CHAPTER 3 Ethics and Privacy Outline for Today
- Slides: 33
CHAPTER 3 Ethics and Privacy
Outline for Today • Chapter 3: Ethics and Privacy • Tech Guide: Protecting Information Assets
Chapter Opening Case
Questions about Wikileaks Was it legal for Wikileaks to post this information? Who is acting unethical? • Wikileaks • US Government • Both
Chapter 3 - Ethics How do you define ethics? 5
3. 1 Ethical Issues - Standards Ethics refers to the principles of right and wrong that individuals use to make choices that guide their behavior Guidelines/Approaches
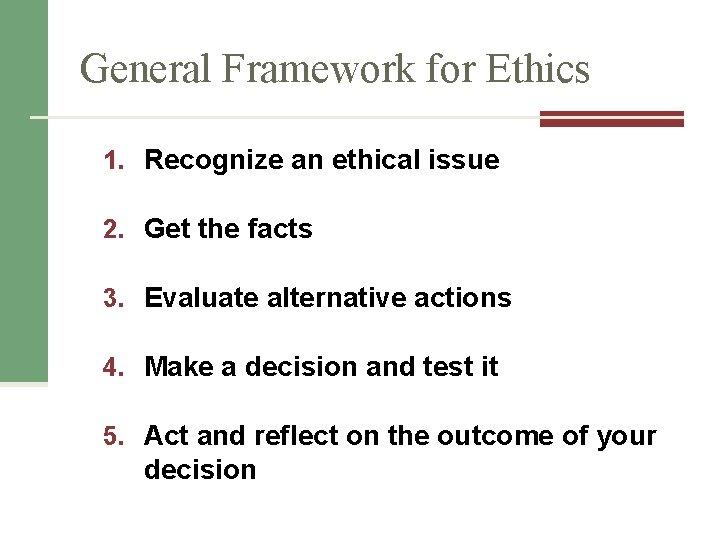
General Framework for Ethics 1. Recognize an ethical issue 2. Get the facts 3. Evaluate alternative actions 4. Make a decision and test it 5. Act and reflect on the outcome of your decision
Ethics in the Corporate Environment Code of ethics / conduct n n Microsoft Google Fundamental tenets of ethics 1. 2. 3. Responsibility Accountability Liability
Unethical vs. Illegal Is everything that is unethical also illegal? n n Enron World Com Subprime Mortgages Other Examples
Ethics and Information Technology Ethical use of information and information technology Should organizations: • monitor employees? • sell customer info? • audit employee computers? (unauthorized software or content) Employers can and will monitor employees at work!
Ethics and Information Technology Do emails last forever? This can also applies to messaging at companies.
Advice for Organization Use 1. Only use company computer for business related work 2. Don’t send emails you wouldn’t want your parents to see 3. Limit who you give work email to
Ethics and Information Technology Four categories of ethical issues involving IT applications: • Privacy Issues • Accuracy Issues • Property Issues • Accessibility Issues
How much privacy do we have left? 1) We Still Have a high level of privacy 2) We are beginning to have less privacy 3) Privacy? What’s that?
Privacy Court decisions have followed two rules: (1) The right of privacy is not absolute. Your privacy must be balanced against the needs of society. (2) The public’s right to know is superior to the individual’s right of privacy.
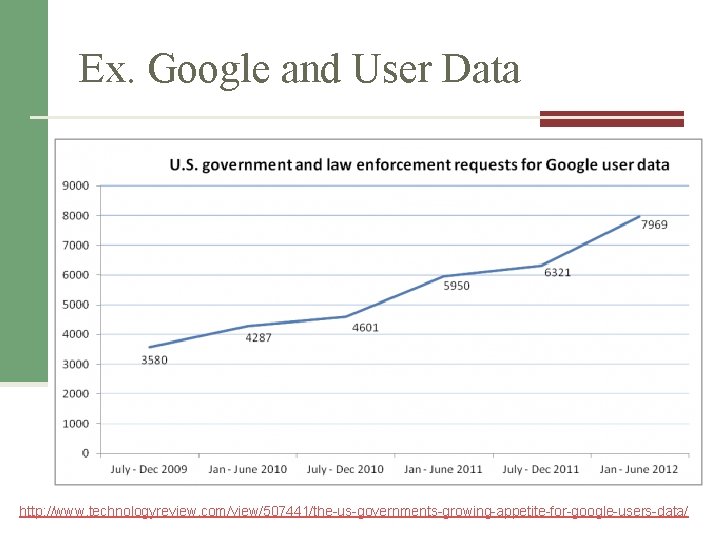
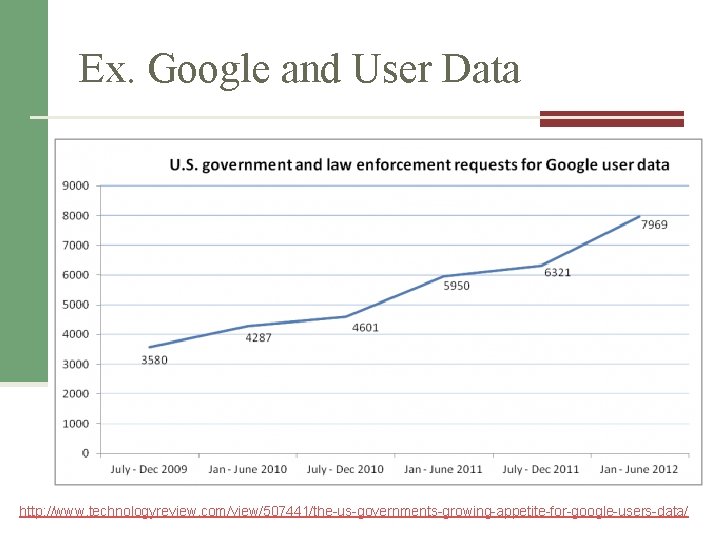
Ex. Google and User Data http: //www. technologyreview. com/view/507441/the-us-governments-growing-appetite-for-google-users-data/
Ex. Mobile Device Location
Threats to Privacy n Data aggregators, digital dossiers, and profiling n Electronic Surveillance n Personal Information in Databases n Information on Internet Bulletin Boards, Newsgroups, and Social Networking Sites
Data Aggregators, Digital Dossiers, and Profiling © Ilin Sergey/Age Fotostock America, Inc.
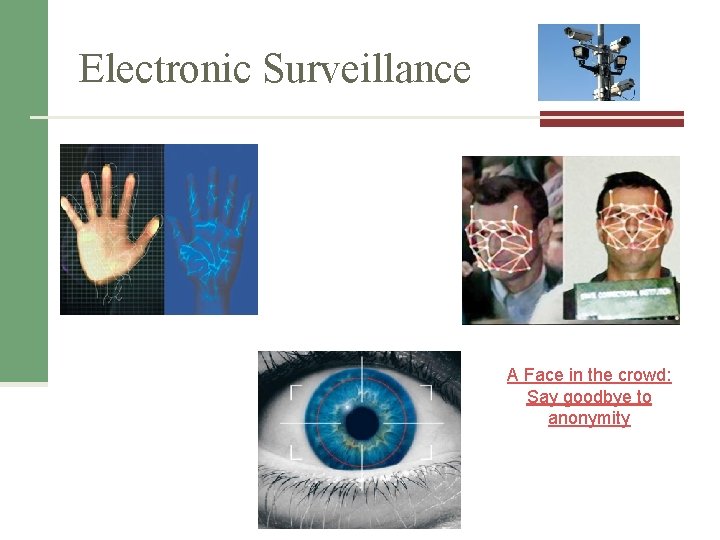
Electronic Surveillance What are employee rights against surveillance? © Ilin Sergey/Age Fotostock America, Inc.
Electronic Surveillance A Face in the crowd: Say goodbye to anonymity
Personal Information in Databases Banks Utility companies Government agencies Credit reporting agencies © Nicolas Nadjar/Age Fotostock America, Inc.
Information on Internet Bulletin Boards, Newsgroups, and Social Networking Sites © Marina Bordjieva/Age Fotostock America, Inc.
Social Networking Sites Can Cause You Problems Anyone can post derogatory information about you anonymously. (See this Washington Post article. ) You can also hurt yourself, as this article shows.
What Can You Do? First, be careful what information you post on social networking sites. Second, a company, Reputation. Defender, says it can remove derogatory information from the Web.
Protecting Privacy Codes and Policies n Ex. Facebook, Apple Opt-out Model Opt-in Model © Gunnar/Age Fotostock America, Inc.
Tech Guide 5 Protecting Your Information Assets
Information Assets What is meant when we say information assets?
Behavioral Actions n Protect SSN# n Secure credit cards n Physical n Virtual n Debit Cards vs. Credit Cards n Proactive Protection
Identity Theft n Dumpster Diving n Skimming n Phishing n Changing your address n Old-Fashioned Stealing n Pretexting Federal Trade Commission http: //www. ftc. gov/bcp/edu/microsites/idtheft 2012/
Computer-Based Actions n Know what sites have been visited n Infected Computers n Malware Infections n Anti-Virus (http: //www. uncw. edu/ITSD/help/antivirus. html) n Security suite (Zone. Alarm) n Antispyware (Ad-Aware)
Computer-Based Actions n Information in SNS n Manage Patches n Browser and Operating Systems
Portable Devices and Information n Data Encryption n Password Protect n Locating Devices n Prey Project n Find my i. Phone n Where’s My Droid http: //thisguyhasmymacbook. tumblr. com/