Chapter 5 The Medium Access Sublayer 1 The
Chapter 5 The Medium Access Sublayer 1
The Medium Access Layer • 5. 1 Channel Allocation problem - Static and dynamic channel allocation in LANs & MANs • 5. 2 Multiple Access Protocols - ALOHA, CSMA/CD, Collision-free protocols, Limitedcontention protocols, Wireless LAN protocols • 5. 3 Ethernet - Cabling, MAC sublayer protocol, Backoff algorithm, Performance, Gigabit Ethernet, 802. 2 Logical Link Control • 5. 4 Wireless LANs - 802. 11 protocol stack, physical layer, MAC sublayer protocol, frame structure 2
• 5. 5 Broadband Wireless - Comparison of 802. 11 with 802. 16, protocol stack, frame structure • 5. 6 Bluetooth - Bluetooth architecture, Application, Protocol stack, Frame structure • 5. 7 Data Link Layer Switching - Bridges from 802. x to 802. y, Local internetworking, Spanning tree bridges, Remote bridges 3
What is MAC • Network assumption: Broadcast channel – One channel, many stations – Competition, interference among stations. • MAC: Medium Access Control – Also known as Multiple-Access Control – The protocol used to determine who goes next on a shared physical media • Classification of MAC protocols – Channel allocation (centralized) – Contention based protocols (distributed) – Contention – free protocols (distributed) 4
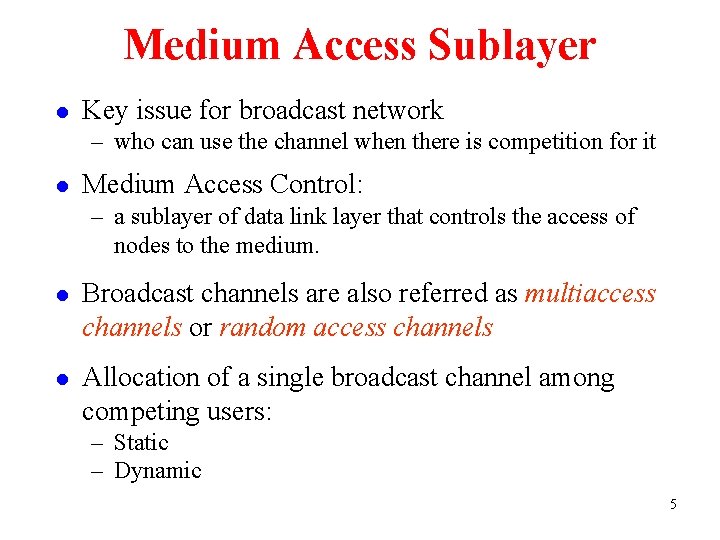
Medium Access Sublayer l Key issue for broadcast network – who can use the channel when there is competition for it l Medium Access Control: – a sublayer of data link layer that controls the access of nodes to the medium. l Broadcast channels are also referred as multiaccess channels or random access channels l Allocation of a single broadcast channel among competing users: – Static – Dynamic 5

5. 1 The Channel Allocation problem Static Channel Allocation l l l FDMA – The whole spectrum is divided into sub-frequency. TDMA – Each user has its own time slot. CDMA – Simultaneous transmission, Orthogonal code – Analogy: 6
![The M/M/1 Queue • Average number of customers E[ ] =L L • Applying The M/M/1 Queue • Average number of customers E[ ] =L L • Applying](http://slidetodoc.com/presentation_image_h/83b4f225d14a83f4a5a5009bf7f92c77/image-7.jpg)
The M/M/1 Queue • Average number of customers E[ ] =L L • Applying Little’s Theorem, we have • Similarly, the average waiting time and number of customers in the queue is given by 7
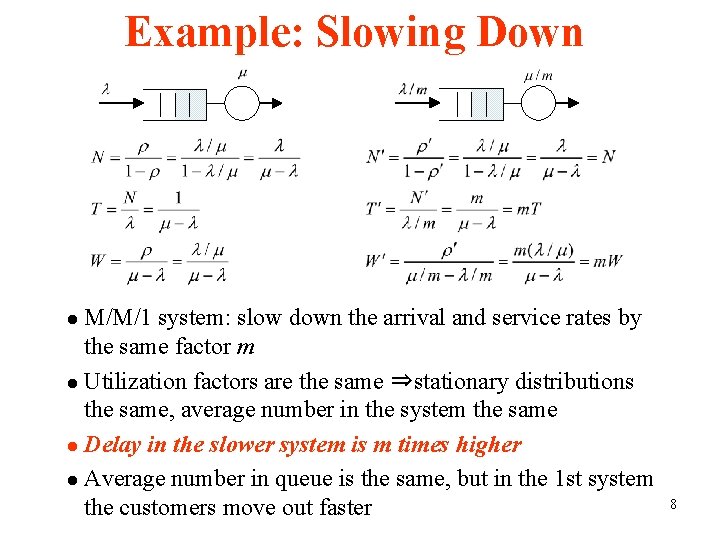
Example: Slowing Down M/M/1 system: slow down the arrival and service rates by the same factor m l Utilization factors are the same ⇒stationary distributions the same, average number in the system the same l Delay in the slower system is m times higher l Average number in queue is the same, but in the 1 st system the customers move out faster l 8
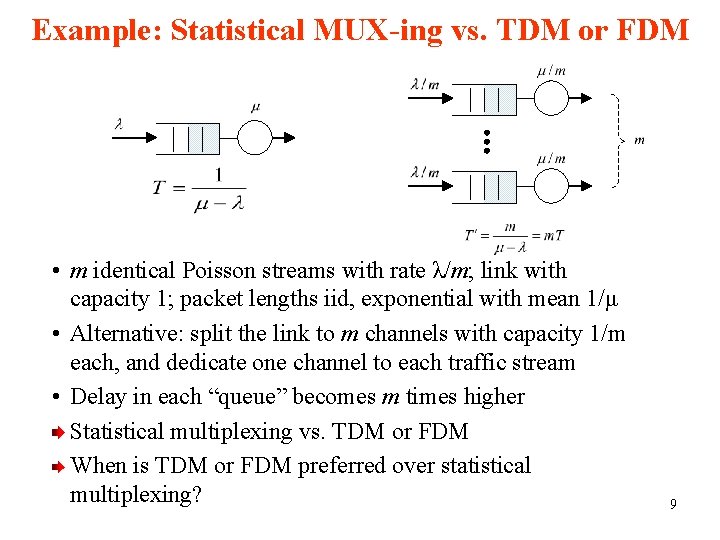
Example: Statistical MUX-ing vs. TDM or FDM • m identical Poisson streams with rate λ/m; link with capacity 1; packet lengths iid, exponential with mean 1/μ • Alternative: split the link to m channels with capacity 1/m each, and dedicate one channel to each traffic stream • Delay in each “queue” becomes m times higher Statistical multiplexing vs. TDM or FDM When is TDM or FDM preferred over statistical multiplexing? 9
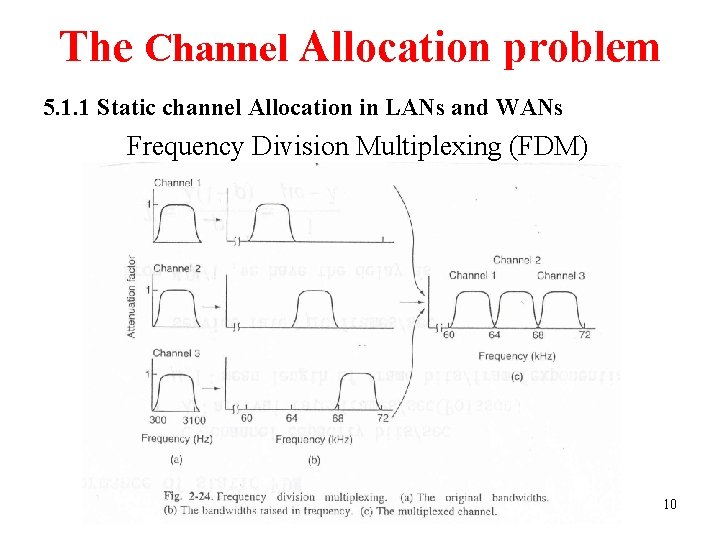
The Channel Allocation problem 5. 1. 1 Static channel Allocation in LANs and WANs Frequency Division Multiplexing (FDM) 10
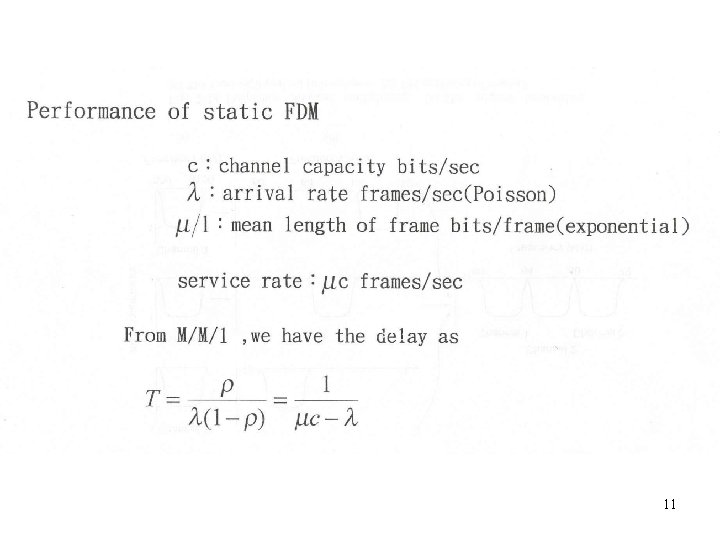
11
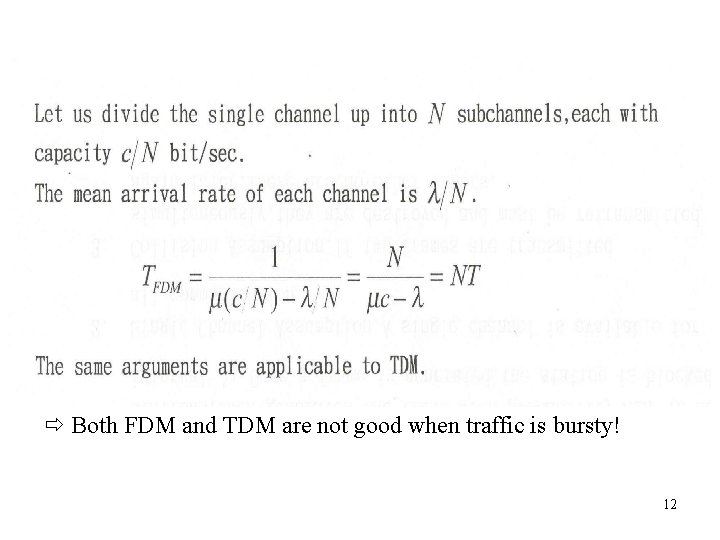
Both FDM and TDM are not good when traffic is bursty! 12
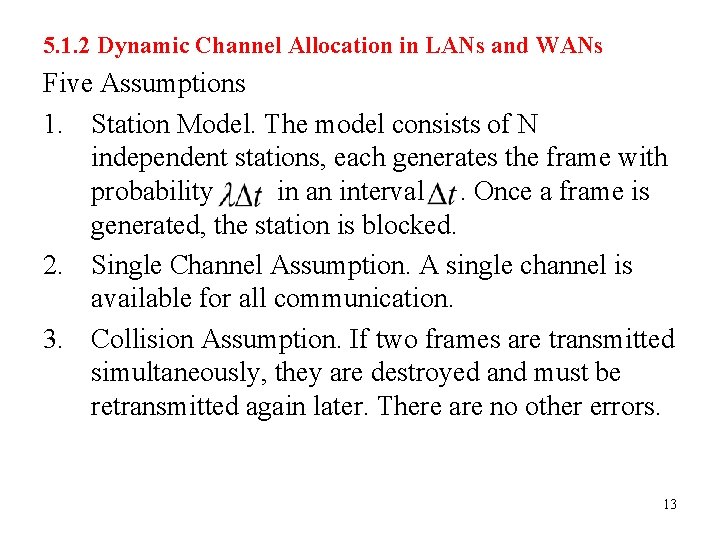
5. 1. 2 Dynamic Channel Allocation in LANs and WANs Five Assumptions 1. Station Model. The model consists of N independent stations, each generates the frame with probability in an interval. Once a frame is generated, the station is blocked. 2. Single Channel Assumption. A single channel is available for all communication. 3. Collision Assumption. If two frames are transmitted simultaneously, they are destroyed and must be retransmitted again later. There are no other errors. 13
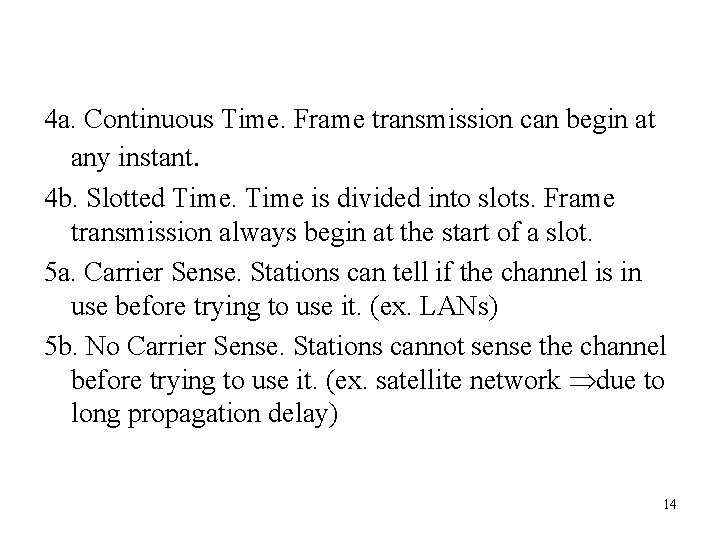
4 a. Continuous Time. Frame transmission can begin at any instant. 4 b. Slotted Time is divided into slots. Frame transmission always begin at the start of a slot. 5 a. Carrier Sense. Stations can tell if the channel is in use before trying to use it. (ex. LANs) 5 b. No Carrier Sense. Stations cannot sense the channel before trying to use it. (ex. satellite network due to long propagation delay) 14
5. 2 Multiple Access Protocols l ALOHA l Carrier Sense Multiple Access Protocols l Collision-Free Protocols l Limited-Contention Protocols l Wavelength Division Multiple Access Protocols l Wireless LAN Protocols 15
ALOHA l Users send whenever they want to send. If it fails, wait random time and resend it. l Independent stations l Single channel assumption l Collision occurs l Types of ALOHA – – – Pure ALOHA: stations transmit at any time (Continuous time) Slotted ALOHA: Transmission can only occur at certain time instances carrier sense vs no carrier senses 16
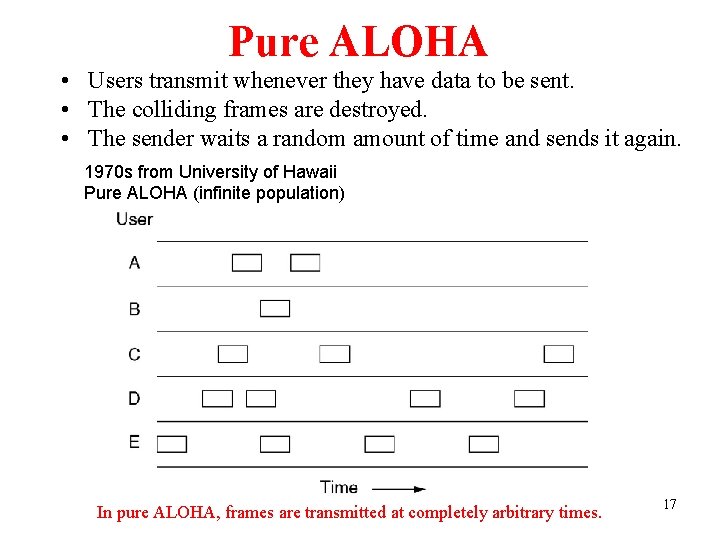
Pure ALOHA • Users transmit whenever they have data to be sent. • The colliding frames are destroyed. • The sender waits a random amount of time and sends it again. 1970 s from University of Hawaii Pure ALOHA (infinite population) In pure ALOHA, frames are transmitted at completely arbitrary times. 17

Pure ALOHA (2) Vulnerable period for the shaded frame. 18
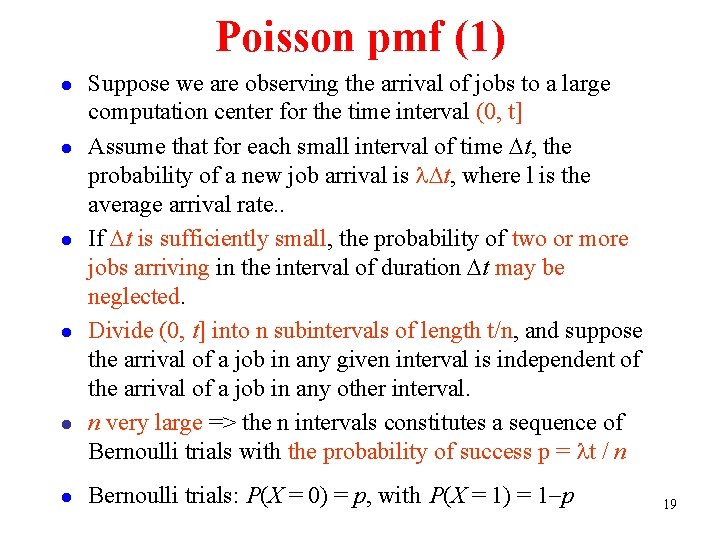
Poisson pmf (1) l l l Suppose we are observing the arrival of jobs to a large computation center for the time interval (0, t] Assume that for each small interval of time Dt, the probability of a new job arrival is l. Dt, where l is the average arrival rate. . If Dt is sufficiently small, the probability of two or more jobs arriving in the interval of duration Dt may be neglected. Divide (0, t] into n subintervals of length t/n, and suppose the arrival of a job in any given interval is independent of the arrival of a job in any other interval. n very large => the n intervals constitutes a sequence of Bernoulli trials with the probability of success p = lt / n Bernoulli trials: P(X = 0) = p, with P(X = 1) = 1 p 19
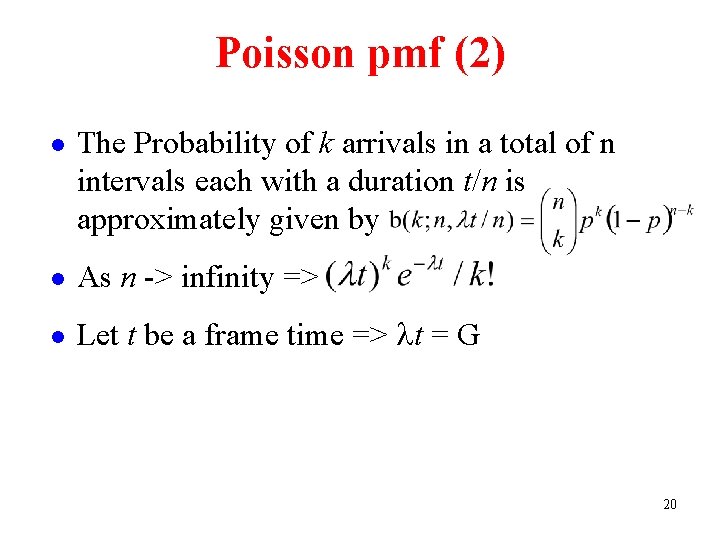
Poisson pmf (2) l The Probability of k arrivals in a total of n intervals each with a duration t/n is approximately given by l As n -> infinity => l Let t be a frame time => lt = G 20

21
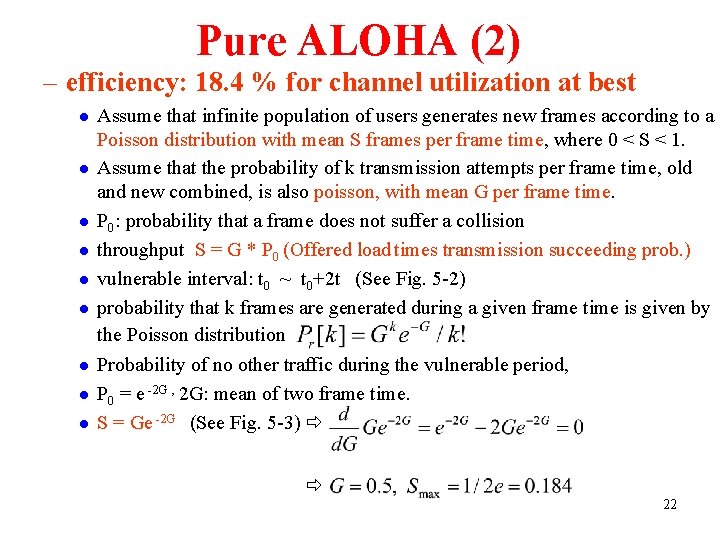
Pure ALOHA (2) – efficiency: 18. 4 % for channel utilization at best l l l l l Assume that infinite population of users generates new frames according to a Poisson distribution with mean S frames per frame time, where 0 < S < 1. Assume that the probability of k transmission attempts per frame time, old and new combined, is also poisson, with mean G per frame time. P 0: probability that a frame does not suffer a collision throughput S = G * P 0 (Offered load times transmission succeeding prob. ) vulnerable interval: t 0 ~ t 0+2 t (See Fig. 5 -2) probability that k frames are generated during a given frame time is given by the Poisson distribution Probability of no other traffic during the vulnerable period, P 0 = e -2 G , 2 G: mean of two frame time. S = Ge -2 G (See Fig. 5 -3) 22
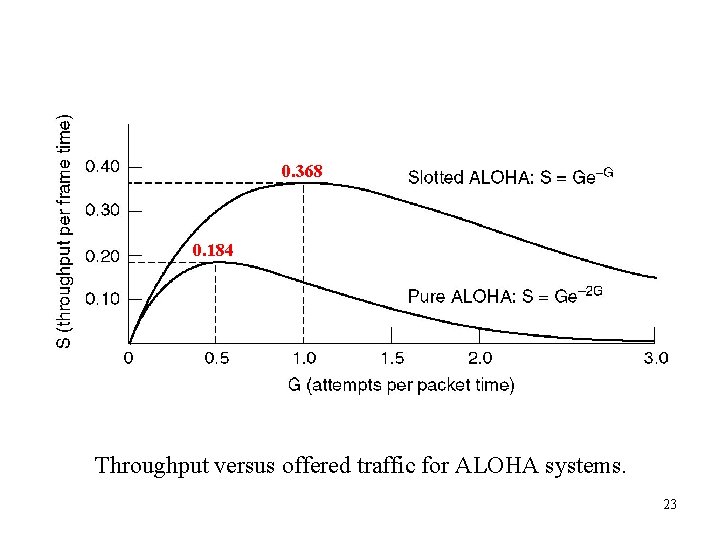
0. 368 0. 184 Throughput versus offered traffic for ALOHA systems. 23
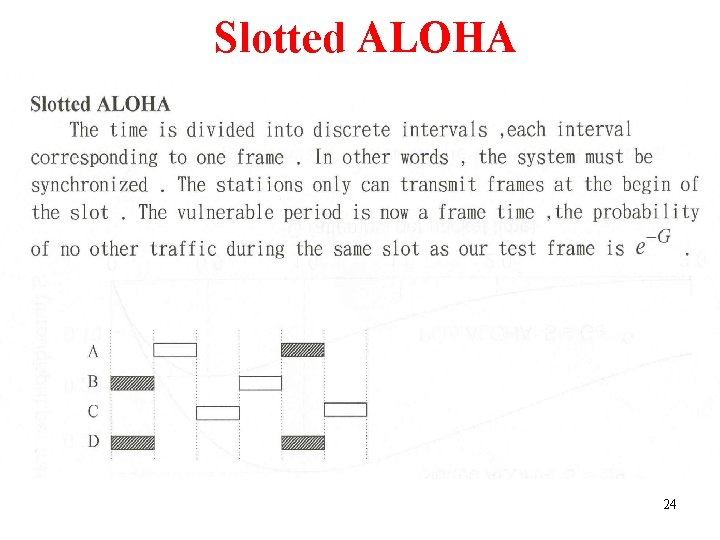
Slotted ALOHA 24
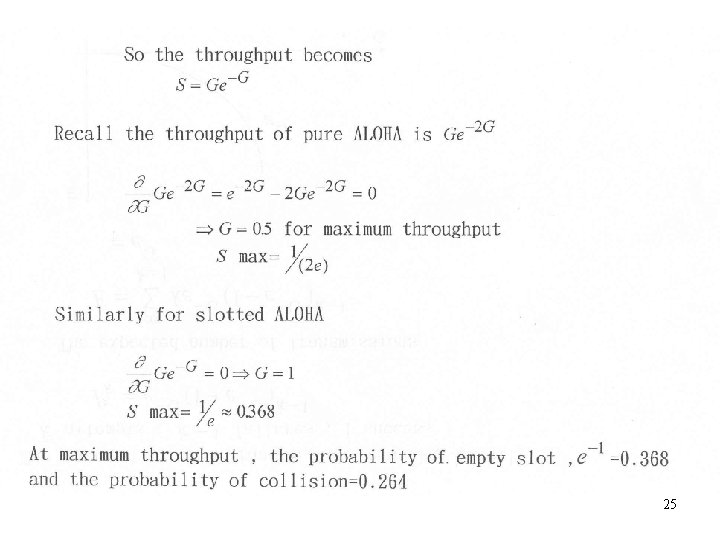
25
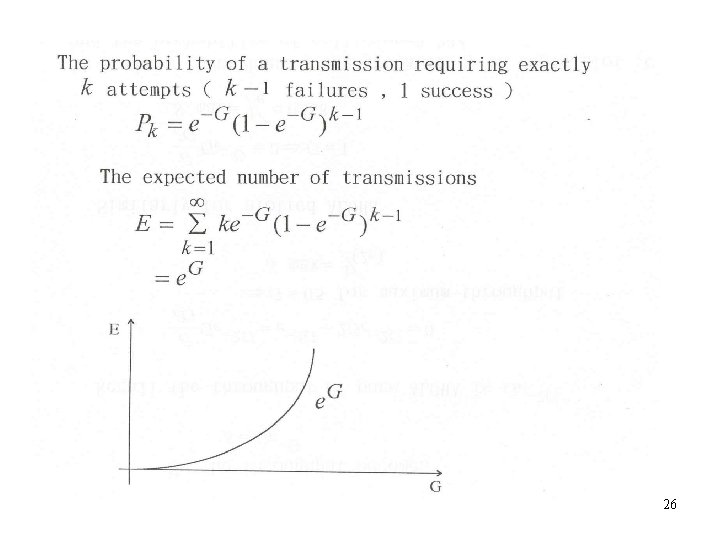
26

27

28
29

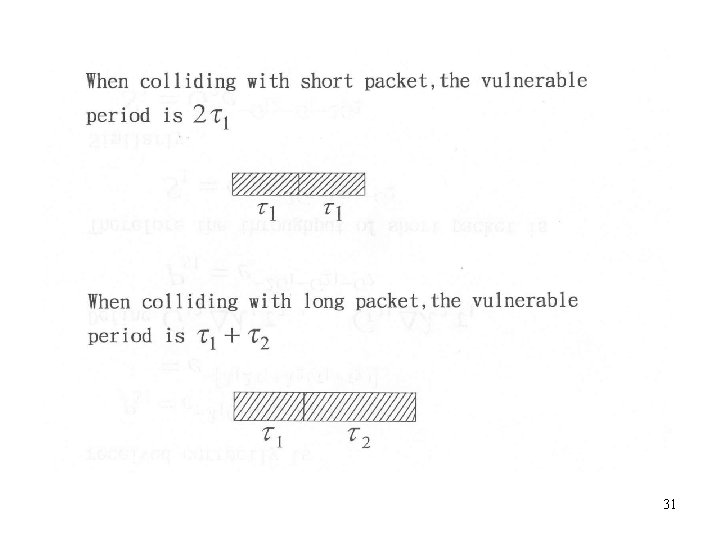
30
31
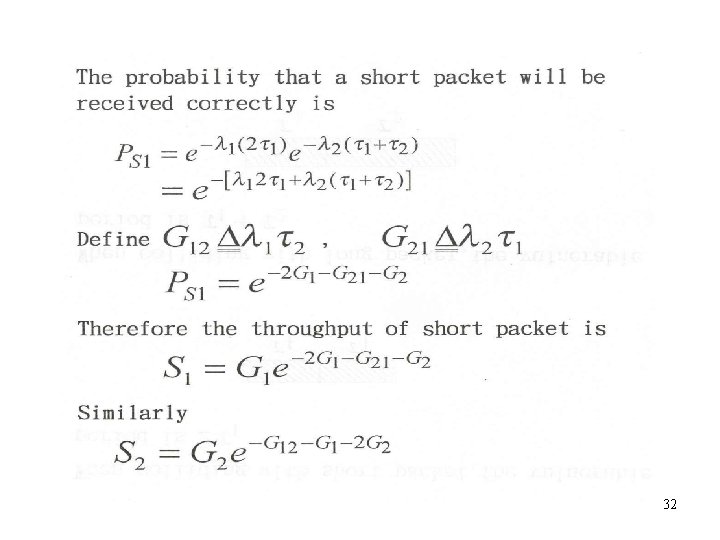
32
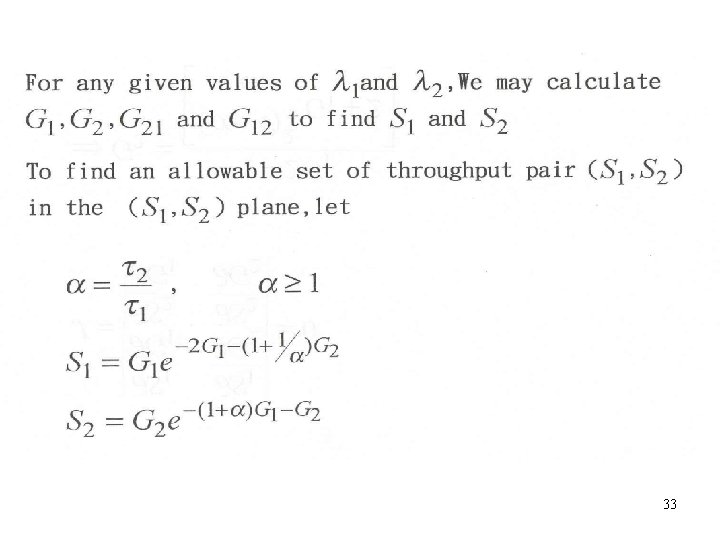
33

34

35
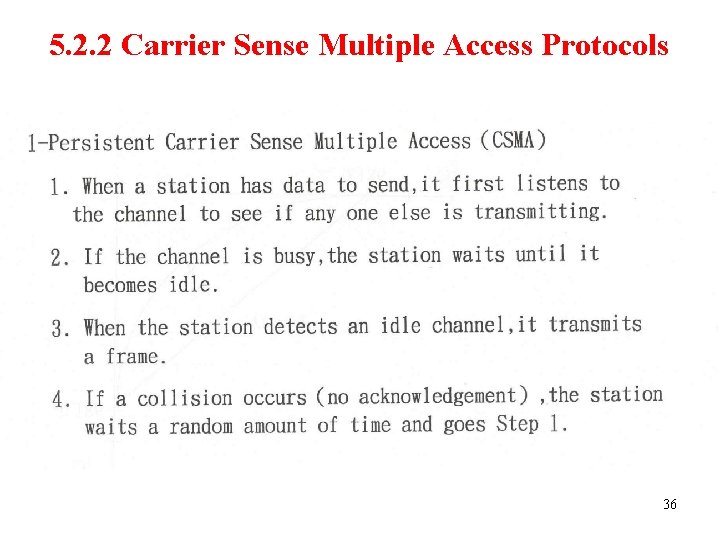
5. 2. 2 Carrier Sense Multiple Access Protocols 36

37
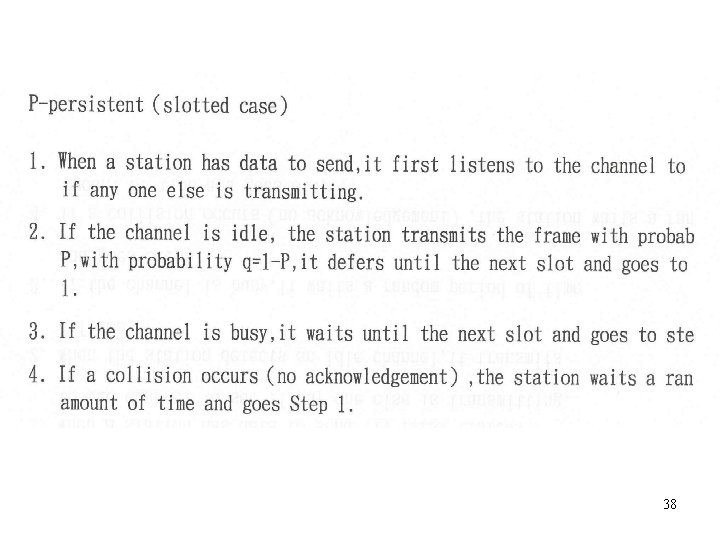
38
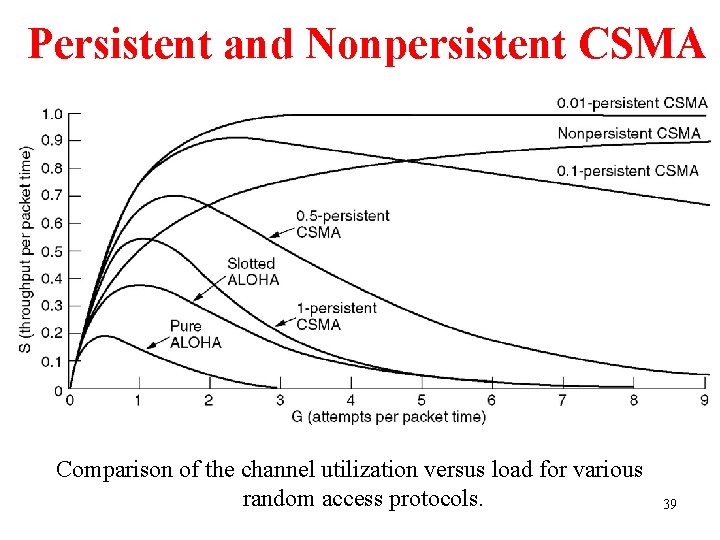
Persistent and Nonpersistent CSMA Comparison of the channel utilization versus load for various random access protocols. 39
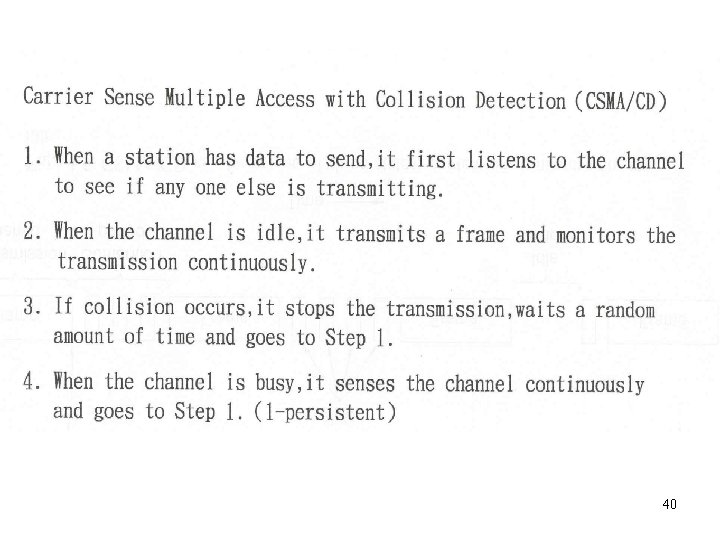
40

CSMA/CD • Abort transmission as soon as they detect a collision – saves time and bandwidth – waits a random time and tries again • Fig. 5 -5 – minimum time to detect collision: the signal propagates from one station to the other – worst case: 2 t (t : propagation time between two farthest stations) – model the contention interval as a slotted ALOHA system with slot = 2 t – special signal encoding: to detect a collision of two 0 -volt signals • No MAC sublayer protocol guarantees reliable delivery. Packets may be lost due to – collision – lack of buffer space – missed interrupt 41
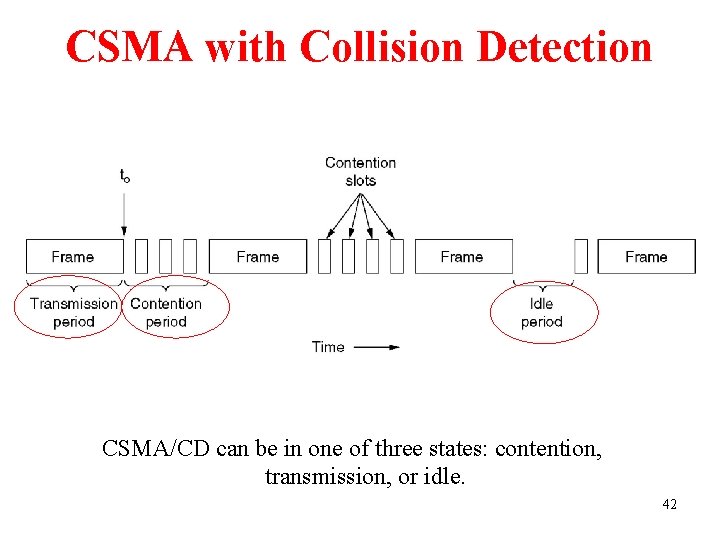
CSMA with Collision Detection CSMA/CD can be in one of three states: contention, transmission, or idle. 42
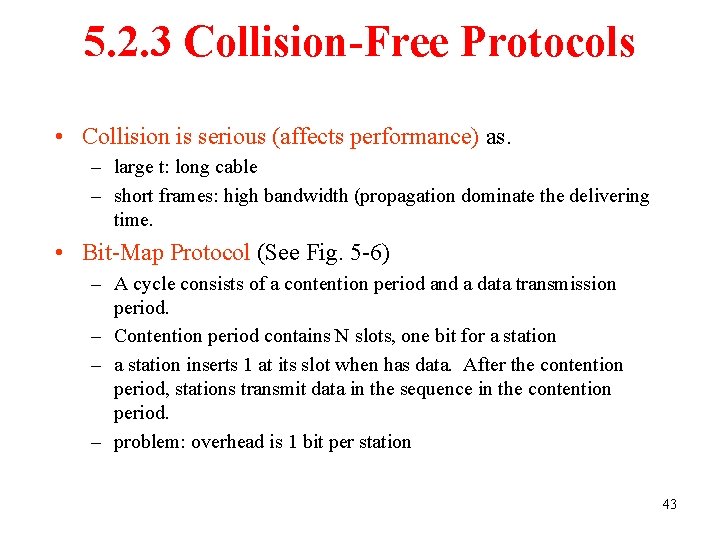
5. 2. 3 Collision-Free Protocols • Collision is serious (affects performance) as. – large t: long cable – short frames: high bandwidth (propagation dominate the delivering time. • Bit-Map Protocol (See Fig. 5 -6) – A cycle consists of a contention period and a data transmission period. – Contention period contains N slots, one bit for a station – a station inserts 1 at its slot when has data. After the contention period, stations transmit data in the sequence in the contention period. – problem: overhead is 1 bit per station 43

5. 2. 3 Collision-Free Protocols 4 - bit-map protocol. The basic 6. 44

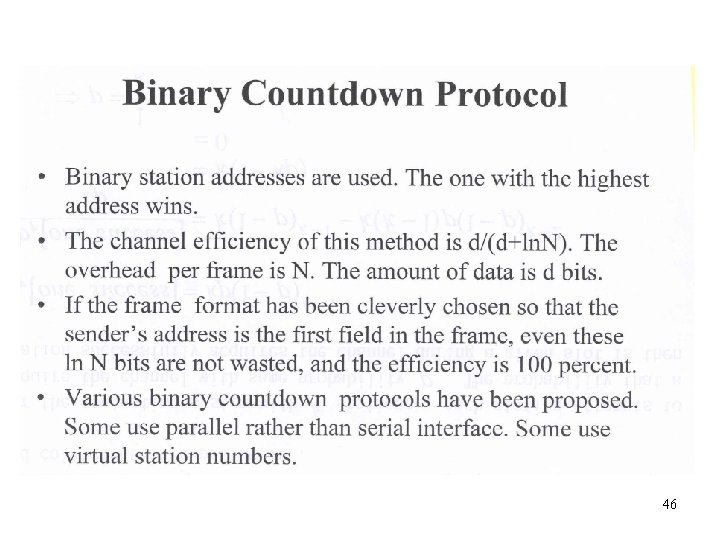
Collision-Free Protocols (2) • Binary Countdown – Give priority to higher address by OR bit-by-bit addresses of the stations waiting for transmission. – virtual station number: to change priority 45 The binary countdown protocol. A dash indicates silence.
46
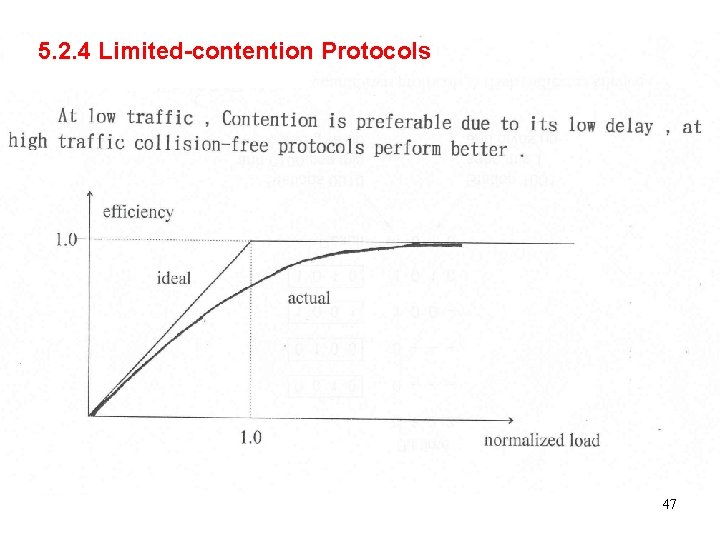
5. 2. 4 Limited-contention Protocols 47

Limited-Contention Protocols 48
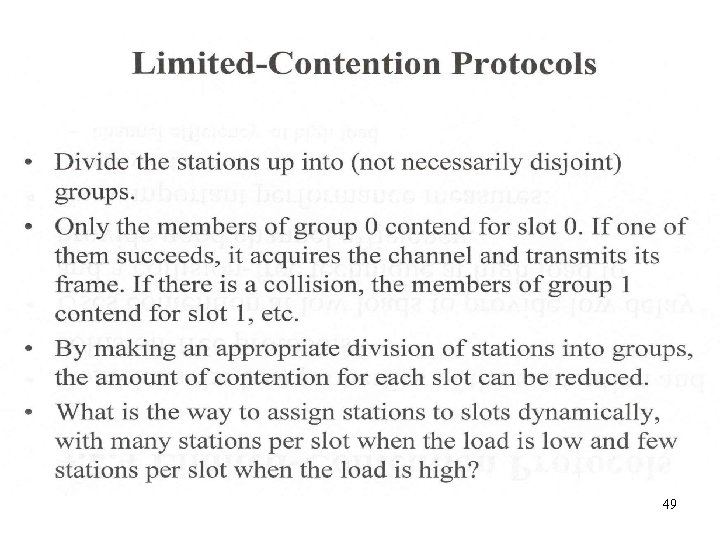
49

50
51
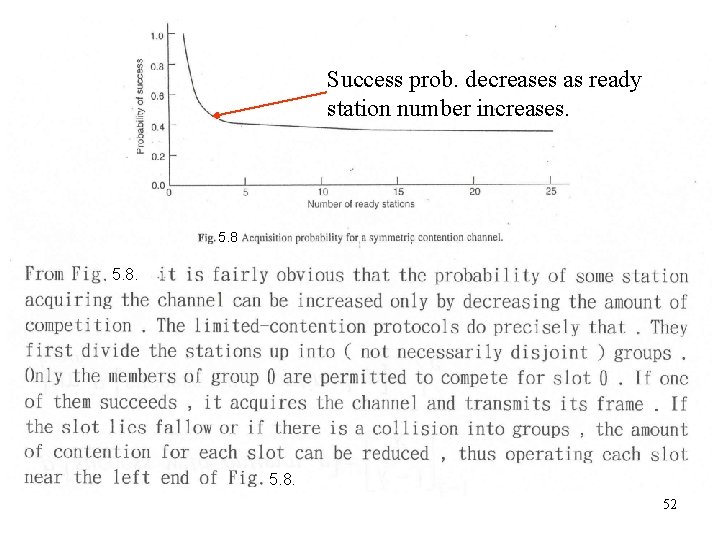
Success prob. decreases as ready station number increases. 5. 8. 52
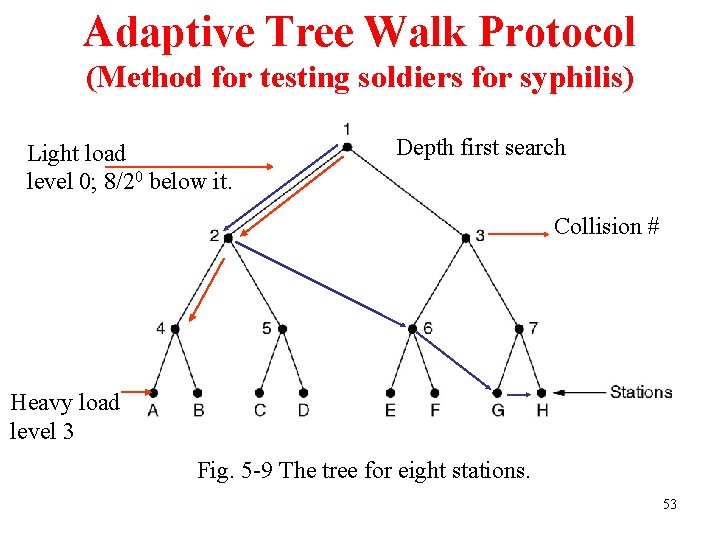
Adaptive Tree Walk Protocol (Method for testing soldiers for syphilis) Light load level 0; 8/20 below it. Depth first search Collision # Heavy load level 3 Fig. 5 -9 The tree for eight stations. 53
54
55

WDMA Protocols (1) l Channel allocation schemes: – divide the channel into subchannels using FDM, TDM, or both, and dynamically allocate them as needed – commonly used in fiber optic LANs: different conversations to use different wavelengths (frequencies) at the same time 56
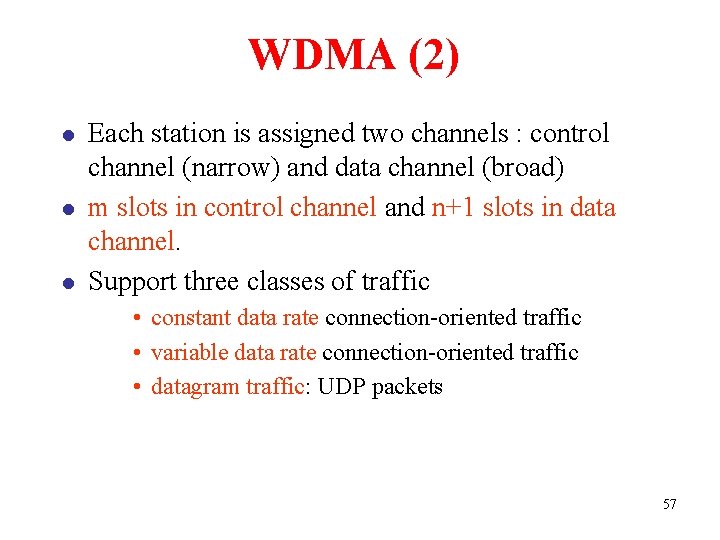
WDMA (2) l l l Each station is assigned two channels : control channel (narrow) and data channel (broad) m slots in control channel and n+1 slots in data channel. Support three classes of traffic • constant data rate connection-oriented traffic • variable data rate connection-oriented traffic • datagram traffic: UDP packets 57

WDMA Protocols (3) l Each station has – – l fixed-wavelength receiver for its own control channel tuneable transmitter to other station’s control channel fixed-wavelength transmitter to output data frames tuneable receiver: selecting a data transmitter to listen to Communication from A to B – A inserts a Connection Request in a free slot on B’s control channel. – If B accepts, A sends its data on its data channel. 58
Wavelength Division Multiple Access Protocols Fig. 5 -10 Wavelength division multiple access. 59
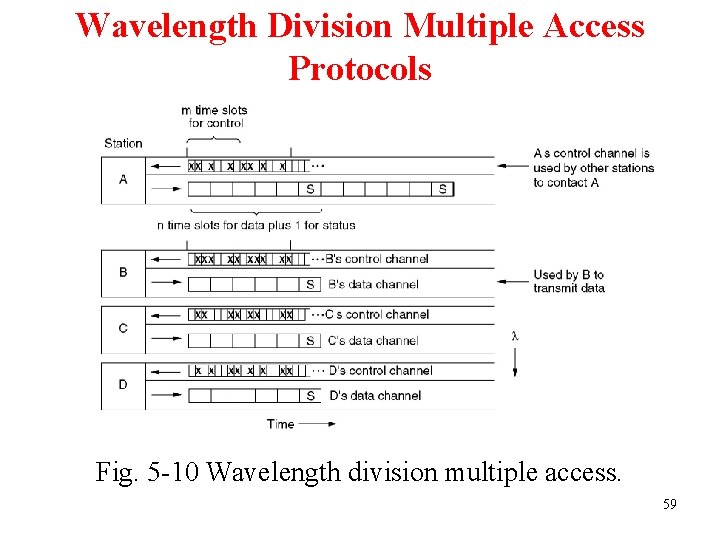
5. 2. 6 Wireless LAN Protocols 60
5 -11. 61
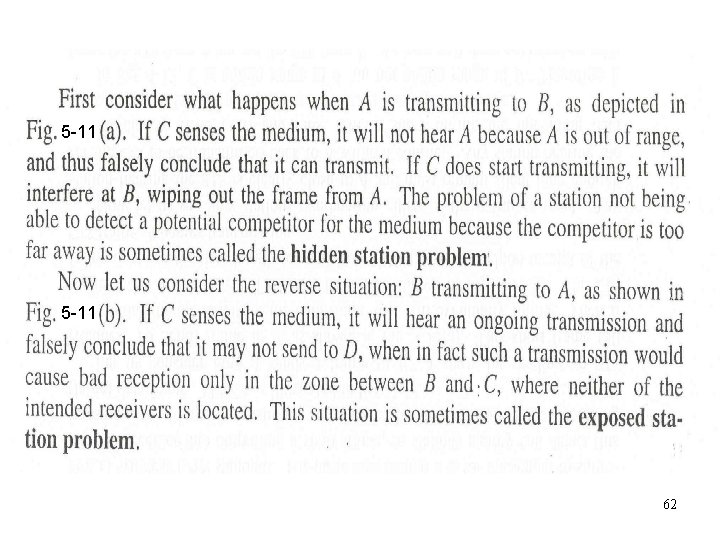
5 -11 62
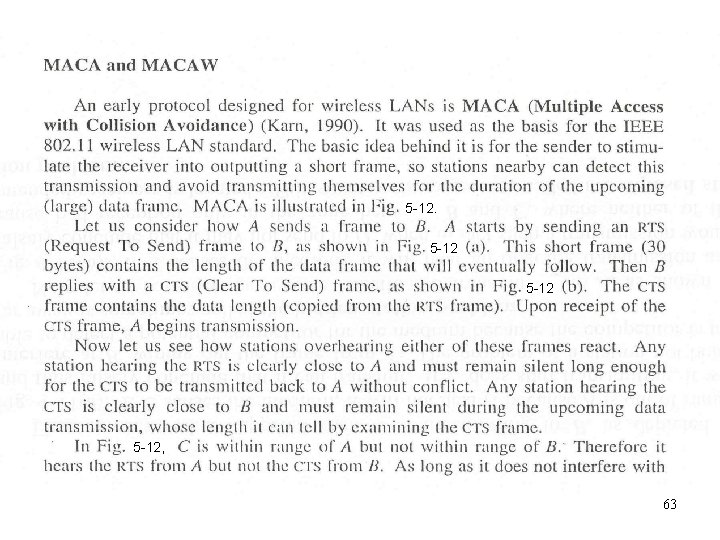
5 -12, 63
5 -12. 64

65
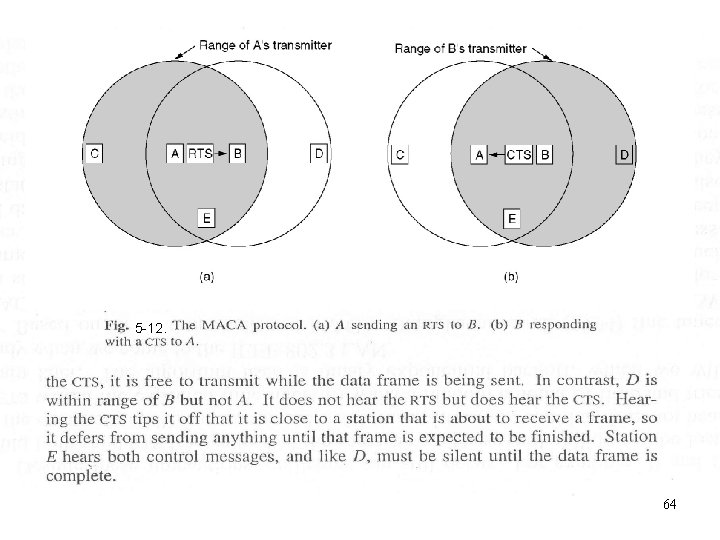
66
5. 3 Ethernet l l l l l Ethernet Cabling Manchester Encoding The Ethernet MAC Sublayer Protocol The Binary Exponential Backoff Algorithm Ethernet Performance Switched Ethernet Fast Ethernet Gigabit Ethernet IEEE 802. 2: Logical Link Control Retrospective on Ethernets 67
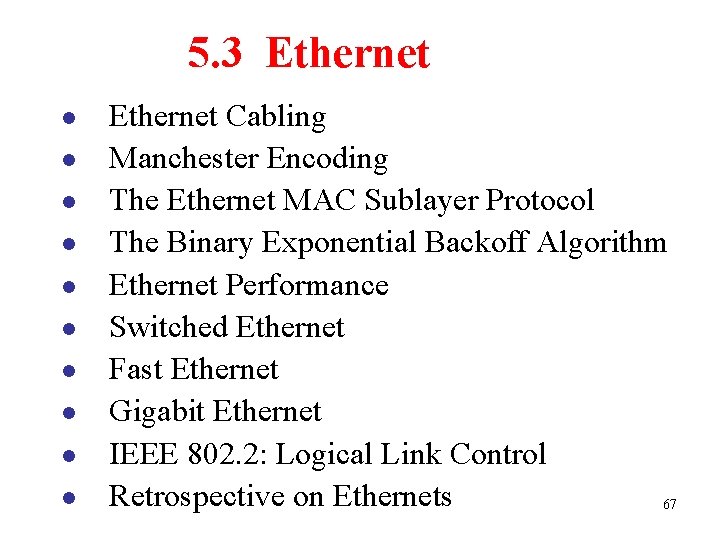
Ethernet Cabling The most common kinds of Ethernet cabling. 68
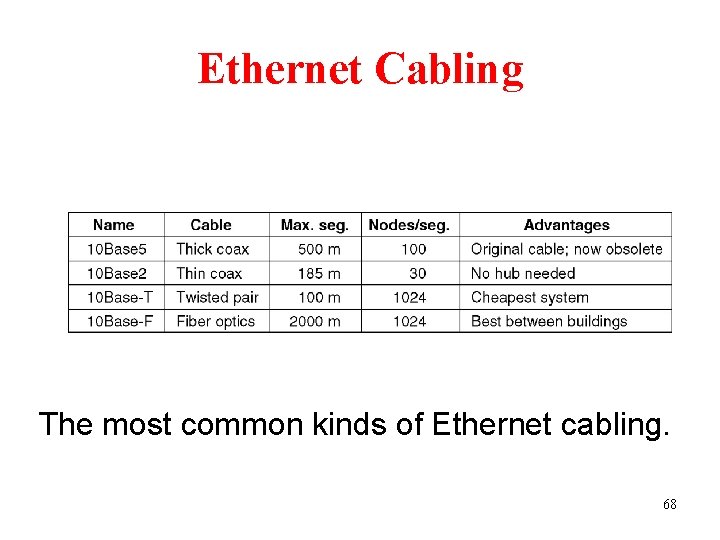
Ethernet Cabling (2) Three kinds of Ethernet cabling. (a) 10 Base 5, (b) 10 Base 2, (c) 10 Base-T 69
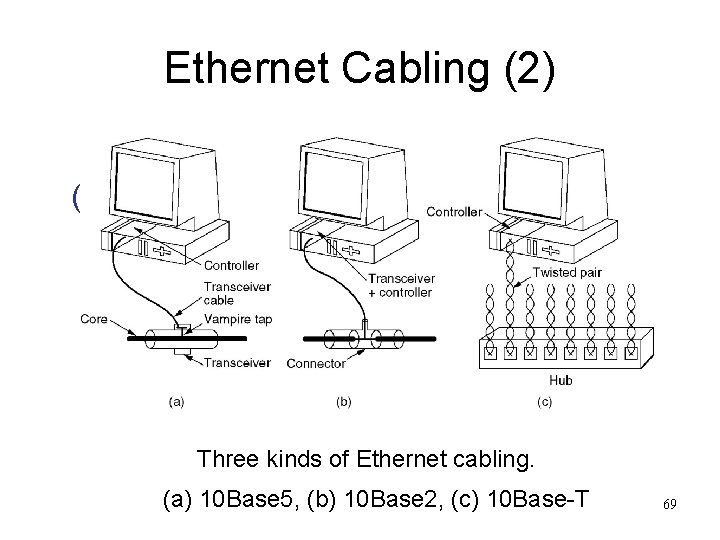
Ethernet Cabling (3) Cable topologies. (a) Linear, (b) Spine, (c) Tree, (d) Segmented. 70
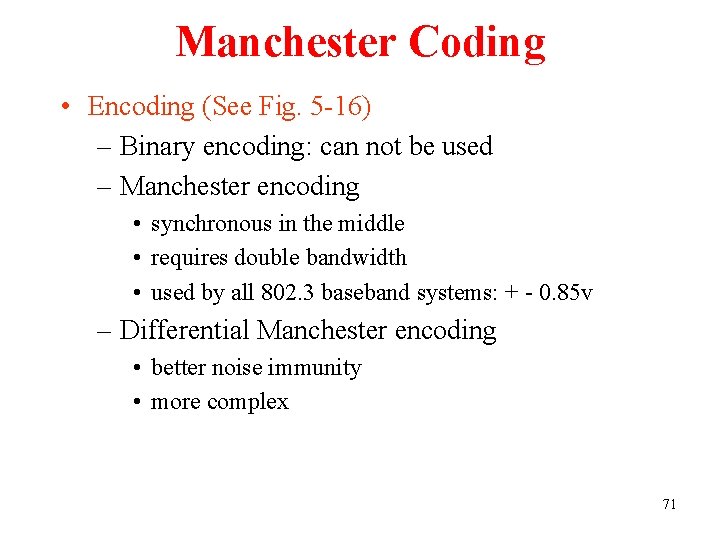
Manchester Coding • Encoding (See Fig. 5 -16) – Binary encoding: can not be used – Manchester encoding • synchronous in the middle • requires double bandwidth • used by all 802. 3 baseband systems: + - 0. 85 v – Differential Manchester encoding • better noise immunity • more complex 71

Ethernet Cabling (4) (a) Binary encoding, (b) Manchester encoding, (c) Differential Manchester encoding. 72
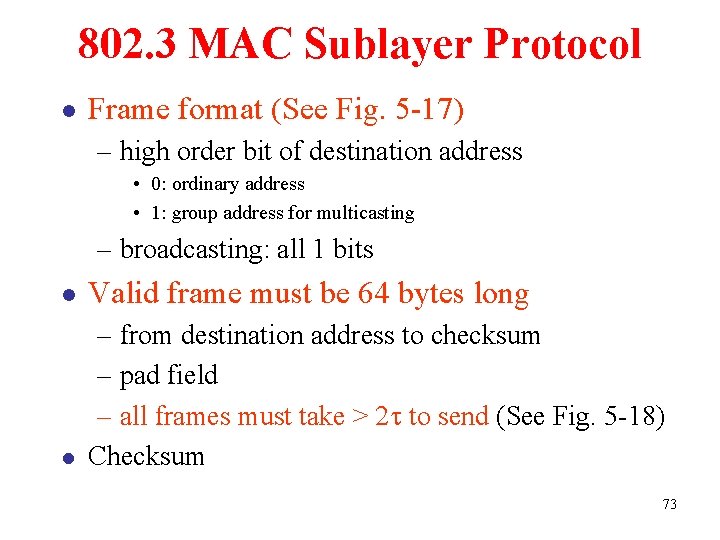
802. 3 MAC Sublayer Protocol l Frame format (See Fig. 5 -17) – high order bit of destination address • 0: ordinary address • 1: group address for multicasting – broadcasting: all 1 bits l Valid frame must be 64 bytes long l – from destination address to checksum – pad field – all frames must take > 2 t to send (See Fig. 5 -18) Checksum 73

Ethernet MAC Sublayer Protocol 0101 7 48 bits 1 SOF: Start of frame Frame formats. (a) DIX Ethernet, (b) IEEE 802. 3. DIX (DEC, Intel, Xerox) 74
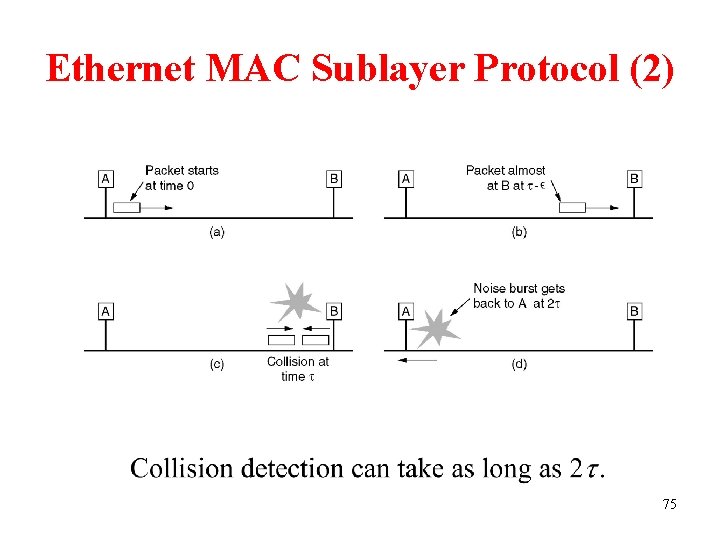
Ethernet MAC Sublayer Protocol (2) 75
Binary Exponential Backoff • After i collisions, random number 0 ~ 2 i - 1 1023 – time slot = 2 t (51. 2 us) – after 16 collisions: failure, recovery by higher layers • Acknowledgement – destination verifies checksum (for fear of noise) – ACK frame (not include in the protocol) – the 1 st contention slot following successful transmission 76

5. 3 Ethernet Performance Assumptions a. Heavy and constant load, that is, stations always ready to transmit b. Each station transmits during a contention slot with probability The probability A that some station acquires the channel in that slot is A is maximized when , with as 77

The probability that the contention interval has exactly it is so the mean number of slots per contention is given by Since each slot has a duration Assuming optimal , i. e. as If the mean frame takes slots in , the mean contention interval seconds to transmit then channel efficiency = where B: bandwidth F: frame length L: cable length C: propagation speed 78
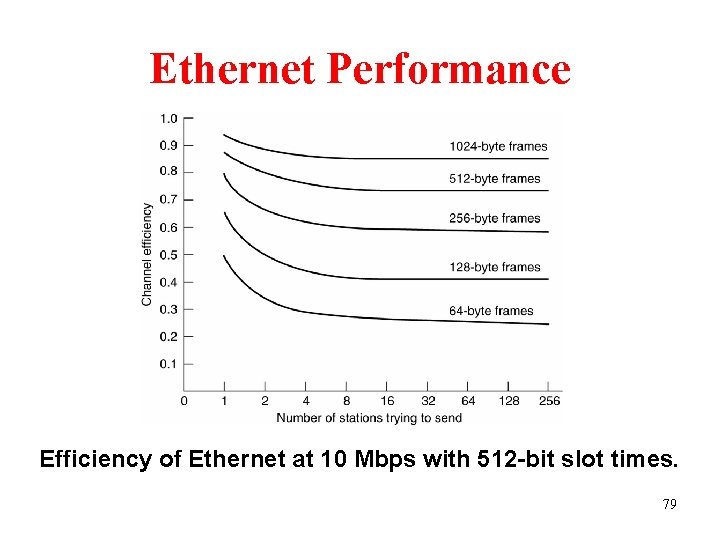
Ethernet Performance Efficiency of Ethernet at 10 Mbps with 512 -bit slot times. 79
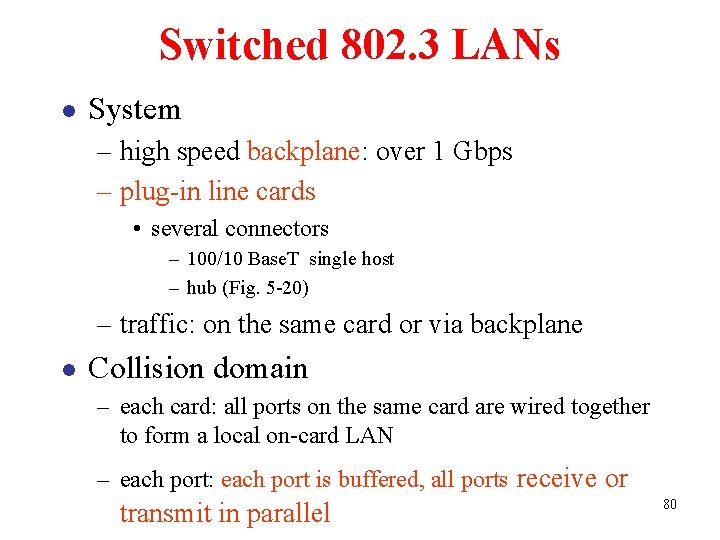
Switched 802. 3 LANs l System – high speed backplane: over 1 Gbps – plug-in line cards • several connectors – 100/10 Base. T single host – hub (Fig. 5 -20) – traffic: on the same card or via backplane l Collision domain – each card: all ports on the same card are wired together to form a local on-card LAN – each port: each port is buffered, all ports receive or transmit in parallel 80
Switched Ethernet 100/ A simple example of switched Ethernet. 81

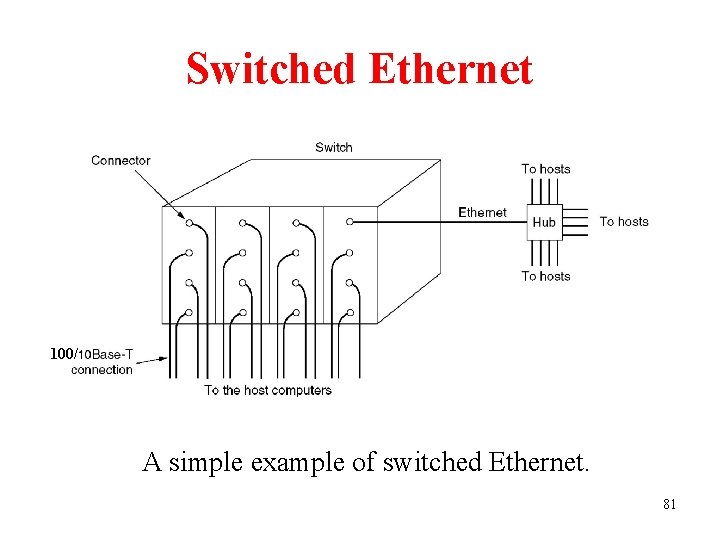
Fast Ethernet The reasons for fast Ethernet 1. The need to be backward compatible with existing Ethernet LANs 2. The fear that a new protocol might have unforeseen problems 3. The desire to get the job done before the technology changed All fast Ethernet systems use hubs and switches 100 Base-T 4 uses 8 B/6 T coding and 100 Base-TX uses 4 B/5 B coding The original fast Ethernet cabling. 82
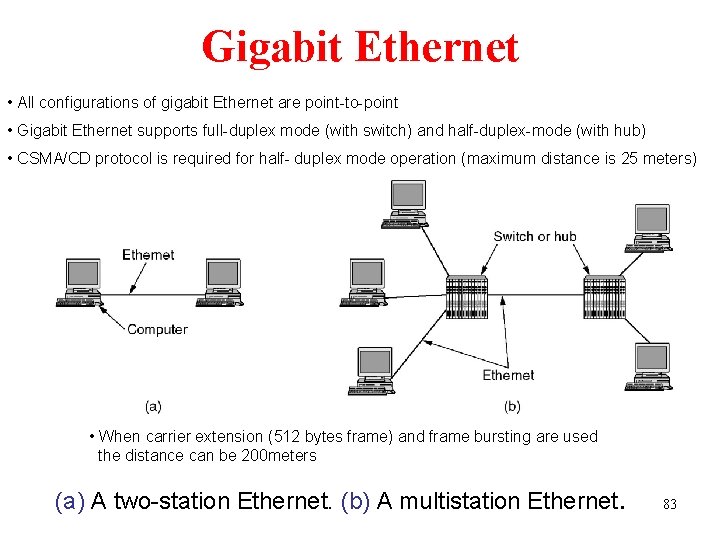
Gigabit Ethernet • All configurations of gigabit Ethernet are point-to-point • Gigabit Ethernet supports full-duplex mode (with switch) and half-duplex-mode (with hub) • CSMA/CD protocol is required for half- duplex mode operation (maximum distance is 25 meters) • When carrier extension (512 bytes frame) and frame bursting are used the distance can be 200 meters (a) A two-station Ethernet. (b) A multistation Ethernet. 83
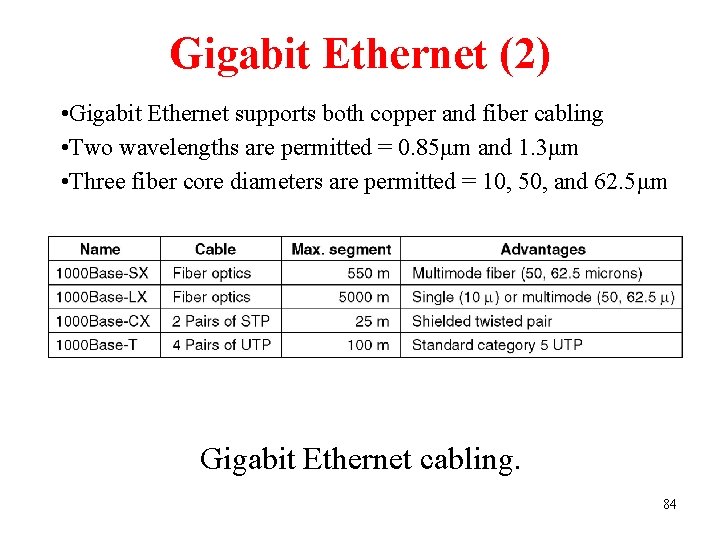
Gigabit Ethernet (2) • Gigabit Ethernet supports both copper and fiber cabling • Two wavelengths are permitted = 0. 85μm and 1. 3μm • Three fiber core diameters are permitted = 10, 50, and 62. 5μm Gigabit Ethernet cabling. 84

IEEE 802. 2: LLC l Logical Link Control – all 802 LANs and MAN: best-effort datagram services – on top of all 802 LANs and MAN: Fig. 4. 33 – a single format and interface to the Network Layer l Three service options of LLC – unreliable datagram service – acknowledged datagram service – reliable connection-oriented service 85
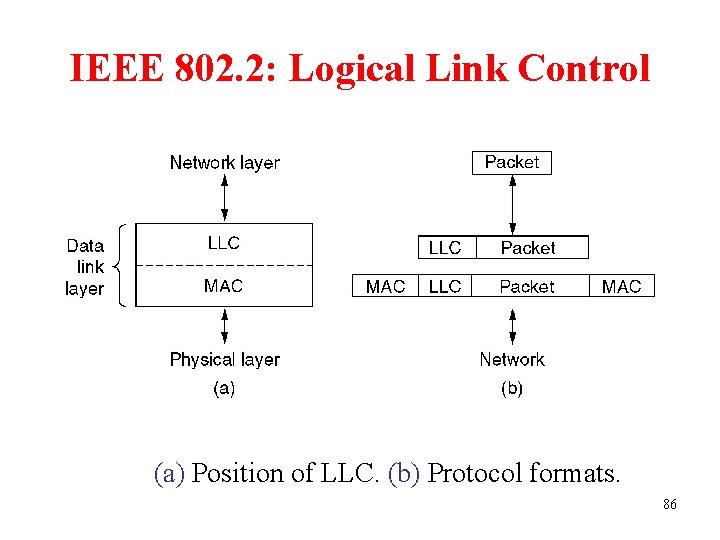
IEEE 802. 2: Logical Link Control (a) Position of LLC. (b) Protocol formats. 86
Retrospective on Ethernet 1. Ethernet is simple and flexible - reliable, cheap, easy to maintain, easy to install 2. Ethernet interworks easily with TCP/IP 3. Ethernet has been able to evolve in certain crucial ways - speeds gone up - hub and switches introduced 87
Wireless LANs l l l The 802. 11 Protocol Stack The 802. 11 Physical Layer The 802. 11 MAC Sublayer Protocol The 802. 11 Frame Structure Services 88
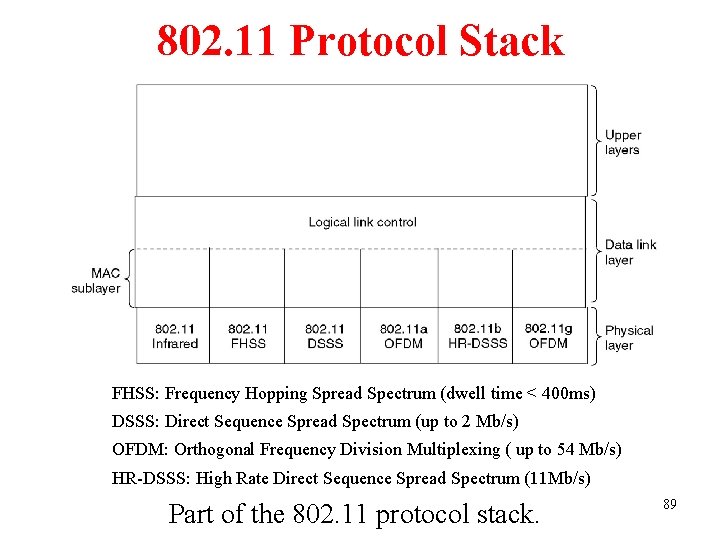
802. 11 Protocol Stack FHSS: Frequency Hopping Spread Spectrum (dwell time < 400 ms) DSSS: Direct Sequence Spread Spectrum (up to 2 Mb/s) OFDM: Orthogonal Frequency Division Multiplexing ( up to 54 Mb/s) HR-DSSS: High Rate Direct Sequence Spread Spectrum (11 Mb/s) Part of the 802. 11 protocol stack. 89
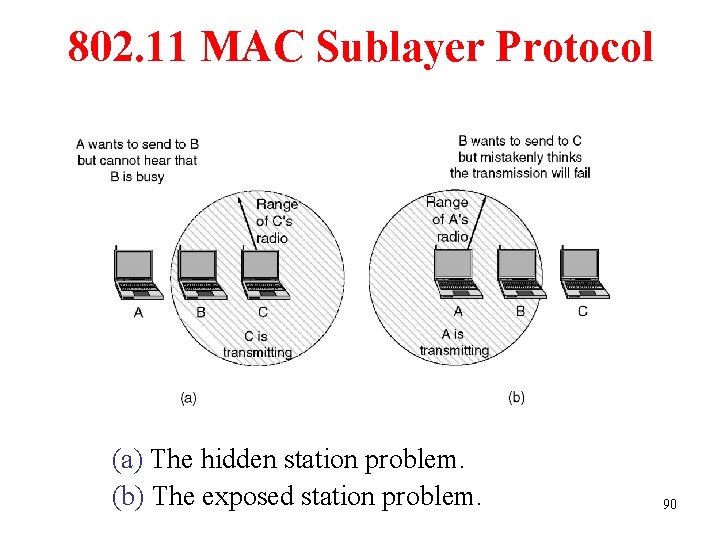
802. 11 MAC Sublayer Protocol (a) The hidden station problem. (b) The exposed station problem. 90
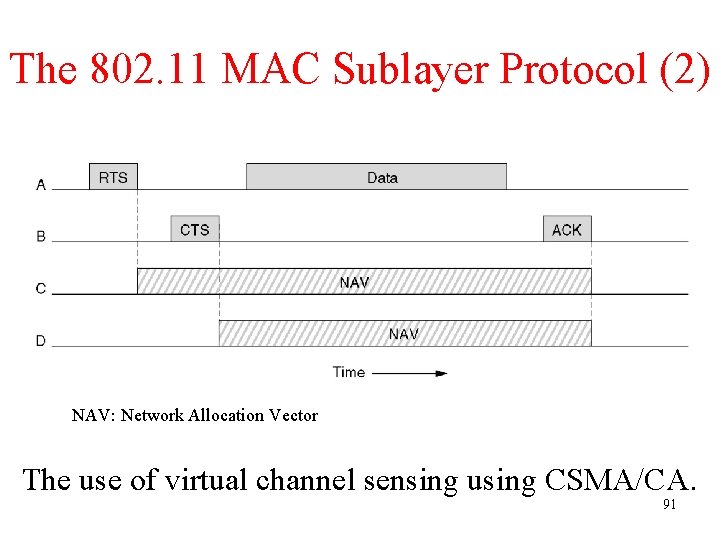
The 802. 11 MAC Sublayer Protocol (2) NAV: Network Allocation Vector The use of virtual channel sensing using CSMA/CA. 91
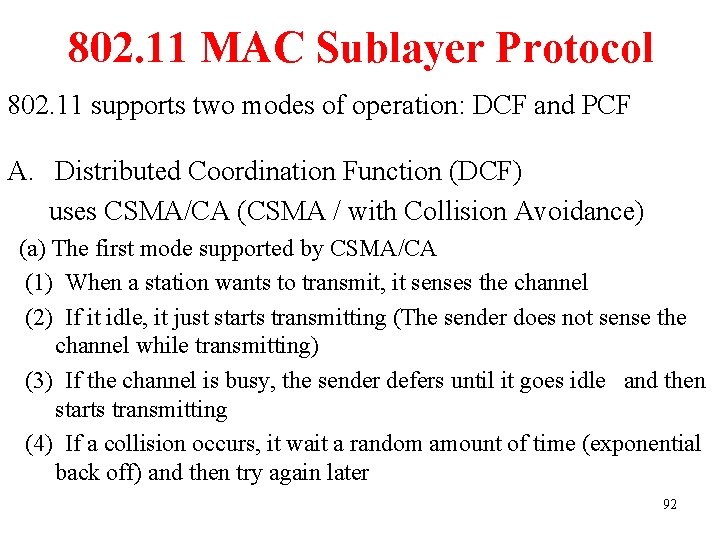
802. 11 MAC Sublayer Protocol 802. 11 supports two modes of operation: DCF and PCF A. Distributed Coordination Function (DCF) uses CSMA/CA (CSMA / with Collision Avoidance) (a) The first mode supported by CSMA/CA (1) When a station wants to transmit, it senses the channel (2) If it idle, it just starts transmitting (The sender does not sense the channel while transmitting) (3) If the channel is busy, the sender defers until it goes idle and then starts transmitting (4) If a collision occurs, it wait a random amount of time (exponential back off) and then try again later 92
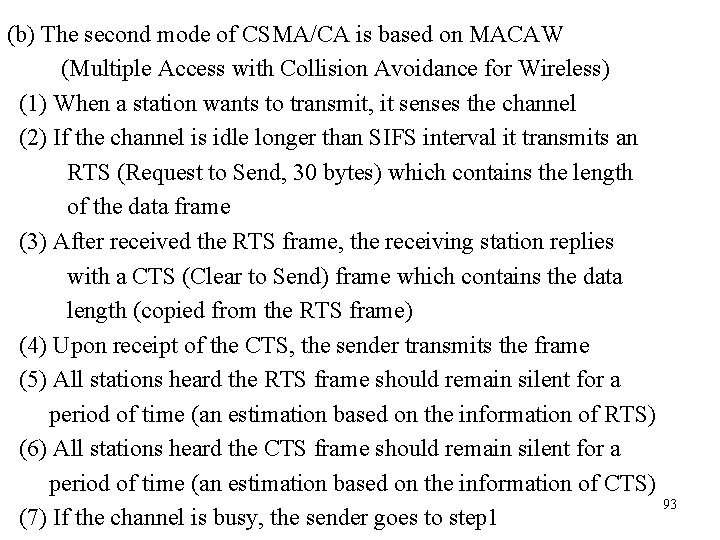
(b) The second mode of CSMA/CA is based on MACAW (Multiple Access with Collision Avoidance for Wireless) (1) When a station wants to transmit, it senses the channel (2) If the channel is idle longer than SIFS interval it transmits an RTS (Request to Send, 30 bytes) which contains the length of the data frame (3) After received the RTS frame, the receiving station replies with a CTS (Clear to Send) frame which contains the data length (copied from the RTS frame) (4) Upon receipt of the CTS, the sender transmits the frame (5) All stations heard the RTS frame should remain silent for a period of time (an estimation based on the information of RTS) (6) All stations heard the CTS frame should remain silent for a period of time (an estimation based on the information of CTS) 93 (7) If the channel is busy, the sender goes to step 1

94
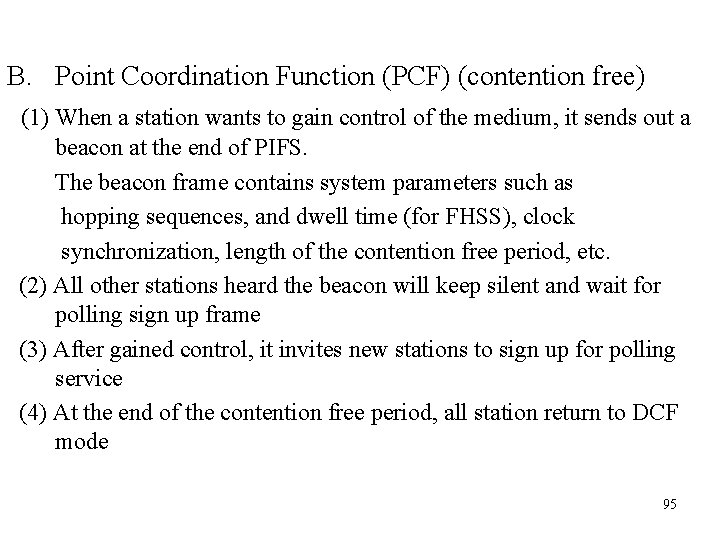
B. Point Coordination Function (PCF) (contention free) (1) When a station wants to gain control of the medium, it sends out a beacon at the end of PIFS. The beacon frame contains system parameters such as hopping sequences, and dwell time (for FHSS), clock synchronization, length of the contention free period, etc. (2) All other stations heard the beacon will keep silent and wait for polling sign up frame (3) After gained control, it invites new stations to sign up for polling service (4) At the end of the contention free period, all station return to DCF mode 95
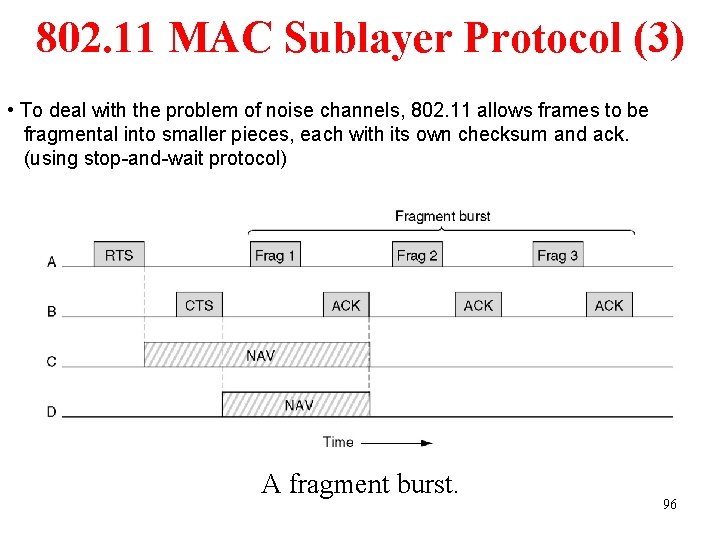
802. 11 MAC Sublayer Protocol (3) • To deal with the problem of noise channels, 802. 11 allows frames to be fragmental into smaller pieces, each with its own checksum and ack. (using stop-and-wait protocol) A fragment burst. 96
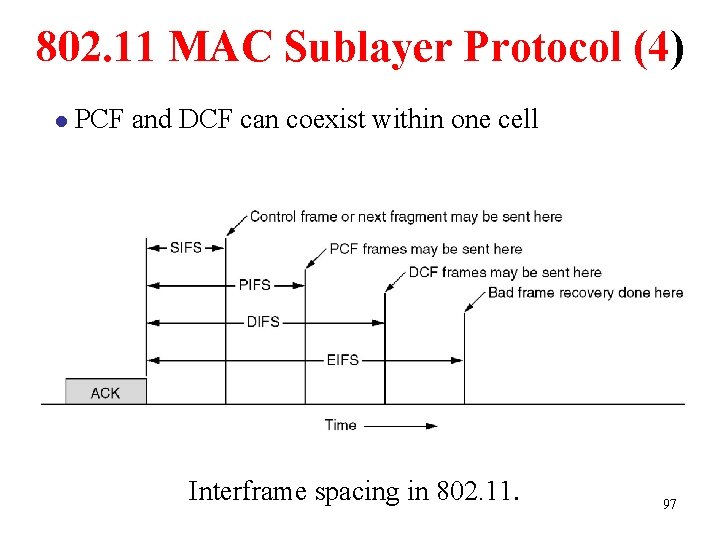
802. 11 MAC Sublayer Protocol (4) l PCF and DCF can coexist within one cell Interframe spacing in 802. 11. 97
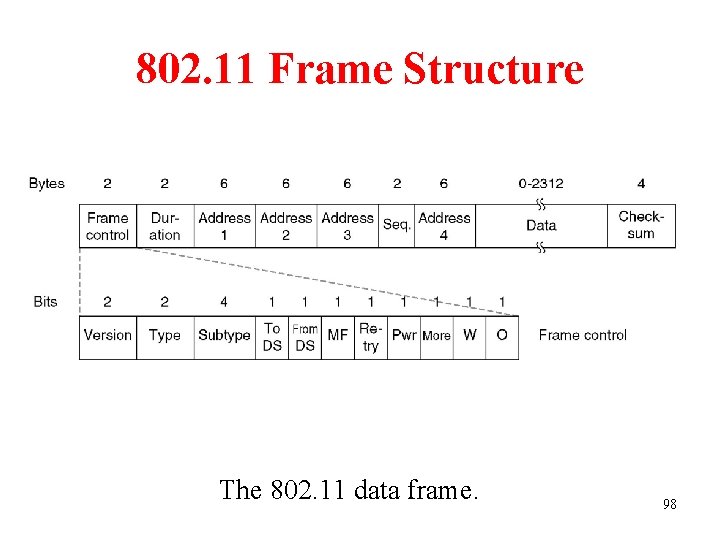
802. 11 Frame Structure The 802. 11 data frame. 98
Version: Protocol version Type: data, control, or management Subtype: RTS, CTS, ack, … To DS and from DS: to or from inter cell distribution system (e. g. Ethernet) MF: more fragments Retry: retransmission Power management: put the receiver into sleep state or take it out More: additional frames coming W: wired equivalent privacy O: processed strictly in order Duration: time length of the frame and ack Addresses 1. 2. 3 and 4: Source, destination, the source and destination base stations for intercell traffic 99 Sequence: Sequence No.
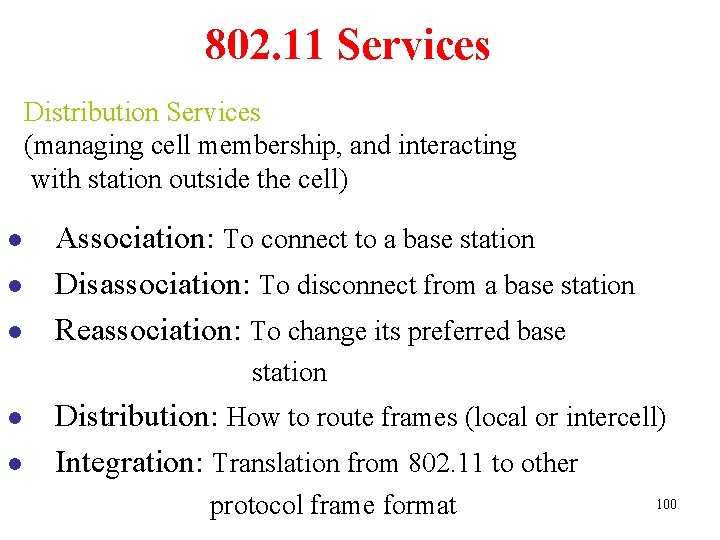
802. 11 Services Distribution Services (managing cell membership, and interacting with station outside the cell) l l l Association: To connect to a base station Disassociation: To disconnect from a base station Reassociation: To change its preferred base station l l Distribution: How to route frames (local or intercell) Integration: Translation from 802. 11 to other protocol frame format 100
802. 11 Services Intracell Services l l Authentication Deauthentication (leave the network) Privacy: managing the encryption and decryption Data Delivery 101
Broadband Wireless l l l Comparison of 802. 11 and 802. 16 The 802. 16 Protocol Stack The 802. 16 Physical Layer The 802. 16 MAC Sublayer Protocol The 802. 16 Frame Structure 102
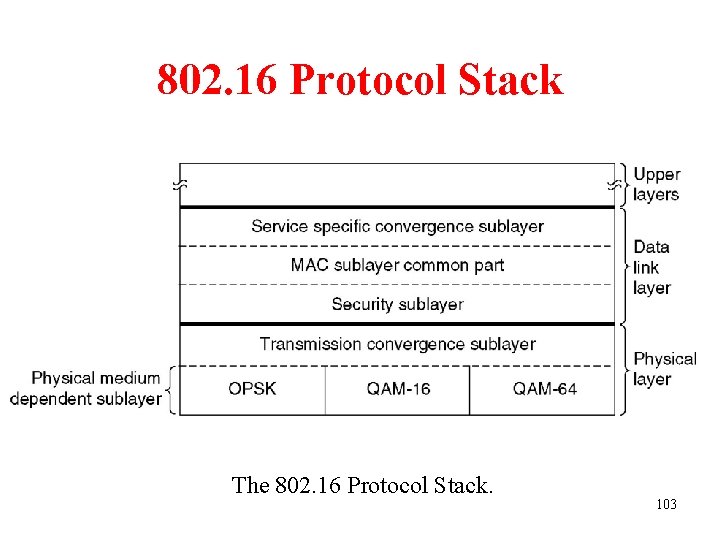
802. 16 Protocol Stack The 802. 16 Protocol Stack. 103
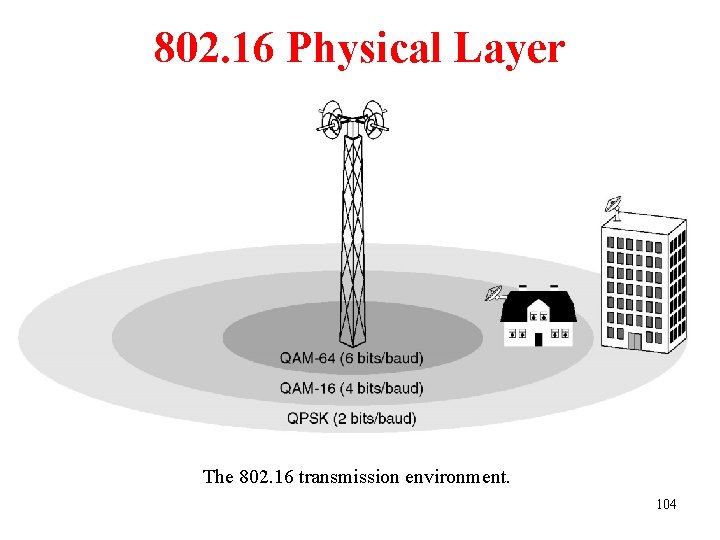
802. 16 Physical Layer The 802. 16 transmission environment. 104
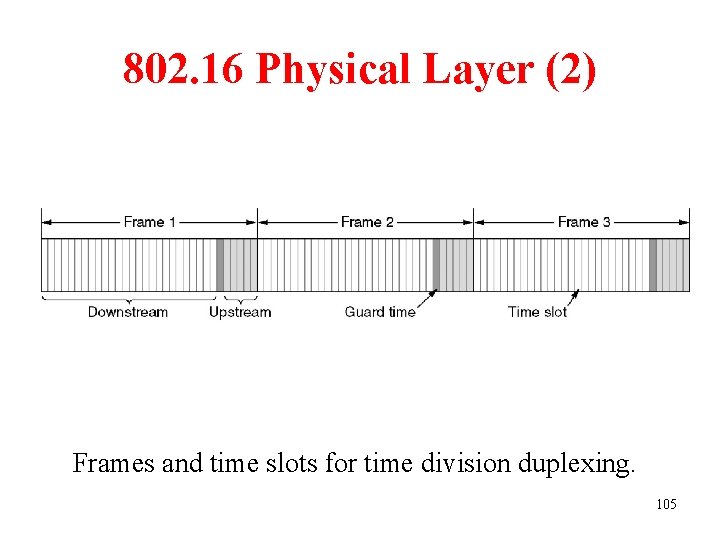
802. 16 Physical Layer (2) Frames and time slots for time division duplexing. 105
802. 16 MAC Sublayer Protocol Service Classes l Constant bit rate service l Real-time variable bit rate service l Non-real-time variable bit rate service l Best efforts service 106
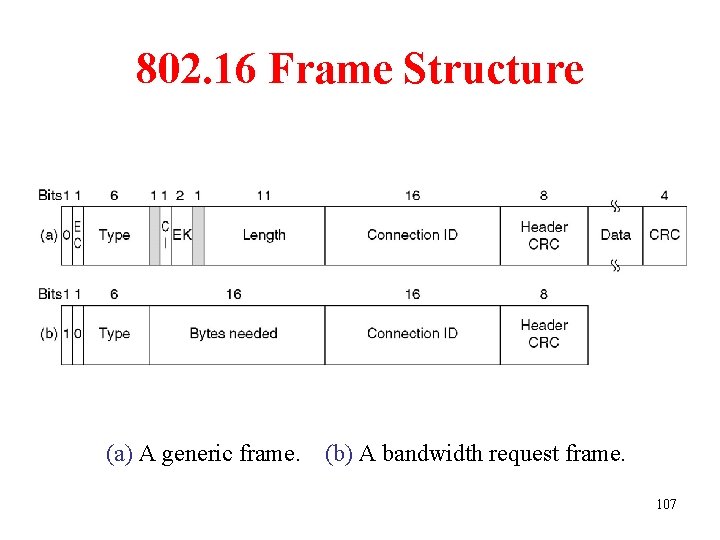
802. 16 Frame Structure (a) A generic frame. (b) A bandwidth request frame. 107
Bluetooth l Bluetooth Architecture l Bluetooth Applications l The Bluetooth Protocol Stack l The Bluetooth Radio Layer l The Bluetooth Baseband Layer l The Bluetooth L 2 CAP Layer l The Bluetooth Frame Structure 108
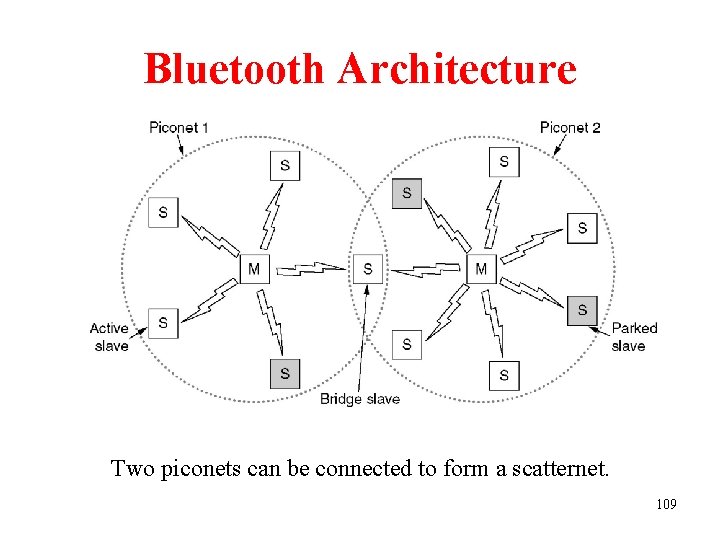
Bluetooth Architecture Two piconets can be connected to form a scatternet. 109
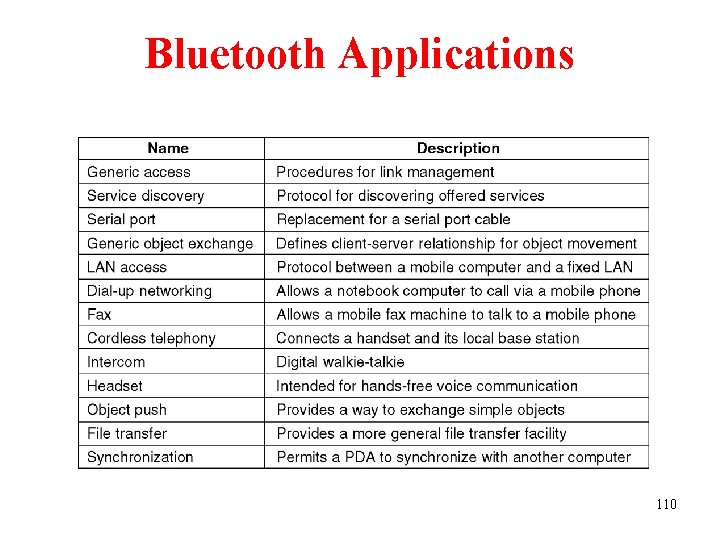
Bluetooth Applications The Bluetooth profiles. 110
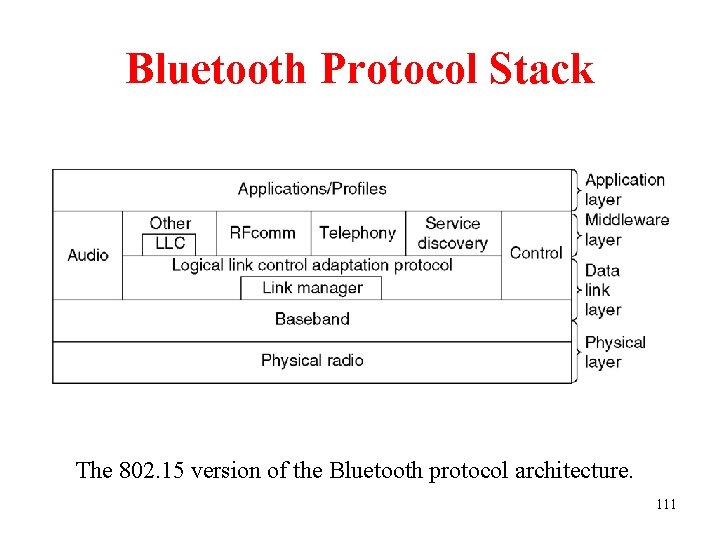
Bluetooth Protocol Stack The 802. 15 version of the Bluetooth protocol architecture. 111
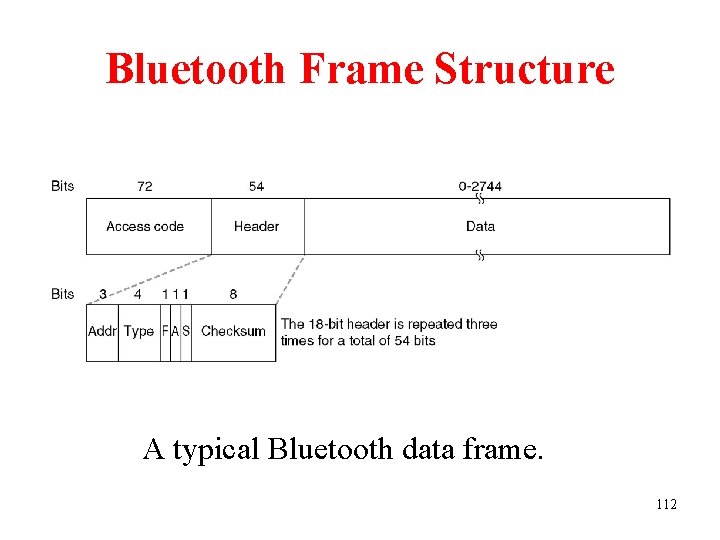
Bluetooth Frame Structure A typical Bluetooth data frame. 112
Data Link Layer Switching • • • Bridges from 802. x to 802. y Local Internetworking Spanning Tree Bridges Remote Bridges Repeaters, Hubs, Bridges, Switches, Routers, Gateways Virtual LANs 113
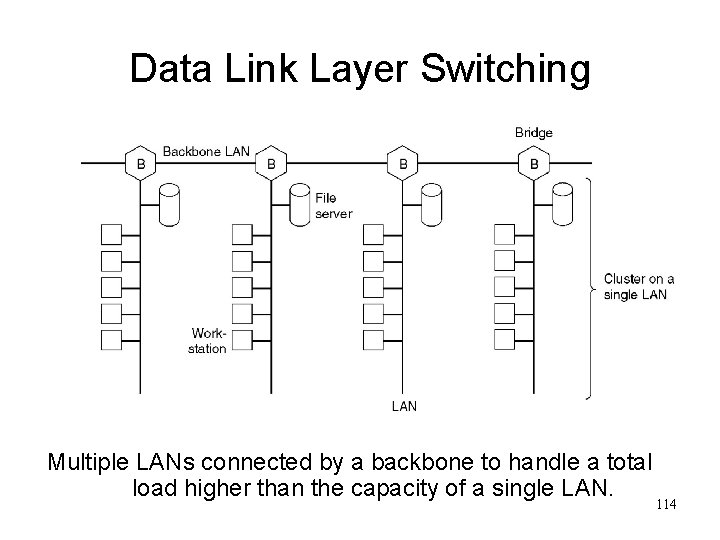
Data Link Layer Switching Multiple LANs connected by a backbone to handle a total load higher than the capacity of a single LAN. 114
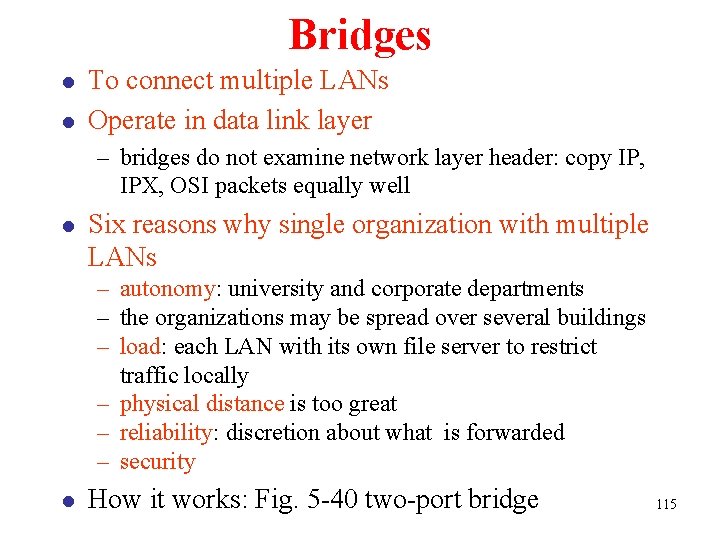
Bridges l l To connect multiple LANs Operate in data link layer – bridges do not examine network layer header: copy IP, IPX, OSI packets equally well l Six reasons why single organization with multiple LANs – autonomy: university and corporate departments – the organizations may be spread over several buildings – load: each LAN with its own file server to restrict traffic locally – physical distance is too great – reliability: discretion about what is forwarded – security l How it works: Fig. 5 -40 two-port bridge 115
Bridges from 802. x to 802. y Operation of a LAN bridge from 802. 11 to 802. 3. 116
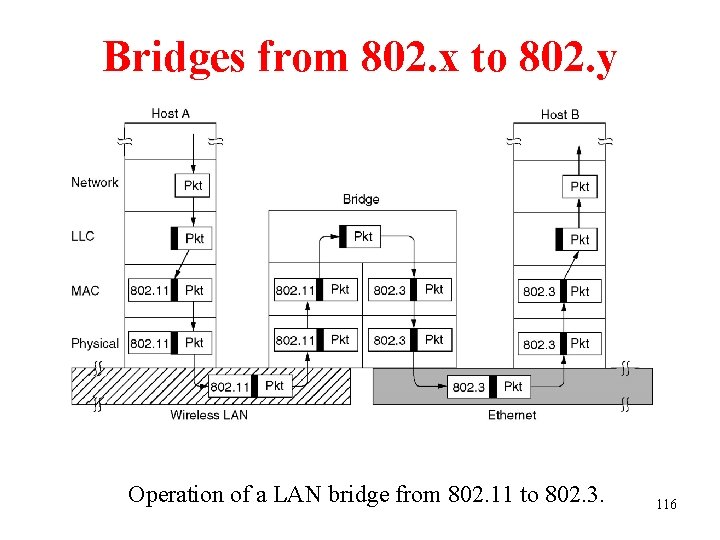
Bridges from 802. x to 802. y (2) The IEEE 802 frame formats. The drawing is not to scale. 117
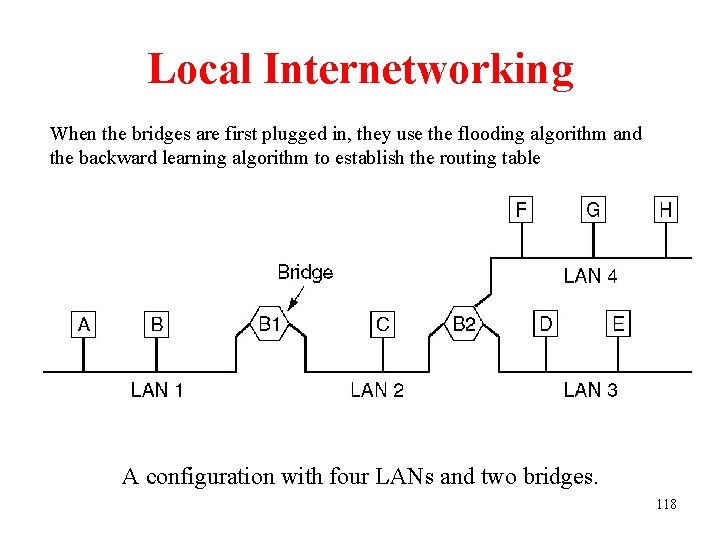
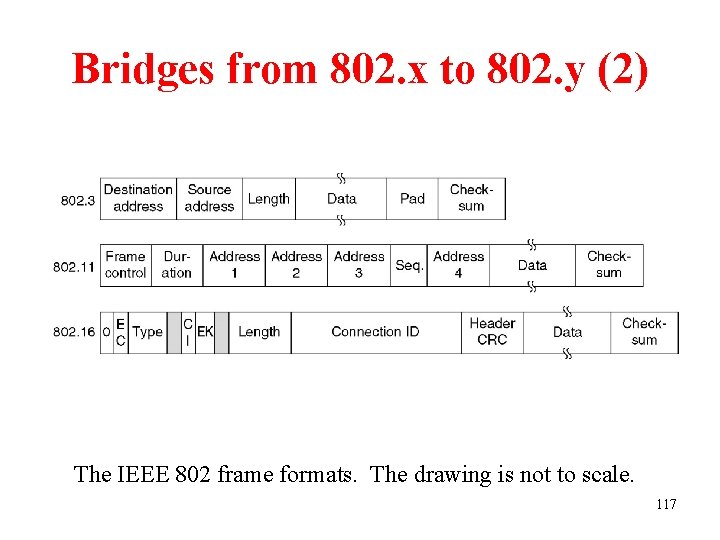
Local Internetworking When the bridges are first plugged in, they use the flooding algorithm and the backward learning algorithm to establish the routing table A configuration with four LANs and two bridges. 118

Routing Procedure of Bridges 1. If destination and source LANs are the same, discard the frame 2. If the destination and source LANs are different, forward the frame 3. If the destination LAN is unknown, use flooding 119
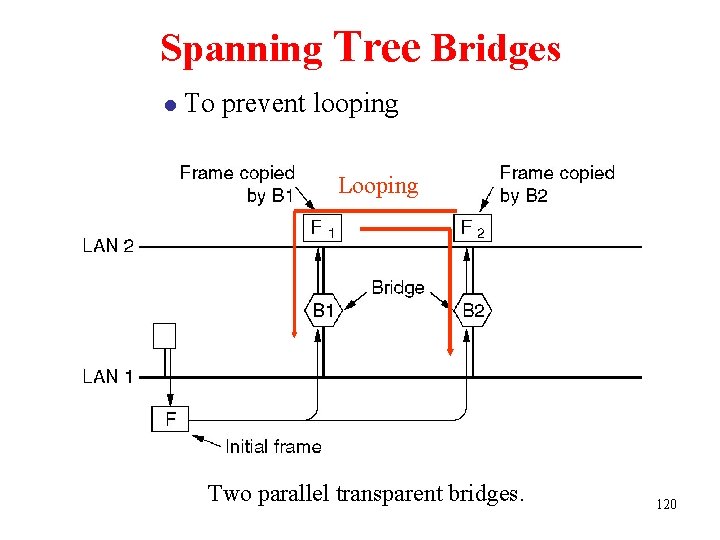
Spanning Tree Bridges l To prevent looping Looping Two parallel transparent bridges. 120

Spanning Tree Bridges l Spanning Tree – Abstraction (See Fig. 5 -44) – exactly one path from every LAN to every other LAN: no loops – root: the bridge with lowest serial number – a tree of shortest paths from root to every other bridge and LAN – can adapt to dynamic topology 121
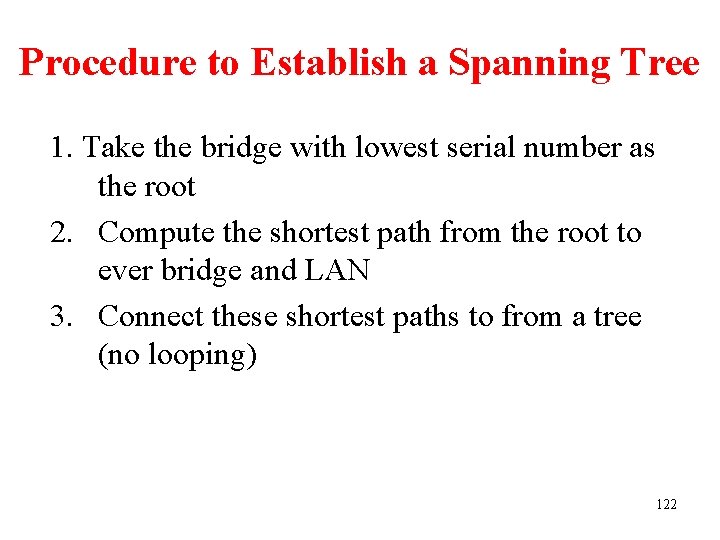
Procedure to Establish a Spanning Tree 1. Take the bridge with lowest serial number as the root 2. Compute the shortest path from the root to ever bridge and LAN 3. Connect these shortest paths to from a tree (no looping) 122
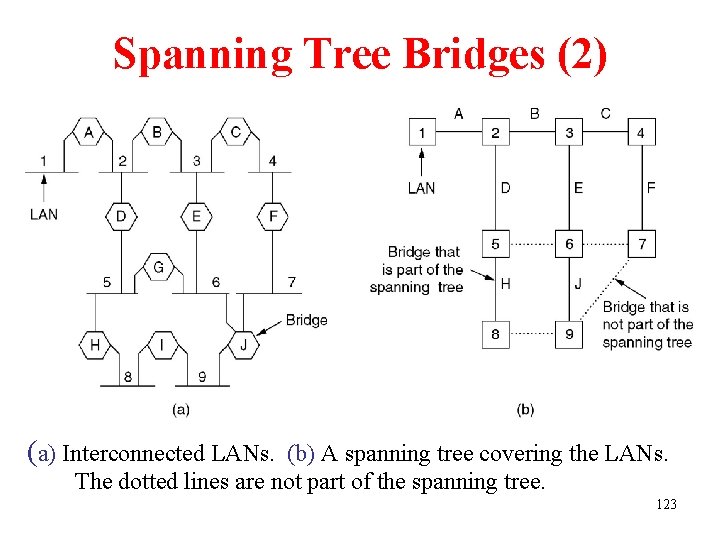
Spanning Tree Bridges (2) (a) Interconnected LANs. (b) A spanning tree covering the LANs. The dotted lines are not part of the spanning tree. 123

Remote Bridges l To connect two (or more) distance LANs Remote bridges can be used to interconnect distant LANs. 124
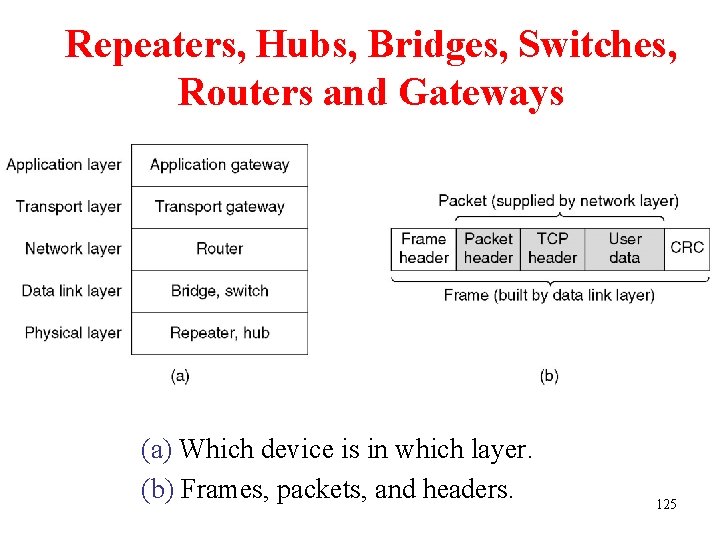
Repeaters, Hubs, Bridges, Switches, Routers and Gateways (a) Which device is in which layer. (b) Frames, packets, and headers. 125

Repeaters, Hubs, Bridges, Switches, Routers and Gateways (2) When two frames arrive simultaneously at a hub, they will collide l Bridges and switched will route the frames based on their destination addresses l l Bridges connect LANs (a) A hub. (b) A bridge. (c) a switch. 126
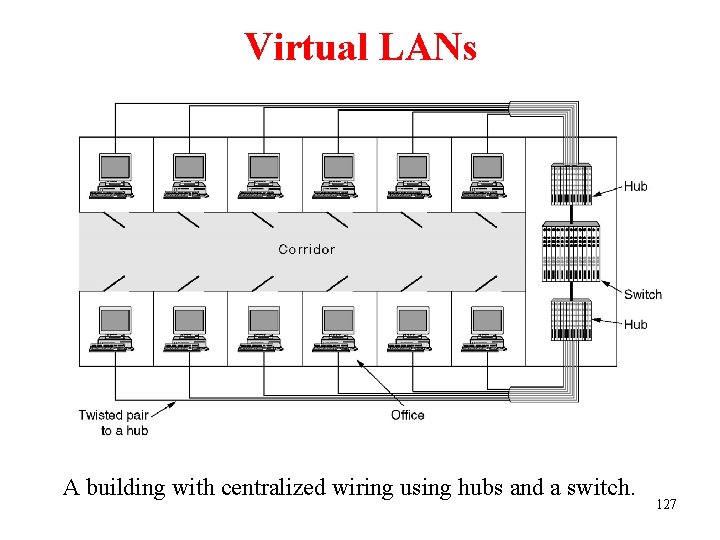
Virtual LANs A building with centralized wiring using hubs and a switch. 127
Reasons for Virtual LANs (a) Fitting into the organization structure (b) Loading partition (c) Relieving broadcast storm 128

Virtual LANs (2) VLANs are based on specially-designed VLAN-aware switches (bridges) (a) Four physical LANs organized into two VLANs, gray and white, by two bridges. (b) The same 15 machines organized into 129 two VLANs by switches.
Each VLAN is assigned a distinct color. Three methods are used to distinguish the color of an incoming frame 1. Every port is assigned a VLAN color (when a host moved, the port must be reassigned) 2. Every MAC address is assigned a VLAN color 3. Every layer 3 protocol or IP address is assigned a VLAN color (The payload must be examined by the data link layer, which violates the rule: independence of the layers. When the layer 3 protocol changed, the switch fails. ) 130
There are some issues for VLAN (a) (b) (c) (d) What is the VLAN field format? How to identify VLAN field? Who generates the VLAN field? What happens to frames that are already the maximum size? The 802. 1 Q will solve these problems 131
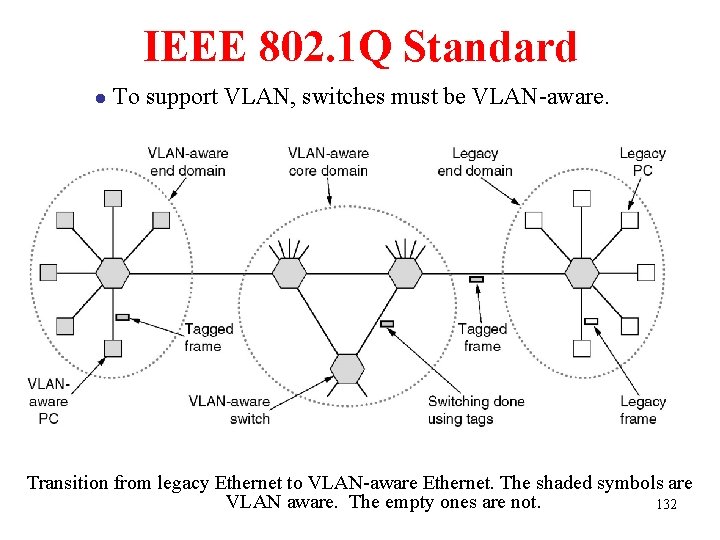
IEEE 802. 1 Q Standard l To support VLAN, switches must be VLAN-aware. Transition from legacy Ethernet to VLAN-aware Ethernet. The shaded symbols are VLAN aware. The empty ones are not. 132
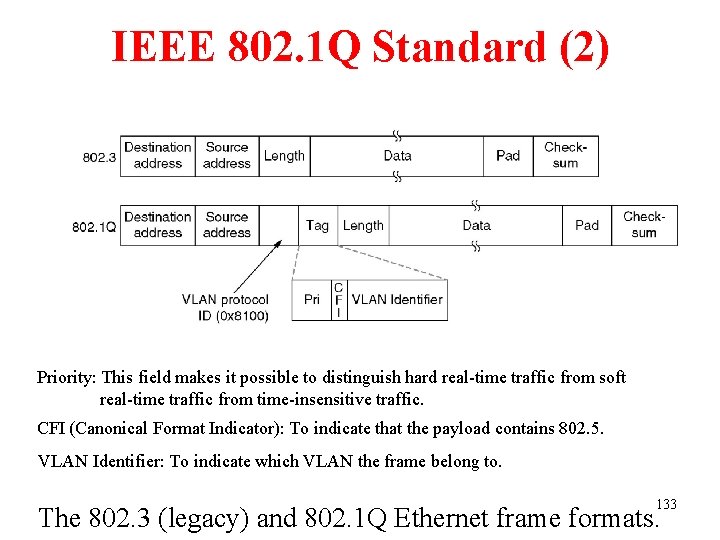
IEEE 802. 1 Q Standard (2) Priority: This field makes it possible to distinguish hard real-time traffic from soft real-time traffic from time-insensitive traffic. CFI (Canonical Format Indicator): To indicate that the payload contains 802. 5. VLAN Identifier: To indicate which VLAN the frame belong to. 133 The 802. 3 (legacy) and 802. 1 Q Ethernet frame formats.
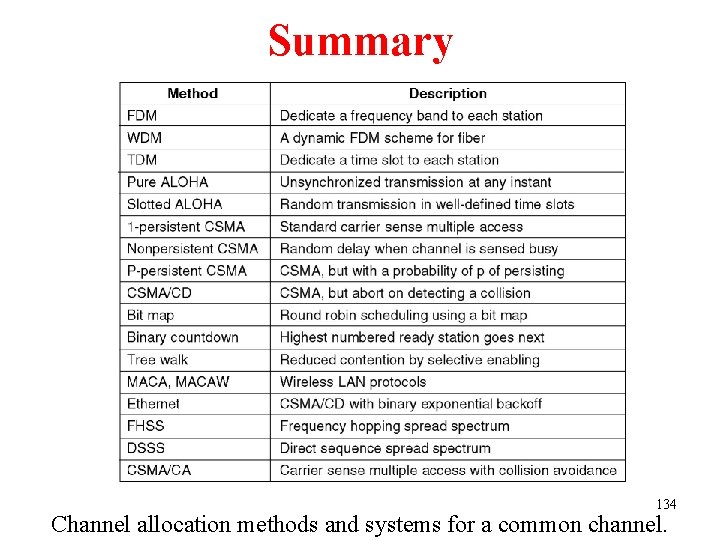
Summary 134 Channel allocation methods and systems for a common channel.
- Slides: 134