CHAPTER 4 Information Security Announcements n Friday Class

- Slides: 39
CHAPTER 4 Information Security
Announcements n Friday Class n Quiz 1 Review n Monday Class n Quiz 1 – Access Basics n Questions/Comments
Security is constantly evolving… https: //www. youtube. com/watch? v=Ie 0 b. Ry XNr. Ts
Personal Security How secure are you? Do you secure your information? How hackable is your digital life?
Key Information Security Terms Information Security n Vulnerability n Threat n Exposure/Attack © Sebastian/Age. Fotostock America, Inc.
Introduction to Information Security Is it possible to secure the Internet? © Sebastian/Age. Fotostock America, Inc.
Five Factors Increasing the Vulnerability of Information Resources 1. Today’s interconnected, interdependent, 2. 3. 4. 5. wirelessly-networked business environment Smaller, faster, cheaper computers and storage devices Decreasing skills necessary to be a hacker Organized crime taking over cybercrime Lack of management support
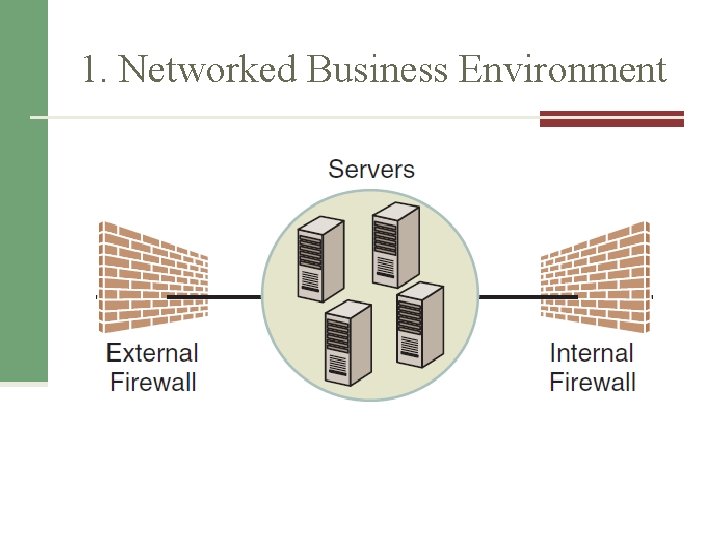
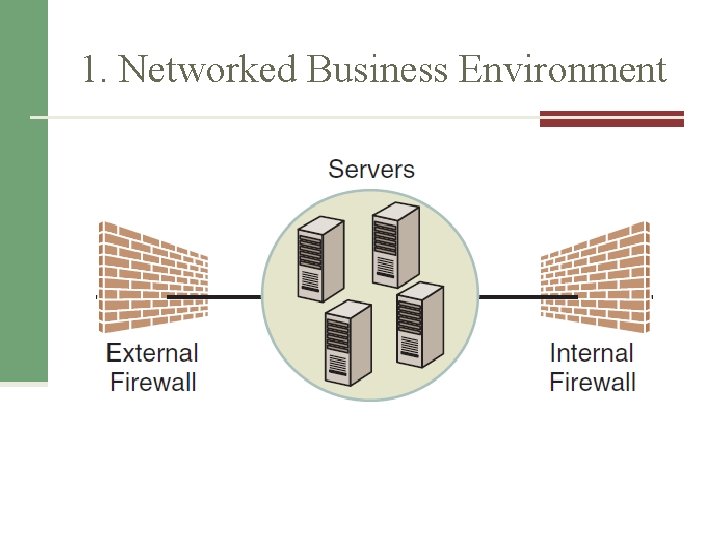
1. Networked Business Environment
2. Smaller, Faster Devices © laggerbomber-Fotolia. com © Dragonian/i. Stockphoto © Photo. Edit/Alamy Limited
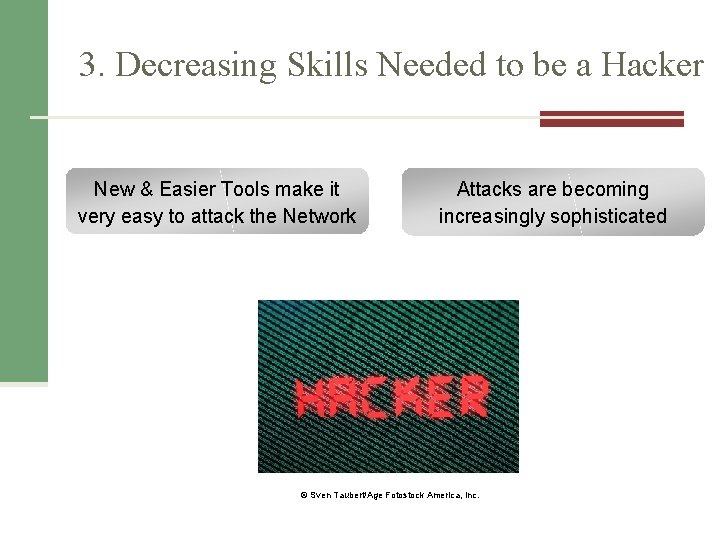
3. Decreasing Skills Needed to be a Hacker New & Easier Tools make it very easy to attack the Network Attacks are becoming increasingly sophisticated © Sven Taubert/Age Fotostock America, Inc.
4. Organized Crime Taking Over Cybercrime Cost of Cybercrime Any Guesses? © Stockbroker xtra/Age. Fotostock America, Inc. http: //www. zdnet. com/norton-cybercrime-cost-110 -billion-last-year-7000003745/? s_cid=e 539
5. Lack of Management Support © Sigrid Olsson/Photo Alto/Age Fotostock
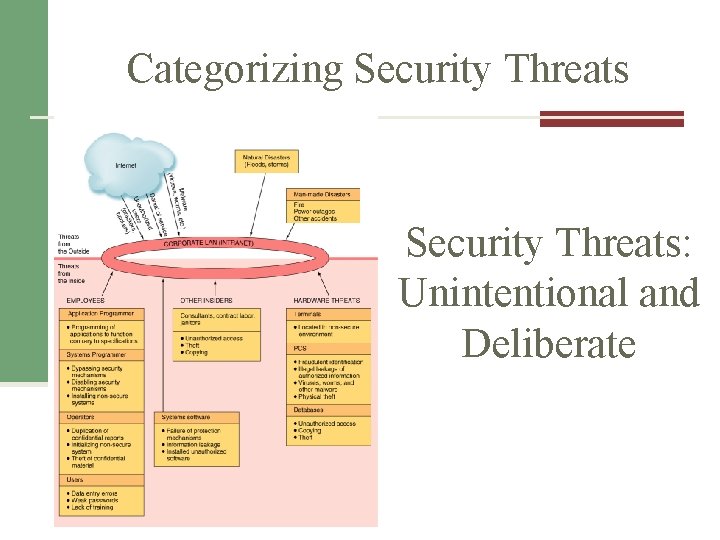
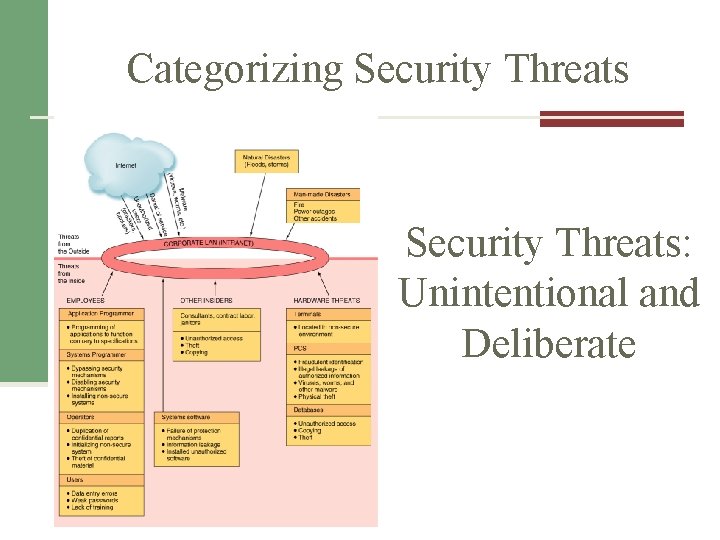
Categorizing Security Threats: Unintentional and Deliberate
Unintentional Threats: Most Dangerous Employees Who are the most dangerous employees? Why are these the most dangerous? © WAVEBREAKMEDIA LTD/Age Fotostock America, Inc.
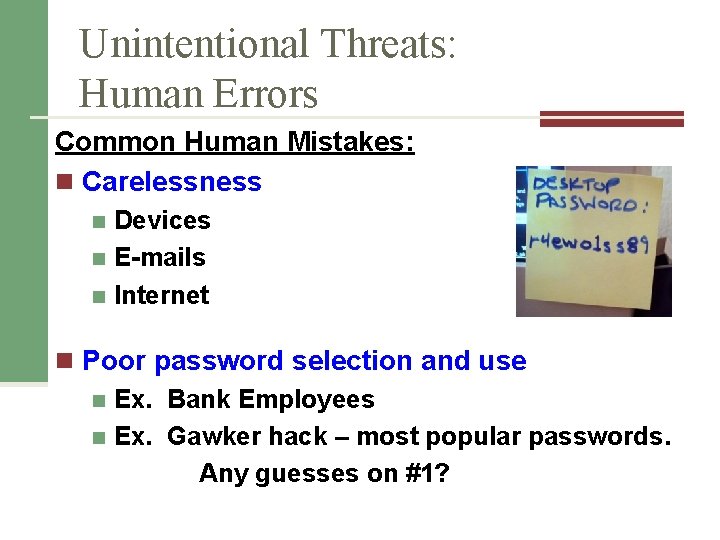
Unintentional Threats: Human Errors Common Human Mistakes: n Carelessness Devices n E-mails n Internet n n Poor password selection and use n Ex. Bank Employees n Ex. Gawker hack – most popular passwords. Any guesses on #1?
Unintentional Threats: Social Engineering the art of manipulating people into performing actions or divulging confidential information. Pretexting Phishing Baiting Vishing (IVR or phone phishing)
Deliberate Threats to Information Security Theft of equipment or information n Examples n n Dumpster diving Laptop stolen from breaking in
Deliberate Threats (continued) Identify theft n Stealing info off org databases n Phishing Frederic Lucano/Stone/Getty Images, Inc. Compromises to intellectual property
Deliberate Threats (continued) Software attacks n Virus n Worm (see the rapid spread of the Slammer worm) n Trojan horse n Logic Bomb n Phishing attacks n Distributed denial-of-service attacks n Ex. US Banks
Deliberate Threats (continued) Alien Software Spyware Spamware Cookies © Manfred Grafweg/Age Fotostock America, Inc. Targeted Attack Supervisory control and data acquisition (SCADA) attacks Stuxnet n
What Organizations Are Doing to Protect Themselves “The only truly secure system is powered off, cast in a block of concrete, and sealed in a lead room with armed guards, and even then I have my doubts”
What Organizations Are Doing to Protect Themselves How do you protect your own networks?
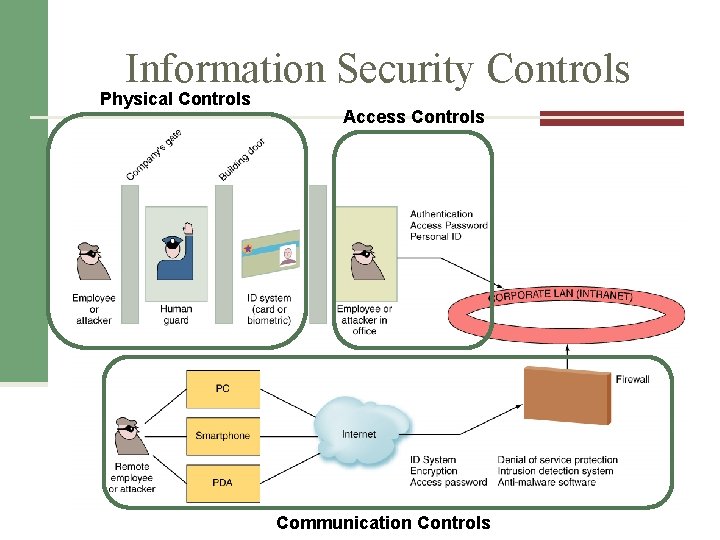
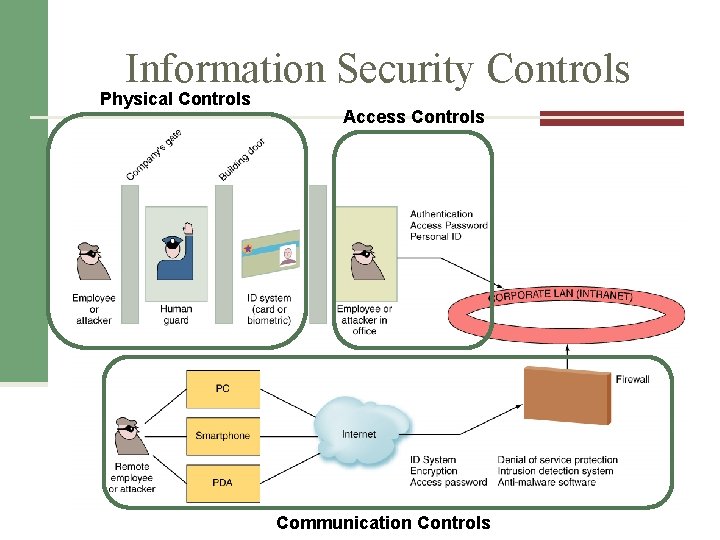
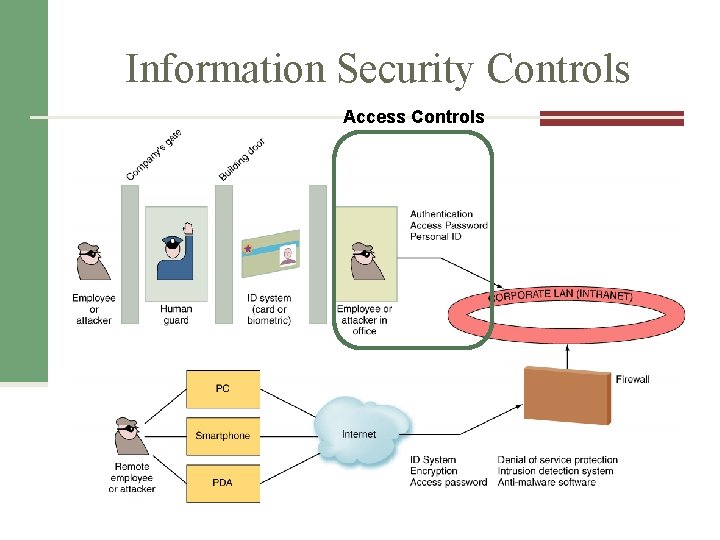
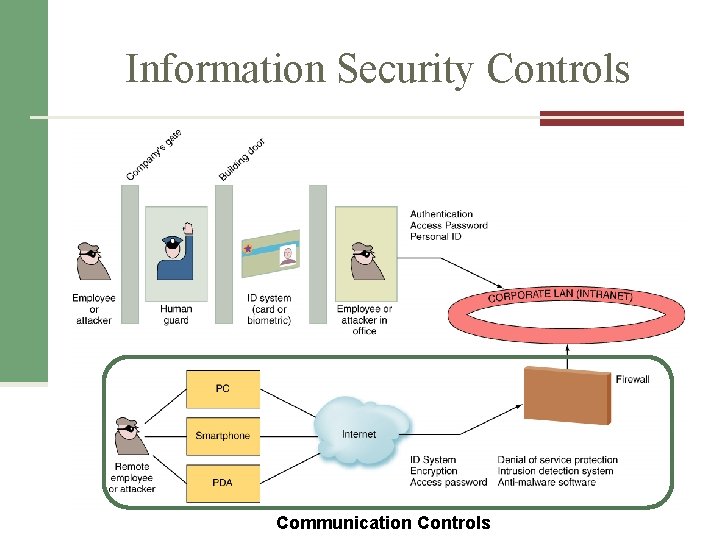
Information Security Controls Physical Controls Access Controls 1. Physical controls 2. Access controls 3. Communications (network) controls Communication Controls
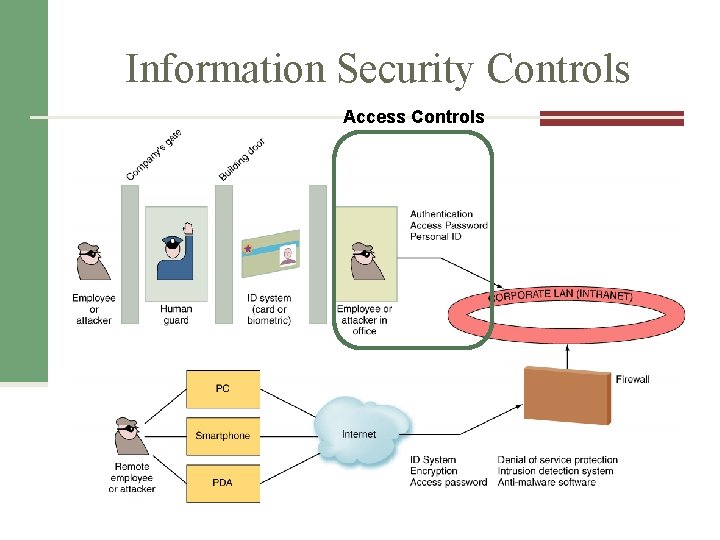
Information Security Controls Access Controls 1. Physical controls 2. Access controls 3. Communications (network) controls
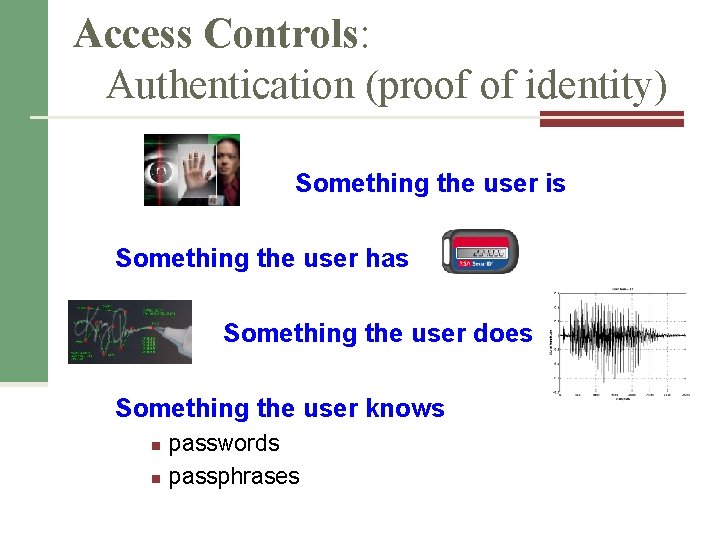
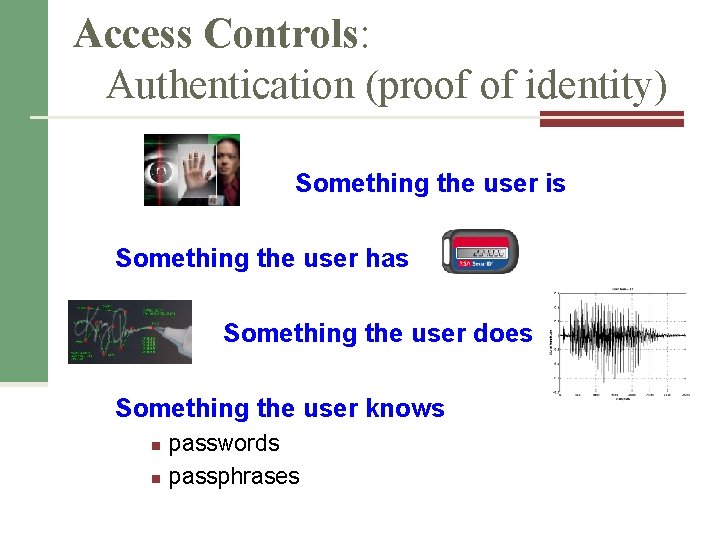
Access Controls: Authentication (proof of identity) Something the user is Something the user has Something the user does Something the user knows n n passwords passphrases
Access Controls: Authorization Permissions issued based on verified identity Privilege – operations that users can perform Least privilege – idea of granting privlege only if there is a justifiable need
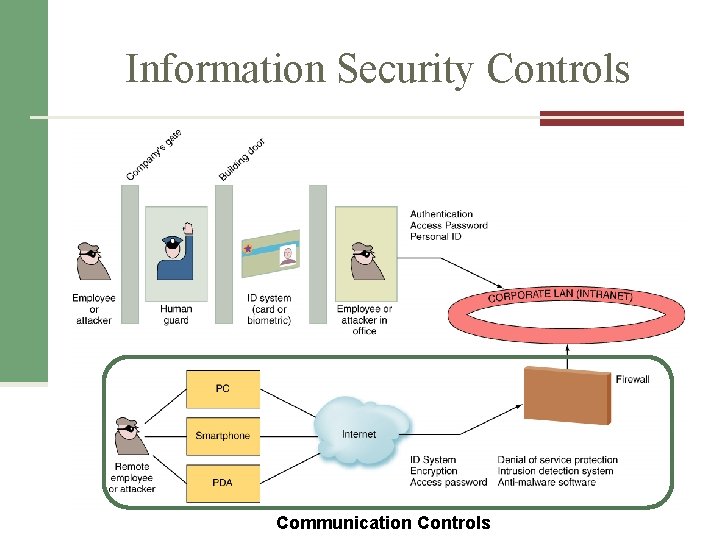
Information Security Controls 1. Physical controls 2. Access controls 3. Communications (network) controls Communication Controls

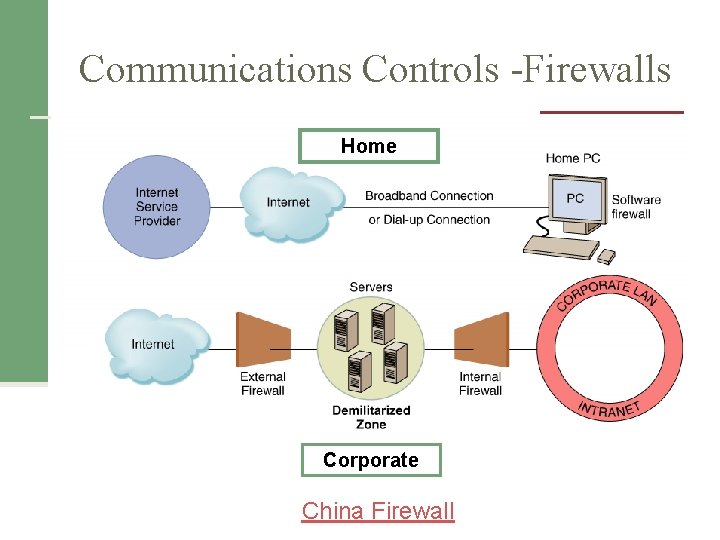
Communications Controls n Firewalls n Anti-malware systems n Whitelisting and Blacklisting n Encryption n VPN
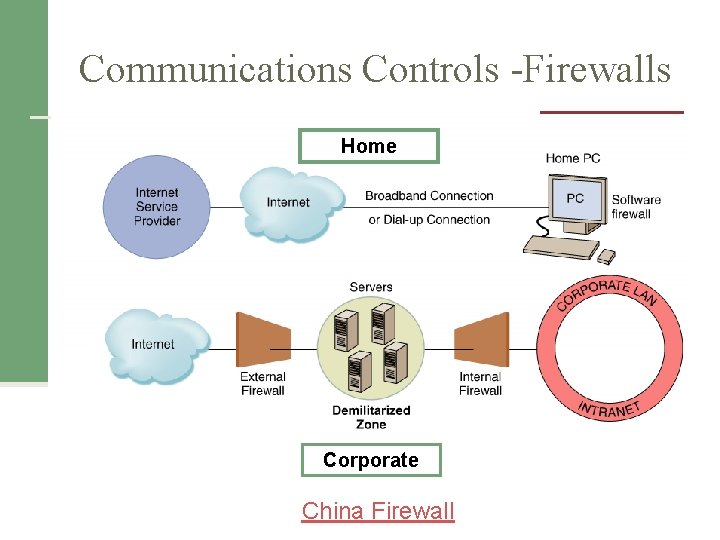
Communications Controls -Firewalls Home Corporate China Firewall
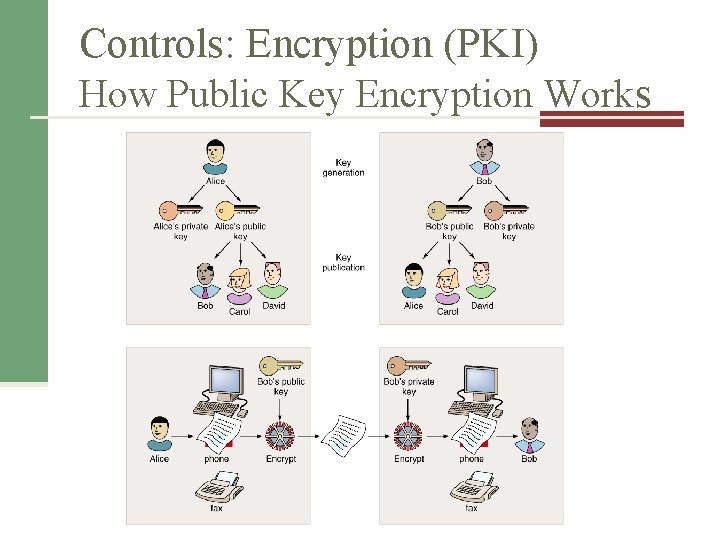
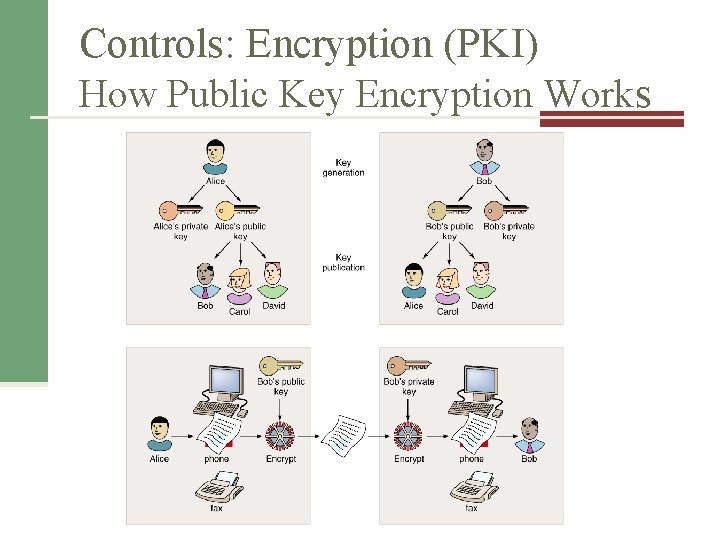
Controls: Encryption (PKI) How Public Key Encryption Works
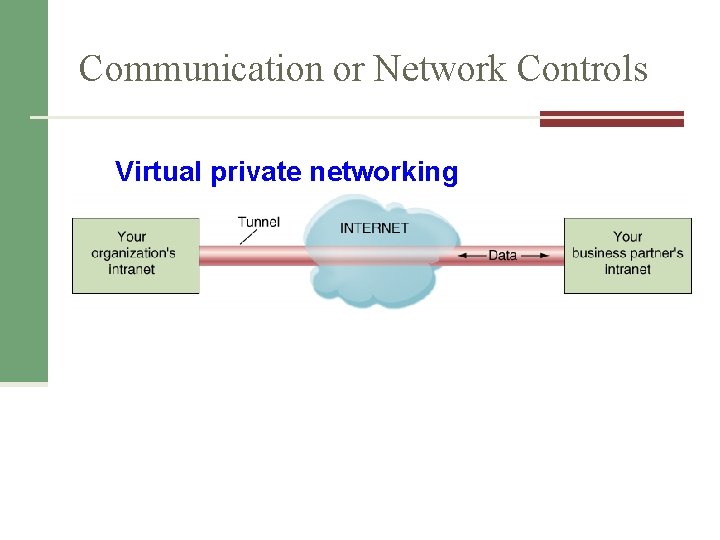
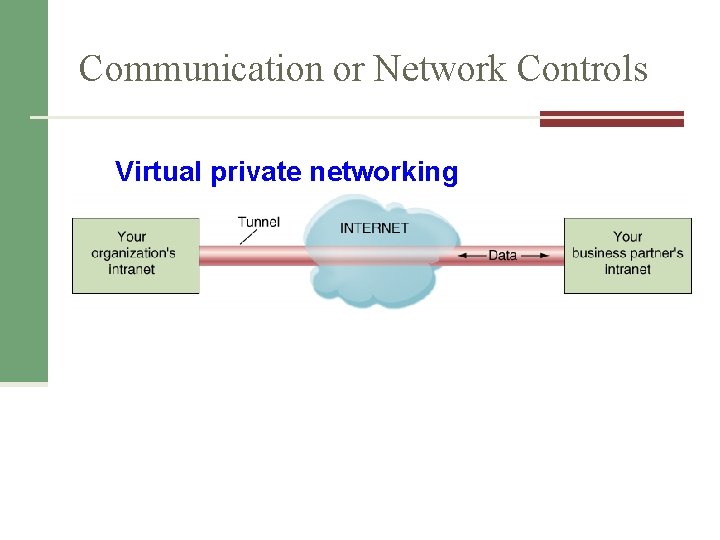
Communication or Network Controls Virtual private networking
Protection of data Government Regulations HIPPA n Sarbanes-Oxley n PA 74 n
Need to understand Risk Management (identify, control, minimize) 1. Risk analysis 2. Risk mitigation (take action) 1. Acceptance 2. Limitation (most common) 3. Transference © Youri van der Schalk/Age Fotostock America, Inc. 3. Controls Evaluation control > cost of asset then the control is not cost effective
Business Continuity Planning, Backup, and Recovery Provide guidance to people who keep business operating after a disaster occurs. Options: n Hot Site n Warm Site n Cold Site
Personal Risk Assessment To understand your own risk, get with another person and create an assessment. List out the following: 1. Assets (e. g. laptop, external drive, etc. ) 2. Threats (e. g. natural, virus, etc. ) 3. Controls (how do you control threats) Other ways to minimize personal risk
LEARNING OBJECTIVES 1. Identify the five factors that contribute to the increasing vulnerability of information resources, and provide a specific example of each one.
LEARNING OBJECTIVES 2. Compare and contrast human mistakes and social engineering, and provide a specific example of each one.
LEARNING OBJECTIVES (continued) 3. Define three risk mitigation strategies, and provide an example of each one in the context of you owning a home.
LEARNING OBJECTIVES (continued) 4. Identify the three major types of controls that organizations can use to protect their information resources, and provide an example of each one.