CHAPTER 6 MAC PROTOCOLS IFA 07 MILANO 1

- Slides: 80
CHAPTER 6. MAC PROTOCOLS IFA’ 07 MILANO 1
Objectives of MAC Protocols * * * * IFA’ 07 Collision Avoidance Energy Efficiency Scalability Latency Fairness Throughput Bandwidth Utilization MILANO 2
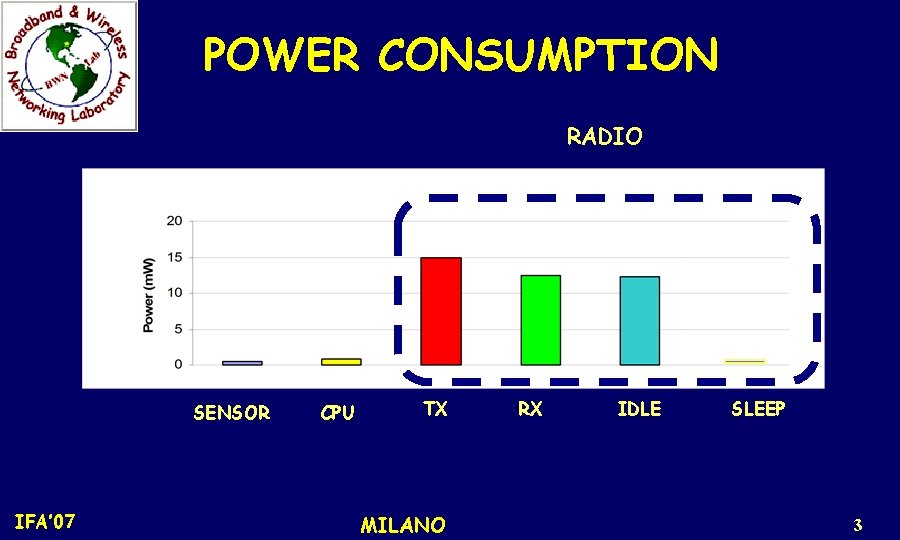
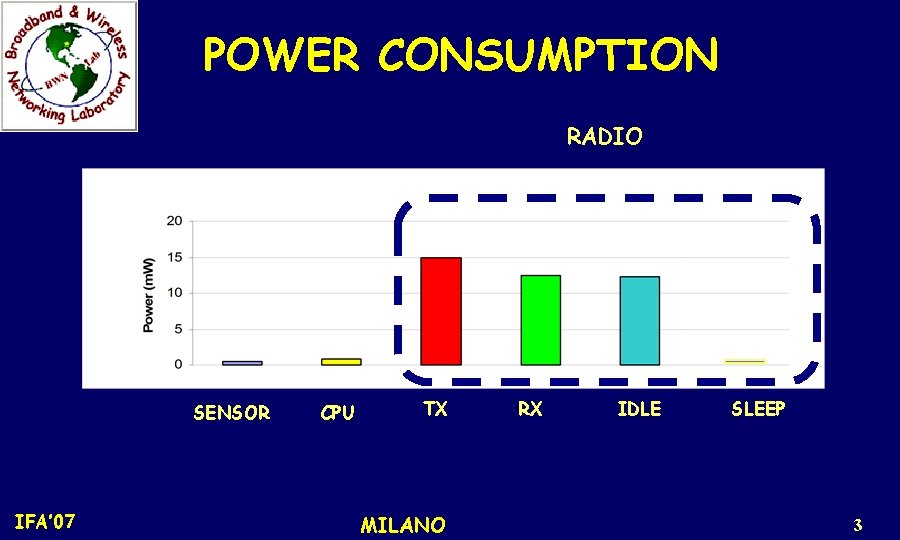
POWER CONSUMPTION RADIO SENSOR IFA’ 07 CPU TX MILANO RX IDLE SLEEP 3
Major Sources of Energy Waste * Idle Listening * Transmitter * Receiver Common to all wireless networks OBJECTIVE: Reduce energy consumption !! IFA’ 07 MILANO 4
Challenges for MAC in WSNs 1. WSN Architecture –High density of nodes –Increased collision probability –Signaling overhead should be minimized to prevent further collisions –Sophisticated and simple collision avoidance protocols required IFA’ 07 MILANO 5
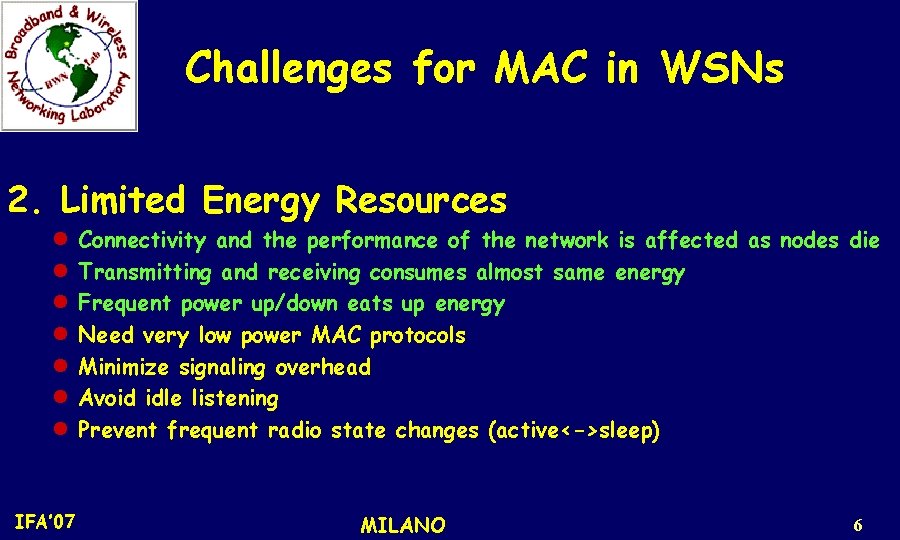
Challenges for MAC in WSNs 2. Limited Energy Resources l l l l IFA’ 07 Connectivity and the performance of the network is affected as nodes die Transmitting and receiving consumes almost same energy Frequent power up/down eats up energy Need very low power MAC protocols Minimize signaling overhead Avoid idle listening Prevent frequent radio state changes (active<->sleep) MILANO 6
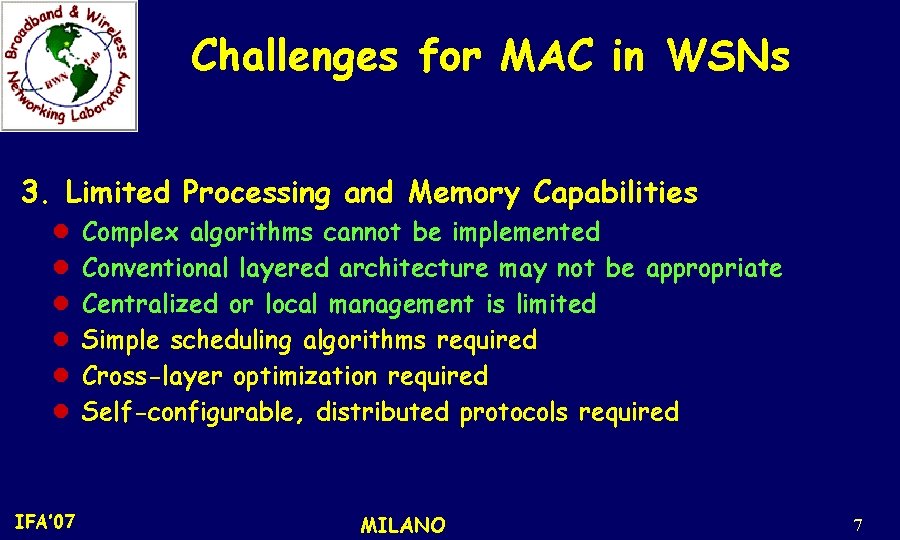
Challenges for MAC in WSNs 3. Limited Processing and Memory Capabilities l l l IFA’ 07 Complex algorithms cannot be implemented Conventional layered architecture may not be appropriate Centralized or local management is limited Simple scheduling algorithms required Cross-layer optimization required Self-configurable, distributed protocols required MILANO 7
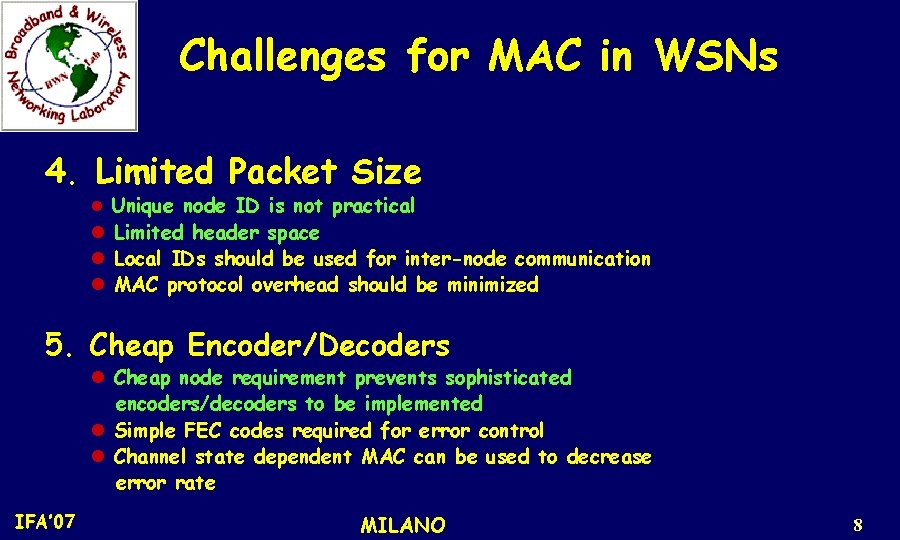
Challenges for MAC in WSNs 4. Limited Packet Size l Unique node ID is not practical l Limited header space Local IDs should be used for inter-node communication MAC protocol overhead should be minimized 5. Cheap Encoder/Decoders l Cheap node requirement prevents sophisticated encoders/decoders to be implemented l Simple FEC codes required for error control l Channel state dependent MAC can be used to decrease error rate IFA’ 07 MILANO 8
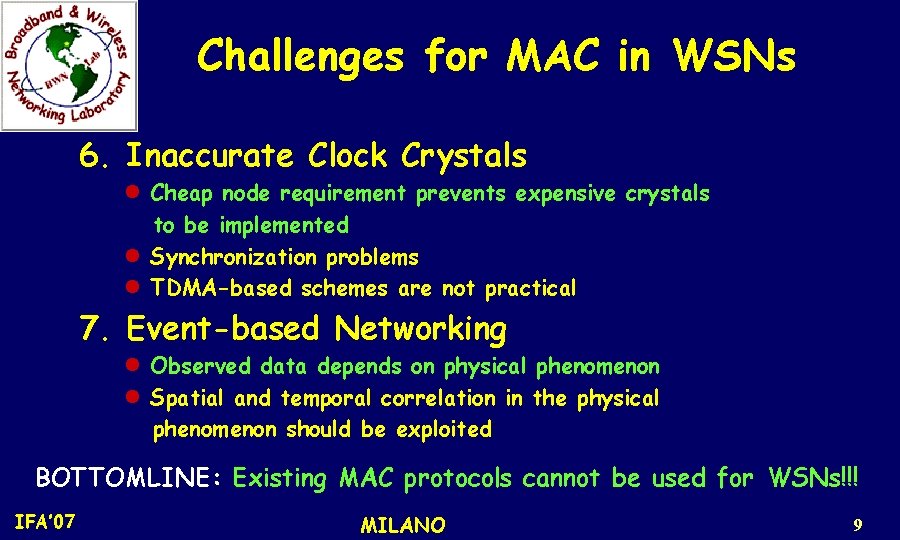
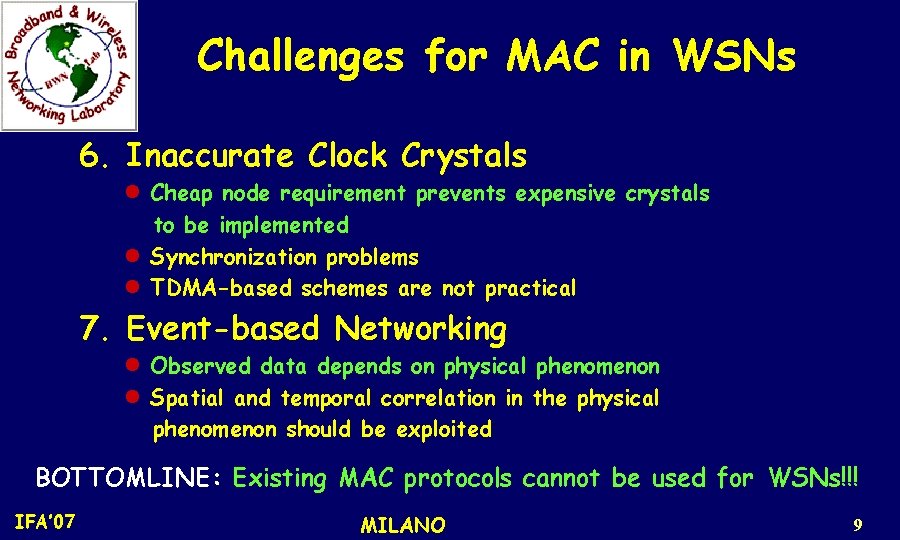
Challenges for MAC in WSNs 6. Inaccurate Clock Crystals l Cheap node requirement prevents expensive crystals to be implemented l Synchronization problems l TDMA-based schemes are not practical 7. Event-based Networking l Observed data depends on physical phenomenon l Spatial and temporal correlation in the physical phenomenon should be exploited BOTTOMLINE: Existing MAC protocols cannot be used for WSNs!!! IFA’ 07 MILANO 9
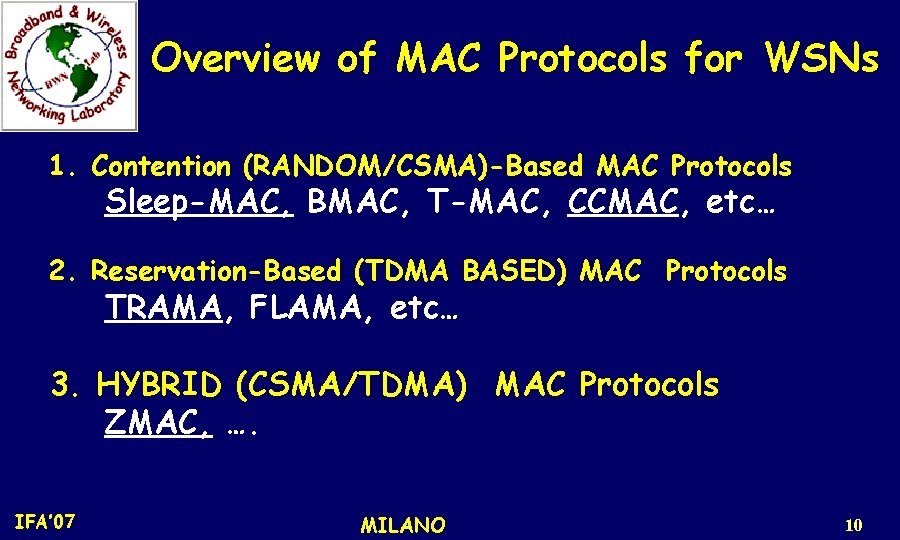
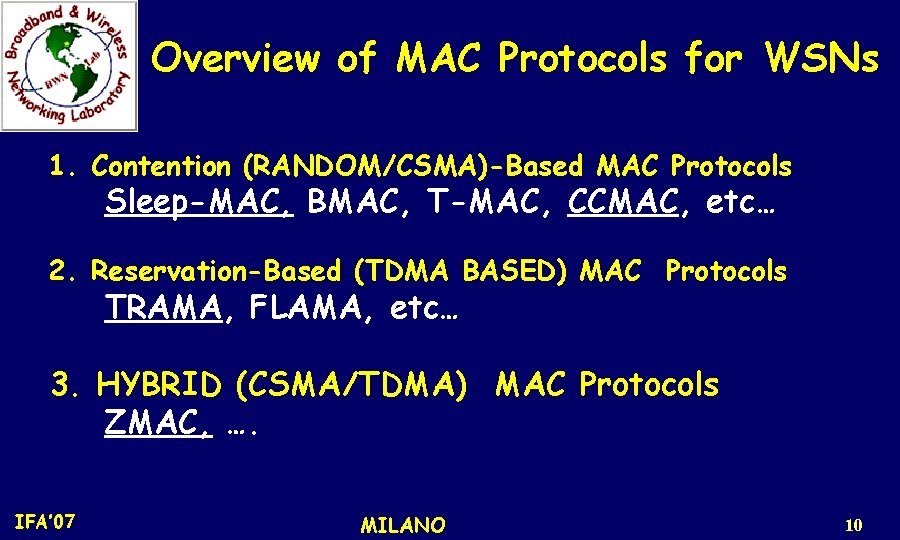
Overview of MAC Protocols for WSNs 1. Contention (RANDOM/CSMA)-Based MAC Protocols Sleep-MAC, BMAC, T-MAC, CCMAC, etc… 2. Reservation-Based (TDMA BASED) MAC Protocols TRAMA, FLAMA, etc… 3. HYBRID (CSMA/TDMA) MAC Protocols ZMAC, …. IFA’ 07 MILANO 10
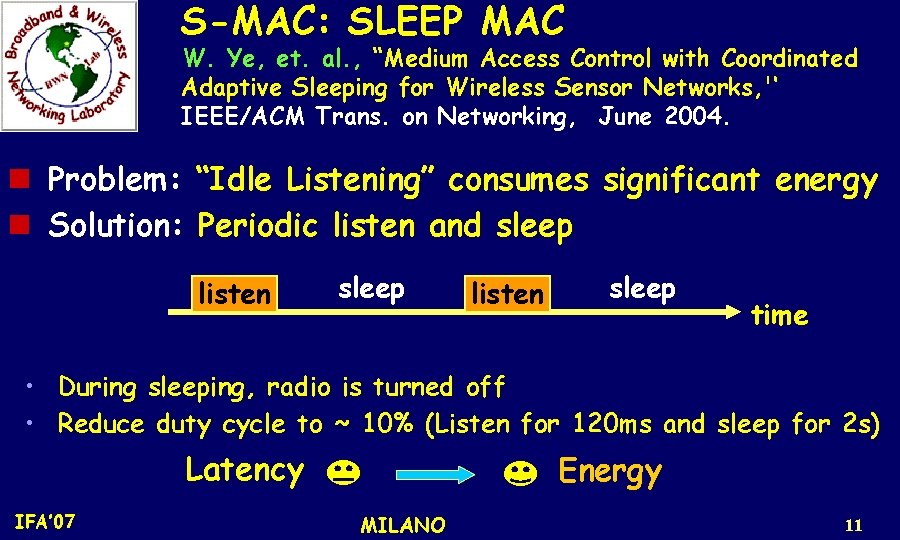
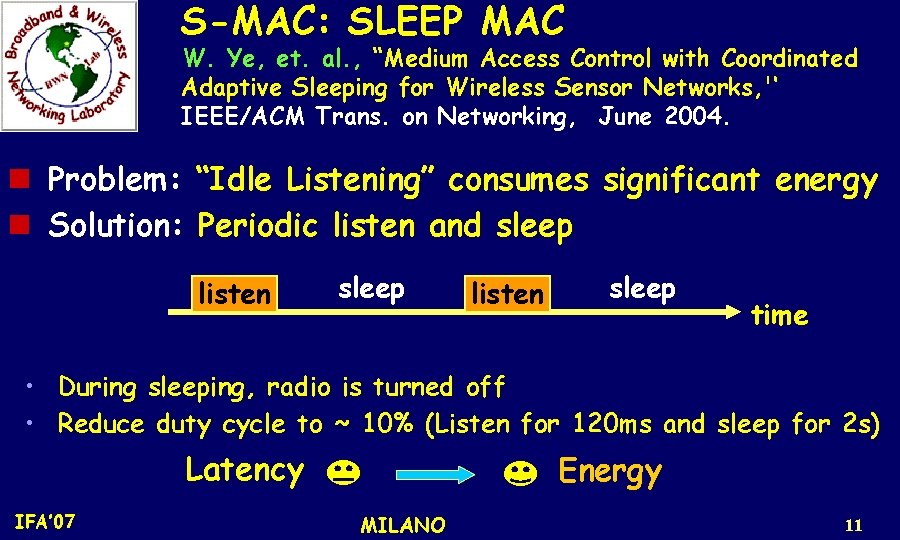
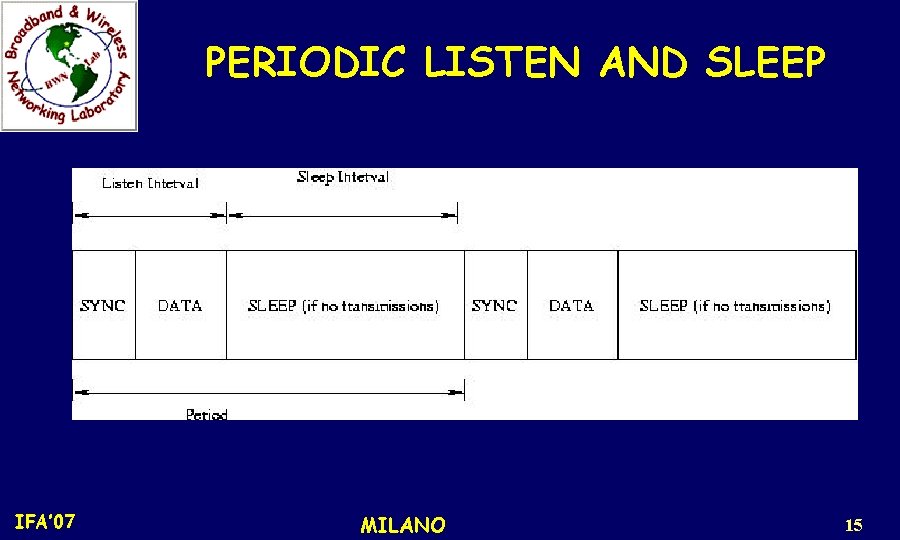
S-MAC: SLEEP MAC W. Ye, et. al. , “Medium Access Control with Coordinated Adaptive Sleeping for Wireless Sensor Networks, '‘ IEEE/ACM Trans. on Networking, June 2004. n Problem: “Idle Listening” consumes significant energy n Solution: Periodic listen and sleep listen sleep time • During sleeping, radio is turned off • Reduce duty cycle to ~ 10% (Listen for 120 ms and sleep for 2 s) Latency IFA’ 07 Energy MILANO 11
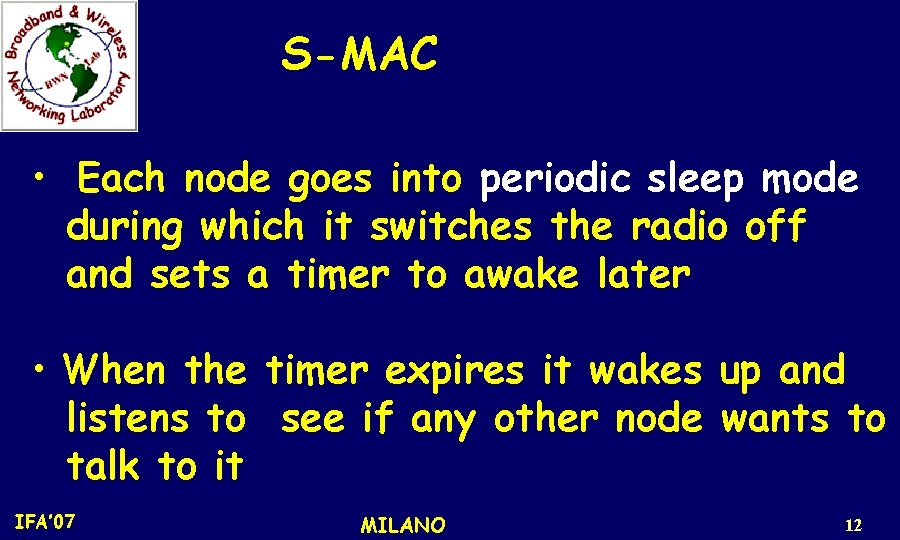
S-MAC • Each node goes into periodic sleep mode during which it switches the radio off and sets a timer to awake later • When the timer expires it wakes up and listens to see if any other node wants to talk to it IFA’ 07 MILANO 12
S-MAC • The duration of the sleep and listen cycles are application dependent and they are set the same for all nodes * Requires a periodic synchronization among nodes to take care of any type of clock drift IFA’ 07 MILANO 13
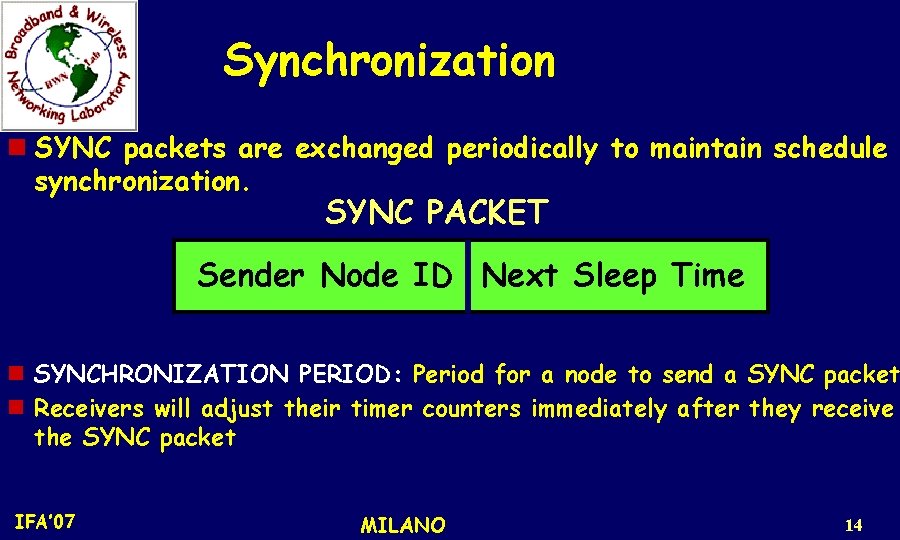
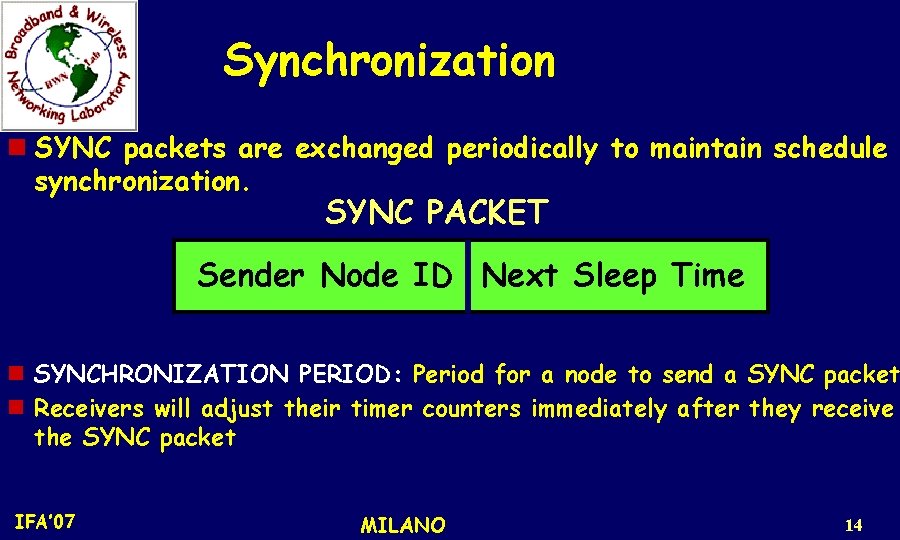
Synchronization n SYNC packets are exchanged periodically to maintain schedule synchronization. SYNC PACKET Sender Node ID Next Sleep Time n SYNCHRONIZATION PERIOD: Period for a node to send a SYNC packet n Receivers will adjust their timer counters immediately after they receive the SYNC packet IFA’ 07 MILANO 14
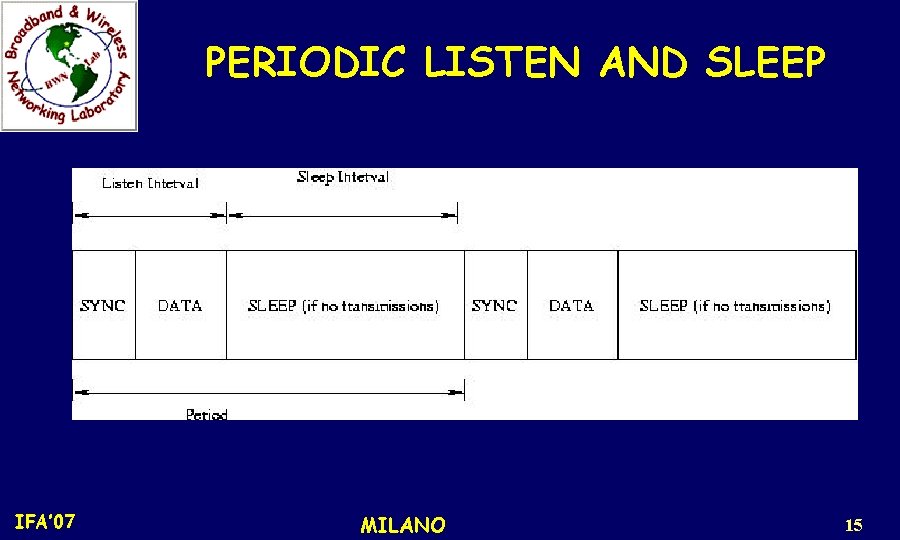
PERIODIC LISTEN AND SLEEP IFA’ 07 MILANO 15
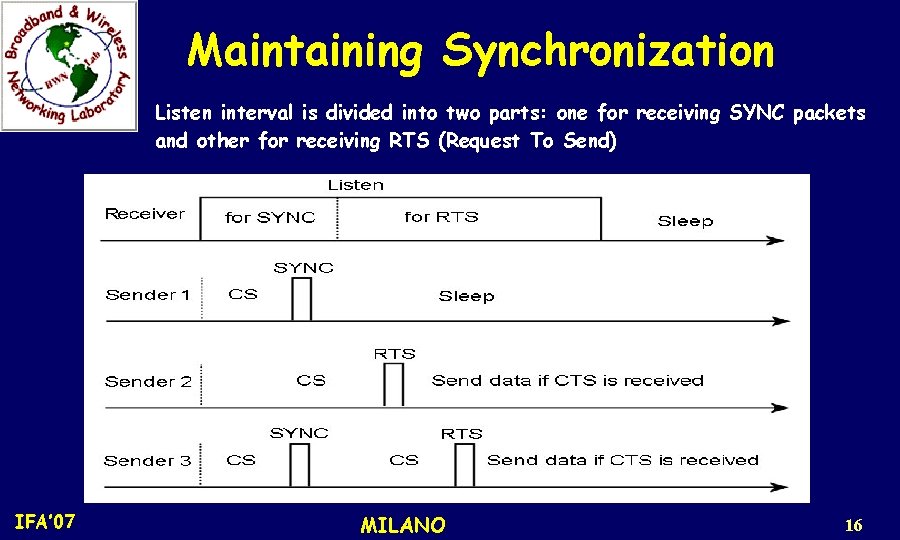
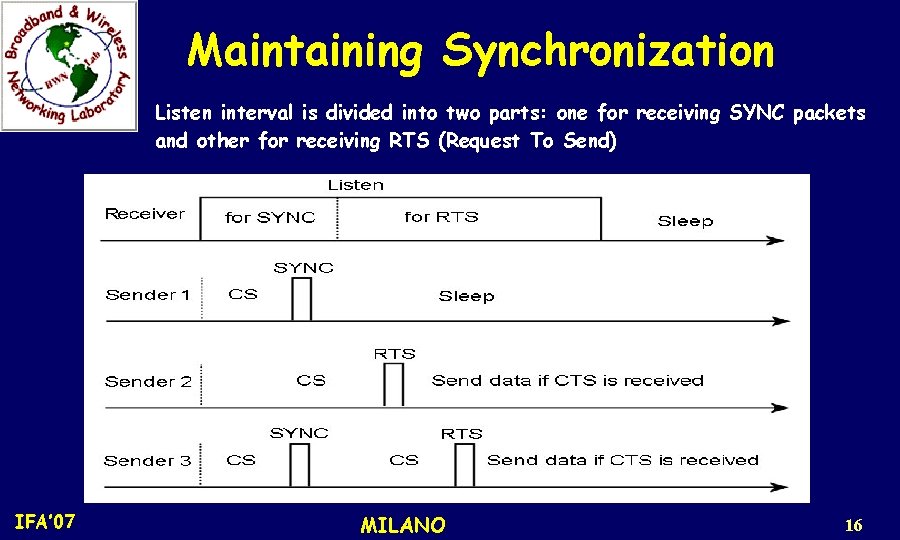
Maintaining Synchronization Listen interval is divided into two parts: one for receiving SYNC packets and other for receiving RTS (Request To Send) IFA’ 07 MILANO 16
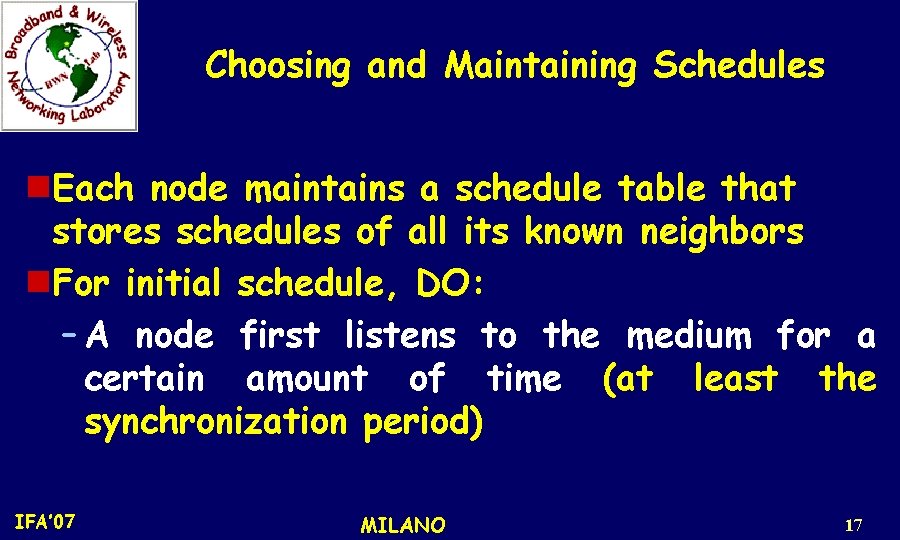
Choosing and Maintaining Schedules n. Each node maintains a schedule table that stores schedules of all its known neighbors n. For initial schedule, DO: – A node first listens to the medium for a certain amount of time (at least the synchronization period) IFA’ 07 MILANO 17
Choosing and Maintaining Schedules – If it does not hear a schedule from another node, it randomly chooses a schedule and broadcasts its schedule with a SYNC packet immediately – This node is called a Synchronizer IFA’ 07 MILANO 18
Choosing and Maintaining Schedules – If a node receives a schedule from a neighbor before choosing its own schedule, it just follows this neighbor’s schedule, i. e. becomes a Follower and it waits for a random delay and broadcasts its schedule IFA’ 07 MILANO 19
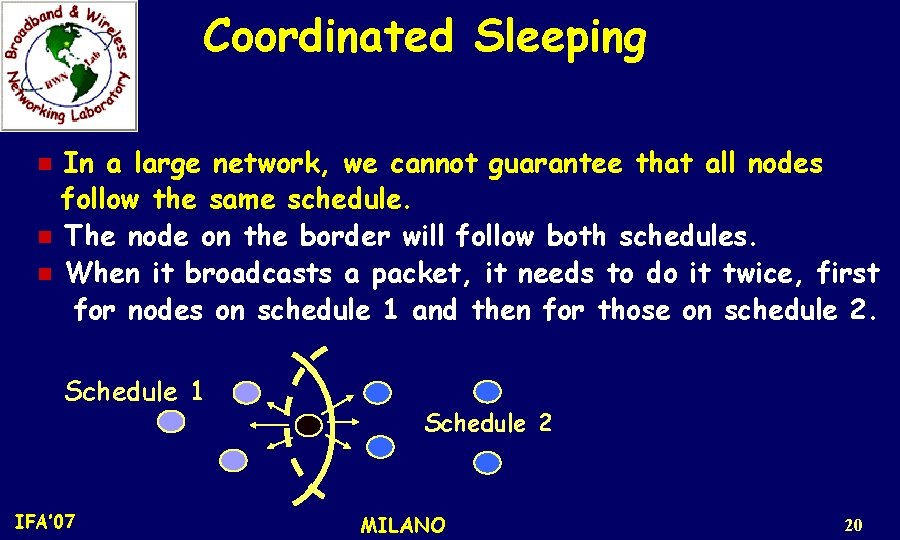
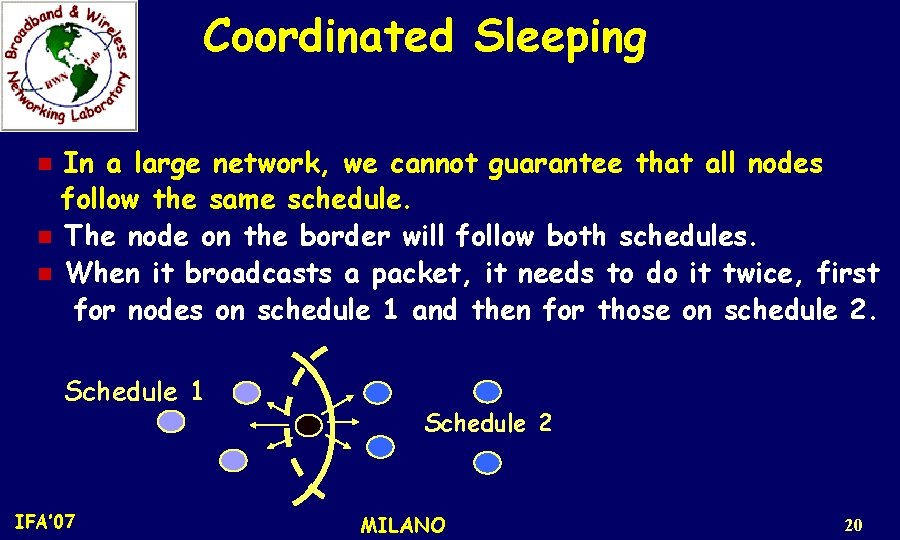
Coordinated Sleeping In a large network, we cannot guarantee that all nodes follow the same schedule. n The node on the border will follow both schedules. n When it broadcasts a packet, it needs to do it twice, first for nodes on schedule 1 and then for those on schedule 2. n Schedule 1 IFA’ 07 Schedule 2 MILANO 20
Border Nodes * Border nodes have less time to sleep and consume more energy than others. OPTION: Let border node adopt only one schedule (received first). IFA’ 07 MILANO 21
Collision Avoidance n S-MAC is based on contention, i. e. , if multiple neighbors want to talk to a node at the same time, they will try to send when the node starts listening. * Similar to IEEE 802. 11, i. e. use RTS/CTS mechanism to address the hidden terminal problem * Perform carrier sense before initiating a transmission IFA’ 07 MILANO 22
Collision Avoidance * If a node fails to get the medium, it goes to sleep and wakes up when the receiver is free and listening again * Broadcast packets are sent without using RTS/CTS. * Unicast data packets follow the sequence of RTS/CTS/DATA/ACK between the sender and receiver IFA’ 07 MILANO 23
Collision Avoidance * Duration field in each transmitted packet indicates how long the remaining transmission will be so if a node receives a packet destined to another node, it knows how long it has to keep silent * The node records this value in network allocation vector (NAV) and sets a timer for it IFA’ 07 MILANO 24
Collision Avoidance * When a node has data to send, it first looks at NAV. * If this value is not zero, then medium is busy (virtual carrier sense) IFA’ 07 MILANO 25
Collision Avoidance * The medium is determined as free if both virtual and physical carrier sense indicate the medium is free * All immediate neighbors of both the sender and receiver should sleep after they hear RTS or CTS packet until the current transmission is over IFA’ 07 MILANO 26
Adaptive Listening Feature - Reduce multi-hop latency due to periodic sleep BASIC IDEA: Let the node who overhears its neighbor’s transmission stay awake IFA’ 07 MILANO 27
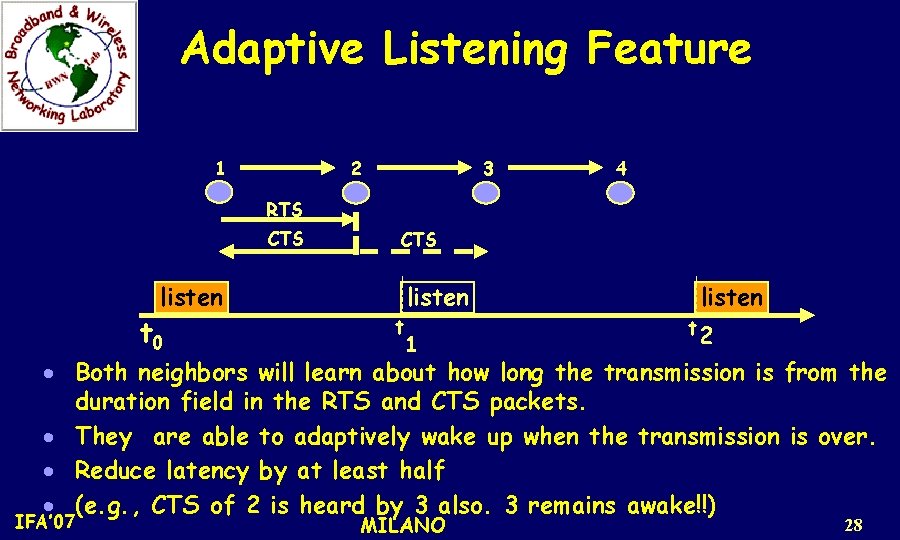
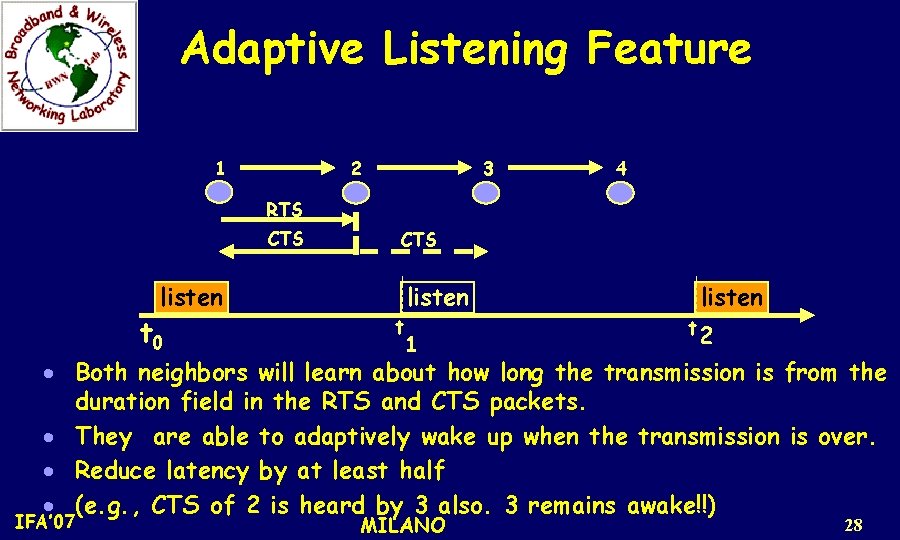
Adaptive Listening Feature 2 1 3 4 RTS CTS listen t 0 CTS t listen 1 listen t 2 · Both neighbors will learn about how long the transmission is from the duration field in the RTS and CTS packets. · They are able to adaptively wake up when the transmission is over. · Reduce latency by at least half · (e. g. , CTS of 2 is heard by 3 also. 3 remains awake!!) IFA’ 07 MILANO 28
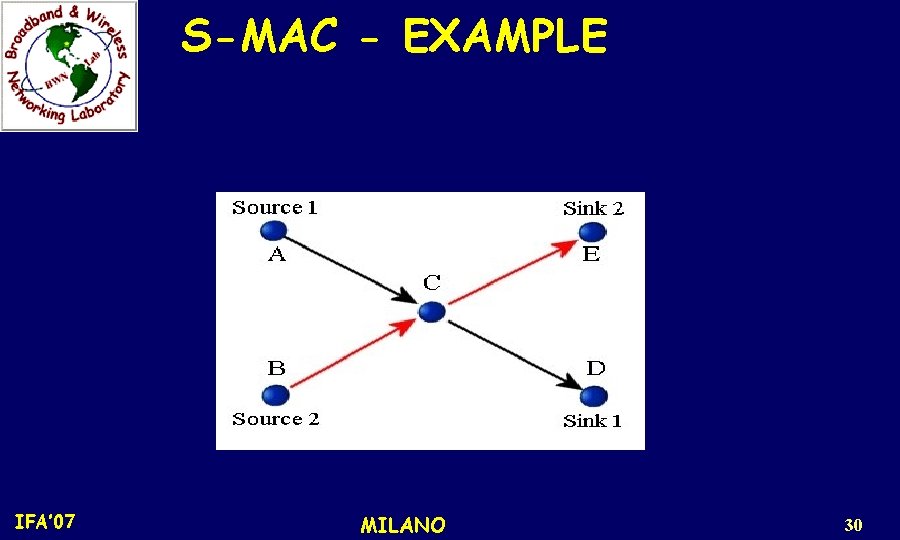
S-MAC - EXAMPLE Topology • Two-hop network with two sources and two sinks • Sources periodically generate a sensing message which is divided into fragments * Traffic load is changed by varying the inter-arrival period of the messages: (for inter-arrival period of 5 s, message is generated every 5 s by each source. Here it varies between 1 -10 s). IFA’ 07 MILANO 29
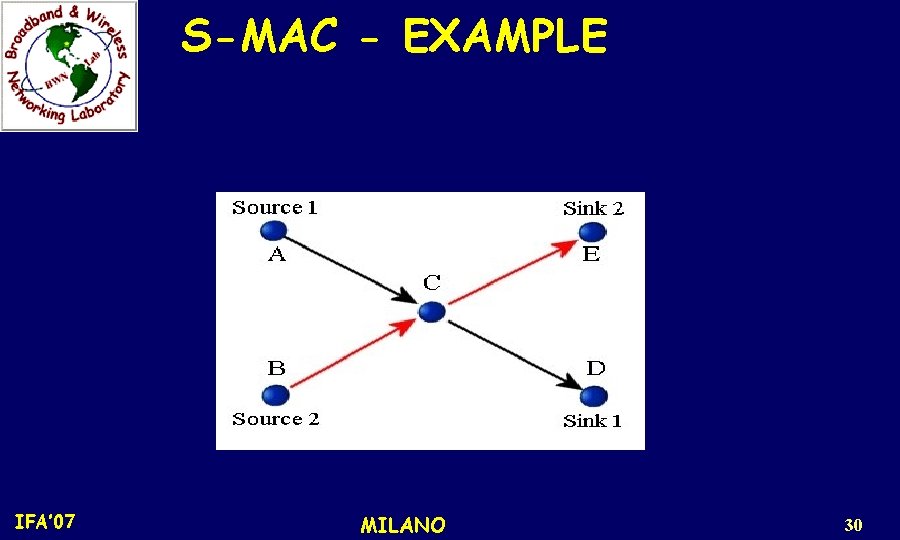
S-MAC - EXAMPLE IFA’ 07 MILANO 30
S-MAC - EXAMPLE n n n In each test, there are 10 messages generated on each source node. Each message has 10 fragments, and each fragment has 40 bytes (200 data packets to be passed from their sources to their sinks). The total energy consumption of each node is measured for sending this fixed amount of data. IFA’ 07 MILANO 31
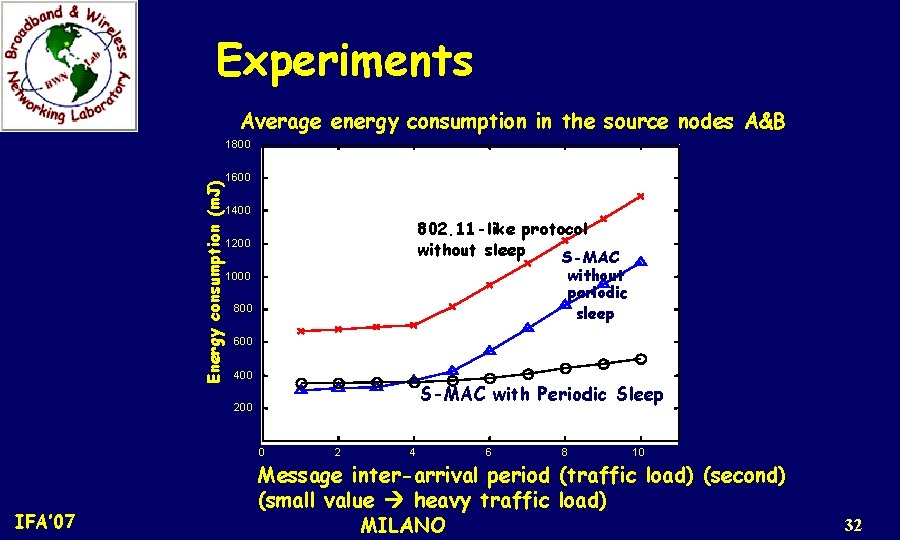
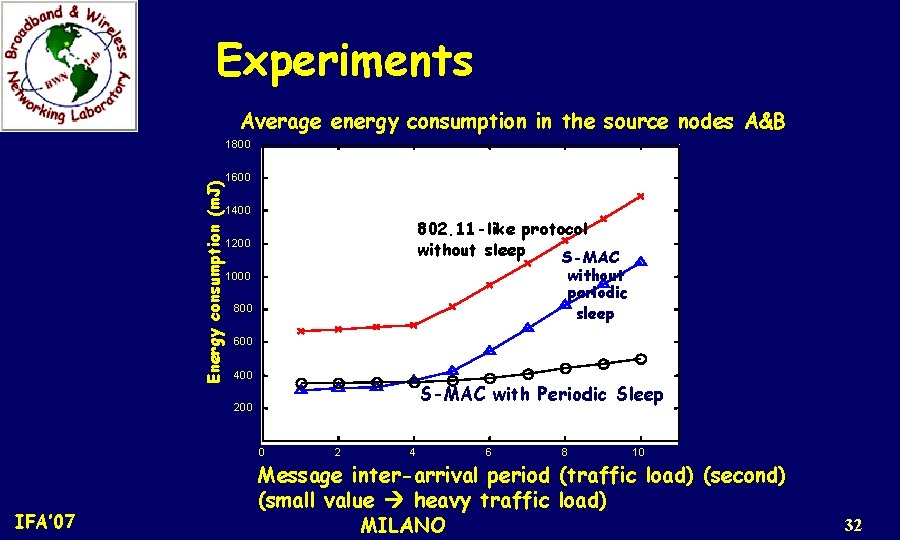
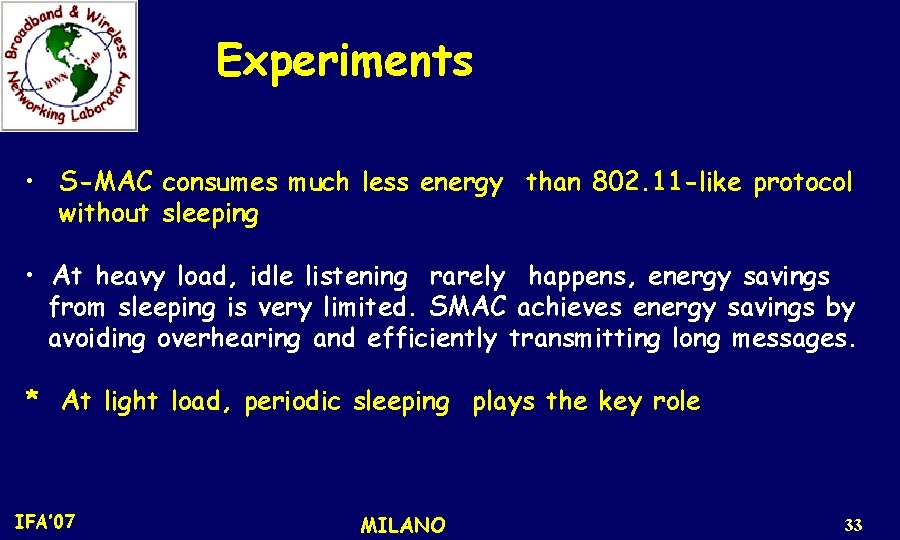
Experiments Average energy consumption in the source nodes A&B Energy consumption (m. J) 1800 1600 1400 802. 11 -like protocol without sleep S-MAC 1200 without periodic sleep 1000 800 600 400 S-MAC with Periodic Sleep 200 0 IFA’ 07 2 4 6 8 10 Message inter-arrival period (traffic load) (second) (small value heavy traffic load) MILANO 32
Experiments • S-MAC consumes much less energy than 802. 11 -like protocol without sleeping • At heavy load, idle listening rarely happens, energy savings from sleeping is very limited. SMAC achieves energy savings by avoiding overhearing and efficiently transmitting long messages. * At light load, periodic sleeping plays the key role IFA’ 07 MILANO 33
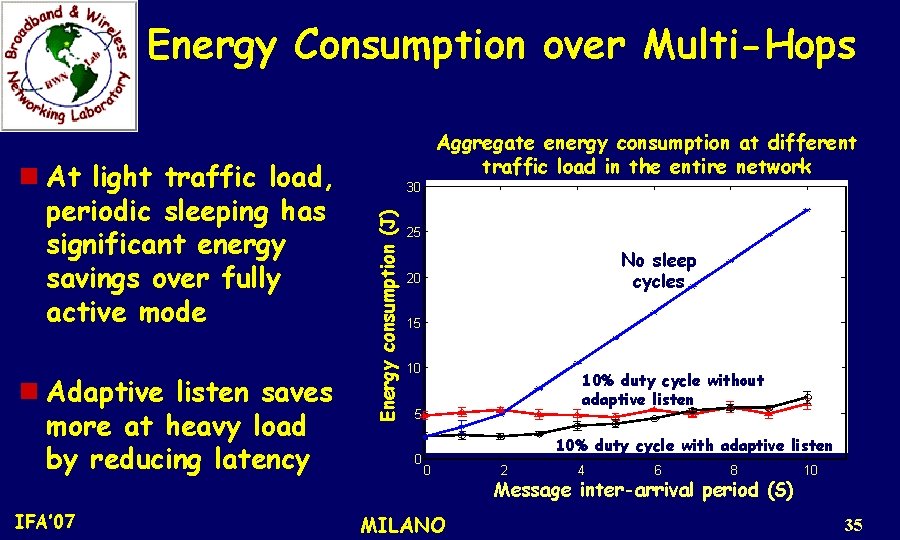
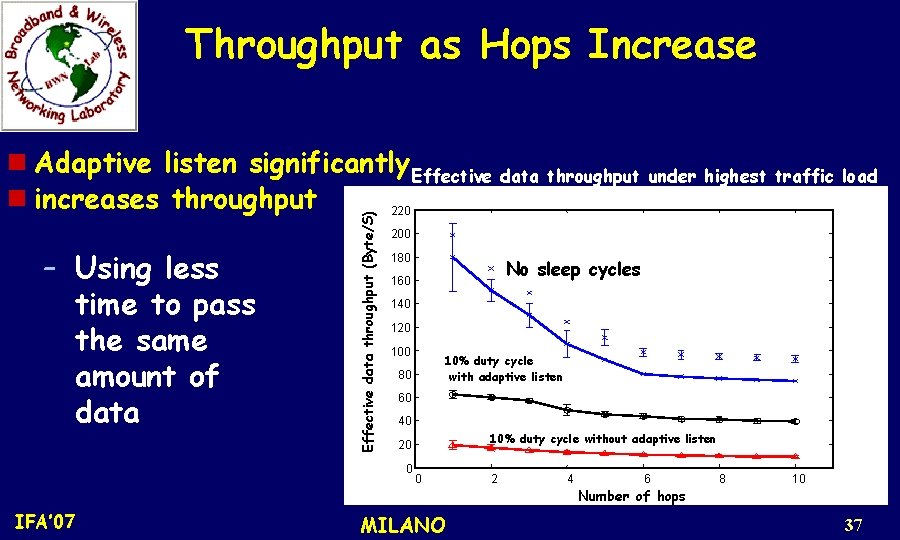
Energy Consumption over Multi-Hops Ten-hop (11 nodes; 1 m apart) linear (tandem) network at different traffic load; inter-arrival time 0 -10 s; source node sends 20 messages with each 100 bytes long. 3 configurations for S-MAC: No sleep cycles; 10% duty cycle without adaptive listening; 10% duty cycle with adaptive listening) (periodic listen interval: 115 ms; 10% duty cycle means a frame length for 1. 15 ssec). IFA’ 07 MILANO 34
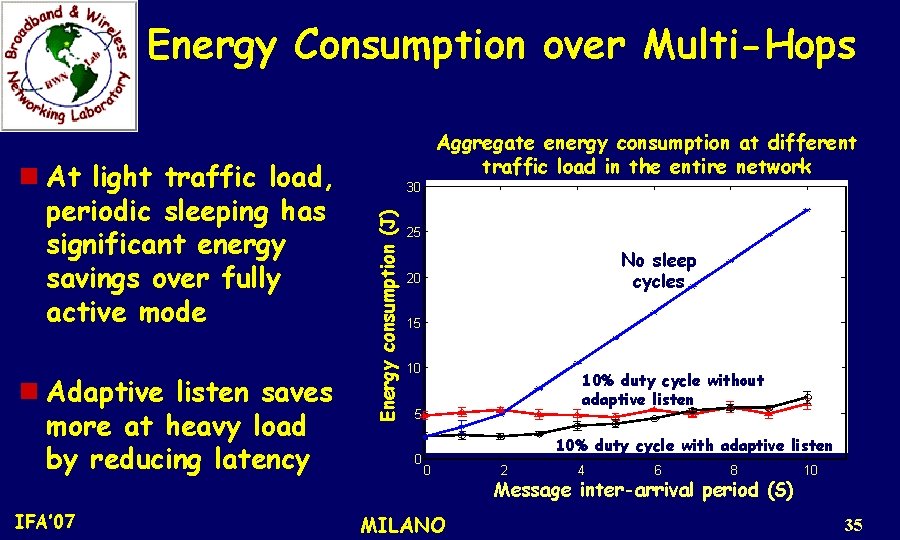
Energy Consumption over Multi-Hops n Adaptive listen saves more at heavy load by reducing latency IFA’ 07 30 Energy consumption (J) n At light traffic load, periodic sleeping has significant energy savings over fully active mode Aggregate energy consumption at different traffic load in the entire network 25 No sleep cycles 20 15 10 10% duty cycle without adaptive listen 5 0 10% duty cycle with adaptive listen 0 MILANO 2 4 6 8 Message inter-arrival period (S) 10 35
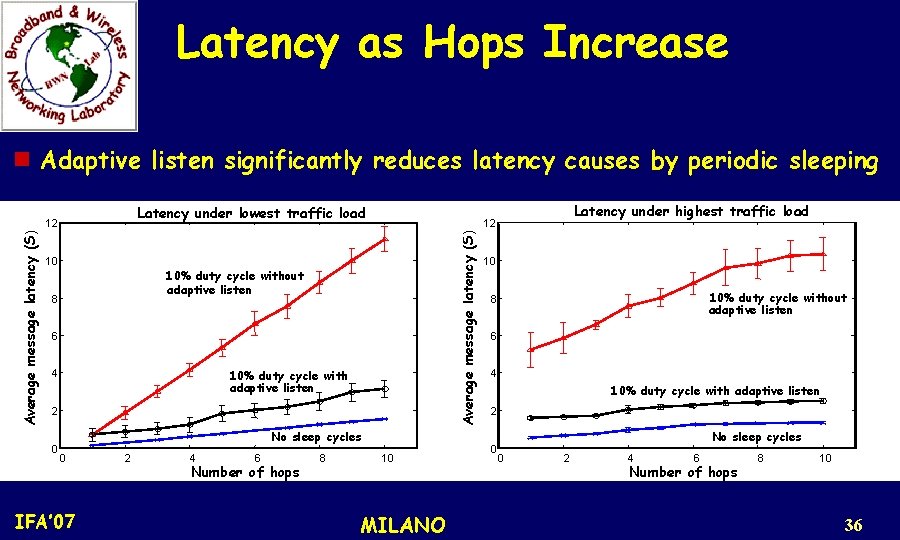
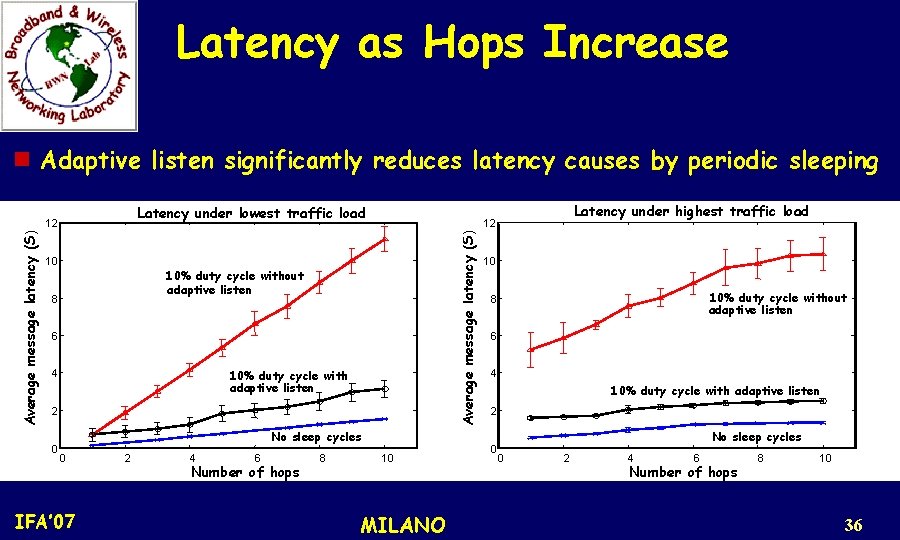
Latency as Hops Increase n Adaptive listen significantly reduces latency causes by periodic sleeping Latency under lowest traffic load 10 10% duty cycle without adaptive listen 8 6 10% duty cycle with adaptive listen 4 2 0 No sleep cycles 0 IFA’ 07 2 4 6 Number of hops 8 Latency under highest traffic load 12 Average message latency (S) 12 10 MILANO 10 10% duty cycle without adaptive listen 8 6 4 10% duty cycle with adaptive listen 2 0 No sleep cycles 0 2 4 6 Number of hops 8 10 36
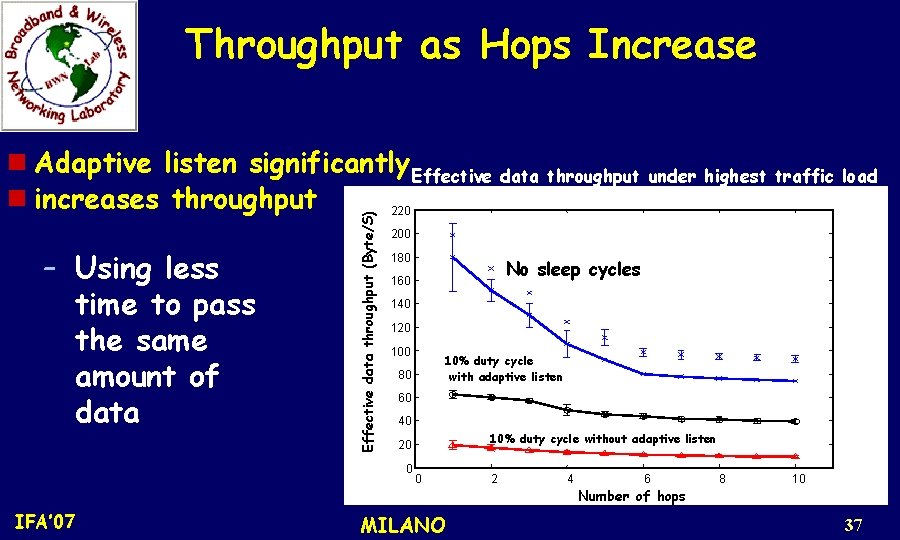
Throughput as Hops Increase – Using less time to pass the same amount of data Effective data throughput (Byte/S) n Adaptive listen significantly Effective data throughput under highest traffic load n increases throughput 220 200 180 140 120 10% duty cycle with adaptive listen 80 60 40 10% duty cycle without adaptive listen 20 0 IFA’ 07 No sleep cycles 160 0 MILANO 2 4 6 Number of hops 8 10 37

Our Vision M. C. Vuran, and I. F. Akyildiz, “Spatial Correlation-based Collaborative Medium Access Control in Wireless Sensor Networks, ” IEEE/ACM Trans. on Networking, vol. 14, pp. 316 -329, April 2006. WSNs are characterized by dense deployment of sensor nodes Exploit spatial correlation to reduce transmissions in MAC layer ! IFA’ 07 MILANO 38
Collaborative MAC (CC-MAC) Protocol Main Components – Iterative Node Selection (INS) Algorithm (@Sink) l Determines protocol parameters (required distance (rcorr) for correlation neighbors) – Event MAC (@Sensors) l Filters out correlated data – Network MAC (@Sensors) l Provides prioritization for route-thru packets IFA’ 07 MILANO 39
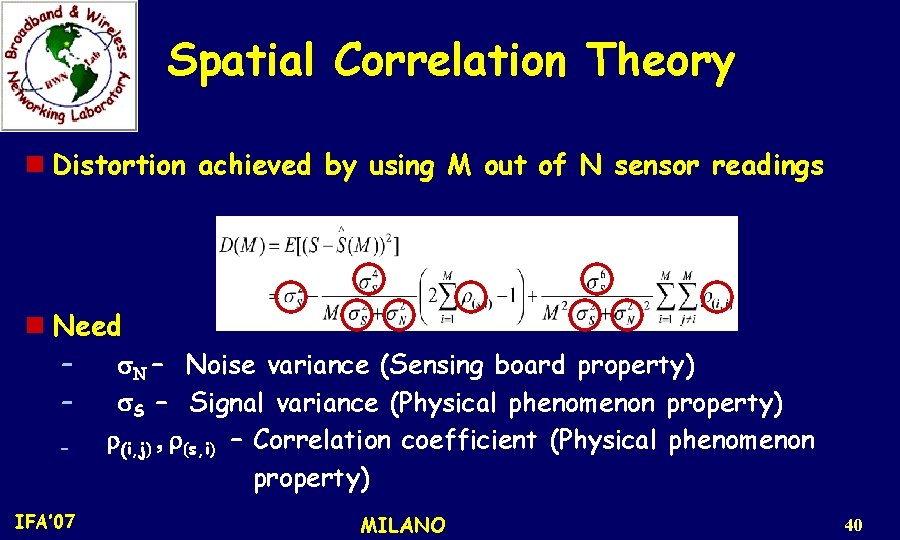
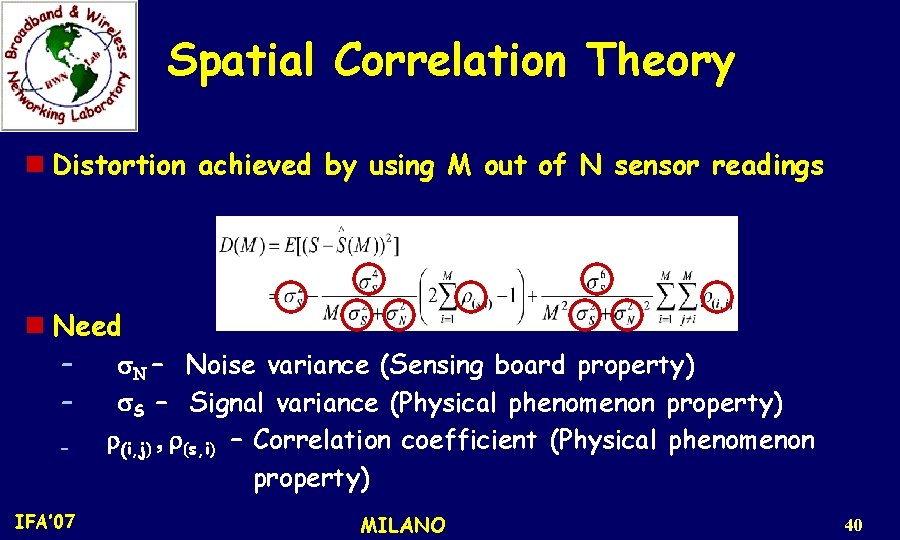
Spatial Correlation Theory n Distortion achieved by using M out of N sensor readings n Need – – – IFA’ 07 s. N – Noise variance (Sensing board property) s. S – Signal variance (Physical phenomenon property) r(i, j) , r(s, i) – Correlation coefficient (Physical phenomenon property) MILANO 40
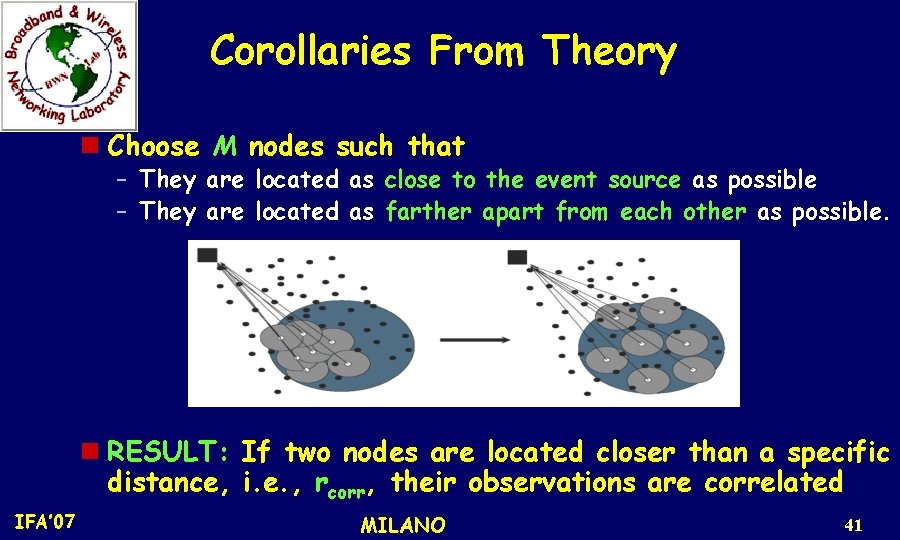
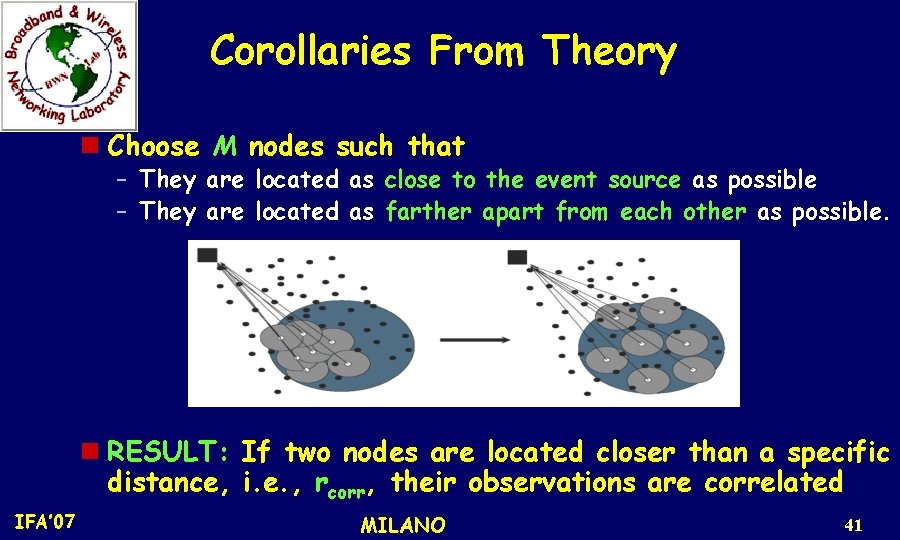
Corollaries From Theory n Choose M nodes such that – – They are located as as close to the event source as possible farther apart from each other as possible n RESULT: If two nodes are located closer than a specific distance, i. e. , rcorr, their observations are correlated IFA’ 07 MILANO 41
Corollaries From Theory Representative nodes are not located close to each other, the probability of collision decreases RESULT: Exploiting spatial correlation not only improves the distortion but also utilizes the wireless channel by avoiding collisions IFA’ 07 MILANO 42
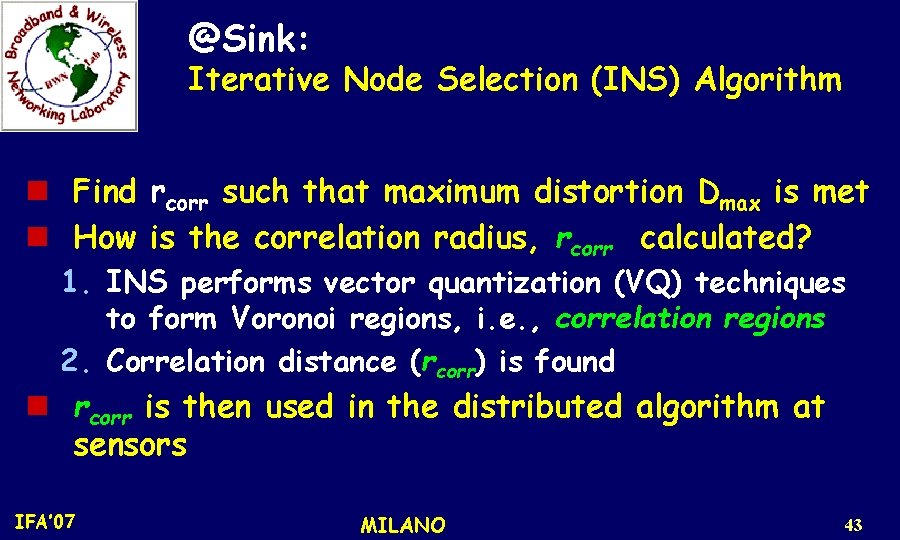
@Sink: Iterative Node Selection (INS) Algorithm n Find rcorr such that maximum distortion Dmax is met n How is the correlation radius, rcorr calculated? 1. INS performs vector quantization (VQ) techniques to form Voronoi regions, i. e. , correlation regions 2. Correlation distance (rcorr) is found n rcorr is then used in the distributed algorithm at sensors IFA’ 07 MILANO 43
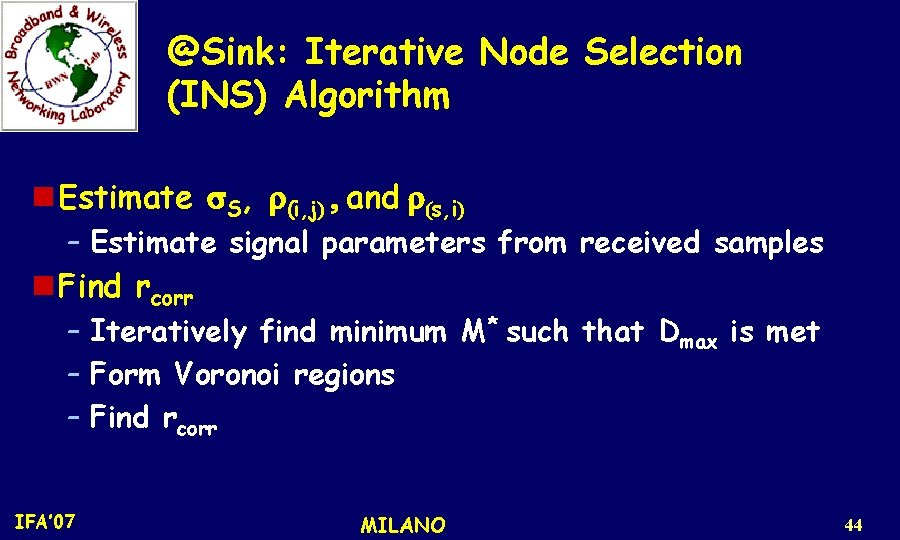
@Sink: Iterative Node Selection (INS) Algorithm n Estimate s. S, r(i, j) , and r(s, i) – Estimate signal parameters from received samples n Find rcorr – Iteratively find minimum M* such that Dmax is met – Form Voronoi regions – Find rcorr IFA’ 07 MILANO 44
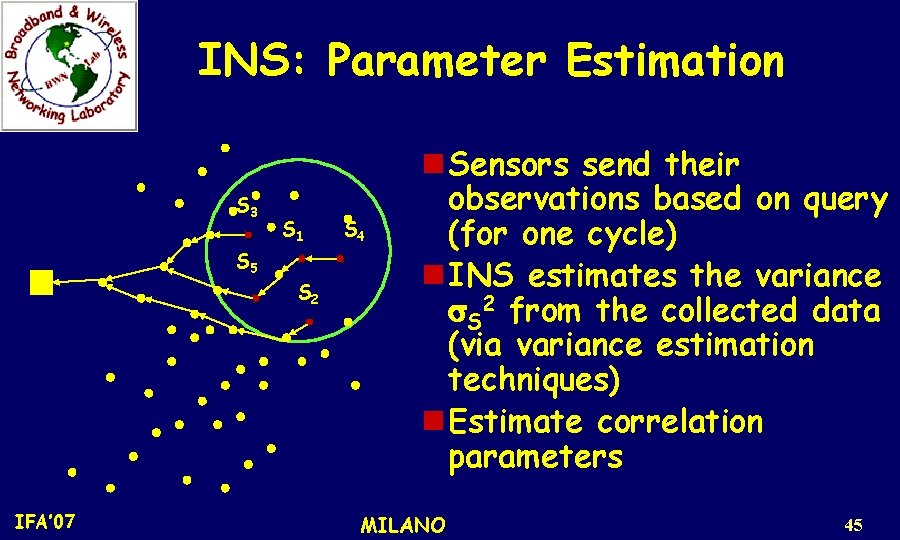
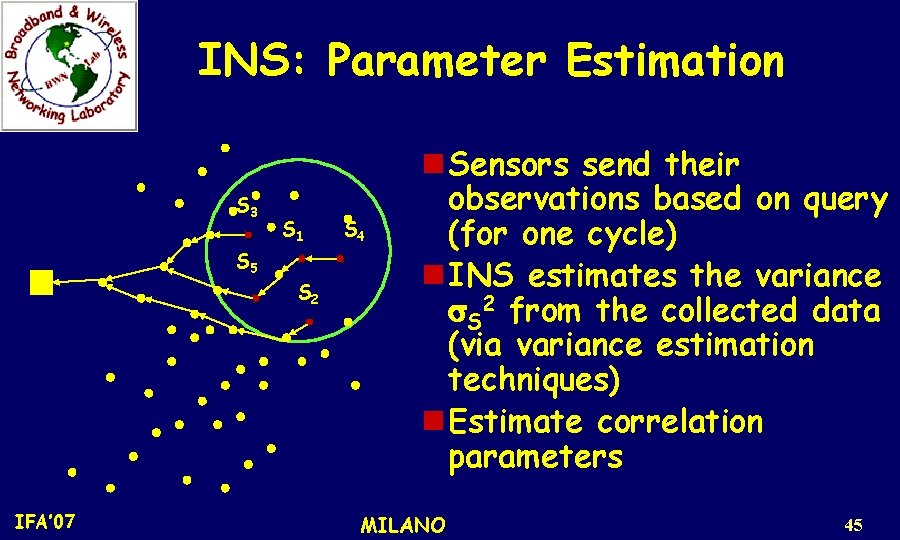
INS: Parameter Estimation S 3 S 1 S 5 S 2 IFA’ 07 S 4 n Sensors send their observations based on query (for one cycle) n INS estimates the variance s. S 2 from the collected data (via variance estimation techniques) n Estimate correlation parameters MILANO 45
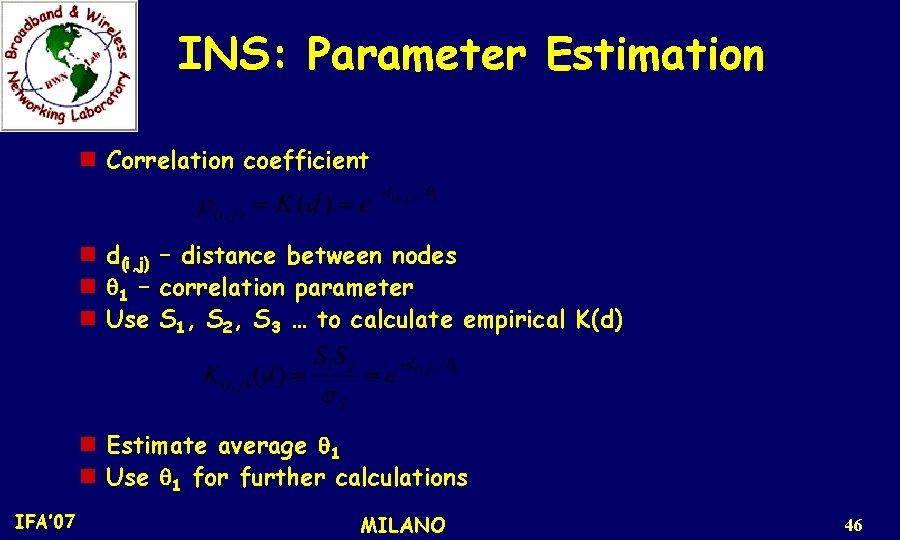
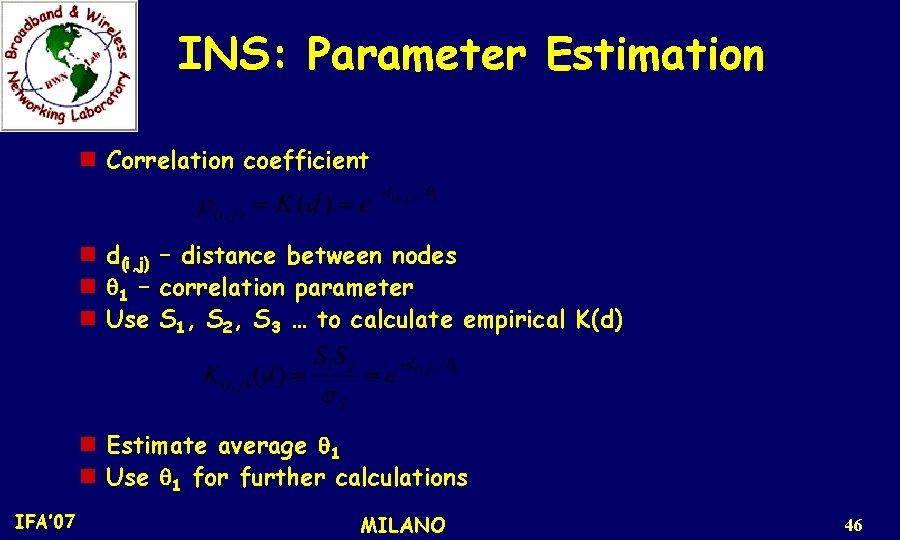
INS: Parameter Estimation n Correlation coefficient n n n d(i, j) q 1 – Use – distance between nodes correlation parameter S 1, S 2, S 3 … to calculate empirical K(d) n Estimate average q 1 n Use q 1 for further calculations IFA’ 07 MILANO 46
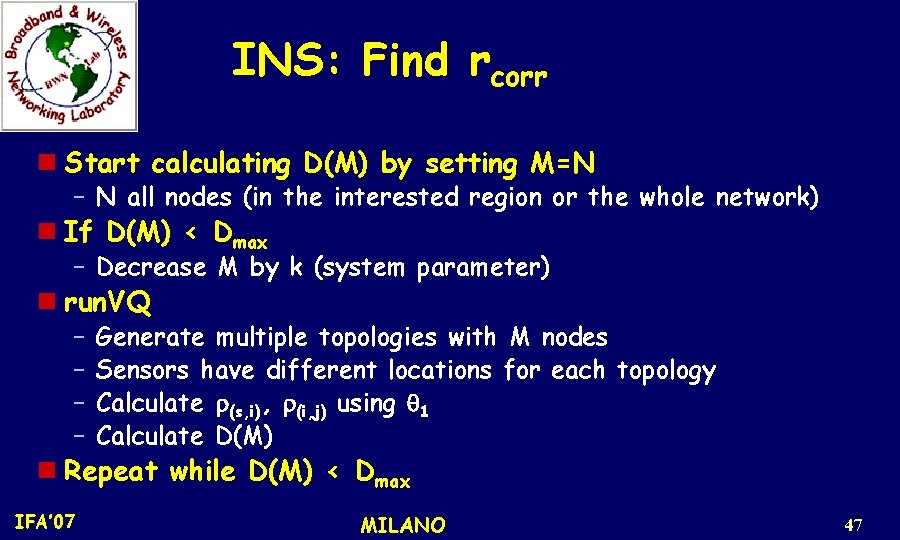
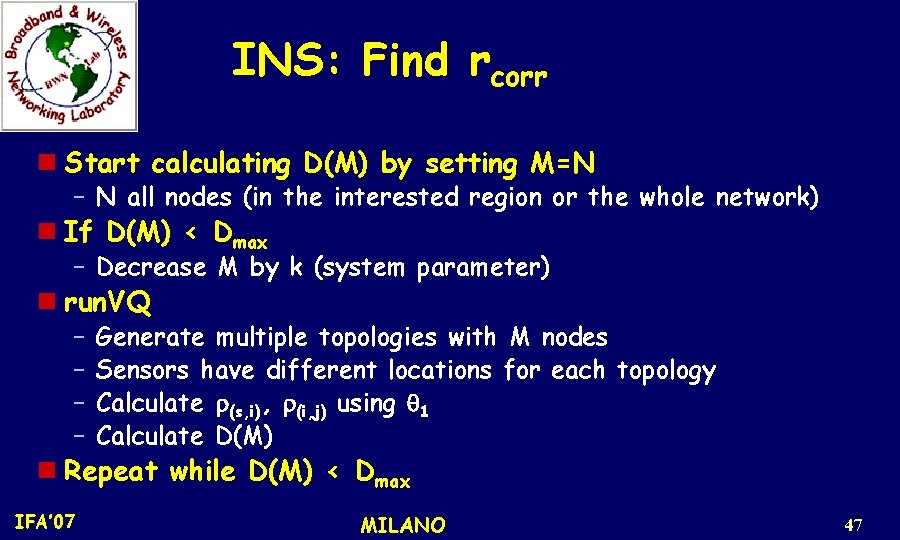
INS: Find rcorr n Start calculating D(M) by setting M=N – N all nodes (in the interested region or the whole network) n If D(M) < Dmax – Decrease M by k (system parameter) n run. VQ – – Generate multiple topologies with M nodes Sensors have different locations for each topology Calculate r(s, i), r(i, j) using q 1 Calculate D(M) n Repeat while D(M) < Dmax IFA’ 07 MILANO 47
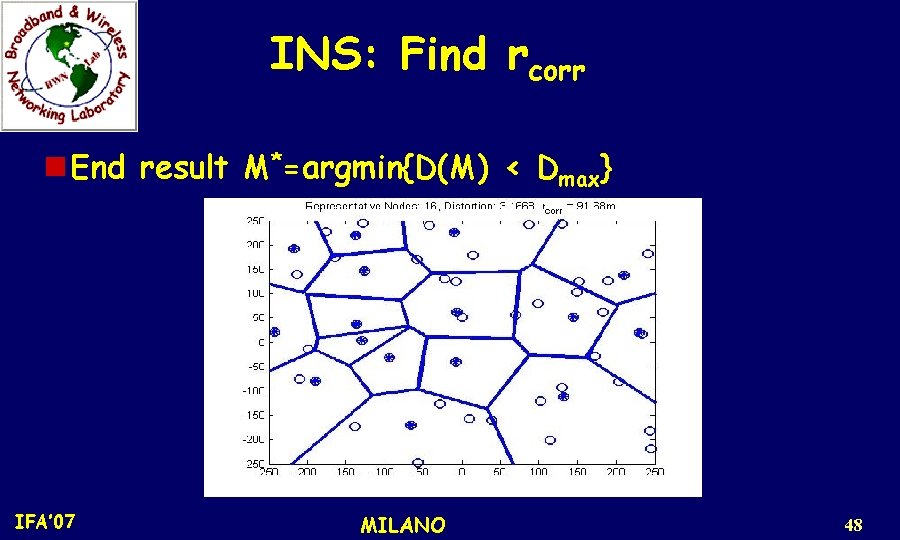
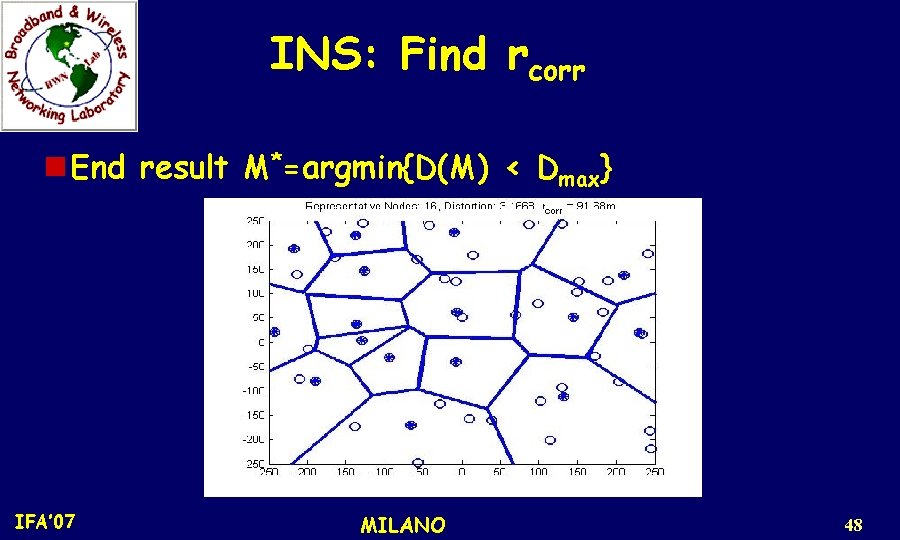
INS: Find rcorr n End result M*=argmin{D(M) < Dmax} IFA’ 07 MILANO 48
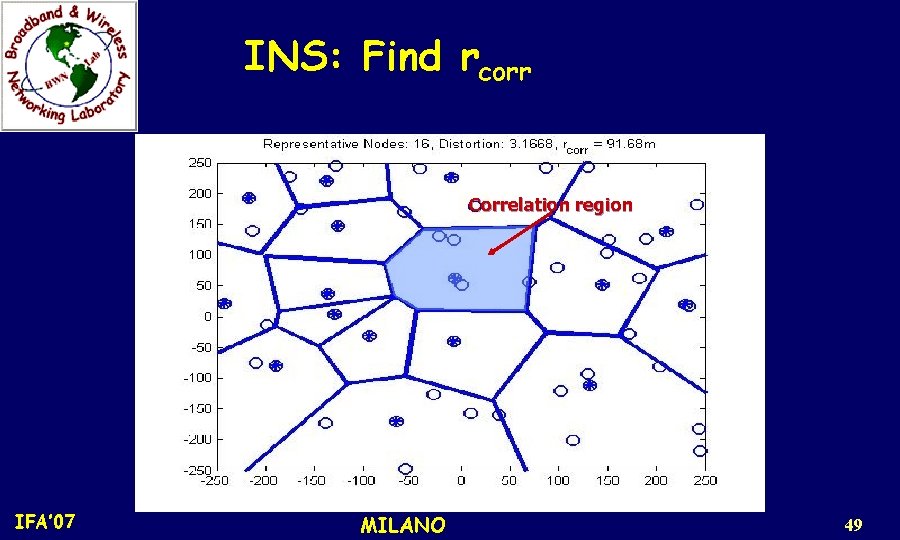
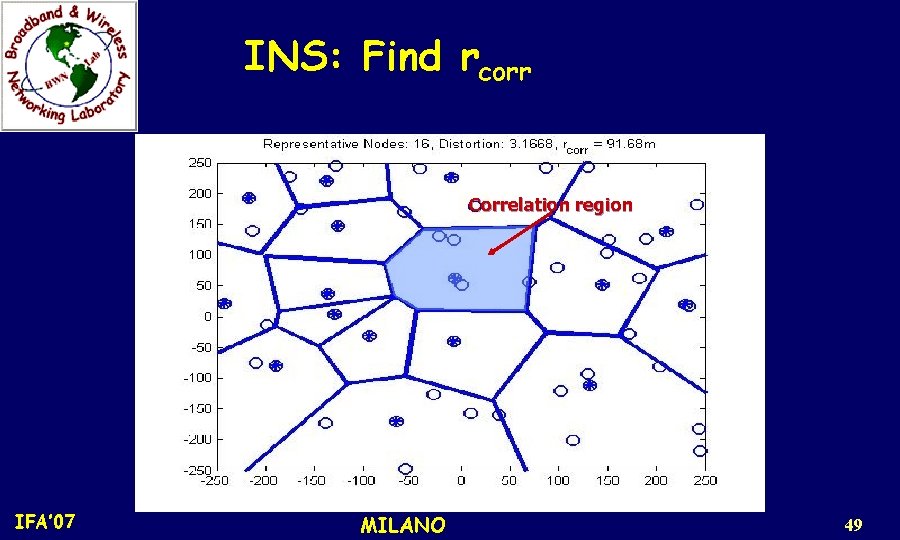
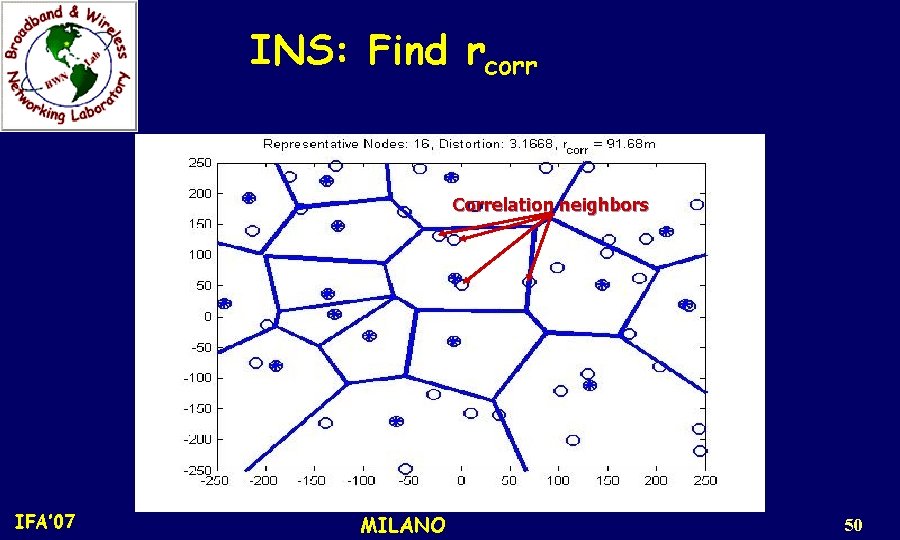
INS: Find rcorr Correlation region IFA’ 07 MILANO 49
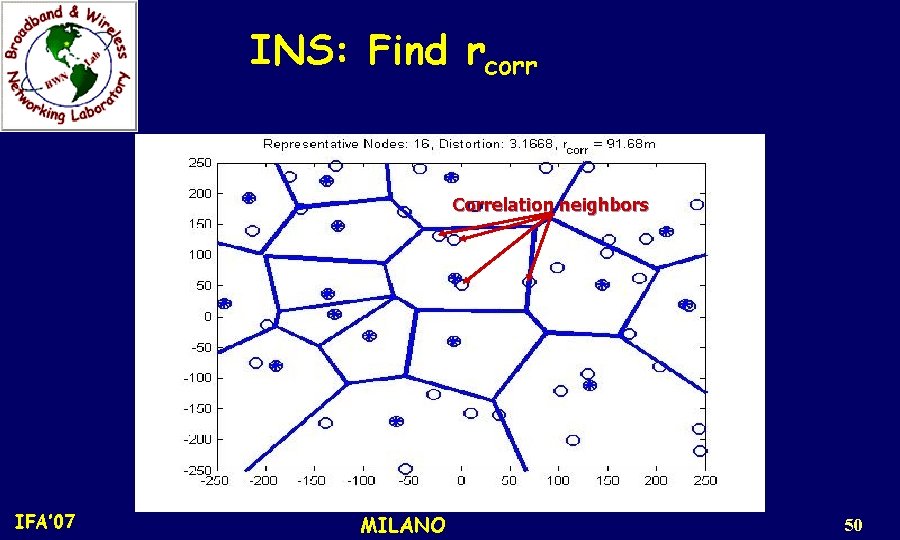
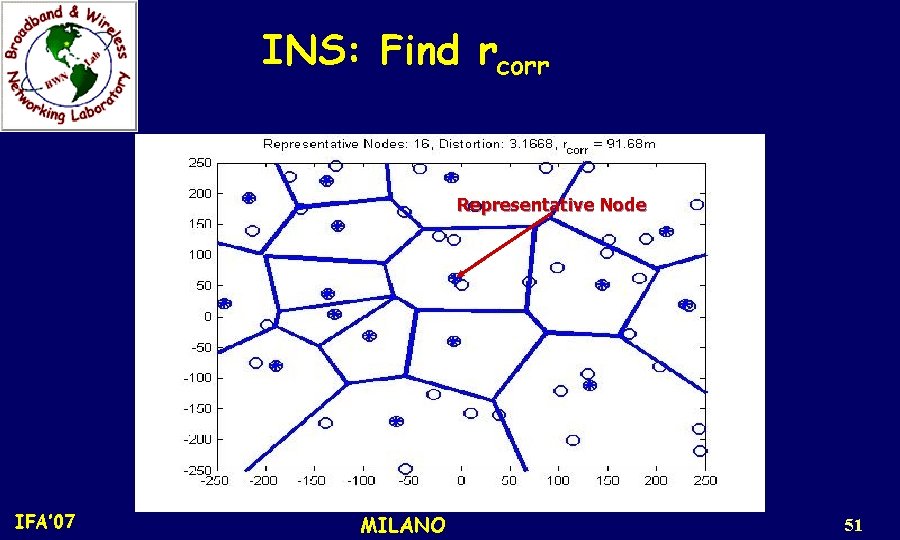
INS: Find rcorr Correlation neighbors IFA’ 07 MILANO 50
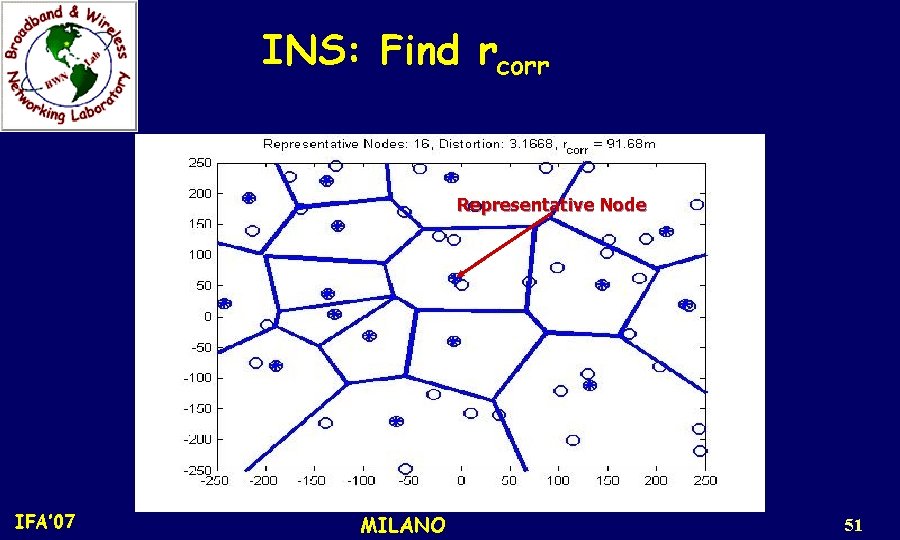
INS: Find rcorr Representative Node IFA’ 07 MILANO 51
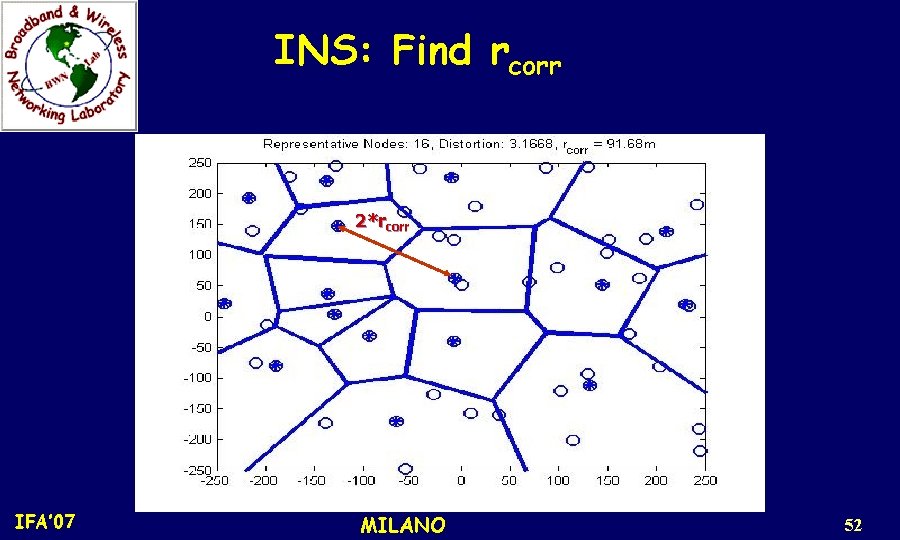
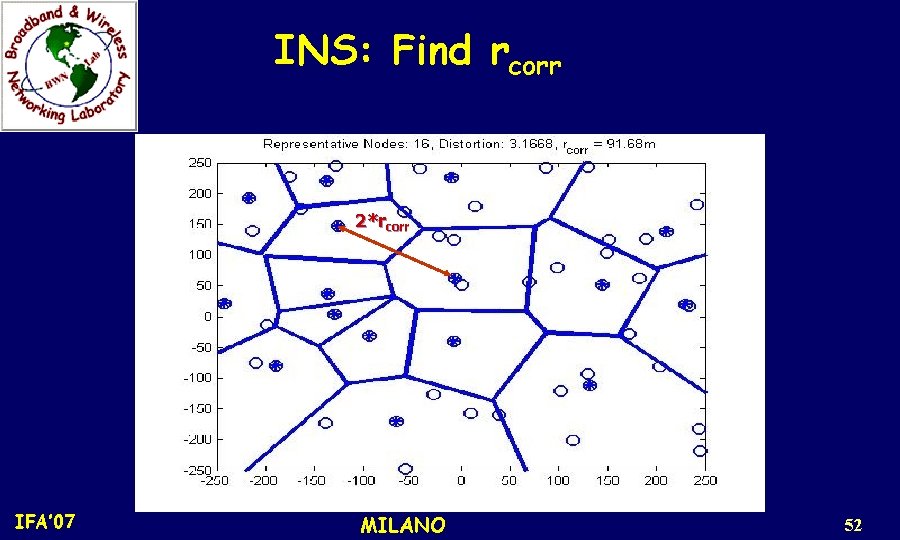
INS: Find rcorr 2*rcorr IFA’ 07 MILANO 52
INS: Find rcorr n Find avg. distance between selected M* nodes = 2 rcorr n Sink sends rcorr to each node in the network n CC-MAC distributed operation is based only on rcorr IFA’ 07 MILANO 53
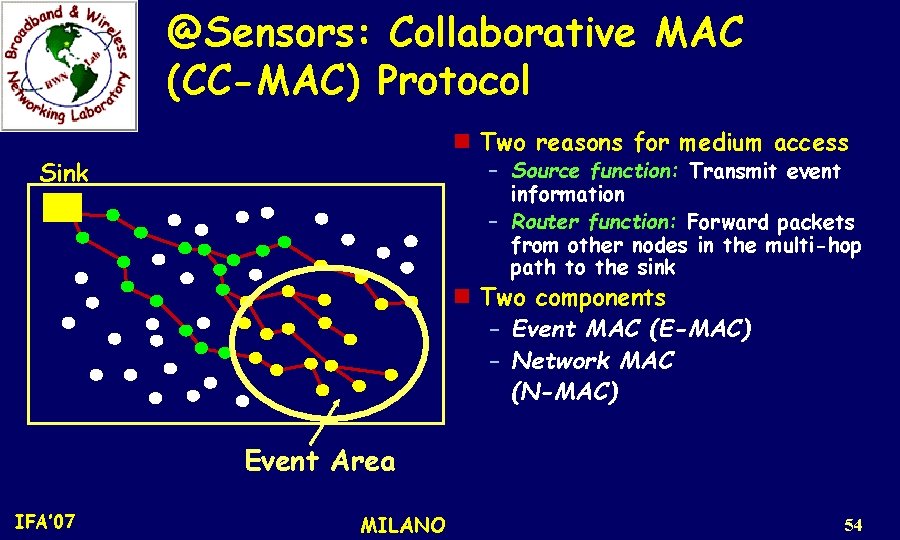
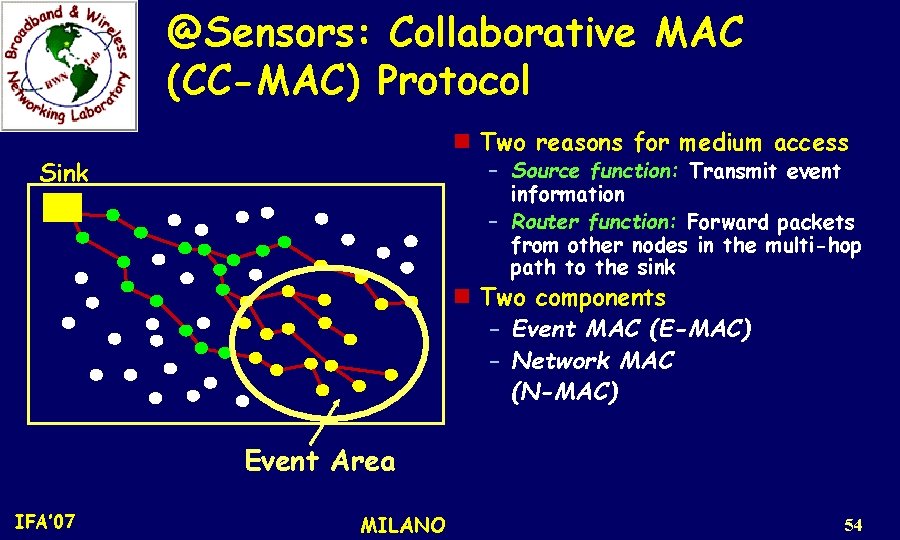
@Sensors: Collaborative MAC (CC-MAC) Protocol n Two reasons for medium access Sink – Source function: Transmit event information – Router function: Forward packets from other nodes in the multi-hop path to the sink n Two components – Event MAC (E-MAC) – Network MAC (N-MAC) Event Area IFA’ 07 MILANO 54
Event MAC (E-MAC) n Aims to filter out correlated sensor records – Choose representative nodes distributively – Form correlation-based clusters n How will a node know it should perform E-MAC? IFA’ 07 MILANO 55
Network MAC (N-MAC) n. N-MAC prioritizes route-thru packets during medium access using – Smaller backoff window size – Smaller inter-frame spacing during contention n. Router nodes have higher prioritization over representative nodes IFA’ 07 MILANO 56
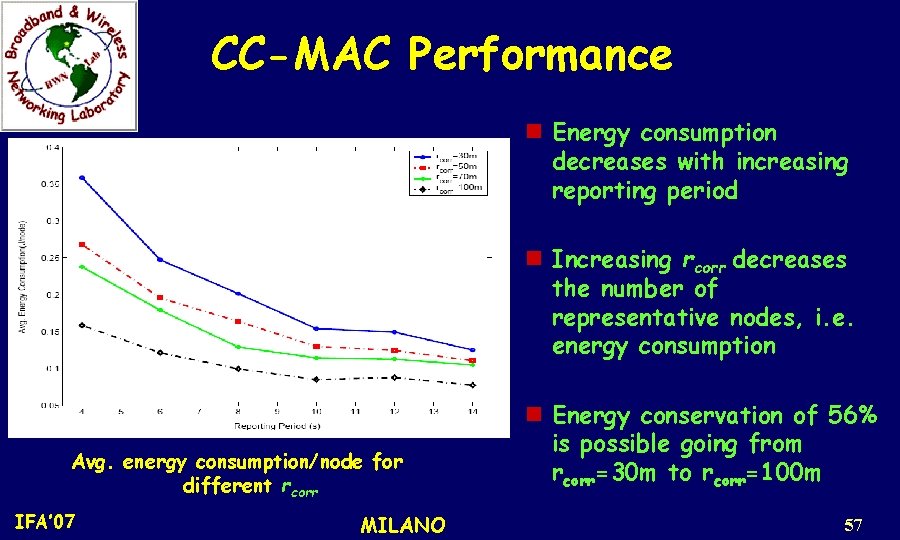
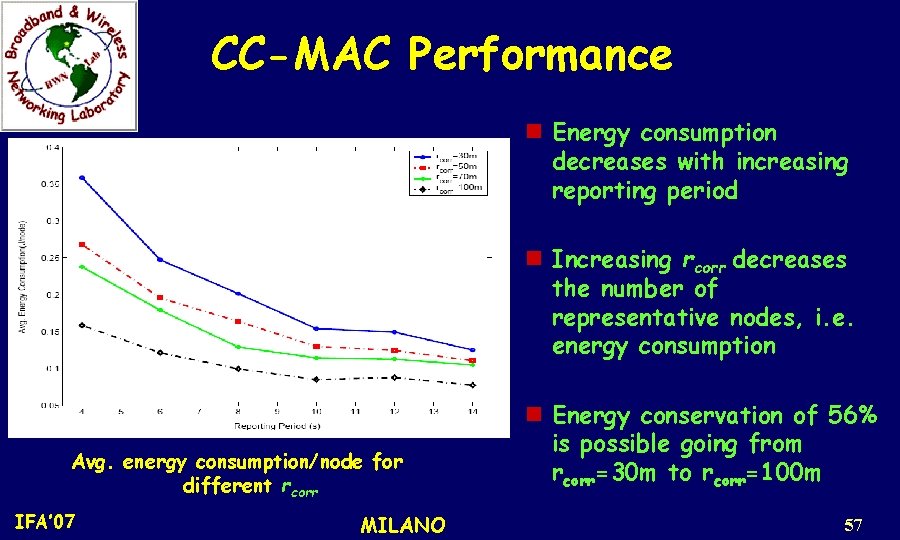
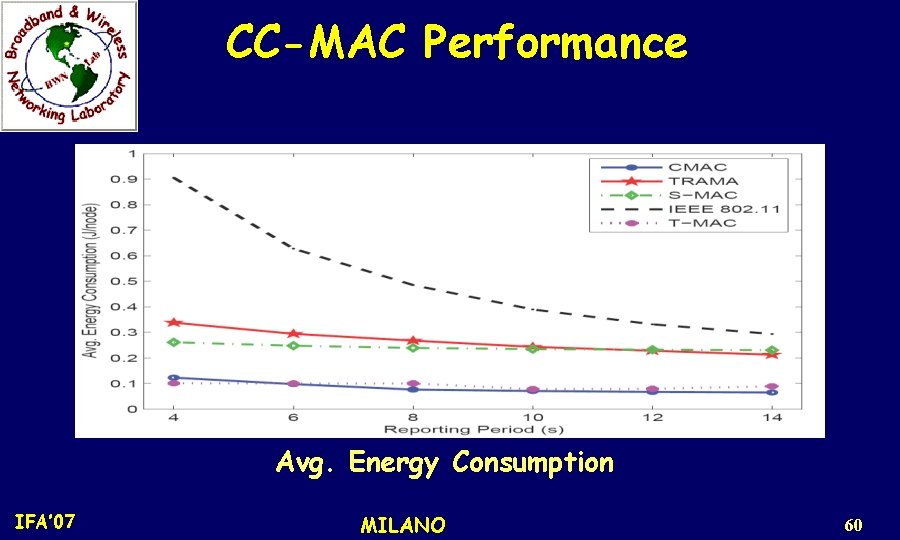
CC-MAC Performance n Energy consumption decreases with increasing reporting period n Increasing rcorr decreases the number of representative nodes, i. e. energy consumption Avg. energy consumption/node for different rcorr IFA’ 07 MILANO n Energy conservation of 56% is possible going from rcorr=30 m to rcorr=100 m 57
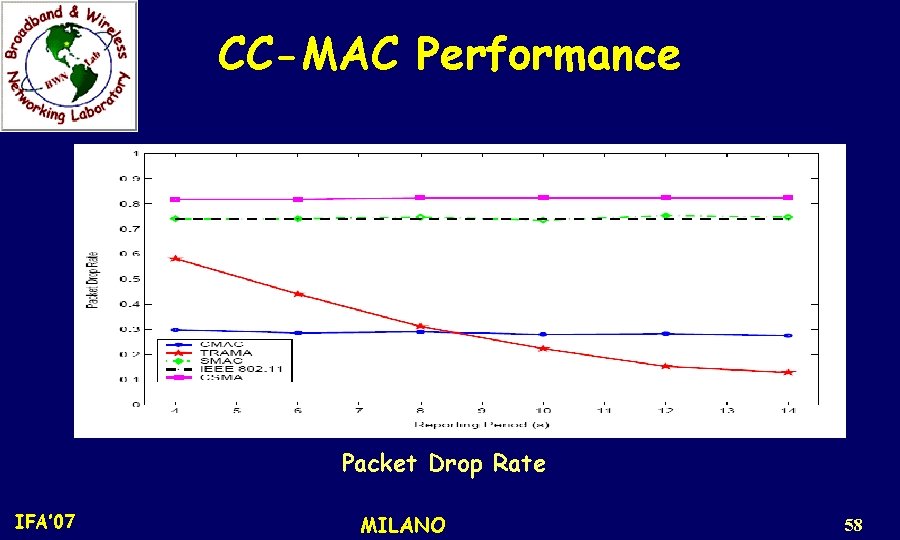
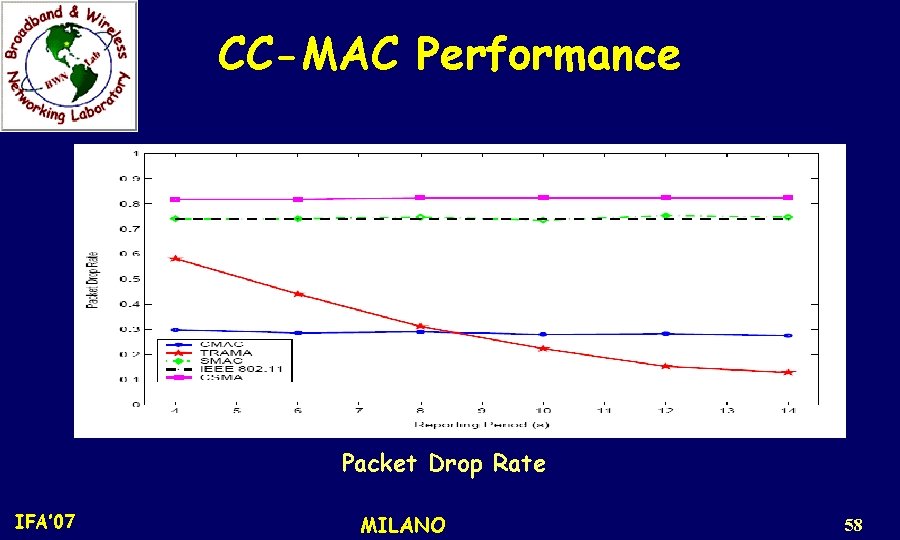
CC-MAC Performance Packet Drop Rate IFA’ 07 MILANO 58
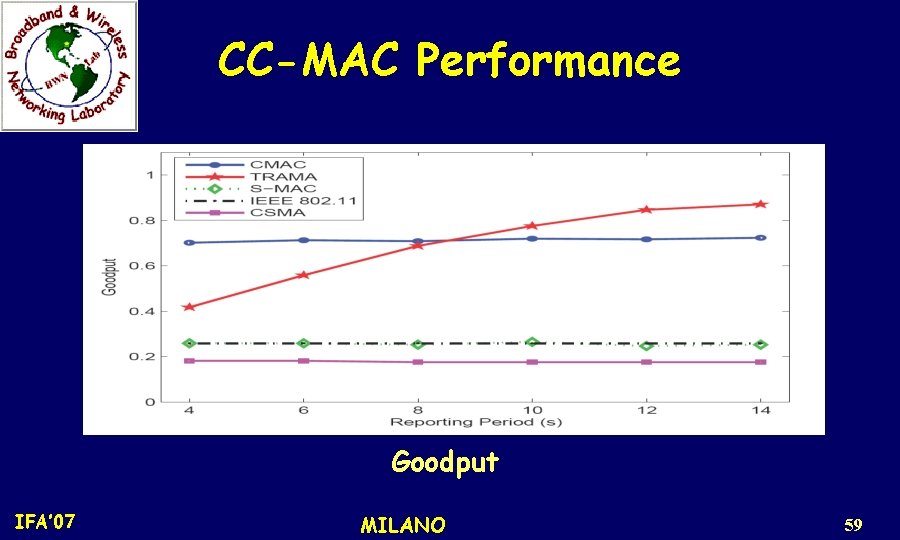
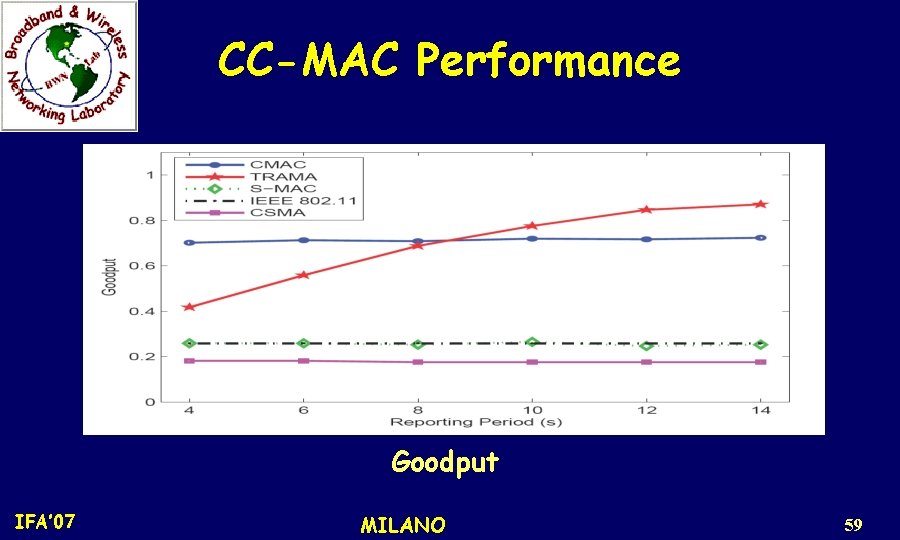
CC-MAC Performance Goodput IFA’ 07 MILANO 59
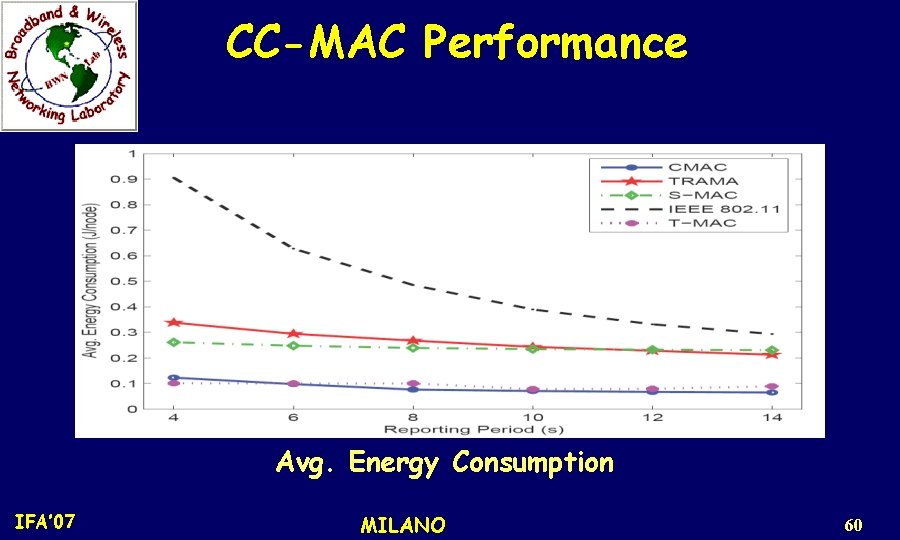
CC-MAC Performance Avg. Energy Consumption IFA’ 07 MILANO 60
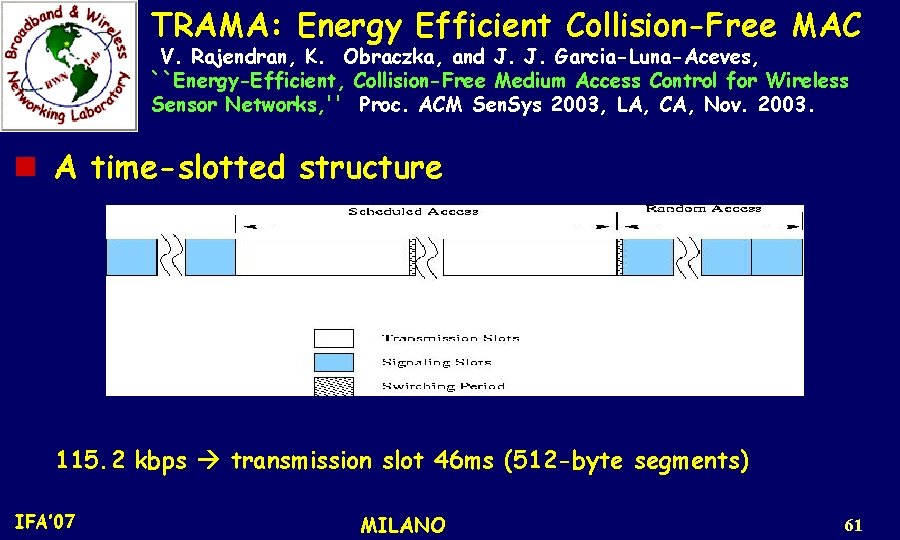
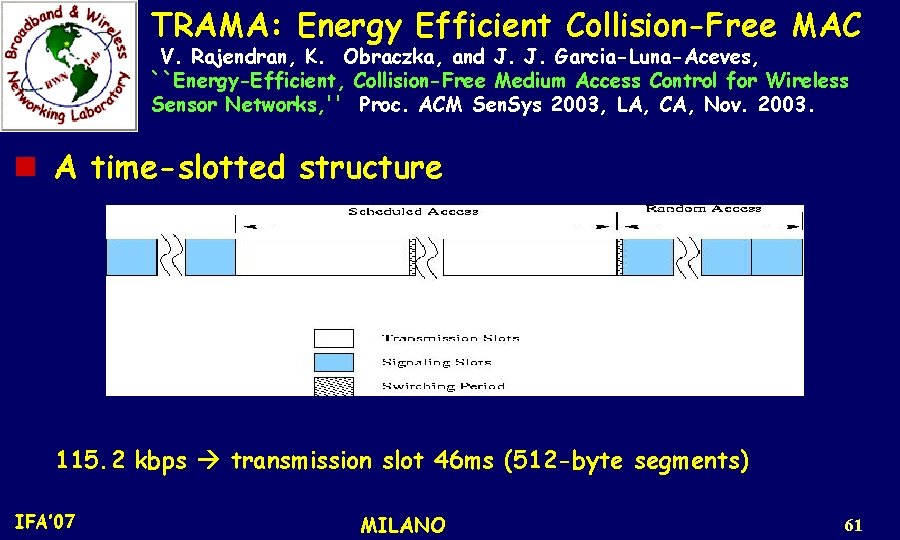
TRAMA: Energy Efficient Collision-Free MAC V. Rajendran, K. Obraczka, and J. J. Garcia-Luna-Aceves, ``Energy-Efficient, Collision-Free Medium Access Control for Wireless Sensor Networks, '' Proc. ACM Sen. Sys 2003, LA, CA, Nov. 2003. n A time-slotted structure 115. 2 kbps transmission slot 46 ms (512 -byte segments) IFA’ 07 MILANO 61
TRAMA Time divided into PERIODS: n Random Access Period – Used for signaling: synchronization and updating two-hop neighbor information. Collision!! n Scheduled Access Period: – Used for contention free data exchange between nodes. – Supports unicast, multicast and broadcast communication. IFA’ 07 MILANO 62
TRAMA SIGNALING SLOTS: are used by the so-called NEIGHBOR PROTOCOL (NP) to propagate one-hop neighbor information among neighboring nodes during the random access period. By this way, a consistent two-hop technology information across all nodes is obtained. IFA’ 07 MILANO 63
TRAMA TRANSMISSION SLOTS: i) For collision free data exchange ii) For schedule propagation Nodes use SEP (Schedule Exchange Protocol) to exchange traffic based information or schedules with neighbors. IFA’ 07 MILANO 64
TRAMA Components n Neighbor Protocol (NP). – Gather 2 -hop neighborhood information. n Schedule Exchange Protocol (SEP). – Gather 1 -hop traffic information for SCHEDULING. n Adaptive Election Algorithm (AEA). – Select transmitters, receivers for current time slot leave other nodes in liberty to switch to low power mode using the NP and SEP results. IFA’ 07 MILANO 65
TRAMA Limitations n Complex election algorithm and data structure. n Overhead due to explicit schedule propagation. n Higher queueing delay. IFA’ 07 MILANO 66
Comparison: TRAMA vs. S-MAC – Energy savings in TRAMA depend on the workload situation – Energy savings in S-MAC depend on duty cycle – TRAMA (as typical for a TDMA scheme) has higher delay but higher maximum throughput than contention -based S-MAC n TRAMA disadvantage: substantial memory/CPU requirements for schedule computation IFA’ 07 MILANO 67
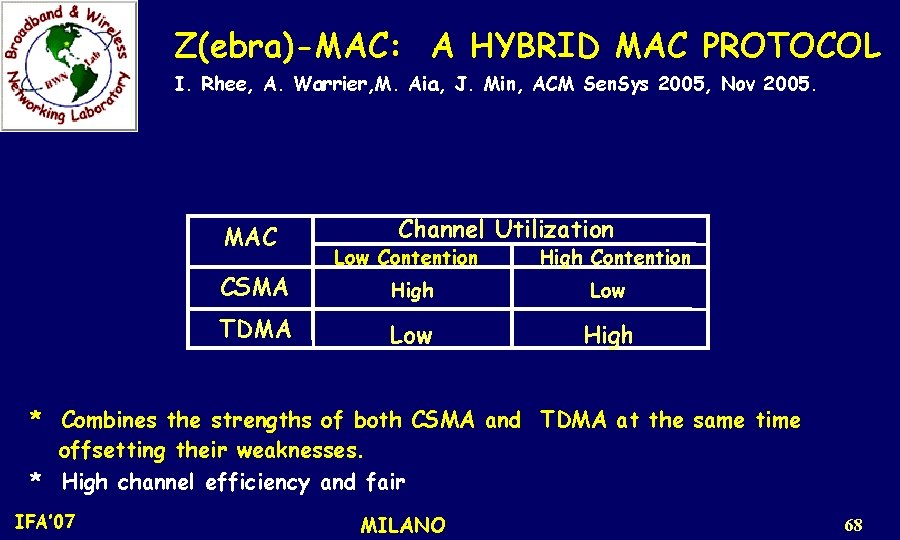
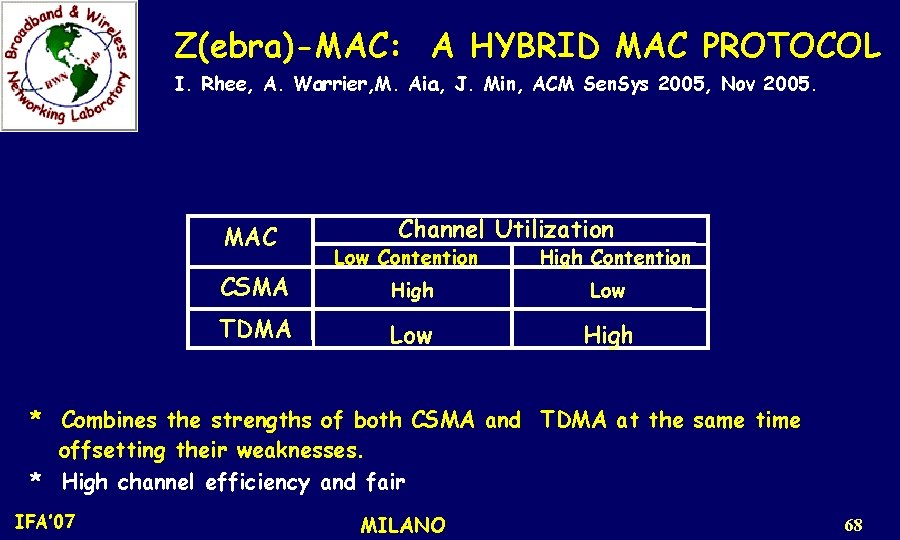
Z(ebra)-MAC: A HYBRID MAC PROTOCOL I. Rhee, A. Warrier, M. Aia, J. Min, ACM Sen. Sys 2005, Nov 2005. MAC CSMA TDMA Channel Utilization Low Contention High Low High * Combines the strengths of both CSMA and TDMA at the same time offsetting their weaknesses. * High channel efficiency and fair IFA’ 07 MILANO 68
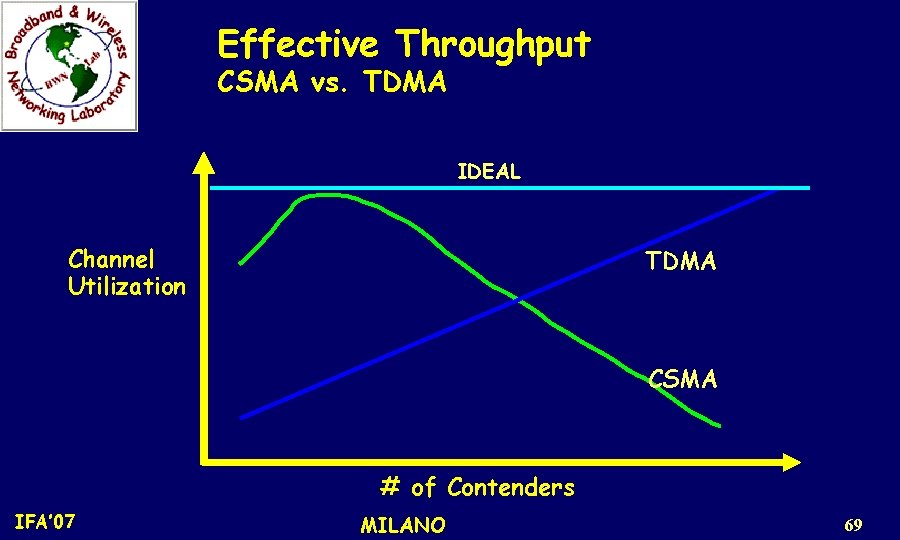
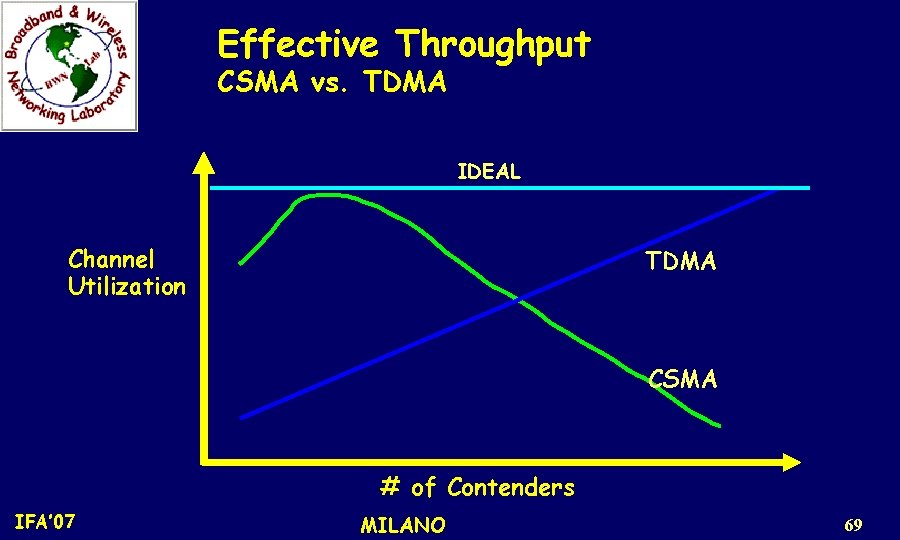
Effective Throughput CSMA vs. TDMA IDEAL Channel Utilization TDMA CSMA # of Contenders IFA’ 07 MILANO 69
Z-MAC • Uses the TDMA schedule created by DRAND as a 'hint' to schedule transmissions. • The owner of a time-slot always has priority over the nonowners while accessing the medium. • Unlike TDMA, non-owners can 'steal' the time-slot when the owners do not have data to send. IFA’ 07 MILANO 70
Z-MAC • This enables Z-MAC to switch between CSMA and TDMA depending on the level of contention. • Hence, under low contention, Z-MAC acts like CSMA (i. e. high channel utilization and low latency), while under high contention, Z-MAC acts like TDMA (i. e. high channel utilization, fairness and low contention overhead). IFA’ 07 MILANO 71
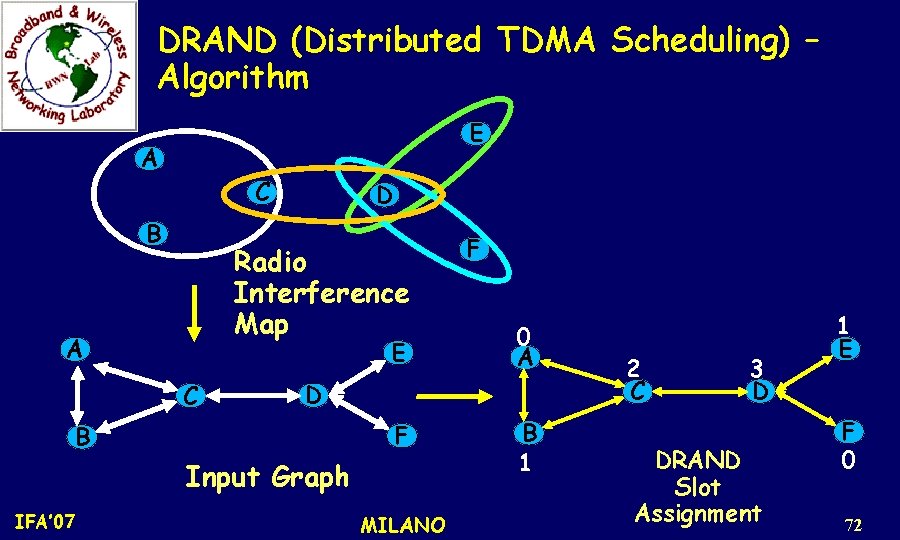
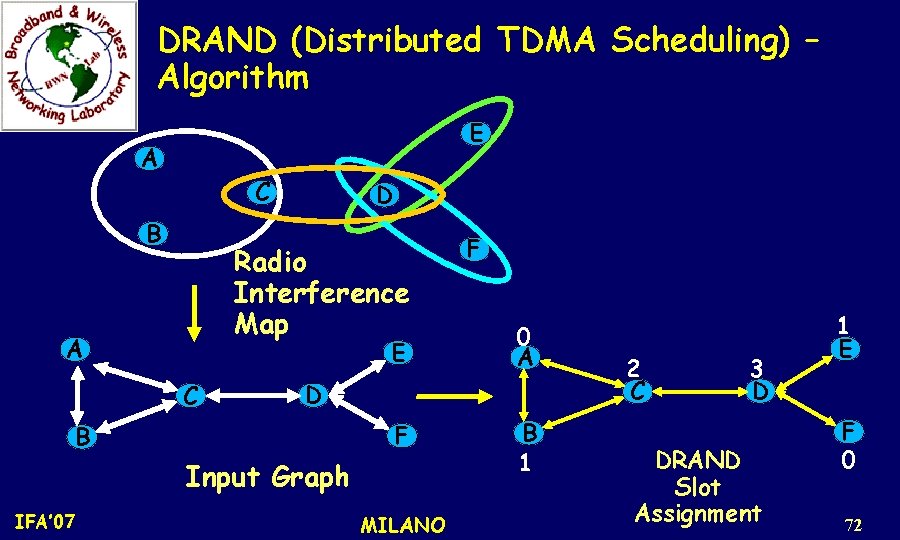
DRAND (Distributed TDMA Scheduling) – Algorithm E A C B D Radio Interference Map A E C 0 A D F B Input Graph IFA’ 07 F MILANO B 1 2 C 3 D DRAND Slot Assignment 1 E F 0 72
Transmission Control Slot Ownership - If current timeslot is the node's assigned time-slot, then it is the Owner, and all other neighboring nodes are Non-Owners. IFA’ 07 MILANO 73
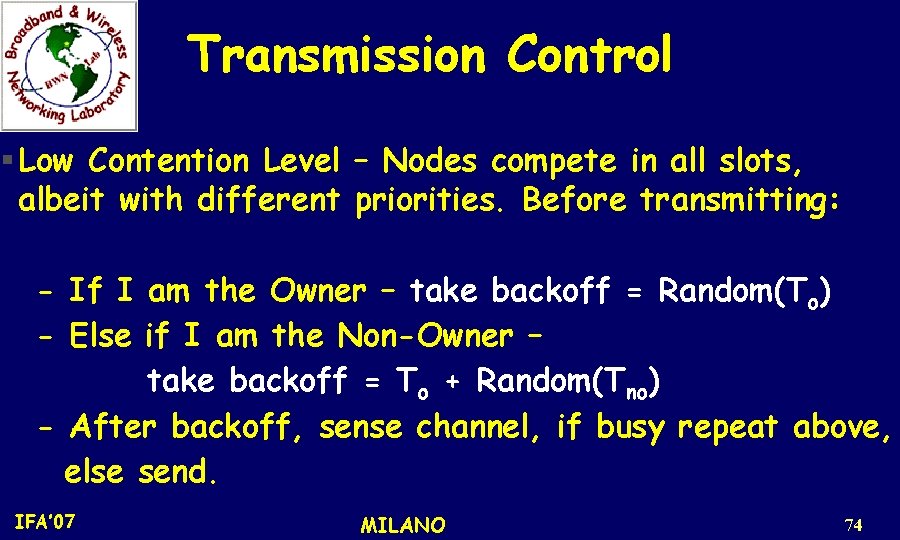
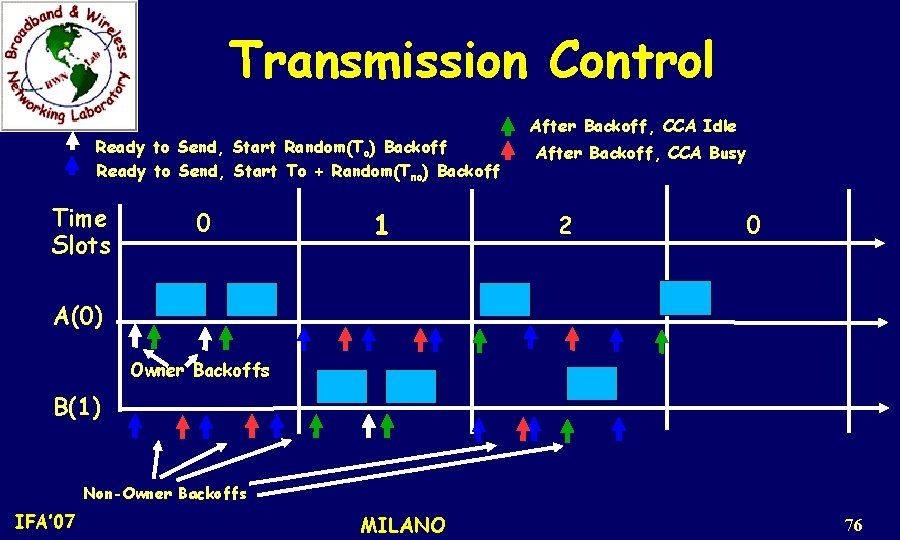
Transmission Control Low Contention Level – Nodes compete in all slots, albeit with different priorities. Before transmitting: - If I am the Owner – take backoff = Random(To) - Else if I am the Non-Owner – take backoff = To + Random(Tno) - After backoff, sense channel, if busy repeat above, else send. IFA’ 07 MILANO 74
Transmission Control * Switches between CSMA and TDMA automatically depending on contention level * Performance depends on specific values of To and Tno * From analysis, To = 8 and Tno = 32 are used for best performance IFA’ 07 MILANO 75
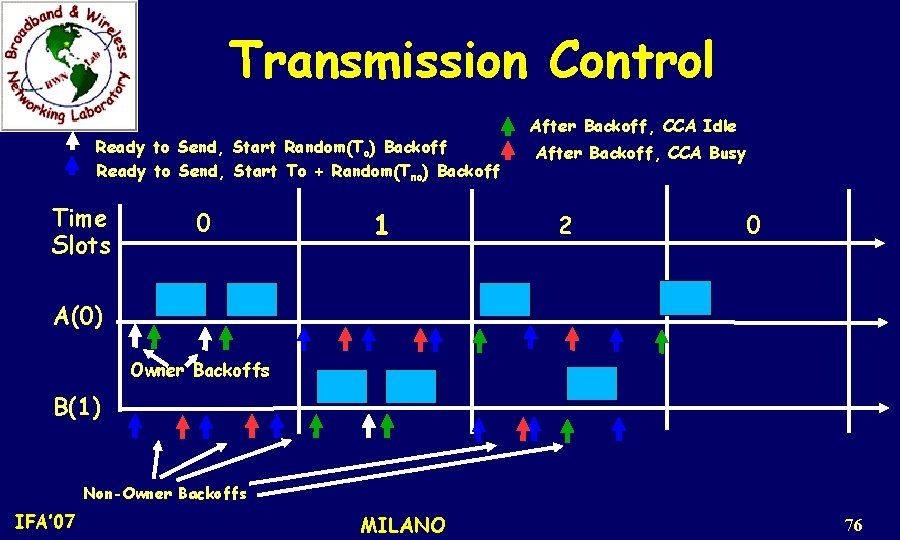
Transmission Control Ready to Send, Start Random(To) Backoff Ready to Send, Start To + Random(Tno) Backoff Time Slots 0 1 After Backoff, CCA Idle After Backoff, CCA Busy 2 0 A(0) Owner Backoffs B(1) Non-Owner Backoffs IFA’ 07 MILANO 76
Performance Results DRAND and ZMAC have been implemented on both NS 2 and on Mica 2 motes (Software can be downloaded from: http: //www. csc. ncsu. edu/faculty/rhee/export/zmac/index. html) IFA’ 07 MILANO 77
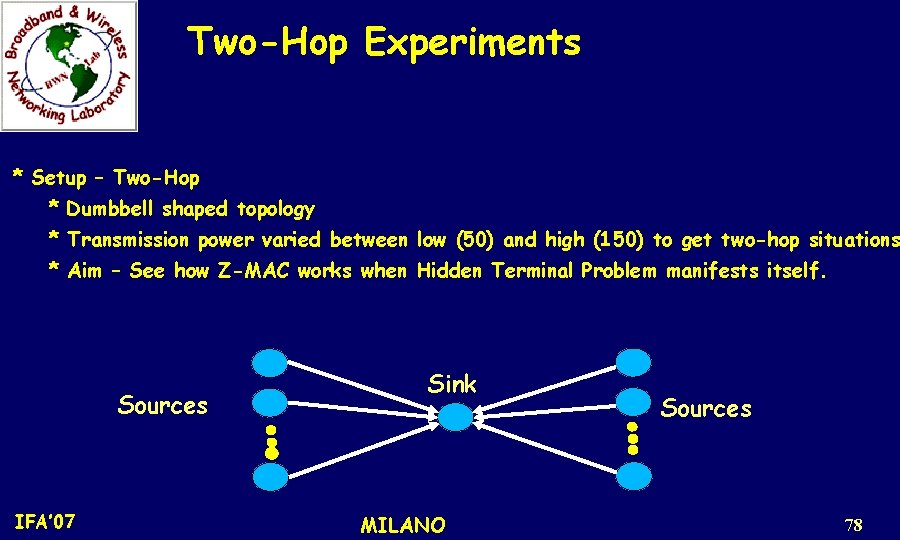
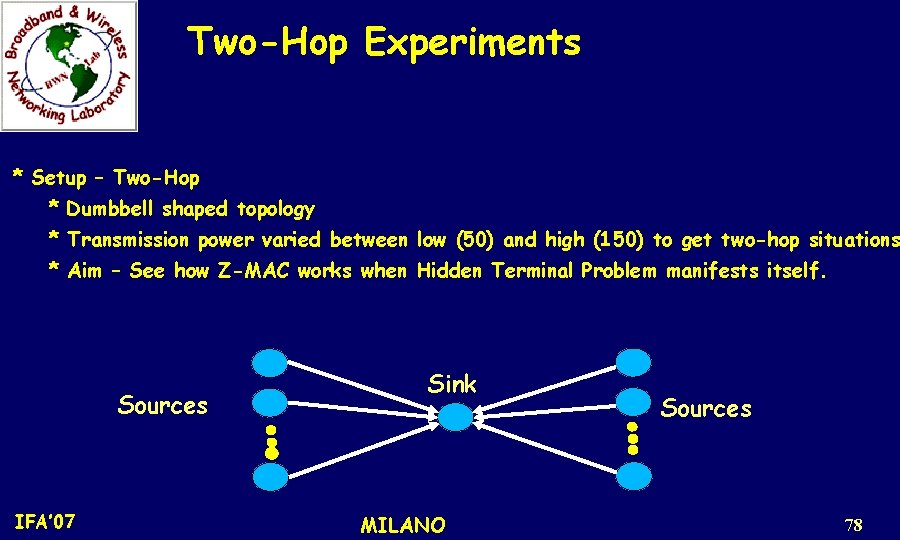
Two-Hop Experiments * Setup – Two-Hop * Dumbbell shaped topology * Transmission power varied between low (50) and high (150) to get two-hop situations * Aim – See how Z-MAC works when Hidden Terminal Problem manifests itself. Sources IFA’ 07 Sink MILANO Sources 78
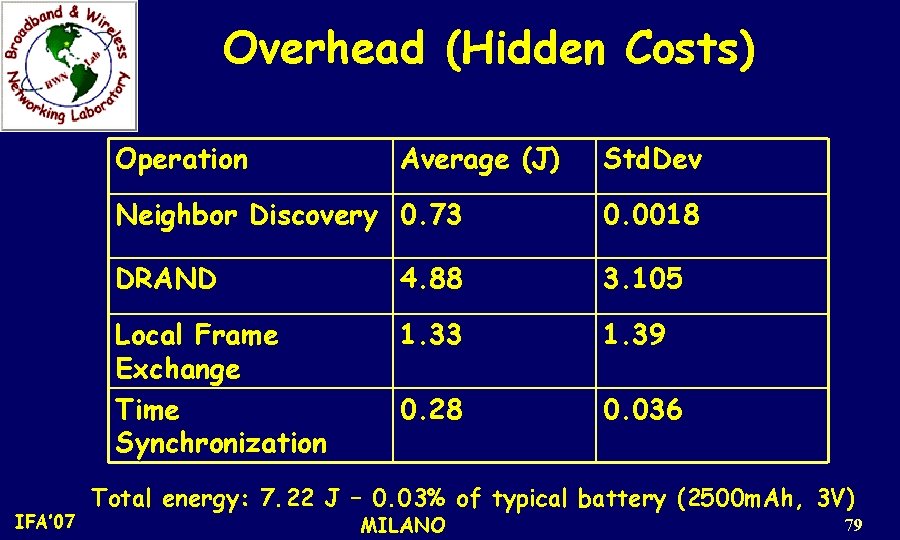
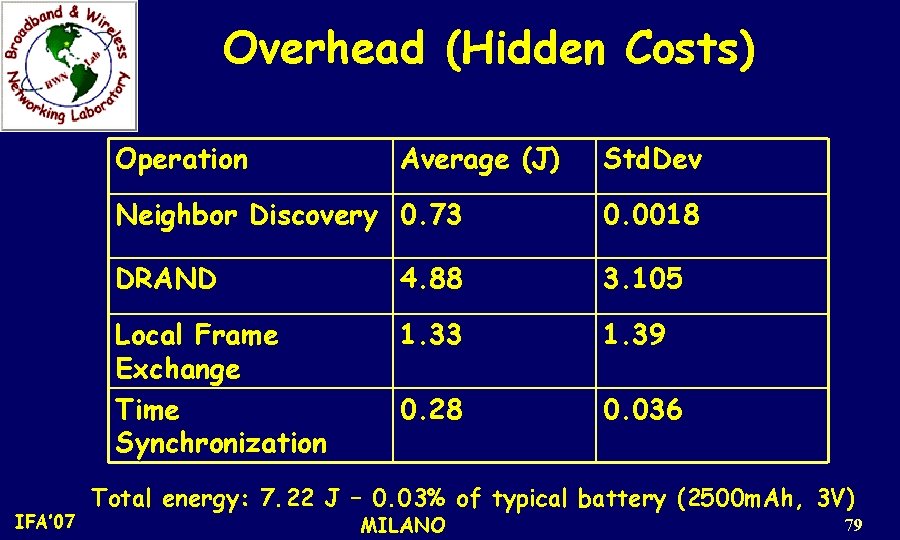
Overhead (Hidden Costs) Operation IFA’ 07 Average (J) Std. Dev Neighbor Discovery 0. 73 0. 0018 DRAND 4. 88 3. 105 Local Frame Exchange Time Synchronization 1. 33 1. 39 0. 28 0. 036 Total energy: 7. 22 J – 0. 03% of typical battery (2500 m. Ah, 3 V) MILANO 79
Open Research Issues 1. Mobility Support 2. Real-time Communication IFA’ 07 MILANO 80