CIT 380 Securing Computer Systems Covert Channels CIT

- Slides: 48
CIT 380: Securing Computer Systems Covert Channels CIT 380: Securing Computer Systems 1
Covert Channels 1. 2. 3. 4. 5. Covert Channels Using Other Protocols Hiding within a Protocol Local Covert Channels Defending against Covert Channels CIT 380: Securing Computer Systems 2
Covert Channels • Covert channel: a path of communication that was not designed for such communication. • IDS look for abnormal traffic – Use traffic that already exists: ping, DNS, HTTP. – Avoid creating abnormal traffic patterns. • Use encryption – Avoids keyword detection by IDS. – Prevents incident response from viewing data. CIT 380: Securing Computer Systems 3
Using Other Protocols • Use non-TCP/UDP protocols – Don’t show up on port scan. – Don’t show up on netstat on machine. • Use standard protocols for other purposes – DNS – HTTP • Reverse the direction of traffic – Internal machine initiates covert channel. CIT 380: Securing Computer Systems 4
Loki Tunnel shell using ICMP echo packets. – Uses ICMP data for commands/responses. – Uses Blowfish encryption algorithm. Loki 2 can also tunnel via DNS lookups. – Can swap between ICMP and DNS tunneling. Other ICMP shells, often use echo reply only – icmp_backdoor – sneaky-sneaky – lyceum CIT 380: Securing Computer Systems 5
Tunnel. Shell • Multi-protocol backdoor with evasion. • ICMP: standard ICMP shell. • TCP: uses only ACK packets to communicate, bypassing packet filters, and showing no port used on local machine. • UDP: UDP shell without binding port. • IP: IP without using a higher level protocol. • Fragment: uses fragmented IP packets. CIT 380: Securing Computer Systems 6
WWW Shells Simple shells – Web program that acts as a shell. – ex: CGI Telnet, PHP Shell Reverse WWW Shell – Web client that checks server for commands. – Use predefined or random time intervals. – Looks like a browser surfing the web. HTTP request (shell prompt) GET /cgibin/order? M 5 m. Aej. Tg. Zdg. YOdg. IO 0 Bq. Ff. VYTgj. FLdgx. Edb 1 He 7 krj HTTP/1. 0 HTTP response (ls command) g 5 m. Alfbknz CIT 380: Securing Computer Systems 7
HTTP Tunnels Tunnel any protocol over HTTP – Bypass firewalls. – Most software supports proxies. – Can use SSL for encryption. – Malware embeds self in IE as a BHO, then uses HTTP to phone home with IE’s permissions. Go. To. My. PC – Commercial HTTP tunnel. – Remote desktop access protocol like VNC. CIT 380: Securing Computer Systems 8
TCP/IP Headers Requirements – Headers must not be used by end systems. – Headers must not be modified by routers. IP Headers – IP Identification – IP options (may be modified by routers) TCP Headers – Sequence numbers – Bits reserved for future use. – TCP options (may be modified by routers) CIT 380: Securing Computer Systems 9
Covert_TCP IP covert channel – Insert one byte into IPID field of each packet. TCP sequence number channel – Inserts one byte into sequence numbers. – Sends SYN with encoded ISN. – Server responds with RST to acknowledge. – Each byte transferred requires two packets. CIT 380: Securing Computer Systems 10
Covert_TCP ACK number bounce channel – Inserts one byte into the ACK number. – Uses 3 hosts: client, server, bounce server Operation 1. Client: SYN w/ encoded ISN, spoofing IP of server. 2. Bounce server: SYN/ACK or RST w/ encoded ISN+1 to spoofed source IP (server) 3. Server: receives bounced packet, recovers byte from ISN. CIT 380: Securing Computer Systems 11
Nushu Passive covert channel. – Inserts data into TCP packets from other apps. – Alters sequence numbers to contain data. – Runs as a Linux kernel module. Receiver sniffs data off network. – Receiver IP address not in any packets. – Receiver must be at gateway where it can sniff all of the packets sent by Nushu. CIT 380: Securing Computer Systems 12
Steganography • A covert channel via data files. • Share data files openly – Use file sharing sites like Flickr. – Use sites with photographs like Ebay. – Hack another site and replace data files. • Both sides must know – Steganographic technique. – Locations used to dump files. CIT 380: Securing Computer Systems 13
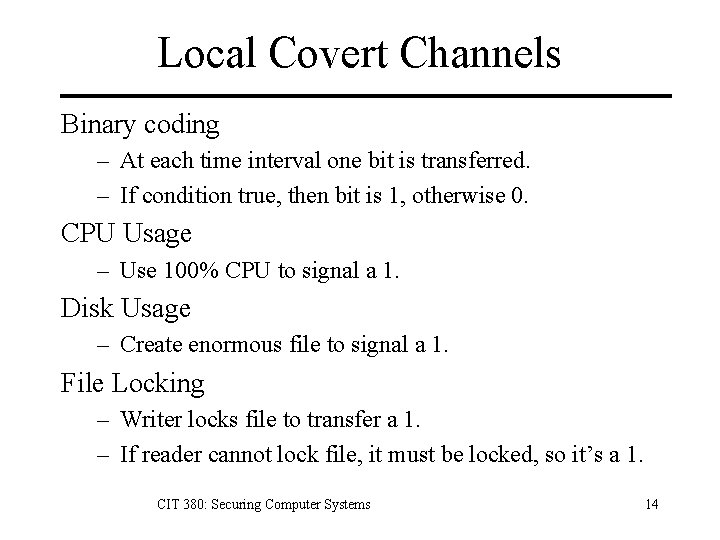
Local Covert Channels Binary coding – At each time interval one bit is transferred. – If condition true, then bit is 1, otherwise 0. CPU Usage – Use 100% CPU to signal a 1. Disk Usage – Create enormous file to signal a 1. File Locking – Writer locks file to transfer a 1. – If reader cannot lock file, it must be locked, so it’s a 1. CIT 380: Securing Computer Systems 14
Covering your Covering Tracks • Covert backdoors hide data from network. • But process listings will show backdoors. • How can you hide the backdoors? – Alter process / command names. – Use rootkit to hide processes. – Embed backdoor in kernel mode rootkit. CIT 380: Securing Computer Systems 15
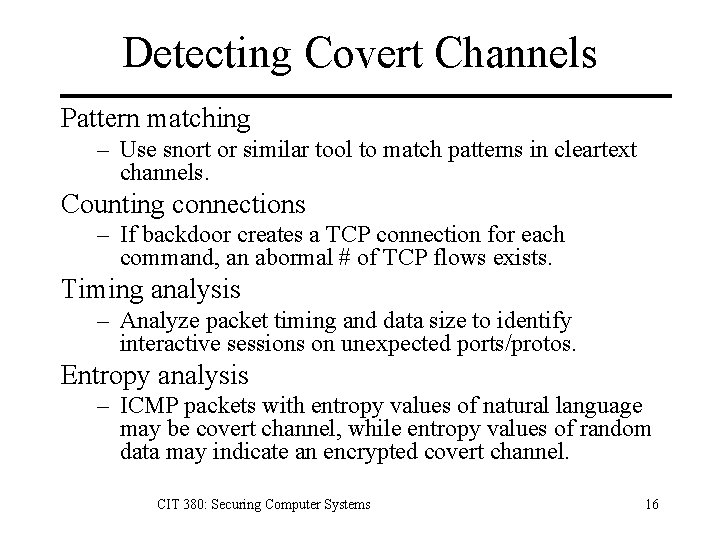
Detecting Covert Channels Pattern matching – Use snort or similar tool to match patterns in cleartext channels. Counting connections – If backdoor creates a TCP connection for each command, an abormal # of TCP flows exists. Timing analysis – Analyze packet timing and data size to identify interactive sessions on unexpected ports/protos. Entropy analysis – ICMP packets with entropy values of natural language may be covert channel, while entropy values of random data may indicate an encrypted covert channel. CIT 380: Securing Computer Systems 16
Stopping Covert Channels Host-based security. – Stop attackers from gaining access to install. Use stateful firewall – Blocks ACK tunneling. Use firewall to limit outgoing data – Stop ICMP echo replies. – Should your db server be browing the web? CIT 380: Securing Computer Systems 17
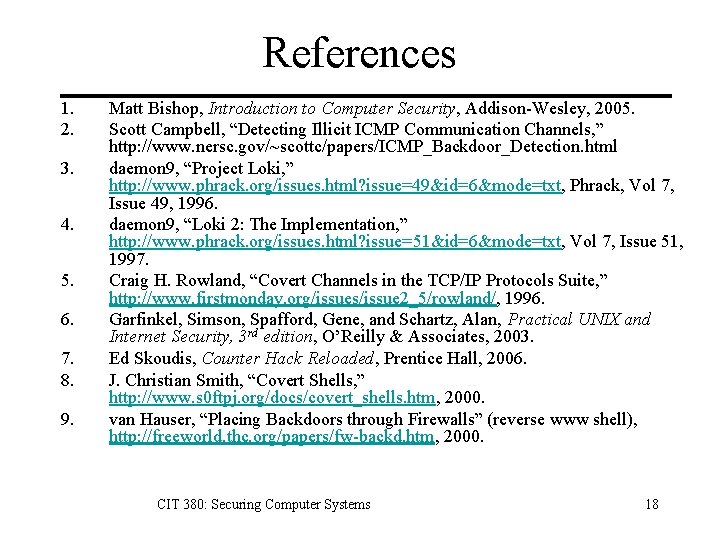
References 1. 2. 3. 4. 5. 6. 7. 8. 9. Matt Bishop, Introduction to Computer Security, Addison-Wesley, 2005. Scott Campbell, “Detecting Illicit ICMP Communication Channels, ” http: //www. nersc. gov/~scottc/papers/ICMP_Backdoor_Detection. html daemon 9, “Project Loki, ” http: //www. phrack. org/issues. html? issue=49&id=6&mode=txt, Phrack, Vol 7, Issue 49, 1996. daemon 9, “Loki 2: The Implementation, ” http: //www. phrack. org/issues. html? issue=51&id=6&mode=txt, Vol 7, Issue 51, 1997. Craig H. Rowland, “Covert Channels in the TCP/IP Protocols Suite, ” http: //www. firstmonday. org/issues/issue 2_5/rowland/, 1996. Garfinkel, Simson, Spafford, Gene, and Schartz, Alan, Practical UNIX and Internet Security, 3 rd edition, O’Reilly & Associates, 2003. Ed Skoudis, Counter Hack Reloaded, Prentice Hall, 2006. J. Christian Smith, “Covert Shells, ” http: //www. s 0 ftpj. org/docs/covert_shells. htm, 2000. van Hauser, “Placing Backdoors through Firewalls” (reverse www shell), http: //freeworld. thc. org/papers/fw-backd. htm, 2000. CIT 380: Securing Computer Systems 18
CIT 380: Securing Computer Systems Software Security CIT 380: Securing Computer Systems 19
Topics 1. 2. 3. 4. 5. 6. Why Software? Vulnerability Databases Buffer Overflows Integer Overflows Attack Techniques Metasploit CIT 380: Securing Computer Systems 20
The Problem is Software “Malicious hackers don’t create security holes; they simply exploit them. Security holes and vulnerabilities – the real root cause of the problem – are the result of bad software design and implementation. ” John Viega & Gary Mc. Graw CIT 380: Securing Computer Systems 21
Why is Software Security poor? 1. Security is seen as something that gets in the way of software functionality. 2. Security is difficult to assess and quantify. 3. Security is often not a primary skill or interest of software developers. 4. Time spent on security is time not spent on adding new and interesting functionality. CIT 380: Securing Computer Systems 22
The Trinity of Trouble • Complexity – Continually increasing. – Windows 3. 1 (3 mloc) to Windows XP (40 mloc) • Extensibility – Plugins. – Mobile code. • Connectivity – Network access. – Wireless networking. CIT 380: Securing Computer Systems 23
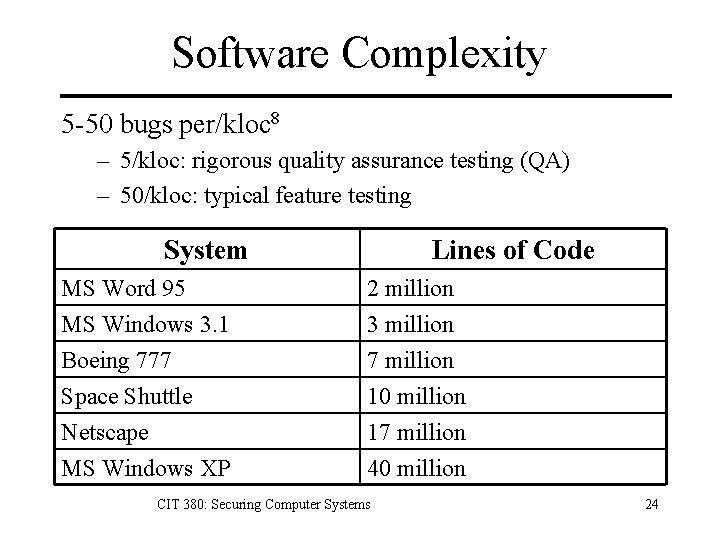
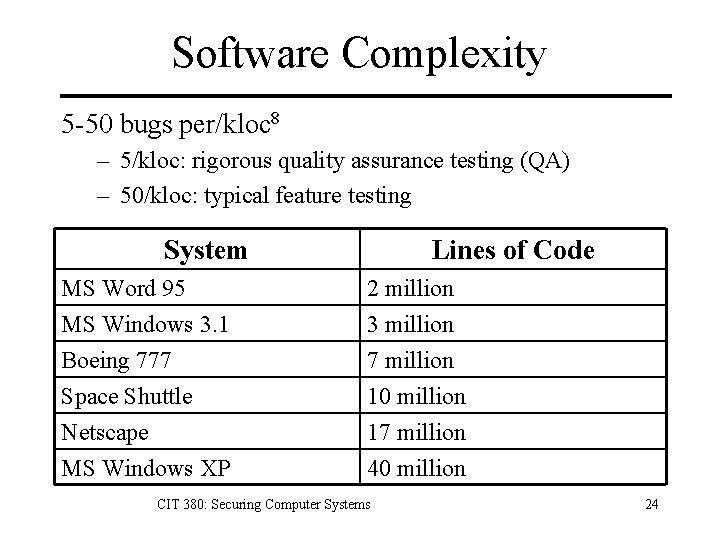
Software Complexity 5 -50 bugs per/kloc 8 – 5/kloc: rigorous quality assurance testing (QA) – 50/kloc: typical feature testing System Lines of Code MS Word 95 MS Windows 3. 1 Boeing 777 2 million 3 million 7 million Space Shuttle Netscape MS Windows XP 10 million 17 million 40 million CIT 380: Securing Computer Systems 24
Vulnerabilities • Vulnerability: A defect in software that allows security policy to be violated. – Confidentiality – Integrity – Availability • Ex: Allowing users to create self-replicating objects on a game server. • Exploit: A program that exercises a vulnerability. CIT 380: Securing Computer Systems 25
Vulnerability Databases • Collect vulnerability reports. – Vendors maintain databases with patches for their own software. – Security firms maintain databases of vulnerabilities that they’ve discovered. • Well known vulnerability databases – CERT – CVE – NVD – OSVDB CIT 380: Securing Computer Systems 26
Why Vulnerability Databases? • Know about vulnerabilities to software that you have deployed so you can mitigate them. • Learn about vulnerability trends. If a JPG library bug is discovered, does the same type of bug exist in GIF or PNG libraries? • Learn about security problems to prevent when you’re programming. CIT 380: Securing Computer Systems 27
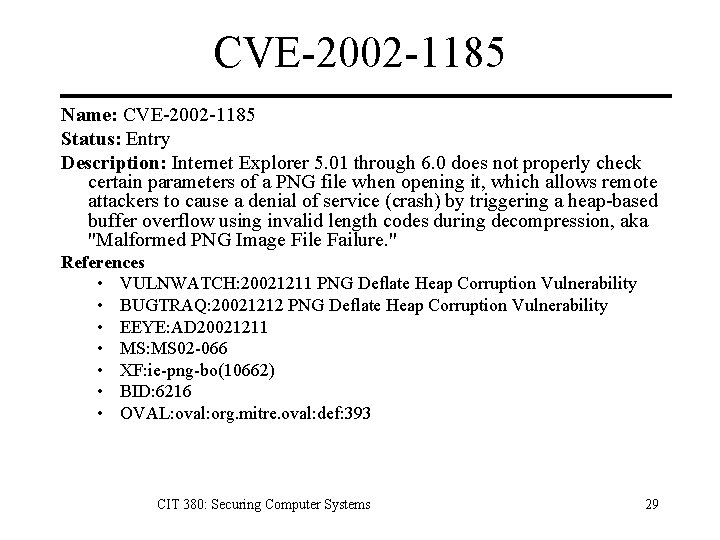
CVE: Common Vulnerabilities and Exposures • Problem: Different researchers and vendors call vulnerabilities by different names. • Solution: CVE, a dictionary that provides – A common public name for each vulnerability. – A common standardized description. – Allows different tools / databases to interoperate. CIT 380: Securing Computer Systems 28
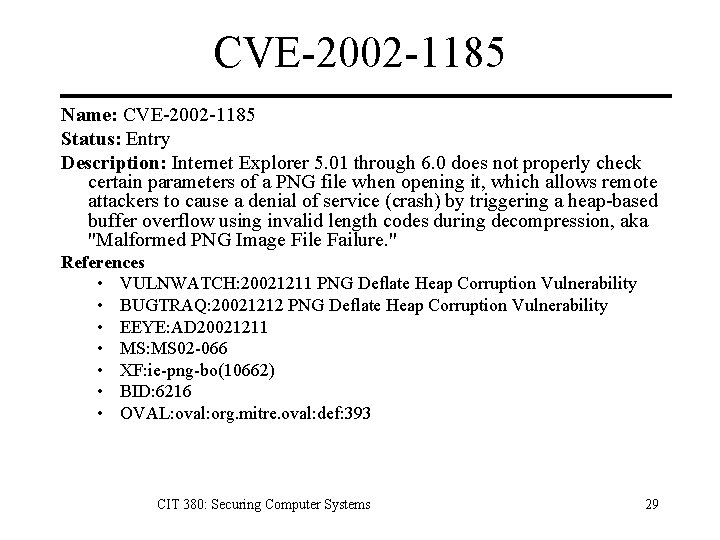
CVE-2002 -1185 Name: CVE-2002 -1185 Status: Entry Description: Internet Explorer 5. 01 through 6. 0 does not properly check certain parameters of a PNG file when opening it, which allows remote attackers to cause a denial of service (crash) by triggering a heap-based buffer overflow using invalid length codes during decompression, aka "Malformed PNG Image File Failure. " References • VULNWATCH: 20021211 PNG Deflate Heap Corruption Vulnerability • BUGTRAQ: 20021212 PNG Deflate Heap Corruption Vulnerability • EEYE: AD 20021211 • MS: MS 02 -066 • XF: ie-png-bo(10662) • BID: 6216 • OVAL: oval: org. mitre. oval: def: 393 CIT 380: Securing Computer Systems 29
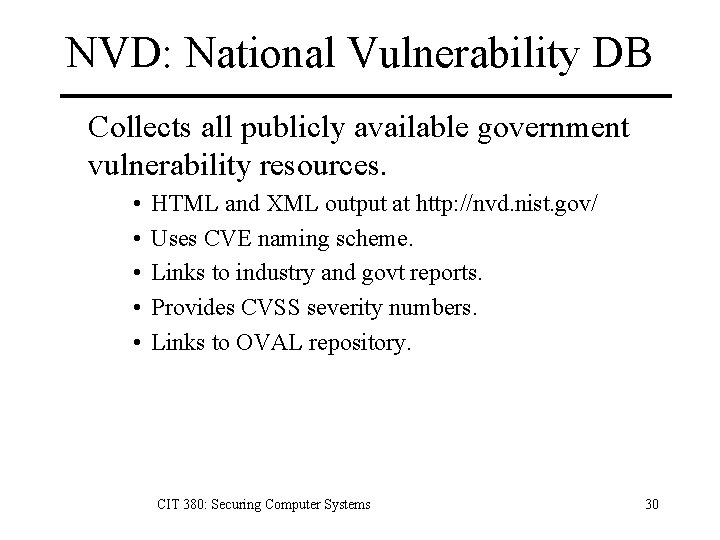
NVD: National Vulnerability DB Collects all publicly available government vulnerability resources. • • • HTML and XML output at http: //nvd. nist. gov/ Uses CVE naming scheme. Links to industry and govt reports. Provides CVSS severity numbers. Links to OVAL repository. CIT 380: Securing Computer Systems 30
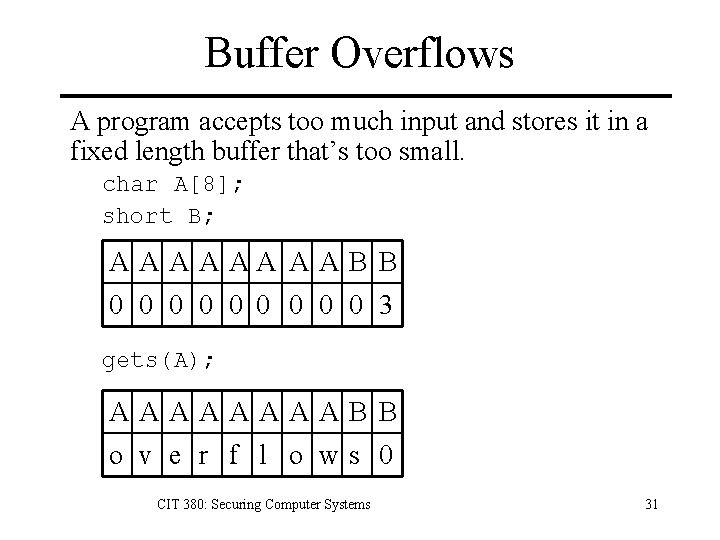
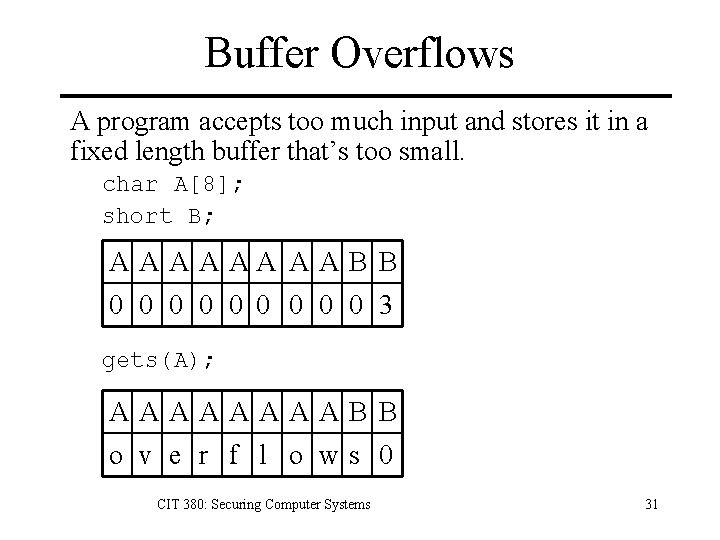
Buffer Overflows A program accepts too much input and stores it in a fixed length buffer that’s too small. char A[8]; short B; A A AA A A B B 0 0 0 0 0 3 gets(A); AAAAB B o v e r f l o ws 0 CIT 380: Securing Computer Systems 31
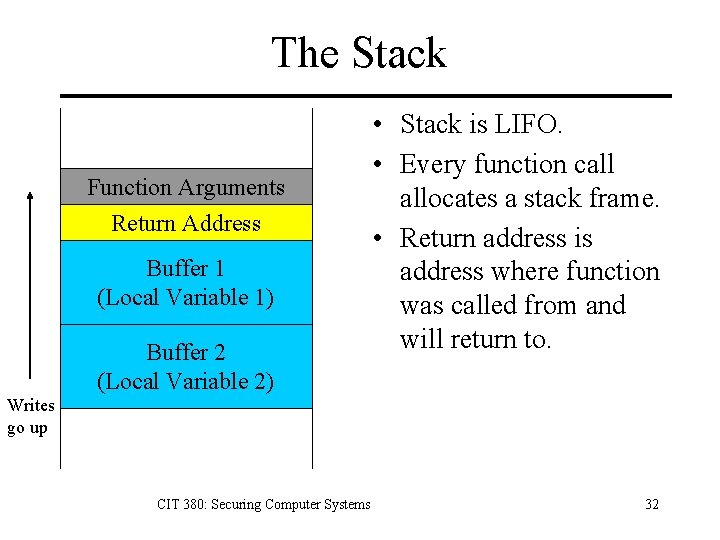
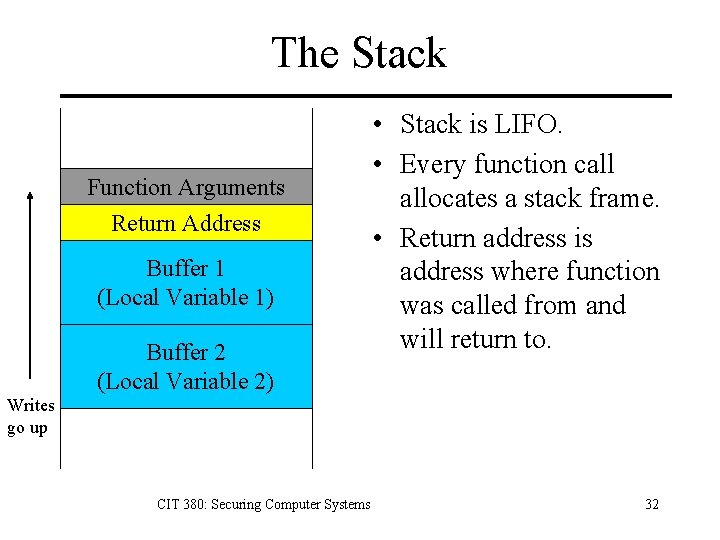
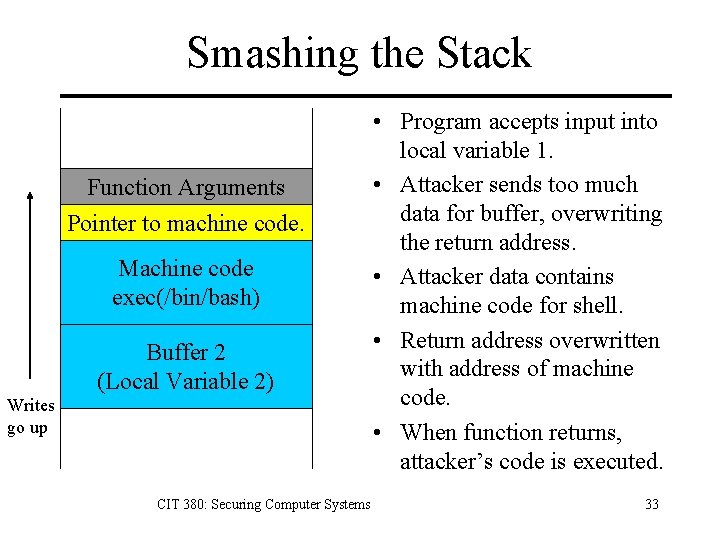
The Stack Function Arguments Return Address Buffer 1 (Local Variable 1) Buffer 2 (Local Variable 2) • Stack is LIFO. • Every function call allocates a stack frame. • Return address is address where function was called from and will return to. Writes go up CIT 380: Securing Computer Systems 32
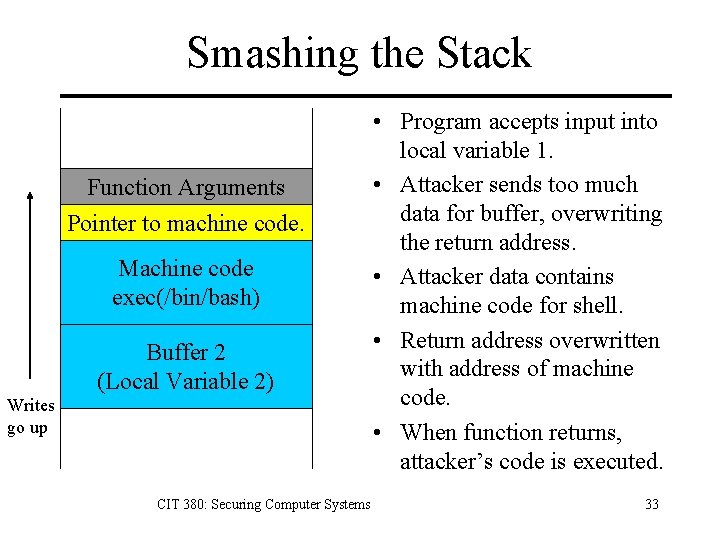
Smashing the Stack Function Arguments Pointer to machine code. Machine code exec(/bin/bash) Buffer 2 (Local Variable 2) Writes go up CIT 380: Securing Computer Systems • Program accepts input into local variable 1. • Attacker sends too much data for buffer, overwriting the return address. • Attacker data contains machine code for shell. • Return address overwritten with address of machine code. • When function returns, attacker’s code is executed. 33
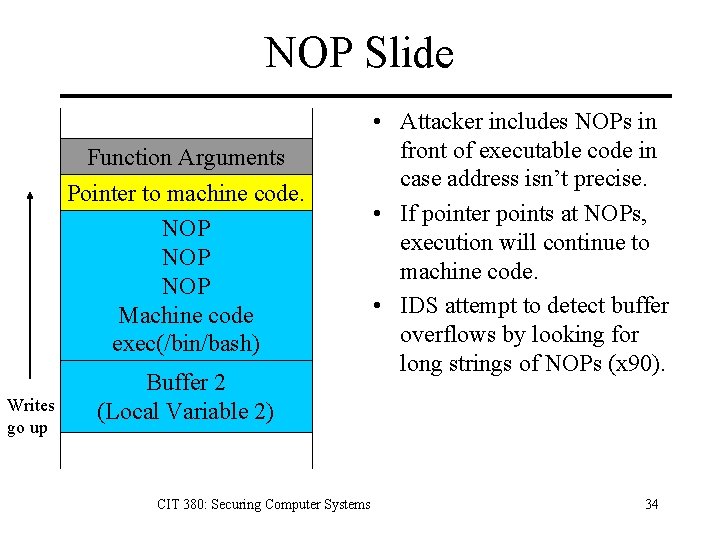
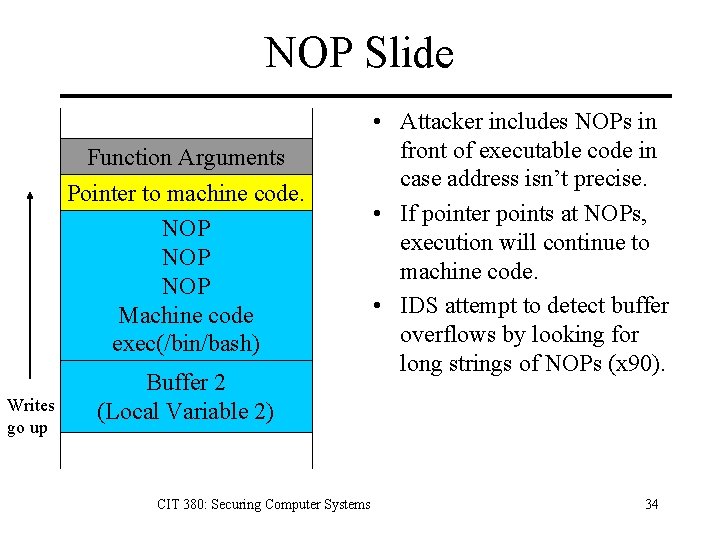
NOP Slide Function Arguments Pointer to machine code. NOP NOP Machine code exec(/bin/bash) Writes go up Buffer 2 (Local Variable 2) CIT 380: Securing Computer Systems • Attacker includes NOPs in front of executable code in case address isn’t precise. • If pointer points at NOPs, execution will continue to machine code. • IDS attempt to detect buffer overflows by looking for long strings of NOPs (x 90). 34
Arc Injection (return-into-libc) Arc injection transfers control to code that already exists in memory. Adds a new arc into program’s CFG. Change return address to existing function. libc has functions to start a shell. Allows exploit even if stack non-executable. Sophisticated arc injection attacks create multiple stack frames to run multiple functions that are in memory. CIT 380: Securing Computer Systems 35
Integer Overflow An integer overflow is when integer operations produce a value that exceeds the computer’s maximum integer value, causing the value to “wrap around” to a negative value or zero. CIT 380: Securing Computer Systems 36
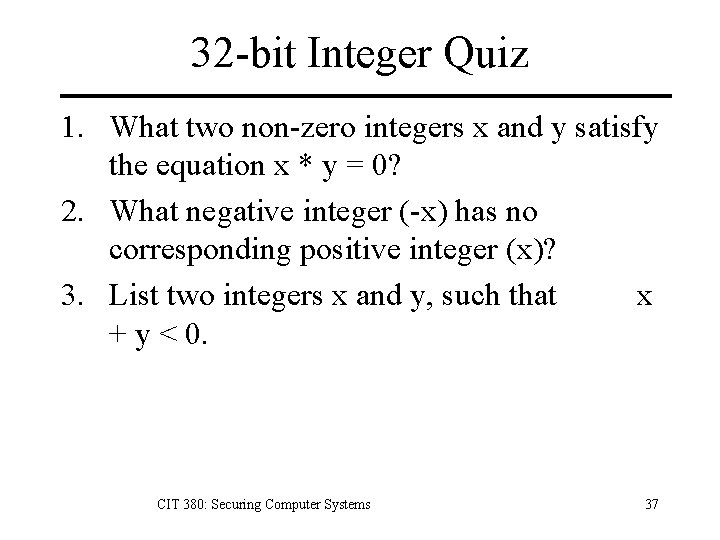
32 -bit Integer Quiz 1. What two non-zero integers x and y satisfy the equation x * y = 0? 2. What negative integer (-x) has no corresponding positive integer (x)? 3. List two integers x and y, such that x + y < 0. CIT 380: Securing Computer Systems 37
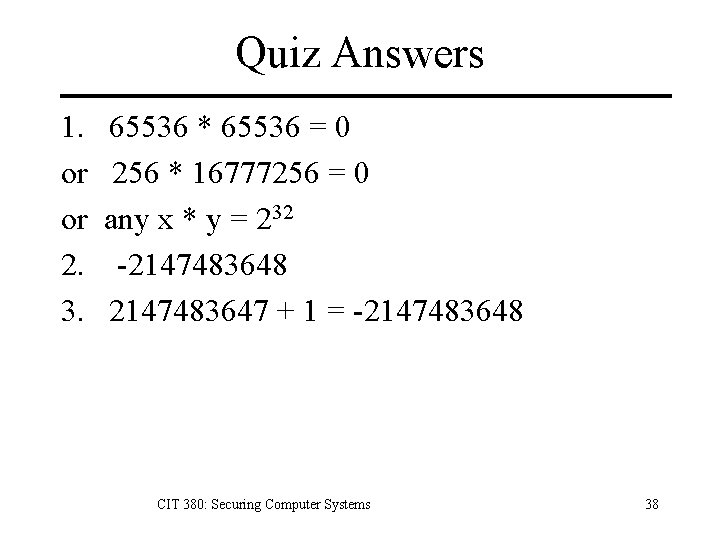
Quiz Answers 1. or or 2. 3. 65536 * 65536 = 0 256 * 16777256 = 0 any x * y = 232 -2147483648 2147483647 + 1 = -2147483648 CIT 380: Securing Computer Systems 38
Are Integer Overflows Important? Broward County November 2004 election – Amendment 4 vote was reported as tied. – Software from ES&S Systems reported a large negative number of votes. – Discovery revealed that Amendment 4 had passed by a margin of over 60, 000 votes. CIT 380: Securing Computer Systems 39
Fuzz Testing Black-box input based testing technique. – Uses random data. – Easily automated. – If application crashes or hangs, it fails. Results of 1995 study 9. – 15 -43% of utilities from commerical UNIX systems failed. – 9% of Linux utilities failed. – 6% of GNU utilities failed. – 50% of X-Windows utilities failed. CIT 380: Securing Computer Systems 40
Attack Trees Decompose threats into individual, testable conditions using attack trees. Attack Trees – Hierarchical decomposition of a threat. – Root of tree is adversary’s goal in the attack. – Each level below root decomposes the attack into finer approaches. – Child nodes are ORed together by default. – Special notes may indicate to AND them. CIT 380: Securing Computer Systems 41
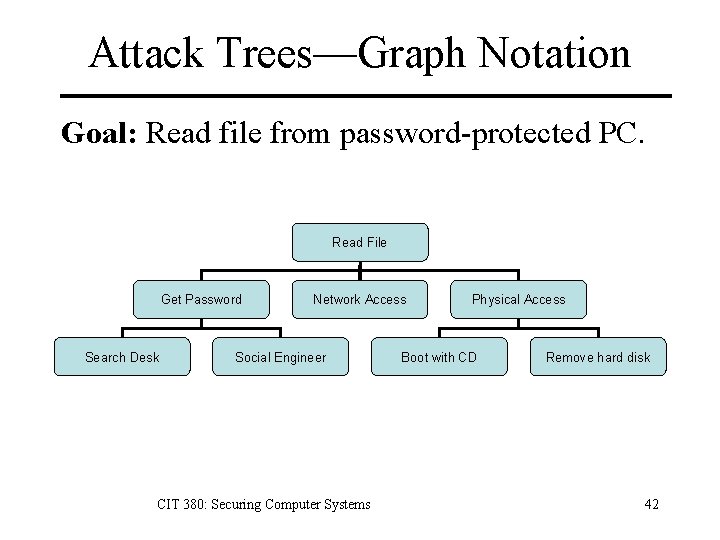
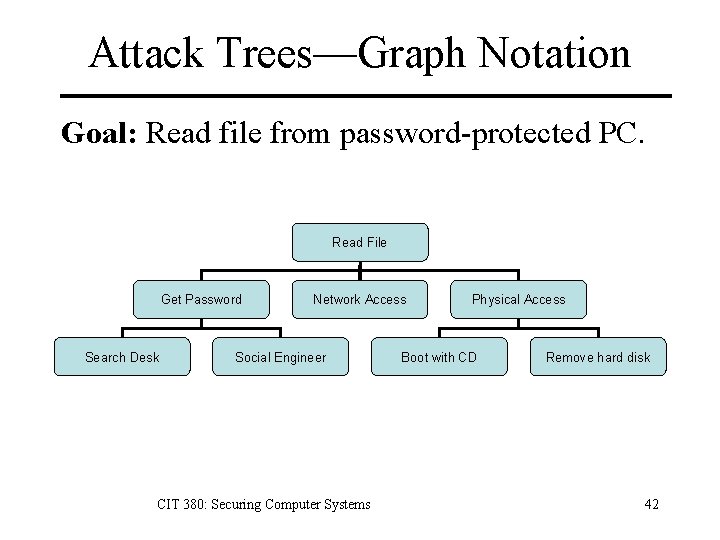
Attack Trees—Graph Notation Goal: Read file from password-protected PC. Read File Get Password Search Desk Network Access Social Engineer CIT 380: Securing Computer Systems Physical Access Boot with CD Remove hard disk 42
Attack Trees—Text Notation Goal: Read message sent from one PC to another. 1. Convince sender to reveal message. 1. 1 Blackmail. 1. 2 Bribe. 2. Read message when entered on sender’s PC. 1. 1 Visually monitor PC screen. 1. 2 Monitor EM radiation from screen. 3. Read message when stored on receiver’s PC. 1. 1 Get physical access to hard drive. 1. 2 Infect user with spyware. 4. Read message in transit. 1. 1 Sniff network. 1. 2 Usurp control of mail server. CIT 380: Securing Computer Systems 43
Metasploit Modular exploit system – Exploit collection: over 100 exploits. – Payloads: machine code to run – Command line and web interfaces. Payloads – Bind shell: opens shell backdoor on port. – Reverse shell: send shell back to attacker. – Windows VNC: remote desktop access. – Create user: add new administrative user. CIT 380: Securing Computer Systems 44
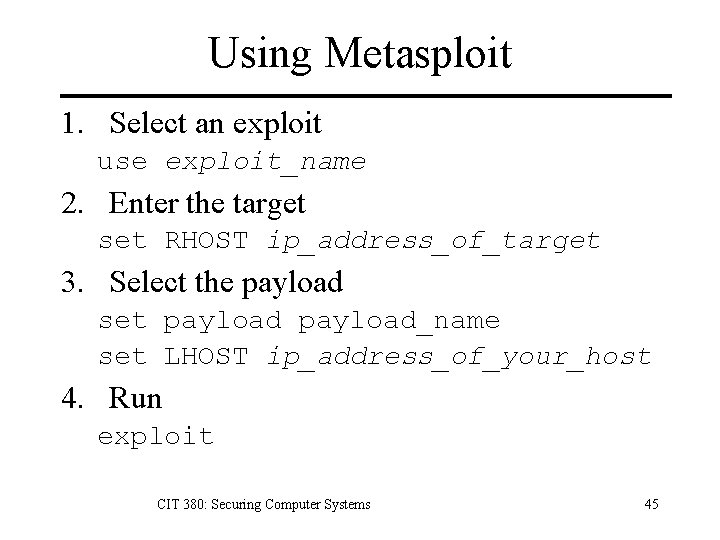
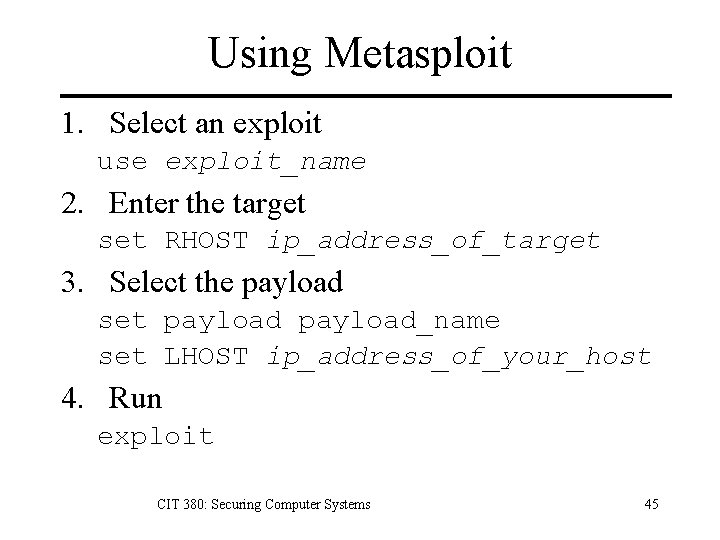
Using Metasploit 1. Select an exploit use exploit_name 2. Enter the target set RHOST ip_address_of_target 3. Select the payload set payload_name set LHOST ip_address_of_your_host 4. Run exploit CIT 380: Securing Computer Systems 45
Advantages of Metasploit • Ease of use – One interface to many exploits. • Flexibility – Can choose whatever payload you need. • Faster development time – Payloads already written. • Reliability – Framework and payloads are well tested. CIT 380: Securing Computer Systems 46

Uses of Metasploit • Vulnerability verification – Scanners report possible vulnerabilities. – Metasploit will give you remote access. • IDS/IPS testing – Test IDS/IPS with real exploit code. • Penetration testing – Easy to develop custom exploits for pen testing. • Convincing management – Remote access is more convincing than a report. CIT 380: Securing Computer Systems 47
References 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. Matt Bishop, Introduction to Computer Security, Addison-Wesley, 2005. Simson Garfinkel, Gene Spafford, and Alan Schartz, Practical UNIX and Internet Security, 3 rd edition, O’Reilly & Associates, 2003. Mark Graff and Kenneth van Wyk, Secure Coding: Principles & Practices, O’Reilly, 2003. Greg Hoglund and Gary Mc. Graw, Exploiting Software: How to Break Code, Addison-Wesley, 2004. Michael Howard, David Le. Blanc, and John Viega, 19 Deadly Sins of Software Security, Mc. Graw-Hill Osborne, 2005. Michael Howard, David Le. Blanc, Writing Secure Code, 2 nd edition, Microsoft Press, 2003. Michael Howard and Steve Lipner, The Security Development Lifecycle, Microsoft Press, 2006. Gary Mc. Graw, Software Security, Addison-Wesley, 2006. John Viega and Gary Mc. Graw, Building Secure Software, Addison-Wesley, 2002. David Wheeler, Secure Programming for UNIX and Linux HOWTO, http: //www. dwheeler. com/secure-programs/Secure-Programs. HOWTO/index. html, 2003. CIT 380: Securing Computer Systems 48