Cisco Security Solutions for Small and Medium Businesses
Cisco Security Solutions for Small and Medium Businesses Make your e-business secure CIBR Security technical solution customer © 2002, Cisco Systems, Inc. All rights reserved. 1
Agenda • Security solution overview • Business issues and security • Security features and benefits • Tell us more about your security needs • Measuring the success of your security deployment • Importance of the network infrastructure in deploying security • Example business scenario • Example network blueprints • URLs for additional information on security CIBR Security technical solution customer © 2002, Cisco Systems, Inc. All rights reserved. 2
Security — Solution Overview • What is security? A process, not a product An integrated system Security requires defense in depth, which includes: Firewalls and router access control lists (ACLs) Network and host-based intrusion detection Scanners Centralized security and policy management Authentication, authorization, and accounting (AAA), access control servers and certificate authorities Encryption and virtual private networks (VPNs) CIBR Security technical solution customer © 2002, Cisco Systems, Inc. All rights reserved. 3
Security is a Process “Security is not a product; it’s a process. You can’t just add it to a system after the fact. It’s vital to understand the real threats to a system, design a security policy commensurate with those threats, and build in appropriate security countermeasures. ” Bruce Schneier “Secrets and Lies” CIBR Security technical solution how customer to sell © 2002, Cisco Systems, Inc. All rights reserved. 4
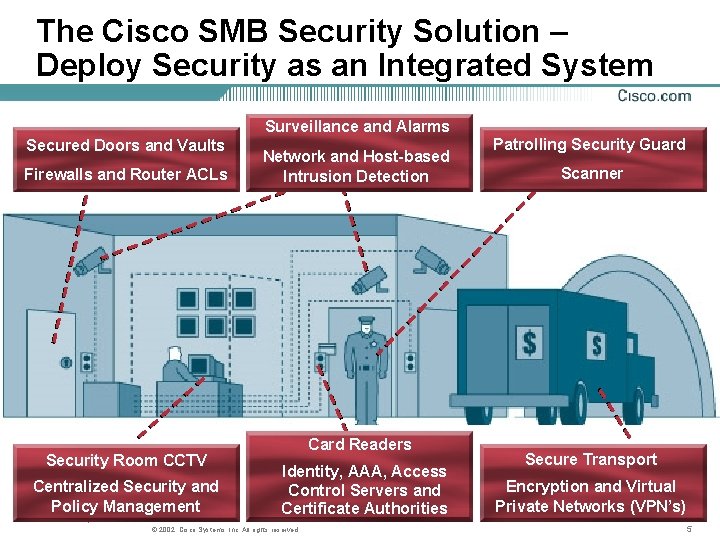
The Cisco SMB Security Solution – Deploy Security as an Integrated System Surveillance and Alarms Secured Doors and Vaults Firewalls and Router ACLs Security Room CCTV Centralized Security and Policy Management CIBR Security technical solution customer Network and Host-based Intrusion Detection Card Readers Identity, AAA, Access Control Servers and Certificate Authorities © 2002, Cisco Systems, Inc. All rights reserved. Patrolling Security Guard Scanner Secure Transport Encryption and Virtual Private Networks (VPN’s) 5

Security for Internet Business Solutions Customer Care Manufacturing and Distribution E-Commerce E-Procurement Financial Management Workforce Optimization Web Communication Supply Chain Management CIBR Security technical solution how customer to sell © 2002, Cisco Systems, Inc. All rights reserved. Salesforce Automation Web Marketing 6 6
Strategic Business Drivers for Security Solutions • Do these issues influence your business? Damage to company image after a security breach Legal liabilities resulting from a breach Lost revenues resulting from a breach Need for customer/supplier confidence in doing ebusiness with the company Fear of theft Fear of fraud Loss of employee morale Wireless security CIBR Security technical solution customer © 2002, Cisco Systems, Inc. All rights reserved. 7
Today’s Network Security Threats • Everything is a target • Internet attacks are on the rise (Computer Security Institute & FBI Report March, 2001) • More and better hacker tools means more hackers • Economic impact of Internet worms and viruses • Theft of proprietary information • Financial fraud • Insider abuse • Sabotage • Unauthorized access by insiders (worse than by outsiders) • Unauthorized access by outsiders • Denial of service attacks CIBR Security technical solution customer © 2002, Cisco Systems, Inc. All rights reserved. 8
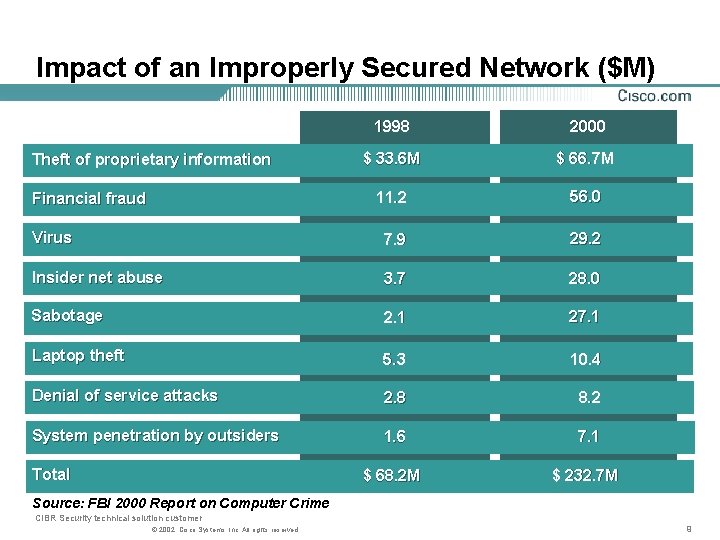
Impact of an Improperly Secured Network ($M) 1998 2000 $ 33. 6 M $ 66. 7 M 11. 2 56. 0 Virus 7. 9 29. 2 Insider net abuse 3. 7 28. 0 Sabotage 2. 1 27. 1 Laptop theft 5. 3 10. 4 Denial of service attacks 2. 8 8. 2 System penetration by outsiders 1. 6 7. 1 $ 68. 2 M $ 232. 7 M Theft of proprietary information Financial fraud Total Source: FBI 2000 Report on Computer Crime CIBR Security technical solution customer © 2002, Cisco Systems, Inc. All rights reserved. 9
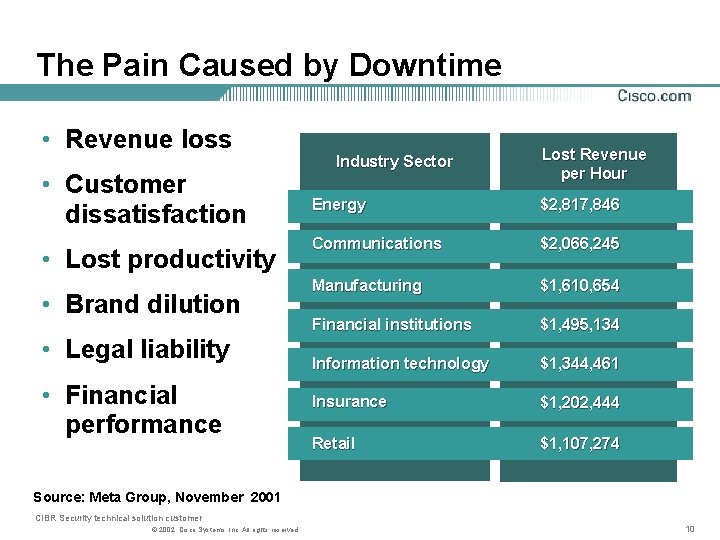
The Pain Caused by Downtime • Revenue loss • Customer dissatisfaction • Lost productivity • Brand dilution • Legal liability • Financial performance Industry Sector Lost Revenue per Hour Energy $2, 817, 846 Communications $2, 066, 245 Manufacturing $1, 610, 654 Financial institutions $1, 495, 134 Information technology $1, 344, 461 Insurance $1, 202, 444 Retail $1, 107, 274 Source: Meta Group, November 2001 CIBR Security technical solution customer © 2002, Cisco Systems, Inc. All rights reserved. 10
Features • Secure connectivity • Perimeter security • Controlled access • Surveillance and alarms • Security monitoring • Centralized security policy management • Centralized security device management • Identity • Secure transport CIBR Security technical solution customer © 2002, Cisco Systems, Inc. All rights reserved. 11
Benefits • Secure connectivity over public networks • Restricted access to network resources • Protection against network attack and misues • Ability to find and close security holes before hackers find them • Ability to identify users and what they are permitted to do on the network • Simplified management of security policies and devices CIBR Security technical solution customer © 2002, Cisco Systems, Inc. All rights reserved. 12
Tell Us More • In the event of disruption, can you: Ensure critical systems and networks are continuously available? Restore mission critical applications? Provide uninterrupted workforce productivity with a secure instant office? • What’s the impact of not properly securing your network in terms of cost? . . . credibility? . . . productivity? . . . viability? . . . liability? • How much revenue loss caused by downtime can you afford? How much customer dissatisfaction caused by downtime can you afford? How much lost productivity? . . . brand dilution? . . . legal liability? . . . reduced financial performance? CIBR Security technical solution customer © 2002, Cisco Systems, Inc. All rights reserved. 13
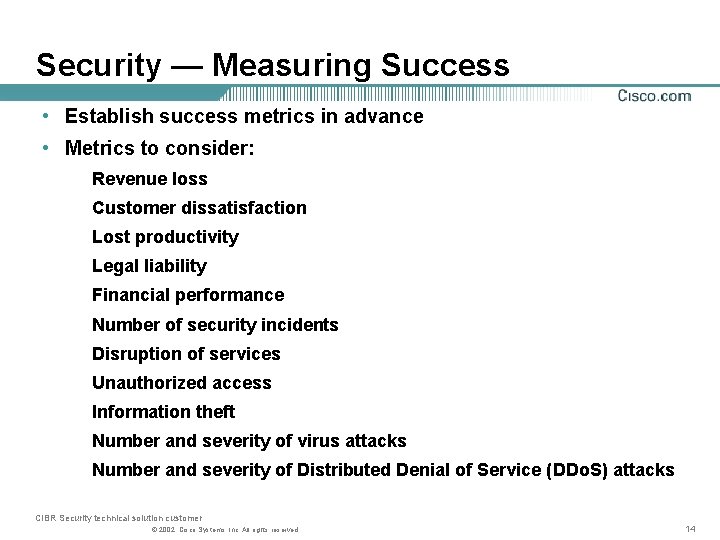
Security — Measuring Success • Establish success metrics in advance • Metrics to consider: Revenue loss Customer dissatisfaction Lost productivity Legal liability Financial performance Number of security incidents Disruption of services Unauthorized access Information theft Number and severity of virus attacks Number and severity of Distributed Denial of Service (DDo. S) attacks CIBR Security technical solution customer © 2002, Cisco Systems, Inc. All rights reserved. 14
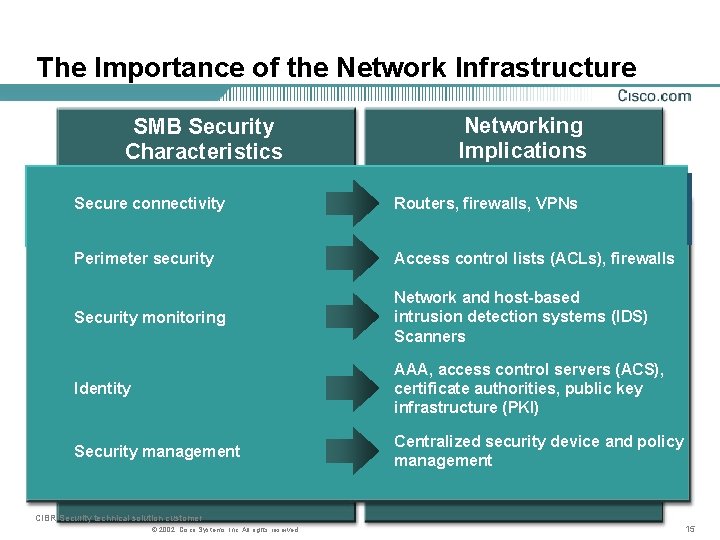
The Importance of the Network Infrastructure SMB Security Characteristics Networking Implications Secure connectivity Routers, firewalls, VPNs Perimeter security Access control lists (ACLs), firewalls Security monitoring Network and host-based intrusion detection systems (IDS) Scanners Identity AAA, access control servers (ACS), certificate authorities, public key infrastructure (PKI) Security management Centralized security device and policy management CIBR Security technical solution customer © 2002, Cisco Systems, Inc. All rights reserved. 15
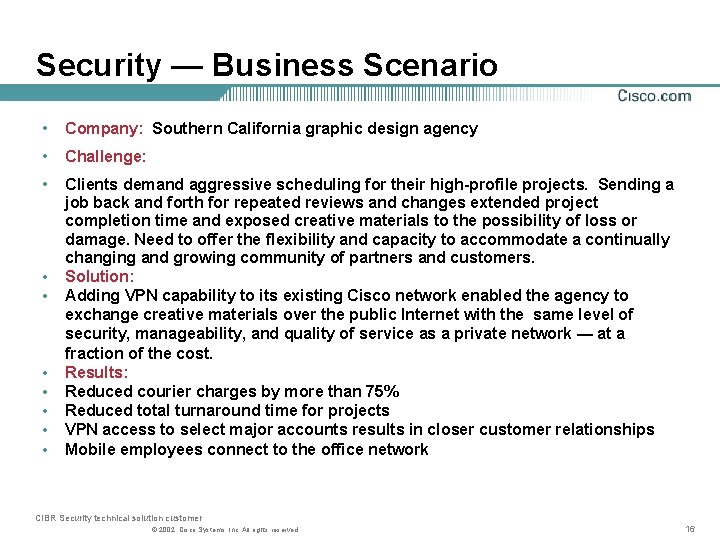
Security — Business Scenario • Company: Southern California graphic design agency • Challenge: • Clients demand aggressive scheduling for their high-profile projects. Sending a job back and forth for repeated reviews and changes extended project completion time and exposed creative materials to the possibility of loss or damage. Need to offer the flexibility and capacity to accommodate a continually changing and growing community of partners and customers. Solution: Adding VPN capability to its existing Cisco network enabled the agency to exchange creative materials over the public Internet with the same level of security, manageability, and quality of service as a private network — at a fraction of the cost. Results: Reduced courier charges by more than 75% Reduced total turnaround time for projects VPN access to select major accounts results in closer customer relationships Mobile employees connect to the office network • • CIBR Security technical solution customer © 2002, Cisco Systems, Inc. All rights reserved. 16
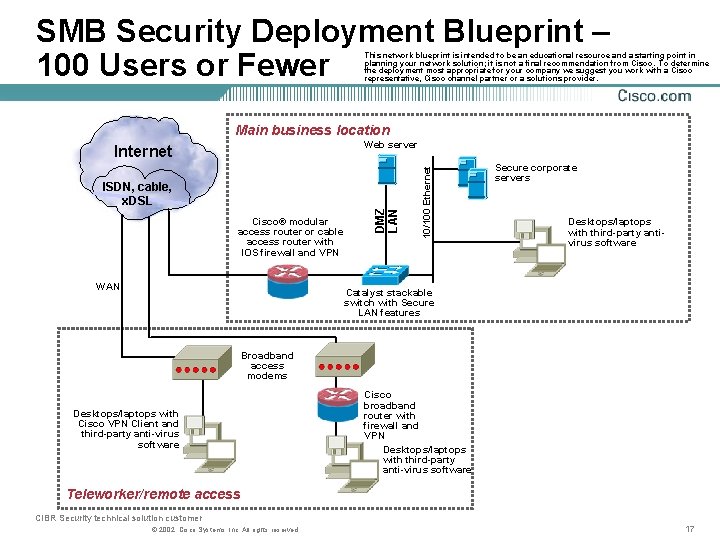
SMB Security Deployment Blueprint – 100 Users or Fewer This network blueprint is intended to be an educational resource and a starting point in planning your network solution; it is not a final recommendation from Cisco. To determine the deployment most appropriate for your company we suggest you work with a Cisco representative, Cisco channel partner or a solutions provider. Main business location Cisco® modular access router or cable access router with IOS firewall and VPN WAN 10/100 Ethernet ISDN, cable, x. DSL DMZ LAN Web server Internet Secure corporate servers Desktops/laptops with third-party antivirus software Catalyst stackable switch with Secure LAN features Broadband access modems Desktops/laptops with Cisco VPN Client and third-party anti-virus software Cisco broadband router with firewall and VPN Desktops/laptops with third-party anti-virus software Teleworker/remote access CIBR Security technical solution customer © 2002, Cisco Systems, Inc. All rights reserved. 17
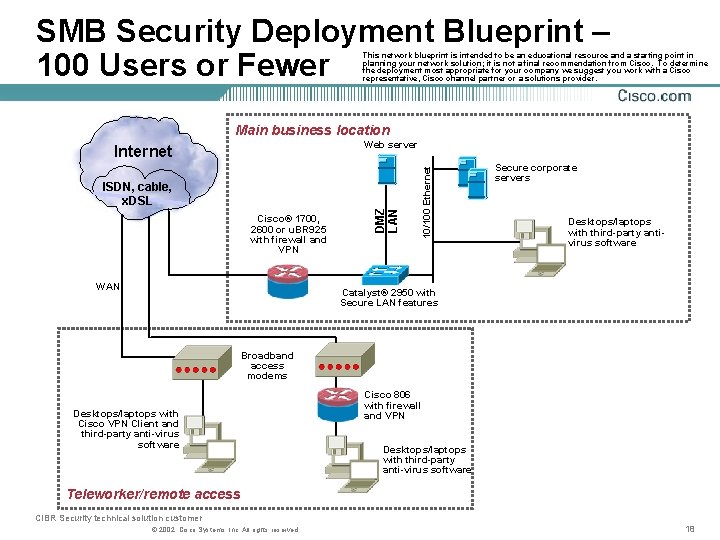
SMB Security Deployment Blueprint – 100 Users or Fewer This network blueprint is intended to be an educational resource and a starting point in planning your network solution; it is not a final recommendation from Cisco. To determine the deployment most appropriate for your company we suggest you work with a Cisco representative, Cisco channel partner or a solutions provider. Main business location Cisco® 1700, 2600 or u. BR 925 with firewall and VPN WAN 10/100 Ethernet ISDN, cable, x. DSL DMZ LAN Web server Internet Secure corporate servers Desktops/laptops with third-party antivirus software Catalyst® 2950 with Secure LAN features Broadband access modems Desktops/laptops with Cisco VPN Client and third-party anti-virus software Cisco 806 with firewall and VPN Desktops/laptops with third-party anti-virus software Teleworker/remote access CIBR Security technical solution customer © 2002, Cisco Systems, Inc. All rights reserved. 18
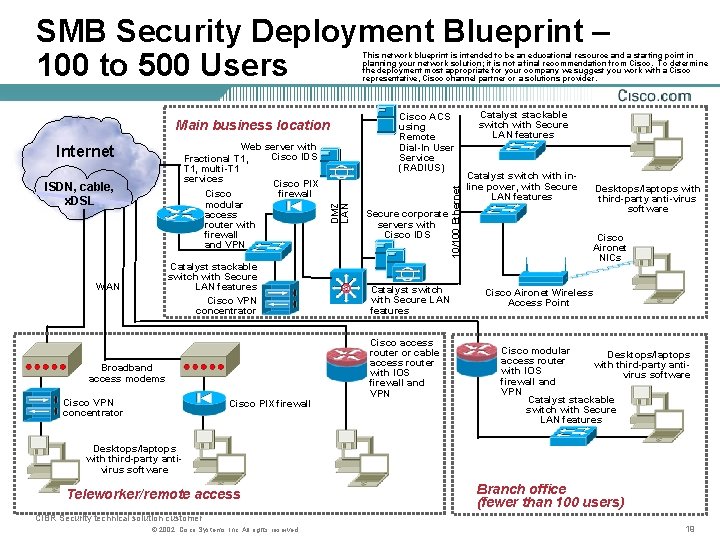
SMB Security Deployment Blueprint – 100 to 500 Users This network blueprint is intended to be an educational resource and a starting point in planning your network solution; it is not a final recommendation from Cisco. To determine the deployment most appropriate for your company we suggest you work with a Cisco representative, Cisco channel partner or a solutions provider. ISDN, cable, x. DSL Catalyst stackable switch with Secure LAN features Cisco VPN concentrator WAN Broadband access modems Cisco VPN concentrator Cisco PIX firewall Cisco ACS using Remote Dial-In User Service (RADIUS) Secure corporate servers with Cisco IDS 10/100 Ethernet Web server with Cisco IDS Fractional T 1, multi-T 1 services Cisco PIX firewall Cisco modular access router with firewall and VPN Internet DMZ LAN Main business location Catalyst switch with Secure LAN features Cisco access router or cable access router with IOS firewall and VPN Catalyst stackable switch with Secure LAN features Catalyst switch with inline power, with Secure LAN features Desktops/laptops with third-party anti-virus software Cisco Aironet NICs Cisco Aironet Wireless Access Point Cisco modular Desktops/laptops access router with third-party antiwith IOS virus software firewall and VPN Catalyst stackable switch with Secure LAN features Desktops/laptops with third-party antivirus software Teleworker/remote access Branch office (fewer than 100 users) CIBR Security technical solution customer © 2002, Cisco Systems, Inc. All rights reserved. 19
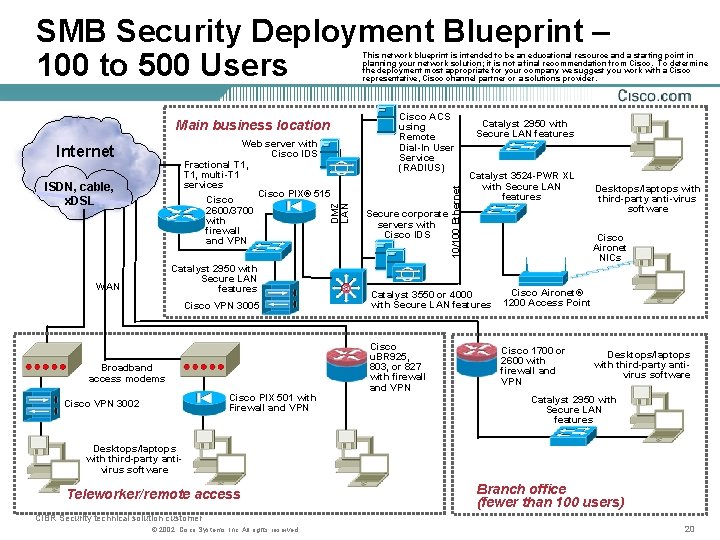
SMB Security Deployment Blueprint – 100 to 500 Users This network blueprint is intended to be an educational resource and a starting point in planning your network solution; it is not a final recommendation from Cisco. To determine the deployment most appropriate for your company we suggest you work with a Cisco representative, Cisco channel partner or a solutions provider. Web server with Cisco IDS Fractional T 1, multi-T 1 services Cisco PIX® 515 Cisco 2600/3700 with firewall and VPN Internet DMZ LAN ISDN, cable, x. DSL Catalyst 2950 with Secure LAN features WAN Cisco VPN 3005 Broadband access modems Cisco PIX 501 with Firewall and VPN Cisco VPN 3002 Cisco ACS using Remote Dial-In User Service (RADIUS) Secure corporate servers with Cisco IDS 10/100 Ethernet Main business location Catalyst 2950 with Secure LAN features Catalyst 3524 -PWR XL with Secure LAN features Desktops/laptops with third-party anti-virus software Cisco Aironet NICs Catalyst 3550 or 4000 with Secure LAN features Cisco Aironet® 1200 Access Point Cisco u. BR 925, 803, or 827 with firewall and VPN Cisco 1700 or 2600 with firewall and VPN Desktops/laptops with third-party antivirus software Catalyst 2950 with Secure LAN features Desktops/laptops with third-party antivirus software Teleworker/remote access Branch office (fewer than 100 users) CIBR Security technical solution customer © 2002, Cisco Systems, Inc. All rights reserved. 20
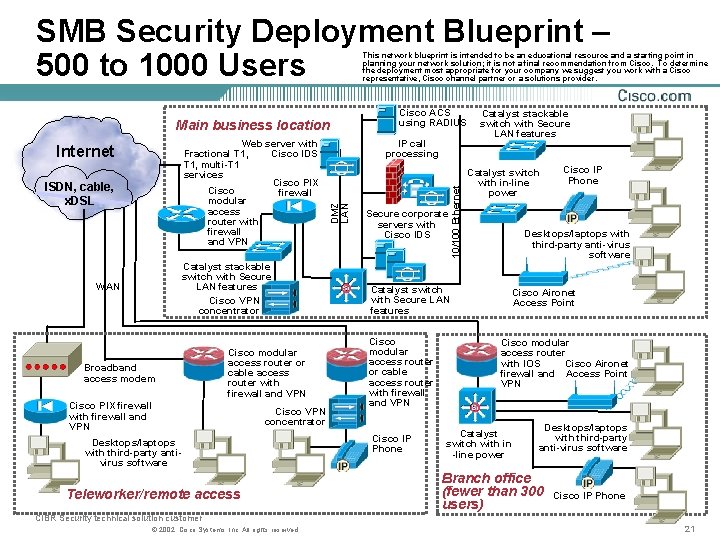
SMB Security Deployment Blueprint – 500 to 1000 Users This network blueprint is intended to be an educational resource and a starting point in planning your network solution; it is not a final recommendation from Cisco. To determine the deployment most appropriate for your company we suggest you work with a Cisco representative, Cisco channel partner or a solutions provider. Main business location Catalyst stackable switch with Secure LAN features Cisco VPN concentrator WAN Broadband access modem Cisco modular access router or cable access router with firewall and VPN Cisco PIX firewall with firewall and VPN Cisco VPN concentrator Desktops/laptops with third-party antivirus software Teleworker/remote access Secure corporate servers with Cisco IDS 10/100 Ethernet ISDN, cable, x. DSL IP call processing DMZ LAN Web server with Cisco IDS Fractional T 1, multi-T 1 services Cisco PIX Cisco firewall modular access router with firewall and VPN Internet Cisco ACS using RADIUS Catalyst stackable switch with Secure LAN features Catalyst switch with in-line power Desktops/laptops with third-party anti-virus software Catalyst switch with Secure LAN features Cisco modular access router or cable access router with firewall and VPN Cisco IP Phone Cisco Aironet Access Point Cisco modular access router with IOS Cisco Aironet firewall and Access Point VPN Catalyst switch with in -line power Desktops/laptops with third-party anti-virus software Branch office (fewer than 300 users) Cisco IP Phone CIBR Security technical solution customer © 2002, Cisco Systems, Inc. All rights reserved. 21
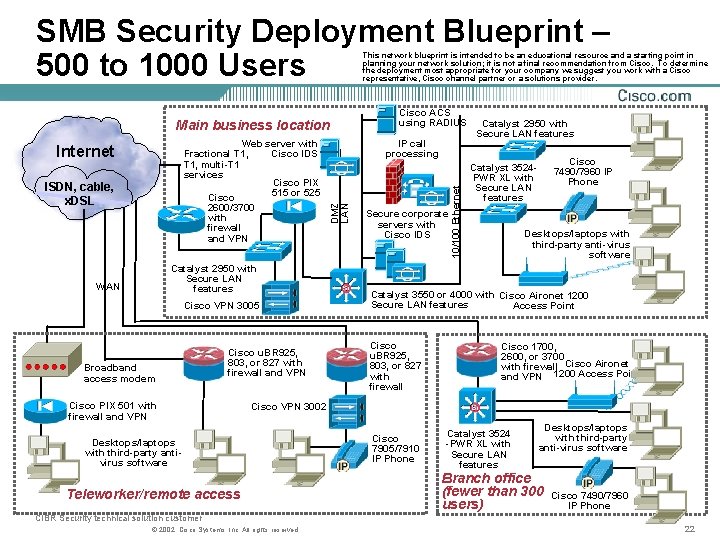
SMB Security Deployment Blueprint – 500 to 1000 Users This network blueprint is intended to be an educational resource and a starting point in planning your network solution; it is not a final recommendation from Cisco. To determine the deployment most appropriate for your company we suggest you work with a Cisco representative, Cisco channel partner or a solutions provider. Main business location 2600/3700 with firewall and VPN Catalyst 2950 with Secure LAN features WAN Cisco VPN 3005 Broadband access modem Cisco u. BR 925, 803, or 827 with firewall and VPN Cisco PIX 501 with firewall and VPN Secure corporate servers with Cisco IDS 10/100 Ethernet ISDN, cable, x. DSL IP call processing DMZ LAN Web server with Cisco IDS Fractional T 1, multi-T 1 services Cisco PIX 515 or 525 Cisco Internet Cisco ACS using RADIUS Catalyst 2950 with Secure LAN features Cisco 7490/7960 IP Phone Catalyst 3524 PWR XL with Secure LAN features Desktops/laptops with third-party anti-virus software Catalyst 3550 or 4000 with Cisco Aironet 1200 Secure LAN features Access Point Cisco u. BR 925, 803, or 827 with firewall Cisco 1700, 2600, or 3700 with firewall Cisco Aironet and VPN 1200 Access Point Cisco VPN 3002 Desktops/laptops with third-party antivirus software Teleworker/remote access Cisco 7905/7910 IP Phone Catalyst 3524 -PWR XL with Secure LAN features Desktops/laptops with third-party anti-virus software Branch office (fewer than 300 users) Cisco 7490/7960 IP Phone CIBR Security technical solution customer © 2002, Cisco Systems, Inc. All rights reserved. 22
SMARTnet and SMARTnet Onsite • What is SMARTnet/SMARTnet Onsite? Cisco’s Technical Support Service, available direct and through resale • What does it offer? Operating system software updates (including IOS) -major, minor, and maintenance releases 24 x 7 x 365 access to highly skilled networking personnel (TAC) via phone, email, and web Access to Self Help technical repositories on-line Advance parts replacement in as little as two hours Onsite field engineers available in as little as two hours (OSS) to assist in hardware replacement CIBR Security technical solution customer © 2002, Cisco Systems, Inc. All rights reserved. 23
Why Cisco for SMB Security? • No one knows your network, the Internet, or security better • Compatibility with the installed Cisco base (80% of the Internet) • Significant savings from a single-vendor solution • Excellent quality, standards-based development, and certified products – • Network intelligent, integrated security solutions • Key partnerships and worldwide security industry leadership • Market-leading solutions, services, and support CIBR Security technical solution customer © 2002, Cisco Systems, Inc. All rights reserved. 24
Important URLs • Cisco security overview • www. cisco. com/go/securitypartners • www. cisco. com/go/security • www. cisco. com/go/netpro • www. cisco. com/go/securitytrng • www. cert. org • www. cisco. com/go/safe • www. happyhacker. org • VPN ROI calculator • www. infosecuritymag. com • Cisco SAFE documents • www. cisco. com/go/evpn • Reseller support Web site • www. cisco. com/go/vsec • Cisco Secure Encyclopedia • www. cisco. com/go/csec CIBR Security technical solution customer © 2002, Cisco Systems, Inc. All rights reserved. 25
www. cisco. com/warp/public/779/smbiz/iroadmap/solutions. html CIBR Security technical solution customer © 2001, Cisco Systems, Inc. 26
- Slides: 26