Chapter 9 Security IT Essentials PC Hardware and

- Slides: 37
Chapter 9: Security IT Essentials: PC Hardware and Software v 4. 0 ITE PC v 4. 0 Chapter 9 © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 1
Purpose of this Presentation To provide to instructors an overview of Chapter 9: § List of chapter objectives § Overview of the chapter contents, including student worksheets student activities some potential student misconceptions § Reflection/Activities for instructors to complete to prepare to teach § Additional resources ITE PC v 4. 0 Chapter 9 © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 2
Chapter 9 Objectives § 9. 1 Explain why security is important § 9. 2 Describe security threats § 9. 3 Identify security procedures § 9. 4 Identify common preventive maintenance techniques for security § 9. 5 Troubleshoot security ITE PC v 4. 0 Chapter 9 © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 3
Chapter 9 Worksheets and Activity § 9. 1 Worksheet: Security Attacks § 9. 2. 1 Worksheet: Third-Party Anti-Virus Software § 9. 2. 3 Activity: Adware, Spyware, and Grayware § 9. 4. 2 Worksheet: Operating System Updates § 9. 5. 6 Worksheet: Gather Information from the Customer ITE PC v 4. 0 Chapter 9 © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 4
The Importance of Security § Private information, company secrets, financial data, computer equipment, and items of national security are placed at risk if proper security procedures are not followed. § A technician’s primary responsibilities include data and network security. ITE PC v 4. 0 Chapter 9 © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 5
Security Threats Types of attacks to computer security: § Physical Theft, damage, or destruction to computer equipment. § Data Removal, corruption, denial of access, unauthorized access, or theft of information. Potential threats to computer security: § Internal threats Employees can cause a malicious threat or an accidental threat. § External threats Outside users can attack in an unstructured or structured way. ITE PC v 4. 0 Chapter 9 © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 6
Viruses, Worms, and Trojan Horses § A computer virus is software code that is deliberately created by an attacker. Viruses may collect sensitive information or may alter or destroy information. § A worm is a self-replicating program that uses the network to duplicate its code to the hosts on the network. At a minimum, worms consume bandwidth in a network. § A Trojan horse is technically a worm and is named for its method of getting past computer defenses by pretending to be something useful. § Anti-virus software is designed to detect, disable, and remove viruses, worms, and Trojan horses before they infect a computer. ITE PC v 4. 0 Chapter 9 © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 7
Web Security Attackers may use any of these tools to install a program on a computer. § Active. X Controls interactivity on web pages § Java Allows applets to run within a browser Example: a calculator or a counter § Java. Script Interacts with HTML source code to allow interactive web sites Example: a rotating banner or a popup window ITE PC v 4. 0 Chapter 9 © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 8
Adware, Spyware, and Grayware § Typically installed without the user’s knowledge, these programs collect information stored on the computer, change the computer configuration, or open extra windows on the computer and all without the user’s consent. ITE PC v 4. 0 Chapter 9 © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 9
Denial of Service (Do. S) § Prevents users from accessing normal services § Sends enough requests to overload a resource or even stopping its operation § Ping of Death is a series of repeated, larger than normal pings intended to crash the receiving computer § E-mail Bomb is a large quantity of bulk e-mail that overwhelms the e-mail server preventing users from accessing e-mail § Distributed Do. S is an attack launched from many computers, called zombies ITE PC v 4. 0 Chapter 9 © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 10
Spam and Popup Windows § Spam is unsolicited email that can be used to send harmful links or deceptive content. § Popups are windows that automatically open and are designed to capture your attention and lead you to advertising sites. Use anti-virus software, options in e-mail software, popup blockers, and common indications of spam to combat these. ITE PC v 4. 0 Chapter 9 © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 11
Social Engineering § Never give out a password § Always ask for the ID of the unknown person § Restrict access of unexpected visitors § Escort all visitors through the facility ITE PC v 4. 0 Chapter 9 © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 12
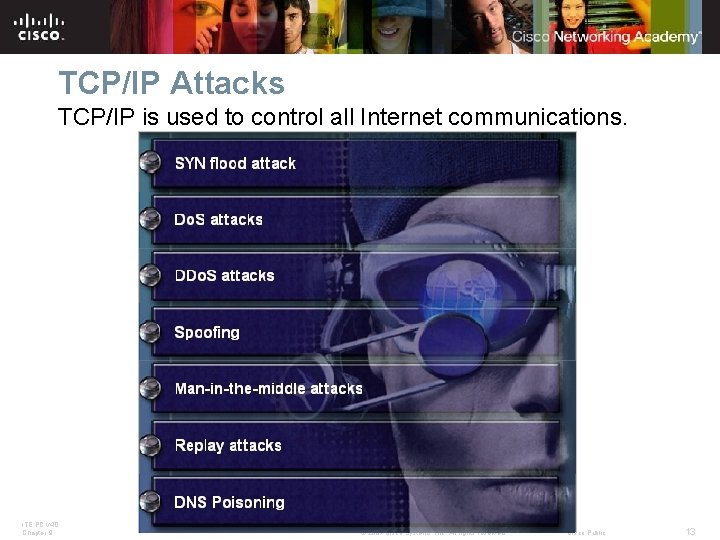
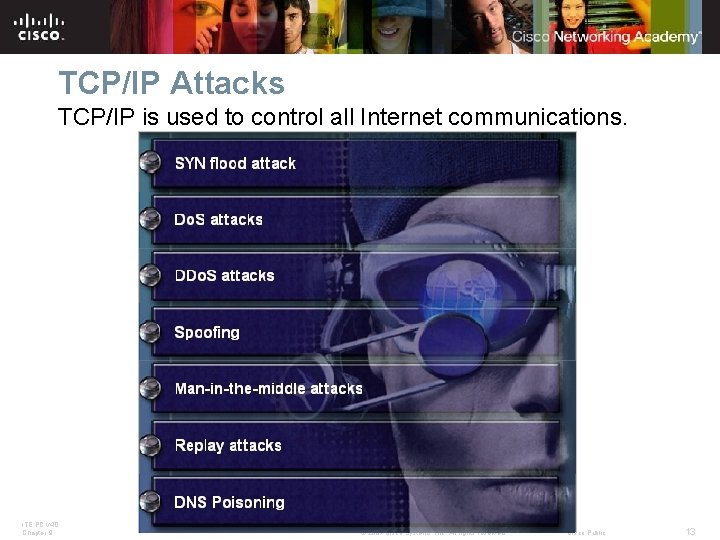
TCP/IP Attacks TCP/IP is used to control all Internet communications. ITE PC v 4. 0 Chapter 9 © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 13
Computer Disposal and Recycling § Erase all hard drives, then use a third-party tool to fully erase all data. § The only way to fully ensure that data cannot be recovered from a hard drive is to carefully shatter the platters with a hammer and safely dispose of the pieces. § To destroy software media (floppy disks and CDs), use a shredding machine designed for shredding these materials. ITE PC v 4. 0 Chapter 9 © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 14
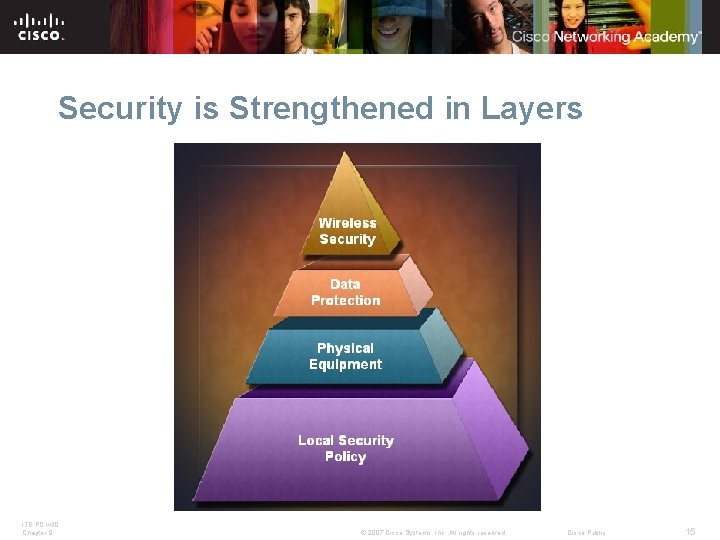
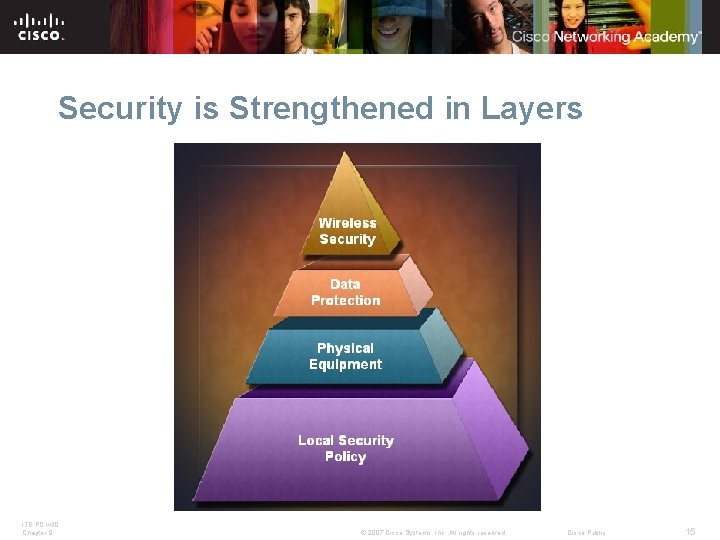
Security is Strengthened in Layers ITE PC v 4. 0 Chapter 9 © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 15
Security Policy Questions to answer in writing a local security policy: § What assets require protection? § What are the possible threats? § What should be done in the event of a security breach? ITE PC v 4. 0 Chapter 9 © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 16
Protecting Equipment Since stealing the whole PC is the easiest way to steal data, physical computer equipment must be secured. § Control access to facilities § Use cable locks § Lock telecommunication rooms § Use security screws § Use security cages around equipment § Label and install sensors on equipment ITE PC v 4. 0 Chapter 9 © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 17
Protecting Data Methods of securing data: § Password protection § Data encryption § Port protection § Data backups § File system security ITE PC v 4. 0 Chapter 9 © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 18
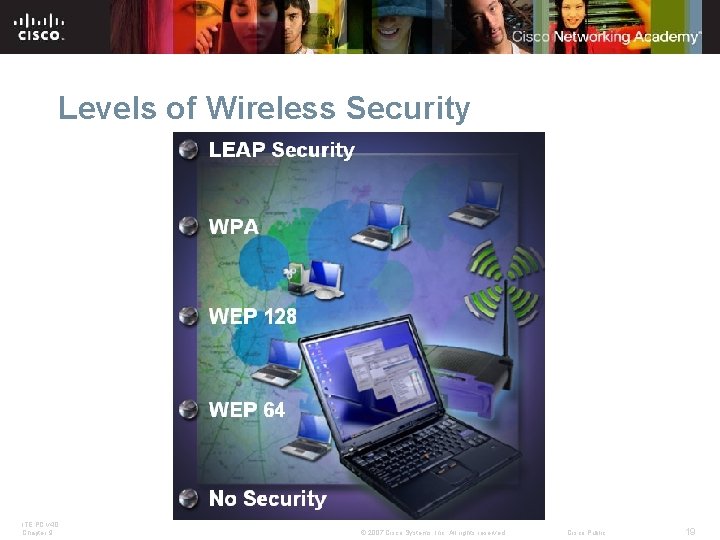
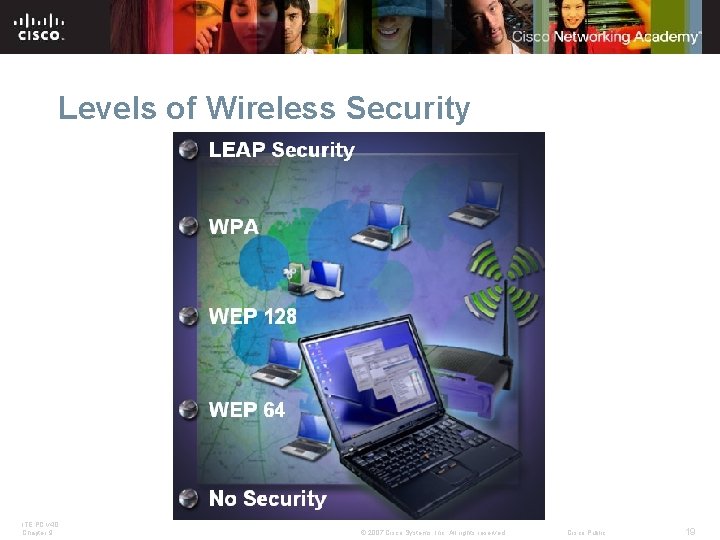
Levels of Wireless Security ITE PC v 4. 0 Chapter 9 © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 19
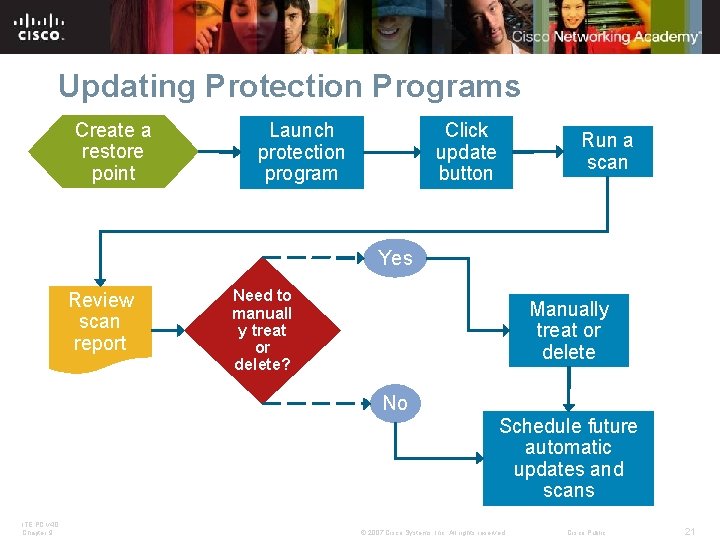
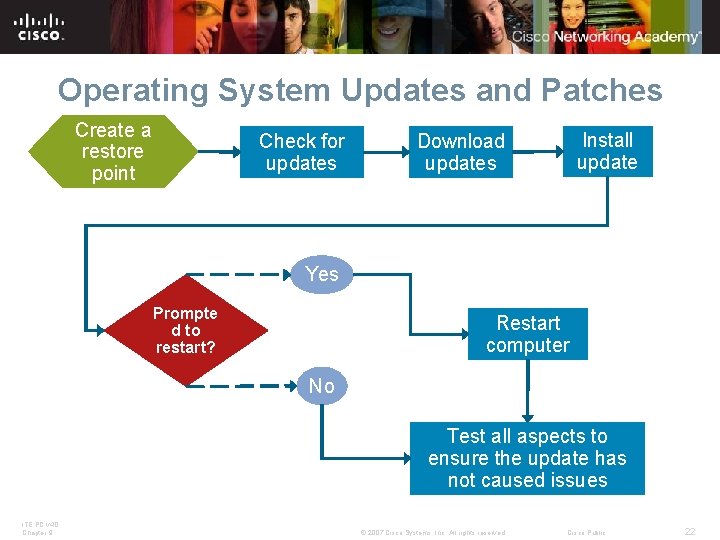
Installing Updates and Patches A technician recognizes when new updates and patches are available and knows how to install them. ITE PC v 4. 0 Chapter 9 © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 20
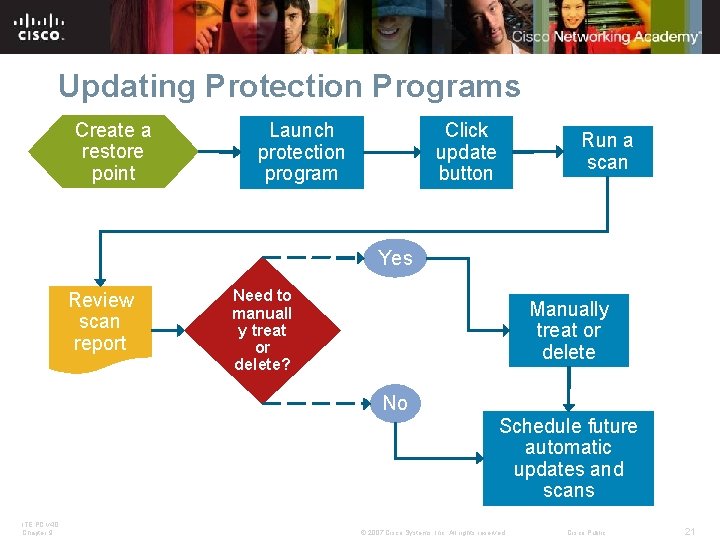
Updating Protection Programs Create a restore point Launch protection program Click update button Run a scan Yes Review scan report Need to manuall y treat or delete? Manually treat or delete No ITE PC v 4. 0 Chapter 9 Schedule future automatic updates and scans © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 21
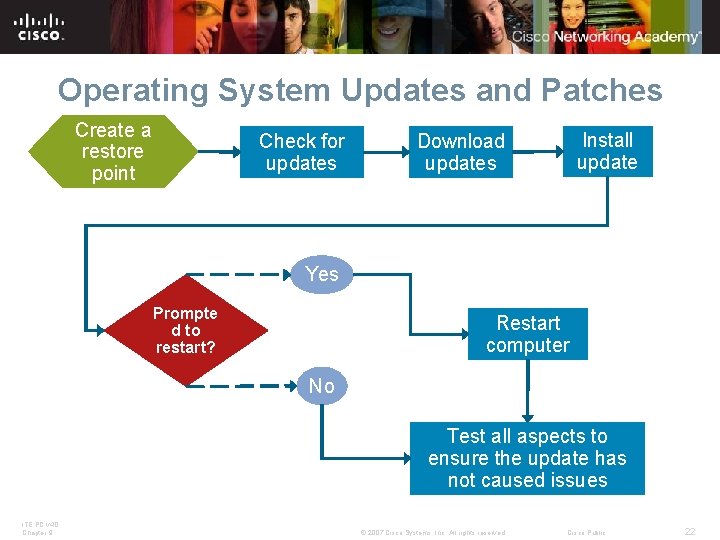
Operating System Updates and Patches Create a restore point Check for updates Install update Download updates Yes Prompte d to restart? Restart computer No Test all aspects to ensure the update has not caused issues ITE PC v 4. 0 Chapter 9 © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 22
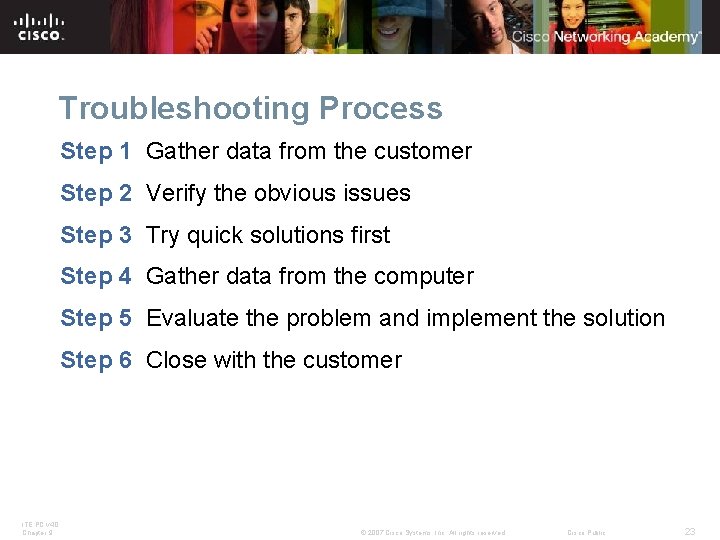
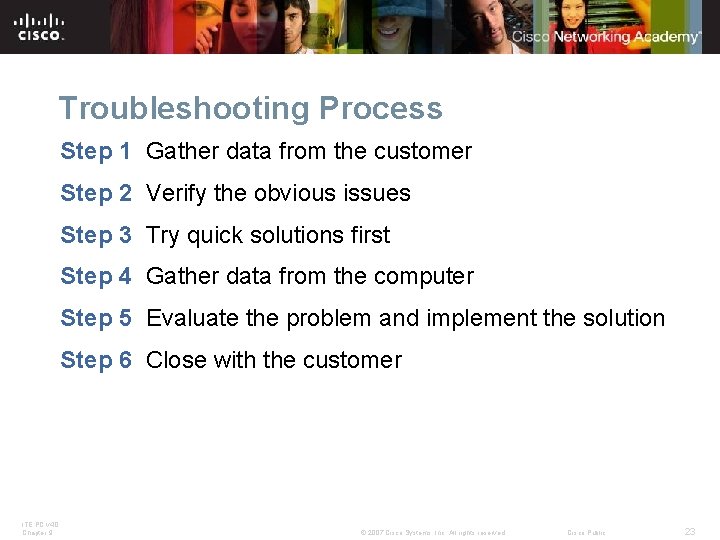
Troubleshooting Process Step 1 Gather data from the customer Step 2 Verify the obvious issues Step 3 Try quick solutions first Step 4 Gather data from the computer Step 5 Evaluate the problem and implement the solution Step 6 Close with the customer ITE PC v 4. 0 Chapter 9 © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 23
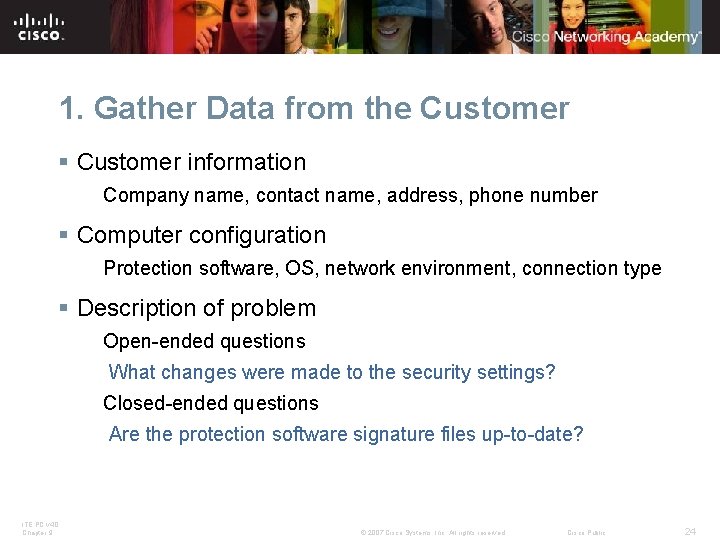
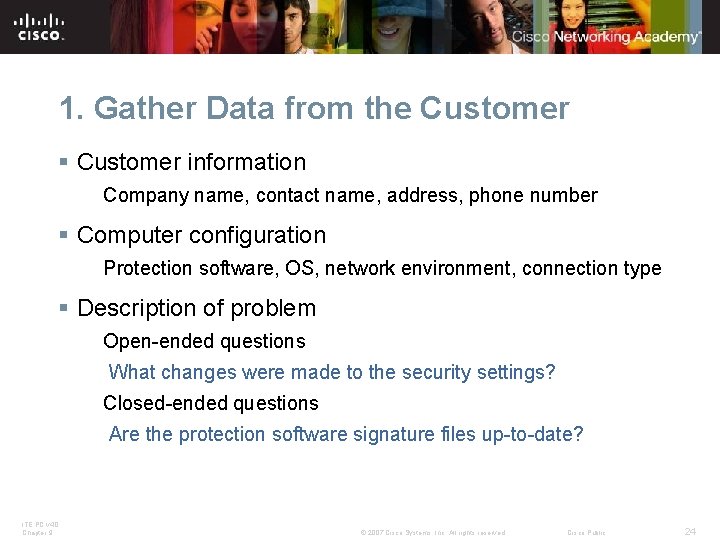
1. Gather Data from the Customer § Customer information Company name, contact name, address, phone number § Computer configuration Protection software, OS, network environment, connection type § Description of problem Open-ended questions What changes were made to the security settings? Closed-ended questions Are the protection software signature files up-to-date? ITE PC v 4. 0 Chapter 9 © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 24
2. Verify the Obvious Issues Examine the most obvious causes of a problem. § A visual inspection can resolve some issues. Broken locks, signs of tampering, missing equipment § Has an attacker accessed the equipment? Unfamiliar login address in login windows, unexplained entries in system security logs, missing or additional patch cords § Wireless network issues Changes in access point configuration, unexplained connections in the access point status display ITE PC v 4. 0 Chapter 9 © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 25

3. Try Quick Solutions First § Check that all cables are connected to the proper locations § Unseat and then reconnect cables and connectors § Reboot the computer or network device § Login as a different user § Check that the anti-virus and spyware signature files are upto-date § Scan computer with protection software § Check computer for the latest OS patches and updates § Disconnect from the network § Change your password ITE PC v 4. 0 Chapter 9 © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 26
4. Gather Data from the Computer § Third-party software, such as anti-virus and antispyware applications, can report on the files that have been infected. § There are several tools available in the operating system that a technician can use: Verify that the signature file is current. Check the security software log file for entries. Task Manager is used to check for unknown applications that are running. ITE PC v 4. 0 Chapter 9 © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 27
5. Evaluate Problem & Implement Solution 1. Evaluate the information gathered from the customer and from the laptop 2. Determine possible solutions 3. Implement the best solution 4. If a proposed solution doesn’t correct the problem, reset the computer back to the original state and try another proposed solution. NOTE: Never ask a customer to reveal a password. ITE PC v 4. 0 Chapter 9 © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 28
6. Close with the Customer § Discuss with customer the solution implemented. § Have customer verify problem is solved. § Provide all paperwork to customer. § Document steps of solution in work order and in technician’s journal. § Document components used in repair. § Document time spent to resolve the problem. ITE PC v 4. 0 Chapter 9 © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 29
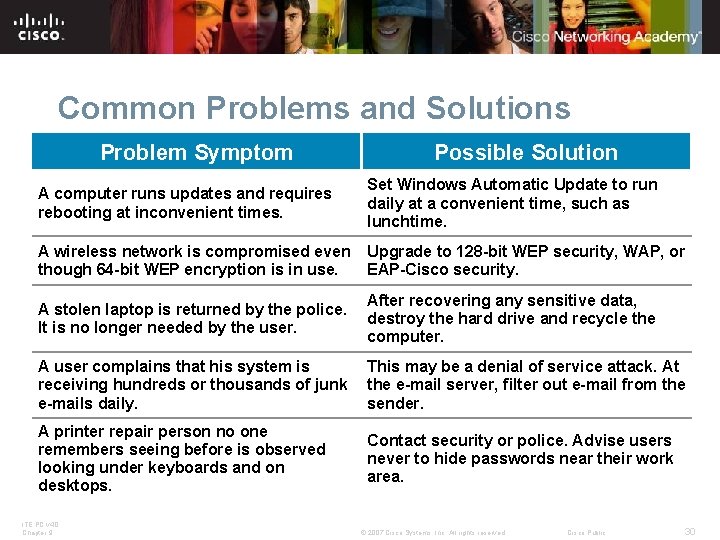
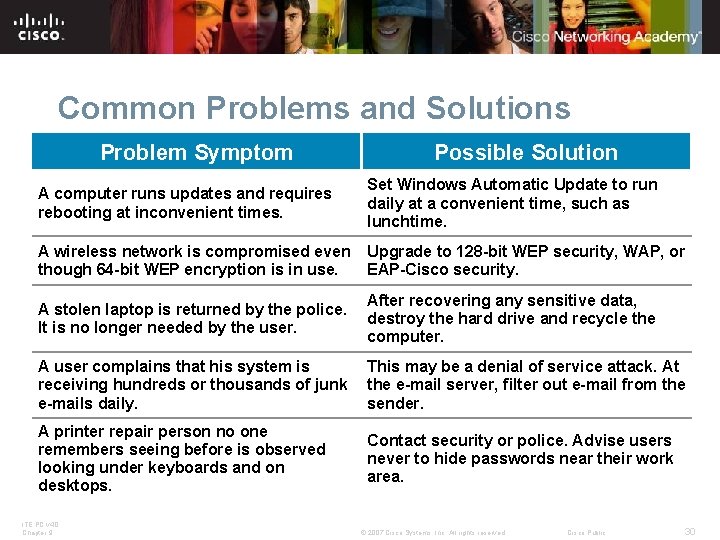
Common Problems and Solutions Problem Symptom Possible Solution A computer runs updates and requires rebooting at inconvenient times. Set Windows Automatic Update to run daily at a convenient time, such as lunchtime. A wireless network is compromised even though 64 -bit WEP encryption is in use. Upgrade to 128 -bit WEP security, WAP, or EAP-Cisco security. A stolen laptop is returned by the police. It is no longer needed by the user. After recovering any sensitive data, destroy the hard drive and recycle the computer. A user complains that his system is receiving hundreds or thousands of junk e-mails daily. This may be a denial of service attack. At the e-mail server, filter out e-mail from the sender. A printer repair person no one remembers seeing before is observed looking under keyboards and on desktops. Contact security or police. Advise users never to hide passwords near their work area. ITE PC v 4. 0 Chapter 9 © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 30
Chapter 9 Summary Following proper security procedures will protect computers and network equipment, and the data they contain, from physical danger such as fire and theft, as well as from loss and damage by employees and attackers. § Security threats can come from inside or outside of an organization. § Viruses and worms are common threats that attack data. § Develop and maintain a security plan to protect both data and physical equipment from loss. § Keep operating systems and applications up to date and secure with patches and service packs. ITE PC v 4. 0 Chapter 9 © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 31
Instructor Training Activities ITE PC v 4. 0 Chapter 9 © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 32
Activities for Instructor Training 1. Take the Quiz provided in Chapter 9 course content. 2. Conduct Internet research to pre-screen online resources for students to use in completing the following student worksheets: 9. 1 Worksheet: Security Attacks 9. 2. 1 Worksheet: Third-Party Anti-Virus Software 9. 4. 2 Worksheet: Operating System Updates 3. Brainstorm a list of at least 4 additional troubleshooting scenarios to provide students more opportunities to practice this skill. ITE PC v 4. 0 Chapter 9 For an example, refer to the student worksheet, 9. 5. 2 Gather Information from the Customer. © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 33
Instructor Training Discussion § Share with the other instructors the list of online resources found that students might use in completing the research activity worksheets. § Share with the other instructors the list of additional troubleshooting scenarios. § Participate in a role-playing activity of one of the troubleshooting scenarios. § Following the role-playing activity, discuss the different ways you might incorporate role-playing activities into your classroom. Share ideas of how to make the student successful in these activities. ITE PC v 4. 0 Chapter 9 © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 34
Additional Resources § Whatis? com: IT Encyclopedia and Learning Center http: //whatis. com § Tech. Target: The Most Targeted IT Media http: //techtarget. com § ZDNet: Tech News, Blogs and White Papers for IT Professionals http: //www. zdnet. com § How. Stuff. Works: It's Good to Know http: //computer. howstuffworks. com § CNET. com http: //www. cnet. com § PC World http: //www. pcworld. com § Computer. World http: //www. computerworld. com § WIRED NEWS http: //www. wired. com § e. WEEK. com http: //www. eweek. com ITE PC v 4. 0 Chapter 9 © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 35
Q and A ITE PC v 4. 0 Chapter 9 © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 36
ITE PC v 4. 0 Chapter 9 © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 37