Chapter 2 Sections 4 and 5 Priority Queues
- Slides: 59
Chapter 2, Sections 4 and 5 • Priority Queues • Heaps • Dictionaries • Hash Tables Spring 2003 CS 315 1
Priority Queues Spring 2003 CS 315 2
Outline and Reading Priority. Queue ADT (§ 2. 4. 1) Total order relation (§ 2. 4. 1) Comparator ADT (§ 2. 4. 1) Sorting with a priority queue (§ 2. 4. 2) Selection-sort (§ 2. 4. 2) Insertion-sort (§ 2. 4. 2) Spring 2003 CS 315 3
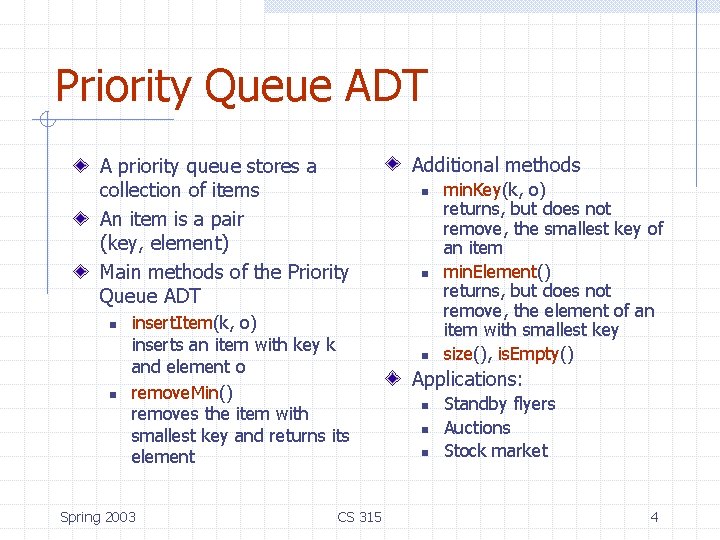
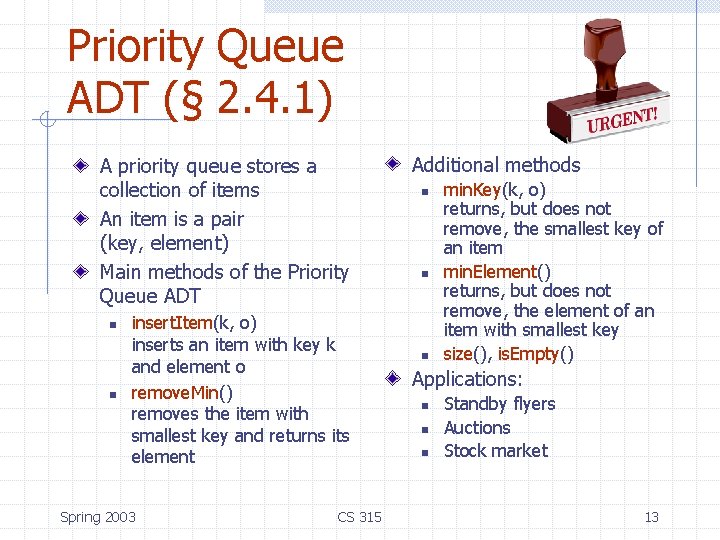
Priority Queue ADT A priority queue stores a collection of items An item is a pair (key, element) Main methods of the Priority Queue ADT n n insert. Item(k, o) inserts an item with key k and element o remove. Min() removes the item with smallest key and returns its element Spring 2003 CS 315 Additional methods n n n min. Key(k, o) returns, but does not remove, the smallest key of an item min. Element() returns, but does not remove, the element of an item with smallest key size(), is. Empty() Applications: n n n Standby flyers Auctions Stock market 4
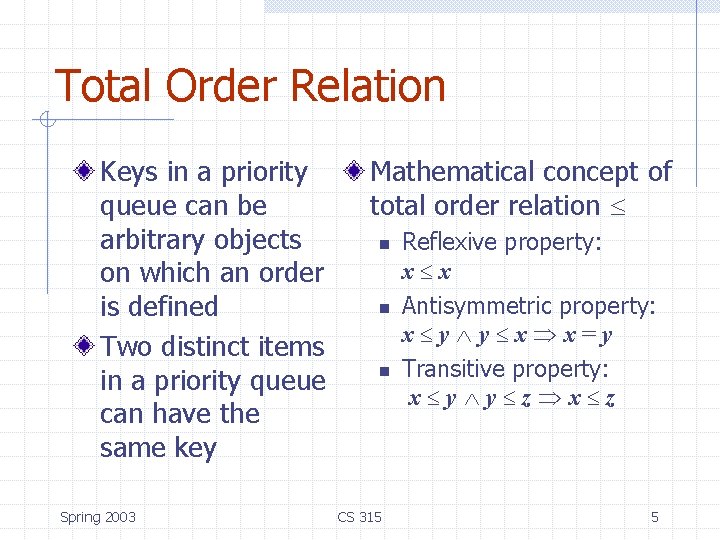
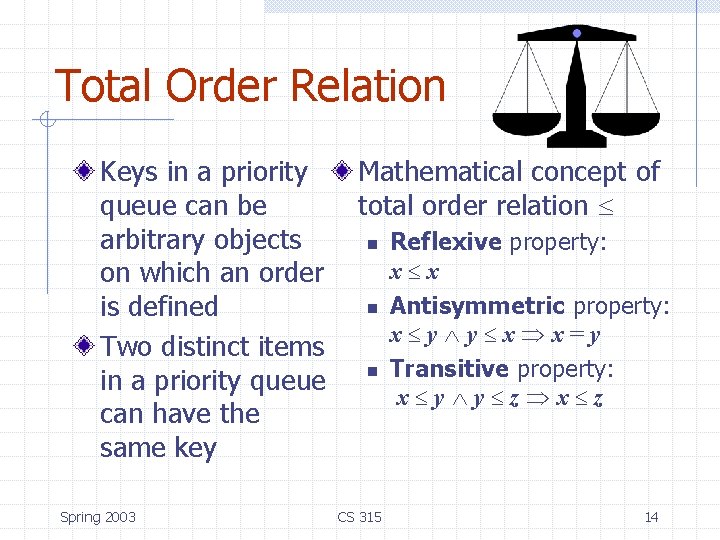
Total Order Relation Keys in a priority queue can be arbitrary objects on which an order is defined Two distinct items in a priority queue can have the same key Spring 2003 Mathematical concept of total order relation n n n CS 315 Reflexive property: x x Antisymmetric property: x y y x x=y Transitive property: x y y z x z 5
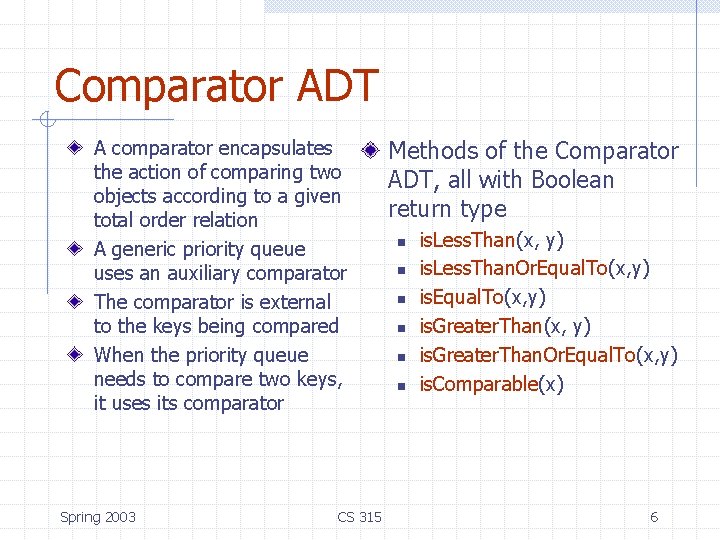
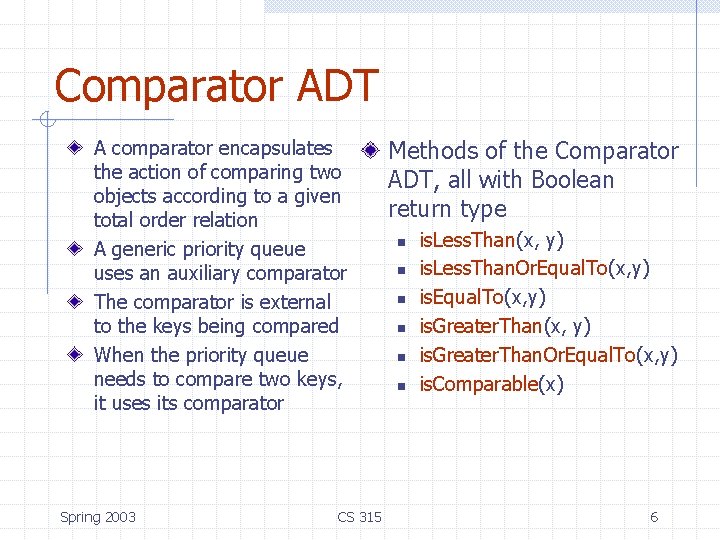
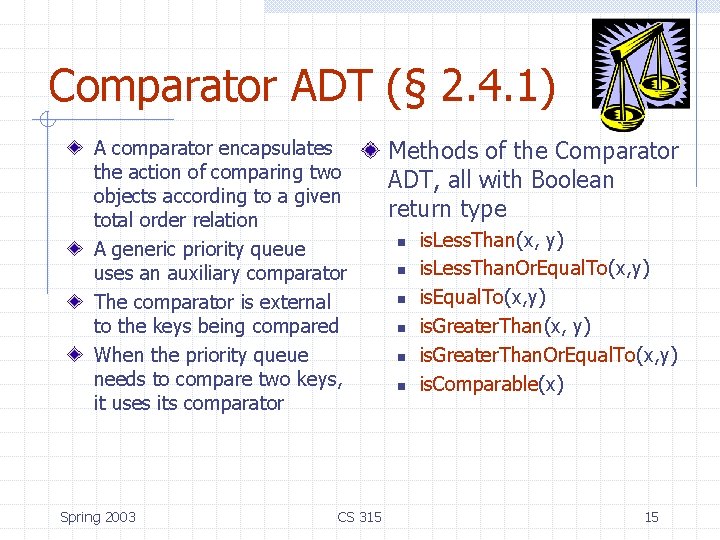
Comparator ADT A comparator encapsulates the action of comparing two objects according to a given total order relation A generic priority queue uses an auxiliary comparator The comparator is external to the keys being compared When the priority queue needs to compare two keys, it uses its comparator Spring 2003 CS 315 Methods of the Comparator ADT, all with Boolean return type n n n is. Less. Than(x, y) is. Less. Than. Or. Equal. To(x, y) is. Greater. Than(x, y) is. Greater. Than. Or. Equal. To(x, y) is. Comparable(x) 6
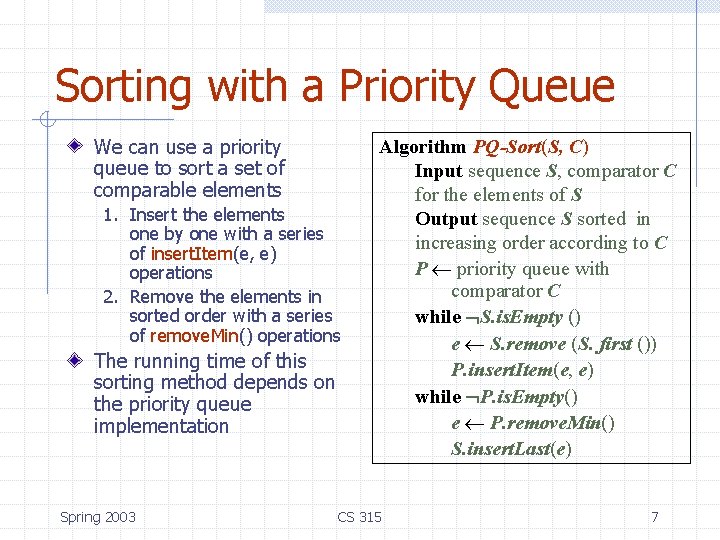
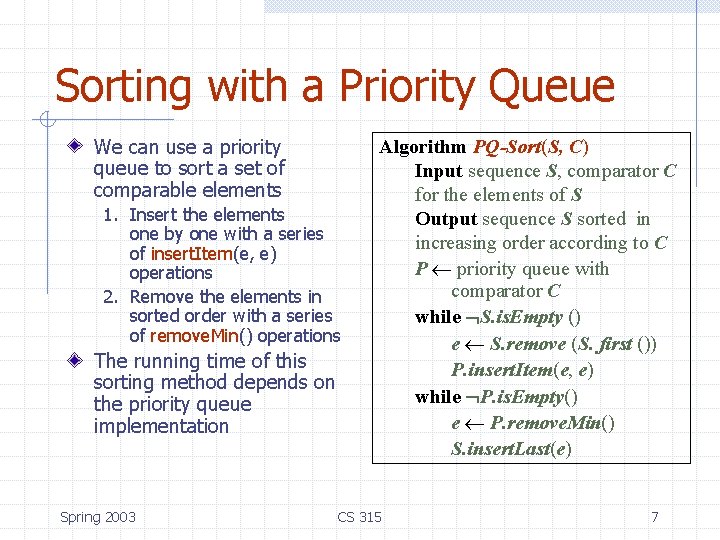
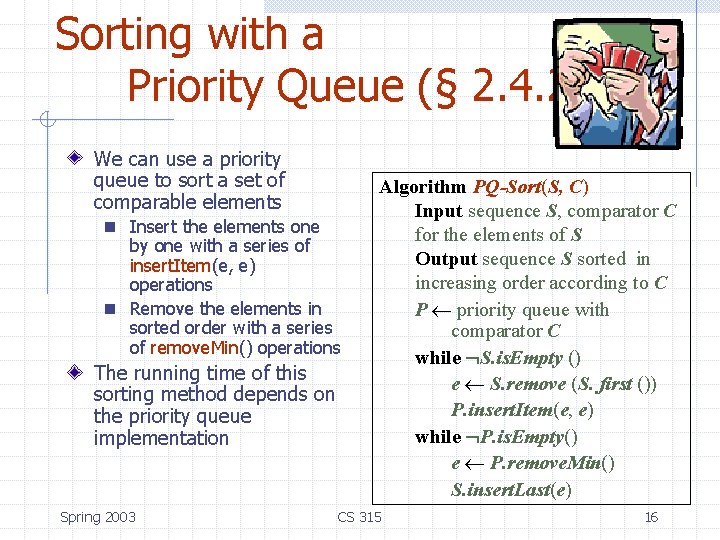
Sorting with a Priority Queue We can use a priority queue to sort a set of comparable elements 1. Insert the elements one by one with a series of insert. Item(e, e) operations 2. Remove the elements in sorted order with a series of remove. Min() operations The running time of this sorting method depends on the priority queue implementation Spring 2003 Algorithm PQ-Sort(S, C) Input sequence S, comparator C for the elements of S Output sequence S sorted in increasing order according to C P priority queue with comparator C while S. is. Empty () e S. remove (S. first ()) P. insert. Item(e, e) while P. is. Empty() e P. remove. Min() S. insert. Last(e) CS 315 7
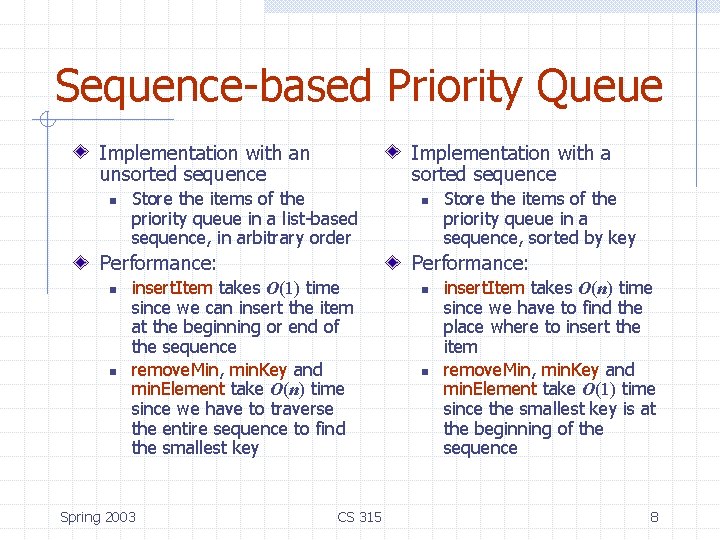
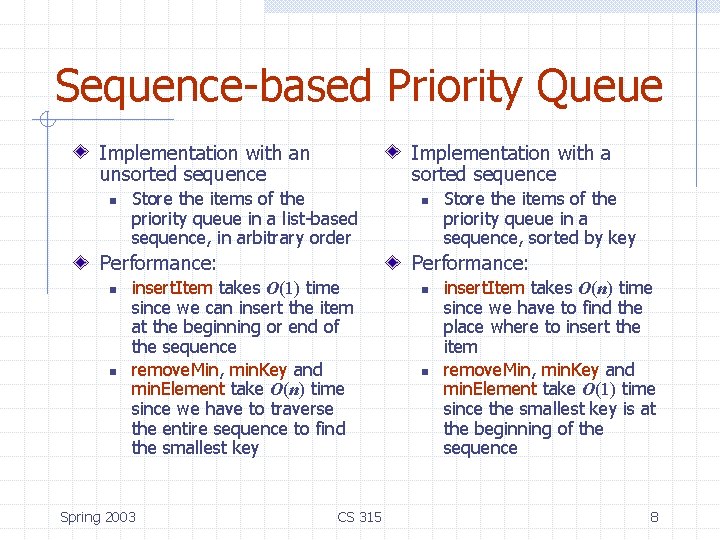
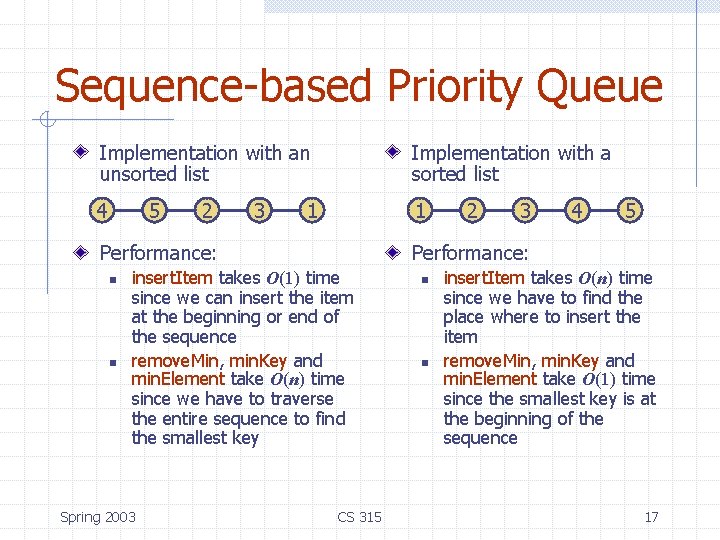
Sequence-based Priority Queue Implementation with an unsorted sequence n Implementation with a sorted sequence Store the items of the priority queue in a list-based sequence, in arbitrary order Performance: n n Store the items of the priority queue in a sequence, sorted by key Performance: insert. Item takes O(1) time since we can insert the item at the beginning or end of the sequence remove. Min, min. Key and min. Element take O(n) time since we have to traverse the entire sequence to find the smallest key Spring 2003 n CS 315 n n insert. Item takes O(n) time since we have to find the place where to insert the item remove. Min, min. Key and min. Element take O(1) time since the smallest key is at the beginning of the sequence 8
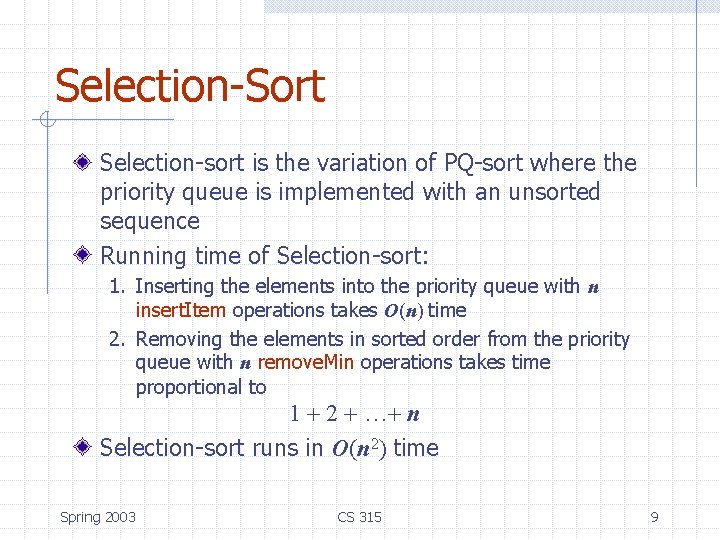
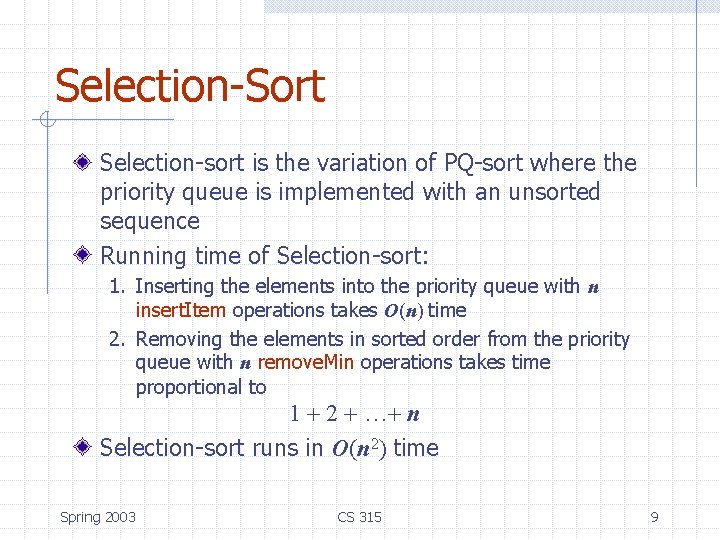
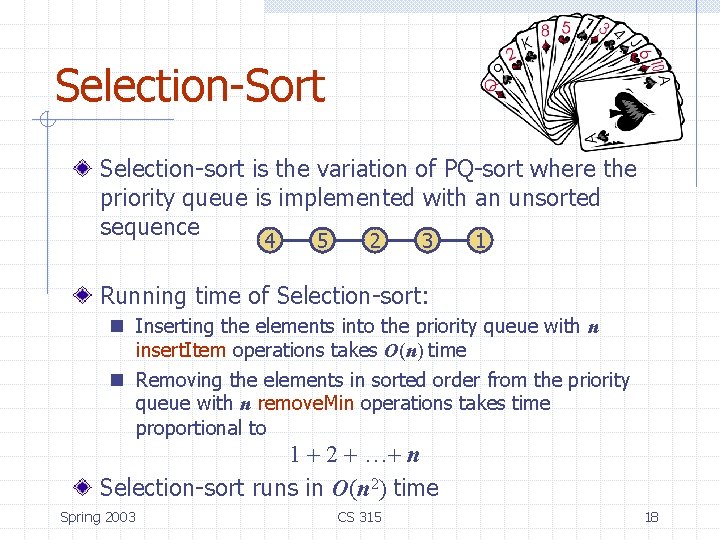
Selection-Sort Selection-sort is the variation of PQ-sort where the priority queue is implemented with an unsorted sequence Running time of Selection-sort: 1. Inserting the elements into the priority queue with n insert. Item operations takes O(n) time 2. Removing the elements in sorted order from the priority queue with n remove. Min operations takes time proportional to 1 + 2 + …+ n Selection-sort runs in O(n 2) time Spring 2003 CS 315 9
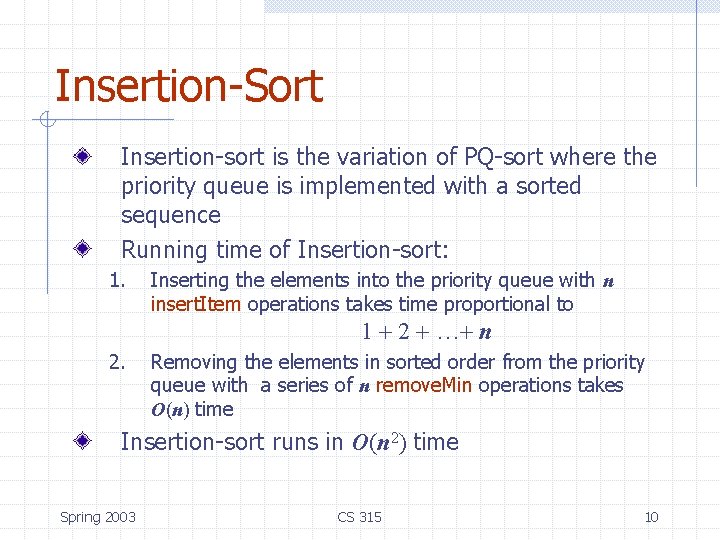
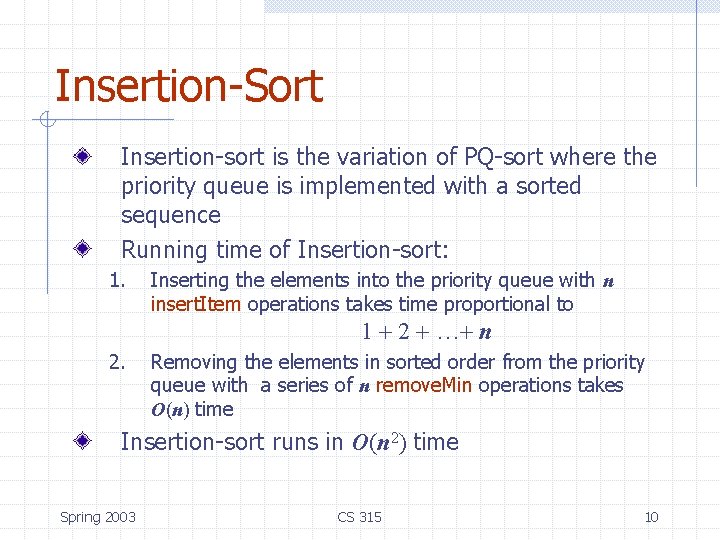
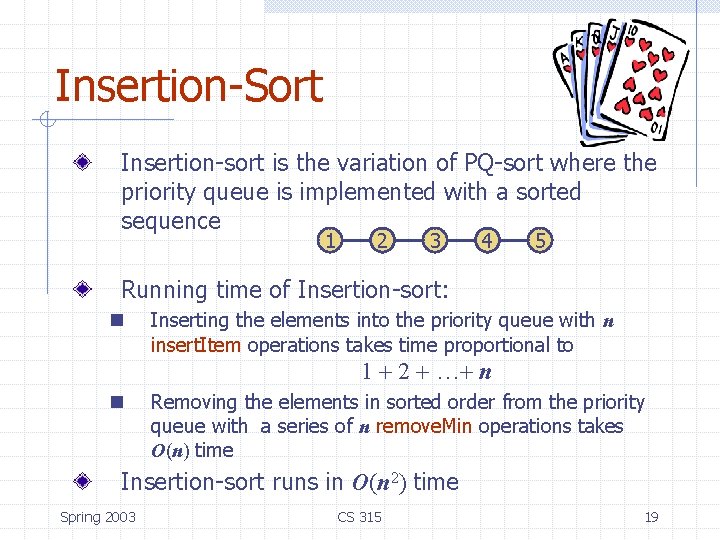
Insertion-Sort Insertion-sort is the variation of PQ-sort where the priority queue is implemented with a sorted sequence Running time of Insertion-sort: 1. Inserting the elements into the priority queue with n insert. Item operations takes time proportional to 1 + 2 + …+ n 2. Removing the elements in sorted order from the priority queue with a series of n remove. Min operations takes O(n) time Insertion-sort runs in O(n 2) time Spring 2003 CS 315 10
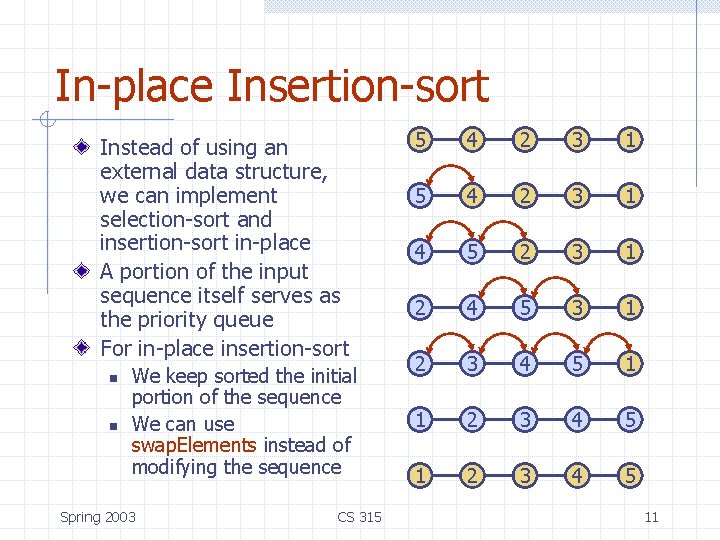
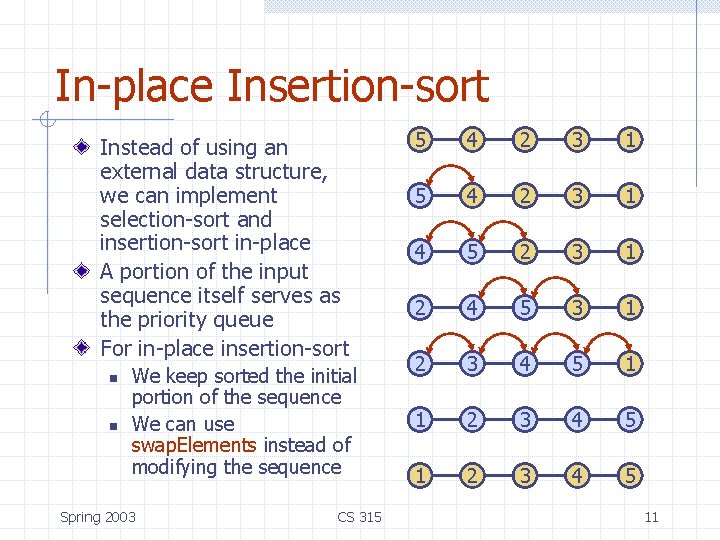
In-place Insertion-sort Instead of using an external data structure, we can implement selection-sort and insertion-sort in-place A portion of the input sequence itself serves as the priority queue For in-place insertion-sort n n We keep sorted the initial portion of the sequence We can use swap. Elements instead of modifying the sequence Spring 2003 CS 315 5 4 2 3 1 4 5 2 3 1 2 4 5 3 1 2 3 4 5 11
Heaps and Priority Queues 2 5 9 Spring 2003 6 7 CS 315 12
Priority Queue ADT (§ 2. 4. 1) A priority queue stores a collection of items An item is a pair (key, element) Main methods of the Priority Queue ADT n n insert. Item(k, o) inserts an item with key k and element o remove. Min() removes the item with smallest key and returns its element Spring 2003 CS 315 Additional methods n n n min. Key(k, o) returns, but does not remove, the smallest key of an item min. Element() returns, but does not remove, the element of an item with smallest key size(), is. Empty() Applications: n n n Standby flyers Auctions Stock market 13
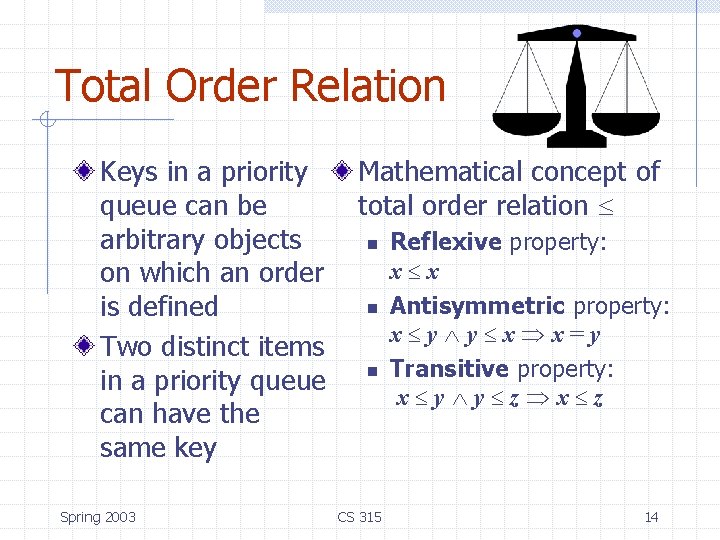
Total Order Relation Keys in a priority queue can be arbitrary objects on which an order is defined Two distinct items in a priority queue can have the same key Spring 2003 Mathematical concept of total order relation n n n CS 315 Reflexive property: x x Antisymmetric property: x y y x x=y Transitive property: x y y z x z 14
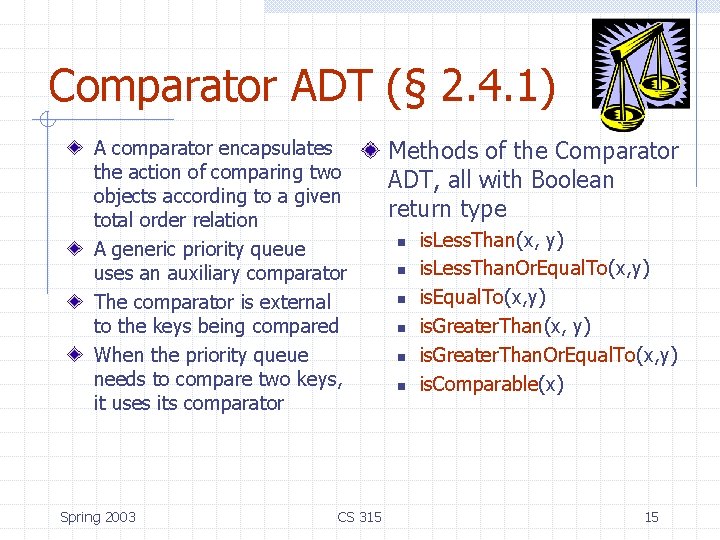
Comparator ADT (§ 2. 4. 1) A comparator encapsulates the action of comparing two objects according to a given total order relation A generic priority queue uses an auxiliary comparator The comparator is external to the keys being compared When the priority queue needs to compare two keys, it uses its comparator Spring 2003 CS 315 Methods of the Comparator ADT, all with Boolean return type n n n is. Less. Than(x, y) is. Less. Than. Or. Equal. To(x, y) is. Greater. Than(x, y) is. Greater. Than. Or. Equal. To(x, y) is. Comparable(x) 15
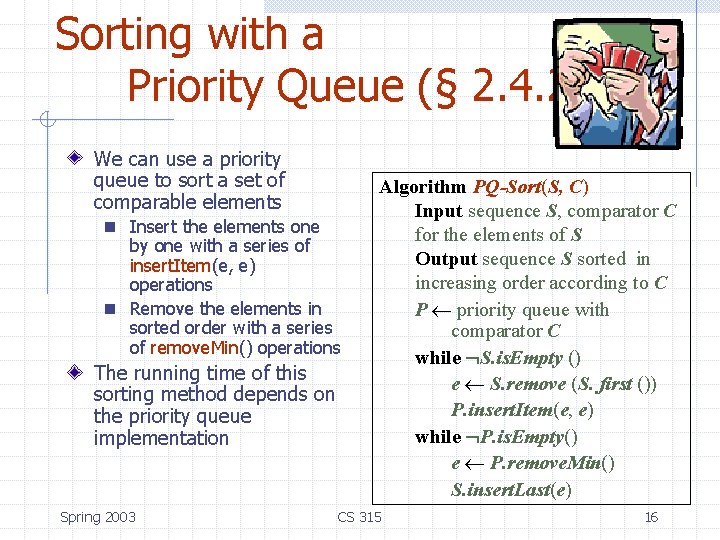
Sorting with a Priority Queue (§ 2. 4. 2) We can use a priority queue to sort a set of comparable elements n Insert the elements one by one with a series of insert. Item(e, e) operations n Remove the elements in sorted order with a series of remove. Min() operations The running time of this sorting method depends on the priority queue implementation Spring 2003 Algorithm PQ-Sort(S, C) Input sequence S, comparator C for the elements of S Output sequence S sorted in increasing order according to C P priority queue with comparator C while S. is. Empty () e S. remove (S. first ()) P. insert. Item(e, e) while P. is. Empty() e P. remove. Min() S. insert. Last(e) CS 315 16
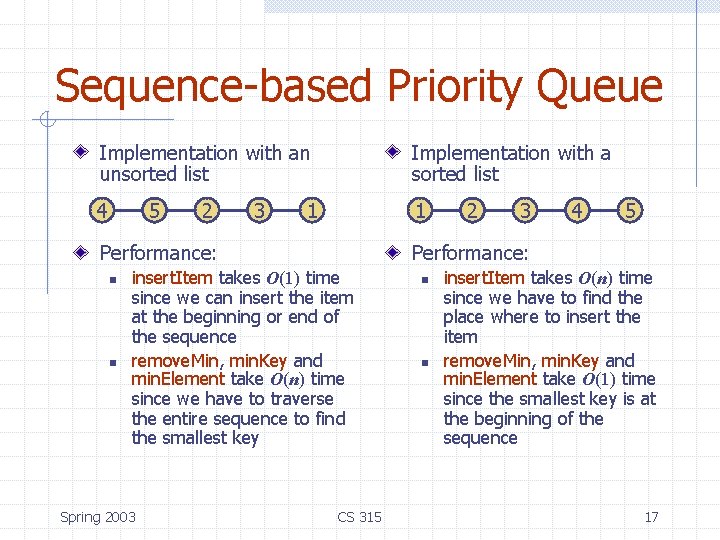
Sequence-based Priority Queue Implementation with an unsorted list Implementation with a sorted list 4 1 5 2 3 1 Performance: n n 3 4 5 Performance: insert. Item takes O(1) time since we can insert the item at the beginning or end of the sequence remove. Min, min. Key and min. Element take O(n) time since we have to traverse the entire sequence to find the smallest key Spring 2003 2 CS 315 n n insert. Item takes O(n) time since we have to find the place where to insert the item remove. Min, min. Key and min. Element take O(1) time since the smallest key is at the beginning of the sequence 17
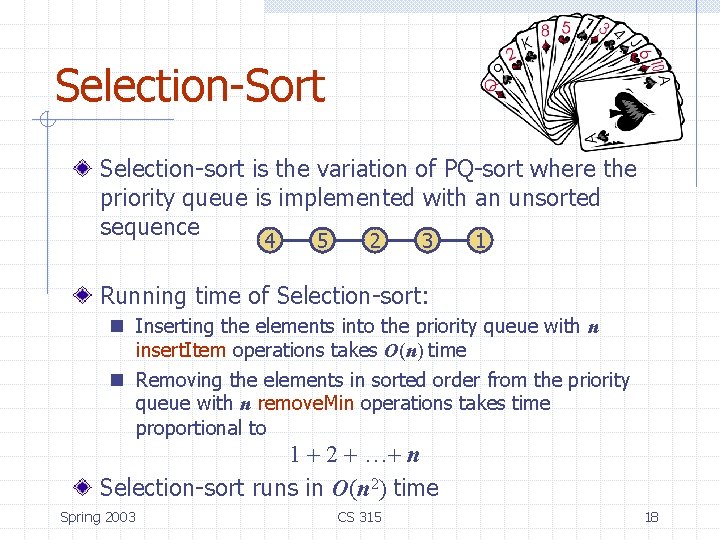
Selection-Sort Selection-sort is the variation of PQ-sort where the priority queue is implemented with an unsorted sequence 4 5 2 3 1 Running time of Selection-sort: n Inserting the elements into the priority queue with n insert. Item operations takes O(n) time n Removing the elements in sorted order from the priority queue with n remove. Min operations takes time proportional to 1 + 2 + …+ n Selection-sort runs in O(n 2) time Spring 2003 CS 315 18
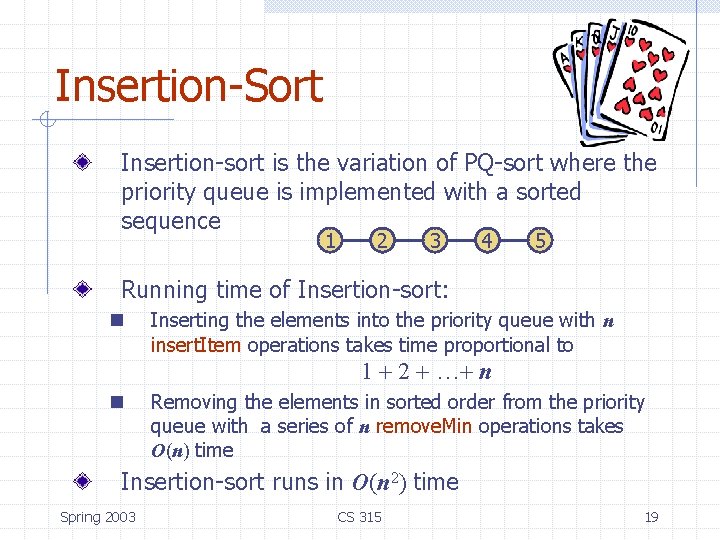
Insertion-Sort Insertion-sort is the variation of PQ-sort where the priority queue is implemented with a sorted sequence 1 2 3 4 5 Running time of Insertion-sort: n Inserting the elements into the priority queue with n insert. Item operations takes time proportional to 1 + 2 + …+ n n Removing the elements in sorted order from the priority queue with a series of n remove. Min operations takes O(n) time Insertion-sort runs in O(n 2) time Spring 2003 CS 315 19
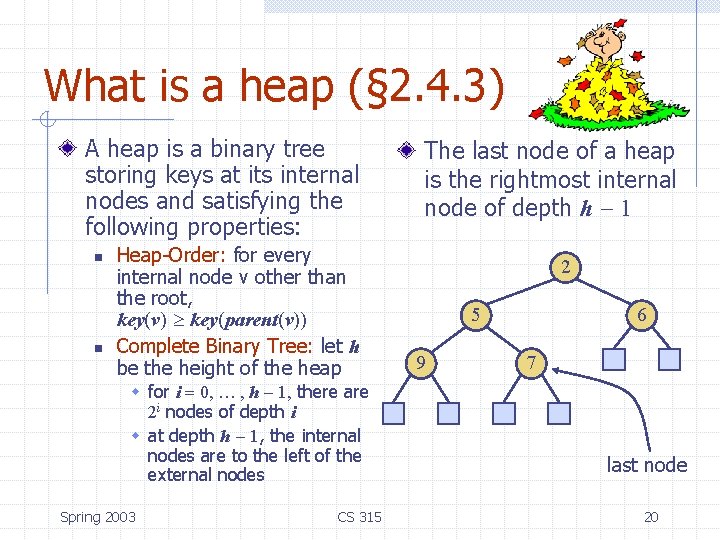
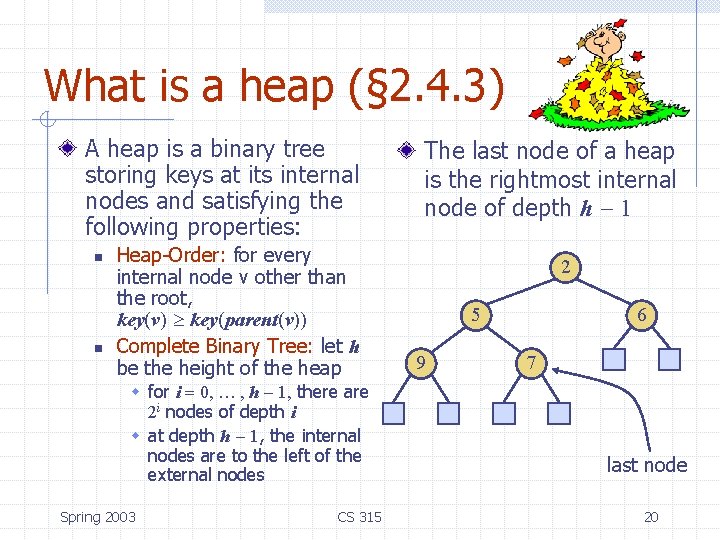
What is a heap (§ 2. 4. 3) A heap is a binary tree storing keys at its internal nodes and satisfying the following properties: n n Heap-Order: for every internal node v other than the root, key(v) key(parent(v)) Complete Binary Tree: let h be the height of the heap w for i = 0, … , h - 1, there are 2 i nodes of depth i w at depth h - 1, the internal nodes are to the left of the external nodes Spring 2003 CS 315 The last node of a heap is the rightmost internal node of depth h - 1 2 5 9 6 7 last node 20
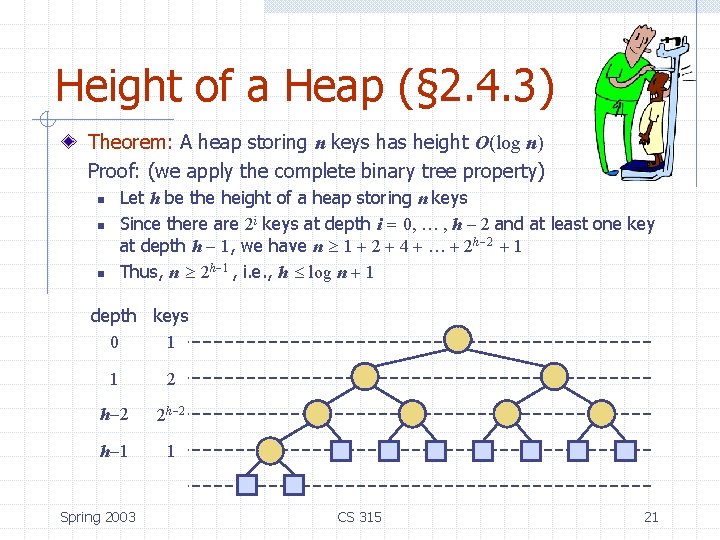
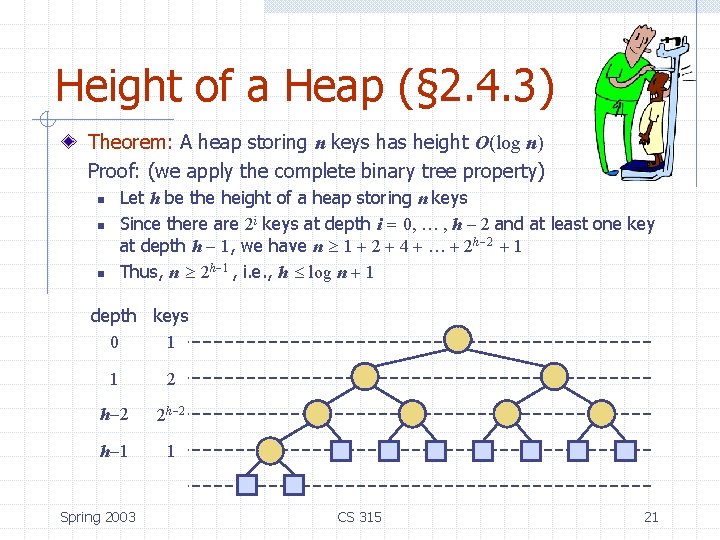
Height of a Heap (§ 2. 4. 3) Theorem: A heap storing n keys has height O(log n) Proof: (we apply the complete binary tree property) Let h be the height of a heap storing n keys Since there are 2 i keys at depth i = 0, … , h - 2 and at least one key at depth h - 1, we have n 1 + 2 + 4 + … + 2 h-2 + 1 Thus, n 2 h-1 , i. e. , h log n + 1 n n n depth keys 0 1 1 2 h-2 2 h-2 h-1 1 Spring 2003 CS 315 21
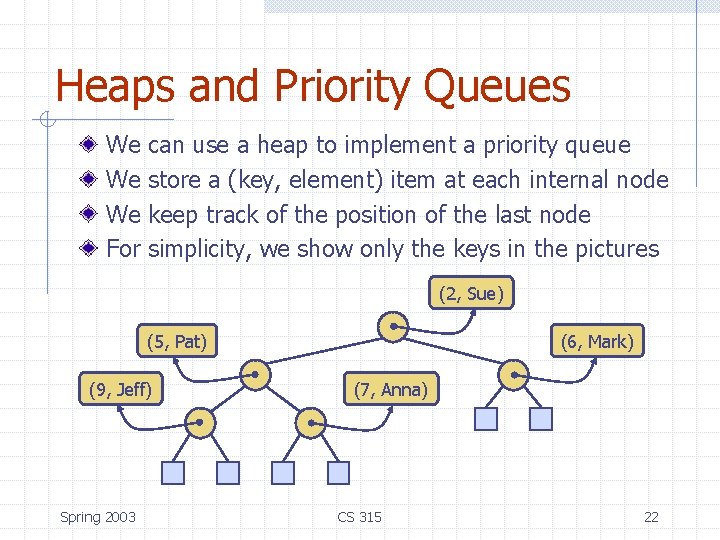
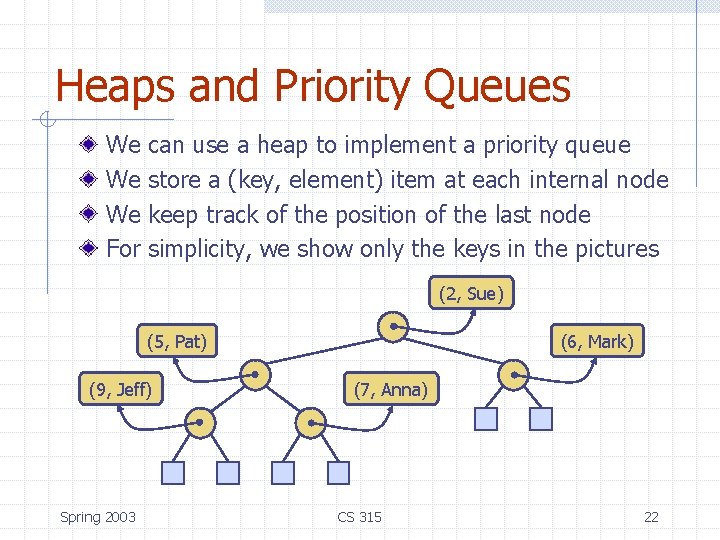
Heaps and Priority Queues We We We For can use a heap to implement a priority queue store a (key, element) item at each internal node keep track of the position of the last node simplicity, we show only the keys in the pictures (2, Sue) (5, Pat) (9, Jeff) Spring 2003 (6, Mark) (7, Anna) CS 315 22
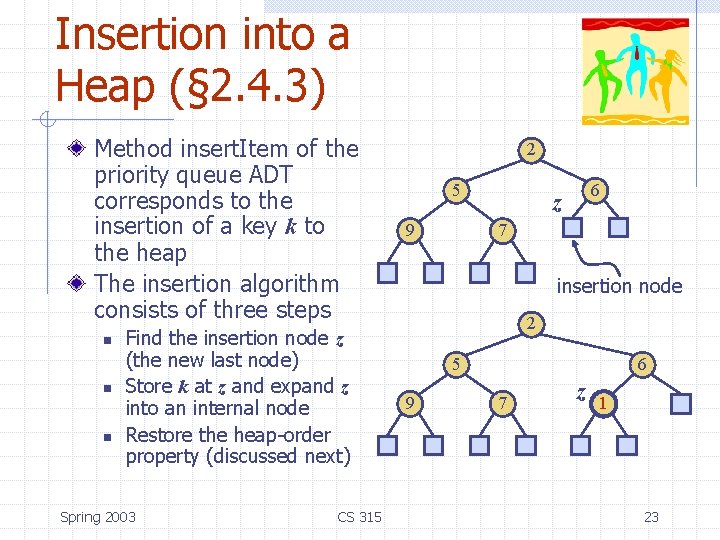
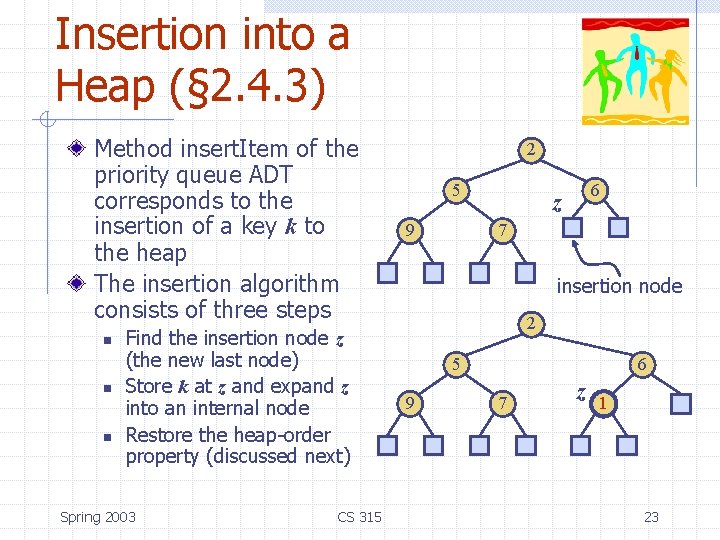
Insertion into a Heap (§ 2. 4. 3) Method insert. Item of the priority queue ADT corresponds to the insertion of a key k to the heap The insertion algorithm consists of three steps n n n Find the insertion node z (the new last node) Store k at z and expand z into an internal node Restore the heap-order property (discussed next) Spring 2003 CS 315 2 5 9 6 z 7 insertion node 2 5 9 6 7 z 1 23
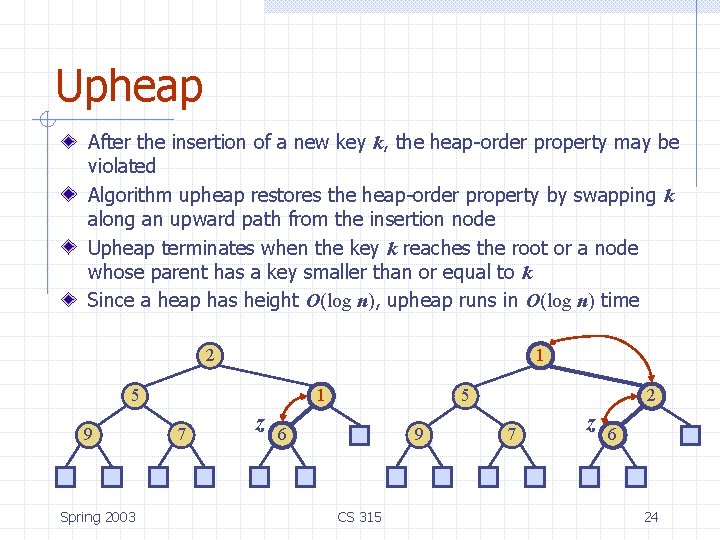
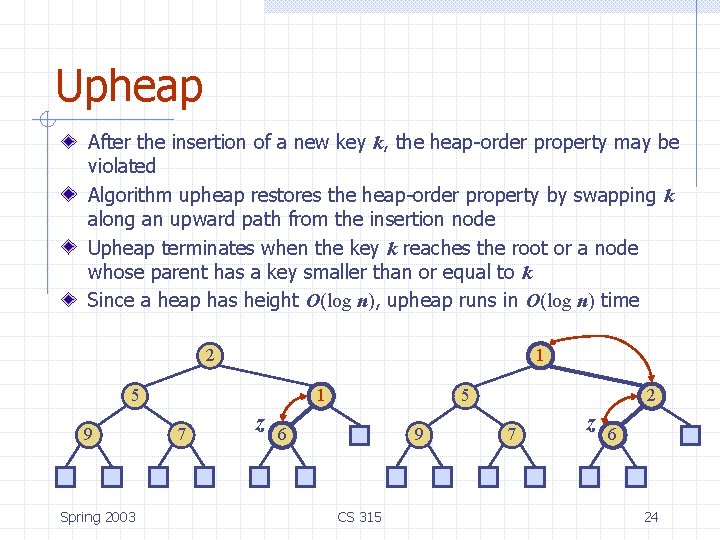
Upheap After the insertion of a new key k, the heap-order property may be violated Algorithm upheap restores the heap-order property by swapping k along an upward path from the insertion node Upheap terminates when the key k reaches the root or a node whose parent has a key smaller than or equal to k Since a heap has height O(log n), upheap runs in O(log n) time 2 1 5 9 Spring 2003 1 7 z 5 6 9 CS 315 2 7 z 6 24
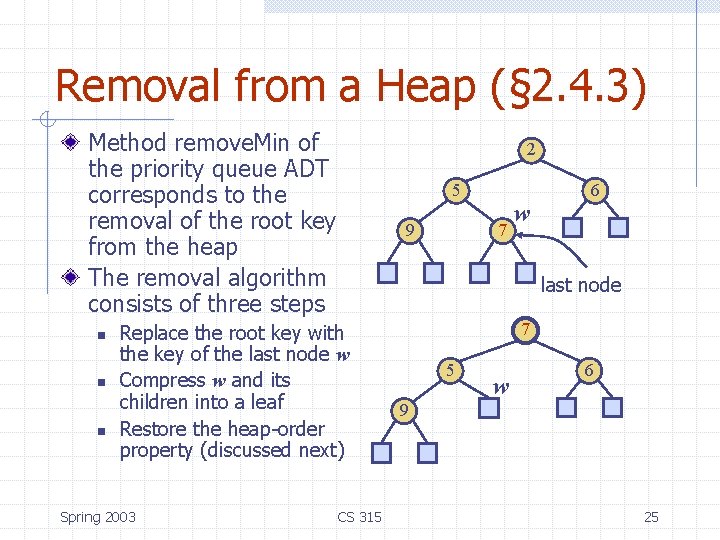
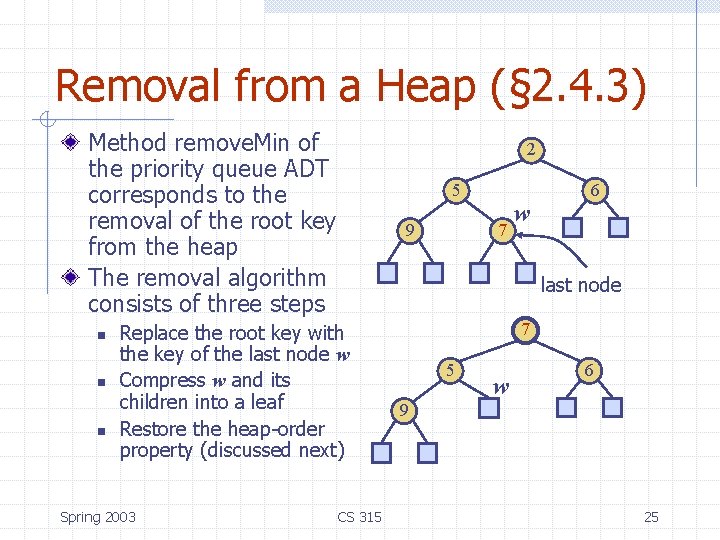
Removal from a Heap (§ 2. 4. 3) Method remove. Min of the priority queue ADT corresponds to the removal of the root key from the heap The removal algorithm consists of three steps n n n 2 5 9 7 w last node Replace the root key with the key of the last node w Compress w and its children into a leaf Restore the heap-order property (discussed next) Spring 2003 6 CS 315 7 5 w 6 9 25
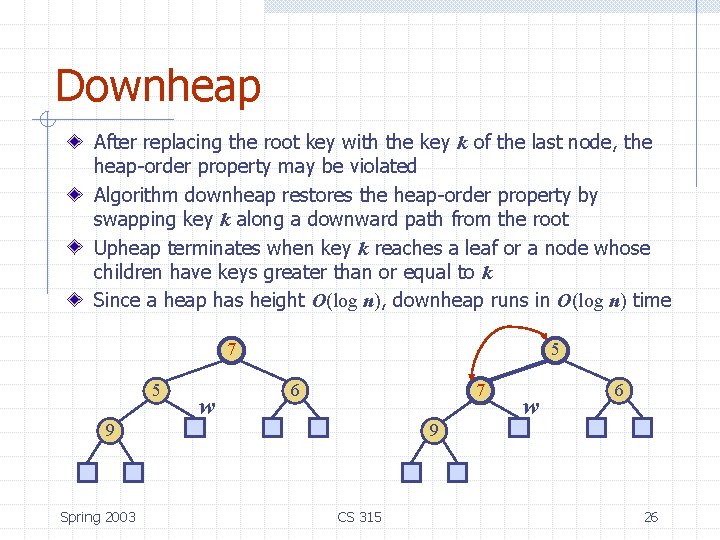
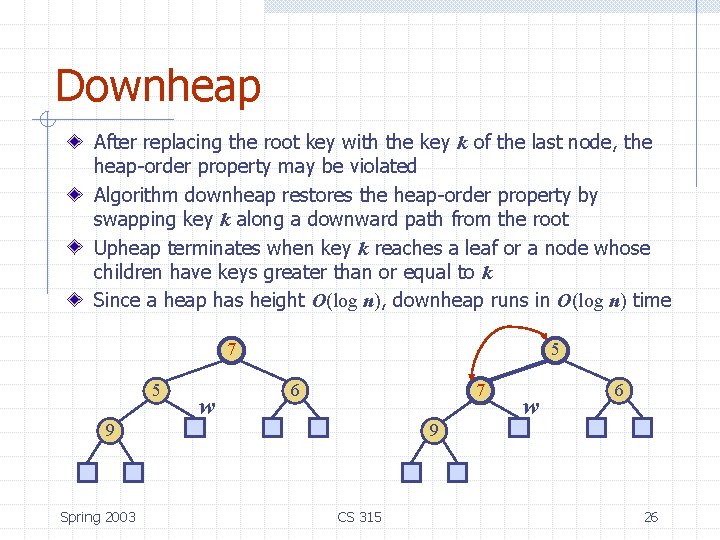
Downheap After replacing the root key with the key k of the last node, the heap-order property may be violated Algorithm downheap restores the heap-order property by swapping key k along a downward path from the root Upheap terminates when key k reaches a leaf or a node whose children have keys greater than or equal to k Since a heap has height O(log n), downheap runs in O(log n) time 7 5 w 5 6 7 9 Spring 2003 w 6 9 CS 315 26
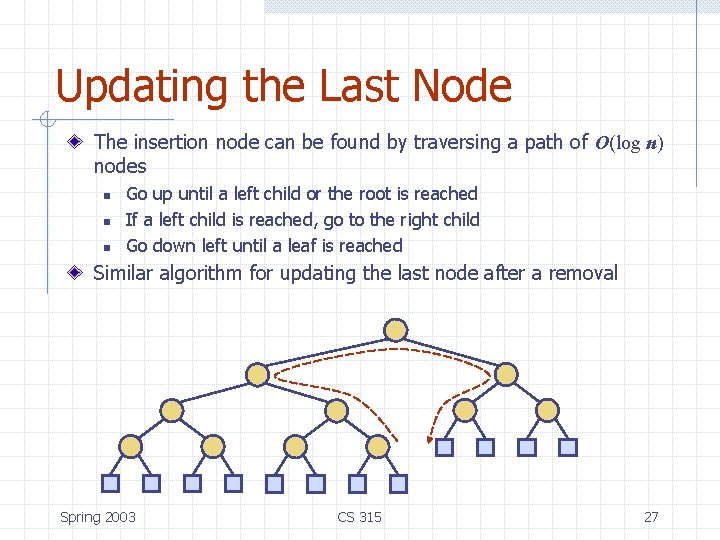
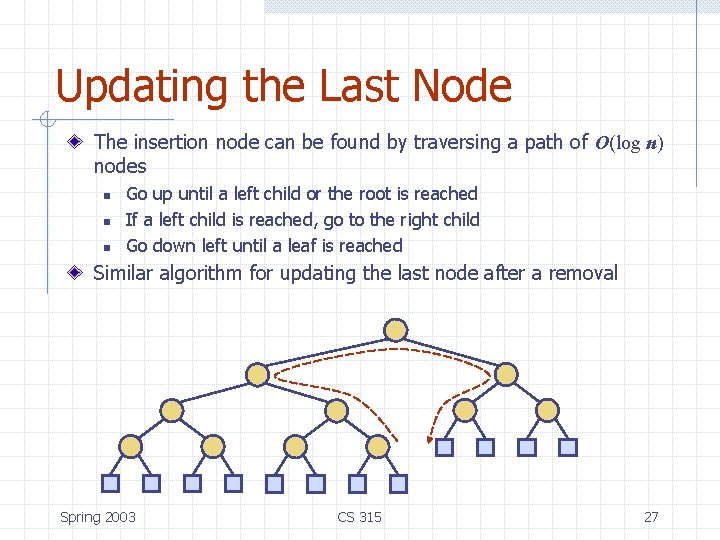
Updating the Last Node The insertion node can be found by traversing a path of O(log n) nodes n n n Go up until a left child or the root is reached If a left child is reached, go to the right child Go down left until a leaf is reached Similar algorithm for updating the last node after a removal Spring 2003 CS 315 27
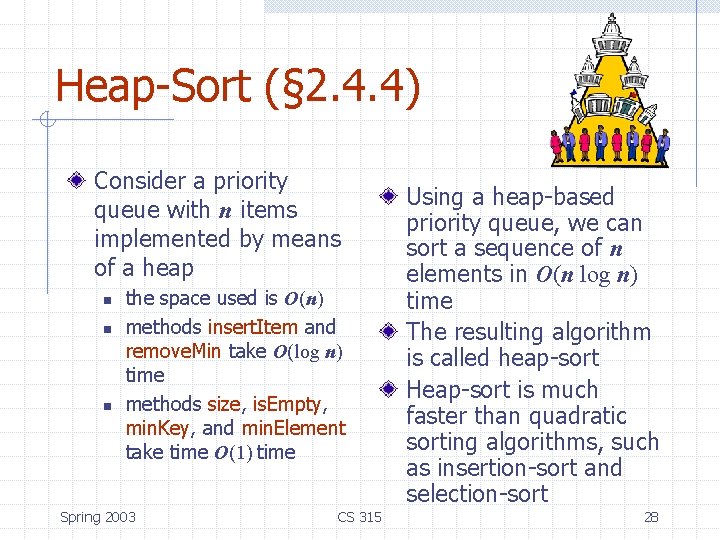
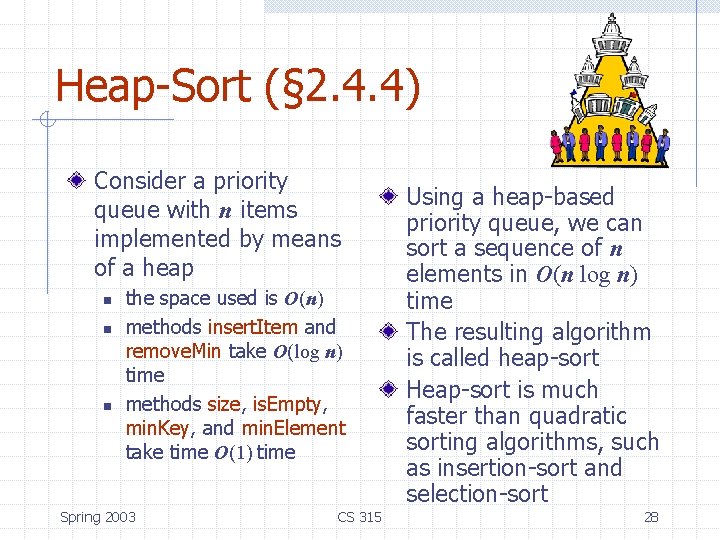
Heap-Sort (§ 2. 4. 4) Consider a priority queue with n items implemented by means of a heap n n n the space used is O(n) methods insert. Item and remove. Min take O(log n) time methods size, is. Empty, min. Key, and min. Element take time O(1) time Spring 2003 CS 315 Using a heap-based priority queue, we can sort a sequence of n elements in O(n log n) time The resulting algorithm is called heap-sort Heap-sort is much faster than quadratic sorting algorithms, such as insertion-sort and selection-sort 28
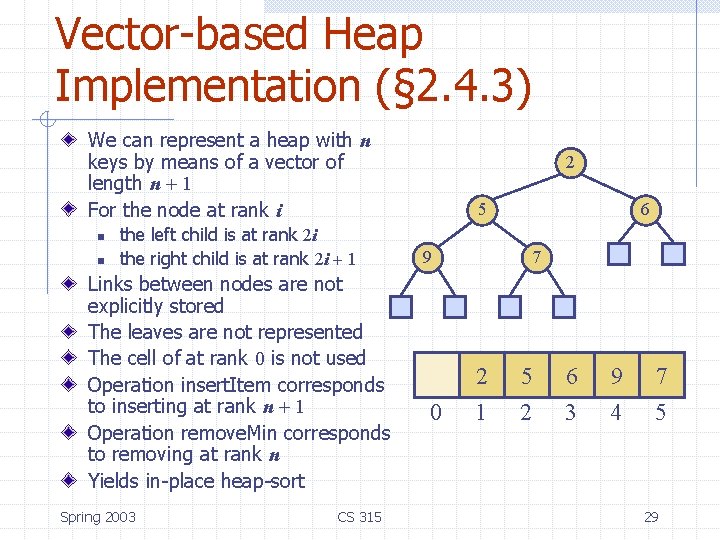
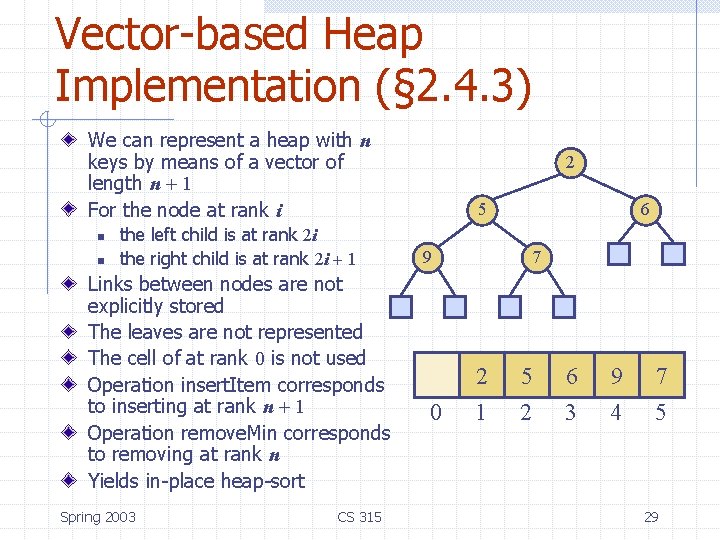
Vector-based Heap Implementation (§ 2. 4. 3) We can represent a heap with n keys by means of a vector of length n + 1 For the node at rank i n n the left child is at rank 2 i the right child is at rank 2 i + 1 Links between nodes are not explicitly stored The leaves are not represented The cell of at rank 0 is not used Operation insert. Item corresponds to inserting at rank n + 1 Operation remove. Min corresponds to removing at rank n Yields in-place heap-sort Spring 2003 CS 315 2 5 6 9 0 7 2 5 6 9 7 1 2 3 4 5 29
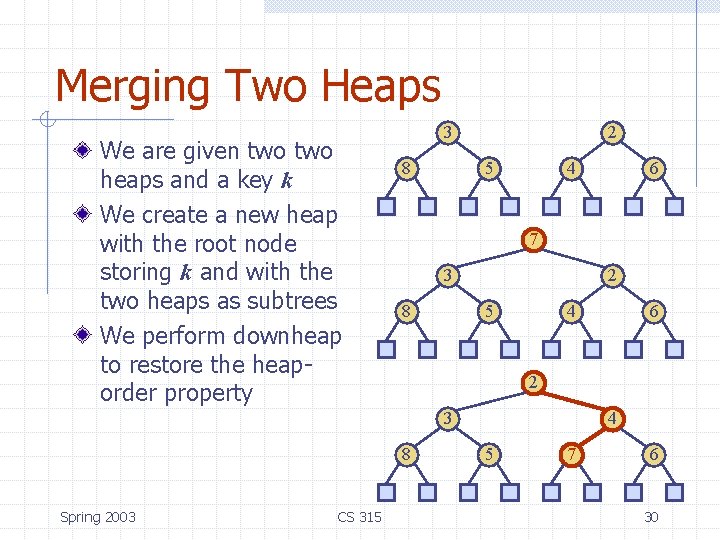
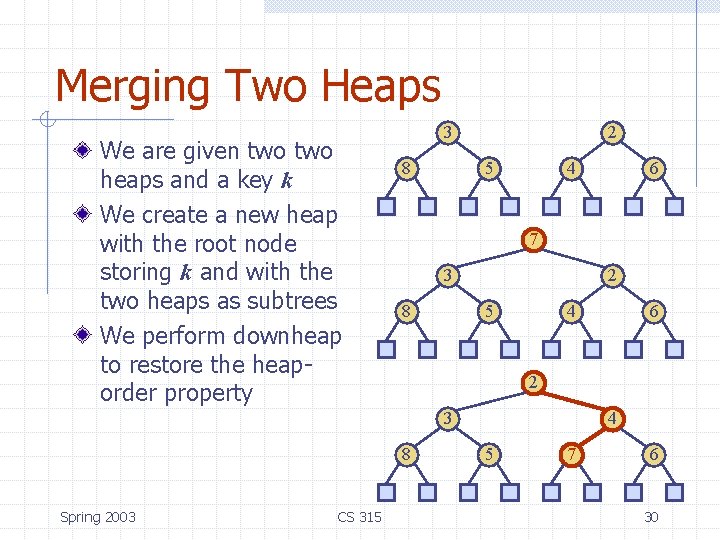
Merging Two Heaps We are given two heaps and a key k We create a new heap with the root node storing k and with the two heaps as subtrees We perform downheap to restore the heaporder property 3 8 2 5 4 7 3 8 2 5 4 8 CS 315 6 2 3 Spring 2003 6 4 5 7 6 30
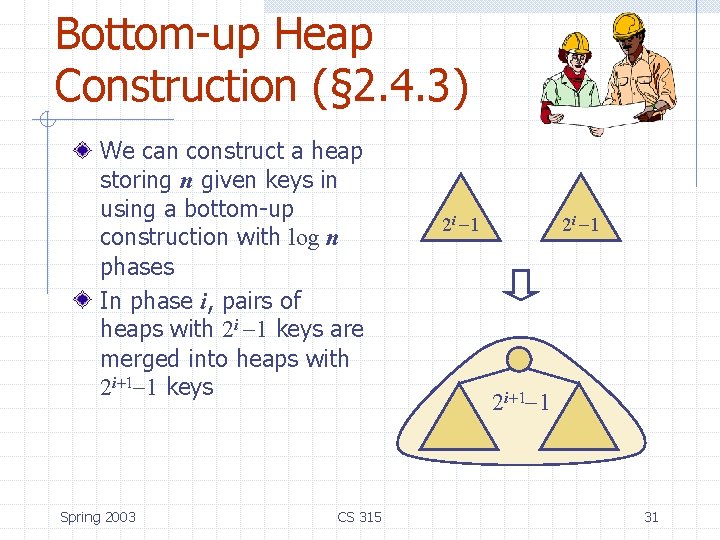
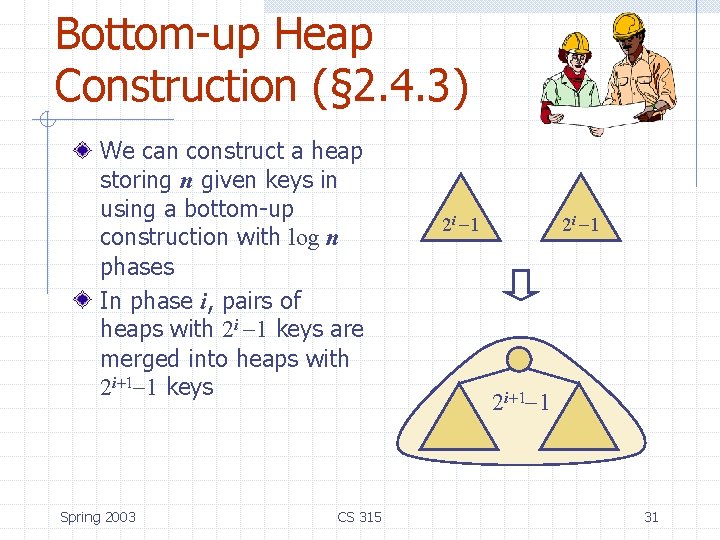
Bottom-up Heap Construction (§ 2. 4. 3) We can construct a heap storing n given keys in using a bottom-up construction with log n phases In phase i, pairs of heaps with 2 i -1 keys are merged into heaps with 2 i+1 -1 keys Spring 2003 CS 315 2 i -1 2 i+1 -1 31
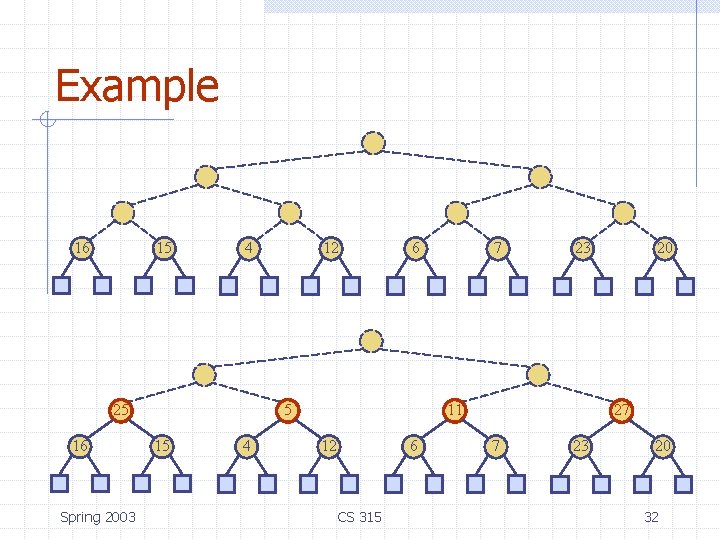
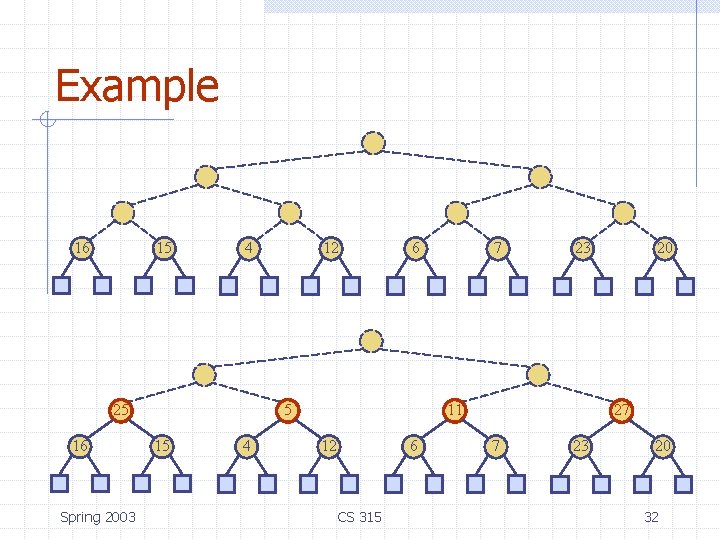
Example 16 15 4 25 16 Spring 2003 12 6 5 15 4 7 23 11 12 6 CS 315 20 27 7 23 20 32
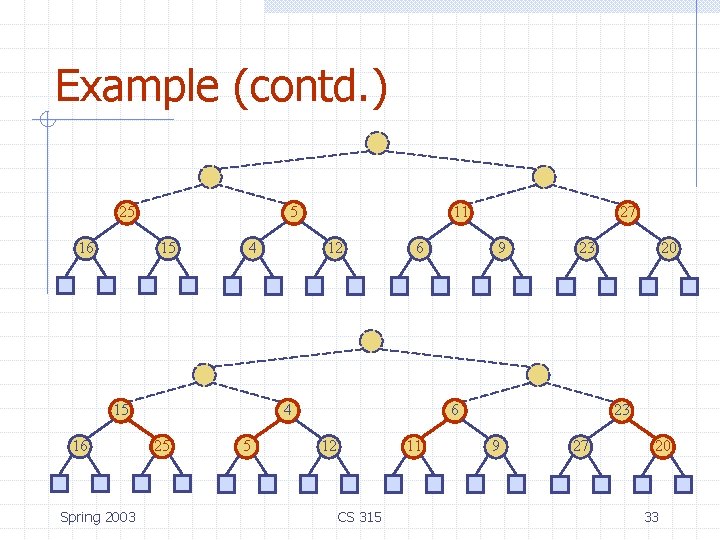
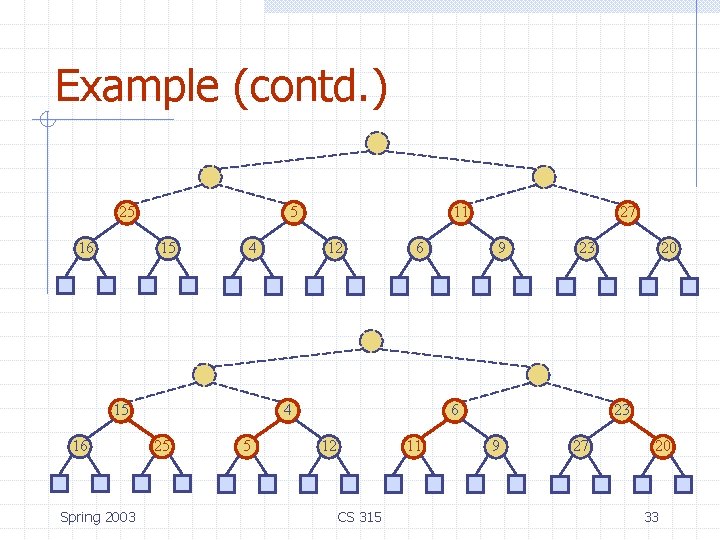
Example (contd. ) 25 16 5 15 4 15 16 Spring 2003 11 12 6 4 25 5 27 9 23 6 12 11 CS 315 20 23 9 27 20 33
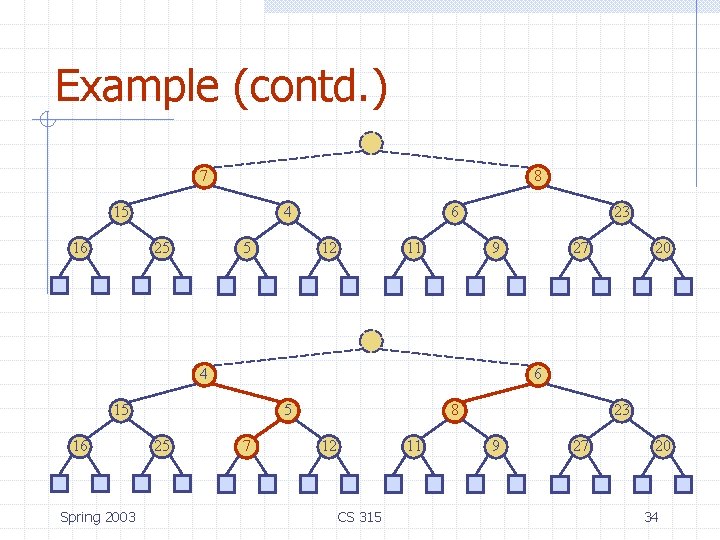
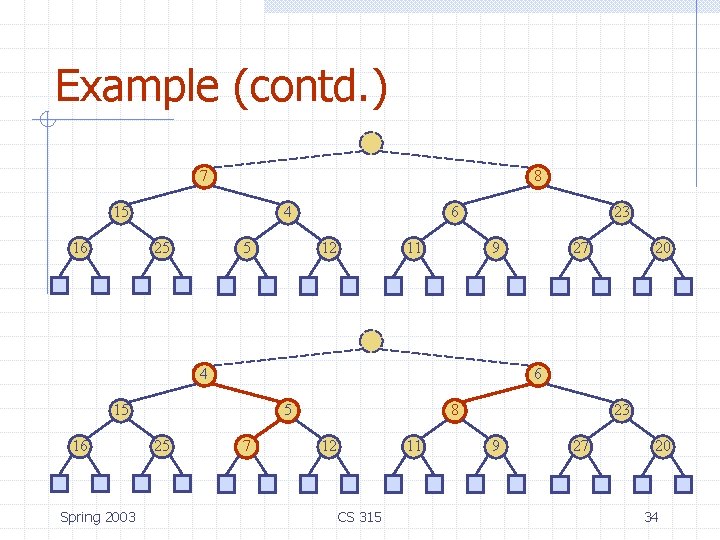
Example (contd. ) 7 8 15 16 4 25 5 6 12 11 23 9 4 Spring 2003 5 25 20 6 15 16 27 7 8 12 11 CS 315 23 9 27 20 34
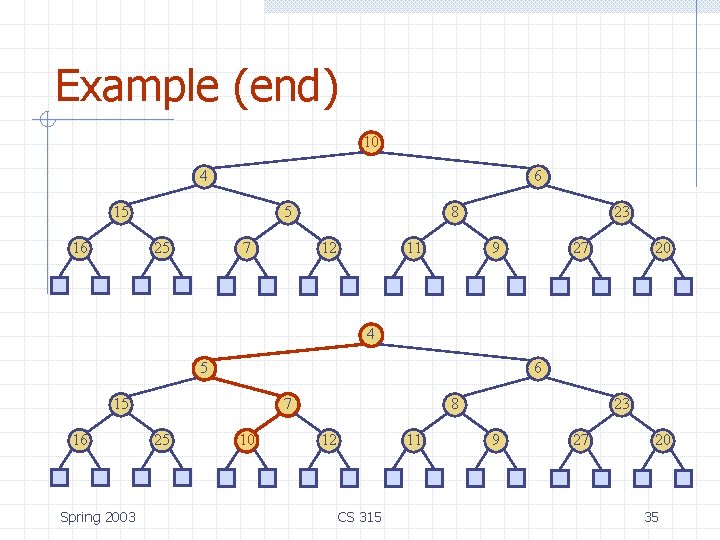
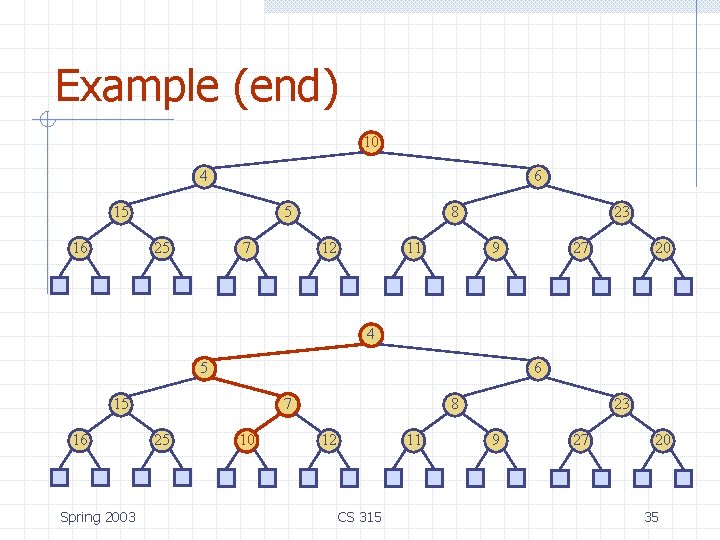
Example (end) 10 4 6 15 16 5 25 7 8 12 11 23 9 27 20 4 5 6 15 16 Spring 2003 7 25 10 8 12 11 CS 315 23 9 27 20 35
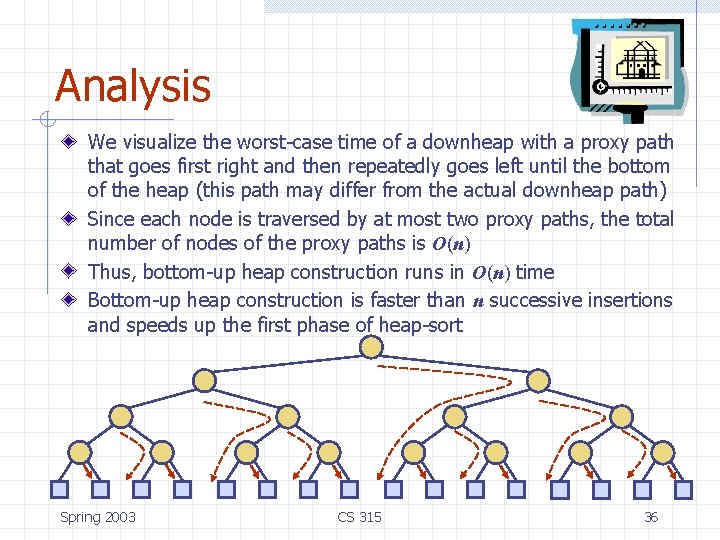
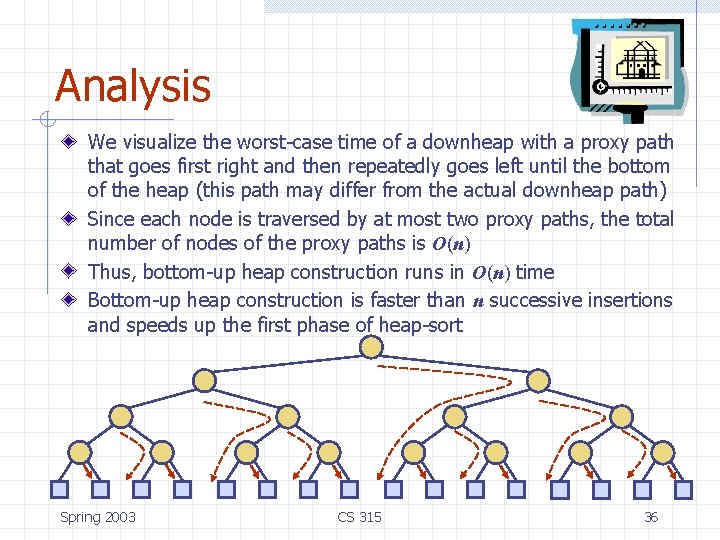
Analysis We visualize the worst-case time of a downheap with a proxy path that goes first right and then repeatedly goes left until the bottom of the heap (this path may differ from the actual downheap path) Since each node is traversed by at most two proxy paths, the total number of nodes of the proxy paths is O(n) Thus, bottom-up heap construction runs in O(n) time Bottom-up heap construction is faster than n successive insertions and speeds up the first phase of heap-sort Spring 2003 CS 315 36
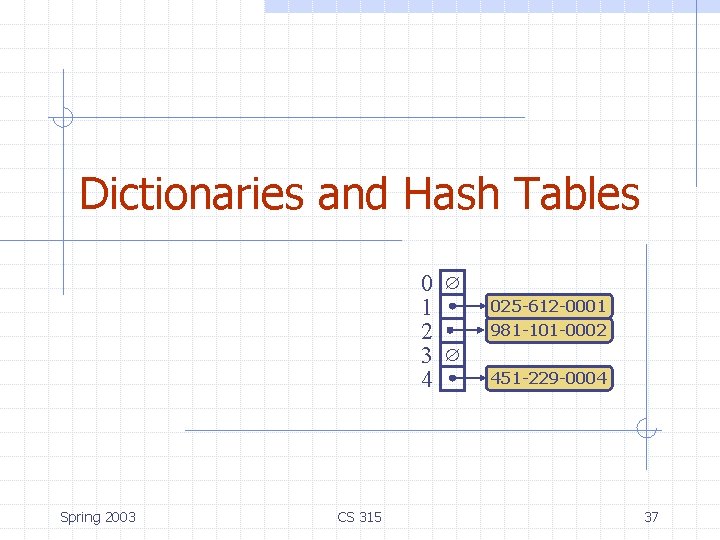
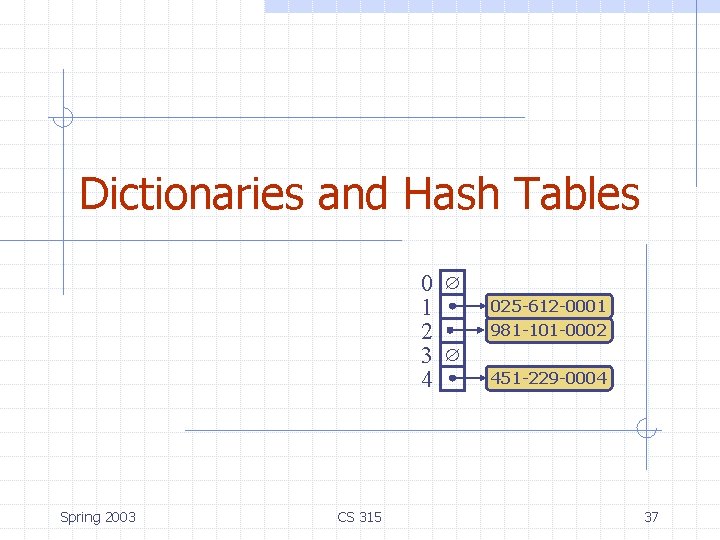
Dictionaries and Hash Tables 0 1 2 3 4 Spring 2003 CS 315 025 -612 -0001 981 -101 -0002 451 -229 -0004 37
Dictionary ADT (§ 2. 5. 1) The dictionary ADT models a searchable collection of keyelement items The main operations of a dictionary are searching, inserting, and deleting items Multiple items with the same key are allowed Applications: n n n address book credit card authorization mapping host names (e. g. , cs 16. net) to internet addresses (e. g. , 128. 148. 34. 101) Dictionary ADT methods: n n n Spring 2003 CS 315 find. Element(k): if the dictionary has an item with key k, returns its element, else, returns the special element NO_SUCH_KEY insert. Item(k, o): inserts item (k, o) into the dictionary remove. Element(k): if the dictionary has an item with key k, removes it from the dictionary and returns its element, else returns the special element NO_SUCH_KEY size(), is. Empty() keys(), Elements() 38
Log File (§ 2. 5. 1) A log file is a dictionary implemented by means of an unsorted sequence n We store the items of the dictionary in a sequence (based on a doubly-linked lists or a circular array), in arbitrary order Performance: n n insert. Item takes O(1) time since we can insert the new item at the beginning or at the end of the sequence find. Element and remove. Element take O(n) time since in the worst case (the item is not found) we traverse the entire sequence to look for an item with the given key The log file is effective only for dictionaries of small size or for dictionaries on which insertions are the most common operations, while searches and removals are rarely performed (e. g. , historical record of logins to a workstation) Spring 2003 CS 315 39
Hash Functions and Hash Tables (§ 2. 5. 2) The basic idea: searching through the entries in a log file can be time consuming. Is there a better way? Hash codes, hash functions, and hash tables are one solution. The idea: place dictionary entries in “buckets” (based on keys) in such as way that the entries of the dictionary are relatively evenly spread throughout the buckets. To access an entry, use the key to find the correct bucket. Presumably searching the bucket is quicker than searching through an entire log file. Spring 2003 CS 315 40
Hash Functions and Hash Tables (§ 2. 5. 2) What does this entail? n Need an efficient way to map keys “evenly” to buckets. The method: First, map keys to integers. The function that does this is called a hash code, and the integer output of such a mapping can be called the hash code for the original key n Want to avoid having more than one key mapped to same integer (called a collision) Next, use another mapping, called a compression map, to map the hash codes to buckets. n The hash codes may vary considerably. That is, they may have a wide range of values, the use of the term compression. The composition of the two operations, that is, the map from keys to buckets, is called a hash function. Spring 2003 CS 315 41
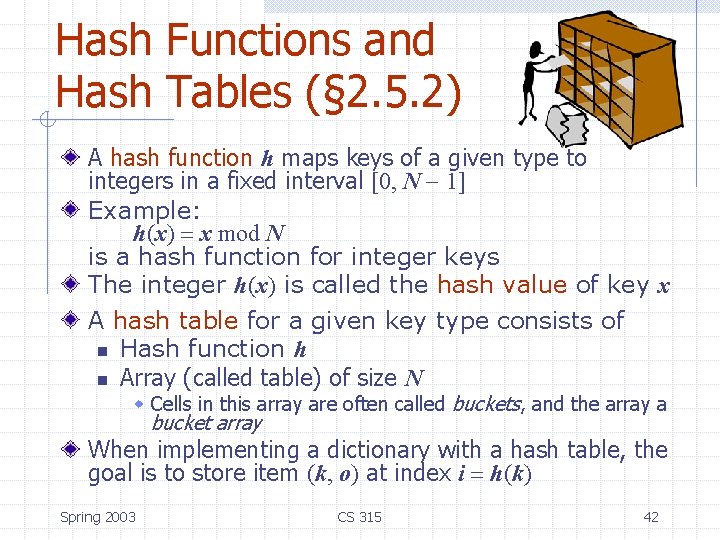
Hash Functions and Hash Tables (§ 2. 5. 2) A hash function h maps keys of a given type to integers in a fixed interval [0, N - 1] Example: h(x) = x mod N is a hash function for integer keys The integer h(x) is called the hash value of key x A hash table for a given key type consists of n Hash function h n Array (called table) of size N w Cells in this array are often called buckets, and the array a bucket array When implementing a dictionary with a hash table, the goal is to store item (k, o) at index i = h(k) Spring 2003 CS 315 42
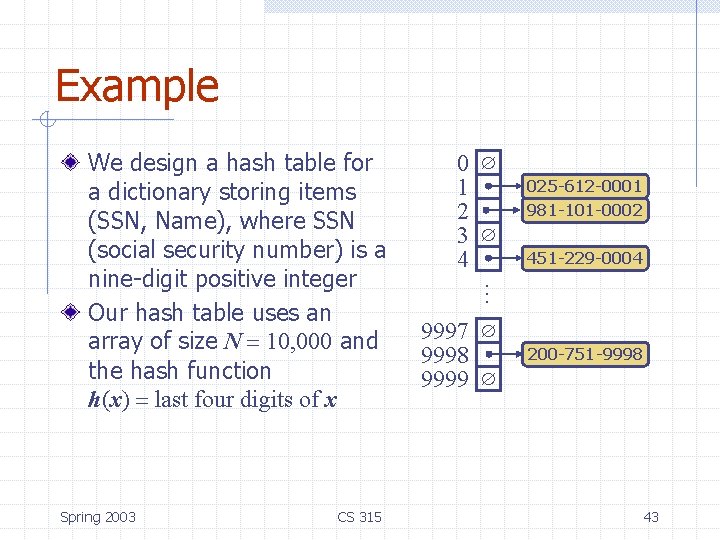
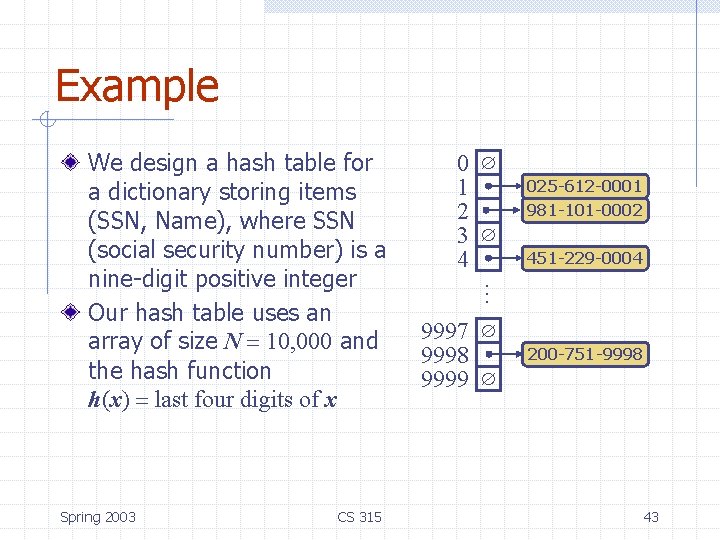
Example Spring 2003 CS 315 0 1 2 3 4 025 -612 -0001 981 -101 -0002 451 -229 -0004 … We design a hash table for a dictionary storing items (SSN, Name), where SSN (social security number) is a nine-digit positive integer Our hash table uses an array of size N = 10, 000 and the hash function h(x) = last four digits of x 9997 9998 9999 200 -751 -9998 43
Again… A hash function is usually specified as the composition of two functions: Hash code map: h 1: keys integers Compression map: h 2: integers [0, N - 1] Spring 2003 CS 315 The hash code map is applied first, and the compression map is applied next on the result, i. e. , h(x) = h 2(h 1(x)) The goal of the hash function is to “disperse” the keys in an apparently random way 44
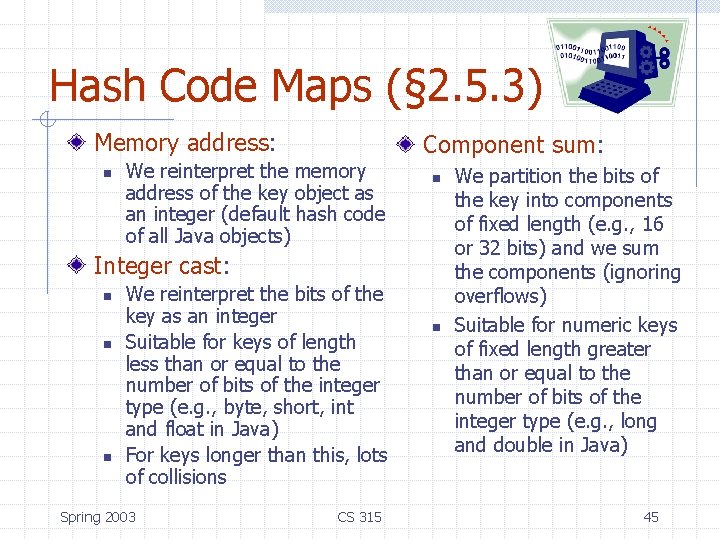
Hash Code Maps (§ 2. 5. 3) Memory address: n We reinterpret the memory address of the key object as an integer (default hash code of all Java objects) Component sum: n Integer cast: n n n We reinterpret the bits of the key as an integer Suitable for keys of length less than or equal to the number of bits of the integer type (e. g. , byte, short, int and float in Java) For keys longer than this, lots of collisions Spring 2003 CS 315 n We partition the bits of the key into components of fixed length (e. g. , 16 or 32 bits) and we sum the components (ignoring overflows) Suitable for numeric keys of fixed length greater than or equal to the number of bits of the integer type (e. g. , long and double in Java) 45
Hash Code Maps (cont. ) Polynomial accumulation: n n n We partition the bits of the key into a sequence of components of fixed length (e. g. , 8, 16 or 32 bits) a 0 a 1 … an-1 We evaluate the polynomial p(z) = a 0 + a 1 z + a 2 z 2 + … … + an-1 zn-1 at a fixed value z, ignoring overflows Especially suitable for strings (e. g. , the choice z = 33 gives at most 6 collisions on a set of 50, 000 English words) Spring 2003 CS 315 Polynomial p(z) can be evaluated in O(n) time using Horner’s rule For sake of speed, some implementations only apply polynomial has to fraction of the characters in a long string n E. g. every eight characters, etc. 46
Compression Maps Division: n n h 2 (y) = y mod N The size N of the hash table is usually chosen to be a prime The reason has to do with number theory and is beyond the scope of this course, but see right column… Even prime N will generate collisions under some recurring numerical patterns Spring 2003 CS 315 Here’s an example of what can happen: n n Consider the following hash codes (200, 205, 210, …, 600) A total of 80 codes Using N = 100, each code collides with three others Using N = 101 produces no collisions 47
Compression Maps Multiply, Add and Divide (MAD): n n n h 2 (y) = (ay + b) mod N a and b are nonnegative integers such that a mod N 0 Otherwise, every integer would map to the same value b Spring 2003 CS 315 The general rule: A well chosen hash function should guarantee that the probability of two different keys being hashed to the same bucket is no more than 1/N. 48
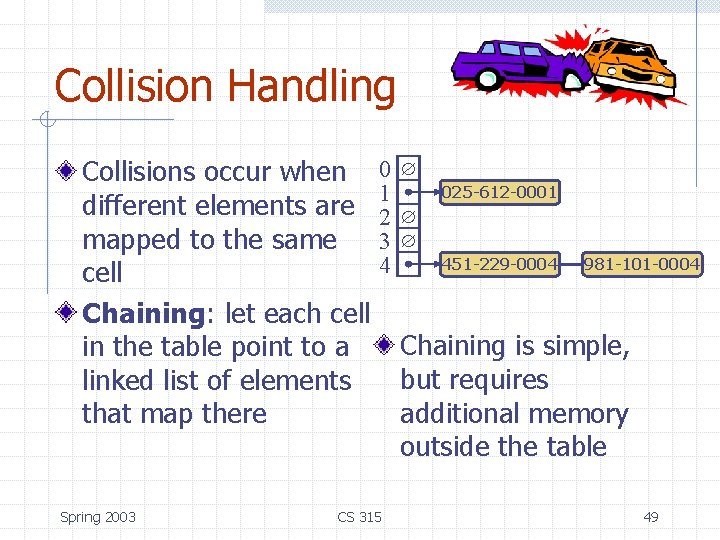
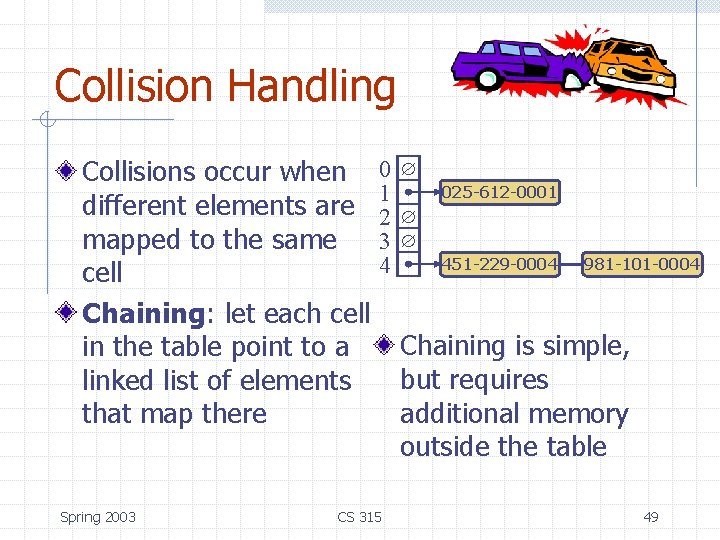
Collision Handling Collisions occur when 0 025 -612 -0001 1 different elements are 2 mapped to the same 3 451 -229 -0004 981 -101 -0004 4 cell Chaining: let each cell Chaining is simple, in the table point to a but requires linked list of elements additional memory that map there outside the table Spring 2003 CS 315 49
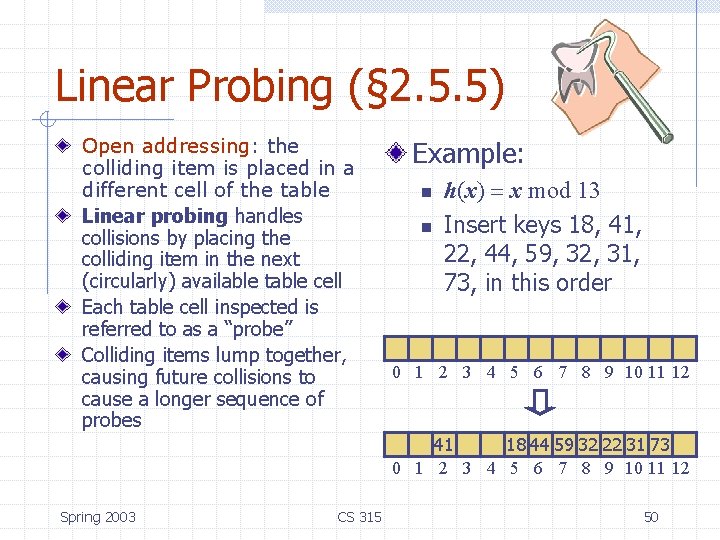
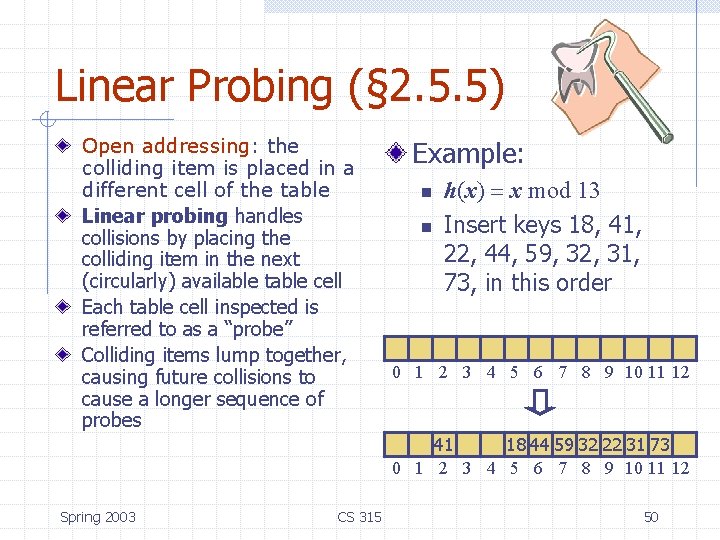
Linear Probing (§ 2. 5. 5) Open addressing: the colliding item is placed in a different cell of the table Linear probing handles collisions by placing the colliding item in the next (circularly) available table cell Each table cell inspected is referred to as a “probe” Colliding items lump together, causing future collisions to cause a longer sequence of probes Example: n n h(x) = x mod 13 Insert keys 18, 41, 22, 44, 59, 32, 31, 73, in this order 0 1 2 3 4 5 6 7 8 9 10 11 12 41 18 44 59 32 22 31 73 0 1 2 3 4 5 6 7 8 9 10 11 12 Spring 2003 CS 315 50
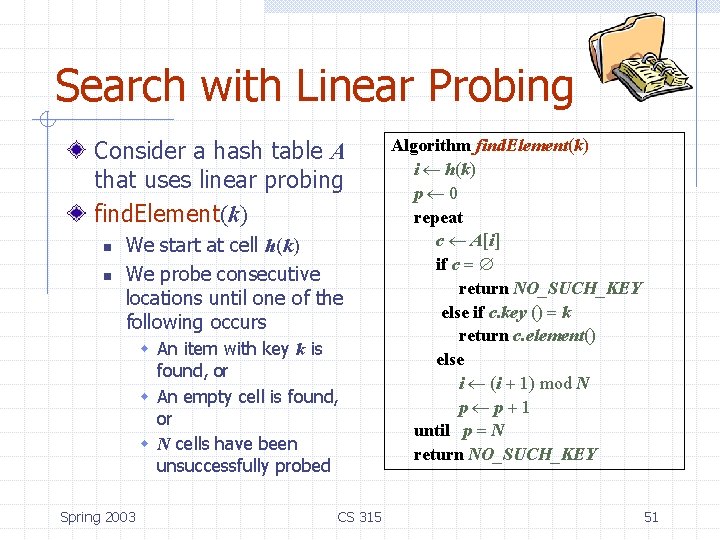
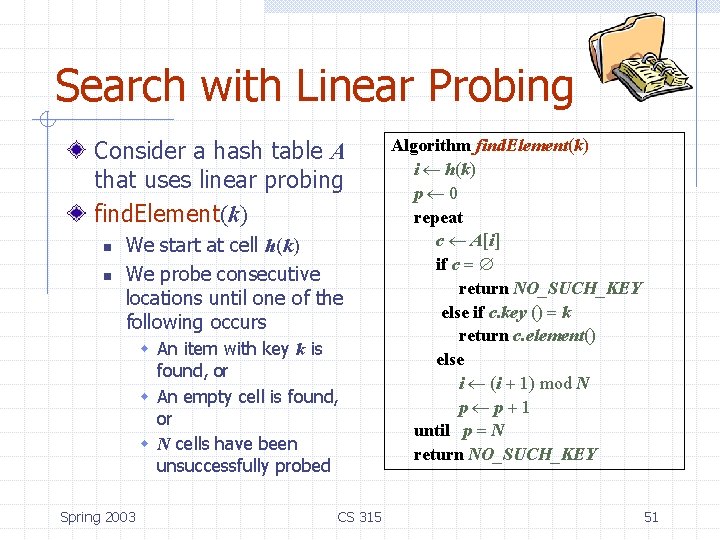
Search with Linear Probing Consider a hash table A that uses linear probing find. Element(k) n n We start at cell h(k) We probe consecutive locations until one of the following occurs w An item with key k is found, or w An empty cell is found, or w N cells have been unsuccessfully probed Spring 2003 CS 315 Algorithm find. Element(k) i h(k) p 0 repeat c A[i] if c = return NO_SUCH_KEY else if c. key () = k return c. element() else i (i + 1) mod N p p+1 until p = N return NO_SUCH_KEY 51
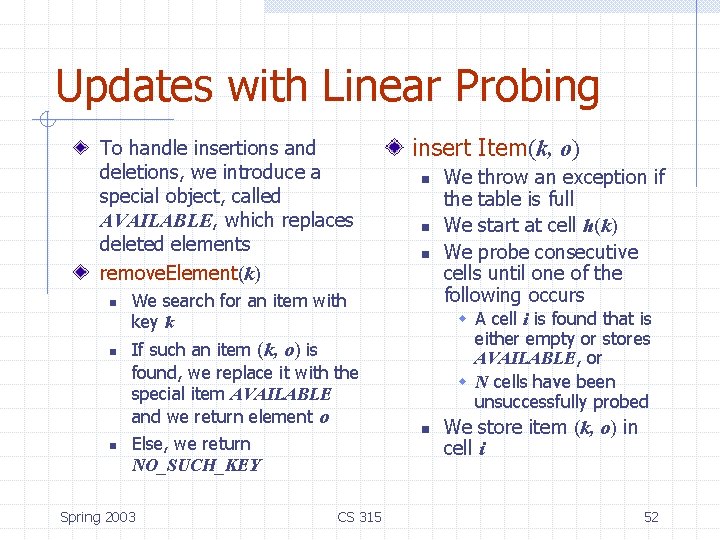
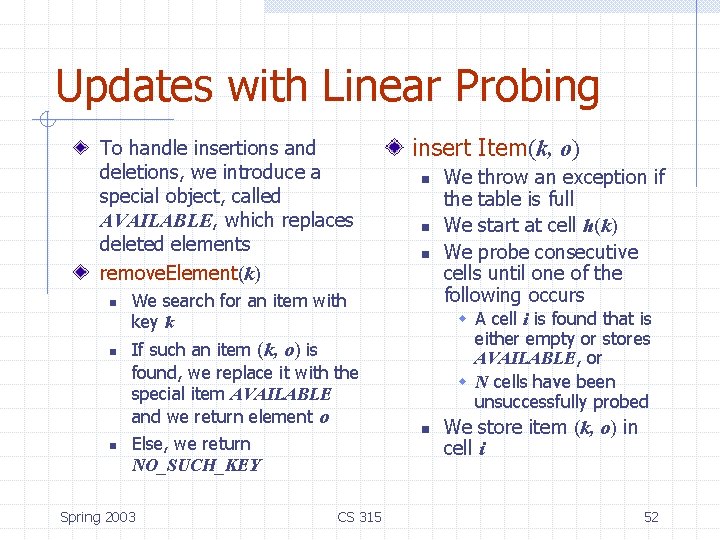
Updates with Linear Probing To handle insertions and deletions, we introduce a special object, called AVAILABLE, which replaces deleted elements remove. Element(k) n n n insert Item(k, o) n n n We search for an item with key k If such an item (k, o) is found, we replace it with the special item AVAILABLE and we return element o Else, we return NO_SUCH_KEY Spring 2003 CS 315 We throw an exception if the table is full We start at cell h(k) We probe consecutive cells until one of the following occurs w A cell i is found that is either empty or stores AVAILABLE, or w N cells have been unsuccessfully probed n We store item (k, o) in cell i 52
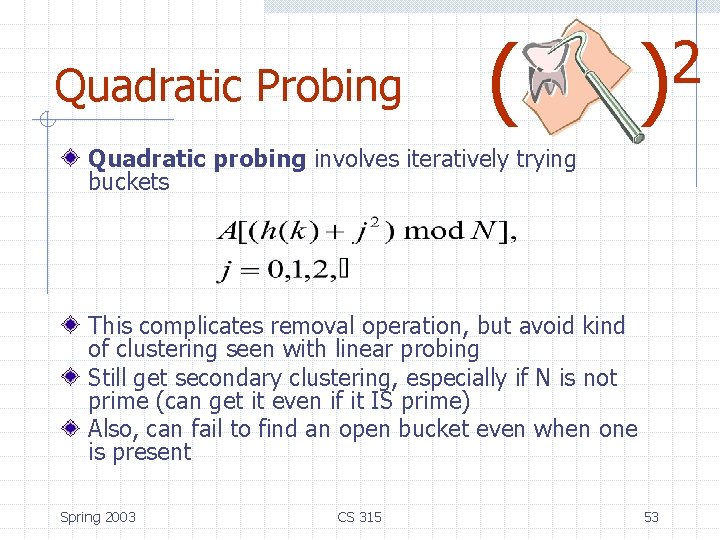
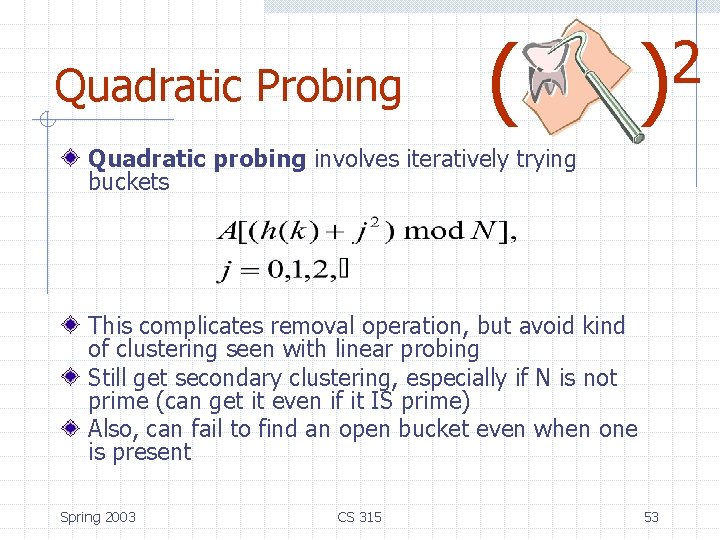
Quadratic Probing ( 2 ) Quadratic probing involves iteratively trying buckets This complicates removal operation, but avoid kind of clustering seen with linear probing Still get secondary clustering, especially if N is not prime (can get it even if it IS prime) Also, can fail to find an open bucket even when one is present Spring 2003 CS 315 53
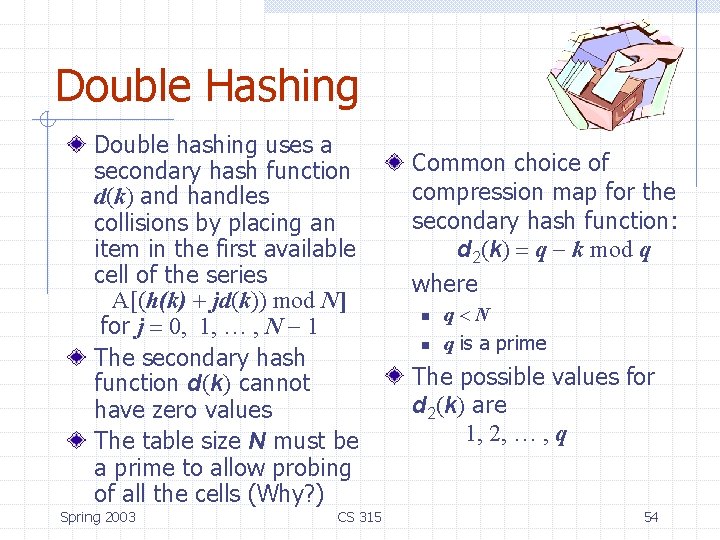
Double Hashing Double hashing uses a secondary hash function d(k) and handles collisions by placing an item in the first available cell of the series A[(h(k) + jd(k)) mod N] for j = 0, 1, … , N - 1 The secondary hash function d(k) cannot have zero values The table size N must be a prime to allow probing of all the cells (Why? ) Spring 2003 CS 315 Common choice of compression map for the secondary hash function: d 2(k) = q - k mod q where n n q<N q is a prime The possible values for d 2(k) are 1, 2, … , q 54
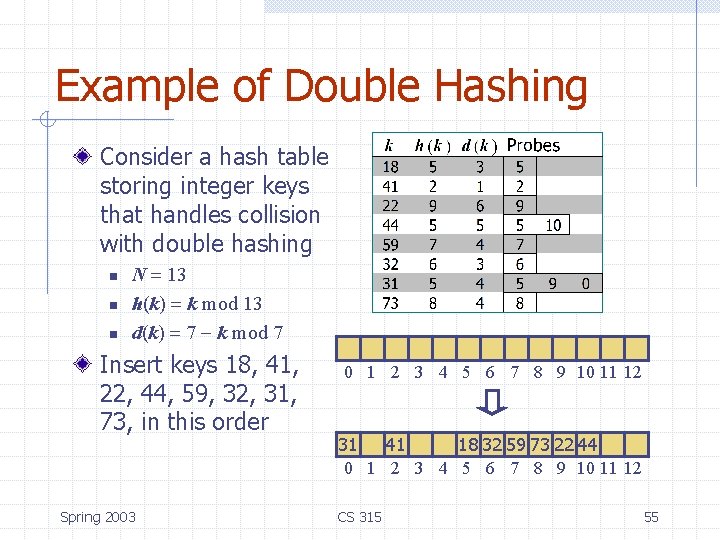
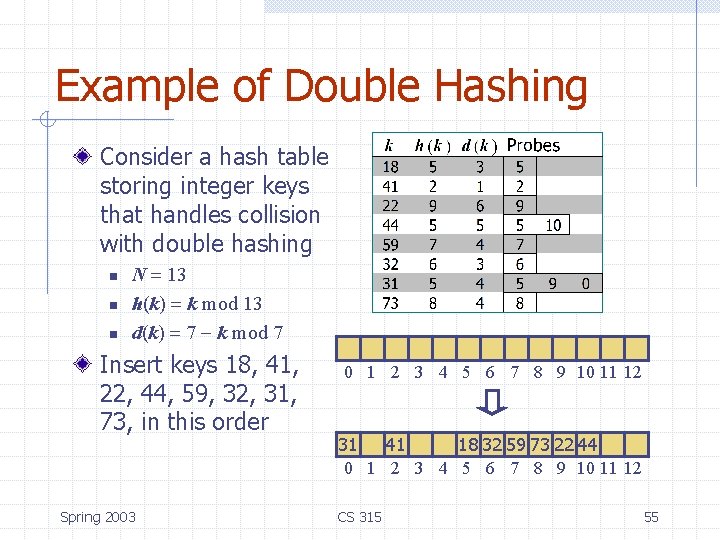
Example of Double Hashing Consider a hash table storing integer keys that handles collision with double hashing n n n N = 13 h(k) = k mod 13 d(k) = 7 - k mod 7 Insert keys 18, 41, 22, 44, 59, 32, 31, 73, in this order Spring 2003 0 1 2 3 4 5 6 7 8 9 10 11 12 31 41 18 32 59 73 22 44 0 1 2 3 4 5 6 7 8 9 10 11 12 CS 315 55
Performance of Hashing In the worst case, searches, insertions and removals on a hash table take O(n) time The worst case occurs when all the keys inserted into the dictionary collide The load factor a = n/N affects the performance of a hash table (load factor is expected size of each bucket) The expected running time of all the dictionary ADT operations in a hash table is O(1) In practice, hashing is very fast provided the load factor is not close to 100% Applications of hash tables: n n n Spring 2003 CS 315 small databases compilers browser caches 56
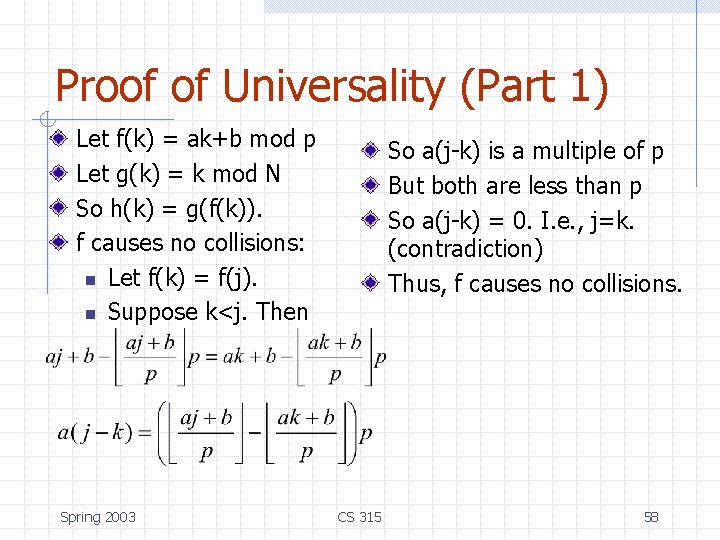
Universal Hashing A family of hash functions is universal if, for any 0<i, j<M-1, Pr(h(j)=h(k)) < 1/N. Choose p as a prime between M and 2 M. Randomly select 0<a<p and 0<b<p, and define h(k)=(ak+b mod p) mod N Spring 2003 CS 315 Theorem: The set of all functions, h, as defined here, is universal. 57
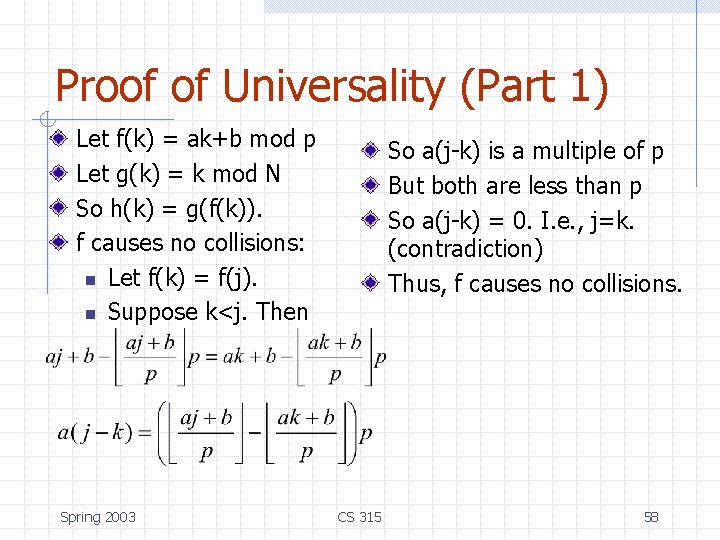
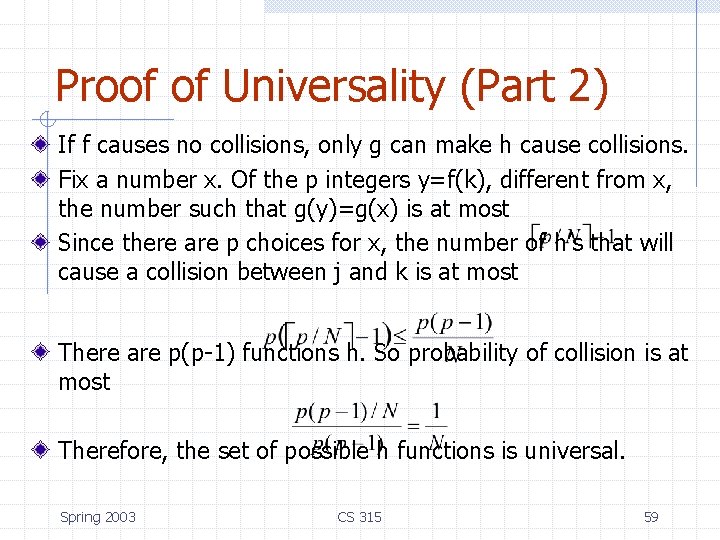
Proof of Universality (Part 1) Let f(k) = ak+b mod p Let g(k) = k mod N So h(k) = g(f(k)). f causes no collisions: n Let f(k) = f(j). n Suppose k<j. Then Spring 2003 So a(j-k) is a multiple of p But both are less than p So a(j-k) = 0. I. e. , j=k. (contradiction) Thus, f causes no collisions. CS 315 58
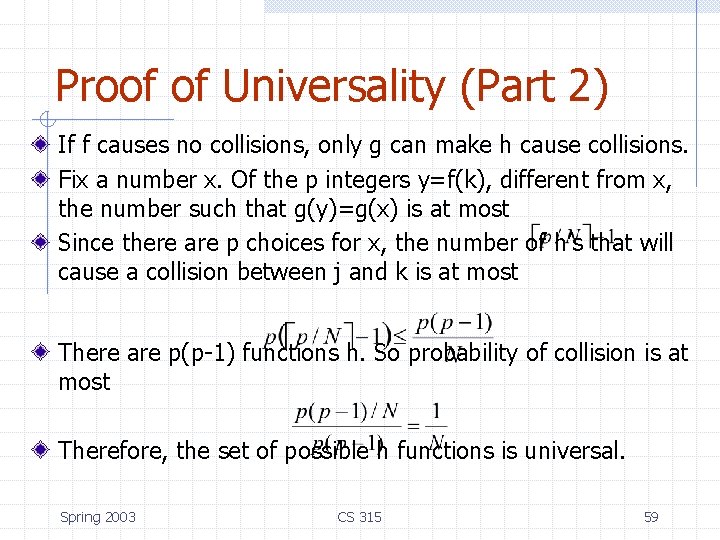
Proof of Universality (Part 2) If f causes no collisions, only g can make h cause collisions. Fix a number x. Of the p integers y=f(k), different from x, the number such that g(y)=g(x) is at most Since there are p choices for x, the number of h’s that will cause a collision between j and k is at most There are p(p-1) functions h. So probability of collision is at most Therefore, the set of possible h functions is universal. Spring 2003 CS 315 59