CHAPTER 7 PRIVACY CRIME AND SECURITY Privacy in
- Slides: 17
CHAPTER 7: PRIVACY, CRIME, AND SECURITY
Privacy in Cyberspace 2 Privacy: an individual’s ability to restrict or eliminate the collection, use and sale of confidential personal information The problem: collection of information without consent Anonymity: the ability to convey a message without disclosing your name or identity
Privacy in Cyberspace 3 Cookies: small files that are written to your computer’s hard disk by many of the Web sites you visit
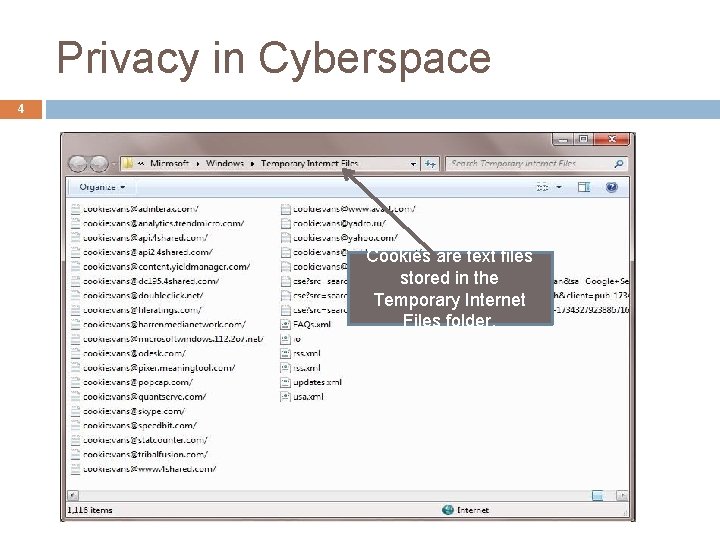
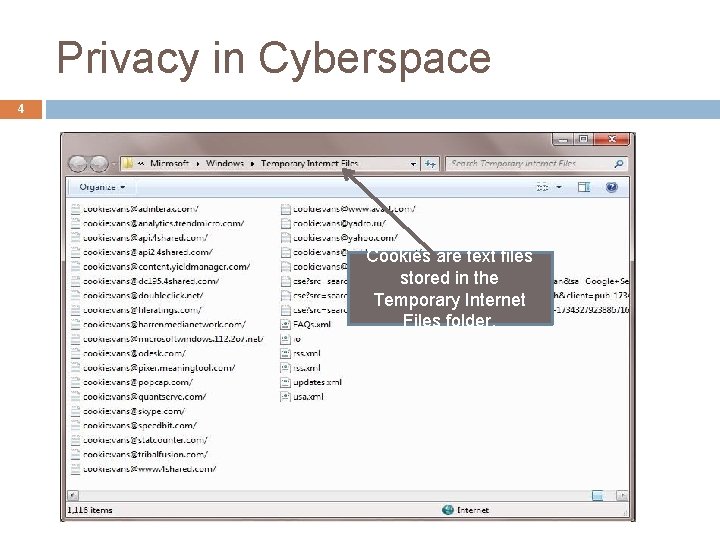
Privacy in Cyberspace 4 Cookies are text files stored in the Temporary Internet Files folder.
Privacy in Cyberspace 5 Global Unique Identifier (GUID): an identification number that is generated by a hardware component or a program
Protecting Your Privacy 6 Browse anonymously by surfing from www. anonymizer. com Disable cookies on your Web browser Use a free e-mail address to place on Web pages, mailing lists, chat rooms, or other public Internet spaces Do not fill out site registration forms unless you see a privacy statement indicating that the information gathered will not be sold to 3 rd parties
Types of Computer Crime 7 Identity Theft Computer Virus: a hidden code within a program that may damage or destroy infected files v Example: Typically, virus infections spread when an infected file or program is downloaded onto a computer. When the program is executed, the viruses spreads to other programs on the user s hard disk. If you copy a file on your computer to a USB drive, CD, or DVD and give it to someone, the infection spreads even further. Time Bomb (Logic Bomb): a virus that sits harmlessly on a system until a certain event causes the program to become active
Types of Computer Crime 8 Worm: a program that can spread from one computer to another and can propagate over a computer network Trojan Horse: a rogue program disguised as a useful program but contains hidden instructions to perform a malicious task instead
Types of Computer Crime 9 Salami Shaving: a method that a programmer alters a program to subtract a very small amount of money from an account and divests the funds to the embezzler’s account Data Diddling: a method that insiders modify data by altering accounts or database records so that it is difficult to tell that they have stolen funds or equipments Forgery: a method that a user makes Internet data appear to come from one place when it is really coming from another Blackmail
Attackers 10 Hackers, Crackers (Black hats), Cybergangs, Virus Authors, Ethical Hackers (White Hats) Swindlers Shills
Security Risks 11 Wireless Network War Driving: an individual drives around with a wireless device to look for wireless networks Corporate Espionage: the unauthorized access of corporate information, usually to the benefit of a competitor Information Warfare: the use of information technologies to corrupt or destroy an enemy’s information and infrastructure Security Loophole Detection Program: a program that automatically search for unprotected or poorly protected computers
Protecting Computer Systems 12 Power-Related Problems: by using Uninterruptible Power Supply (UPS) Controlling Access: by using password authentication, know-and-have authentication, or biometric authentication Firewall: a computer program or device that permits an organization’s internal computer users to access the T. Ibtissem Ajmi external Internet but severely limits the ability of
Protecting Computer Systems 13 Avoiding Scams Preventing Cyber stalking T. Ibtissem Ajmi
Encryption 14 Encryption: a coding or scrambling process that renders a message unreadable by anyone except the intended recipient Public Key Encryption Key (Public Key) Decryption Key (Private Key) T. Ibtissem Ajmi
Encryption 15 Digital Signature: a technique that guarantees a message has not been tampered with
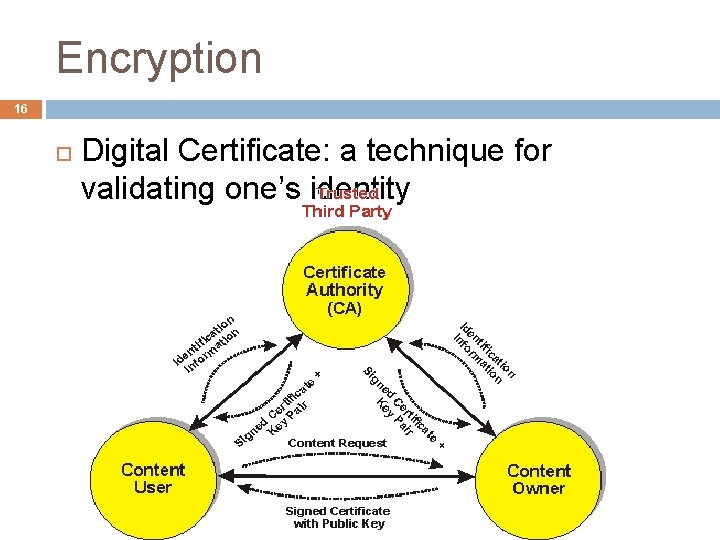
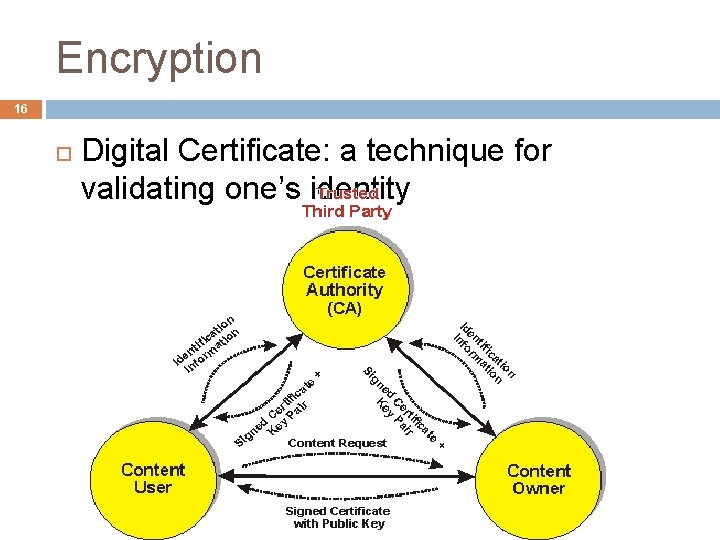
Encryption 16 Digital Certificate: a technique for validating one’s identity
Encryption 17 Public Key Infrastructure (PKI): a uniform set of encryption standards that specify how public key encryption, digital signatures, digital certificates should be implemented in computer systems and on the Internet