CIS 5371 Cryptography 8 Asymmetric encryption 1 Public
CIS 5371 Cryptography 8. Asymmetric encryption- 1
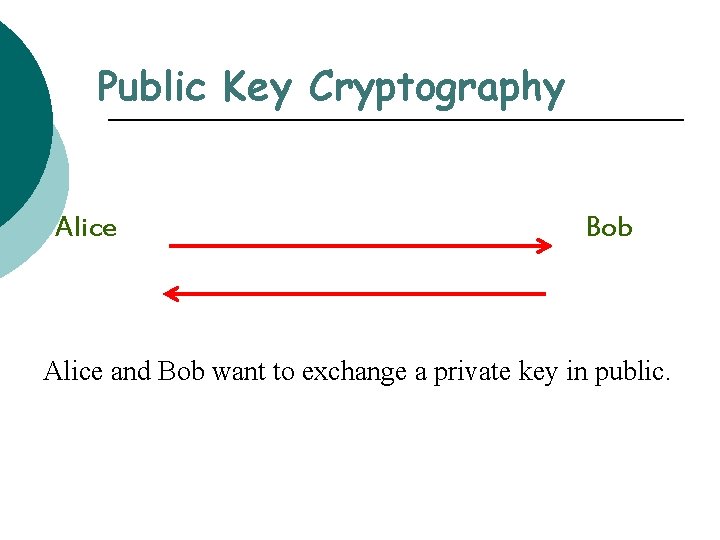
Public Key Cryptography Alice Bob Alice and Bob want to exchange a private key in public.
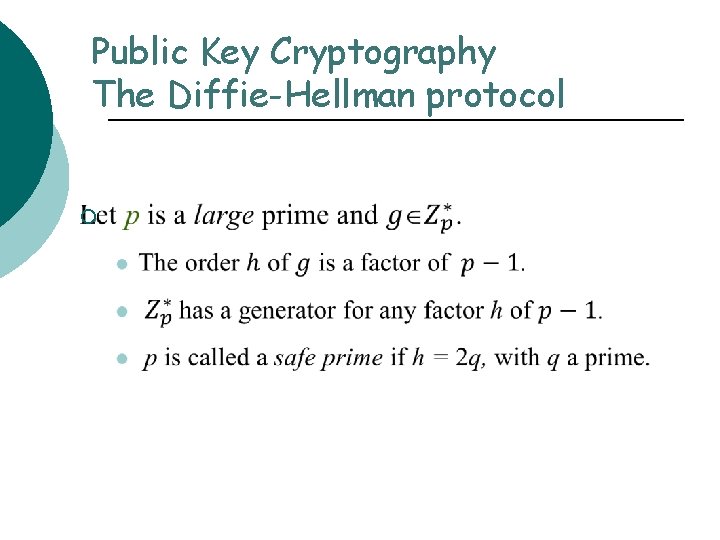
Public Key Cryptography The Diffie-Hellman protocol ¡
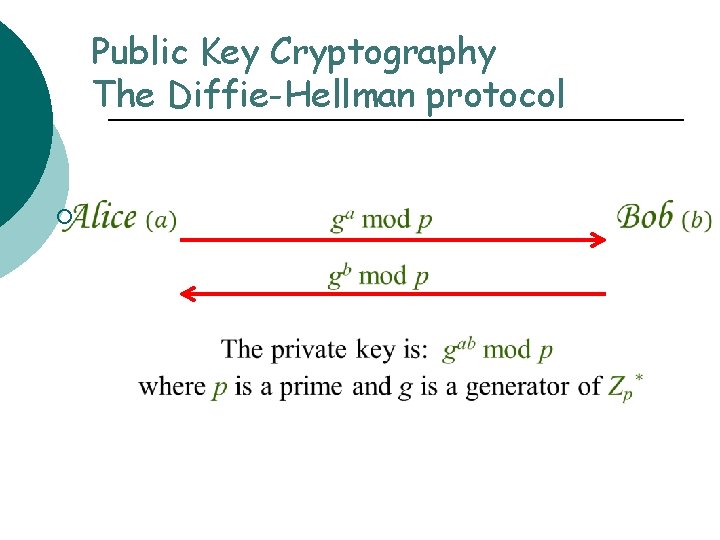
Public Key Cryptography The Diffie-Hellman protocol ¡
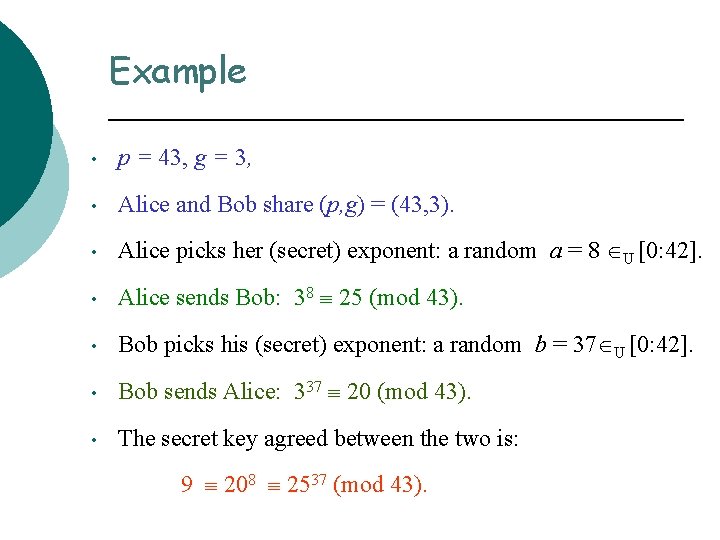
Example • p = 43, g = 3, • Alice and Bob share (p, g) = (43, 3). • Alice picks her (secret) exponent: a random a = 8 U [0: 42]. • Alice sends Bob: 38 25 (mod 43). • Bob picks his (secret) exponent: a random b = 37 U [0: 42]. • Bob sends Alice: 337 20 (mod 43). • The secret key agreed between the two is: 9 208 2537 (mod 43).
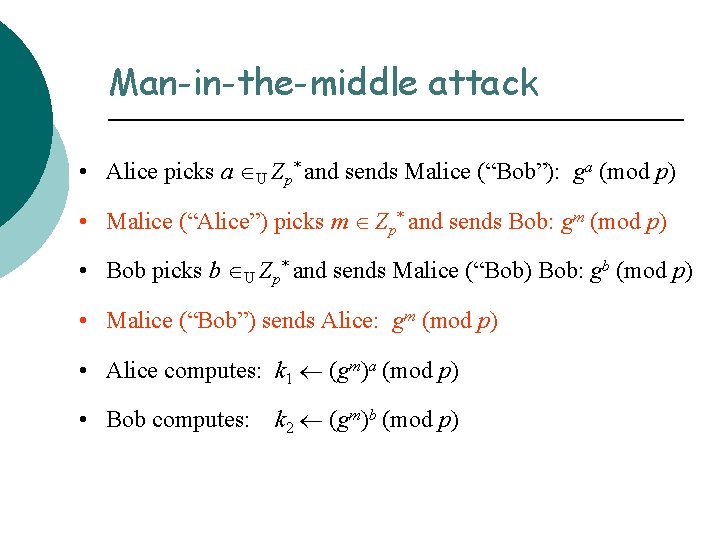
Man-in-the-middle attack • Alice picks a U Zp* and sends Malice (“Bob”): ga (mod p) • Malice (“Alice”) picks m Zp* and sends Bob: gm (mod p) • Bob picks b U Zp* and sends Malice (“Bob) Bob: gb (mod p) • Malice (“Bob”) sends Alice: gm (mod p) • Alice computes: k 1 (gm)a (mod p) • Bob computes: k 2 (gm)b (mod p)
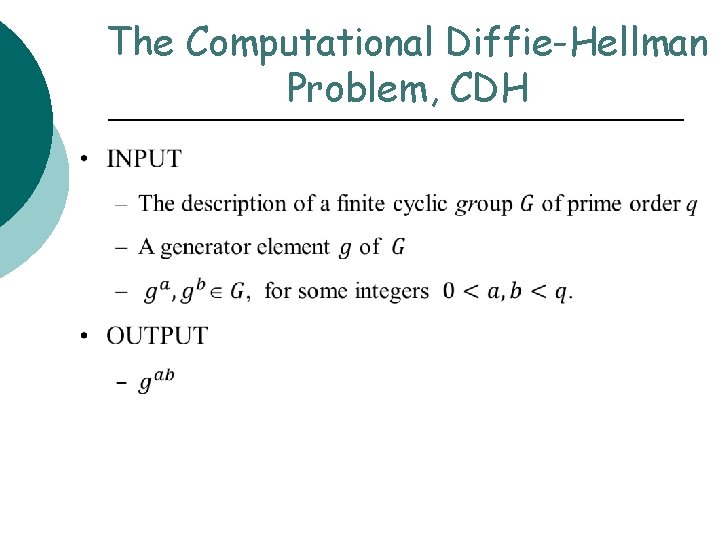
The Computational Diffie-Hellman Problem, CDH
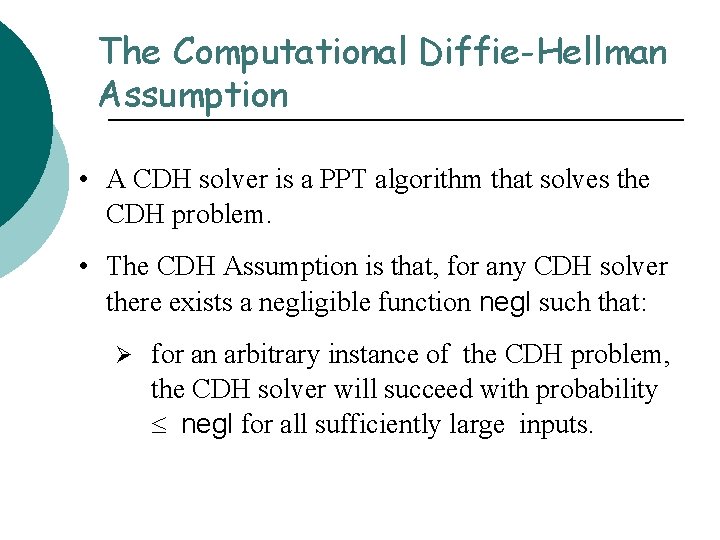
The Computational Diffie-Hellman Assumption • A CDH solver is a PPT algorithm that solves the CDH problem. • The CDH Assumption is that, for any CDH solver there exists a negligible function negl such that: Ø for an arbitrary instance of the CDH problem, the CDH solver will succeed with probability negl for all sufficiently large inputs.
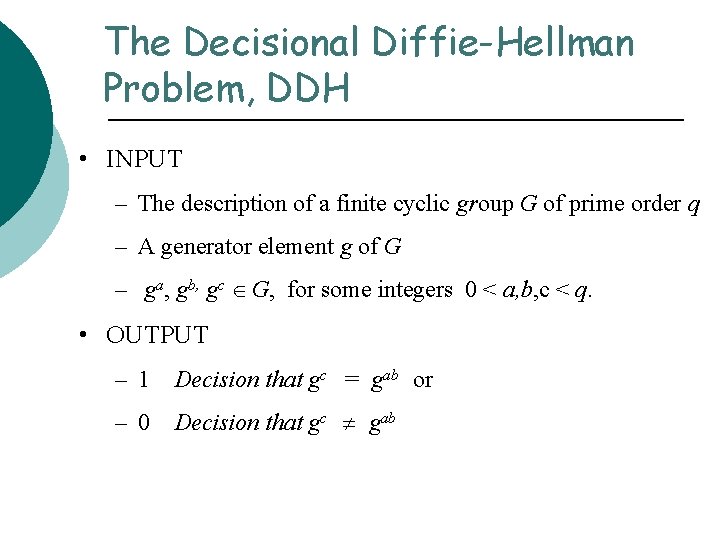
The Decisional Diffie-Hellman Problem, DDH • INPUT – The description of a finite cyclic group G of prime order q – A generator element g of G – ga, gb, gc G, for some integers 0 < a, b, c < q. • OUTPUT – 1 Decision that gc = gab or – 0 Decision that gc gab
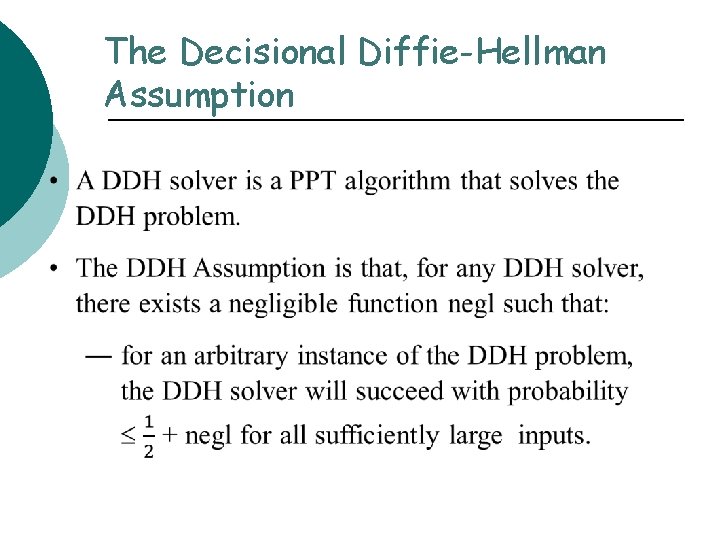
The Decisional Diffie-Hellman Assumption
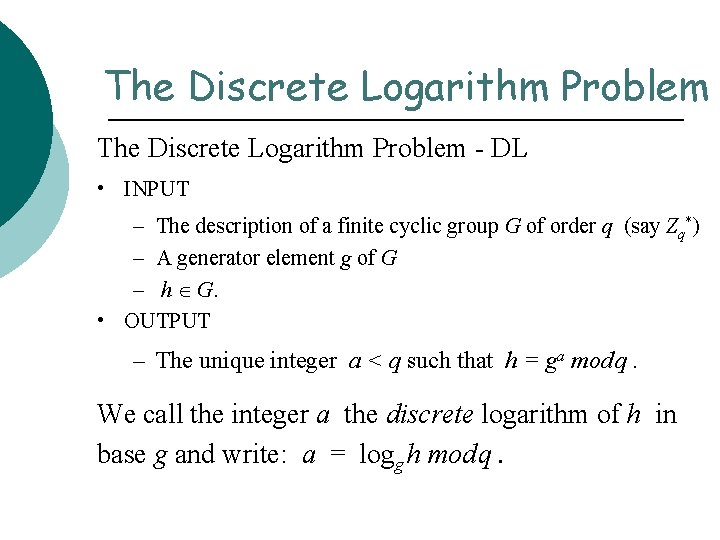
The Discrete Logarithm Problem - DL • INPUT – The description of a finite cyclic group G of order q (say Zq*) – A generator element g of G – h G. • OUTPUT – The unique integer a < q such that h = ga mod q. We call the integer a the discrete logarithm of h in base g and write: a = logg h mod q.
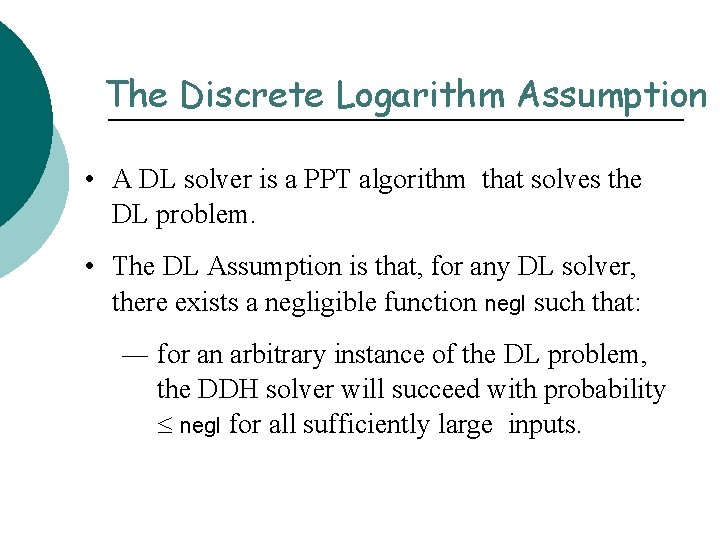
The Discrete Logarithm Assumption • A DL solver is a PPT algorithm that solves the DL problem. • The DL Assumption is that, for any DL solver, there exists a negligible function negl such that: ― for an arbitrary instance of the DL problem, the DDH solver will succeed with probability negl for all sufficiently large inputs.
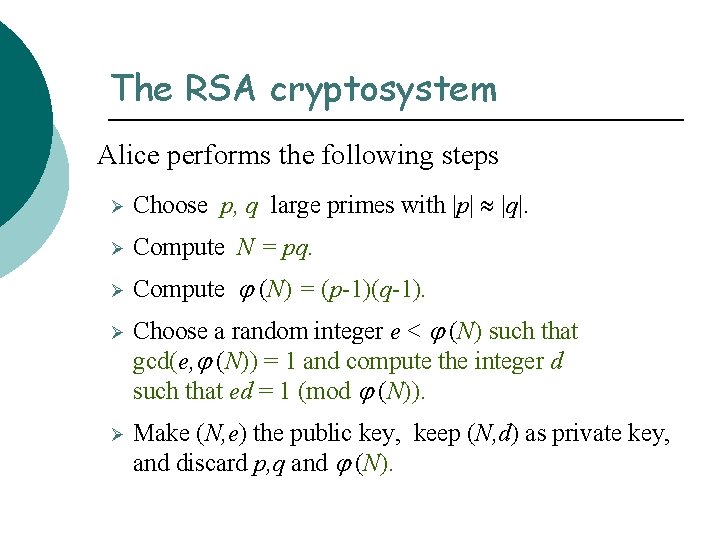
The RSA cryptosystem Alice performs the following steps Ø Choose p, q large primes with |p| |q|. Ø Compute N = pq. Ø Compute (N) = (p-1)(q-1). Ø Ø Choose a random integer e < (N) such that gcd(e, (N)) = 1 and compute the integer d such that ed = 1 (mod (N)). Make (N, e) the public key, keep (N, d) as private key, and discard p, q and (N).
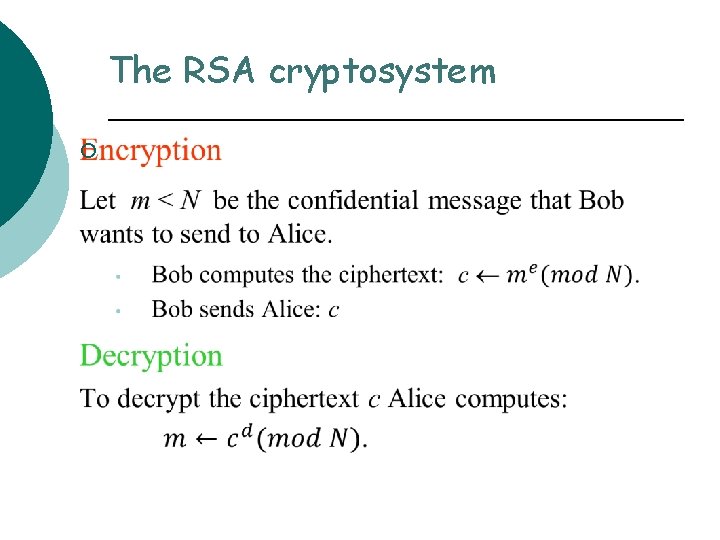
The RSA cryptosystem ¡
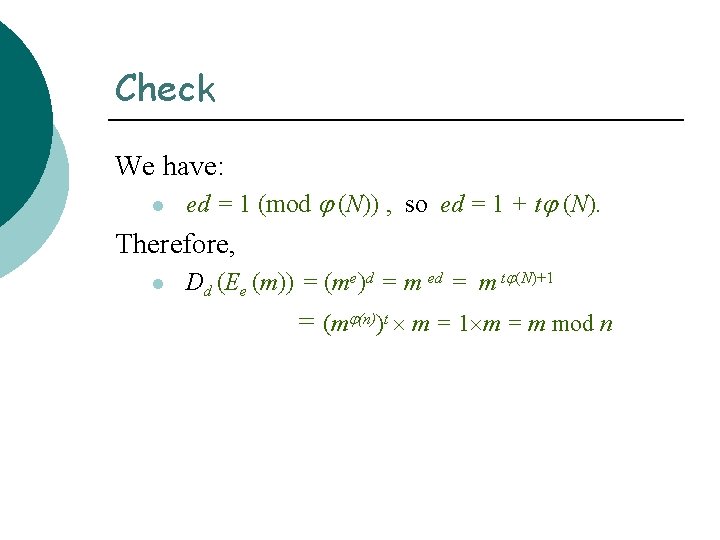
Check We have: l ed = 1 (mod (N)) , so ed = 1 + t (N). Therefore, l Dd (Ee (m)) = (me)d = m ed = m t (N)+1 = (m (n))t m = 1 m = m mod n
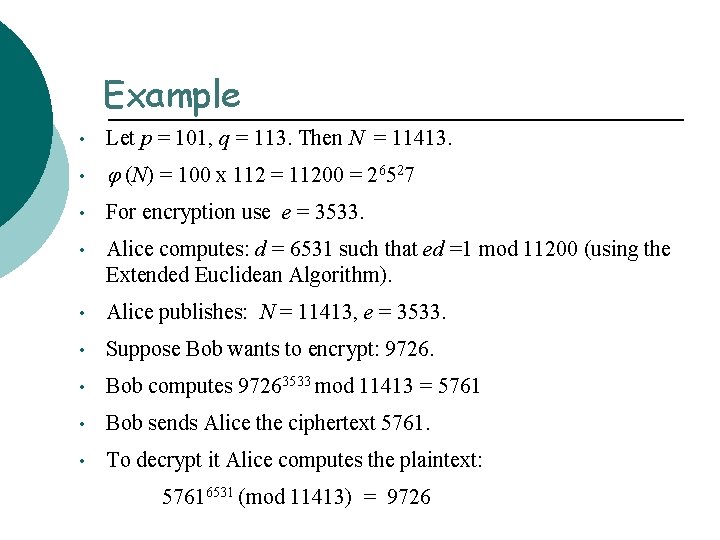
Example • Let p = 101, q = 113. Then N = 11413. • (N) = 100 x 112 = 11200 = 26527 • For encryption use e = 3533. • Alice computes: d = 6531 such that ed =1 mod 11200 (using the Extended Euclidean Algorithm). • Alice publishes: N = 11413, e = 3533. • Suppose Bob wants to encrypt: 9726. • Bob computes 97263533 mod 11413 = 5761 • Bob sends Alice the ciphertext 5761. • To decrypt it Alice computes the plaintext: 57616531 (mod 11413) = 9726
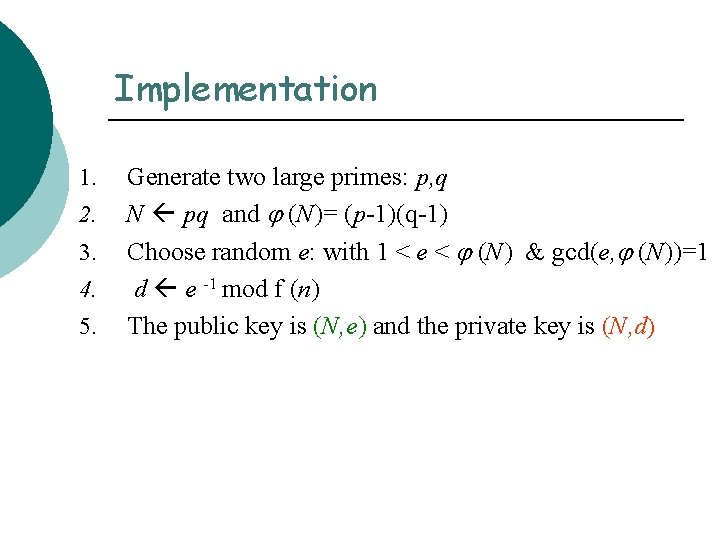
Implementation 1. 2. 3. 4. 5. Generate two large primes: p, q N pq and (N)= (p-1)(q-1) Choose random e: with 1 < e < (N) & gcd(e, (N))=1 d e -1 mod f (n) The public key is (N, e) and the private key is (N, d)
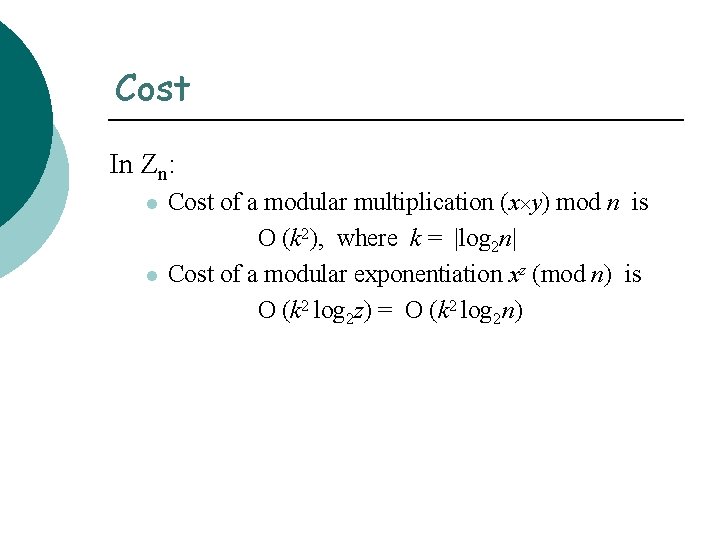
Cost In Zn: l l Cost of a modular multiplication (x y) mod n is O (k 2), where k = |log 2 n| Cost of a modular exponentiation xz (mod n) is O (k 2 log 2 z) = O (k 2 log 2 n)
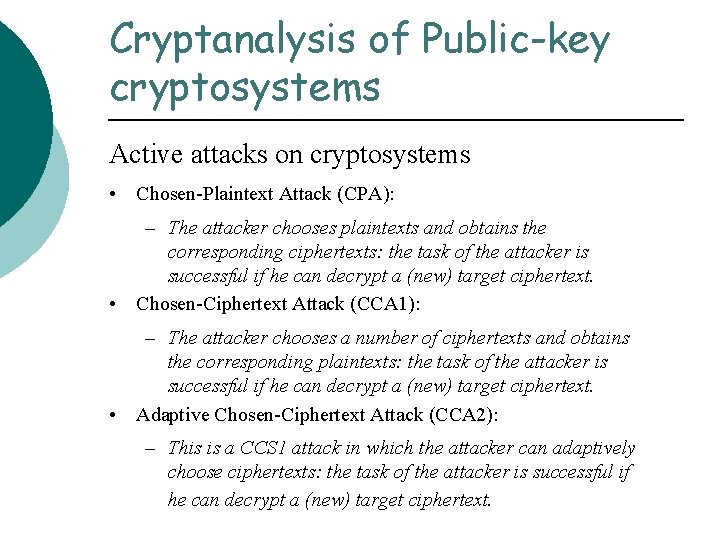
Cryptanalysis of Public-key cryptosystems Active attacks on cryptosystems • Chosen-Plaintext Attack (CPA): – The attacker chooses plaintexts and obtains the corresponding ciphertexts: the task of the attacker is successful if he can decrypt a (new) target ciphertext. • Chosen-Ciphertext Attack (CCA 1): – The attacker chooses a number of ciphertexts and obtains the corresponding plaintexts: the task of the attacker is successful if he can decrypt a (new) target ciphertext. • Adaptive Chosen-Ciphertext Attack (CCA 2): – This is a CCS 1 attack in which the attacker can adaptively choose ciphertexts: the task of the attacker is successful if he can decrypt a (new) target ciphertext.
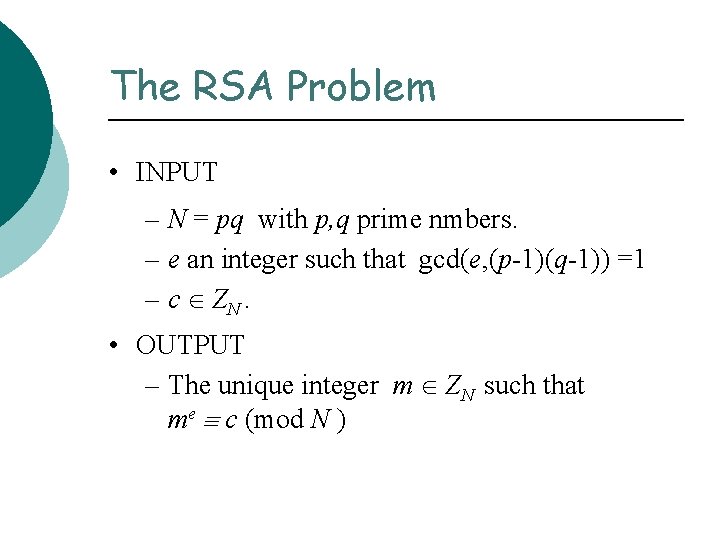
The RSA Problem • INPUT – N = pq with p, q prime nmbers. – e an integer such that gcd(e, (p-1)(q-1)) =1 – c ZN. • OUTPUT – The unique integer m ZN such that me c (mod N )
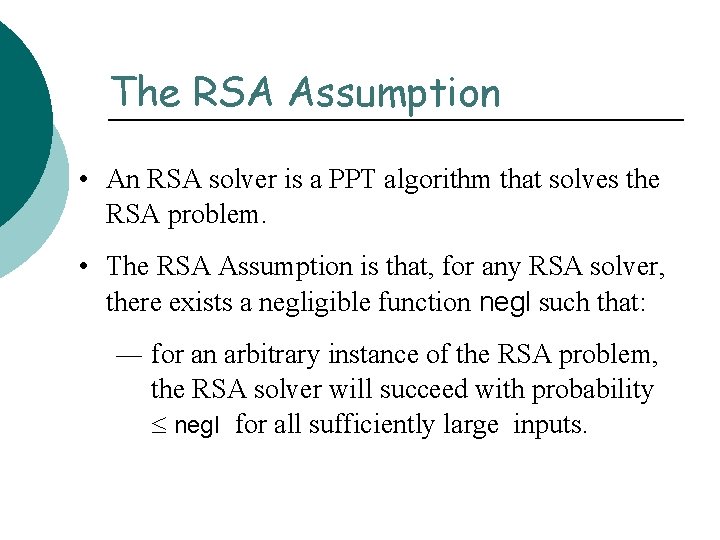
The RSA Assumption • An RSA solver is a PPT algorithm that solves the RSA problem. • The RSA Assumption is that, for any RSA solver, there exists a negligible function negl such that: ― for an arbitrary instance of the RSA problem, the RSA solver will succeed with probability negl for all sufficiently large inputs.
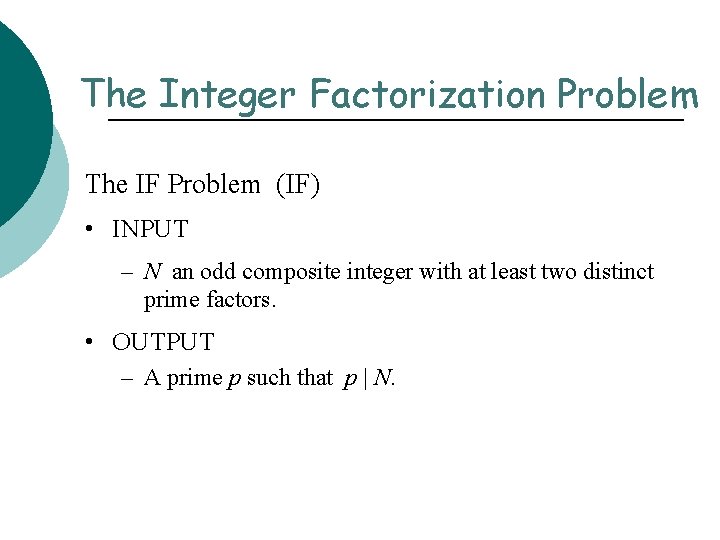
The Integer Factorization Problem The IF Problem (IF) • INPUT – N an odd composite integer with at least two distinct prime factors. • OUTPUT – A prime p such that p | N.
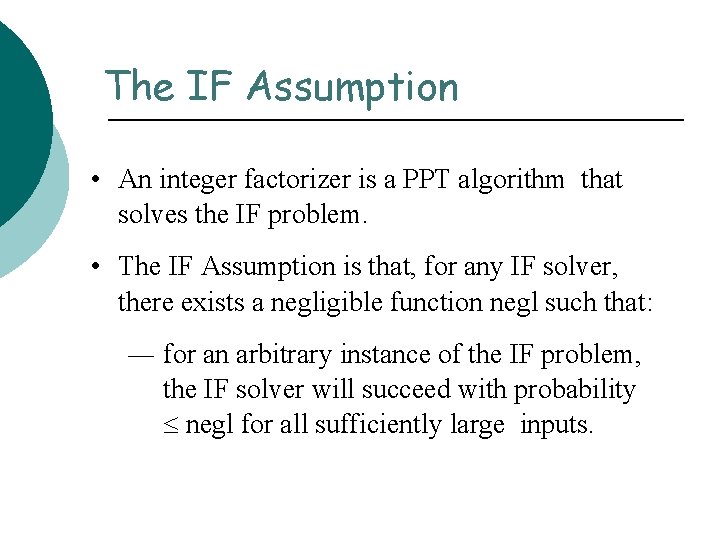
The IF Assumption • An integer factorizer is a PPT algorithm that solves the IF problem. • The IF Assumption is that, for any IF solver, there exists a negligible function negl such that: ― for an arbitrary instance of the IF problem, the IF solver will succeed with probability negl for all sufficiently large inputs.
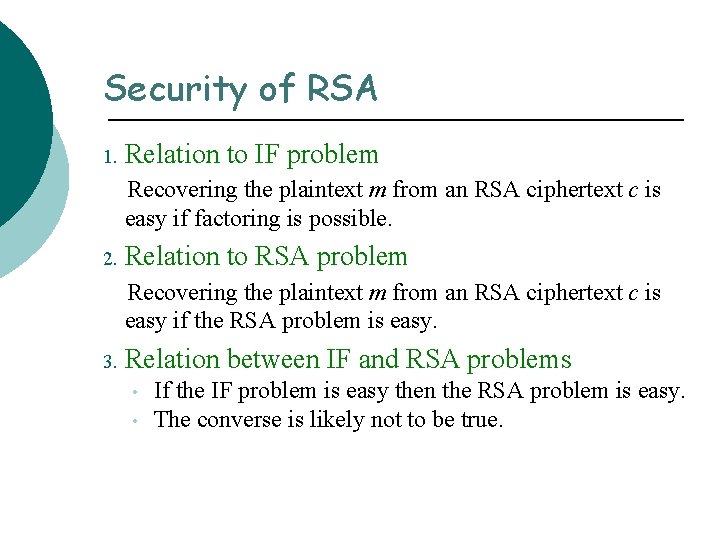
Security of RSA 1. Relation to IF problem Recovering the plaintext m from an RSA ciphertext c is easy if factoring is possible. 2. Relation to RSA problem Recovering the plaintext m from an RSA ciphertext c is easy if the RSA problem is easy. 3. Relation between IF and RSA problems • • If the IF problem is easy then the RSA problem is easy. The converse is likely not to be true.
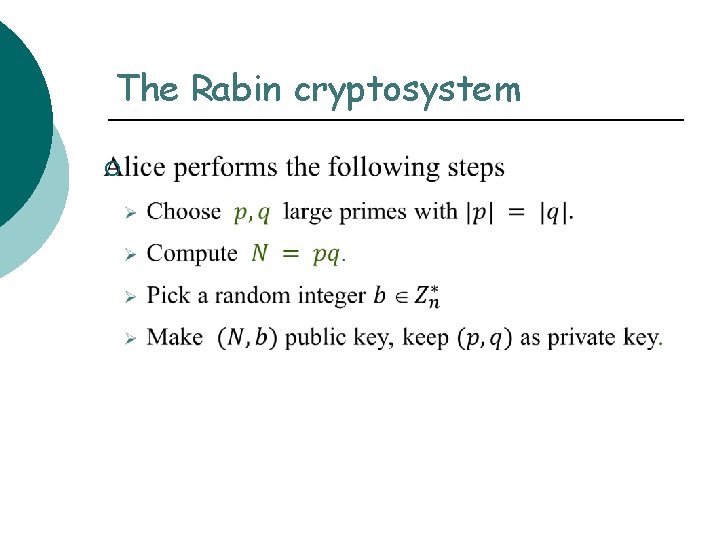
The Rabin cryptosystem ¡
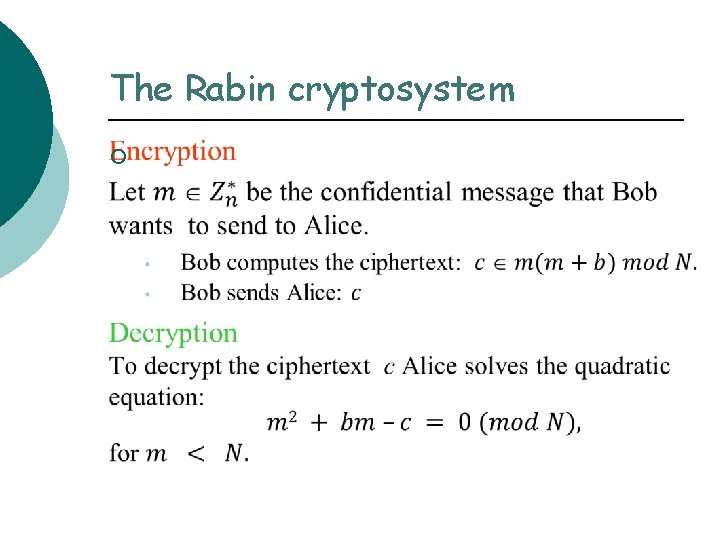
The Rabin cryptosystem ¡
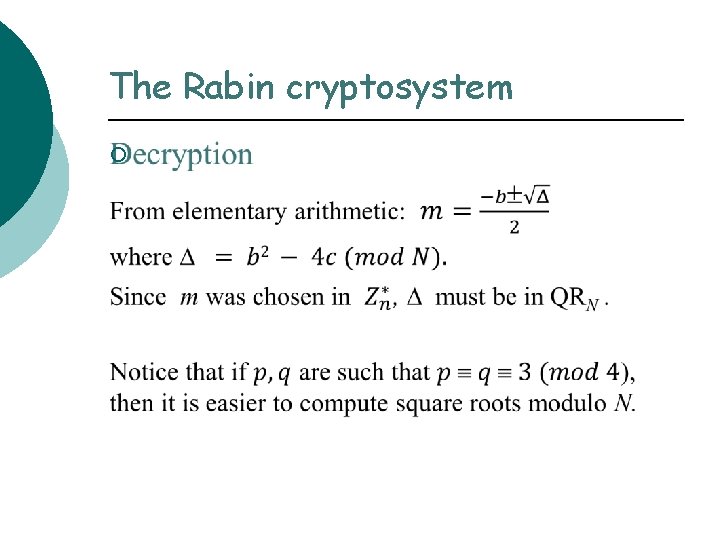
The Rabin cryptosystem ¡
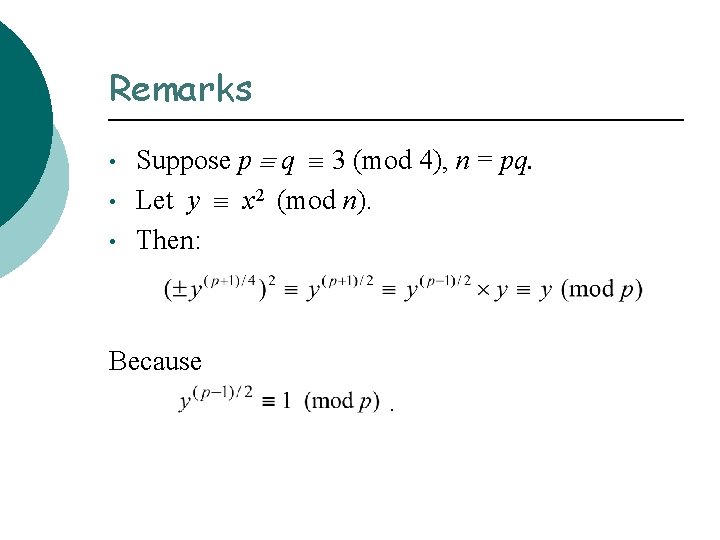
Remarks • • • Suppose p q 3 (mod 4), n = pq. Let y x 2 (mod n). Then: Because.
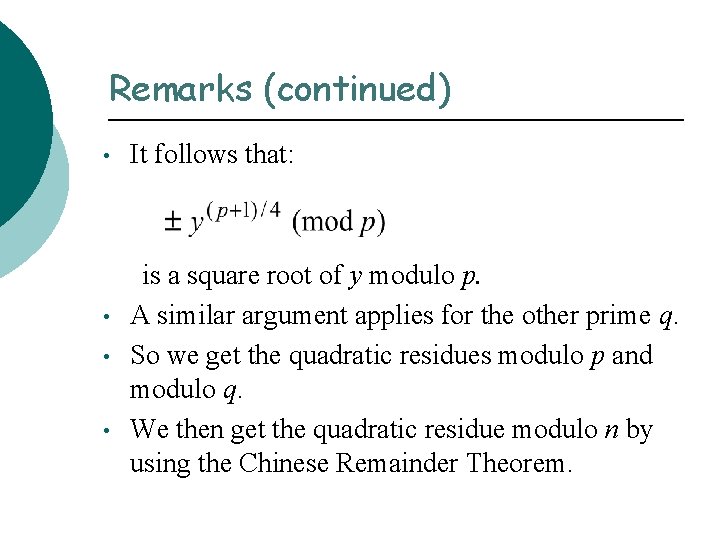
Remarks (continued) • • It follows that: is a square root of y modulo p. A similar argument applies for the other prime q. So we get the quadratic residues modulo p and modulo q. We then get the quadratic residue modulo n by using the Chinese Remainder Theorem.
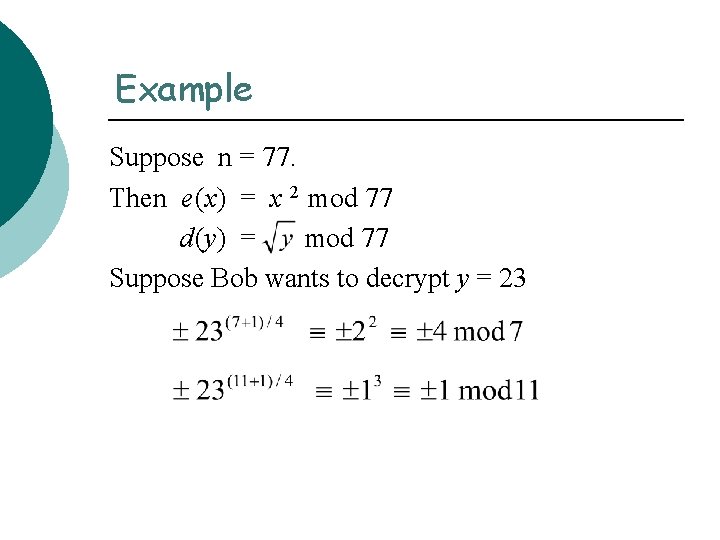
Example Suppose n = 77. Then e (x) = x 2 mod 77 d (y) = mod 77 Suppose Bob wants to decrypt y = 23
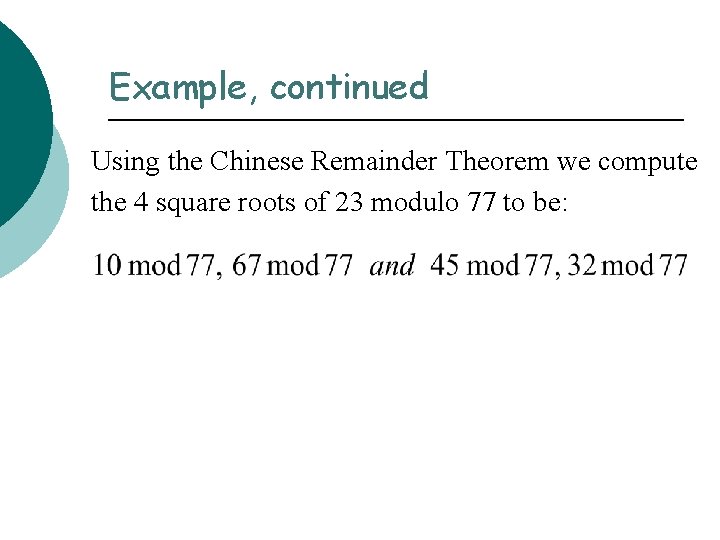
Example, continued Using the Chinese Remainder Theorem we compute the 4 square roots of 23 modulo 77 to be:
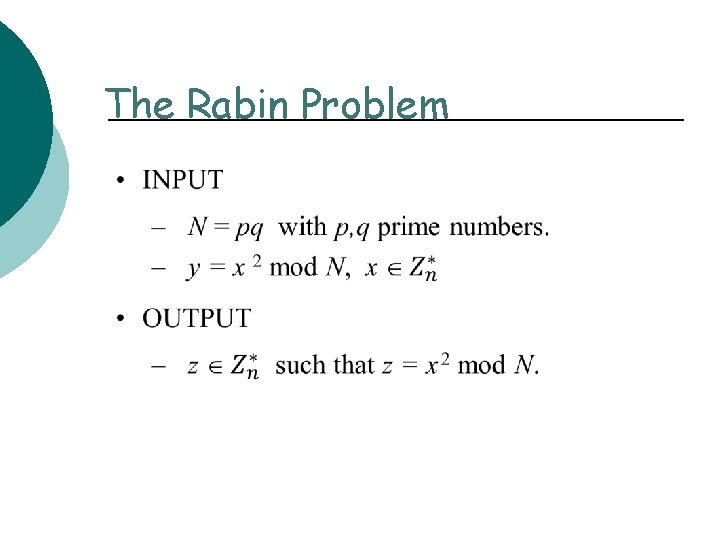
The Rabin Problem
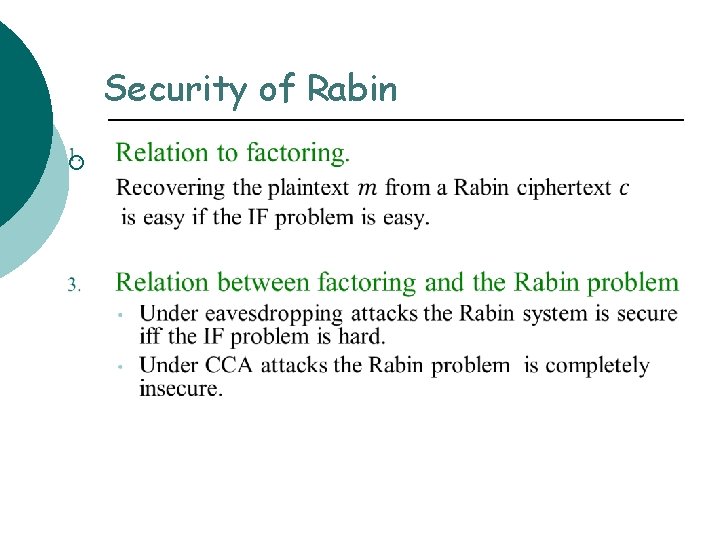
Security of Rabin ¡
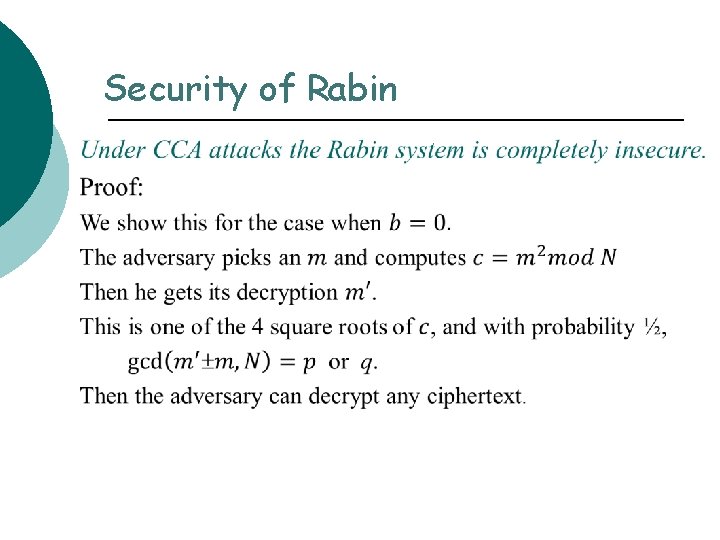
Security of Rabin
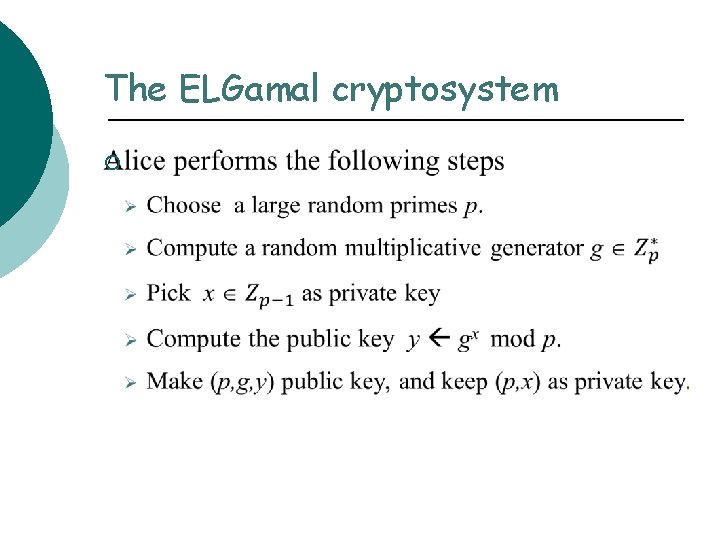
The ELGamal cryptosystem ¡
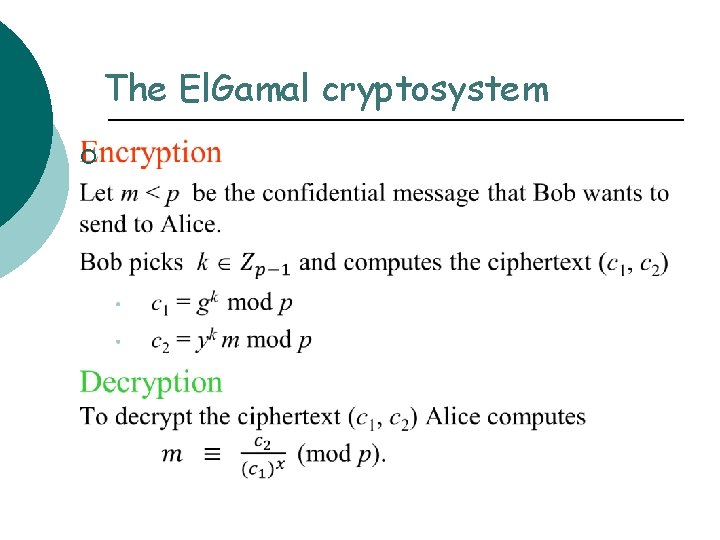
The El. Gamal cryptosystem ¡
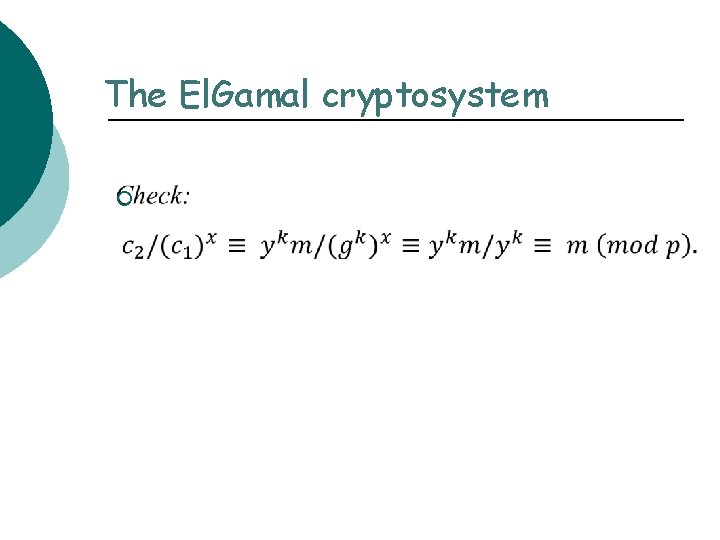
The El. Gamal cryptosystem ¡
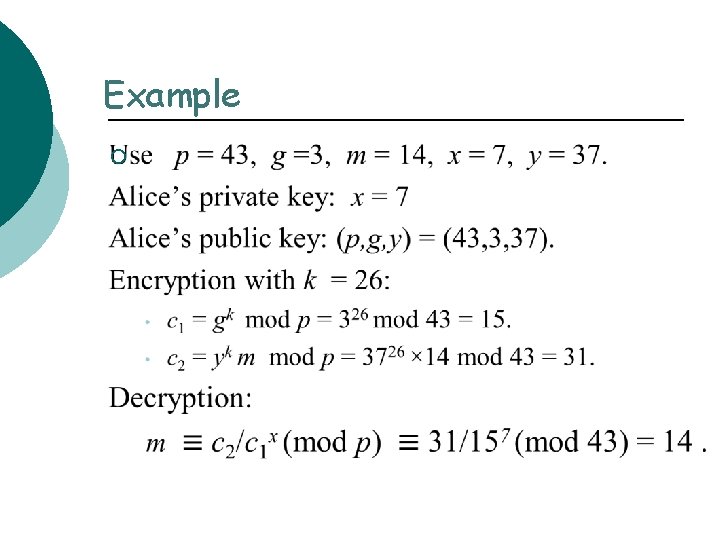
Example ¡
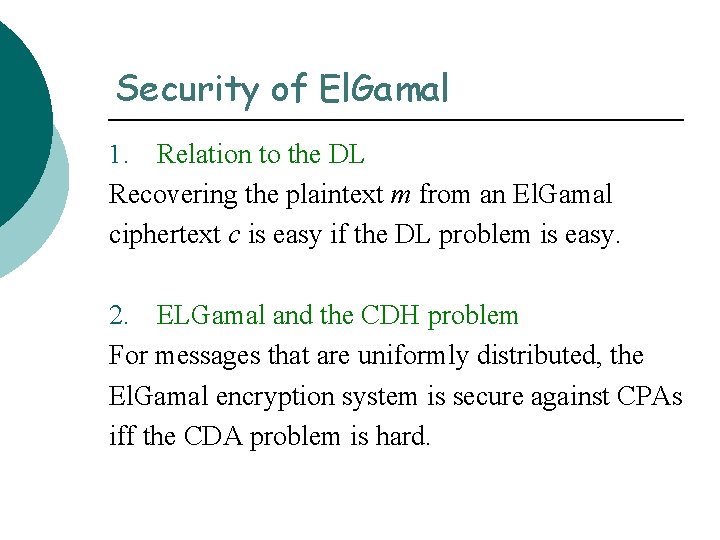
Security of El. Gamal Relation to the DL Recovering the plaintext m from an El. Gamal ciphertext c is easy if the DL problem is easy. 1. 2. ELGamal and the CDH problem For messages that are uniformly distributed, the El. Gamal encryption system is secure against CPAs iff the CDA problem is hard.
Security of El. Gamal For messages that are uniformly distributed, the El. Gamal encryption system is secure against CPAs iff the CDH problem is hard.
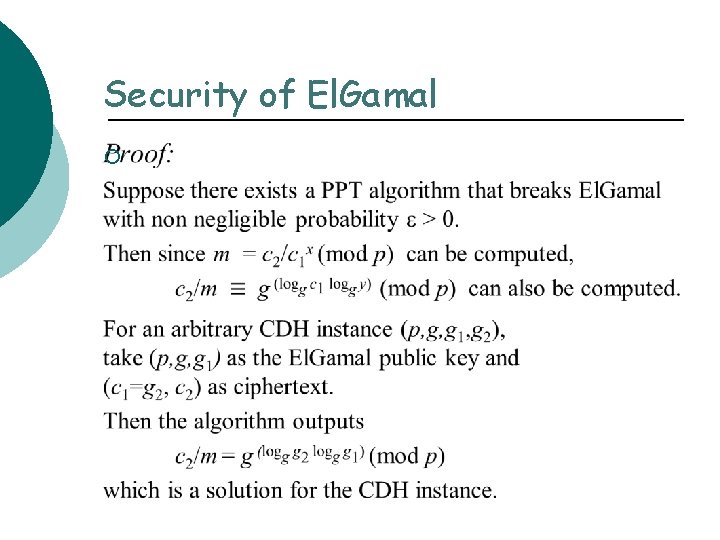
Security of El. Gamal ¡
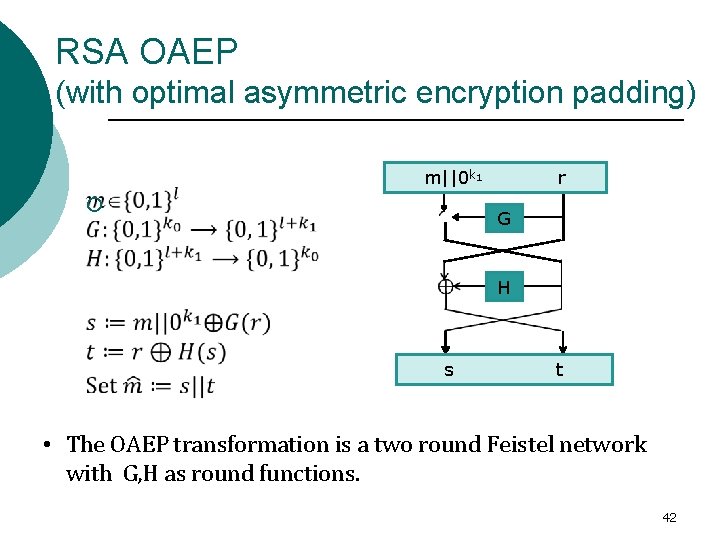
RSA OAEP (with optimal asymmetric encryption padding) m||0 k 1 ¡ r G H s t • The OAEP transformation is a two round Feistel network with G, H as round functions. 42
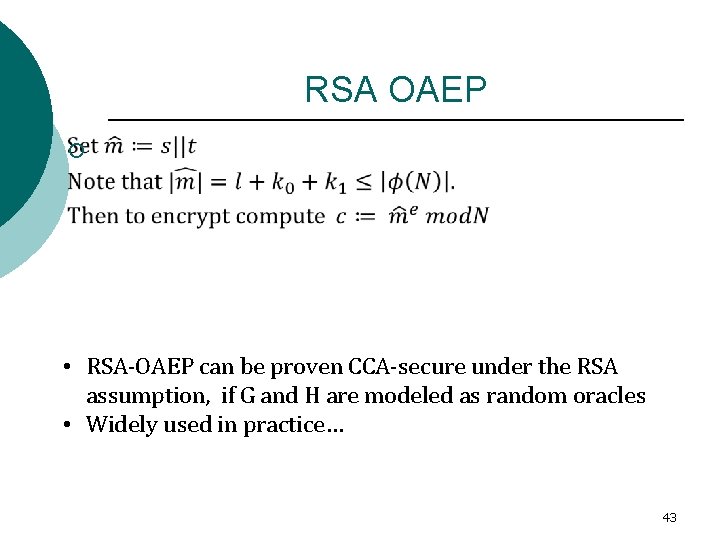
RSA OAEP ¡ • RSA-OAEP can be proven CCA-secure under the RSA assumption, if G and H are modeled as random oracles • Widely used in practice… 43
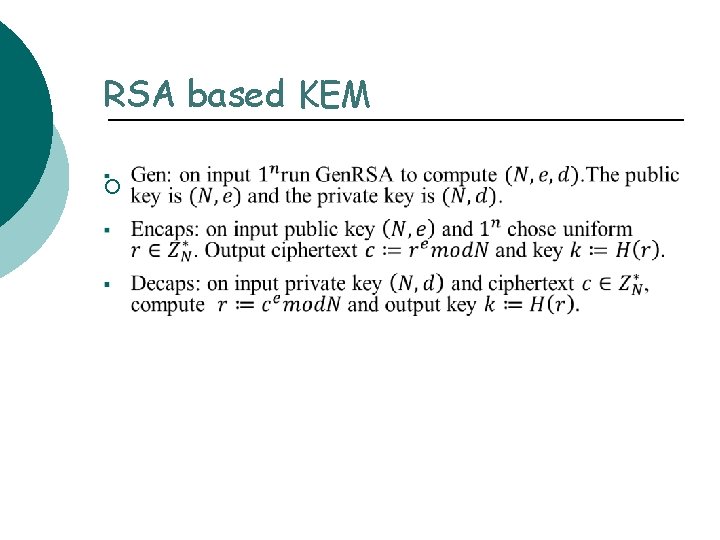
RSA based KEM ¡
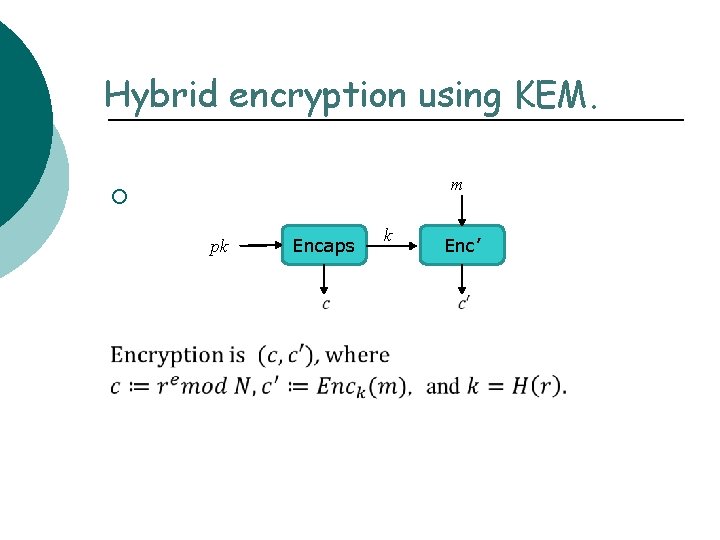
Hybrid encryption using KEM. m ¡ pk Encaps k Enc’
- Slides: 45