Child Sexual Exploitation and Abuse The online threat
Child Sexual Exploitation and Abuse The online threat and challenges of an effective risk based response. Gary KIBBEY
The online threat and challenges of an effective risk based response � Online threat to children � Threat vectors - where are they? � European Union direction � Global initiatives in response � UK response � Gaps, risks and challenges � Discussion and questions?
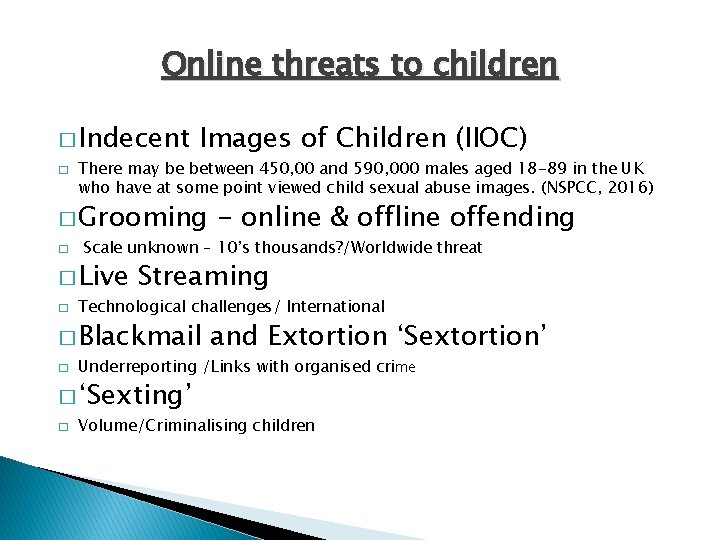
Online threats to children � Indecent � Images of Children (IIOC) There may be between 450, 00 and 590, 000 males aged 18 -89 in the UK who have at some point viewed child sexual abuse images. (NSPCC, 2016) � Grooming � Scale unknown – 10’s thousands? /Worldwide threat � Live � Streaming Technological challenges/ International � Blackmail � and Extortion ‘Sextortion’ Underreporting /Links with organised crime � ‘Sexting’ � - online & offline offending Volume/Criminalising children
Where are they? � Social Media � The Surface web � The Deep web � The Dark web � Tor � Internet Relay Chat � Peer to Peer � Encrypted Applications � Live conferencing � Dark Market
European Union Direction � � Council Framework Decision 2004/68/JHA on combating the sexual exploitation of children and child pornography. (22 nd December 2003) It introduces a framework of common provisions on criminalisation, sanctions, aggravating circumstances, assistance to victims and jurisdiction. Replaced 13 th December 2011 by � � DIRECTIVE 2011/92/EU OF THE EUROPEAN PARLIAMENT AND OF COUNCIL on combating the sexual abuse and sexual exploitation of children and child pornography. The Directive within its 52 points and 28 Articles sort a comprehensive approach by the public authorities and private institutions of Member States in protecting the rights of a child (age 18) against sexual abuse and exploitation. The Directive sort consistency of an effective response with compatibility of legislation and penalties.

Global Initiatives � We. PROTECT - UK initiated � INHOPE � Virtual Global Taskforce � Europol EC 3– Empact/FP Twins � Interpol – ICSE database � UNODC � ECPAT � NCMEC
� Key Legislation UK Response Children Act 1989 � S 47 – Local Authorities duty to investigate significant harm Sexual Offences Act 2003 � � � S. 5 -8 Rape and other sexual offences against children under 13 S. 14 Arranging or facilitating commission of a child sex offence S. 15 Meeting a child following sexual grooming (amended 2. 4. 17) S. 47 Paying for sexual services of a child S. 48 Causing or inciting ‘child prostitution’ or pornography S. 49 Controlling a child prostitute or a child involved in pornography Children Act 2004 � S 11– Safeguarding and Welfare by public bodies as under the guidance of the Secretary of State � National � SDSR (2015) / National Chief Council Policing Delivery Plan (2016)/ National Strategic Assessment of Serious and Organised Crime (2016) � Criminal � Security and Policing Priority Justice and Specialist Support Child Exploitation Online Protection Centre (CEOP) /National Cyber Crime Unit (NCCU) / National Cyber Security Centre ( NCSC) / Crown Prosecution Service specialist case workers/ National & Local Government Services and the vital contribution of the charity sector.
National Strategic Assessment of Serious and Organised Crime (2016) Child Sexual Exploitation and Abuse Key judgements � � � The large increase in the volume of reported crime intelligence generated from industry, and forensics continues to have very significant resourcing implications for law enforcement. The advancement of technology poses challenges for law enforcement. Live streaming and cloud storage of CSEA content which can be hosted on infrastructure outside UK jurisdiction, together with challenges in identifying online offenders, mean that current law enforcement approaches may need to be refined. The practice of live streaming is one example of how offenders can simultaneously create indecent images of children (IIOC) online, view IIOC, and commit contact abuse by proxy overseas. This convergence across all CSEA threat areas is an indicator of the threat evolving with new technologies. www. nationalcrimeagency. gov. uk
Gaps, risks and challenges � Increase knowledge and understand of threat � Evolving threat � Technological opportunities and challenges � Appropriate response to volume/scale � Training needs � Content removal � National and transnational jurisdictional issues � High risk environment – high political/media interest � Theme of Independent Inquiries (Jayet al) � Maintain momentum with competing resources demands
Question? Gary KIBBEY gary@gcjkservices. co. uk
- Slides: 10