Chapter 2 Basic Encryption and Decryption csci 5233
Chapter 2 Basic Encryption and Decryption csci 5233 computer security & integrity
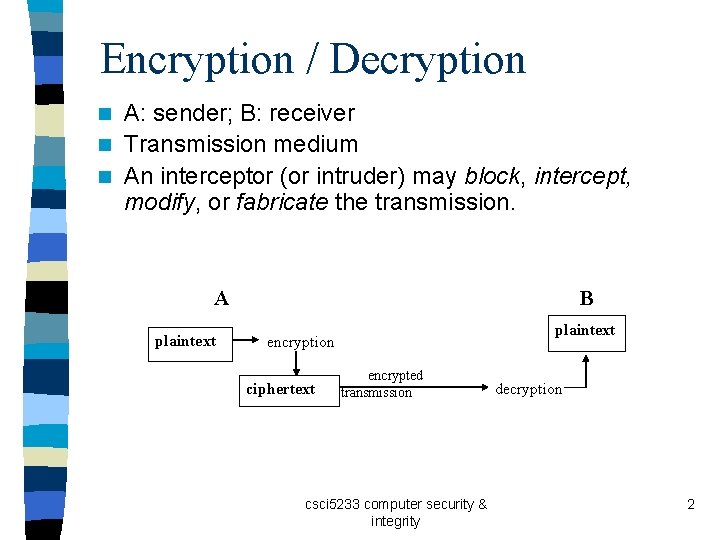
Encryption / Decryption A: sender; B: receiver n Transmission medium n An interceptor (or intruder) may block, intercept, modify, or fabricate the transmission. n B A plaintext encryption ciphertext encrypted transmission csci 5233 computer security & integrity decryption 2
Encryption / Decryption n Encryption: A process of encoding a message, so that its meaning is not obvious. (= encoding, enciphering) n Decryption: A process of decoding an encrypted message back into its original form. (= decoding, deciphering) n A cryptosystem is a system for encryption and decryption. csci 5233 computer security & integrity 3
Plaintext / ciphertext n P: plaintext n C: ciphertext n E: encryption n D: decryption n C = E (P) n P = D (C) n P = D ( E(P) ) csci 5233 computer security & integrity 4
Cryptosystems n Symmetric encryption: P = D (Key, E(Key, P) ) n Asymmetric encryption: P = D (Key. D, E(Key. E, P) ) n Symmetric cryptosystem: A cryptosystem that uses symmetric encryption. n Asymmetric cryptosystem n See Fig. 2 -2 (p. 23) csci 5233 computer security & integrity 5
Keys n Use of a key provides additional security. n Exposure of the encryption algorithm does not expose the future messages< as long as the key(s) are kept secret. n c. f. , keyless cipher csci 5233 computer security & integrity 6
Terminology n Cryptography: The practice of using encryption to conceal text. (cryptographer) n Cryptanalysis: The study of encryption and encrypted messages, with the goal of finding the hidden meanings of the messages. (cryptanalyst) n Cryptology = cryptography + cryptanalysis csci 5233 computer security & integrity 7
Cryptanalysis n A cryptanalyst may work with various data (intercepted messages, data items known or suspected to be in a ciphertext message), known encryption algorithms, mathematical or statistical tools and techniques, properties of languages, computers, and plenty of ingenuity and luck. 1. Attempt to break a single message 2. Attempt to recognize patterns in encrypted messages 3. Attempt to find general weakness in an encryption algorithm csci 5233 computer security & integrity 8
Breakability of an encryption An encryption algorithm may be breakable, meaning that given enough time and data, an analyst could determine the algorithm. n Suppose there exists 1030 possible decipherments for a given cipher scheme. A computer performs 1010 operations per second. Finding the decipherment would require 1020 seconds (or roughly 1012 years). n csci 5233 computer security & integrity 9
Modular arithmetic n. A . . Z: 0. . 25 n Example: p. 24 C = P mod 26 csci 5233 computer security & integrity 10
Two forms of encryption n Substitutions One letter is exchanged for another Examples: monoalphabetic substitution ciphers, polyalphabetic substitution ciphers n Transpositions (= permutations) The order of the letters is rearranged Examples: columnar transpositions csci 5233 computer security & integrity 11
Substitutions n Caesar cipher: Each letter is translated to the letter a fixed number of letters after it in the alphabet. Ci = E(Pi) = Pi + 3 n Advantage: simple n Weakness csci 5233 computer security & integrity 12
Cryptanalysis of the Caesar Cipher n Exercise (p. 26): Decrypt the encrypted message. n Deduction based on guesses versus frequency distribution (p. 28) csci 5233 computer security & integrity 13
Other monoalphabetic substitutions n Using permutation Pi (lambda) = 25 – lambda n Weakness: Double correspondence E(F) = u and D(u) = F n Using a key A key is a word that controls the ciphering. p. 27 csci 5233 computer security & integrity 14
Complexity of monoalphabetic substitutions n Monoalphabetic substitutions amount to table lookups. n The time to encrypt a message of n characters is proportional to n. csci 5233 computer security & integrity 15
Frequency distribution n Table 2 -1 (p. 29) shows the counts and relative frequencies of letters in English. n Frequencies in a sample cipher: Table 2 -2 (p. 30) n Compare the sample cipher against the normal frequency distribution: Fig. 2 -4 csci 5233 computer security & integrity 16
Polyalphabetic substitutions n By combining distributions that are high with the ones that are low n Using multiple substitution tables n Example (p. 32): table for odd positions, table for even positions csci 5233 computer security & integrity 17
Vigenère Tableaux n Table 2 -5: p. 34 n Example: p. 35 n Exercise: Complete the encryption of the original message. n Exercise: Decipher the encrypted message using the key (‘juliet’) csci 5233 computer security & integrity 18
Cryptanalysis of Polyalphabetic substitutions n The Kasiski method: a method to find the number of alphabets used for encryption n Works on duplicate fragments in the ciphertext n The distance between the repeated patterns must be a multiple of the keyword length csci 5233 computer security & integrity 19
Steps for the Kasiski method n p. 36 n Initial find + verification using frequency distribution csci 5233 computer security & integrity 20
Index of coincidence A measure of the variation between frequencies in a distribution n To measure the nonuniformity of a distribution n To rate how well a particular distribution matches the distribution of letters in English n RFreq versus Prob (p. 38) n Example: n – In the English language, RFreqa = Proba = 7. 49 (from Table 2. 1) – In the sample cipher in Table 2 -2 (p. 30): RFreqa = 0 Proba csci 5233 computer security & integrity 21
Index of Coincidence n n n Measure of roughness (or the variance): a measure of the size of the peaks and valleys (See Fig. 2 -6, p. 38) The var of a perfectly flat distribution = 0. The variance can be estimated by counting the number of pairs of identical letters and dividing by the total number of pairs possible – Example (Given 200 letters): 60 / 100 csci 5233 computer security & integrity 22
Index of Coincidence n IC (index of coincidence): a way to approximate variance from observed data (p. 39) n 0. 0384 (perfect) IC 0. 068 (English) csci 5233 computer security & integrity 23
Combined use of IC with Kasiski method n Bottom of p. 39 n All the subsets from the Kasiski method, if the key length was correct, should have distributions close to 0. 068. csci 5233 computer security & integrity 24
Analyzing a polyalphabetic cipher Use the Kasiski method to predict the likely numbers of enciphering alphabets. 2. Compute the IC to validate the predictions 3. (When 1 and 2 show promises) Generate subsets and calculate IC’s for the subsets 1. csci 5233 computer security & integrity 25
The “Perfect” Substitution Cipher n Use an infinite nonrepeating sequence of alphabets n A key with an infinite number of nonrepeating digits n Examples: one-time pads, the Vernam cipher, … csci 5233 computer security & integrity 26
Vernam Cipher n Sample function: c = ( p + random( ) ) mod 26 n Example: p. 42 n Binary Vernam Cipher p. 43: How would you decipher a ciphertext encrypted by Binary Vernam Cipher? Ans. : p = (c – random( ) ) mod 26 Example (p. 42): c = 19 (‘t’), random( ) = 76 p = (19 -76) mod 26 = 21 csci 5233 computer security & integrity 27
Random Number Generators A pseudo-random number generator is a computer program that generates numbers from a predictable, repeating sequence. n Example: The linear congruential random number generator ri+1 = (a * ri + b) mod n Note: 12 is congruent to 2 (modulo 5), since (12 -2) mod 5 = 0 n Problem? Its dependability; probable word attack n csci 5233 computer security & integrity 28
The six frequent letters n P. 45 n. A correction: (E, e) i n How to use the table ‘inside out’? csci 5233 computer security & integrity 29
Dual-Message Entrapment n P. 46 n Encipher two messages at once n One message is real; the other is the dummy. n Both the sender and the receiver know the dummy message (the key). n The key cannot be distinguished from the real message. csci 5233 computer security & integrity 30
Summary n Substitutions and permutations together form a basis for the most widely used encryption algorithms Chap. 3. n Next: Pf, Ch 2 (part b) csci 5233 computer security & integrity 31
- Slides: 31