Cisco Router Forensics Thomas Akin CISSP Director Southeast
- Slides: 21
Cisco Router Forensics Thomas Akin, CISSP Director, Southeast Cybercrime Institute Kennesaw State University Black. Hat Briefings, USA, 2002
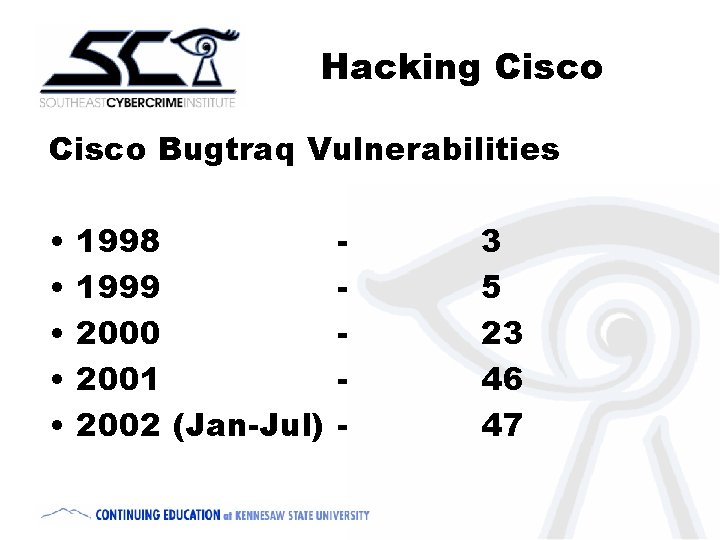
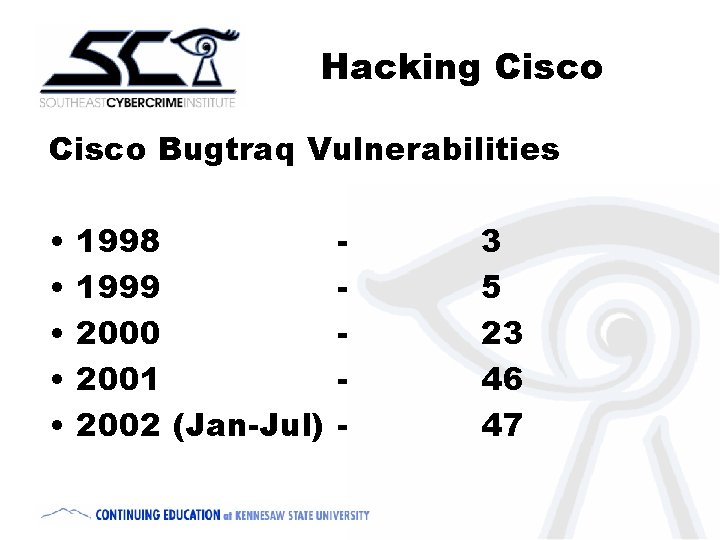
Hacking Cisco Bugtraq Vulnerabilities • • • 1998 1999 2000 2001 2002 (Jan-Jul) - 3 5 23 46 47
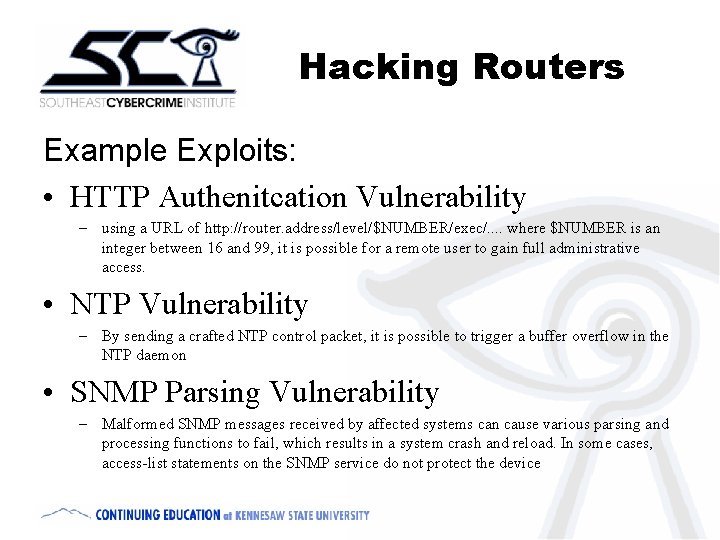
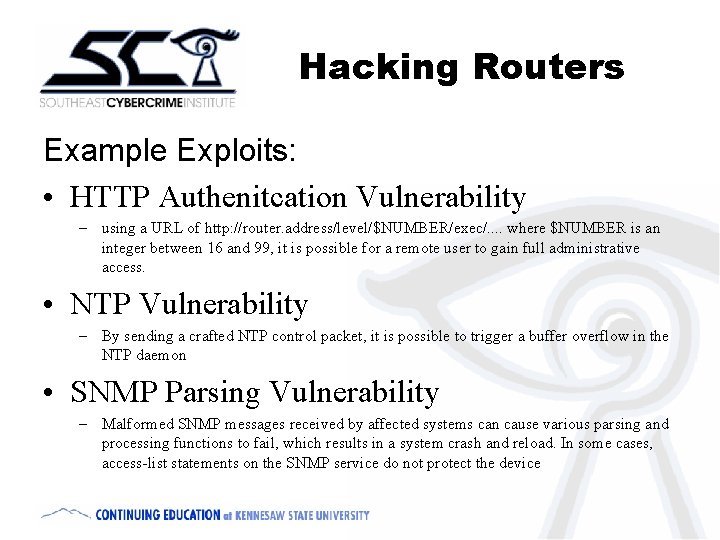
Hacking Routers Example Exploits: • HTTP Authenitcation Vulnerability – using a URL of http: //router. address/level/$NUMBER/exec/. . where $NUMBER is an integer between 16 and 99, it is possible for a remote user to gain full administrative access. • NTP Vulnerability – By sending a crafted NTP control packet, it is possible to trigger a buffer overflow in the NTP daemon • SNMP Parsing Vulnerability – Malformed SNMP messages received by affected systems can cause various parsing and processing functions to fail, which results in a system crash and reload. In some cases, access-list statements on the SNMP service do not protect the device
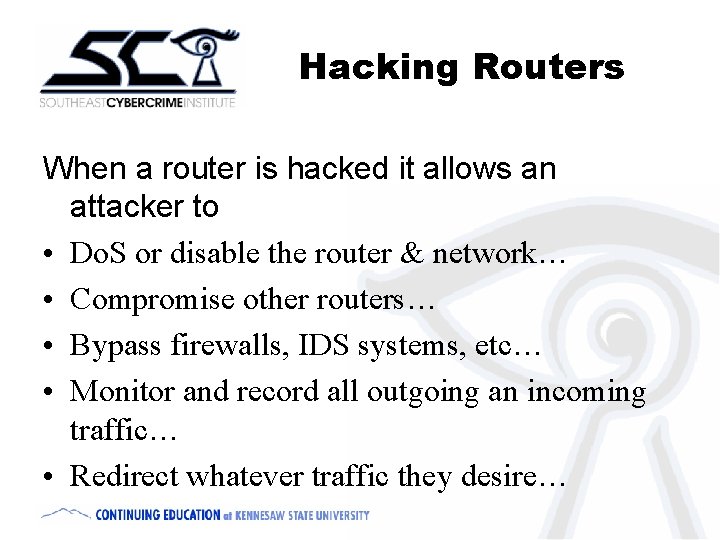
Hacking Routers When a router is hacked it allows an attacker to • Do. S or disable the router & network… • Compromise other routers… • Bypass firewalls, IDS systems, etc… • Monitor and record all outgoing an incoming traffic… • Redirect whatever traffic they desire…
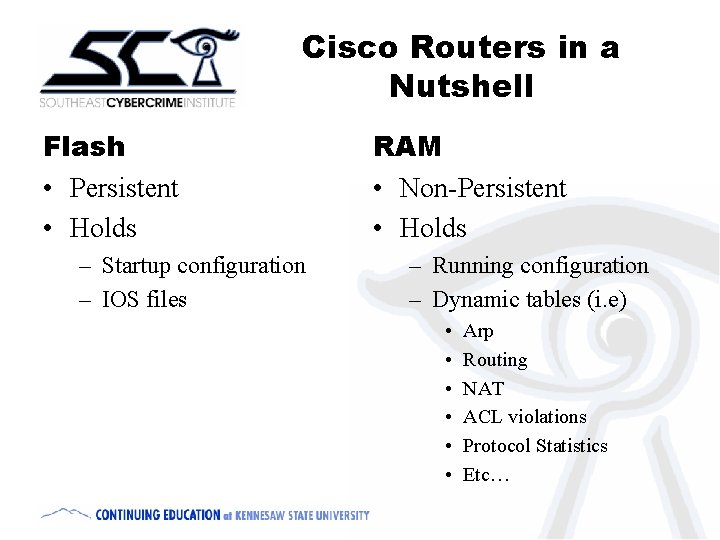
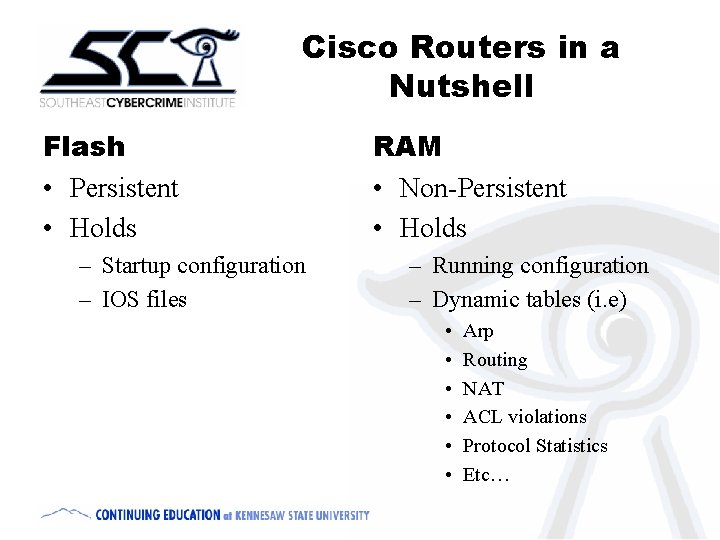
Cisco Routers in a Nutshell Flash • Persistent • Holds – Startup configuration – IOS files RAM • Non-Persistent • Holds – Running configuration – Dynamic tables (i. e) • • • Arp Routing NAT ACL violations Protocol Statistics Etc…
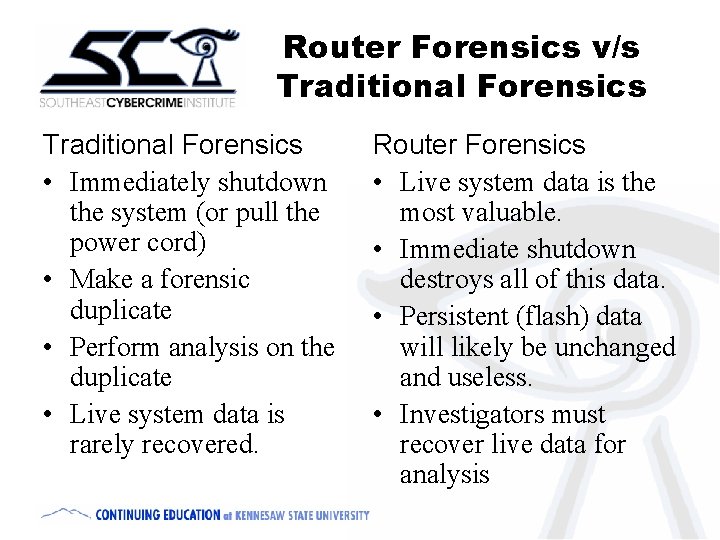
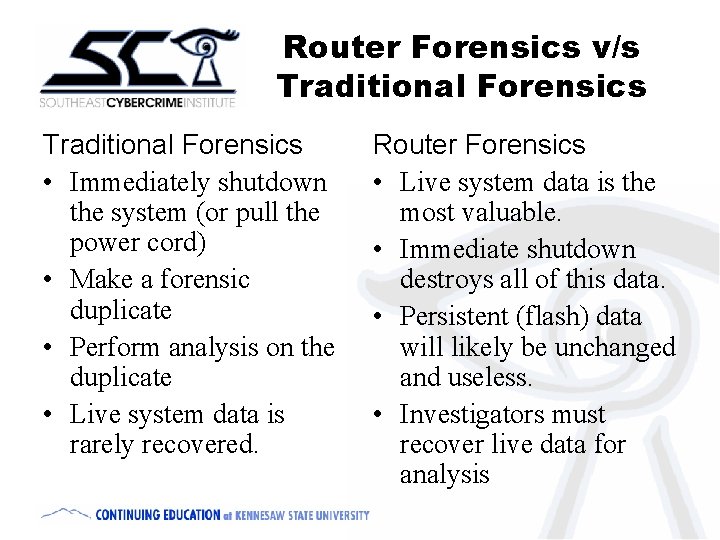
Router Forensics v/s Traditional Forensics • Immediately shutdown the system (or pull the power cord) • Make a forensic duplicate • Perform analysis on the duplicate • Live system data is rarely recovered. Router Forensics • Live system data is the most valuable. • Immediate shutdown destroys all of this data. • Persistent (flash) data will likely be unchanged and useless. • Investigators must recover live data for analysis
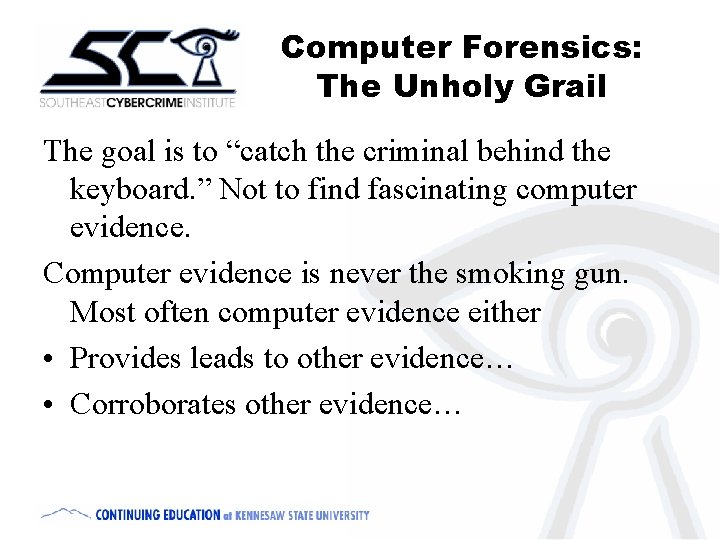
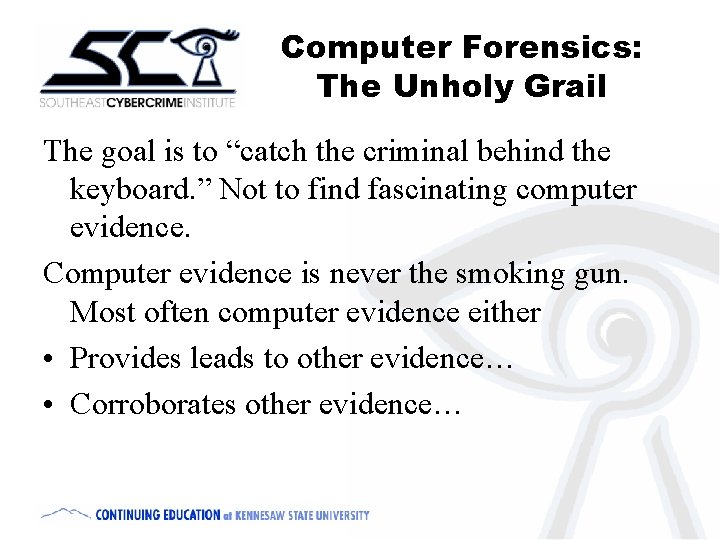
Computer Forensics: The Unholy Grail The goal is to “catch the criminal behind the keyboard. ” Not to find fascinating computer evidence. Computer evidence is never the smoking gun. Most often computer evidence either • Provides leads to other evidence… • Corroborates other evidence…
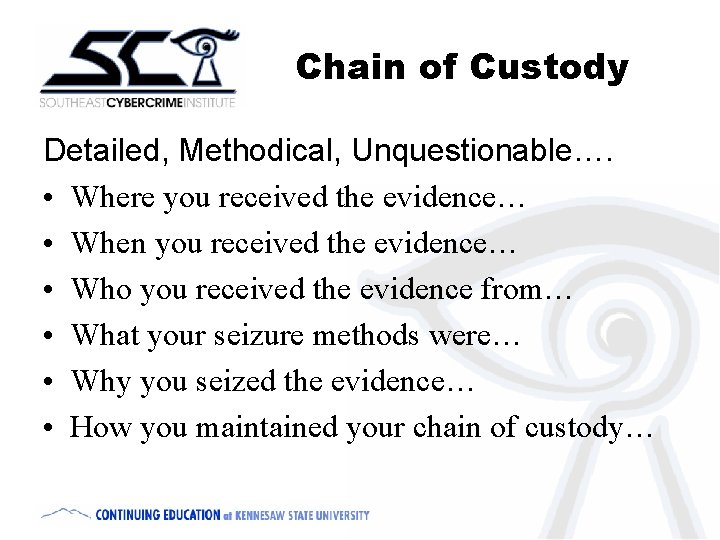
Chain of Custody Detailed, Methodical, Unquestionable…. • Where you received the evidence… • When you received the evidence… • Who you received the evidence from… • What your seizure methods were… • Why you seized the evidence… • How you maintained your chain of custody…
Incident Response • DO NOT REBOOT THE ROUTER. • Change nothing, record everything. • Before you say it is an accident, make sure it isn’t an incident… • Before you say it is an incident, make sure it isn’t an accident…
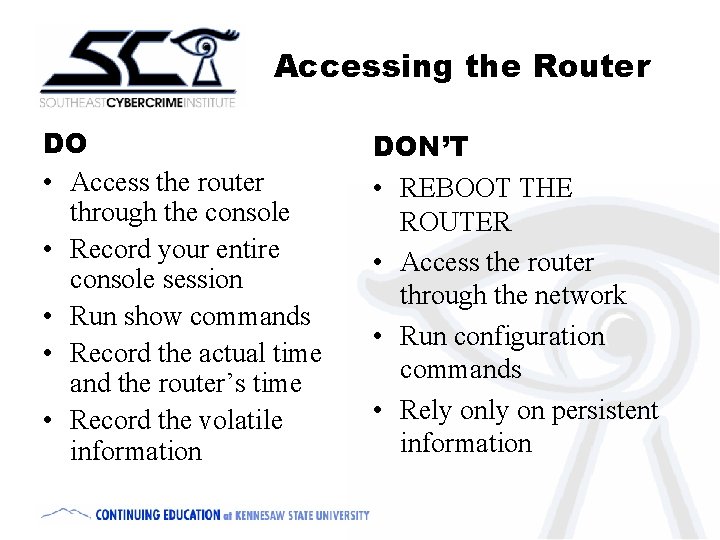
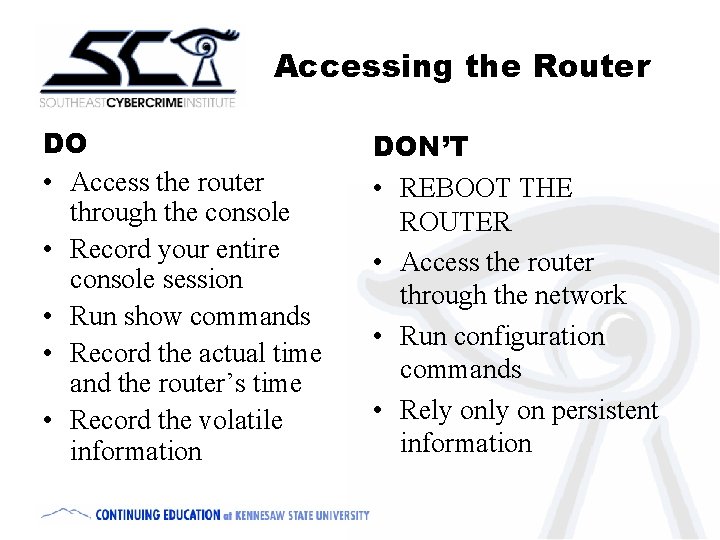
Accessing the Router DO • Access the router through the console • Record your entire console session • Run show commands • Record the actual time and the router’s time • Record the volatile information DON’T • REBOOT THE ROUTER • Access the router through the network • Run configuration commands • Rely on persistent information
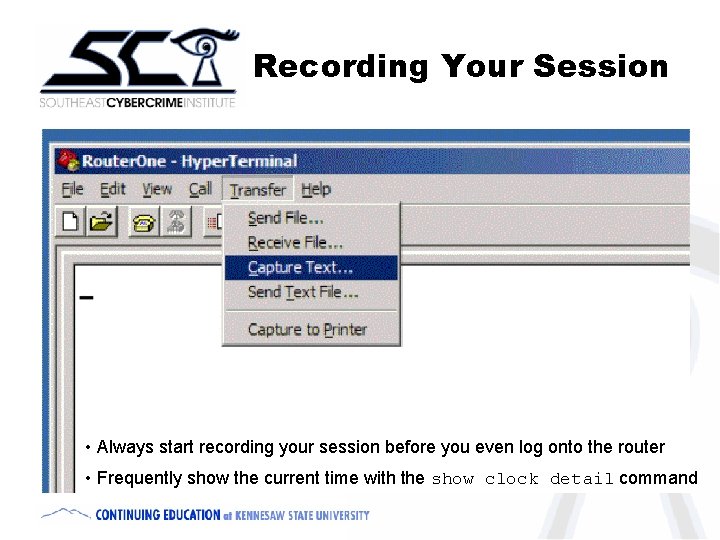
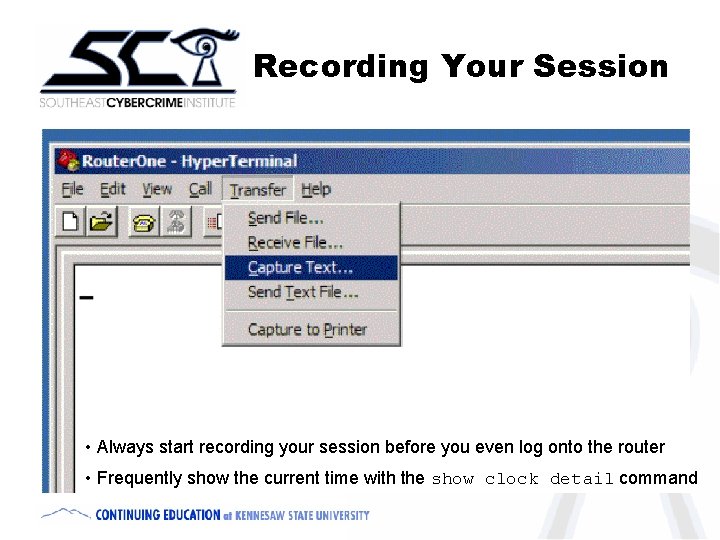
Recording Your Session • Always start recording your session before you even log onto the router • Frequently show the current time with the show clock detail command
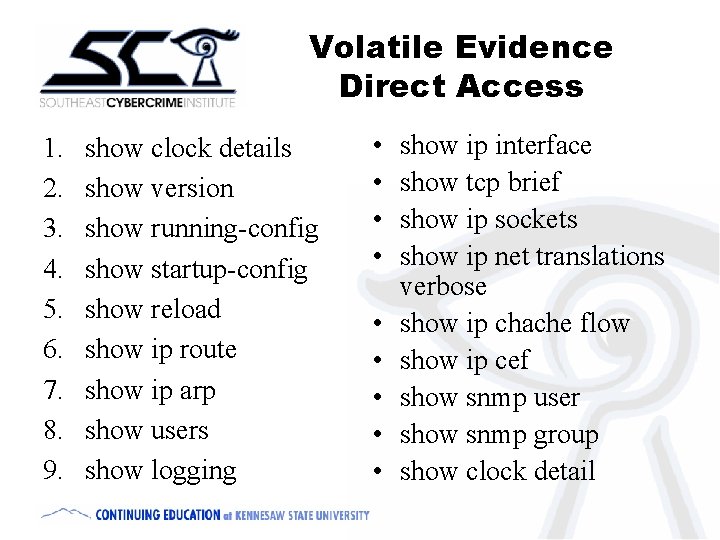
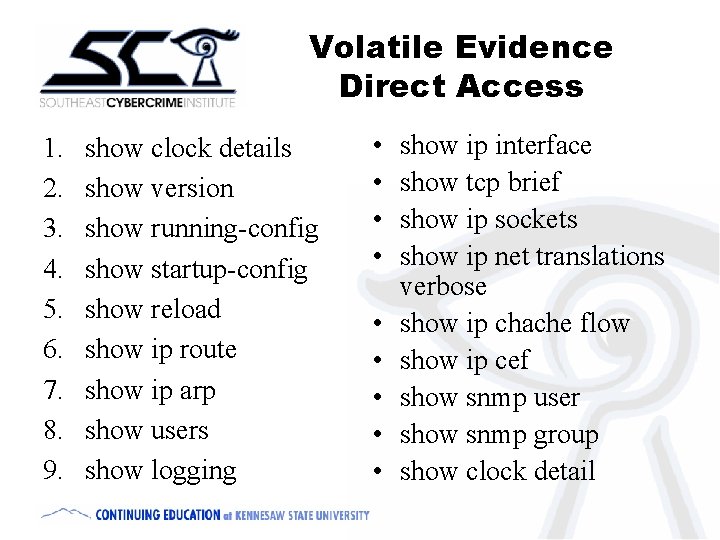
Volatile Evidence Direct Access 1. 2. 3. 4. 5. 6. 7. 8. 9. show clock details show version show running-config show startup-config show reload show ip route show ip arp show users show logging • • • show ip interface show tcp brief show ip sockets show ip net translations verbose show ip chache flow show ip cef show snmp user show snmp group show clock detail
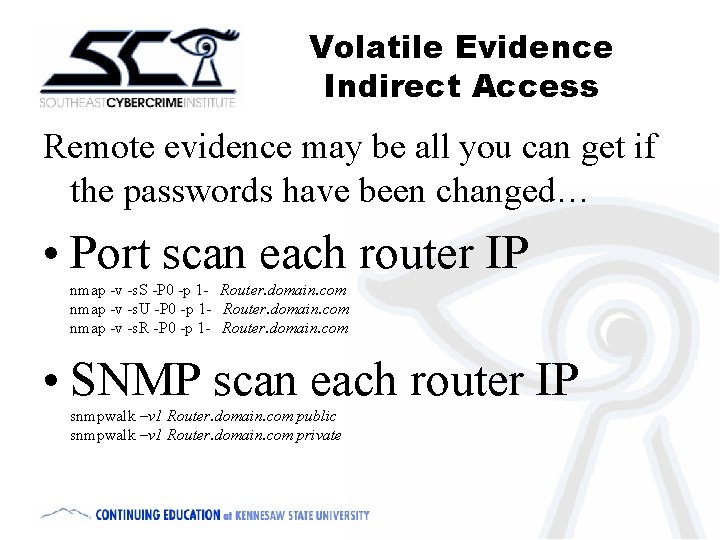
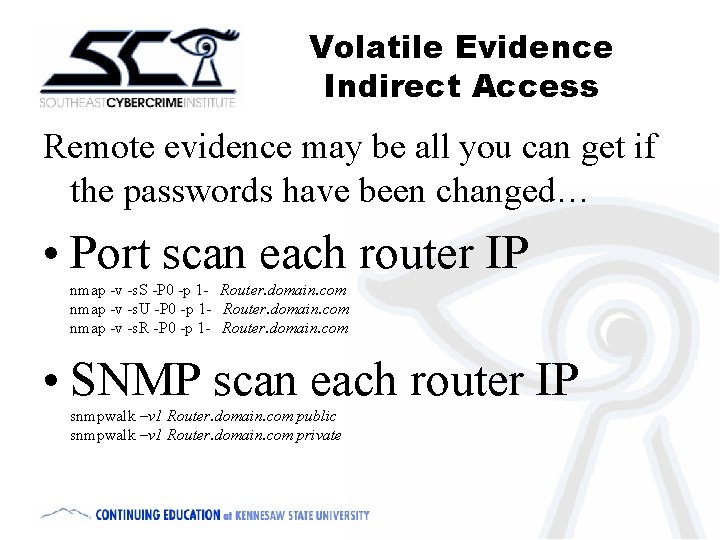
Volatile Evidence Indirect Access Remote evidence may be all you can get if the passwords have been changed… • Port scan each router IP nmap -v -s. S -P 0 -p 1 - Router. domain. com nmap -v -s. U -P 0 -p 1 - Router. domain. com nmap -v -s. R -P 0 -p 1 - Router. domain. com • SNMP scan each router IP snmpwalk –v 1 Router. domain. com public snmpwalk –v 1 Router. domain. com private
Intrusion Analysis • IOS Vulnerabilities • Running v/s Startup configurations • Logging • Timestamps
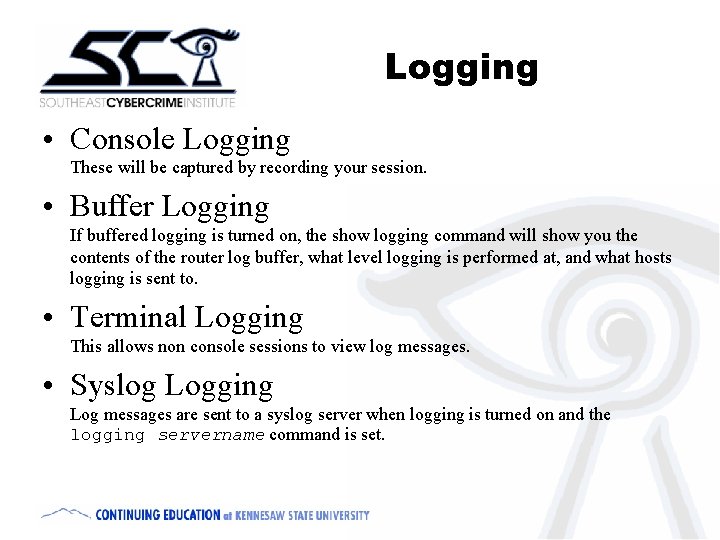
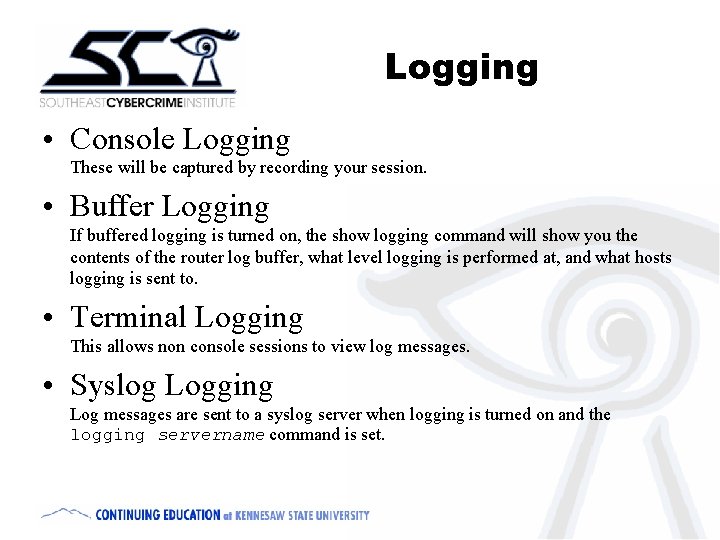
Logging • Console Logging These will be captured by recording your session. • Buffer Logging If buffered logging is turned on, the show logging command will show you the contents of the router log buffer, what level logging is performed at, and what hosts logging is sent to. • Terminal Logging This allows non console sessions to view log messages. • Syslog Logging Log messages are sent to a syslog server when logging is turned on and the logging servername command is set.
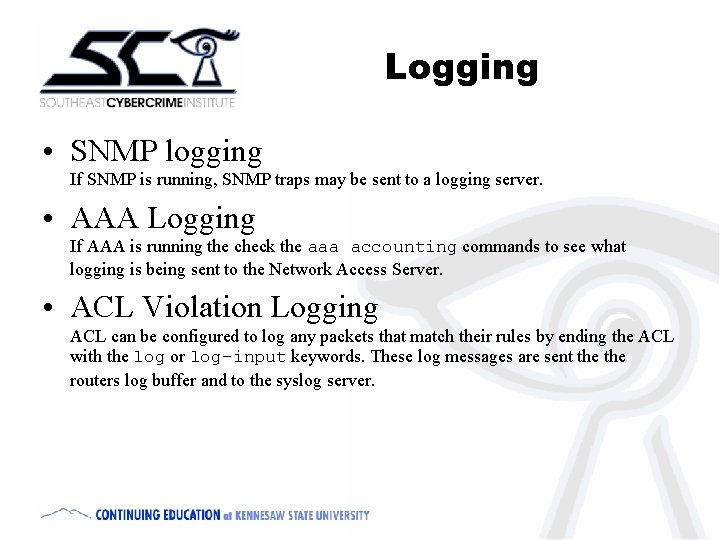
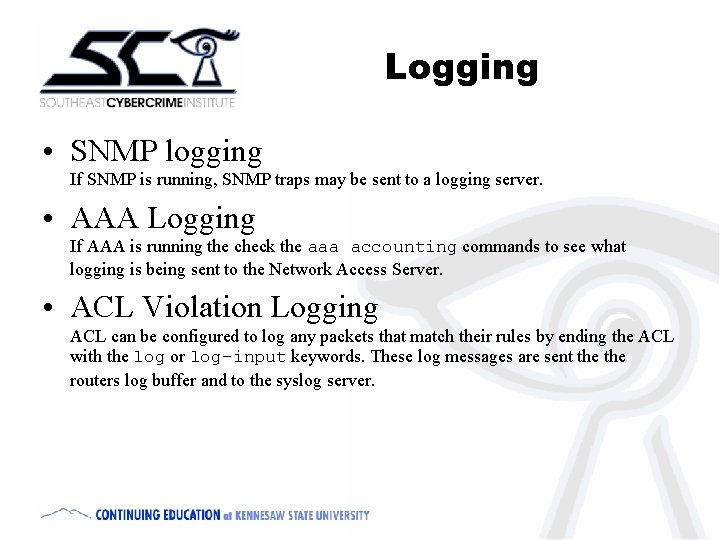
Logging • SNMP logging If SNMP is running, SNMP traps may be sent to a logging server. • AAA Logging If AAA is running the check the aaa accounting commands to see what logging is being sent to the Network Access Server. • ACL Violation Logging ACL can be configured to log any packets that match their rules by ending the ACL with the log or log-input keywords. These log messages are sent the routers log buffer and to the syslog server.
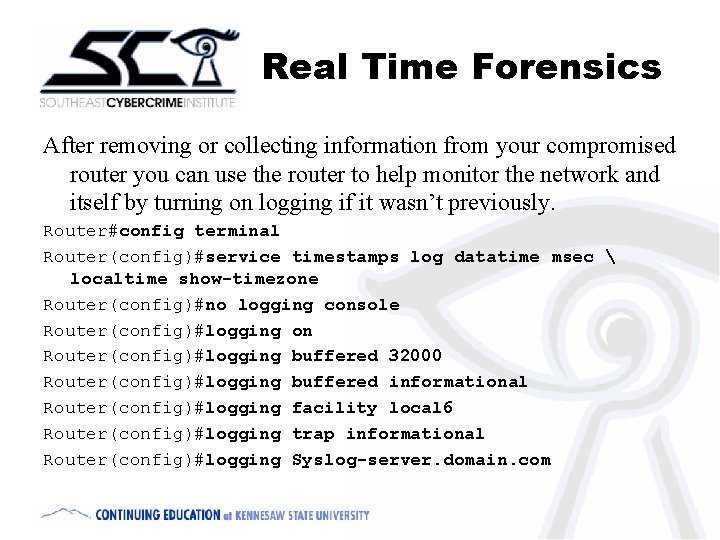
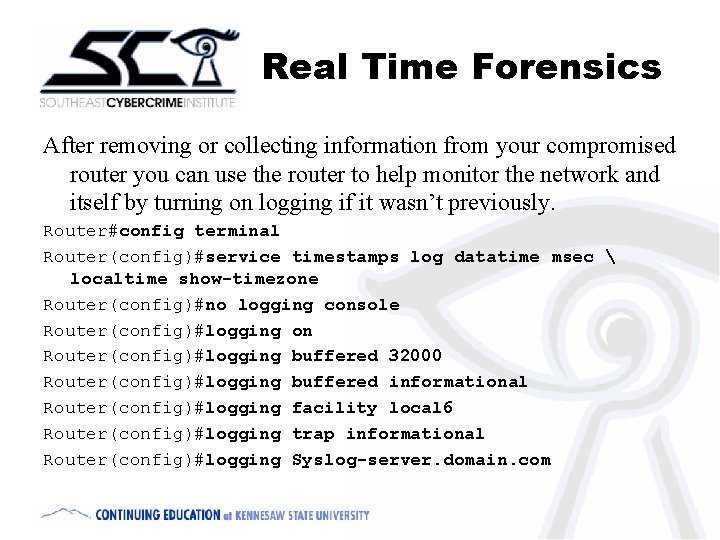
Real Time Forensics After removing or collecting information from your compromised router you can use the router to help monitor the network and itself by turning on logging if it wasn’t previously. Router#config terminal Router(config)#service timestamps log datatime msec localtime show-timezone Router(config)#no logging console Router(config)#logging on Router(config)#logging buffered 32000 Router(config)#logging buffered informational Router(config)#logging facility local 6 Router(config)#logging trap informational Router(config)#logging Syslog-server. domain. com
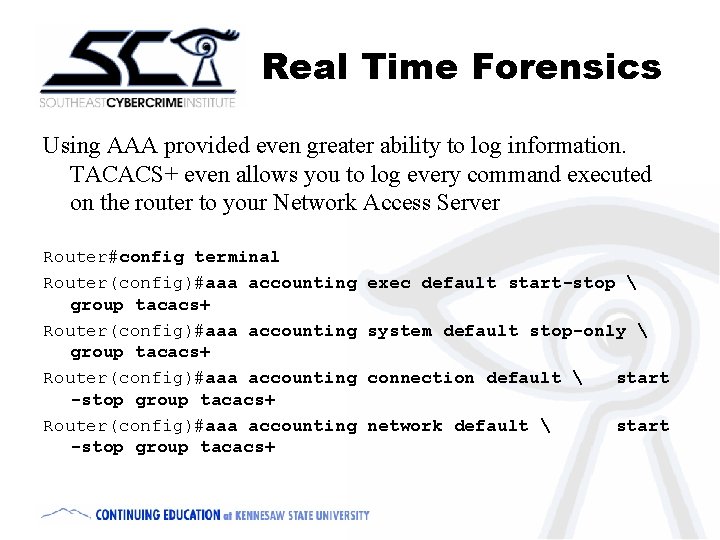
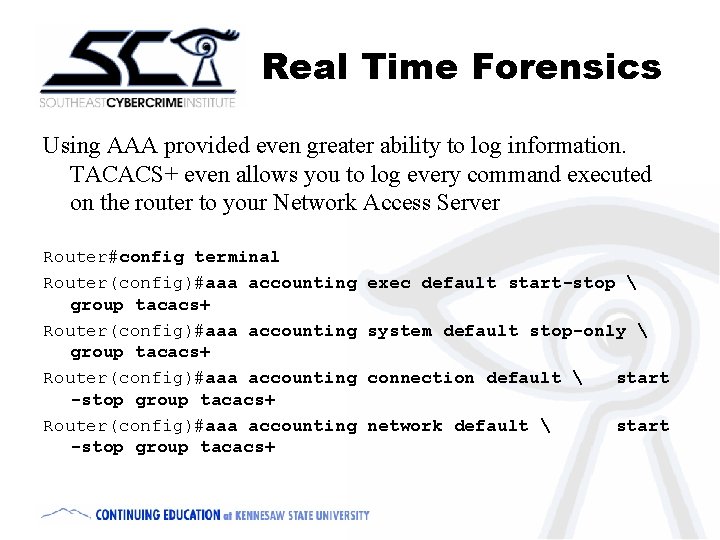
Real Time Forensics Using AAA provided even greater ability to log information. TACACS+ even allows you to log every command executed on the router to your Network Access Server Router#config terminal Router(config)#aaa accounting group tacacs+ Router(config)#aaa accounting -stop group tacacs+ exec default start-stop system default stop-only connection default start network default start
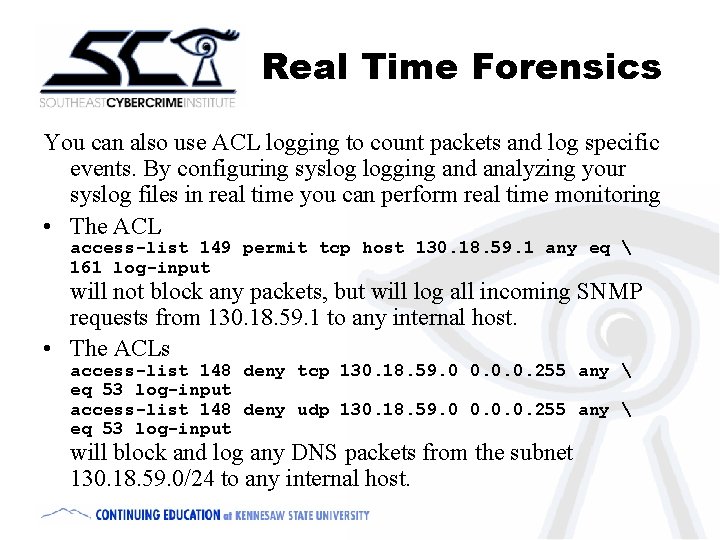
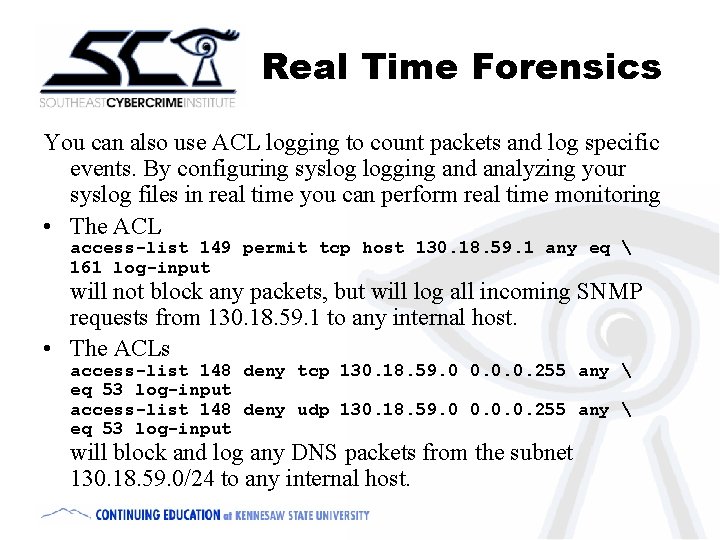
Real Time Forensics You can also use ACL logging to count packets and log specific events. By configuring syslog logging and analyzing your syslog files in real time you can perform real time monitoring • The ACL access-list 149 permit tcp host 130. 18. 59. 1 any eq 161 log-input will not block any packets, but will log all incoming SNMP requests from 130. 18. 59. 1 to any internal host. • The ACLs access-list 148 deny tcp 130. 18. 59. 0 0. 0. 0. 255 any eq 53 log-input access-list 148 deny udp 130. 18. 59. 0 0. 0. 0. 255 any eq 53 log-input will block and log any DNS packets from the subnet 130. 18. 59. 0/24 to any internal host.
Summary • • • Hacking Cisco Routers Router Hardware & Software Router Forensics v/s Traditional Forensics Computer Evidence & Chain of Custody Incident Response Accessing the Router Gathering volatile evidence—internal & external Gathering logging evidence Performing Real Time Network Forensics
Thank you! Thomas Akin takin@kennesaw. edu http: //cybercrime. kennesaw. edu On you conference CD you will find: • A copy of this presentation • A router forensics checklist • A sample Chain of Custody form • A sample Evidence Reciept tag