CHAPTER 7 Administering Security Objectives explain the concept
CHAPTER 7 Administering Security
Objectives explain the concept of security in administration explain the needs of security planning in secured computing system list and explain the characteristics of security plan design a IT security plan for an organization explain about risk analysis and its importance in obtaining a secured system list and explain various policies, procedures and a range of technical controls in physical security
In this chapter we complete our study of security controls by considering administrative and physical aspects. We look at four related areas: Planning. What advance preparation and study lets us know that our implementation meets our security needs for today and tomorrow? Risk analysis. How do we weigh the benefits of controls against their costs, and how do we justify any controls? Policy. How do we establish a framework to see that our computer security needs continue to be met? Physical control. What aspects of the computing environment have an impact on security?
Security Planning A security plan is a document that describes how an organization will address its security needs. The plan is subject to periodic review and revision as the organization's security needs change. Contents of a Security Plan policy , indicating the goals of a computer security effort and the willingness of the people involved to work to achieve those goals current state , describing the status of security at the time of the plan requirements, recommending ways to meet the security goals recommended controls , mapping controls to the vulnerabilities identified in the policy and requirements accountability , describing who is responsible for each security activity timetable , identifying when different security functions are to be done continuing attention , specifying a structure for periodically
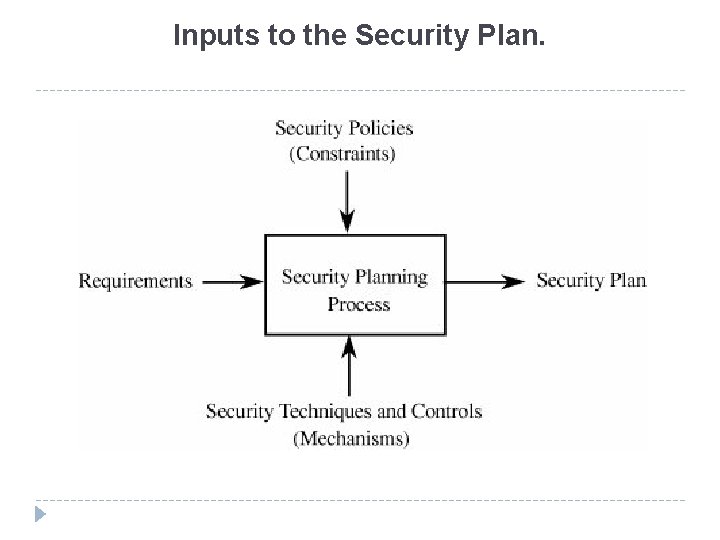
Inputs to the Security Plan.
the security planning process must allow customers or users to specify desired functions, independent of the implementation. The requirements should address all aspects of security: confidentiality, integrity, and availability make sure that the requirements have these characteristics: Correctness: Are the requirements understandable? Are they stated without error? Consistency: Are there any conflicting or ambiguous requirements? Completeness: Are all possible situations addressed by the requirements? Realism: Is it possible to implement what the requirements mandate ? Need: Are the requirements unnecessarily restrictive ? Verifiability: Can tests be written to demonstrate conclusively and objectively that the requirements have been met? Can the system or its functionality be measured in some way that will assess the degree to which the requirements are met? Traceability: Can each requirement be traced to the functions and data related to it so that changes in a requirement can lead to easy reevaluation ?
Risk Analysis Good, effective security planning includes a careful risk analysis. A risk is a potential problem that the system or its users may experience. distinguish a risk from other project events by looking for three things: A loss associated with an event. The likelihood that the event will occur The degree to which we can change the outcome
three strategies for dealing with risk: 1. avoiding the risk, by changing requirements for security or other system characteristics 2. transferring the risk, by allocating the risk to other systems, people, organizations, or assets; or by buying insurance to cover any financial loss should the risk become a reality 3. assuming the risk, by accepting it, controlling it with available resources, and preparing to deal with the loss if it occurs
Organizational Security Policies A security policy is a high-level management document to inform all users of the goals of and constraints on using a system A security policy must answer three questions: who can access which resources in what manner ?
Characteristics of a Good Security Policy Coverage -A security policy must be comprehensive: It must either apply to or explicitly exclude all possible situations Durability -A security policy must grow and adapt well. In large measure, it will survive the system's growth and expansion without change Realism -The policy must be realistic. That is, it must be possible to implement the stated security requirements with existing technology Usefulness -An obscure or incomplete security policy will not be implemented properly, if at all. The policy must be written in language that can be read, understood, and followed by anyone who must implement it or is affected by it
Physical Security Physical security is the term used to describe protection needed outside the computer system.
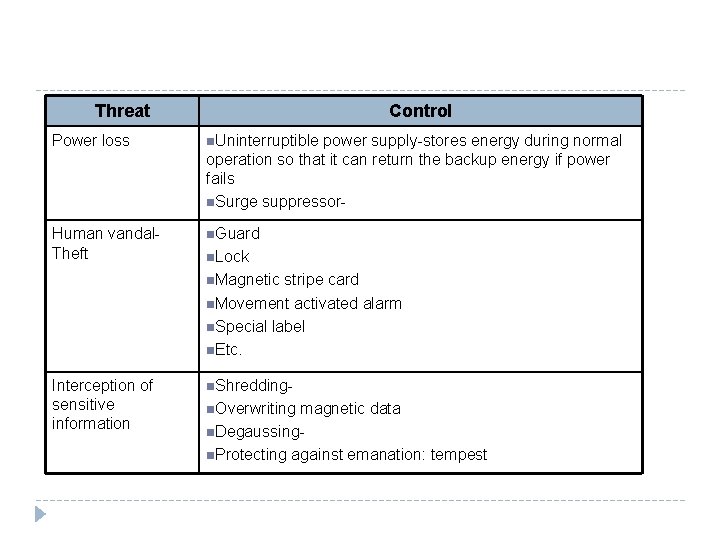
Threat Control Power loss n. Uninterruptible power supply-stores energy during normal operation so that it can return the backup energy if power fails n. Surge suppressor- Human vandal. Theft n. Guard n. Lock n. Magnetic stripe card n. Movement activated alarm n. Special label n. Etc. Interception of sensitive information n. Shreddingn. Overwriting magnetic data n. Degaussingn. Protecting against emanation: tempest
Contingency Planning Backup -is a copy of all or a part of a file to assist in reestablishing a lost file revolving backups , in which the last several backups are kept. Each time a backup is done, the oldest backup is replaced with the newest one. selective backup , in which only files that have been changed (or created) since the last backup are saved.
Offsite Backup -Keeping a backup version separate from the actual system reduces the risk of its loss. Networked Storage -Storage providers sell space in which you can store data Cold Site- is a facility with power and cooling available, in which a computing system can be installed to begin immediate operation Hot site- is a computer facility with an installed and ready-to-run computing system.
- Slides: 14