Chapter Four CRYPTOGRAPHY DR Musaab Riyadh Abdulrazzaq Mustansiriyah
Chapter Four CRYPTOGRAPHY DR. Musaab Riyadh Abdulrazzaq Mustansiriyah University College of Science- Computer Dept.
What Is Cryptography? § Cryptography is the art of transforming a readable message into a form that is only readable by authorized users. § Encryption is the process of scrambling plaintext into cipher text. Decryption is the process of unscrambling cipher text into plain text. Encryption ciphers fall into two general categories: § Those that use the same key to encrypt and decrypt are private (symmetric) key ciphers. § Those that use different keys to encrypt and decrypt are public (asymmetric) key ciphers.
Cryptography’s Role in Information Security In today’s information systems, you will encounter two primary uses of cryptography to protect data in transit and to protect data at rest: § Data in transit refers to any data as they are exchanged, most commonly via a network connection. the encryption (and decryption) of Data in transit occurs at the transport layer in the network stack. Common examples of transport encryption protocols include Secure Sockets Layer (SSL) § Data at rest are any data that are stored on some storage media. It requires some software to encrypt and decrypt messages separate from the communications functions. cryptography can satisfy these requirements: Confidentiality, Integrity, and Authentication
Types of Ciphers (Substitution ) § A substitution cipher replaces bits, characters, or blocks of information with other bits, characters, or blocks. § One of the simplest substitution ciphers is the Caesar cipher. It shifts each letter in the English alphabet a fixed number of positions, with Z wrapping back to A. ATTACK AT DAWN DWWDFN DW GDZQ § A keyword mixed alphabet cipher uses a cipher alphabet that consists of a keyword, minus duplicates, followed by the remaining letters of the alphabet. For example, using the key word CRYPTOGRAPHY, this type of cipher would yield the following: ABCDEFGHIJKLMNOPQRSTUVWXYZ CRYPTOGAHBDEFIJKLMNQSUVWXZ § Thus, the plaintext word ALPHABET would encrypt to CEKACRTQ
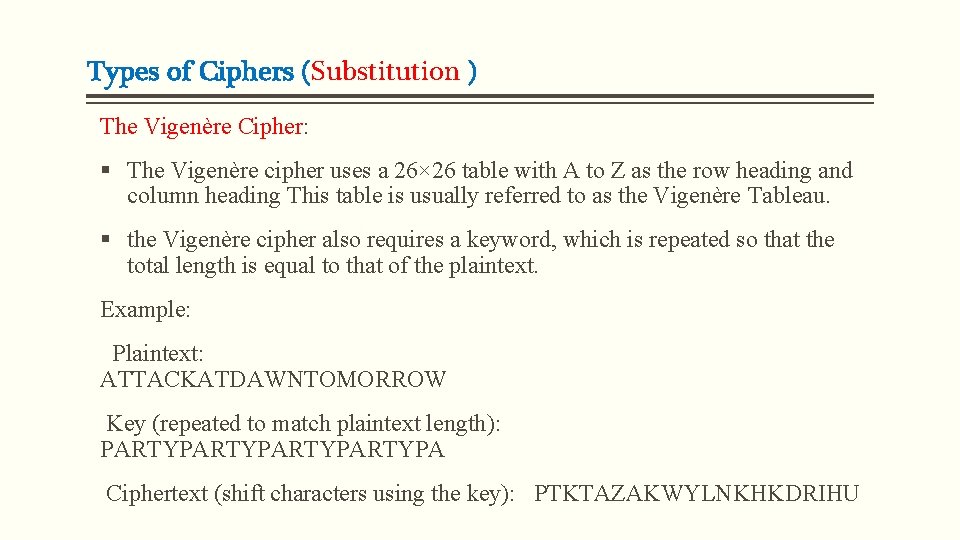
Types of Ciphers (Substitution ) The Vigenère Cipher: § The Vigenère cipher uses a 26× 26 table with A to Z as the row heading and column heading This table is usually referred to as the Vigenère Tableau. § the Vigenère cipher also requires a keyword, which is repeated so that the total length is equal to that of the plaintext. Example: Plaintext: ATTACKATDAWNTOMORROW Key (repeated to match plaintext length): PARTYPARTYPA Ciphertext (shift characters using the key): PTKTAZAKWYLNKHKDRIHU
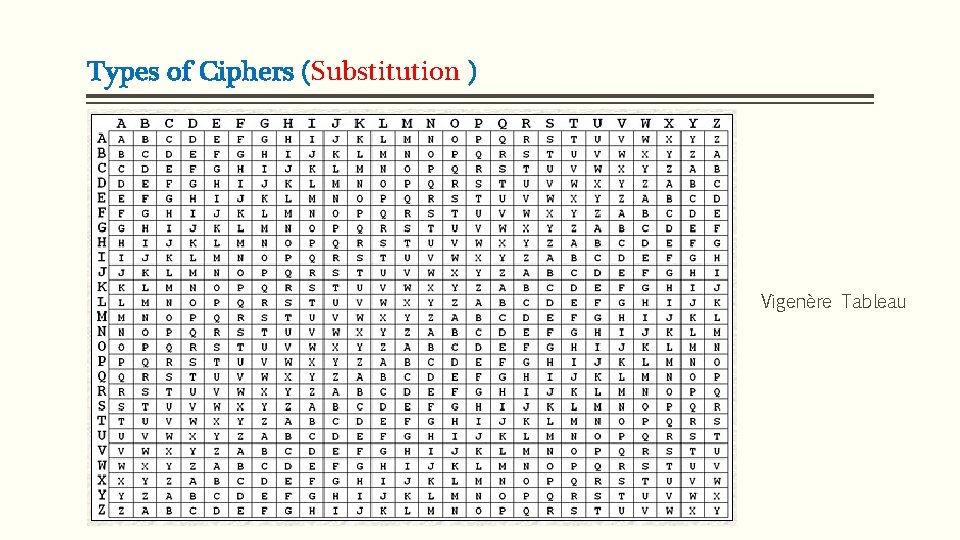
Types of Ciphers (Substitution ) Vigenère Tableau
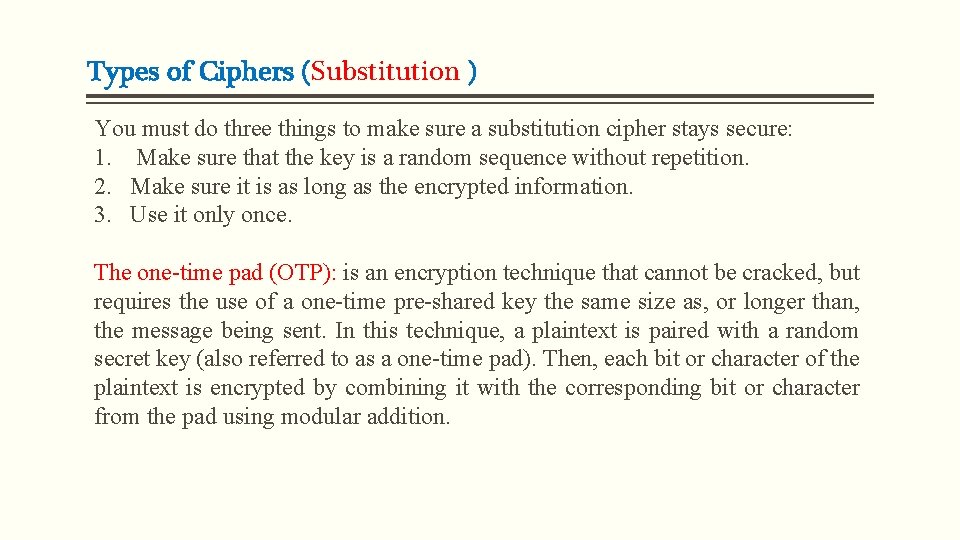
Types of Ciphers (Substitution ) You must do three things to make sure a substitution cipher stays secure: 1. Make sure that the key is a random sequence without repetition. 2. Make sure it is as long as the encrypted information. 3. Use it only once. The one-time pad (OTP): is an encryption technique that cannot be cracked, but requires the use of a one-time pre-shared key the same size as, or longer than, the message being sent. In this technique, a plaintext is paired with a random secret key (also referred to as a one-time pad). Then, each bit or character of the plaintext is encrypted by combining it with the corresponding bit or character from the pad using modular addition.
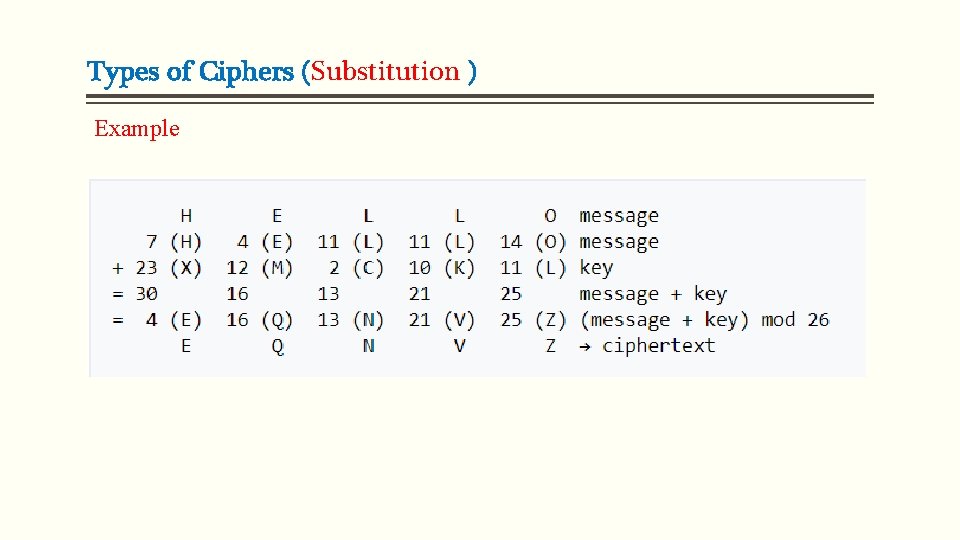
Types of Ciphers (Substitution ) Example
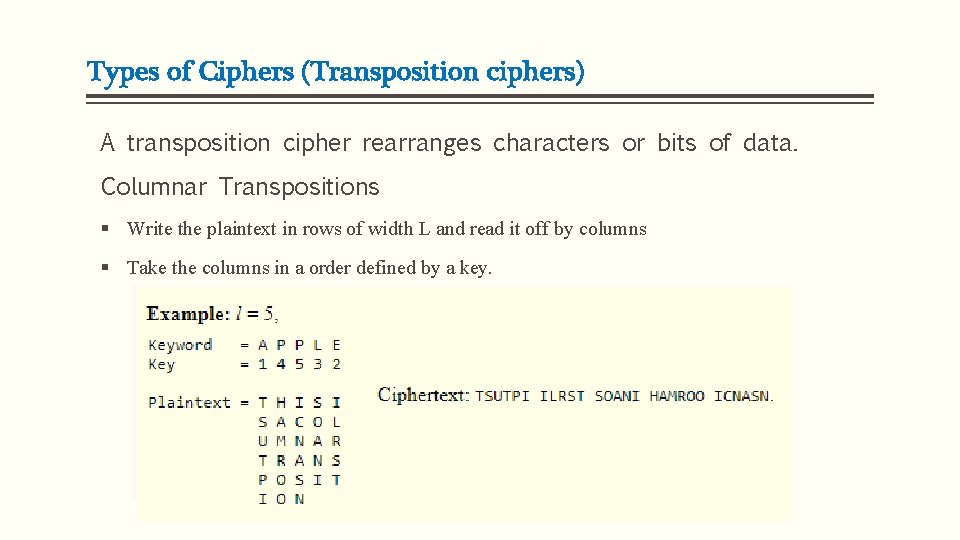
Types of Ciphers (Transposition ciphers) A transposition cipher rearranges characters or bits of data. Columnar Transpositions § Write the plaintext in rows of width L and read it off by columns § Take the columns in a order defined by a key.
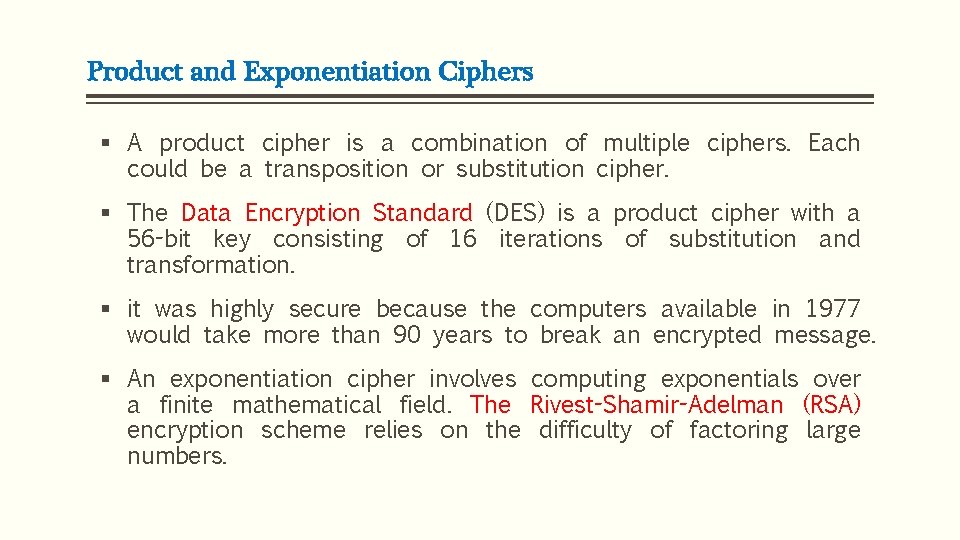
Product and Exponentiation Ciphers § A product cipher is a combination of multiple ciphers. Each could be a transposition or substitution cipher. § The Data Encryption Standard (DES) is a product cipher with a 56 -bit key consisting of 16 iterations of substitution and transformation. § it was highly secure because the computers available in 1977 would take more than 90 years to break an encrypted message. § An exponentiation cipher involves computing exponentials over a finite mathematical field. The Rivest-Shamir-Adelman (RSA) encryption scheme relies on the difficulty of factoring large numbers.
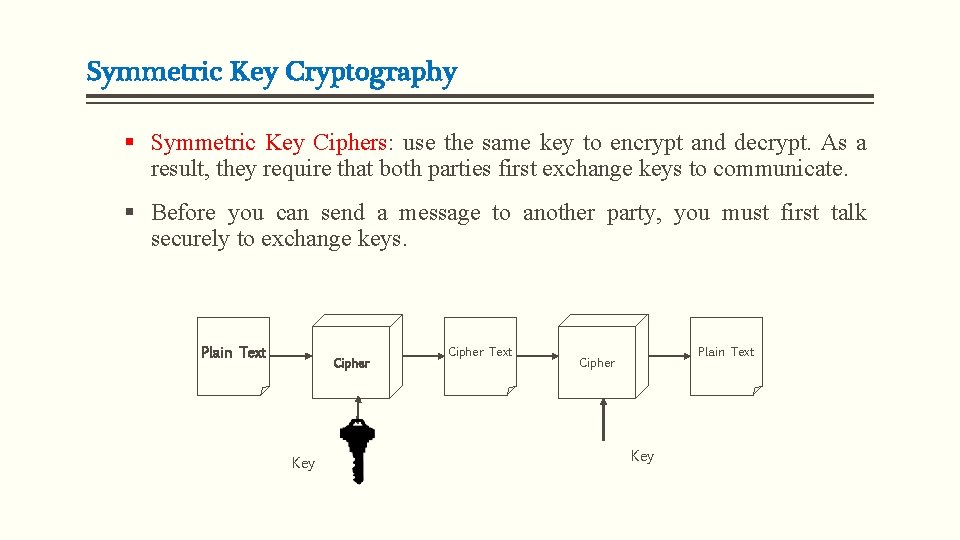
Symmetric Key Cryptography § Symmetric Key Ciphers: use the same key to encrypt and decrypt. As a result, they require that both parties first exchange keys to communicate. § Before you can send a message to another party, you must first talk securely to exchange keys. Plain Text Cipher Key Cipher Text Plain Text Cipher Key
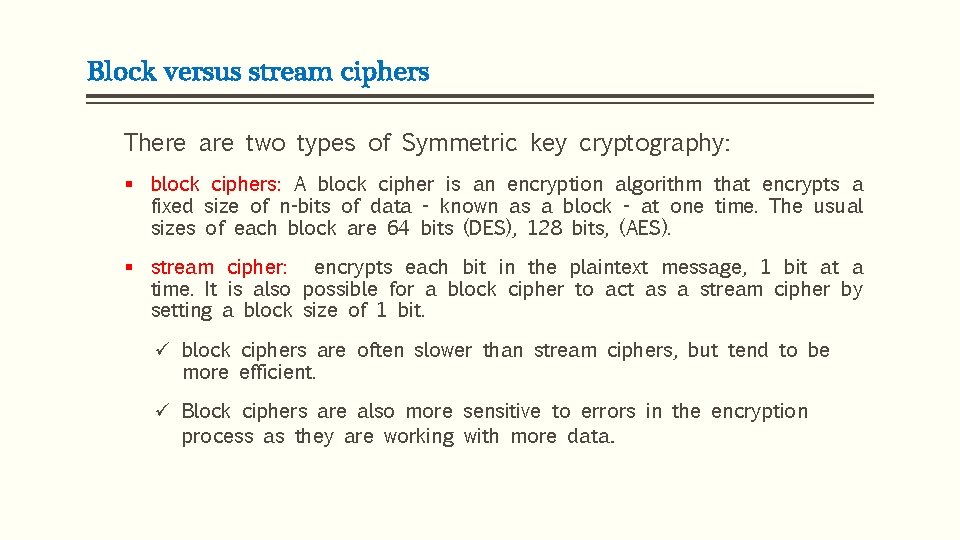
Block versus stream ciphers There are two types of Symmetric key cryptography: § block ciphers: A block cipher is an encryption algorithm that encrypts a fixed size of n-bits of data - known as a block - at one time. The usual sizes of each block are 64 bits (DES), 128 bits, (AES). § stream cipher: encrypts each bit in the plaintext message, 1 bit at a time. It is also possible for a block cipher to act as a stream cipher by setting a block size of 1 bit. ü block ciphers are often slower than stream ciphers, but tend to be more efficient. ü Block ciphers are also more sensitive to errors in the encryption process as they are working with more data.
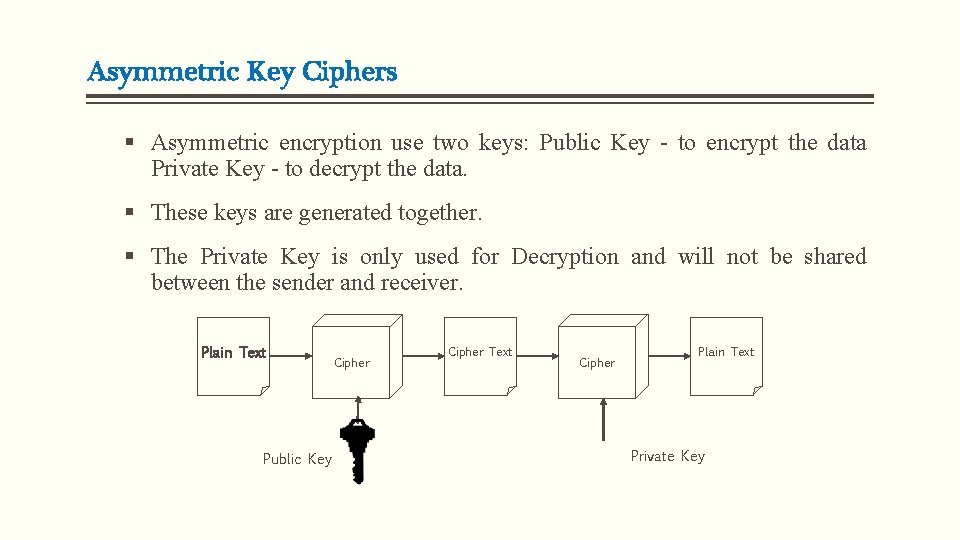
Asymmetric Key Ciphers § Asymmetric encryption use two keys: Public Key - to encrypt the data Private Key - to decrypt the data. § These keys are generated together. § The Private Key is only used for Decryption and will not be shared between the sender and receiver. Plain Text Public Key Cipher Text Cipher Plain Text Private Key
Cryptographic Keys and Key space § The key participates in transforming the message in a particular manner. A well-designed cryptosystem produces different outputs of the same message for each key used. § The set of all possible keys is a key space. Usually, although not always, the larger the key space, the more secure the algorithm. § Key management: refers to management of cryptographic keys in a cryptosystem. This includes dealing with the generation, exchange, storage, use, crypto-shredding (destruction) and replacement of keys. It includes cryptographic protocol design, key servers, user procedures, and other relevant protocols. [1]
Hash Functions and Digital Signatures Hash Functions: § To ensure that the values of a message have not changed either deliberately or through transmission error you can append some summary of the information that you can verify through a repeatable process. § A hash is like a checksum but operates so that a forged message will not result in the same hash as a legitimate message. § Hashes are usually a fixed size usually have to be long enough so that creating an alternative message that matched the hash value would take far too much time. . The result is a hash value act as a fingerprint for the data. § Software publishers often provide hash values so that customers can check the integrity of the software they receive.
Hash Functions and Digital Signatures Credit cards have a hash digit that validates the card number. The algorithm for calculating this digit is the LUHN formula, based on ANSI X 4. 13. To calculate whether a credit card number is valid, follow these four steps: 1. From the rightmost digit, which is the check digit, and moving left, double the value of every second digit. 2. Take the sum of all the digits. 3. If the total modulo 10 is equal to 0 (if the total ends in zero) then the number is valid according to the Luhn formula; else it is not valid.
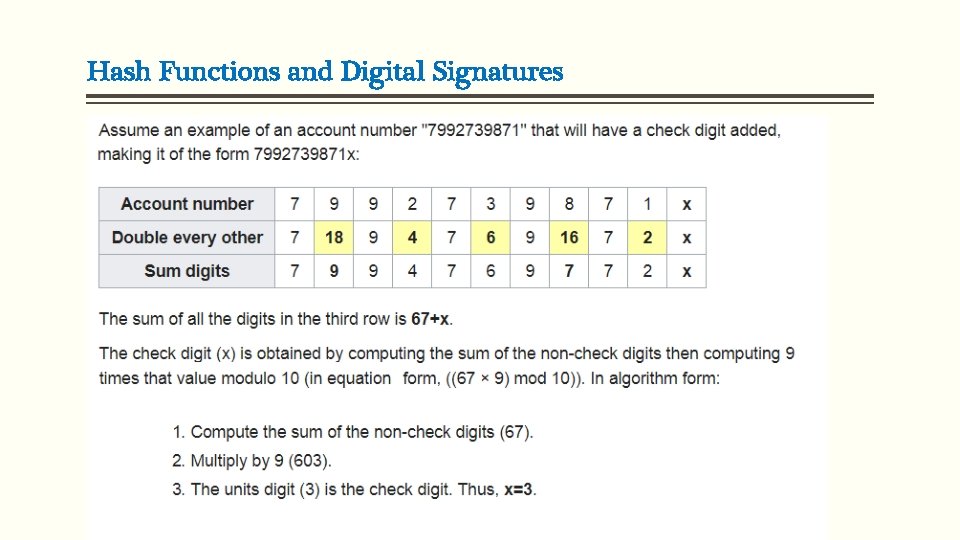
Hash Functions and Digital Signatures
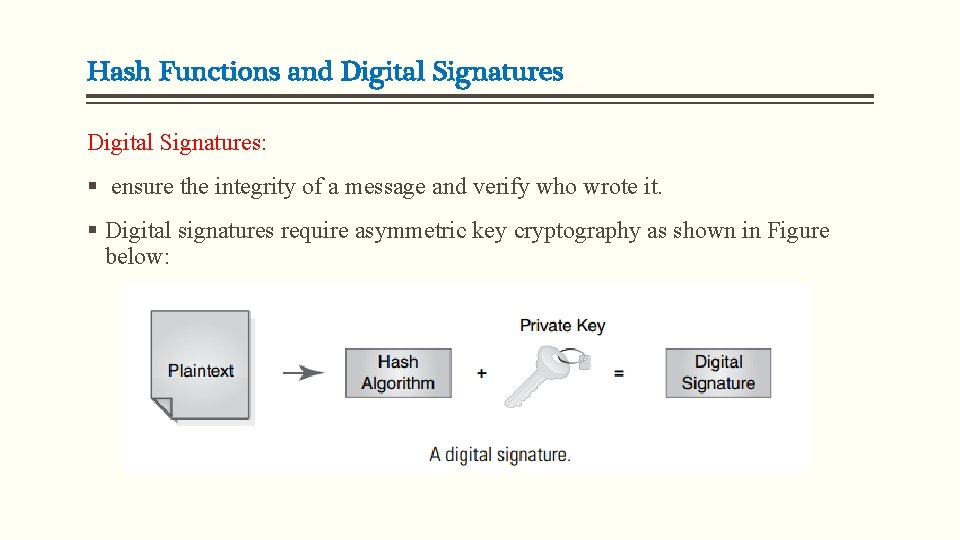
Hash Functions and Digital Signatures: § ensure the integrity of a message and verify who wrote it. § Digital signatures require asymmetric key cryptography as shown in Figure below:
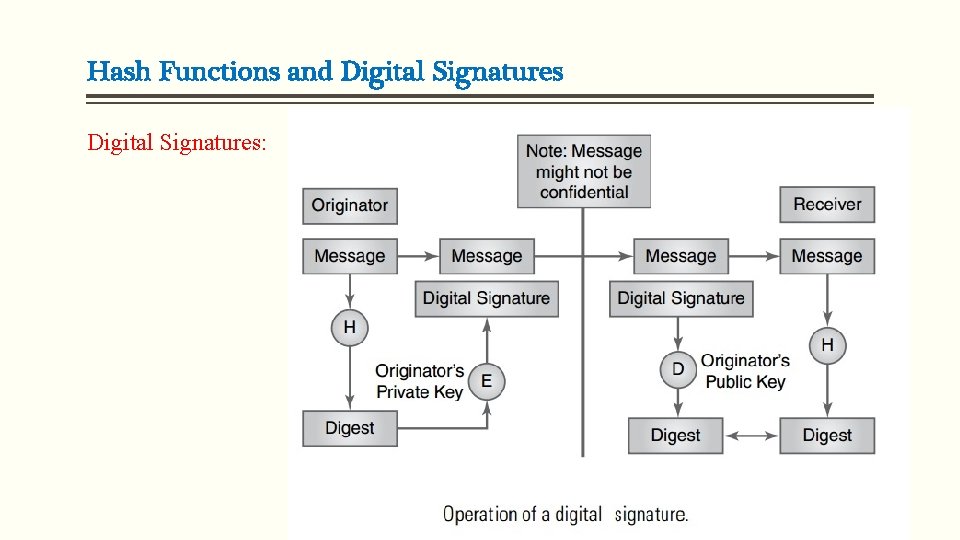
Hash Functions and Digital Signatures:
Cryptanalysis and Public Versus Private Keys You can break a cipher in two ways: § Analyzing the cipher text to find the plaintext or key § Analyzing the ciphe rtext and its associated plaintext to find the key You can break almost any cipher, given enough time and resources. However, a cipher’s main purpose is to make it so difficult to break that it is computationally infeasible to crack. For example, assume that an organization generates new keys every week. If an attacker can crack any key in 13 days, the cracked keys would be useless by the time the attacker tried to use it; it would already have been superseded by a new key.
Cryptanalysis and Public Versus Private Keys There are four basic forms of cryptographic attack: § Cipher text-only attack (COA): In a cipher text-only attack, the cryptanalyst has access only to a segment of encrypted data and has no choice as to what those data may be. § Known-plaintext attack (KPA): In a known-plaintext attack, the cryptanalyst possesses certain pieces of information before and after encryption. § Chosen-plaintext attack: In a chosen-plaintext attack, the cryptanalyst can encrypt any information and observe the output. This is the best case for the cryptanalyst. It offers the most flexibility (and insight) into the encryption mechanism.

THANK YOU
- Slides: 22