CISA CYBERSECURITY AND INFRASTRUCTURE SECURITY AGENCY CYBER ESSENTIALS
CISA | CYBERSECURITY AND INFRASTRUCTURE SECURITY AGENCY CYBER ESSENTIALS Building Cybersecurity Resilience Into Your Organization R. S. Richard Jr. , CISM, CCISO Cybersecurity Advisor, Region II (NY, NJ, PR, VI) Cybersecurity Advisor Program Cybersecurity and Infrastructure Security Agency
Cybersecurity Advisor Program CISA mission: Lead the collaborative national effort to strengthen the security and resilience of America’s critical infrastructure In support of that mission: Cybersecurity Advisors (CSAs): • Assess: Evaluate critical infrastructure cyber risk. • Promote: Encourage best practices and risk mitigation strategies. • Build: Initiate, develop capacity, and support cyber communities-ofinterest and working groups. • Educate: Inform and raise awareness. • Listen: Collect stakeholder requirements. • Coordinate: Bring together incident support and lessons learned.
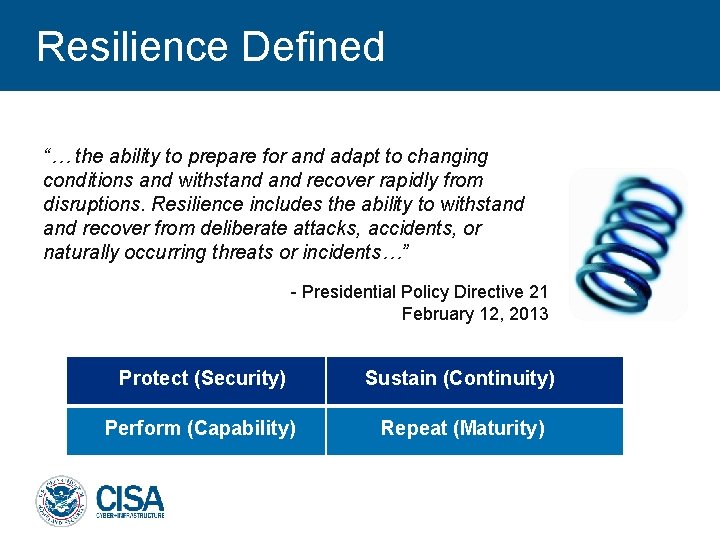
Resilience Defined “… the ability to prepare for and adapt to changing conditions and withstand recover rapidly from disruptions. Resilience includes the ability to withstand recover from deliberate attacks, accidents, or naturally occurring threats or incidents…” - Presidential Policy Directive 21 February 12, 2013 Protect (Security) Sustain (Continuity) Perform (Capability) Repeat (Maturity)
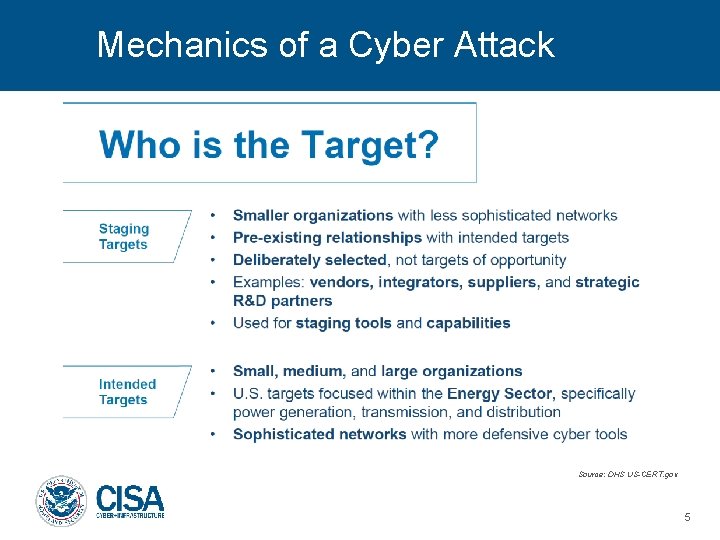
Mechanics of a Cyber Attack Source: DHS US-CERT. gov 5
Overview o The Cyber Essentials is a new national initiative to reach small government agencies and small businesses, particularly those that have limited resources and that have not been part of the national cyber dialogue. o As the name implies, the initiative will focus on the very basic steps – that is, what organizations need to do to get started on the road to cyber resilience. o The Cyber Essentials are the starting point for leaders and their organizations to get into the mindset of understanding and addressing cyber risks like other operational risks. 6
Why Cyber Essentials Are Needed o Cyber attackers are becoming more indiscriminate in their choice of targets, they are finding a wider range of victims – including many small or medium-size organizations that are less prepared to protect their own networks. o If you aren’t a large business, it’s easy to think you’re less-attractive as a target to bad actors, “I’m just a small family business. They don’t know about me, much less care about me. I must be safe. ” o The result of this false sense of security: A lack of awareness of the risks, of how to prepare for them, and how to respond. o Where does that leave us? With teachers who can’t teach because ransomware has made their lesson plans inaccessible. With sheriffs who can’t respond to 9 -1 -1 calls because malware crashed their dispatch servers. With small business owners losing the trust of their customers because phishing attacks have resulted in stolen credit card information. 7
Intended Audience for Cyber Essentials o The Cyber Essentials can be adopted by any organization, but are designed specifically for small business owners and “small of the small” local government entities; such as school districts, police departments and other public service providers. o Often, these are organizations in which, because of their size and limited resources, the job of managing IT is left to someone for whom IT is not their primary day job – or even area of expertise. 8
Features o The Cyber Essentials are a set of easy to adopt and understand cybersecurity practices that together constitute “the basics. ” They are CISA’s answer to the question we hear often from stakeholders - “Where do I start? ” o The Cyber Essentials are written for those with limited or no knowledge of cybersecurity practice or terminology but who nevertheless are responsible for safeguarding their organizations. o The Cyber Essentials will take a holistic risk-management approach from a leadership-driven perspective and encourage organizations to approach cyber risks as they would other operational risks. 9
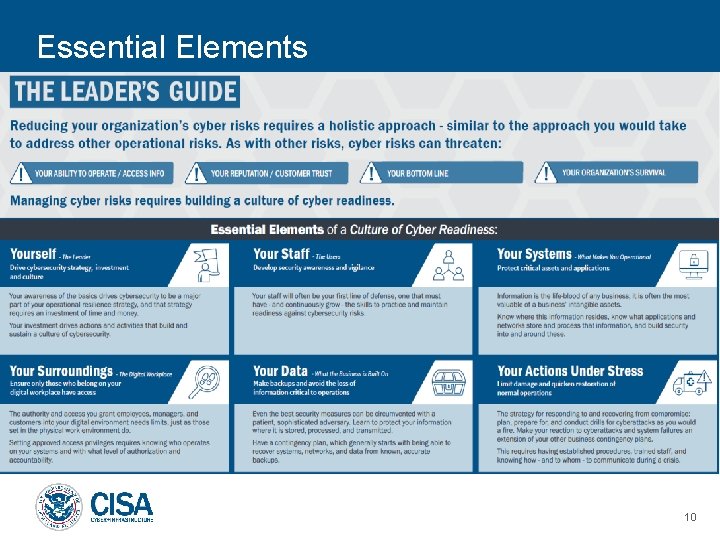
Essential Elements 10
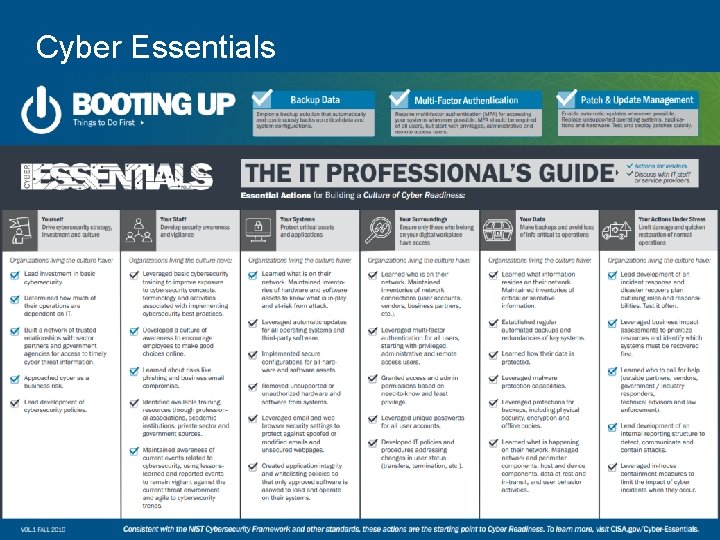
Cyber Essentials 11
Essential Elements: Practice 1 12
Drive Strategy, Investment, and Culture o Cyber should be approached as a business risk. o Look into your organizations’ operations to learn how much you are dependent on IT. o Lead investment into basic cybersecurity. o Leverage sector partners and government agencies to build a network of trusted relationships to better collaborate and quickly access cyber threat information. 13
Essential Elements: Practice 2 14
Develop Security Awareness and Vigilance o Learn what training resources are available through professional associations, academic institutions, private sector and government sources. o Develop a culture of awareness to encourage employees to make better choices online. o Always uphold cybersecurity policies and continuously look for ways to reinforce these policies. o Take advantage of available training resources to educate employees on recognizing and responding to cyber threats. 15
Essential Elements: Practice 3 16
Protect Critical Assets and Applications o Understand what is on you network to create an inventory of all your hardware and software assets. o Safeguard your network by removing unsupported or unauthorized hardware and software from systems. o Implement secure configurations for all hardware and software assets. o Leverage automatic updates for all operating systems and third-party software. PATCH YOUR SYSTEMS o Use email and web browser security settings to protect against spoofed or modified emails, and unsecured webpages. 17
Essential Elements: Practice 4 18
Ensure Access Control of Digital Workspace o Identify who is on your network and create an inventory of all your network connections (user accounts, vendors, business partners, etc. ). o Create a culture focused on access and admin permissions based on need-to-know and least privileged. o Foster the development of IT policies and procedures addressing changes in user status (transfers, termination, etc. ). o Leverage multiple forms of authentication to gain admin privileges and remote access. o Enforce the use of unique passwords for all user accounts. 19
Essential Elements: Practice 5 20
Make Backups and Avoid Loss of Critical Info o Learn what information resides on your network. Inventory critical or sensitive information. o Establish regular automated backups and redundancies of key systems. TEST YOUR BACKUPS o Be aware of what is happening on your network. Manage network and perimeter components, host and device components, data at rest and in transit, and user behavior and activities. o Understand how your data is protected. o Protect your backups with physical security, encryption and offline copies. o Learn ways in which you can protect yourself from malware. 21
Essential Elements: Practice 6 22
Limit Damage and Quicken Restoration of Ops o Identify who to call for help (e. g. , outside partners, vendors, government/industry responders, technical advisors and law enforcement). o Spearhead the development of incident response and disaster recovery plans outlining roles and responsibilities. Test these plans often. o Lead the development of internal reporting structures to detect, communicate, and contain attacks. o Prioritize your resources and identify which systems must be recovered first by conducting business impact assessments. 23
Booting Up: Things To Do First Even before your organization has begun to adopt a Culture of Cyber Readiness, there are things you can begin doing today to make your organization more prepared against cyber risks: o Backup Data Ø Employ a backup solution that automatically and continuously backs up critical data and system configurations. Test those backups!! o Multi-Factor Authentication Ø Require multi-factor authentication (MFA) for accessing your systems whenever possible. Ø MFA should be required of all users, but start with privileged, administrative, and remote access users. o Patch &Update Management Ø Enable automatic updates whenever possible. Ø Replace unsupported operating systems, applications and hardware. Ø Test and deploy patches quickly. 24
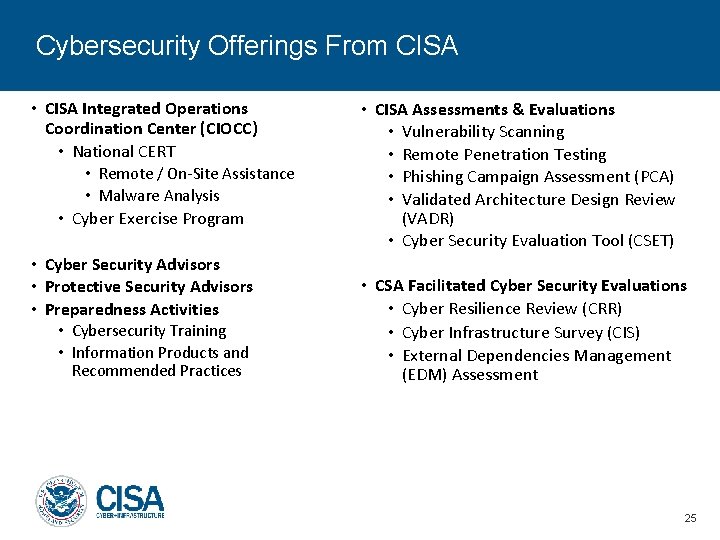
Cybersecurity Offerings From CISA • CISA Integrated Operations Coordination Center (CIOCC) • National CERT • Remote / On-Site Assistance • Malware Analysis • Cyber Exercise Program • Cyber Security Advisors • Protective Security Advisors • Preparedness Activities • Cybersecurity Training • Information Products and Recommended Practices • CISA Assessments & Evaluations • Vulnerability Scanning • Remote Penetration Testing • Phishing Campaign Assessment (PCA) • Validated Architecture Design Review (VADR) • Cyber Security Evaluation Tool (CSET) • CSA Facilitated Cyber Security Evaluations • Cyber Resilience Review (CRR) • Cyber Infrastructure Survey (CIS) • External Dependencies Management (EDM) Assessment 25

STOP. THINK. CONNECT. for User Awareness https: //www. dhs. gov/stopthinkconnect 26
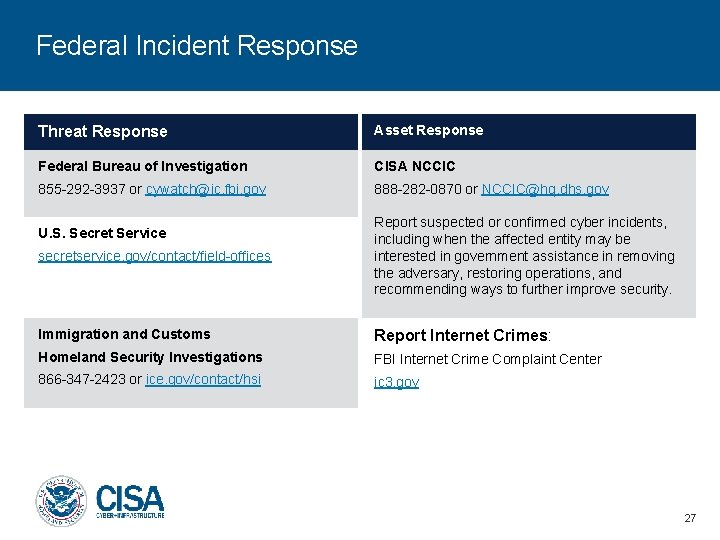
Federal Incident Response Threat Response Asset Response Federal Bureau of Investigation CISA NCCIC 855 -292 -3937 or cywatch@ic. fbi. gov 888 -282 -0870 or NCCIC@hq. dhs. gov secretservice. gov/contact/field-offices Report suspected or confirmed cyber incidents, including when the affected entity may be interested in government assistance in removing the adversary, restoring operations, and recommending ways to further improve security. Immigration and Customs Report Internet Crimes: Homeland Security Investigations FBI Internet Crime Complaint Center 866 -347 -2423 or ice. gov/contact/hsi ic 3. gov U. S. Secret Service 27
CISA Contact Information R. S. Richard Jr. Cyber Security Advisor, Region II Cybersecurity & Infrastructure Security Agency Email: richard@hq. dhs. gov Mobile: (631) 241 -3662
- Slides: 28