Chapter 9 Applications Benevolent Malware q Benevolent malware
Chapter 9 Applications
Benevolent Malware q Benevolent malware? o “Obviously a contradiction in terms” o Malware characteristics, but tries to do “good” q Den Zuk --- 1988, removed Brain virus o Later versions would reformat disk… q Cheese --- 2001, remove li 0 n worm o Created lots of network traffic q Welchia --- 2003, patched problem that Blaster exploited (used official MS patch) o Lots of traffic, cure worse than disease
Predator Worms q Like Cheese and Welchia q Destroy malware and/or immunize o o Trying to do good, but it’s still illegal Previous “predators” caused problems Might be OK on local network But how to prevent spread to Internet? q Other technical problems o Control, bandwidth use, monitoring, etc.
Benevolent Malware q No “killer app” for benevolent malware q Everything can be done by more controlled means q Many unresolved issues… o Legal issues o Ethical issues o Technical issues q Mobile agents --- a niche application?
Mobile Agents q Program transfers itself over network o It does things on behalf of a user o For example, propagate to various airline sites in search of best airfare q Questions about mobile agent security o Has a lot in common with malware o A “solution in search of a problem”? o Mobile agents have some advantages, but what they do can be done by other means
Mobile Agents q Previous master’s project q Platform for Privacy Preferences Project (P 3 P) o Privacy policies that websites follow q Student developed an “agent-based privacy enhancing model” o Used agents to analyze P 3 P preferences o Essentially, a reputation system o Research papers are here and here
Spam q Infection may be “means to an end” o For example, DDo. S attacks or q May use zombies/bots for spam o Harvest your email address o Customized spam so that it looks like it came from you , and so on q Aycock has lots of interest in spam o Spam simulator: Spamulator
Access-for-Sale Worms q “Scalable, targeted intrusion” q Compromise machine, install back door q Access to the back door is for sale o o Might, for example, use key for access Can’t allow unauthorized access So, patch flaws once access obtained Good for ID theft, blackmail, etc. q Like a botnet, but single machine(s)
Access-for-Sale Worms q Two 1. “business models” Organized crime o Attacker and cyberthieves work together o Defenses? 2. Disorganized crime o Attacker sells access to cyberthieves o How to advertise? o Defenses?
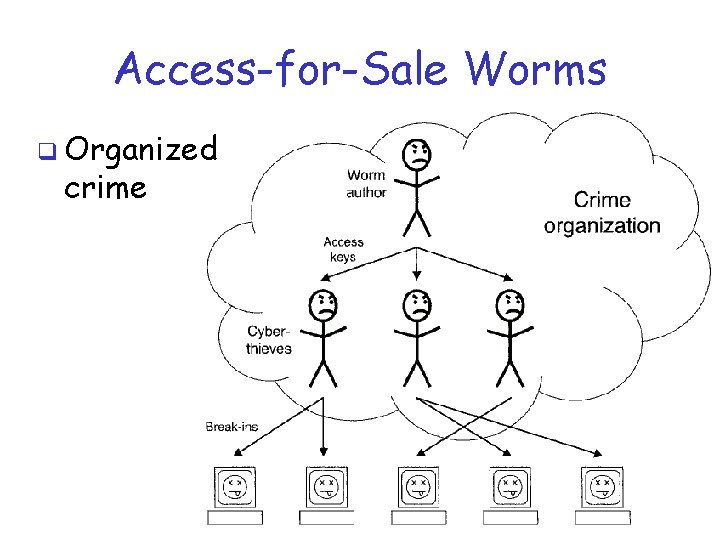
Access-for-Sale Worms q Organized crime
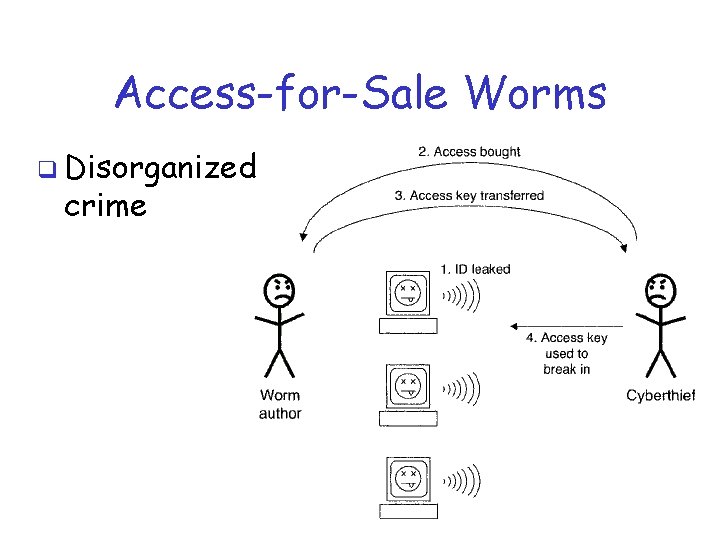
Access-for-Sale Worms q Disorganized crime
Access-for-Sale Worms q Good idea to use public key crypto o That is, worm carries public key, and… o Private key used to access back door q What is the advantage of public key crypto over symmetric key crypto?
Cryptovirology q Use malware for extortion q Example: virus encrypts valuable data o Victim must pay to get decryption key o Again, public key crypto is best here o Note that data encrypted with symmetric key, and symmetric key is encrypted with a public key (we call this “hybrid crypto” in CS 265) o Password-protected may be good enough

Cryptovirology q Examples q AIDS Trojan --- 1989 o Floppy disk, sent by mail, with “curious software license” o Encrypted files if user didn’t pay q PGPCoder Trojan (Gpcode, 2006) o Encrypted files having various extensions o Cost $200 to buy decryptor
Information Warfare q Use computers to supplement (or supplant? ) conventional warfare o Acquire info from adversary’s computers o Plant false info, corrupt data, denial of service, etc. q Laws and such are not clear q Of limited use if communication infrastructure is damaged…

Information Warfare q Electronic countermeasures (ECM) o Deny enemy use of electronic technology o For example, radar jamming q Information warfare analog of ECM? o Denial of service o Comparison with traditional ECM?
Information Warfare q ECM vs Do. S o Persistence --- jamming usually temporary, malware can last longer o Targeting --- ECM uses direct targeting, malware could be direct or indirect o Deception --- possible in both cases o Range of effects --- limited in ECM, much broader with malware (logic bomb, Do. S, precision attack, intelligence gathering, forced quarantine, …)

Information Warfare q ECM vs Do. S o Reliability --- ECM may be more difficult to test, so reliability is less certain o Continuity --- ECM subject to “ECCM”, while malware only has to succeed once and can attack weakest link q Indirect ways to insert malware? o Software vendors, dormant in systems, deliberately leak infected systems, etc.

Cyberterrorism q Difficult to define? q Create fear, not just irritate users o Inability to use facebook does not strike fear of death into (most) users q So cyberterrorist must somehow create tangible results in real world o Nuclear power plants, utility grid, … ? ? ?
Cyberterrorism q Similar uses as info warfare o That is, supplement to real attacks o For example, attack communication infrastructure during physical attack to delay response, cause confusion, etc. q Disinformation attack q Other? before and during
- Slides: 20