CIT 380 Securing Computer Systems Authentication CIT 380

- Slides: 31

CIT 380: Securing Computer Systems Authentication CIT 380: Securing Computer Systems 1
Authentication 1. 2. 3. 4. 5. 6. Identity Groups and Roles Network Identities Authentication Biometrics UNIX Authentication CIT 380: Securing Computer Systems 2
What is Identity? Computer’s representation of an entity – Entities can be subjects or objects. Authentication binds a principal to an identity. Example: – username expresses your identity. – password binds the person typing to that particular identity (username). CIT 380: Securing Computer Systems 3
Purpose of Identity Access Control – Most systems base access rights on identity of principal executing the process. Accountability – Logging and auditing functions. – Need to track identity across account/role changes (e. g. , sudo). CIT 380: Securing Computer Systems 4
Groups and Roles An “entity” may be a set of entities referred to by a single identifier. Principals often need to share access to files, and thus are taken as groups. – static: alias for a group of principles. – dynamic: principal changes from one group to another as different privileges are needed. role: a group that ties membership to function CIT 380: Securing Computer Systems 5
Network Identity Ethernet (MAC) Address – 48 -bit data link level identifier – example: 00: 0 B: DB: 78: 39: 8 A IP Address – 32 -bit network level identifier – ex: 10. 17. 0. 101 IPv 6 Address – 128 -bit network level identifier – ex: fe 80: : 2 a 0: c 9 ff: fe 97: 153 d/64 Hostname (DNS name) – string application level identifier – ex: www. nku. edu CIT 380: Securing Computer Systems 6
What is Authentication? Binding of an identity to a subject Based on: 1. 2. 3. 4. What the entity knows (e. g. , passwords) What the entity has (e. g. , access card) What the entity is (e. g. , fingerprints) Where the entity is (e. g. , local terminal) Two-factor authentication CIT 380: Securing Computer Systems 7
What You Know • Passwords • Pass Phrases • PINs CIT 380: Securing Computer Systems 8
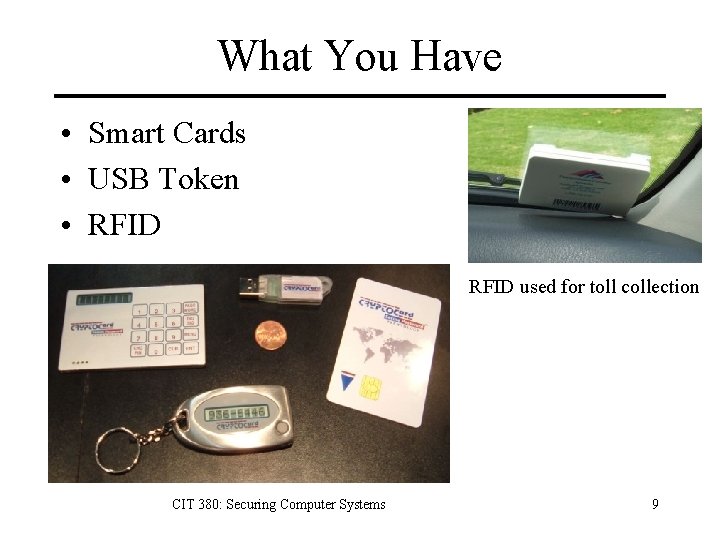
What You Have • Smart Cards • USB Token • RFID used for toll collection CIT 380: Securing Computer Systems 9
USB Tokens and Smart Cards • Small device with storage and processor. – USB tokens tend to focus on storage. – Smart cards on processor + small storage. – Differences are growing smaller. • Methods of use – By Hand (read card and type one-time password) – USB – Wireless CIT 380: Securing Computer Systems 10
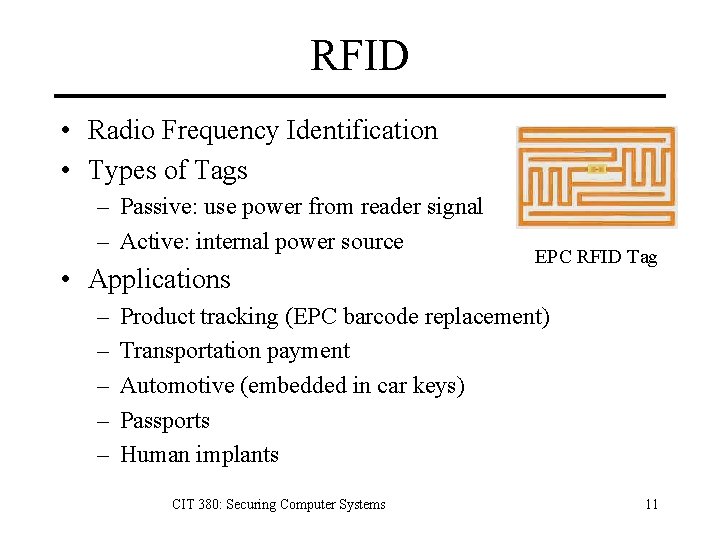
RFID • Radio Frequency Identification • Types of Tags – Passive: use power from reader signal – Active: internal power source • Applications – – – EPC RFID Tag Product tracking (EPC barcode replacement) Transportation payment Automotive (embedded in car keys) Passports Human implants CIT 380: Securing Computer Systems 11
What You Are: Biometrics Identification by human characteristics: 1. Physiological 2. Behavioral A biometric characteristic should be: 1. 2. 3. 4. universal: everyone should have it unique: no two people should share it permanent: it should not change with time quantifiable: it must be practically measurable CIT 380: Securing Computer Systems 12
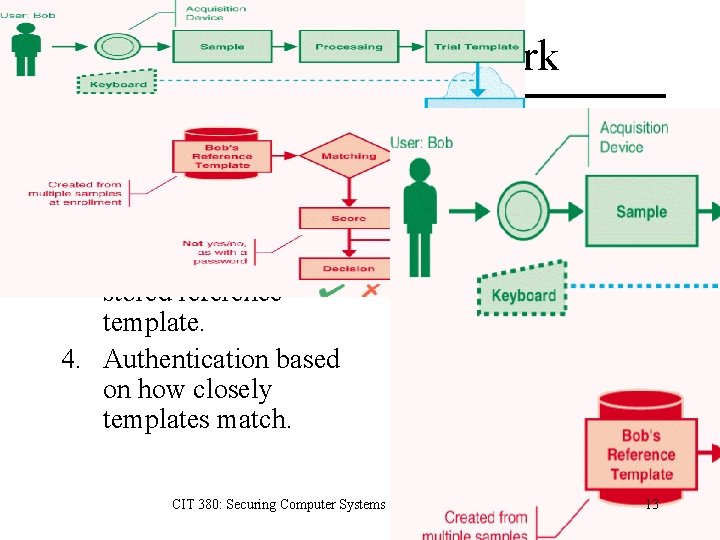
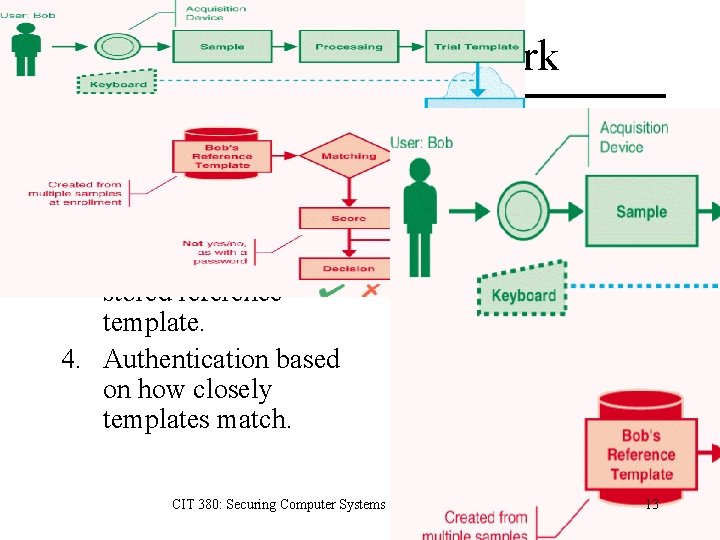
How Biometrics Work 1. User submits sample. 2. Software turns sample into digital template. 3. Software compares template against stored reference template. 4. Authentication based on how closely templates match. CIT 380: Securing Computer Systems 13
Biometric Measurement Possible Outcomes: 1. 2. 3. 4. Correct person accepted Imposter rejected Correct person rejected (False Rejection) Imposter accepted (False Acceptance) CIT 380: Securing Computer Systems 14
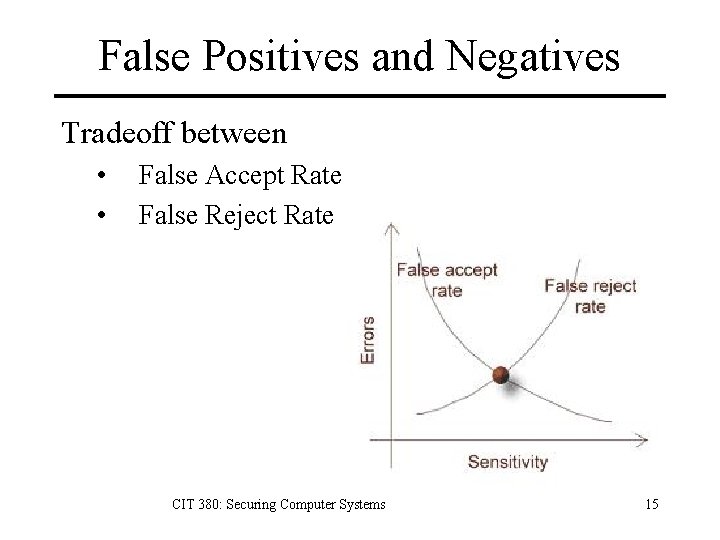
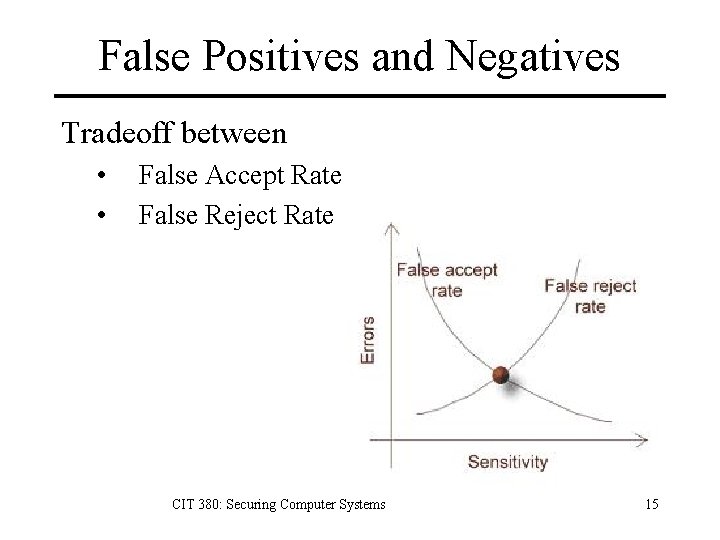
False Positives and Negatives Tradeoff between • • False Accept Rate False Reject Rate CIT 380: Securing Computer Systems 15
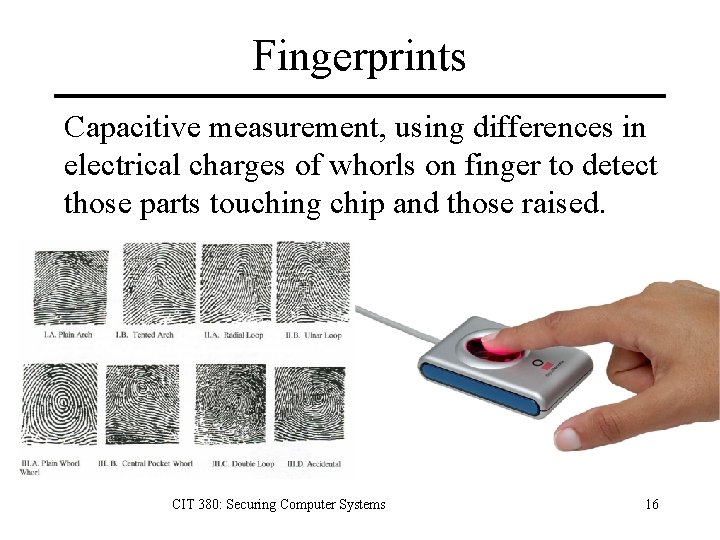
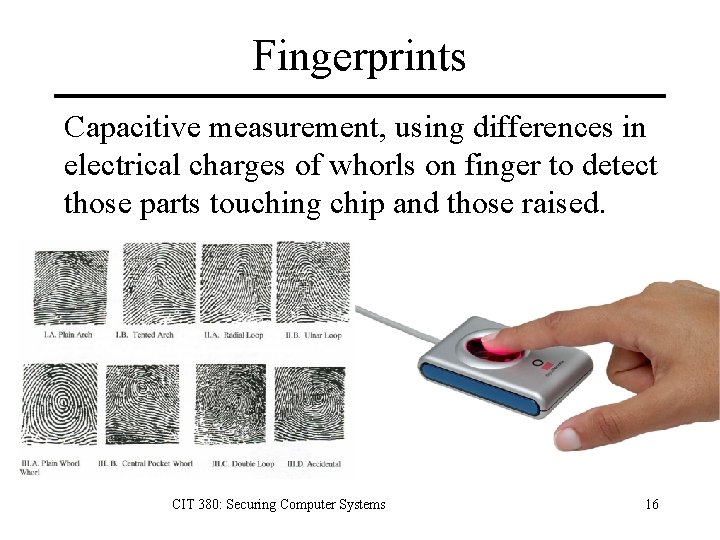
Fingerprints Capacitive measurement, using differences in electrical charges of whorls on finger to detect those parts touching chip and those raised. CIT 380: Securing Computer Systems 16
Brandon Mayfield • Fingerprints found in 2004 Madrid bombing. • Brandon arrested May 6, 2004. • FBI claimed “ 100 percent positive” match. – Held under a false name. – Then transferred to unidentified location. • Spanish police identify fingerprint as belonging to an Algerian man May 21, 2004. • Brandon released May 25, 2004. CIT 380: Securing Computer Systems 17
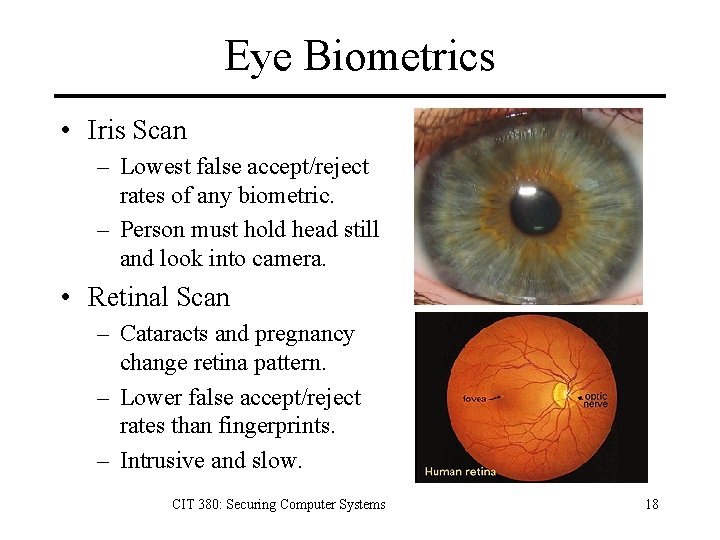
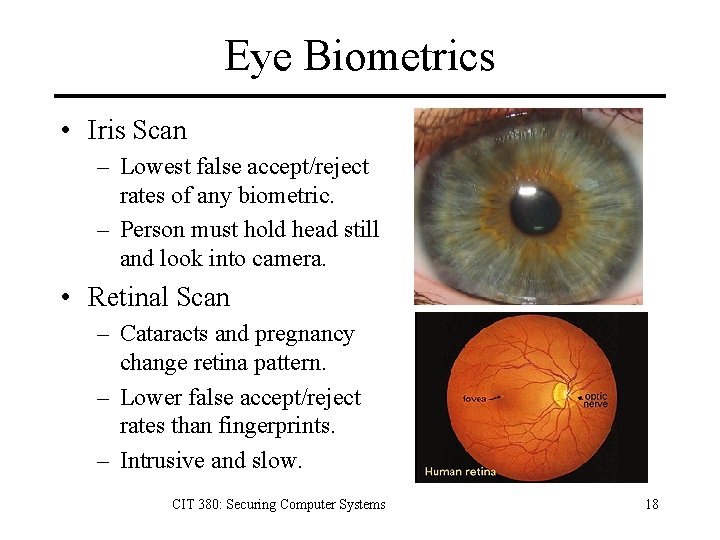
Eye Biometrics • Iris Scan – Lowest false accept/reject rates of any biometric. – Person must hold head still and look into camera. • Retinal Scan – Cataracts and pregnancy change retina pattern. – Lower false accept/reject rates than fingerprints. – Intrusive and slow. CIT 380: Securing Computer Systems 18
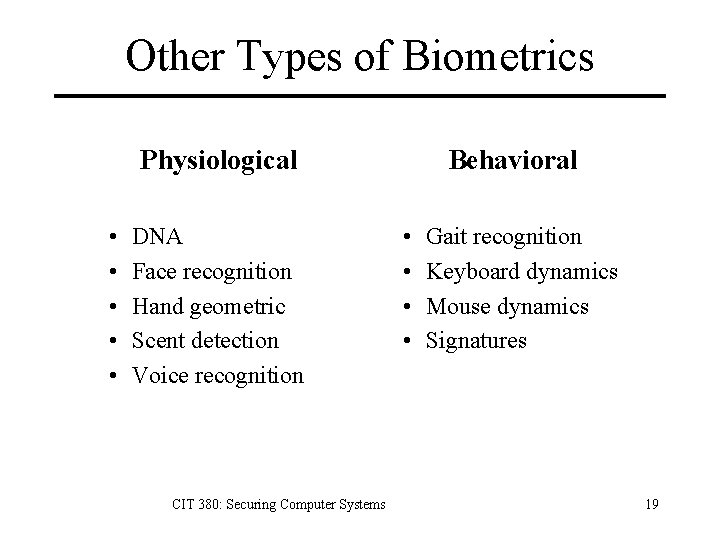
Other Types of Biometrics Physiological • • • DNA Face recognition Hand geometric Scent detection Voice recognition CIT 380: Securing Computer Systems Behavioral • • Gait recognition Keyboard dynamics Mouse dynamics Signatures 19
Biometrics are not infallible What are False Accept and Reject Rates? Do the characteristics change over time? – Retina changes during pregnancy. – Fingerprint damage due to work/pipe smoking. – Young and old people have fainter fingerprints. Is it accurate in the installed environment? – Is someone observing fingerprint or voiceprint checks? – i. e. , did you collect biometric from the person? CIT 380: Securing Computer Systems 20
Biometrics can be compromised. Unique identifiers, not secrets. – You can change a password. – You can’t change your iris scan. Examples: – You leave your fingerprints every place. – It’s easy to take a picture of your face. Other compromises. – Use faux ATM-style devices to collect biometrics. – Obtain all biometric templates from server. CIT 380: Securing Computer Systems 21
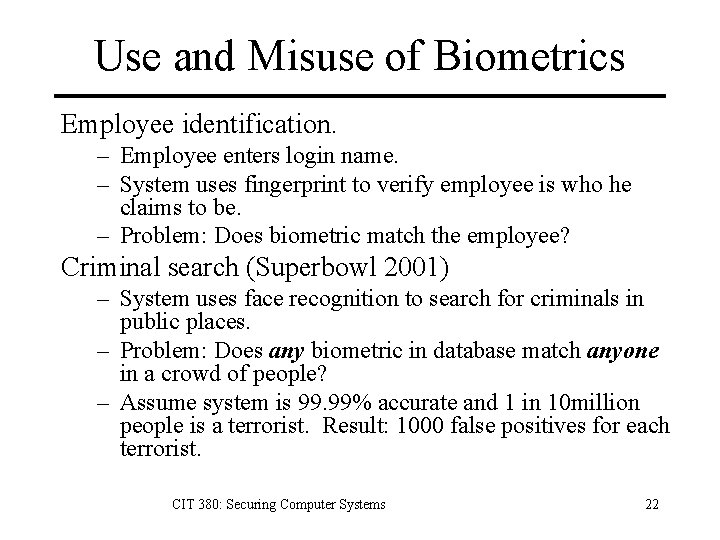
Use and Misuse of Biometrics Employee identification. – Employee enters login name. – System uses fingerprint to verify employee is who he claims to be. – Problem: Does biometric match the employee? Criminal search (Superbowl 2001) – System uses face recognition to search for criminals in public places. – Problem: Does any biometric in database match anyone in a crowd of people? – Assume system is 99. 99% accurate and 1 in 10 million people is a terrorist. Result: 1000 false positives for each terrorist. CIT 380: Securing Computer Systems 22
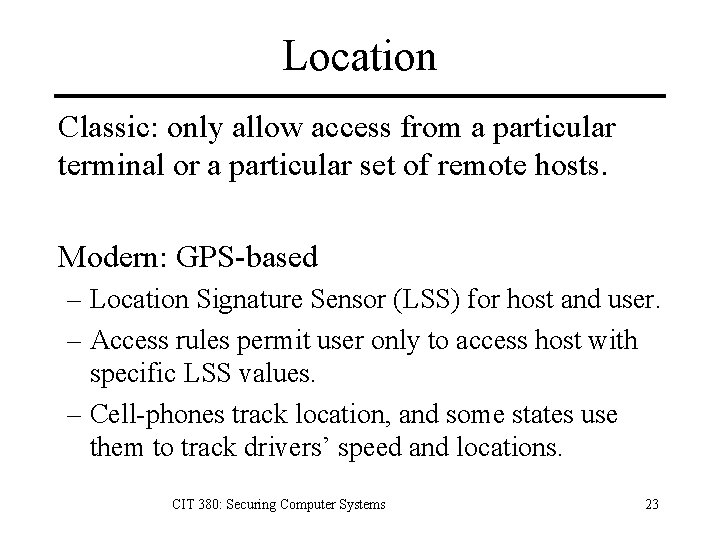
Location Classic: only allow access from a particular terminal or a particular set of remote hosts. Modern: GPS-based – Location Signature Sensor (LSS) for host and user. – Access rules permit user only to access host with specific LSS values. – Cell-phones track location, and some states use them to track drivers’ speed and locations. CIT 380: Securing Computer Systems 23
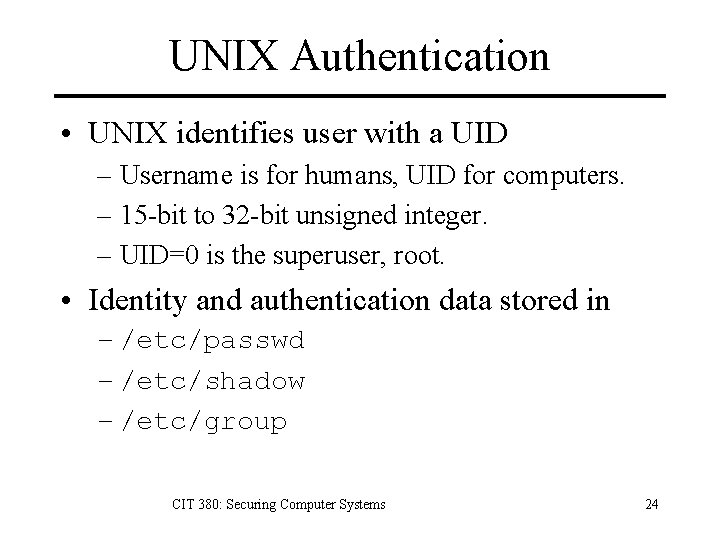
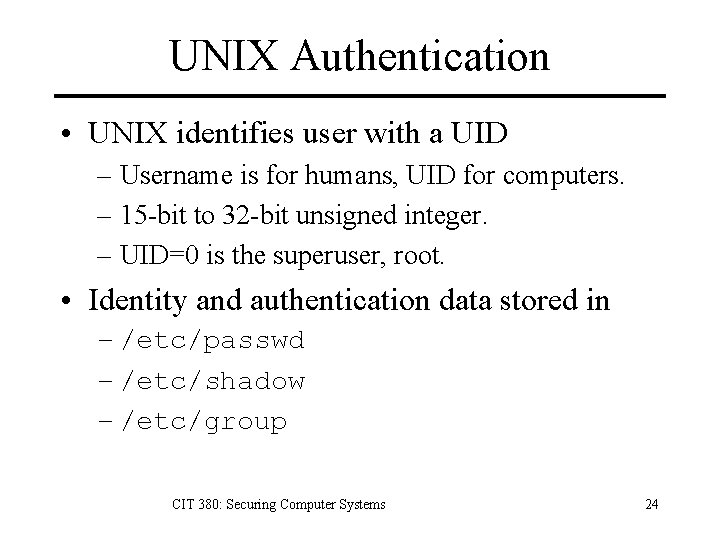
UNIX Authentication • UNIX identifies user with a UID – Username is for humans, UID for computers. – 15 -bit to 32 -bit unsigned integer. – UID=0 is the superuser, root. • Identity and authentication data stored in – /etc/passwd – /etc/shadow – /etc/group CIT 380: Securing Computer Systems 24
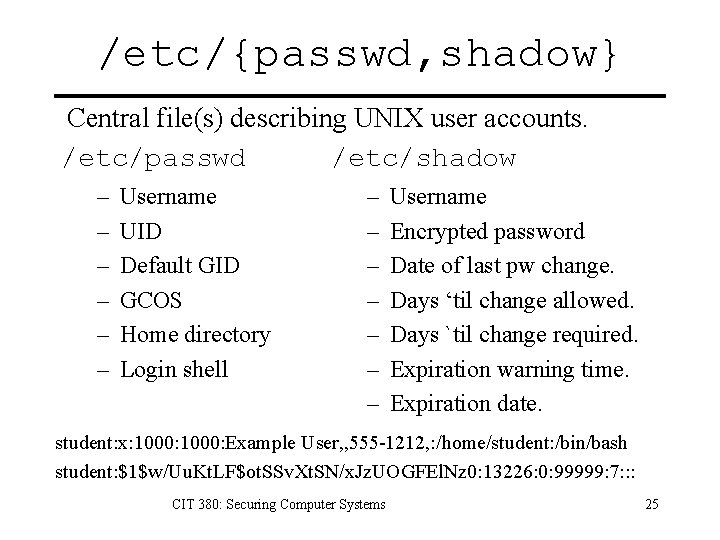
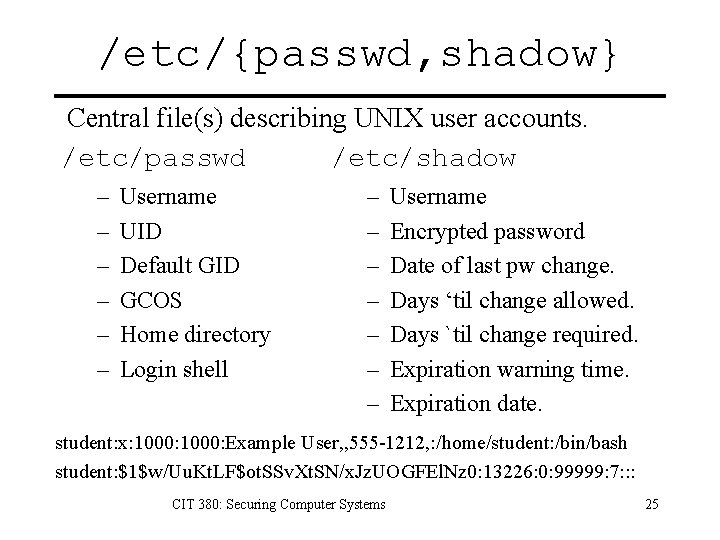
/etc/{passwd, shadow} Central file(s) describing UNIX user accounts. /etc/passwd /etc/shadow – – – Username UID Default GID GCOS Home directory Login shell – – – – Username Encrypted password Date of last pw change. Days ‘til change allowed. Days `til change required. Expiration warning time. Expiration date. student: x: 1000: Example User, , 555 -1212, : /home/student: /bin/bash student: $1$w/Uu. Kt. LF$ot. SSv. Xt. SN/x. Jz. UOGFEl. Nz 0: 13226: 0: 99999: 7: : : CIT 380: Securing Computer Systems 25
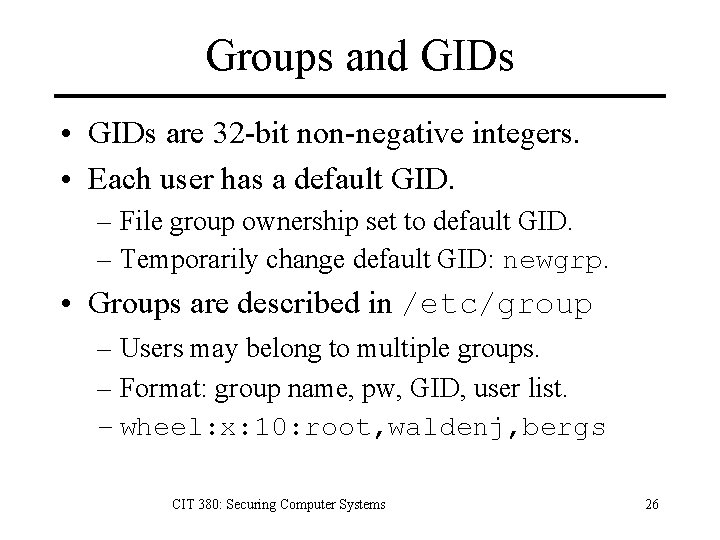
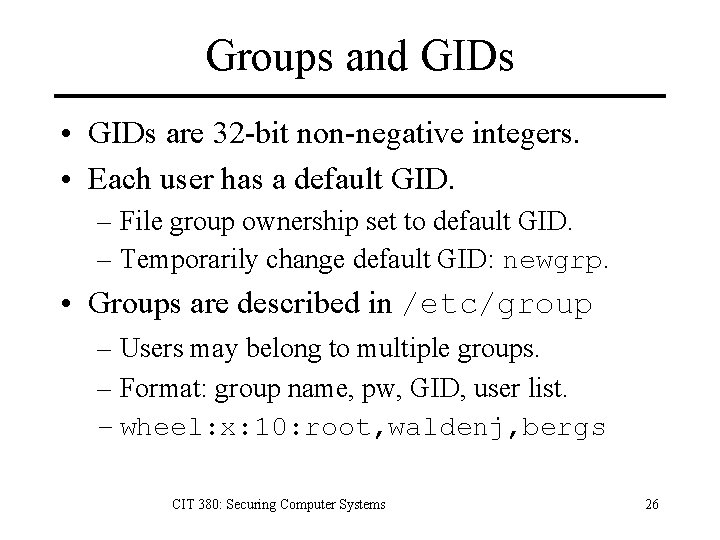
Groups and GIDs • GIDs are 32 -bit non-negative integers. • Each user has a default GID. – File group ownership set to default GID. – Temporarily change default GID: newgrp. • Groups are described in /etc/group – Users may belong to multiple groups. – Format: group name, pw, GID, user list. – wheel: x: 10: root, waldenj, bergs CIT 380: Securing Computer Systems 26
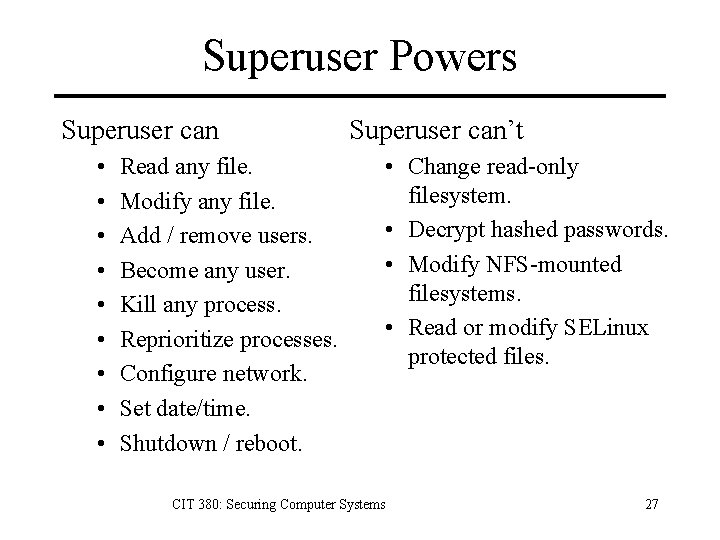
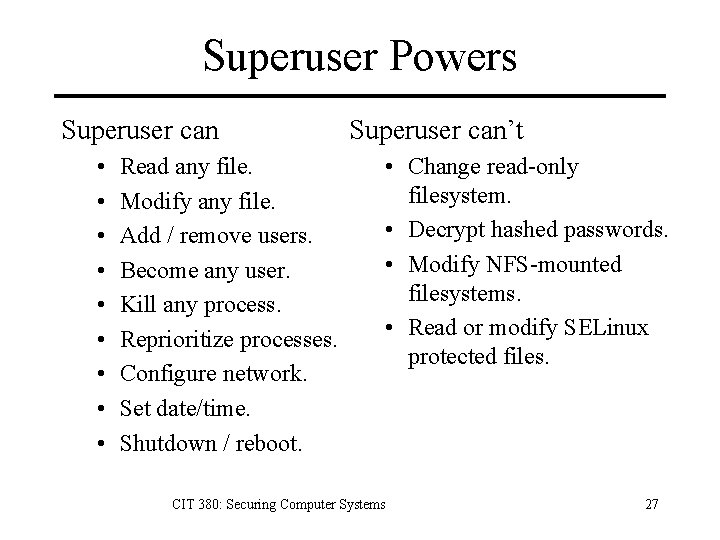
Superuser Powers Superuser can • • • Read any file. Modify any file. Add / remove users. Become any user. Kill any process. Reprioritize processes. Configure network. Set date/time. Shutdown / reboot. Superuser can’t • Change read-only filesystem. • Decrypt hashed passwords. • Modify NFS-mounted filesystems. • Read or modify SELinux protected files. CIT 380: Securing Computer Systems 27
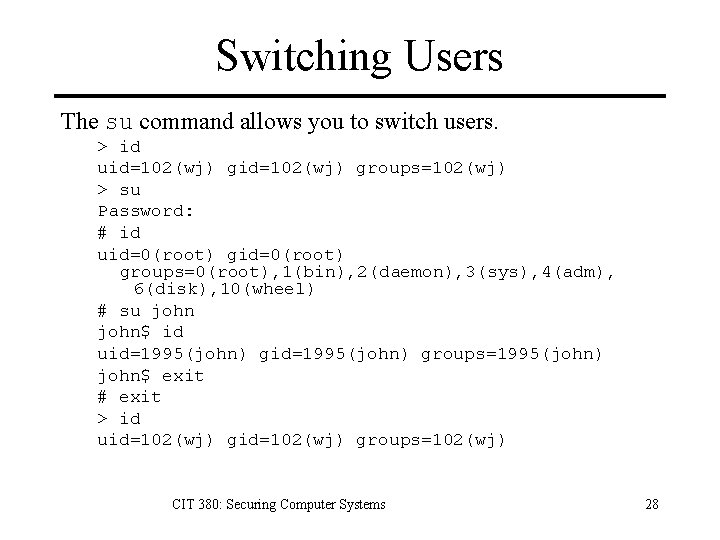
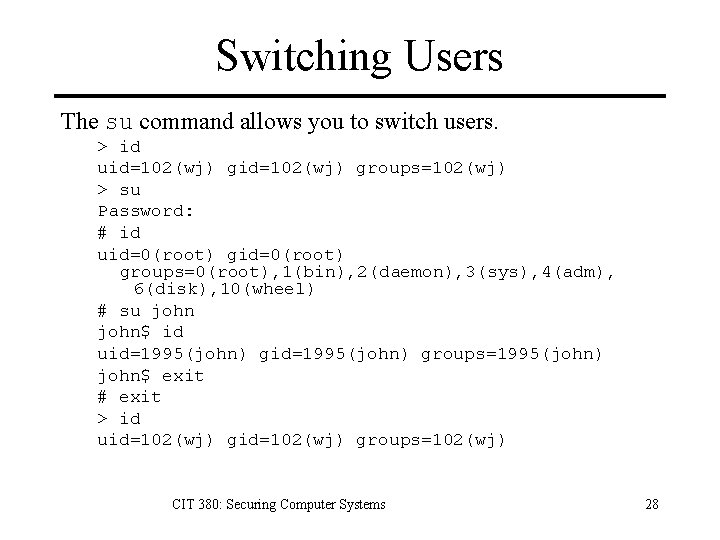
Switching Users The su command allows you to switch users. > id uid=102(wj) groups=102(wj) > su Password: # id uid=0(root) groups=0(root), 1(bin), 2(daemon), 3(sys), 4(adm), 6(disk), 10(wheel) # su john$ id uid=1995(john) groups=1995(john) john$ exit # exit > id uid=102(wj) groups=102(wj) CIT 380: Securing Computer Systems 28
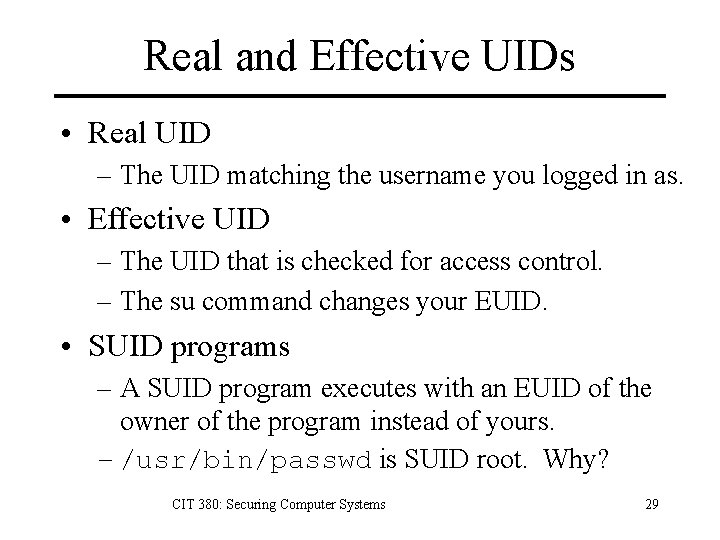
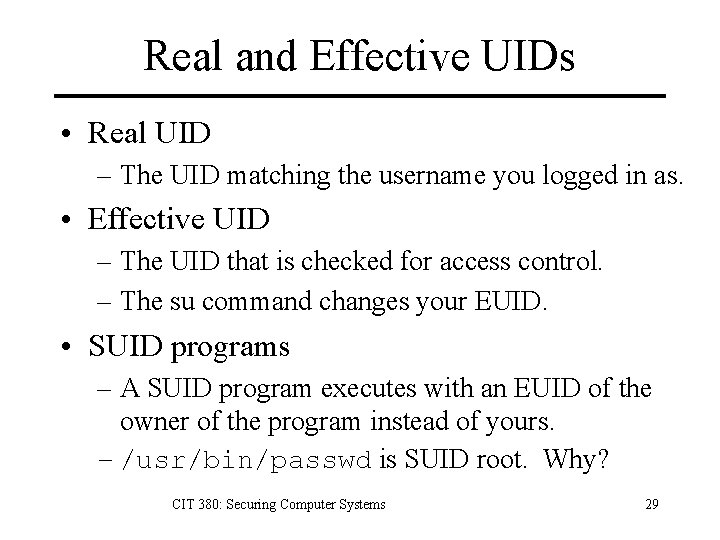
Real and Effective UIDs • Real UID – The UID matching the username you logged in as. • Effective UID – The UID that is checked for access control. – The su command changes your EUID. • SUID programs – A SUID program executes with an EUID of the owner of the program instead of yours. – /usr/bin/passwd is SUID root. Why? CIT 380: Securing Computer Systems 29
Key Points 1. Access control is based on identity. 2. Authentication consists of an entity, the user, attempting to convince another entity, the verifier, of the user’s identity 1. something you know 2. something you have 3. something you are 3. Authentication Types 1. Passwords 2. Security Tokens 3. Biometrics CIT 380: Securing Computer Systems 30
References 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. 11. 12. 13. 14. 15. 16. Phil Agre. “Your Face is not a Bar Code, ” http: //polaris. gseis. ucla. edu/pagre/bar-code. html, 2003. Ross Anderson, Security Engineering, Wiley, 2001. Matt Bishop, Introduction to Computer Security, Addison-Wesley, 2005. Digital. Persona, http: //www. digitalpersona. com/company/news/press. Kit. php, 2006. Simson Garfinkel, Gene Spafford, and Alan Schwartz, Practical UNIX and Internet Security, 3/e O’Reilly, 2003. Ben Mook, “Md. pilot program tracks drivers’ speed, location via cell phones, ” The Daily Record, October 21, 2005, http: //www. mddailyrecord. com/pub/5_398_friday/businessnews/172883 -1. html Bruce Schneier, “Biometrics: Truths and Fictions, ” Cryptogram, http: //www. schneier. com/crypto-gram -9808. html#biometrics, 1998. Bruce Schneier, “The Curse of the Secret Question, ” http: //www. schneier. com/essay-081. html, 2005. Ed Skoudis, Counter Hack Reloaded, Prentice Hall, 2006. Wikipedia, http: //en. wikipedia. org/wiki/Biometrics, 2006. Wikipedia, http: //en. wikipedia. org/wiki/Fingerprint, 2006. Wikipedia, http: //en. wikipedia. org/wiki/Iris_%28 anatomy%29, 2006. Wikipedia, http: //en. wikipedia. org/wiki/RFID, 2006. Wikipedia, http: //en. wikipedia. org/wiki/Security_token, 2006. Orville Wilson, “Privacy & Identity - Security and Usability: The viability of Passwords & Biometrics, ” http: //facweb. cs. depaul. edu/research/vc/CIPLIT 2004/ppt/Orville_Wilson. ppt, 2004. “Simple Anatomy of the Retina, ” http: //webvision. med. utah. edu/sretina. html, 2006. CIT 380: Securing Computer Systems 31