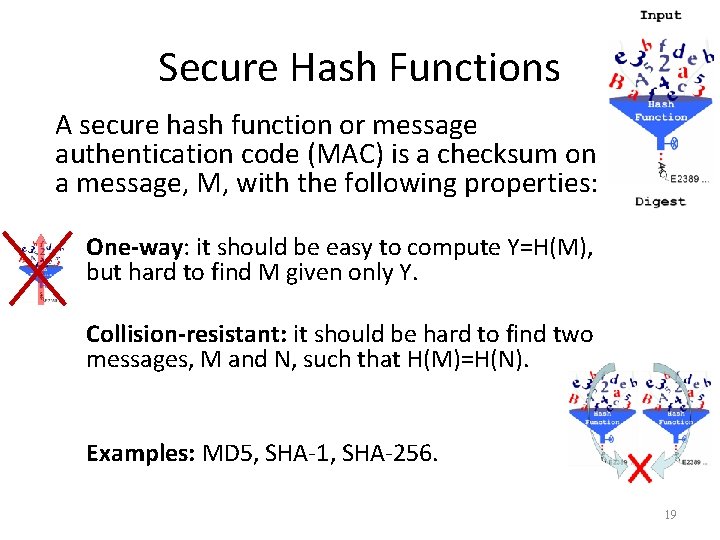
Secure Hash Functions A secure hash function or message authentication code (MAC) is a checksum on a message, M, with the following properties: One-way: it should be easy to compute Y=H(M), but hard to find M given only Y. Collision-resistant: it should be hard to find two messages, M and N, such that H(M)=H(N). Examples: MD 5, SHA-1, SHA-256. 19
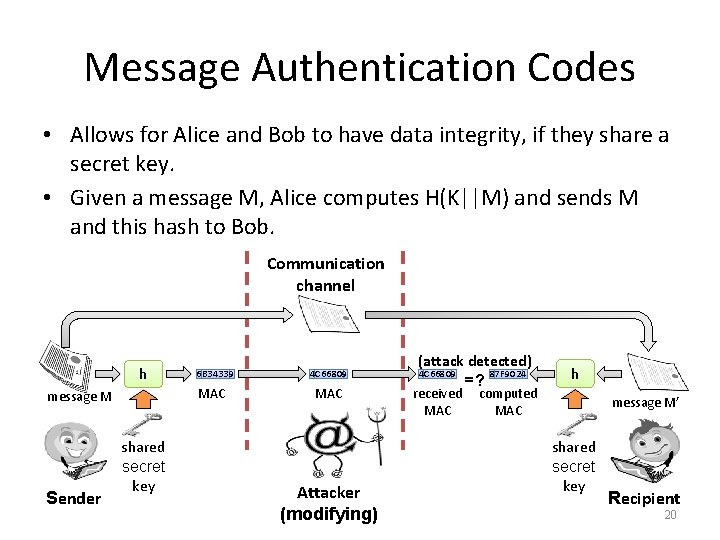
Message Authentication Codes • Allows for Alice and Bob to have data integrity, if they share a secret key. • Given a message M, Alice computes H(K||M) and sends M and this hash to Bob. Communication channel h message M Sender shared secret key 6 B 34339 4 C 66809 MAC Attacker (modifying) (attack detected) 4 C 66809 87 F 9024 =? received MAC h computed MAC message M’ shared secret key Recipient 20
References 1. Anderson, Security Engineering 2 nd Edition, Wiley, 2008. 2. Bishop, Computer Security: Art and Science, Addison-Wesley, 2002. 3. Goodrich and Tammasia, Introduction to Computer Security, Pearson, 2011. CIT 380: Securing Computer Systems Slide #21
- Slides: 21