CISA CYBERSECURITY AND INFRASTRUCTURE SECURITY AGENCY Dave Sonheim
CISA | CYBERSECURITY AND INFRASTRUCTURE SECURITY AGENCY Dave Sonheim Cybersecurity Advisor Region VIII | Colorado, South Dakota, North Dakota Cybersecurity and Infrastructure Security Agency (CISA) DEFEND TODAY SECURE TOMORROW A secure and resilient critical infrastructure for the American People
CISA | CYBERSECURITY AND INFRASTRUCTURE SECURITY AGENCY DAVE SONHEIM Cybersecurity Advisor Region VIII (CO, SD, ND) CISA - Cybersecurity and Infrastructure Security Agency CISA. GOV
CISA. GOV 3
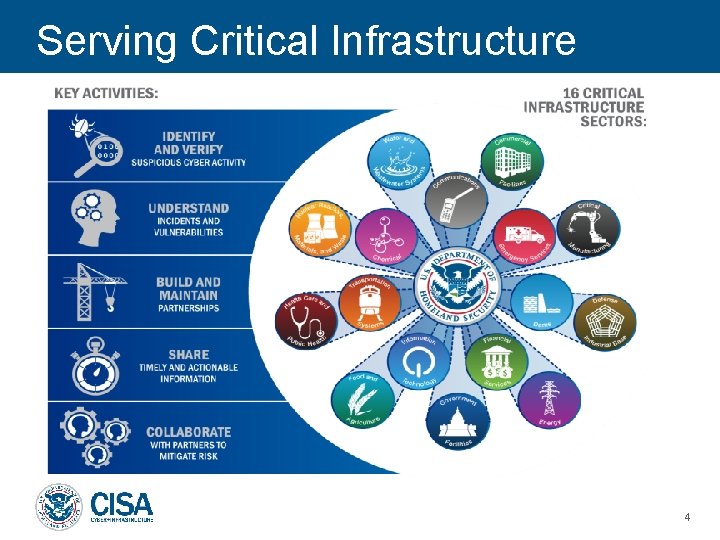
Serving Critical Infrastructure 4
CISA. GOV/Cybersecurity Resource HUB CISA CYBERSECURITY - CISA. GOV site provides a one stop shop for all things Cyber. - Complete list of all CISA issued Activity Alerts - Cyber Incident Reporting Portal access - Cyber Resource HUB *Complete CISA nocost service and resource guide for assessment and vulnerability scanning. https: //www. cisa. gov/cyber-resource-hub 5
NCAS – Subscriptions & Mailing Lists Subscribe to any or all of the National Cyber Awareness system products or feeds by navigating to this link. https: //us-cert. cisa. gov/ncas 6
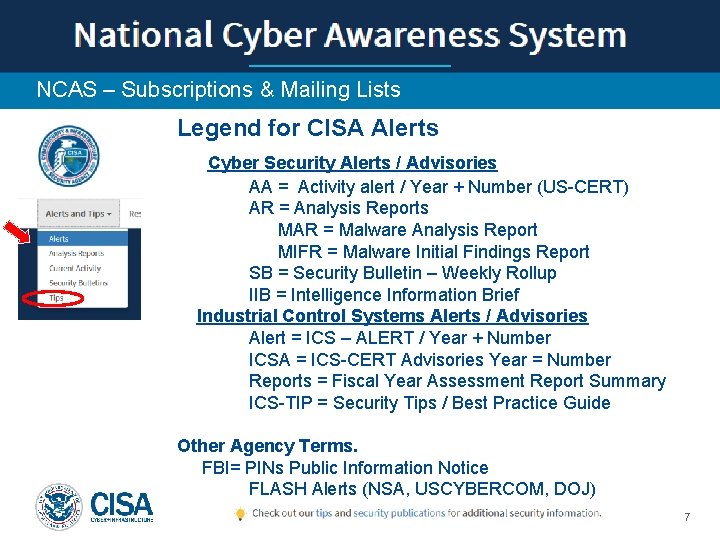
NCAS – Subscriptions & Mailing Lists Legend for CISA Alerts Cyber Security Alerts / Advisories AA = Activity alert / Year + Number (US-CERT) AR = Analysis Reports MAR = Malware Analysis Report MIFR = Malware Initial Findings Report SB = Security Bulletin – Weekly Rollup IIB = Intelligence Information Brief Industrial Control Systems Alerts / Advisories Alert = ICS – ALERT / Year + Number ICSA = ICS-CERT Advisories Year = Number Reports = Fiscal Year Assessment Report Summary ICS-TIP = Security Tips / Best Practice Guide Other Agency Terms. FBI= PINs Public Information Notice FLASH Alerts (NSA, USCYBERCOM, DOJ) 7
Cybersecurity Advisors (CSAs) CSA Mission and Priorities To provide direct coordination, outreach, and regional support in order to protect cyber components essential to the sustainability, preparedness, and protection of the Nation’s Critical Infrastructure and Key Resources (CIKR) and State, Local, Tribal, and Territorial (SLTT) governments. In support of that mission: Cybersecurity Advisors (CSAs): • Assess: Evaluate critical infrastructure cyber risk. • Promote: Encourage leading practices and risk mitigation strategies. • Build: Initiate, develop capacity, and support cyber communities-of-interest and working groups. • Educate: Inform and raise awareness. • Listen: Collect stakeholder requirements. • Coordinate: Bring together incident support and lessons learned. 8
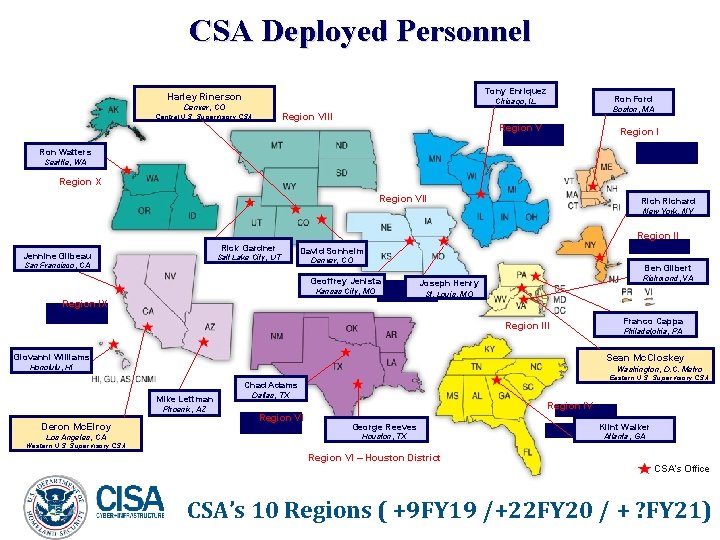
CSA Deployed Personnel Tony Enriquez Harley Rinerson Ron Ford Chicago, IL Denver, CO Region VIII Central U. S. Supervisory CSA Boston, MA Region V Region I Ron Watters Seattle, WA Region X Region VII Richard New York, NY Region II Rick Gardner Jennine Gilbeau Salt Lake City, UT San Francisco, CA David Sonheim Denver, CO Ben Gilbert Geoffrey Jenista Kansas City, MO Region IX Richmond, VA Joseph Henry St. Louis, MO Franco Cappa Region III Philadelphia, PA Giovanni Williams Sean Mc. Closkey Honolulu, HI Washington, D. C. Metro Eastern U. S. Supervisory CSA Chad Adams Mike Lettman Phoenix, AZ Deron Mc. Elroy Los Angeles, CA Dallas, TX Region IV Region VI George Reeves Houston, TX Klint Walker Region IV Atlanta, GA Western U. S. Supervisory CSA Region VI – Houston District CSA’s Office CSA’s 10 Regions ( +9 FY 19 /+22 FY 20 / + ? FY 21)

CISA Cybersecurity Offerings Local CSA Provided • CISA HQ Response Assistance • • Remote / On-Site Assistance Malware Analysis Hunt and Incident Response Teams Incident Coordination • Cybersecurity Advisors • • • Assessments Working group collaboration Resiliency Workshops Best Practices private-public Incident assistance coordination • Protective Security Advisors • Physical Security Assessments • Incident liaisons between government and private sector for CI protection • Support for National Special Security Events 10
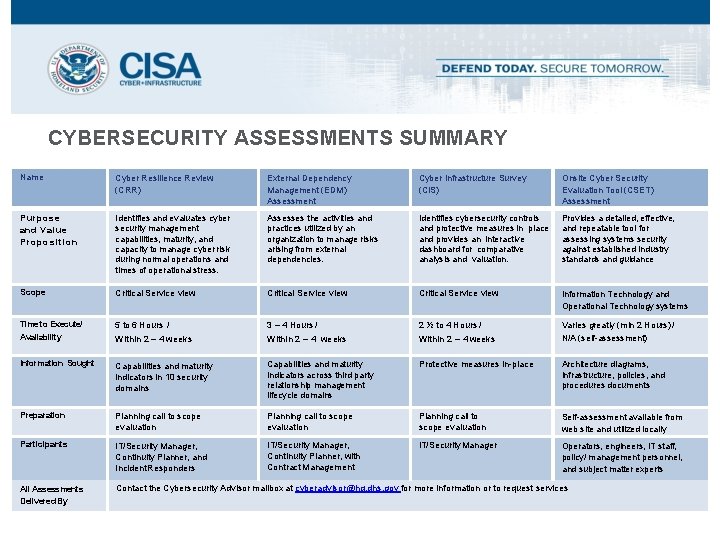
CYBERSECURITY ASSESSMENTS SUMMARY Name Cyber Resilience Review (CRR) External Dependency Management (EDM) Assessment Cyber Infrastructure Survey (CIS) Onsite Cyber Security Evaluation Tool (CSET) Assessment Purpose and Value Proposition Identifies and evaluates cyber security management capabilities, maturity, and capacity to manage cyber risk during normal operations and times of operational stress. Assesses the activities and practices utilized by an organization to manage risks arising from external dependencies. Identifies cybersecurity controls and protective measures in place and provides an interactive dashboard for comparative analysis and valuation. Provides a detailed, effective, and repeatable tool for assessing systems security against established industry standards and guidance Scope Critical Service view Information Technology and Operational Technology systems Time to Execute/ Availability 5 to 6 Hours / 3 – 4 Hours / 2 ½ to 4 Hours / Within 2 – 4 weeks Varies greatly (min 2 Hours) / N/A (self-assessment) Information Sought Capabilities and maturity indicators in 10 security domains Capabilities and maturity indicators across third party relationship management lifecycle domains Protective measures in-place Architecture diagrams, infrastructure, policies, and procedures documents Preparation Planning call to scope evaluation Self-assessment available from web site and utilized locally Participants IT/Security Manager, Continuity Planner, and Incident Responders IT/Security Manager, Continuity Planner, with Contract Management IT/Security Manager Operators, engineers, IT staff, policy/ management personnel, and subject matter experts All Assessments Delivered By Contact the Cybersecurity Advisor mailbox at cyberadvisor@hq. dhs. gov for more information or to request services

Cyber Resilience Review (CRR) CRR Assessment (CERT-RMM) § Purpose: The CRR is an assessment intended to evaluate an organization’s operational resilience and cybersecurity practices of its critical service. § Delivery: The CRR can be § CSA Facilitated § Self-Assessment CRR Self-Assessment Package is available on the C-Cubed Voluntary Program website. § Helps public and private sector partners understand measure cyber security capabilities as they relate to operational resilience and cyber risk § Based on the CERT ® Resilience Management Model (CERT® RMM) The CRR provides organizations with a no-cost method to assess their cybersecurity postures and measure against the NIST CSF. 12
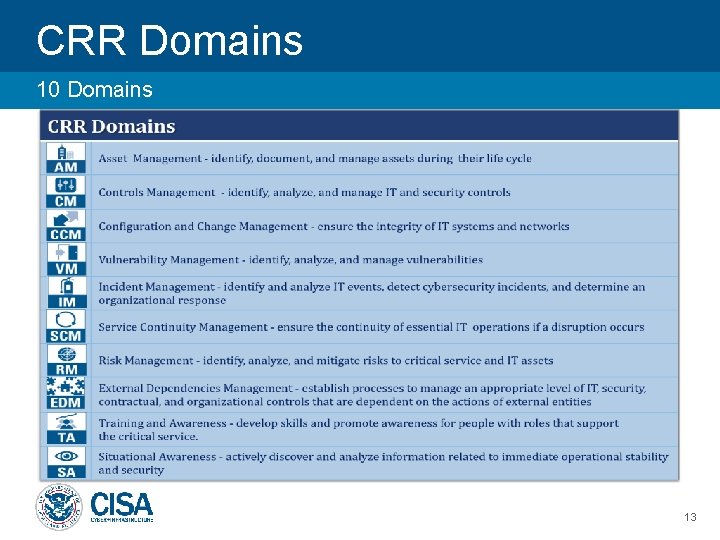
CRR Domains 10 Domains 13
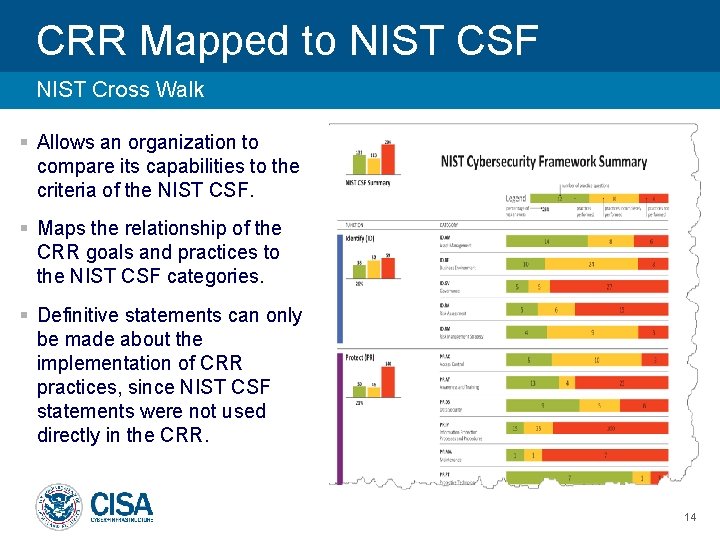
CRR Mapped to NIST CSF NIST Cross Walk § Allows an organization to compare its capabilities to the criteria of the NIST CSF. § Maps the relationship of the CRR goals and practices to the NIST CSF categories. § Definitive statements can only be made about the implementation of CRR practices, since NIST CSF statements were not used directly in the CRR. 14
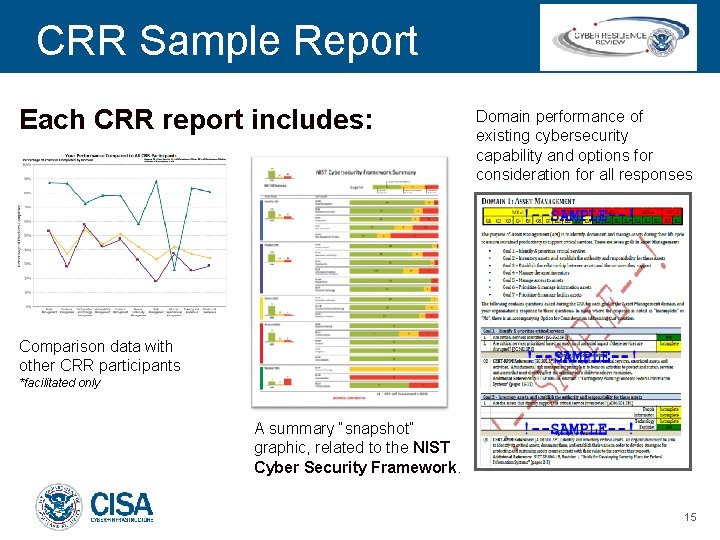
CRR Sample Report Each CRR report includes: Domain performance of existing cybersecurity capability and options for consideration for all responses Comparison data with other CRR participants *facilitated only A summary “snapshot” graphic, related to the NIST Cyber Security Framework. 15
External Dependencies Management EDM Assessment – Supply Chain & 3 rd Party Risk Management Supply Chain & 3 rd Party Risk management assessment tool Information and communication technology supply chain risk by assessing activities and practices No cost, voluntary, nontechnical assessment 16
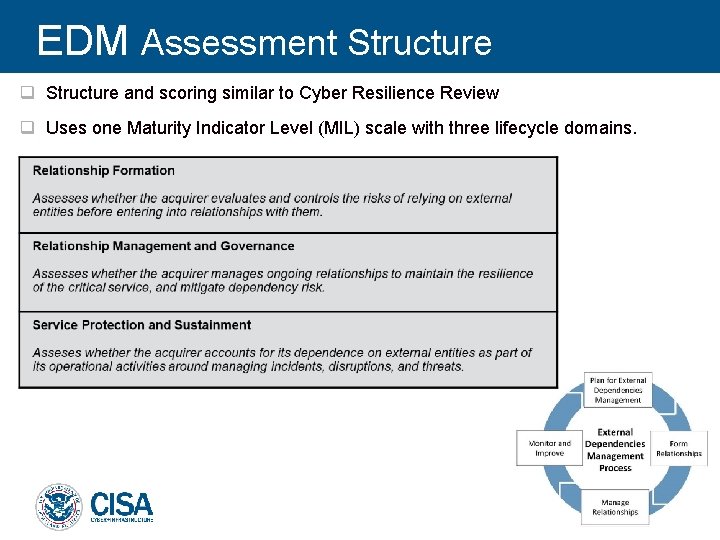
EDM Assessment Structure q Structure and scoring similar to Cyber Resilience Review q Uses one Maturity Indicator Level (MIL) scale with three lifecycle domains. 17
EDM Assessment Report Performance Summary 18

Cyber Infrastructure Survey (CIS) CIS Assessment 19
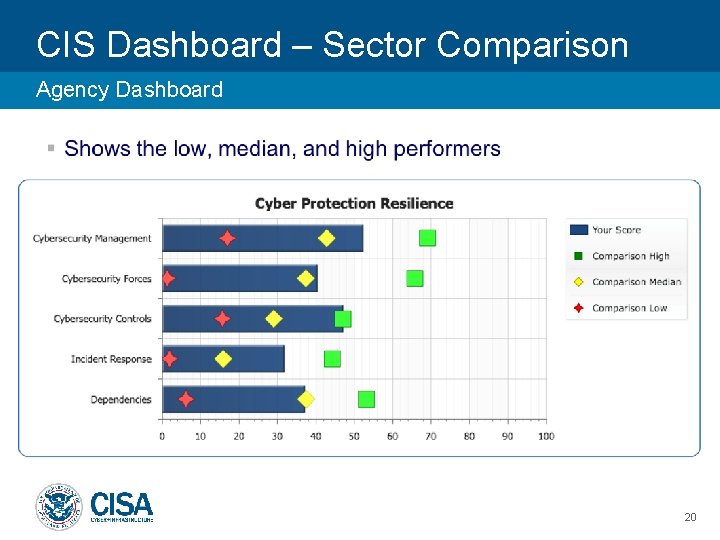
CIS Dashboard – Sector Comparison Agency Dashboard 20
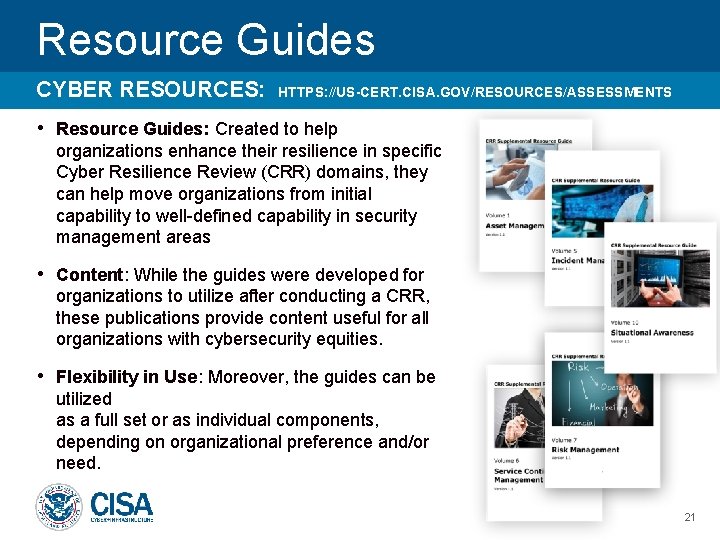
Resource Guides CYBER RESOURCES: HTTPS: //US-CERT. CISA. GOV/RESOURCES/ASSESSMENTS • Resource Guides: Created to help organizations enhance their resilience in specific Cyber Resilience Review (CRR) domains, they can help move organizations from initial capability to well-defined capability in security management areas • Content: While the guides were developed for organizations to utilize after conducting a CRR, these publications provide content useful for all organizations with cybersecurity equities. • Flexibility in Use: Moreover, the guides can be utilized as a full set or as individual components, depending on organizational preference and/or need. 21
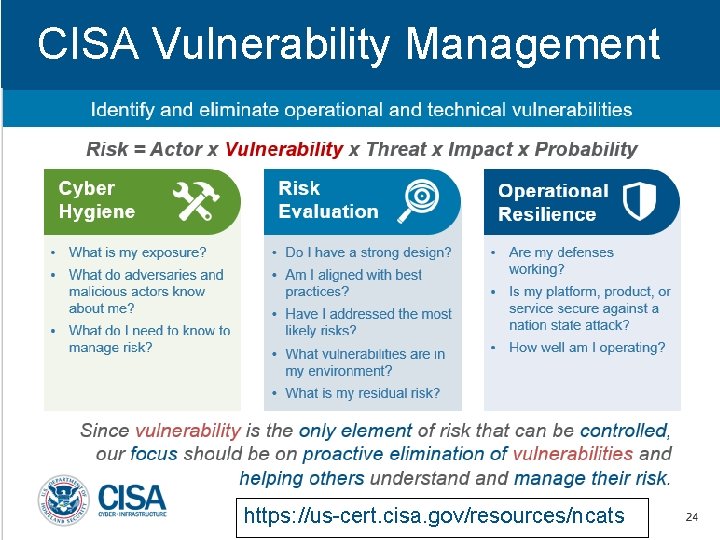
CISA Vulnerability Management https: //us-cert. cisa. gov/resources/ncats
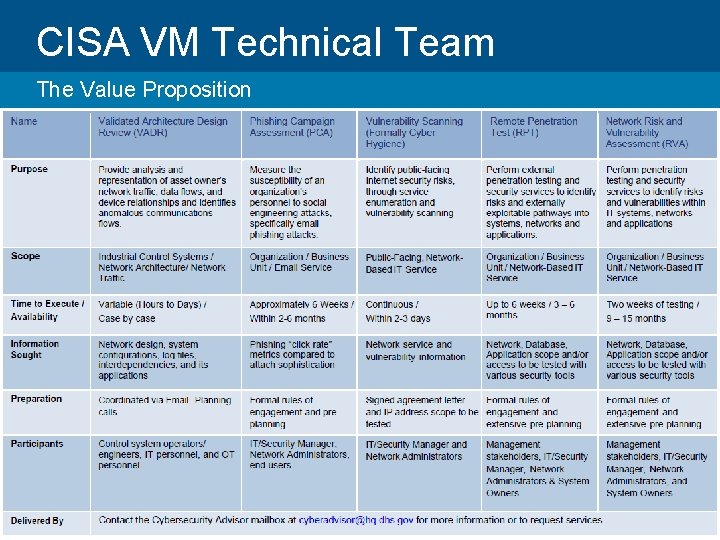
CISA VM Technical Team The Value Proposition 23
Cy. Hy Cyber Hygiene Scanning System & Application Vulnerability Scanning CRITICAL HIGH MEDIUM § Automated scanning of Internet accessible systems (Top 1000 Ports / NMAP & NESUS) § Helps individual customer understand their exposure § Informs national risk management efforts § Weekly report card that include current scan results, historic trends, and result comparisons to the national average LOW NONE INACTIVE § Federal agencies must mitigate critical vulnerabilities within 30 days of detection § 3 -4 weeks wait time to get request processed § Unlimited capacity of subscribers 25
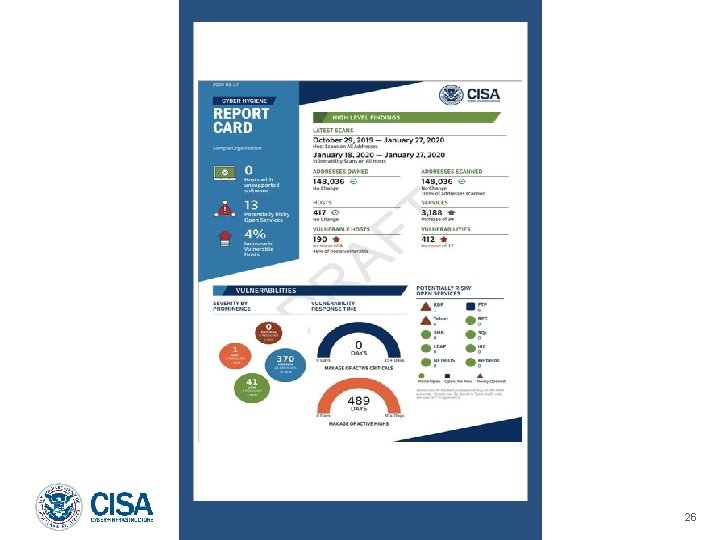
26
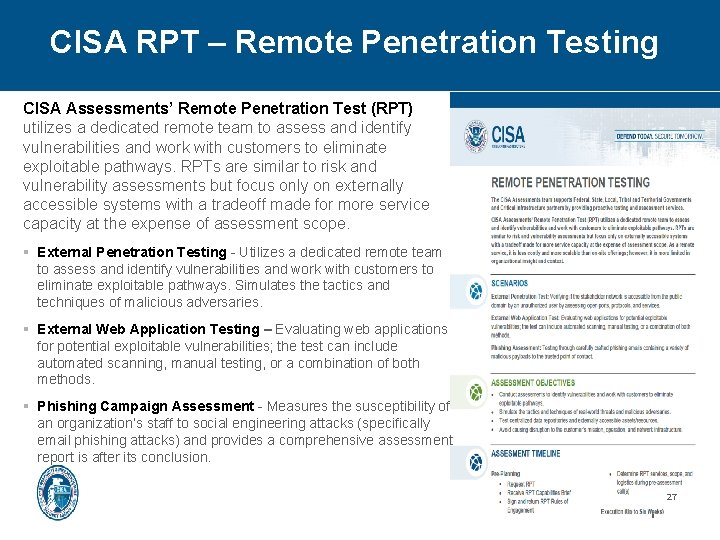
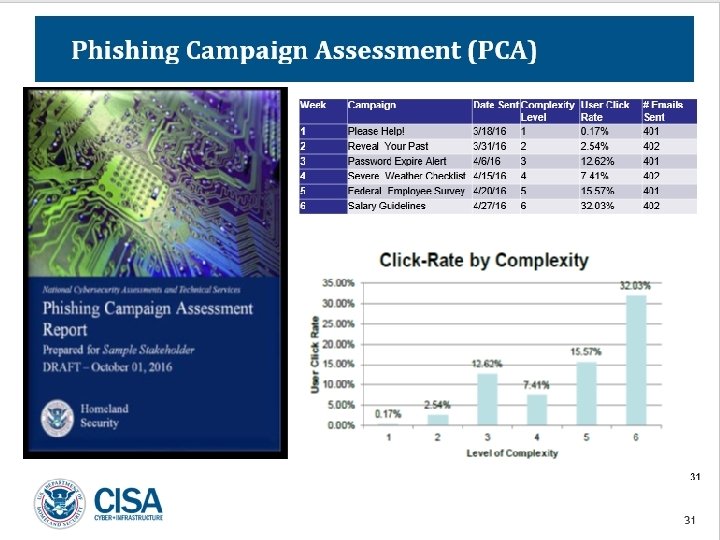
CISA RPT – Remote Penetration Testing CISA Assessments’ Remote Penetration Test (RPT) utilizes a dedicated remote team to assess and identify vulnerabilities and work with customers to eliminate exploitable pathways. RPTs are similar to risk and vulnerability assessments but focus only on externally accessible systems with a tradeoff made for more service capacity at the expense of assessment scope. § External Penetration Testing - Utilizes a dedicated remote team to assess and identify vulnerabilities and work with customers to eliminate exploitable pathways. Simulates the tactics and techniques of malicious adversaries. § External Web Application Testing – Evaluating web applications for potential exploitable vulnerabilities; the test can include automated scanning, manual testing, or a combination of both methods. § Phishing Campaign Assessment - Measures the susceptibility of an organization’s staff to social engineering attacks (specifically email phishing attacks) and provides a comprehensive assessment report is after its conclusion. Presenter’s Name December 19, 2021 27
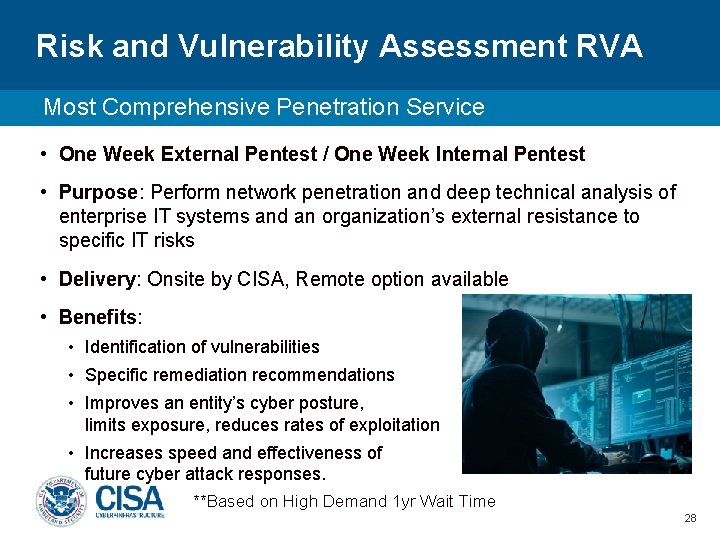
Risk and Vulnerability Assessment RVA Most Comprehensive Penetration Service • One Week External Pentest / One Week Internal Pentest • Purpose: Perform network penetration and deep technical analysis of enterprise IT systems and an organization’s external resistance to specific IT risks • Delivery: Onsite by CISA, Remote option available • Benefits: • Identification of vulnerabilities • Specific remediation recommendations • Improves an entity’s cyber posture, limits exposure, reduces rates of exploitation • Increases speed and effectiveness of future cyber attack responses. § **Based on High Demand 1 yr Wait Time 28
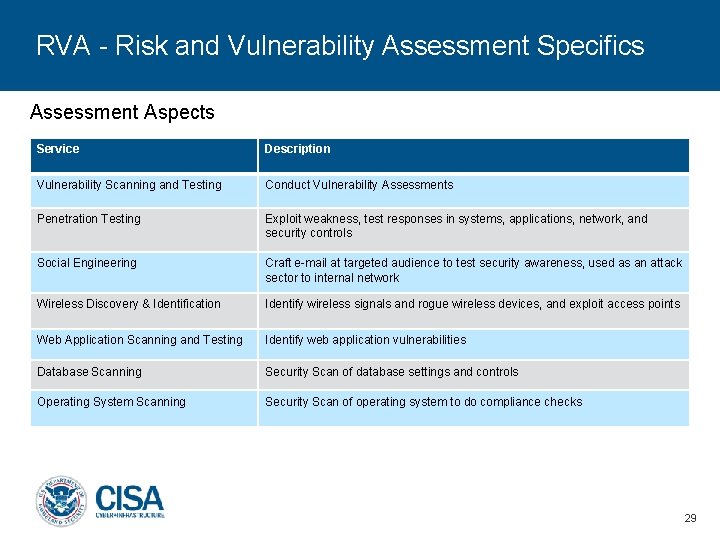
RVA - Risk and Vulnerability Assessment Specifics Assessment Aspects Service Description Vulnerability Scanning and Testing Conduct Vulnerability Assessments Penetration Testing Exploit weakness, test responses in systems, applications, network, and security controls Social Engineering Craft e-mail at targeted audience to test security awareness, used as an attack sector to internal network Wireless Discovery & Identification Identify wireless signals and rogue wireless devices, and exploit access points Web Application Scanning and Testing Identify web application vulnerabilities Database Scanning Security Scan of database settings and controls Operating System Scanning Security Scan of operating system to do compliance checks 29
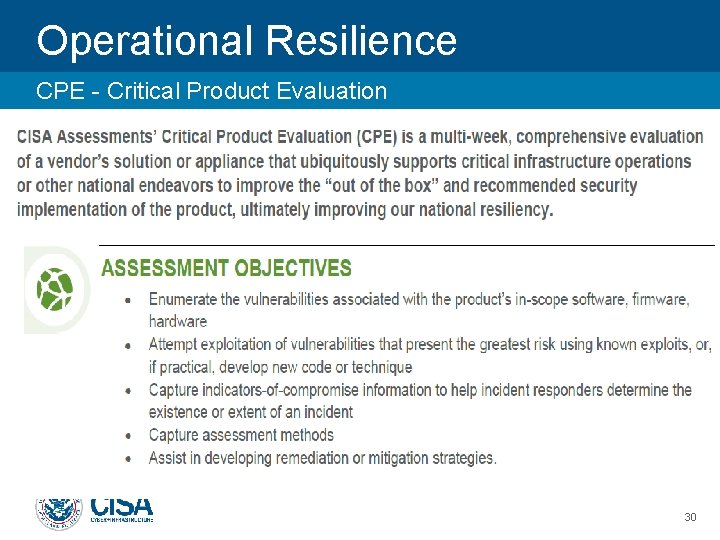
Operational Resilience CPE - Critical Product Evaluation 30
- Provides 24 x 7 dynamic analyses of malicious code. - Experts will detail recommendations for malware removal and recovery activities.
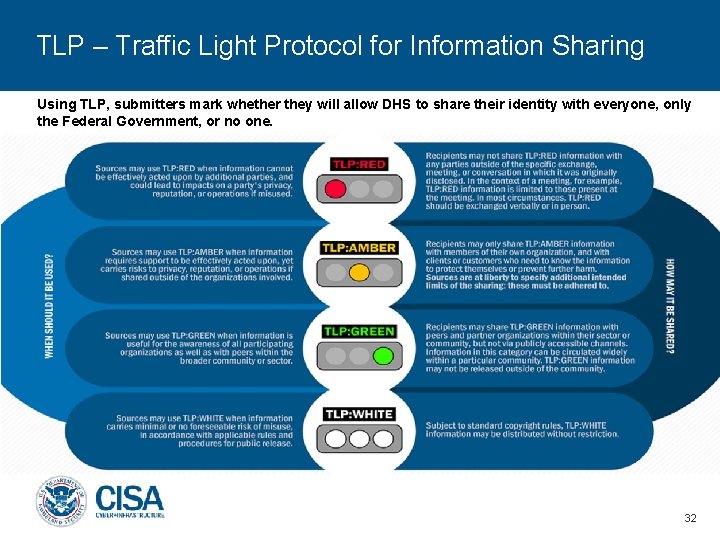
TLP – Traffic Light Protocol for Information Sharing Using TLP, submitters mark whether they will allow DHS to share their identity with everyone, only the Federal Government, or no one. 32
Automated Indicator Sharing • Automated Indicator Sharing (AIS): Rapid and wide sharing of machine-readable cyber threat indicators and defensive measures at machine-speed for network defense purposes • AIS is about volume and velocity of sharing indicators, not human validation. 33
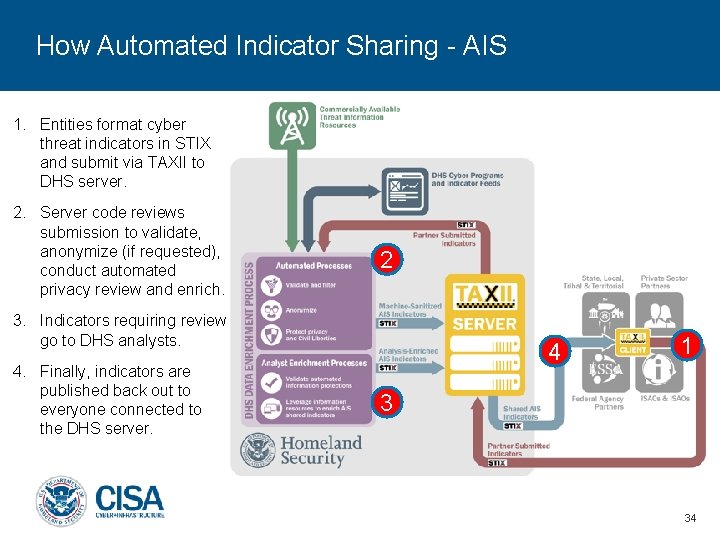
How Automated Indicator Sharing - AIS 1. Entities format cyber threat indicators in STIX and submit via TAXII to DHS server. 2. Server code reviews submission to validate, anonymize (if requested), conduct automated privacy review and enrich. 2 3. Indicators requiring review go to DHS analysts. 4. Finally, indicators are published back out to everyone connected to the DHS server. 4 1 3 34

Latest Cyber Threats / Alerts TLP WHITE 8/27/2020 35
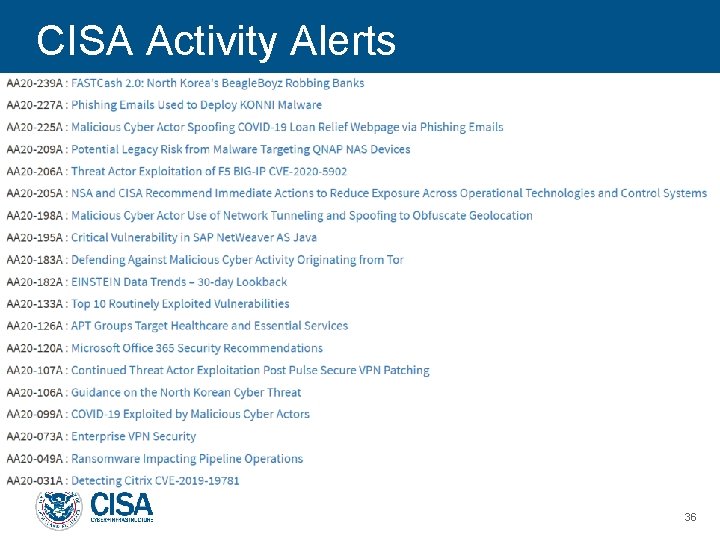
CISA Activity Alerts 36
CISA Incident Reporting/Malware Analysis CISA Integrated Operations Coordination Center – CISA Central 24 x 7 contact number: 1 -888 -282 -0870 Where/How/When to Report: CISA. GOV - Yellow “Report Cyber Issue” • If there is a suspected or confirmed cyber attack or incident that: • Affects core government or critical infrastructure functions; • Results in the loss of data, system availability; or control of systems; • Indicates malicious software is present on critical systems 37
CISA Region VIII

- Slides: 39