Chapter 3 Authentication Authorization and Accounting CCNA Security

- Slides: 54
Chapter 3: Authentication, Authorization, and Accounting CCNA Security v 2. 0
3. 0 Introduction 3. 1 Purpose of the AAA 3. 2 Local AAA Authentication 3. 3 Server-Based AAA 3. 4 Server-Based AAA Authentication 3. 5 Server-Based Authorization and Accounting 3. 6 Summary © 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 2
Upon completion of this section, you should be able to: • Explain why AAA is critical to network security. • Describe the characteristics of AAA. © 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 3
© 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 4
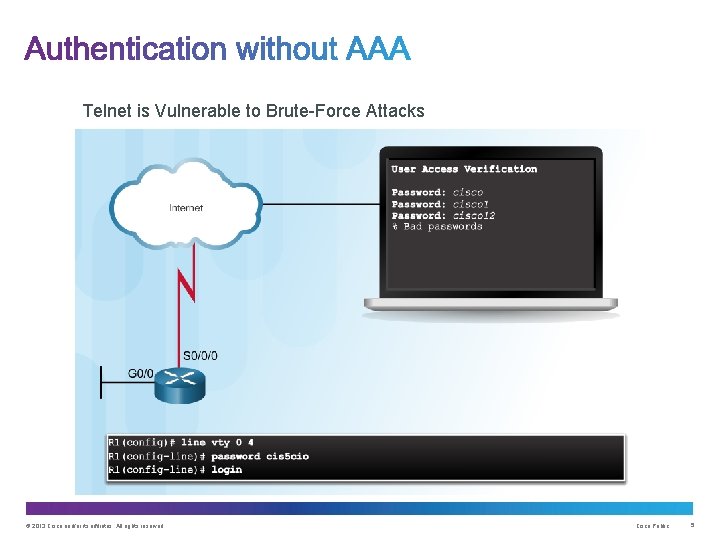
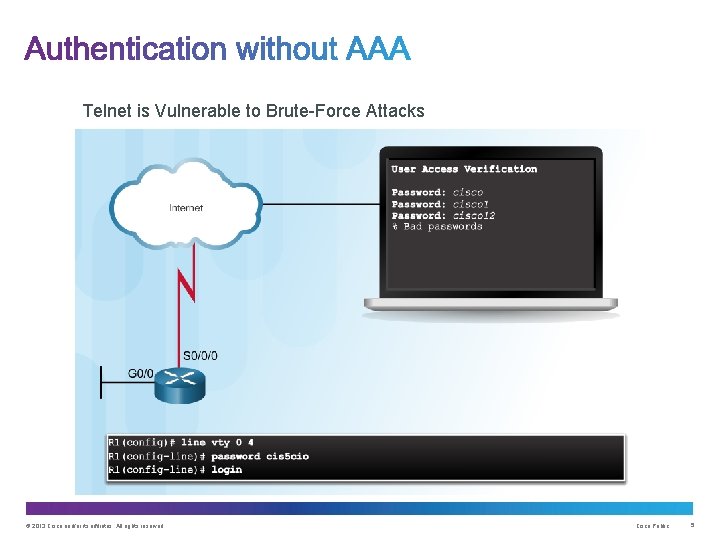
Telnet is Vulnerable to Brute-Force Attacks © 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 5
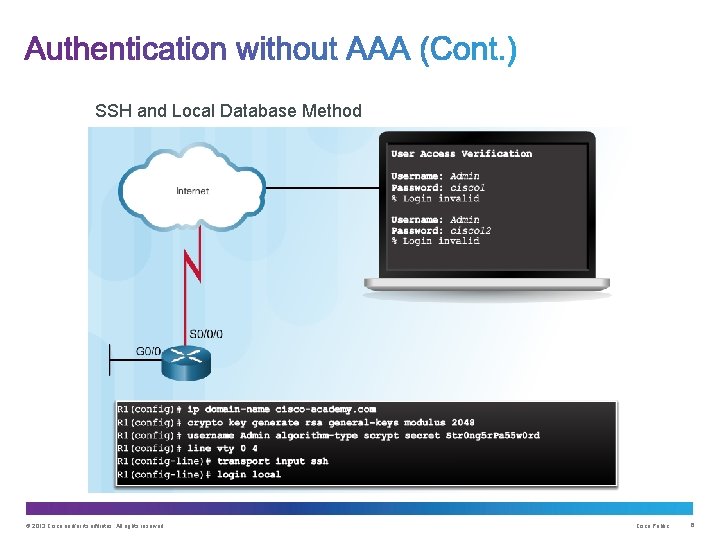
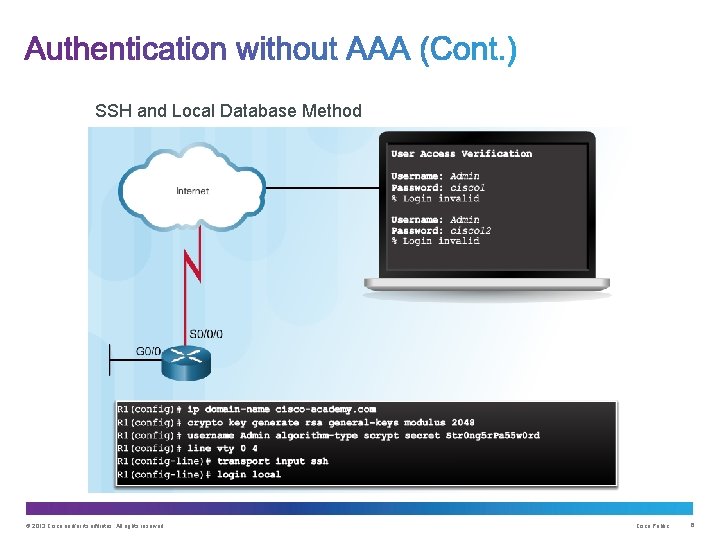
SSH and Local Database Method © 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 6
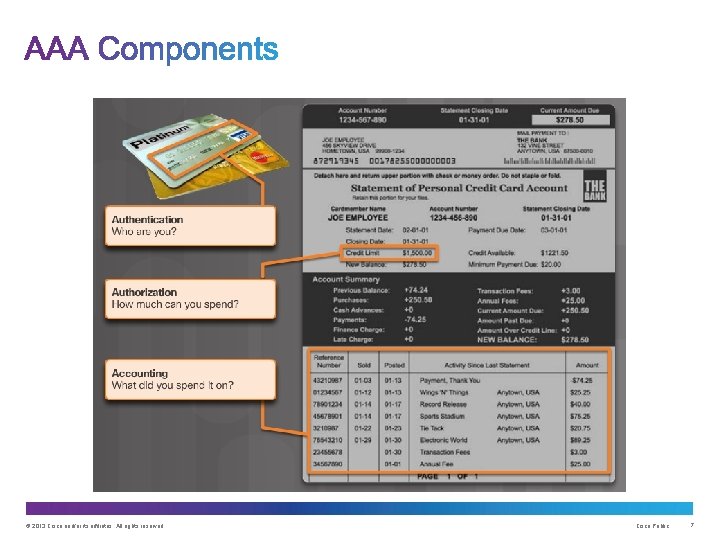
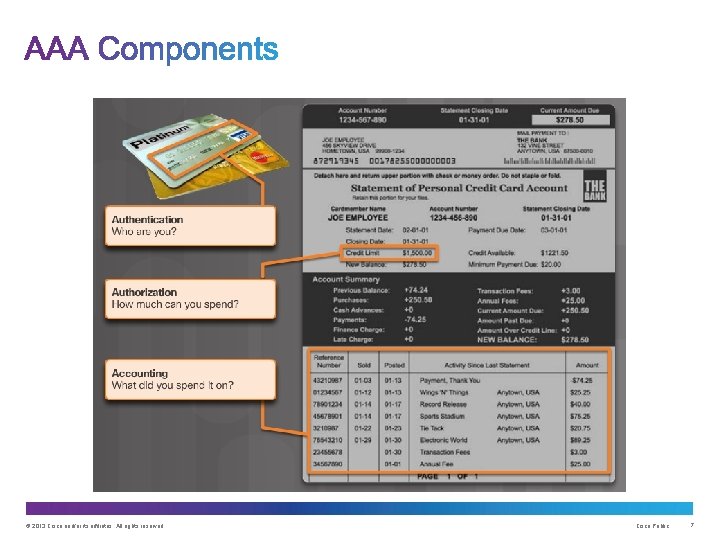
© 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 7
© 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 8
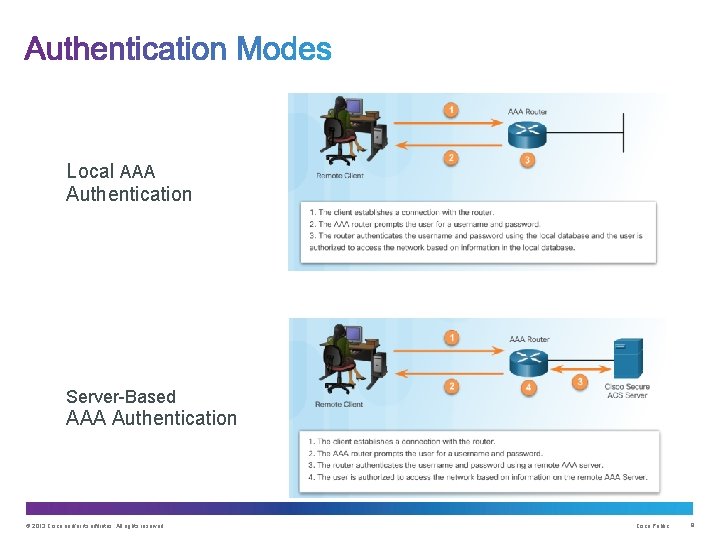
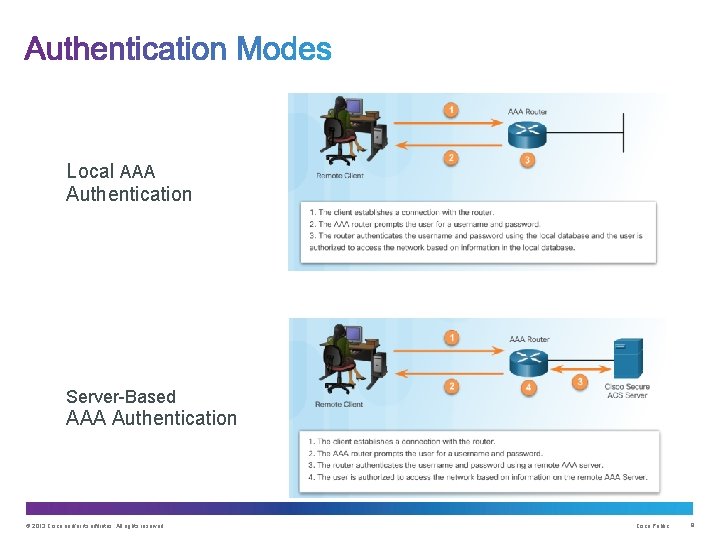
Local AAA Authentication Server-Based AAA Authentication © 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 9
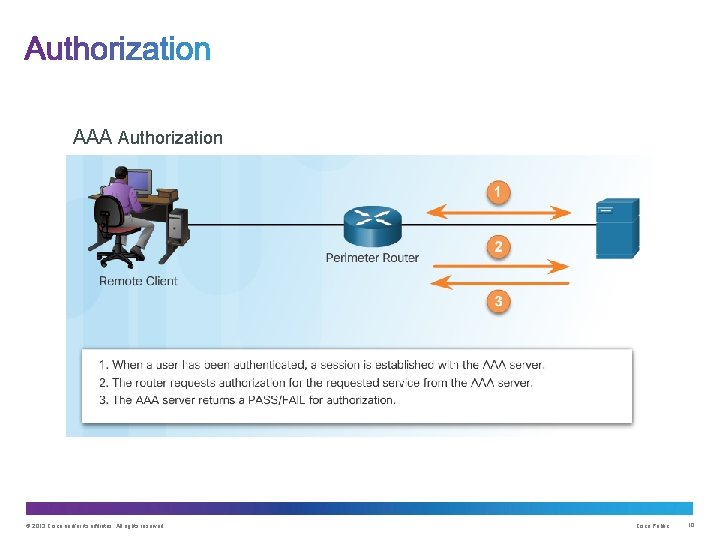
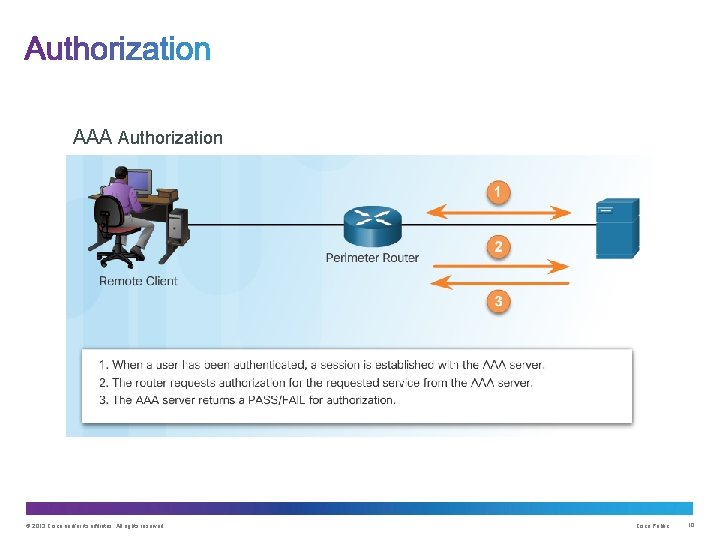
AAA Authorization © 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 10
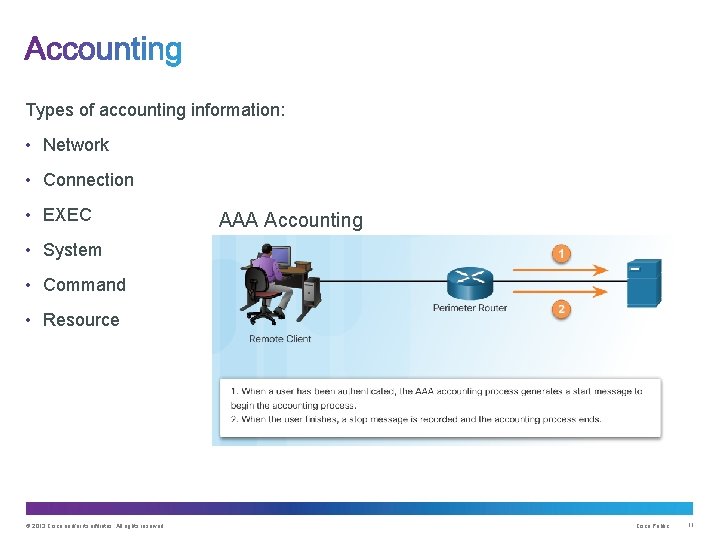
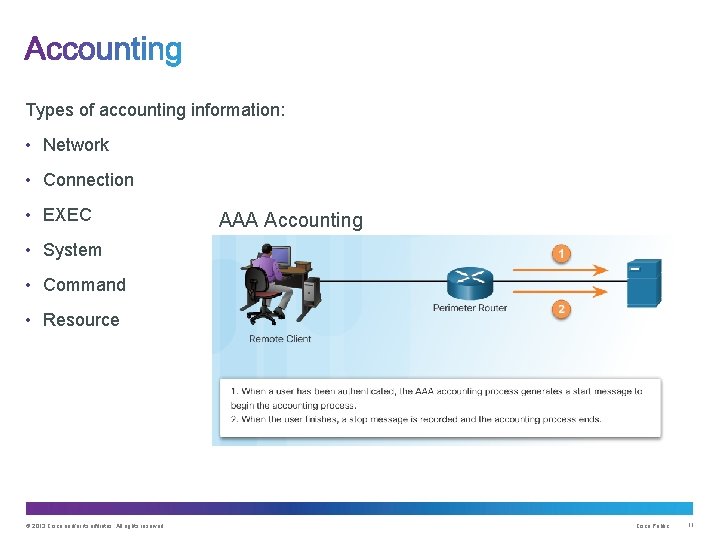
Types of accounting information: • Network • Connection • EXEC AAA Accounting • System • Command • Resource © 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 11
Upon completion of this section, you should be able to: • Configure AAA authentication, using the CLI, to validate users against a local database. • Troubleshoot AAA authentication that validates users against a local database. © 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 12
© 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 13
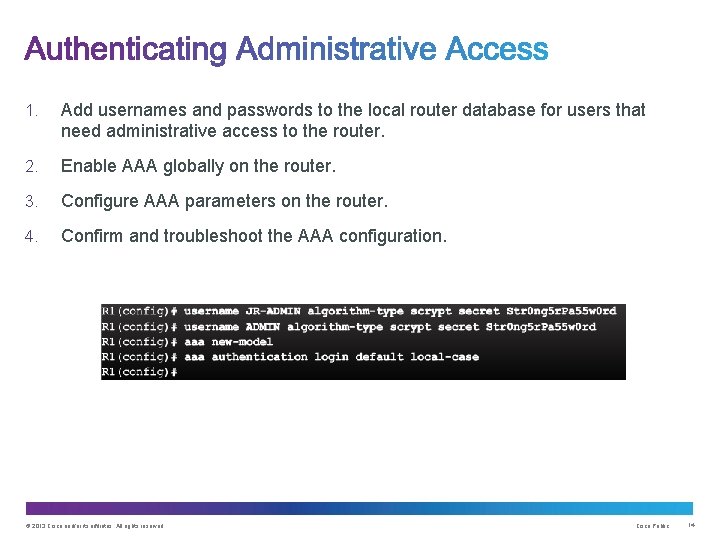
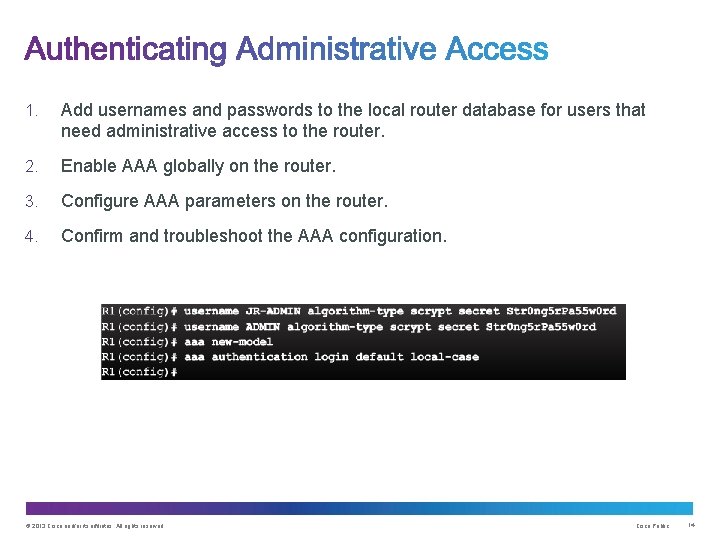
1. Add usernames and passwords to the local router database for users that need administrative access to the router. 2. Enable AAA globally on the router. 3. Configure AAA parameters on the router. 4. Confirm and troubleshoot the AAA configuration. © 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 14
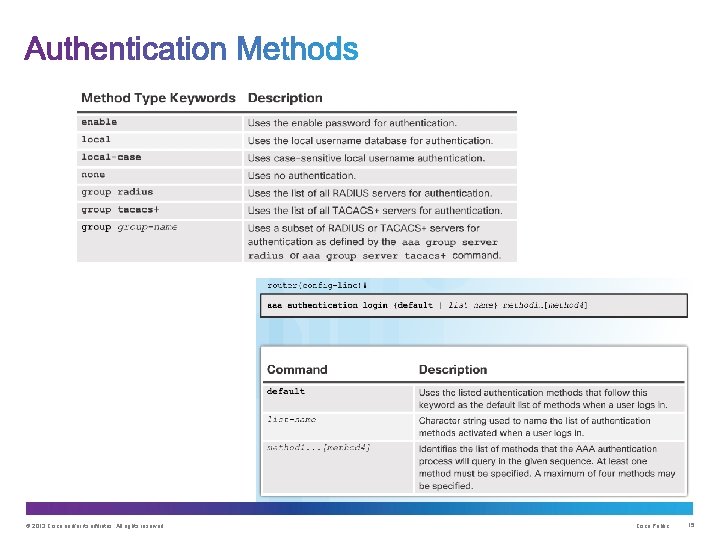
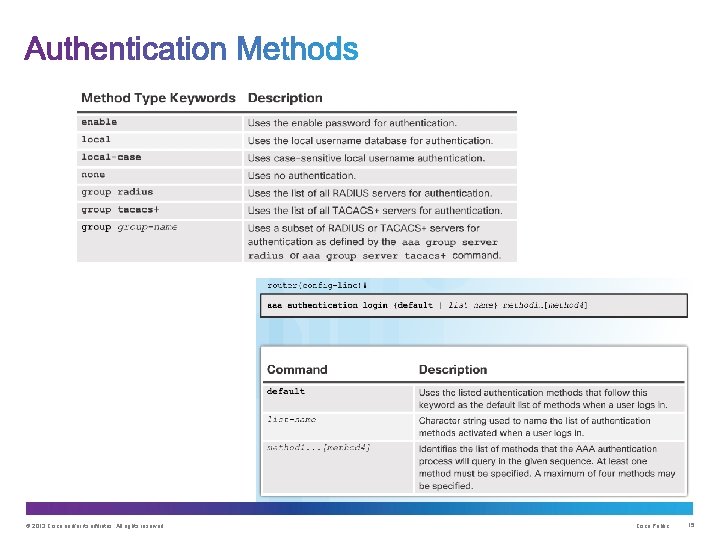
© 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 15
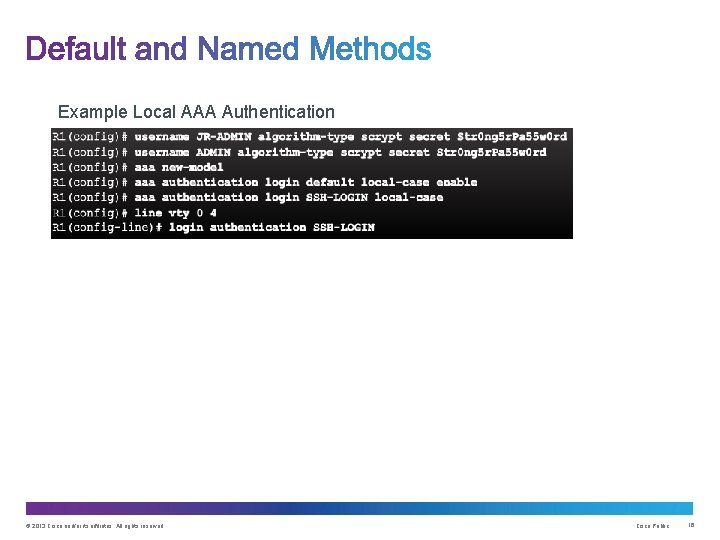
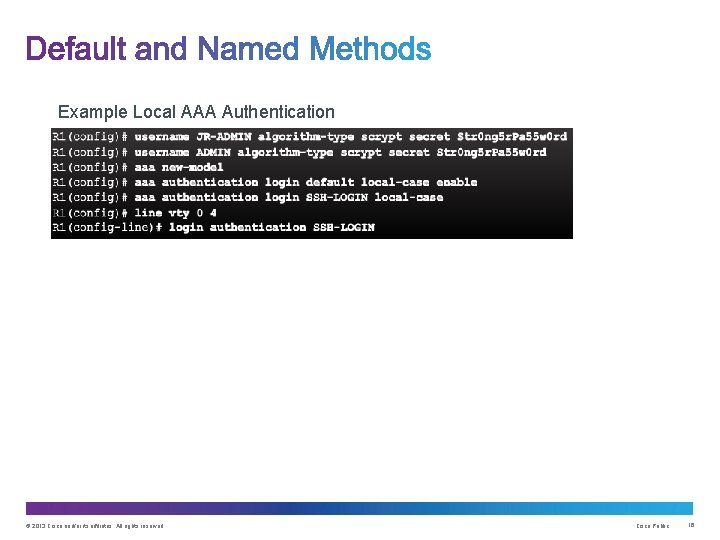
Example Local AAA Authentication © 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 16
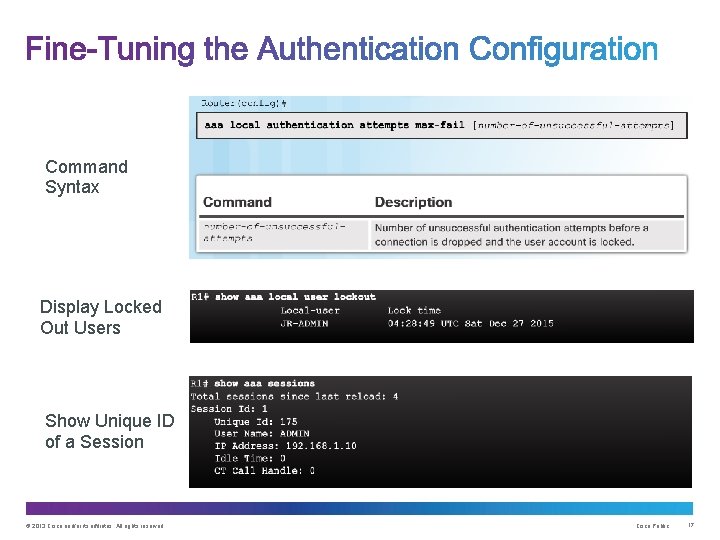
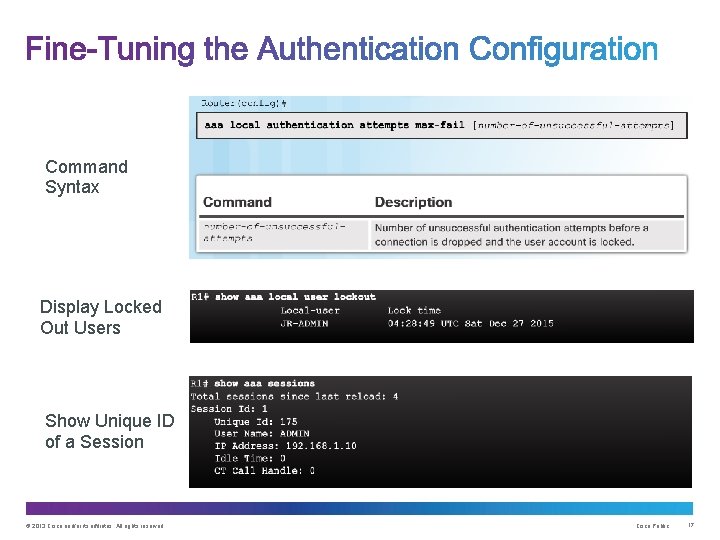
Command Syntax Display Locked Out Users Show Unique ID of a Session © 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 17
© 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 18
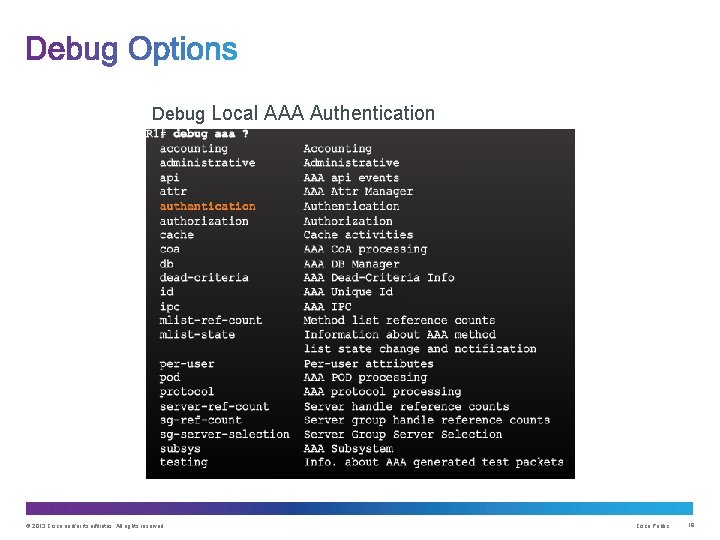
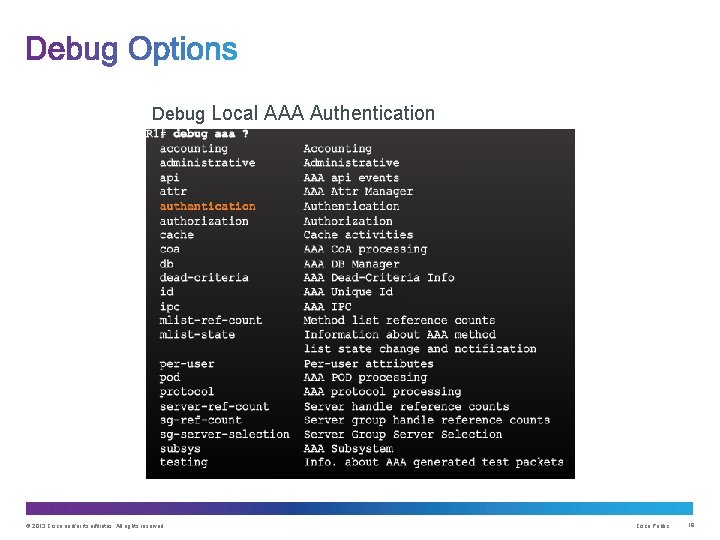
Debug Local AAA Authentication © 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 19
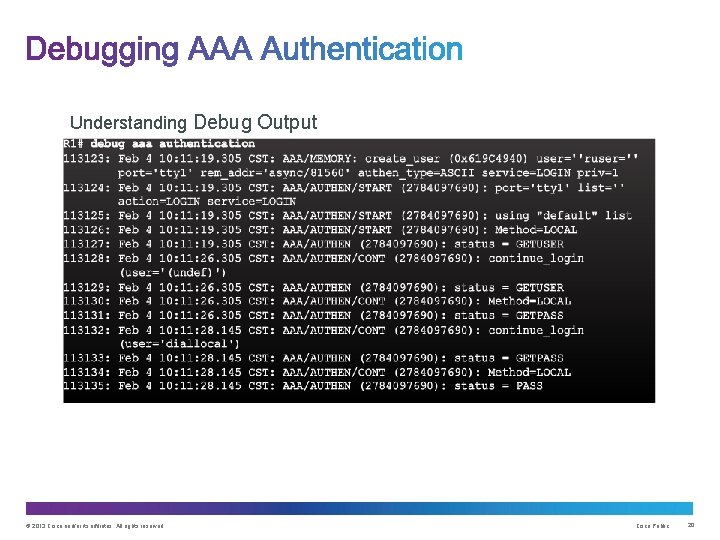
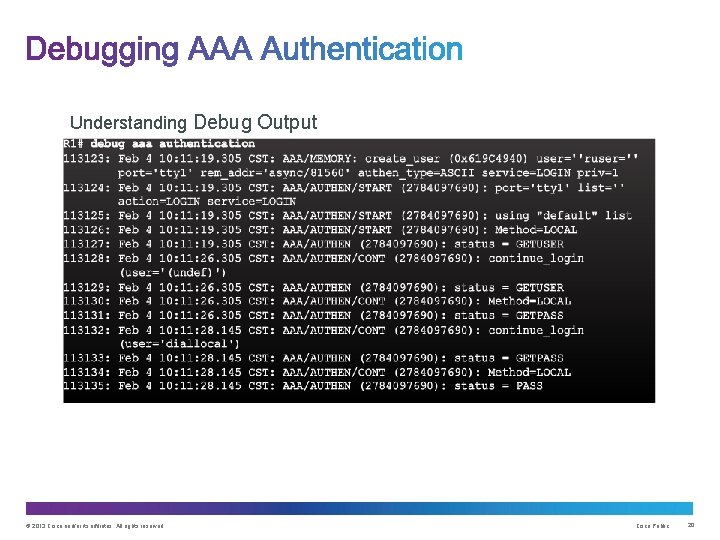
Understanding Debug Output © 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 20
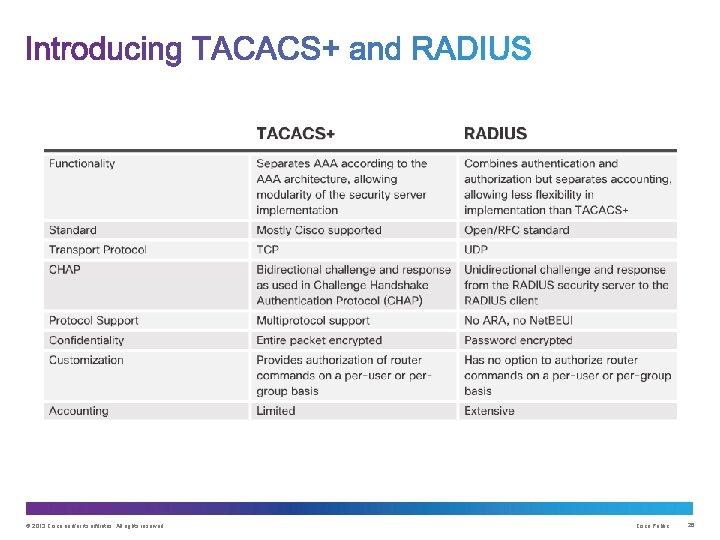
Upon completion of this section, you should be able to: • Describe the benefits of server-based AAA. • Compare the TACACS+ and RADIUS authentication protocols. © 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 21
© 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 22
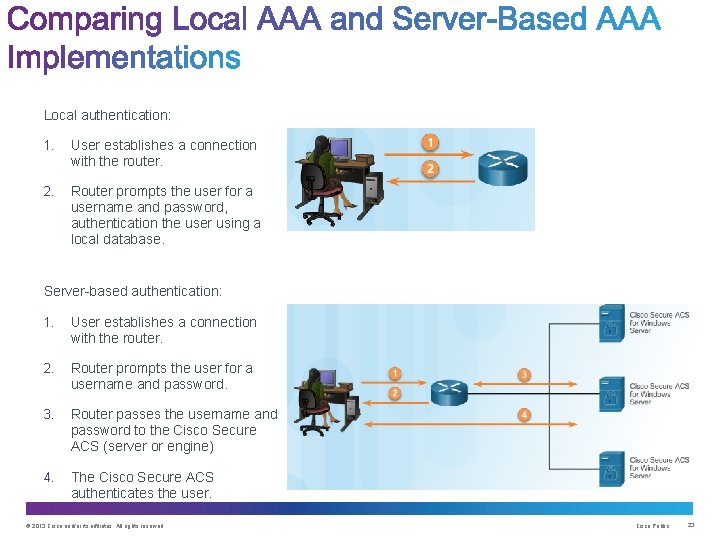
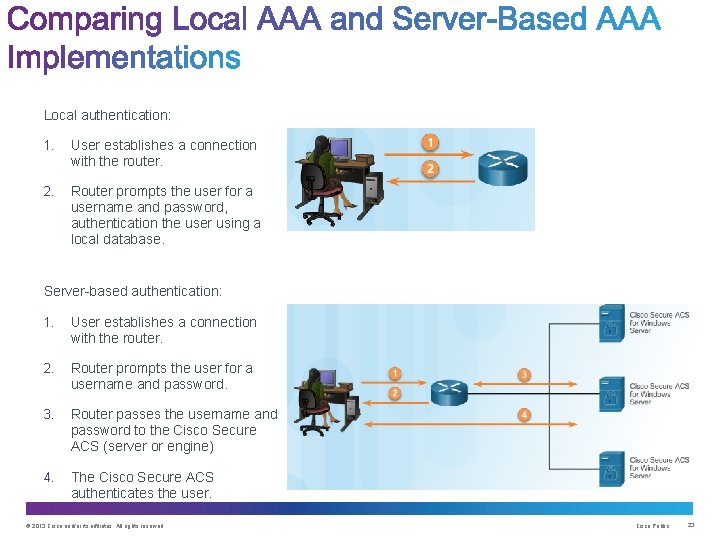
Local authentication: 1. User establishes a connection with the router. 2. Router prompts the user for a username and password, authentication the user using a local database. Server-based authentication: 1. User establishes a connection with the router. 2. Router prompts the user for a username and password. 3. Router passes the username and password to the Cisco Secure ACS (server or engine) 4. The Cisco Secure ACS authenticates the user. © 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 23
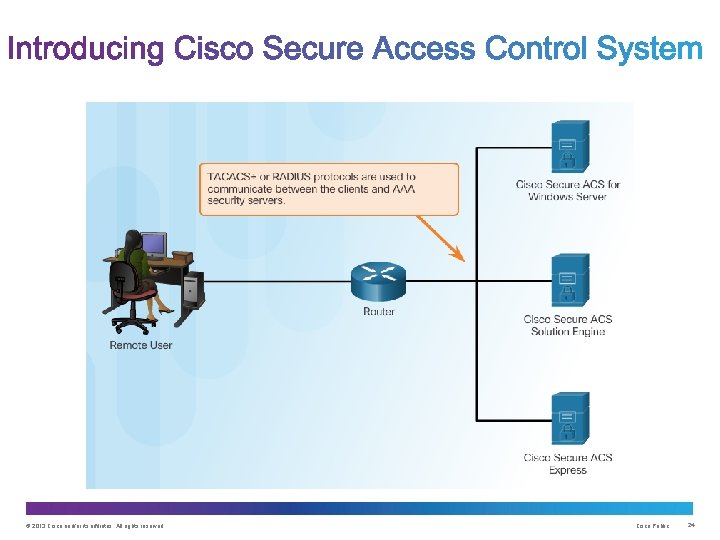
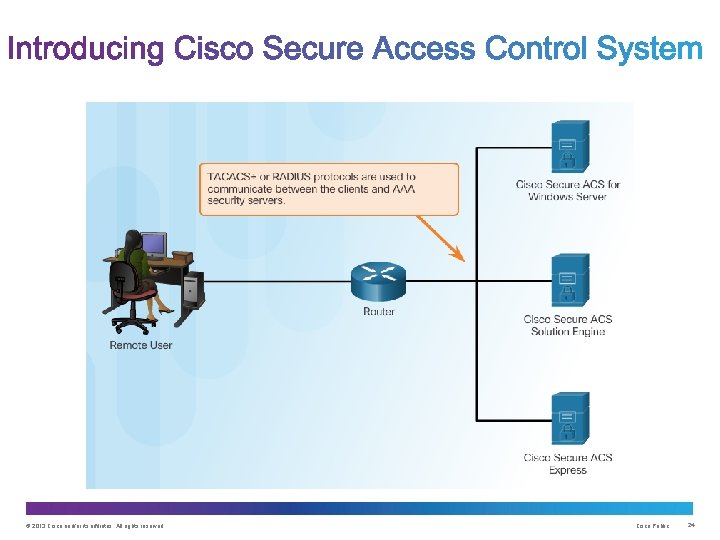
© 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 24
© 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 25
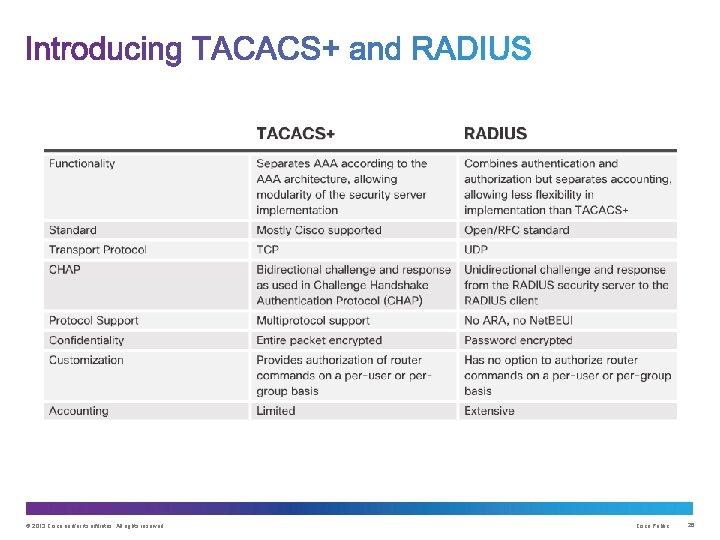
© 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 26
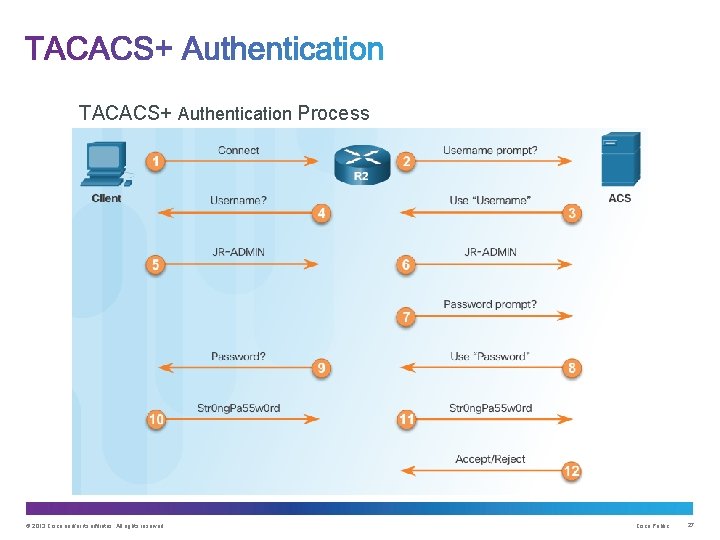
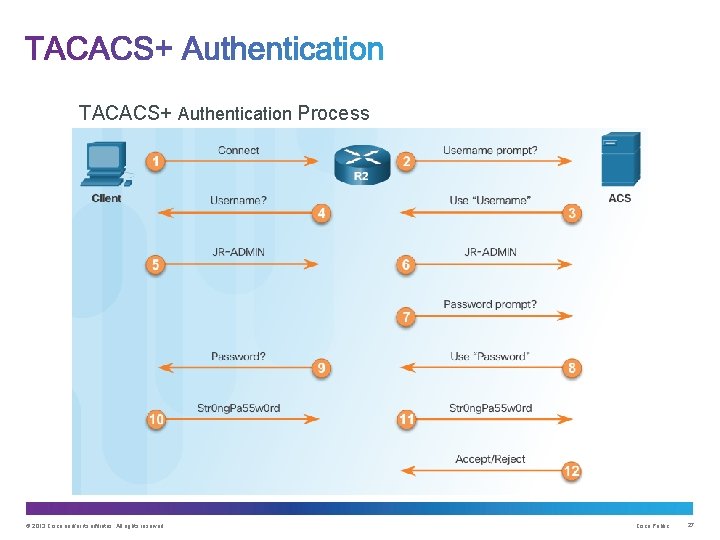
TACACS+ Authentication Process © 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 27
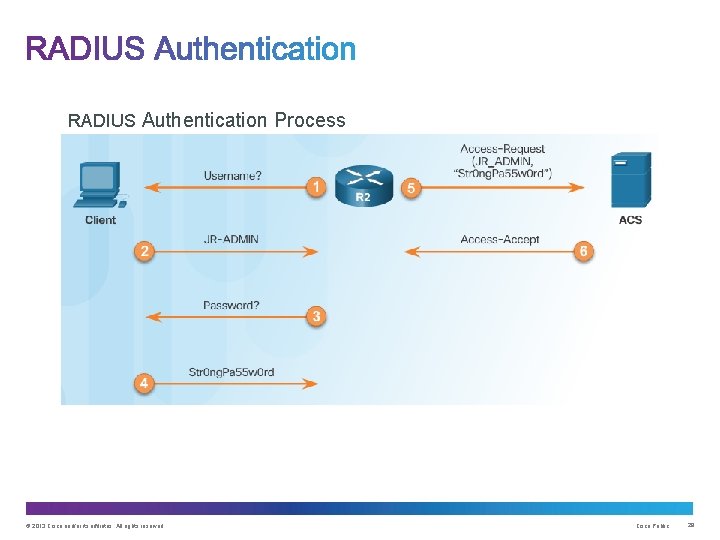
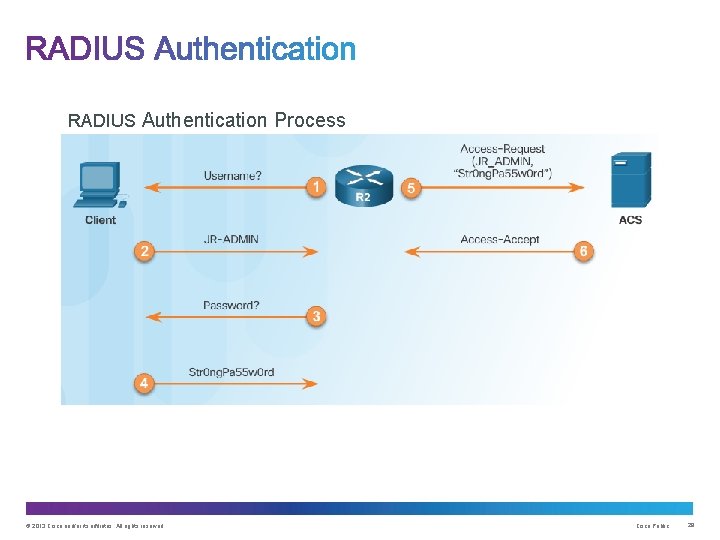
RADIUS Authentication Process © 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 28
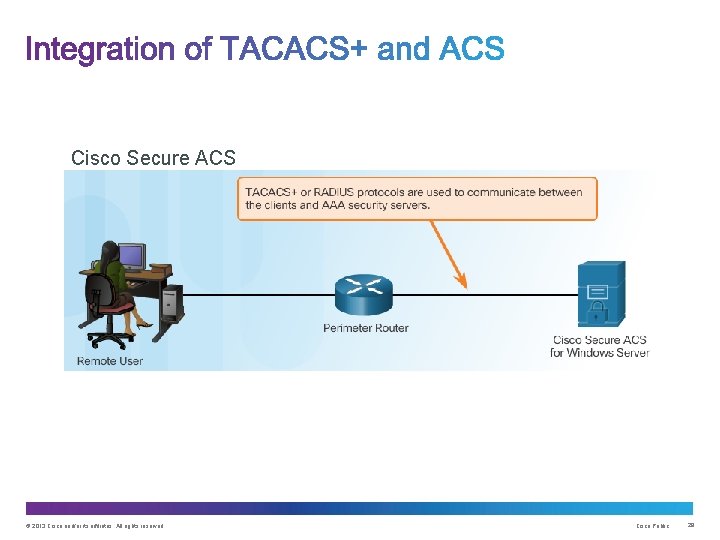
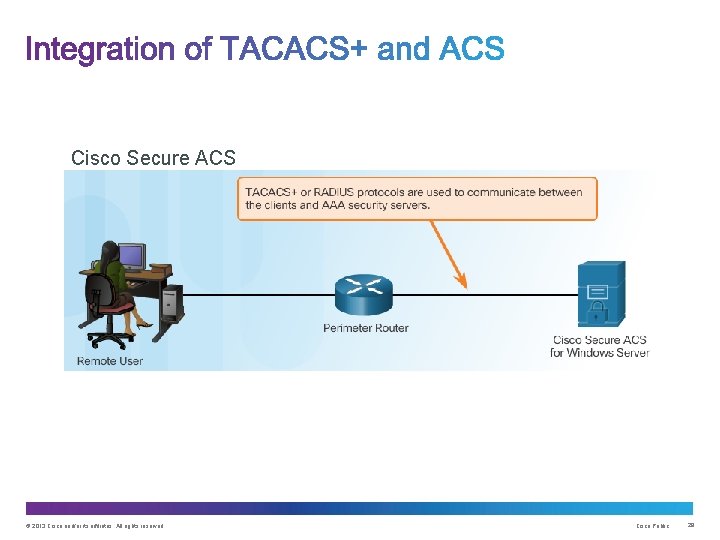
Cisco Secure ACS © 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 29
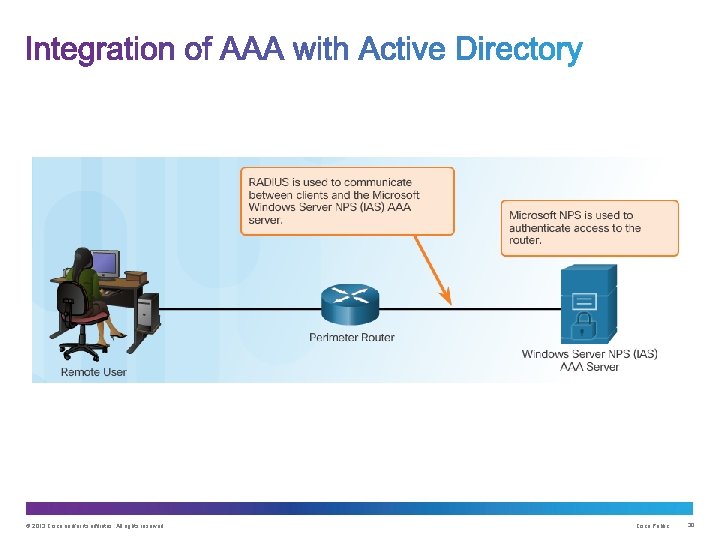
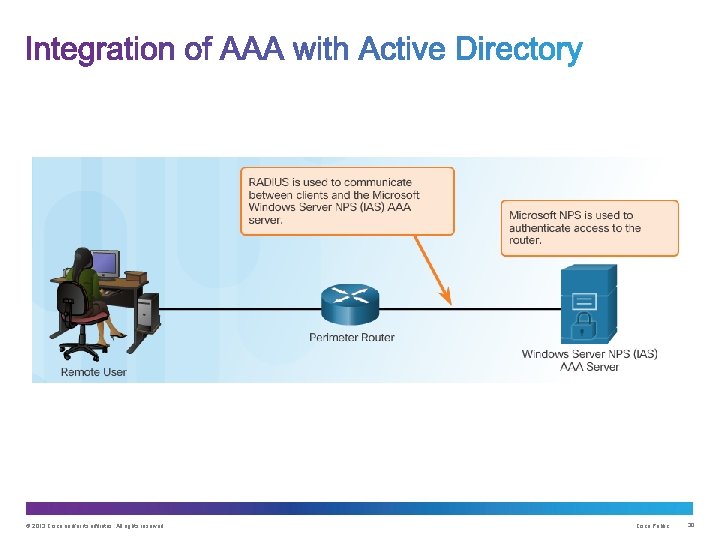
© 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 30
Upon completion of this section, you should be able to: • Configure server-based AAA authentication, using the CLI, on Cisco routers. • Troubleshoot server-based AAA authentication. © 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 31
© 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 32
1. Enable AAA. 2. Specify the IP address of the ACS server. 3. Configure the secret key. 4. Configure authentication to use either the RADIUS or TACACS+ server. © 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 33
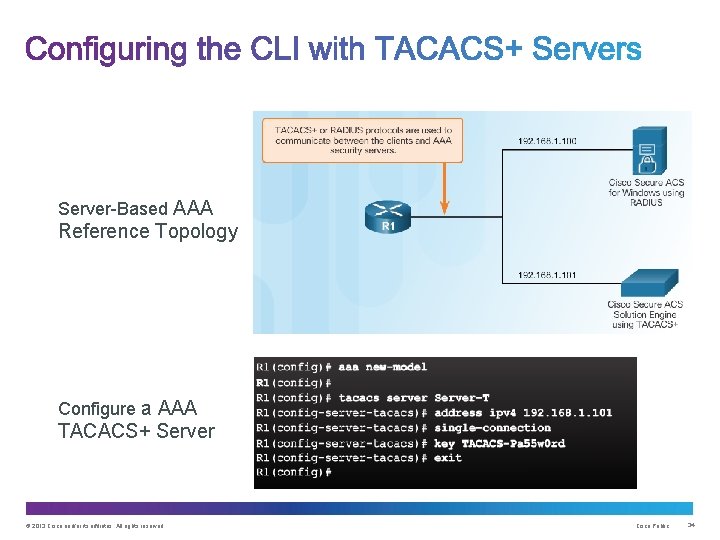
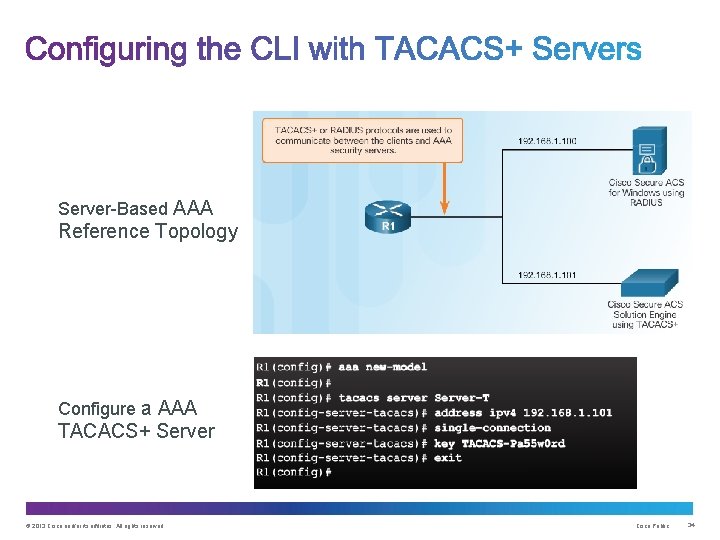
Server-Based AAA Reference Topology Configure a AAA TACACS+ Server © 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 34
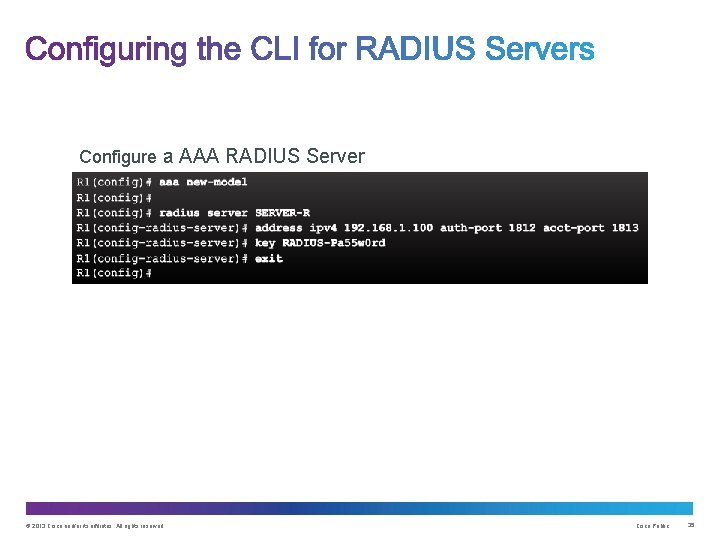
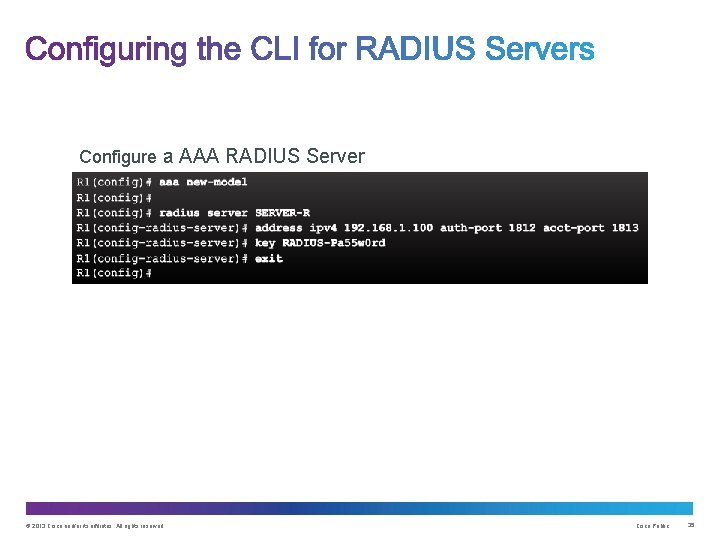
Configure a AAA RADIUS Server © 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 35
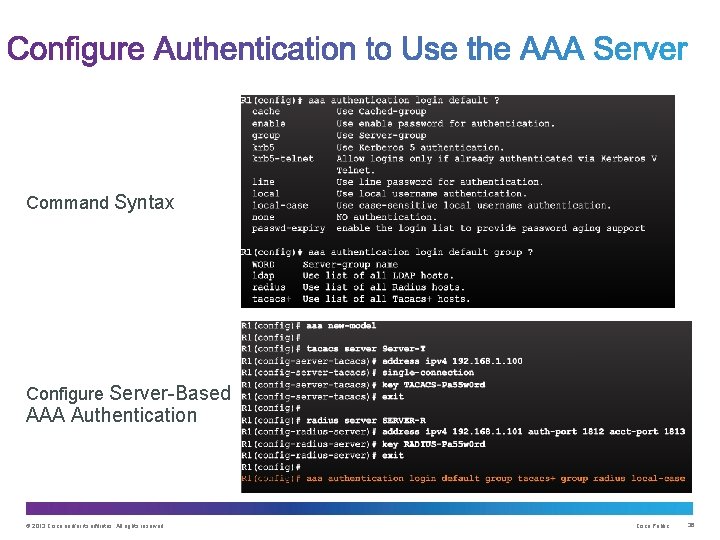
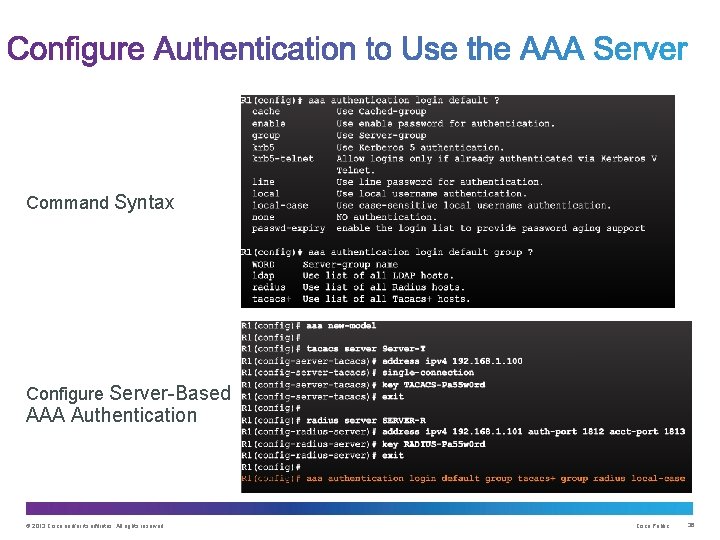
Command Syntax Configure Server-Based AAA Authentication © 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 36
© 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 37
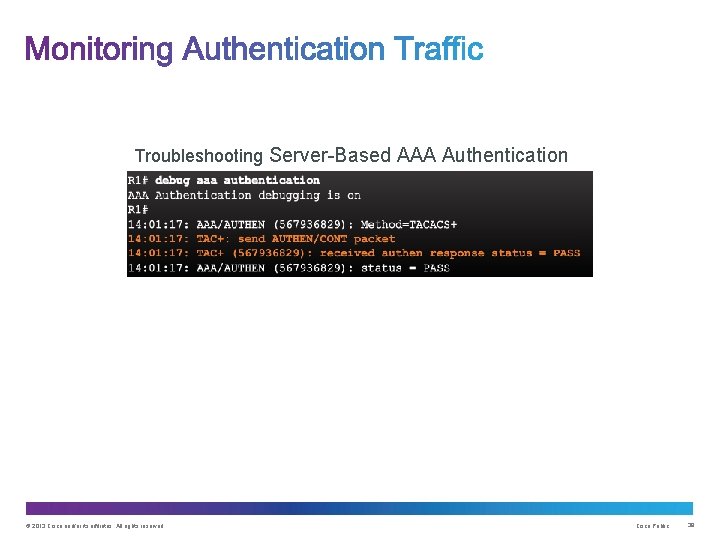
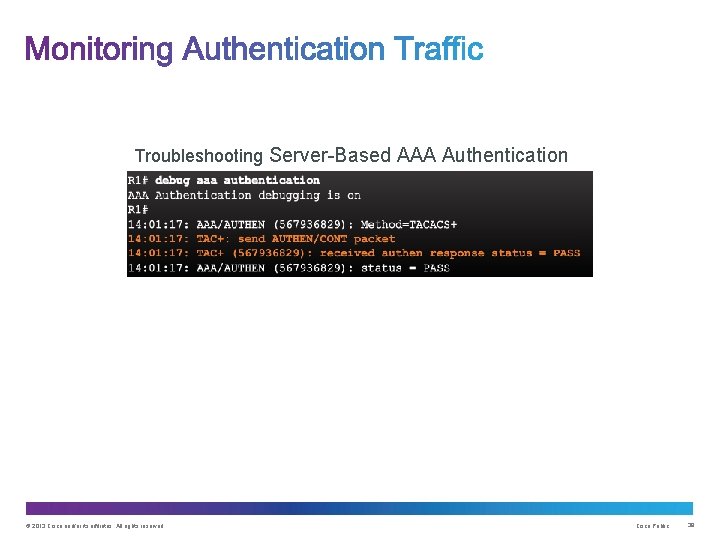
Troubleshooting Server-Based AAA Authentication © 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 38
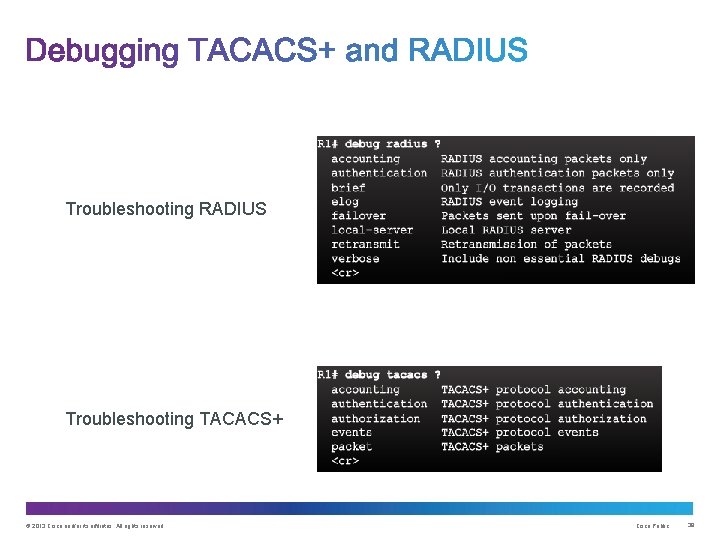
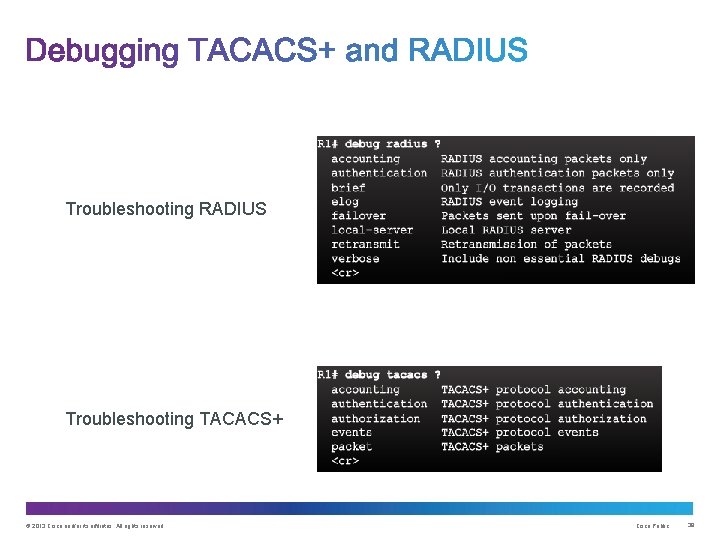
Troubleshooting RADIUS Troubleshooting TACACS+ © 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 39
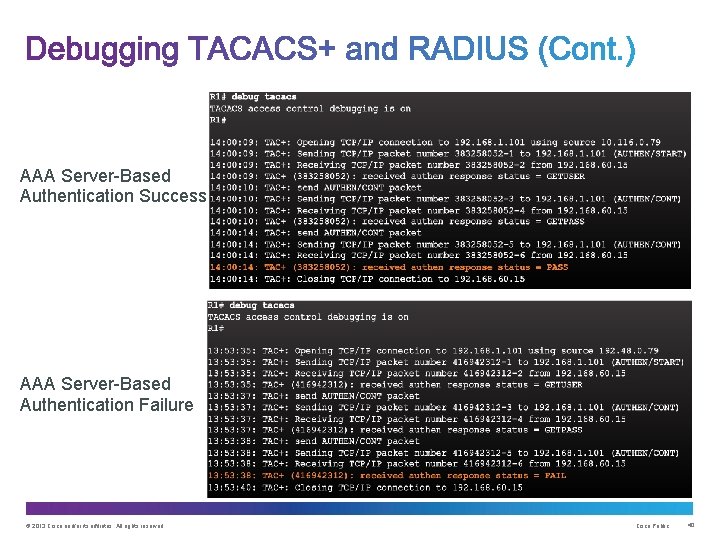
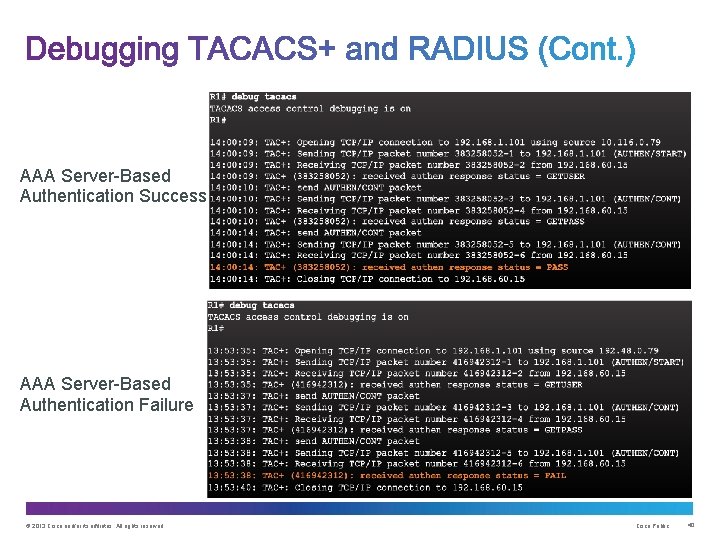
AAA Server-Based Authentication Success AAA Server-Based Authentication Failure © 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 40
Upon completion of this section, you should be able to: • Configure server-based AAA authorization. • Configure server-based AAA accounting. • Explain the functions of 802. 1 x components. © 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 41
© 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 42
Authentication vs. Authorization • Authentication ensures a device or end-user is legitimate • Authorization allows or disallows authenticated users access to certain areas and programs on the network. TACACS+ vs. RADIUS • TACACS+ separates authentication from authorization • RADIUS does not separate authentication from authorization © 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 43
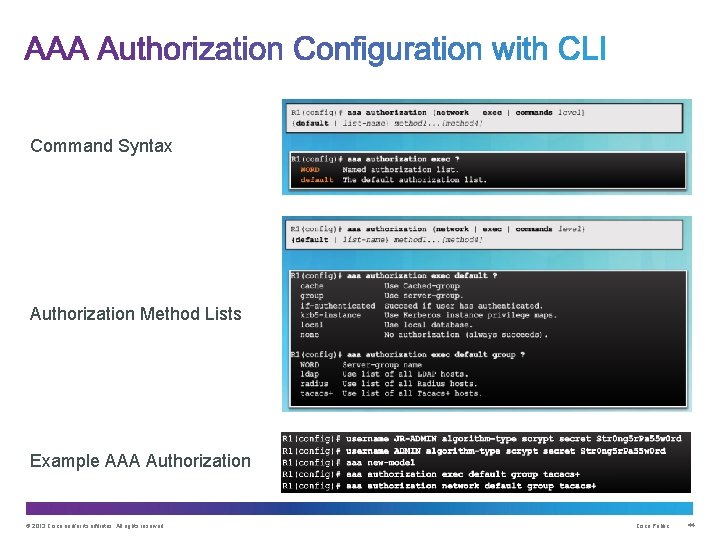
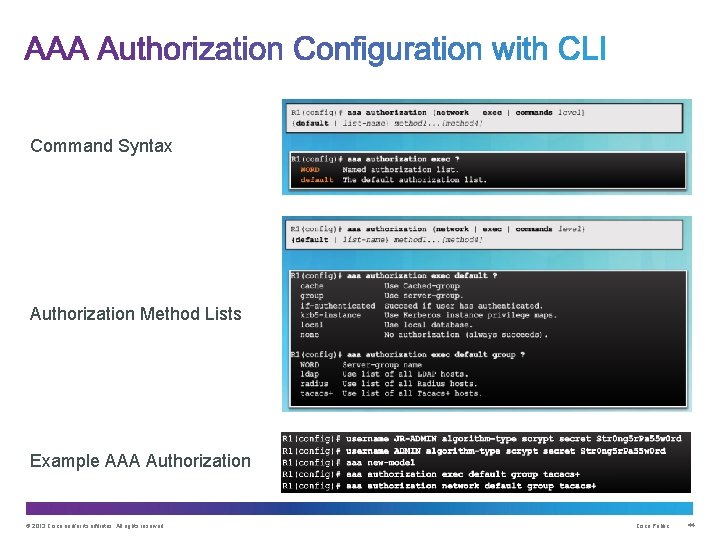
Command Syntax Authorization Method Lists Example AAA Authorization © 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 44
© 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 45
© 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 46
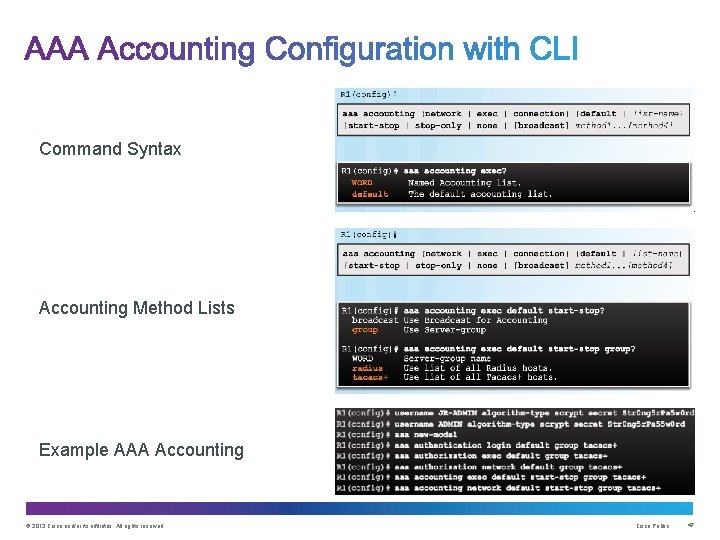
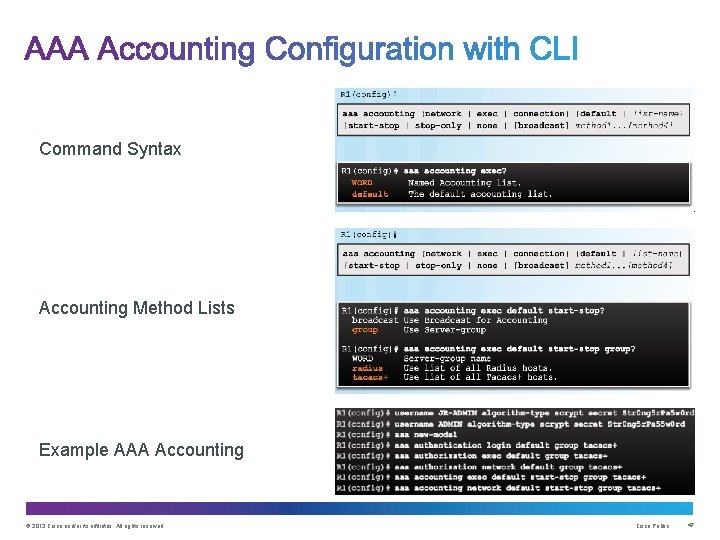
Command Syntax Accounting Method Lists Example AAA Accounting © 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 47
© 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 48
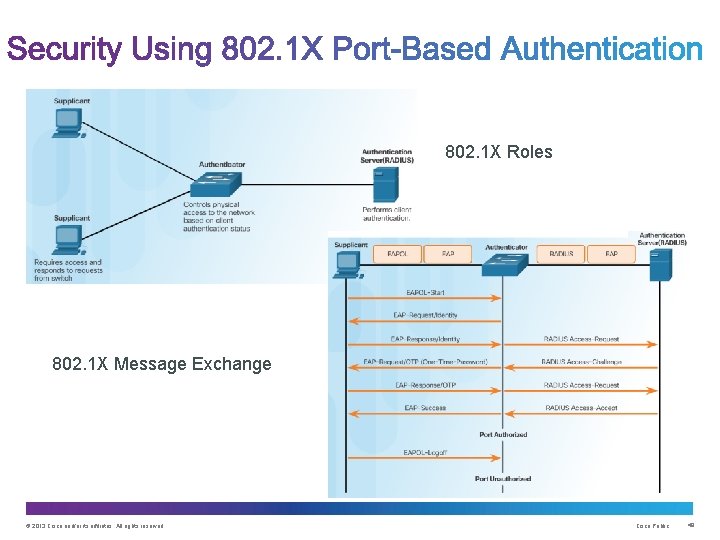
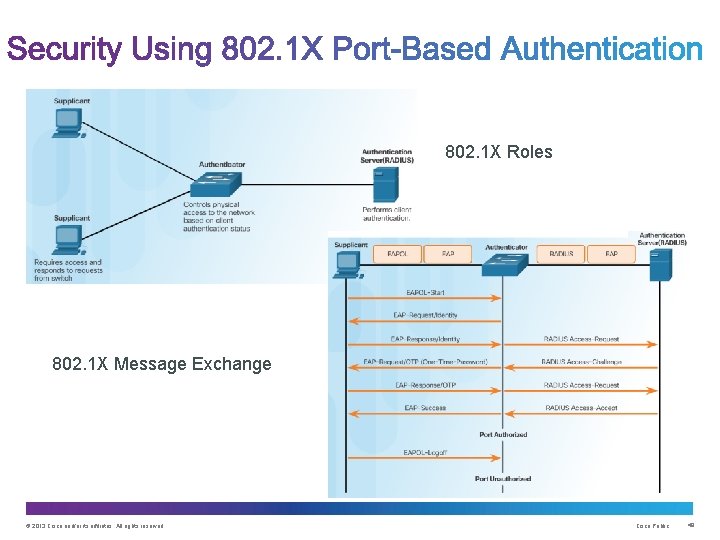
802. 1 X Roles 802. 1 X Message Exchange © 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 49
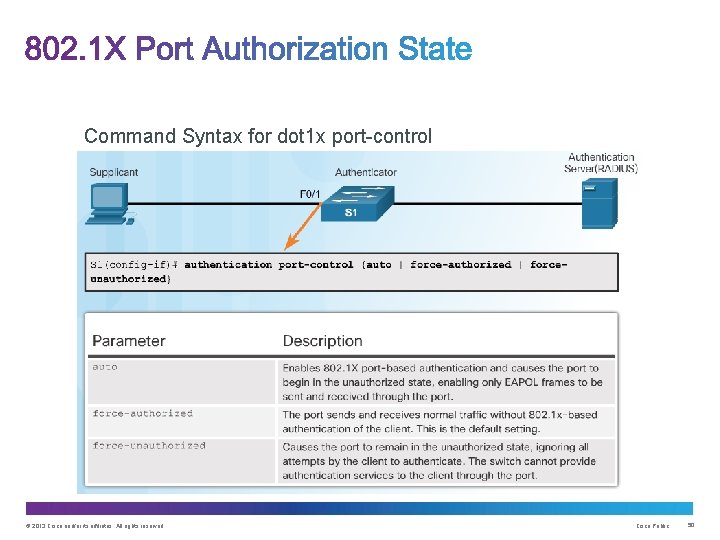
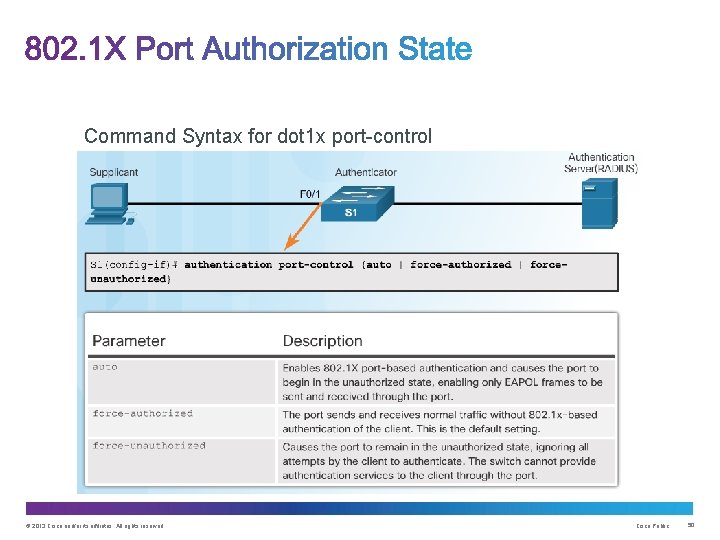
Command Syntax for dot 1 x port-control © 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 50
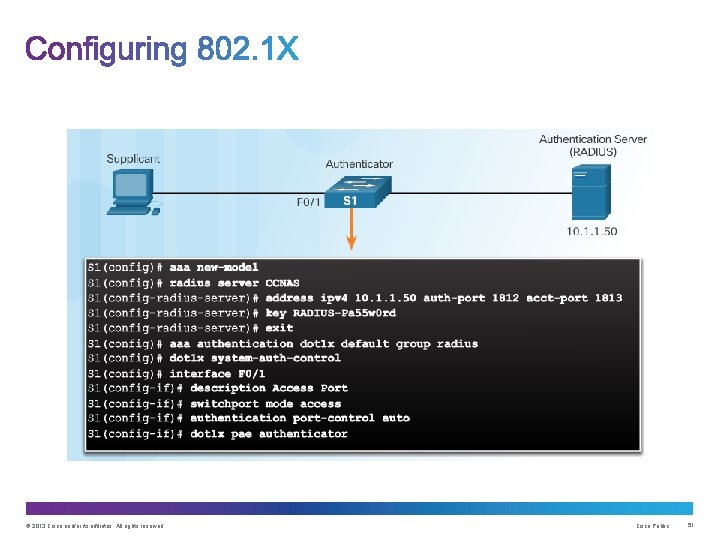
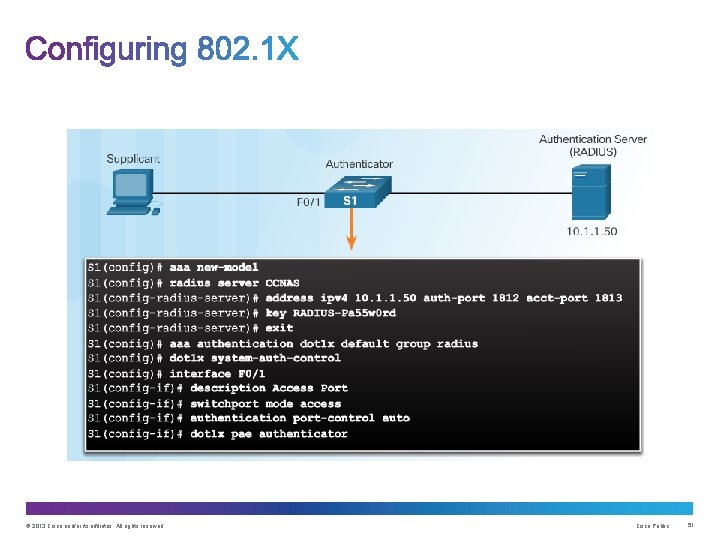
© 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 51
Chapter Objectives: • Explain how AAA is used to secure a network. • Implement AAA authentication that validates users against a local database. • Implement server-based AAA authentication using TACACS+ and RADIUS protocols. • Configure server-based AAA authorization and accounting. © 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 52

Thank you.
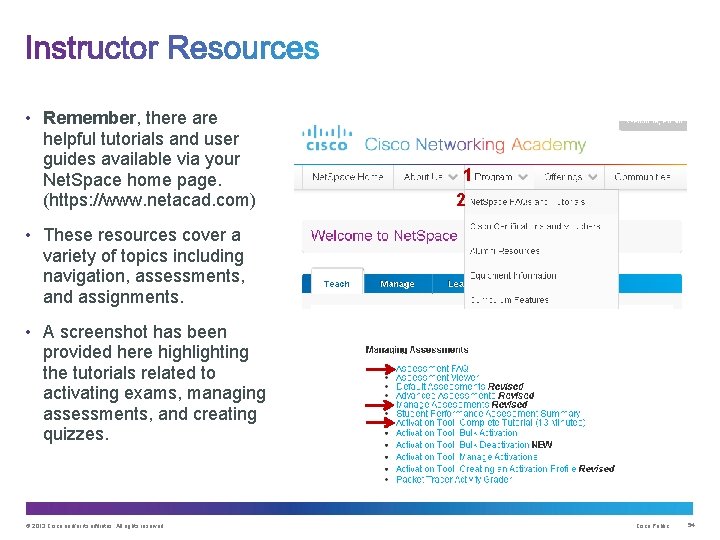
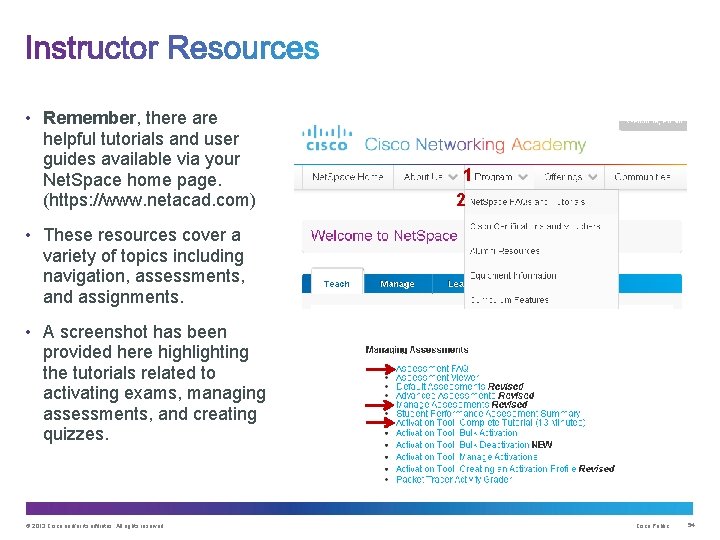
• Remember, there are helpful tutorials and user guides available via your Net. Space home page. (https: //www. netacad. com) 1 2 • These resources cover a variety of topics including navigation, assessments, and assignments. • A screenshot has been provided here highlighting the tutorials related to activating exams, managing assessments, and creating quizzes. © 2013 Cisco and/or its affiliates. All rights reserved. Cisco Public 54