Chapter 2 Access Control Matrix Overview Access Control
![Primitive Operations enter r into A[s, o] Adds r rights for subject s over Primitive Operations enter r into A[s, o] Adds r rights for subject s over](https://slidetodoc.com/presentation_image/1773964689c371de4d993cc4279bb105/image-15.jpg)
![Primitive Operations delete r from A[s, o] Removes r rights from subject s over Primitive Operations delete r from A[s, o] Removes r rights from subject s over](https://slidetodoc.com/presentation_image/1773964689c371de4d993cc4279bb105/image-16.jpg)
- Slides: 21
Chapter 2: Access Control Matrix Overview Access Control Matrix Model Protection State Transitions Commands Conditional Commands Introduction to Computer Security © 2004 Matt Bishop Slide #2 -1
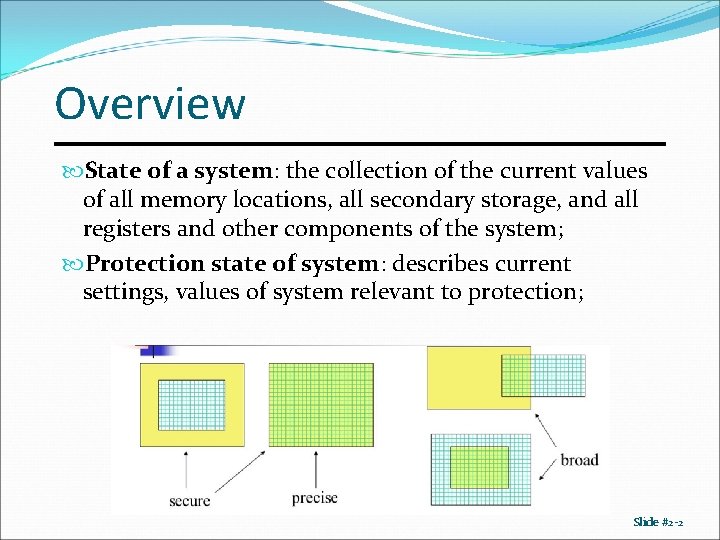
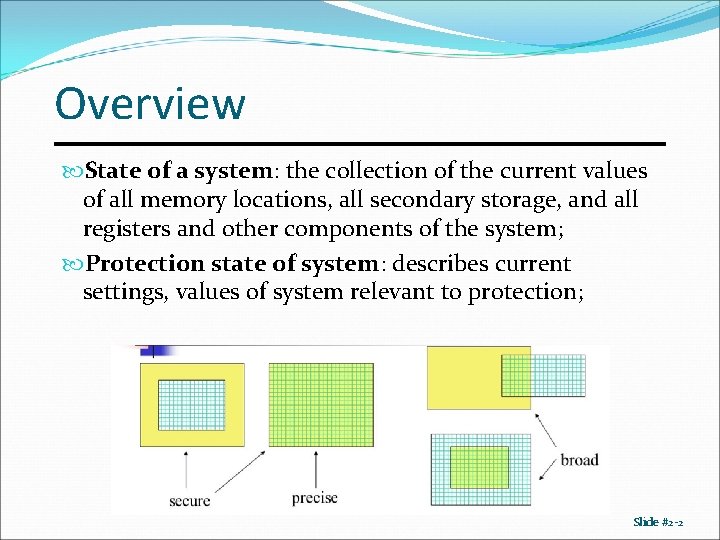
Overview State of a system: the collection of the current values of all memory locations, all secondary storage, and all registers and other components of the system; Protection state of system: describes current settings, values of system relevant to protection; Slide #2 -2
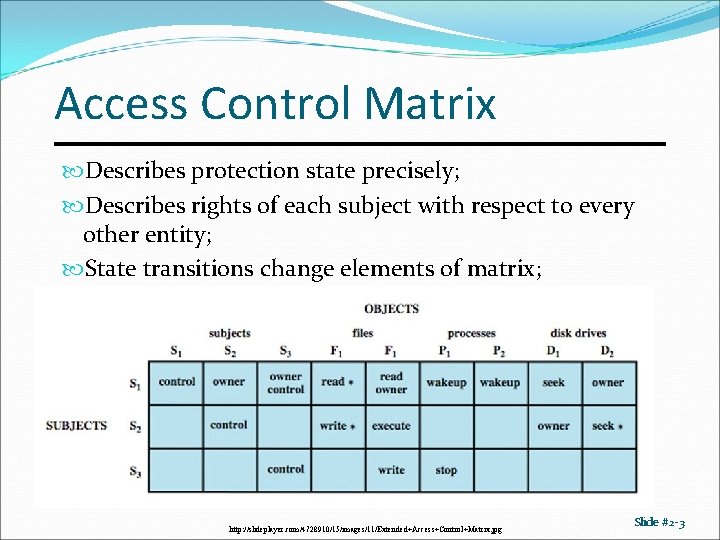
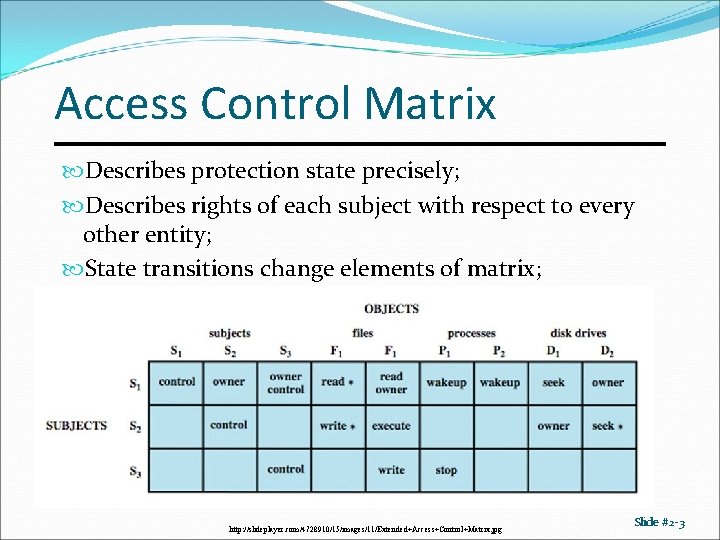
Access Control Matrix Describes protection state precisely; Describes rights of each subject with respect to every other entity; State transitions change elements of matrix; http: //slideplayer. com/4728910/15/images/11/Extended+Access+Control+Matrix. jpg Slide #2 -3
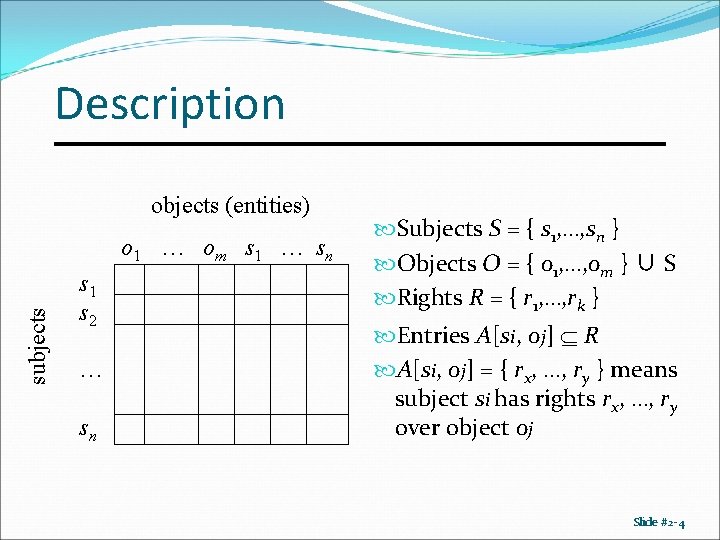
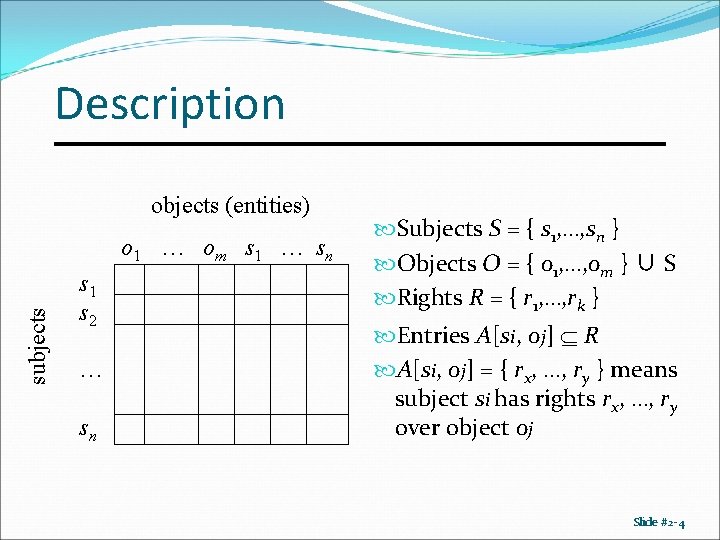
Description objects (entities) subjects o 1 … om s 1 … sn s 1 s 2 … sn Subjects S = { s 1, …, sn } Objects O = { o 1, …, om } ∪ S Rights R = { r 1, …, rk } Entries A[si, oj] R A[si, oj] = { rx, …, ry } means subject si has rights rx, …, ry over object oj Slide #2 -4
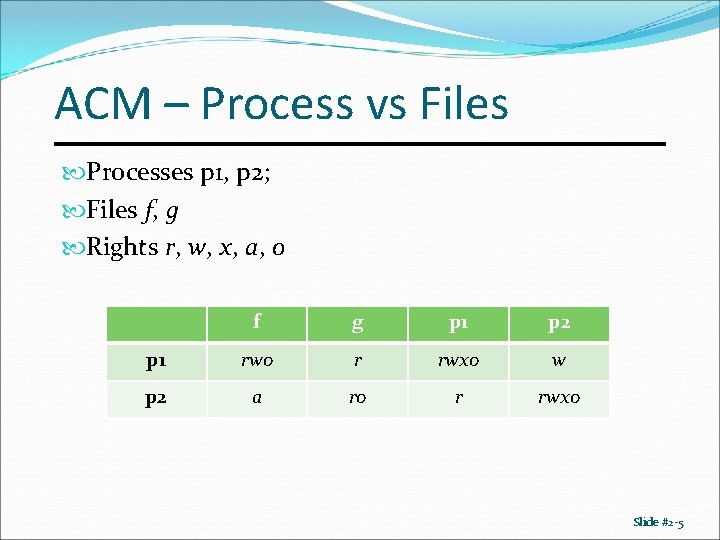
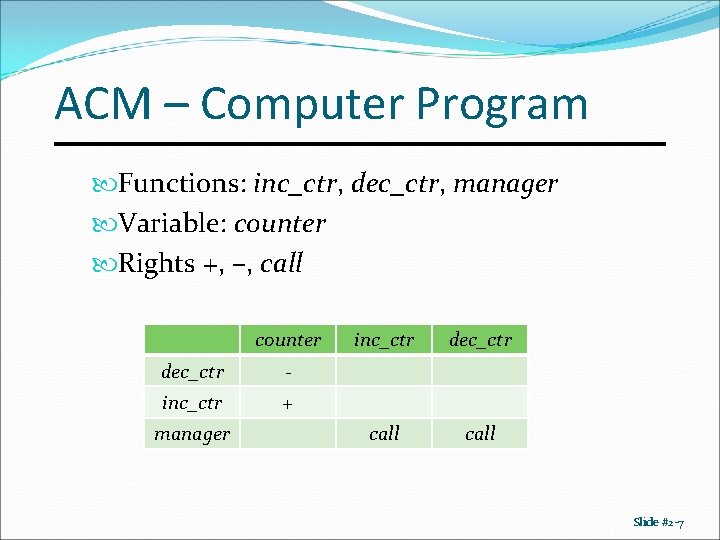
ACM – Process vs Files Processes p 1, p 2; Files f, g Rights r, w, x, a, o f g p 1 p 2 p 1 rwo r rwxo w p 2 a ro r rwxo Slide #2 -5
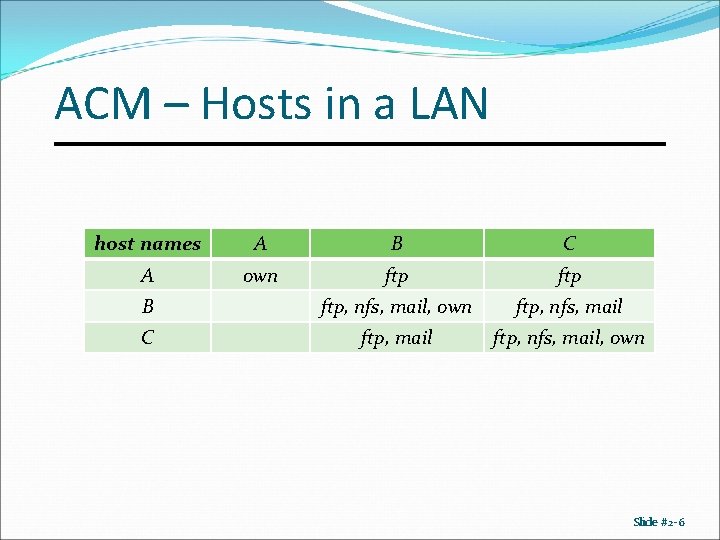
ACM – Hosts in a LAN host names A B C A own ftp B ftp, nfs, mail, own ftp, nfs, mail C ftp, mail ftp, nfs, mail, own Slide #2 -6
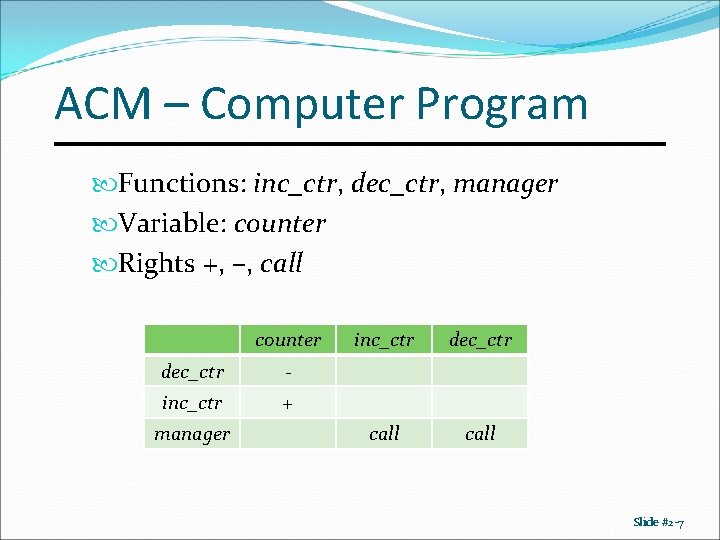
ACM – Computer Program Functions: inc_ctr, dec_ctr, manager Variable: counter Rights +, –, call counter dec_ctr - inc_ctr + manager inc_ctr dec_ctr call Slide #2 -7
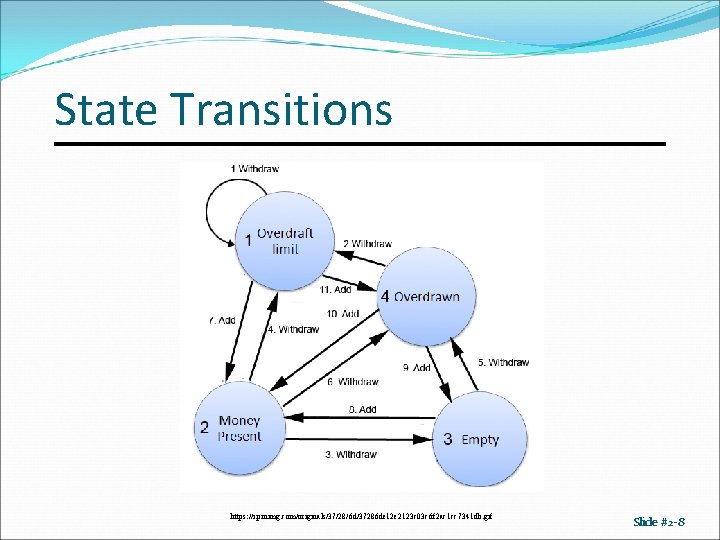
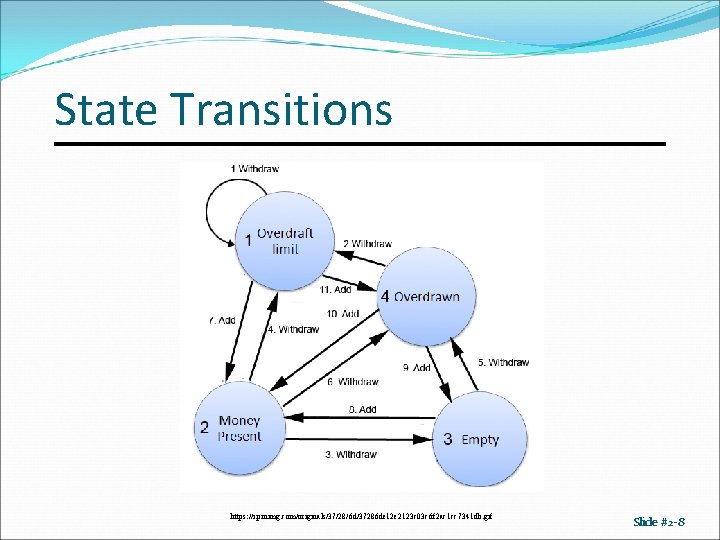
State Transitions https: //i. pinimg. com/originals/37/28/6 d/37286 de 12 e 2123 c 03 c 6 f 2 ac 1 cc 7341 db. gif Slide #2 -8
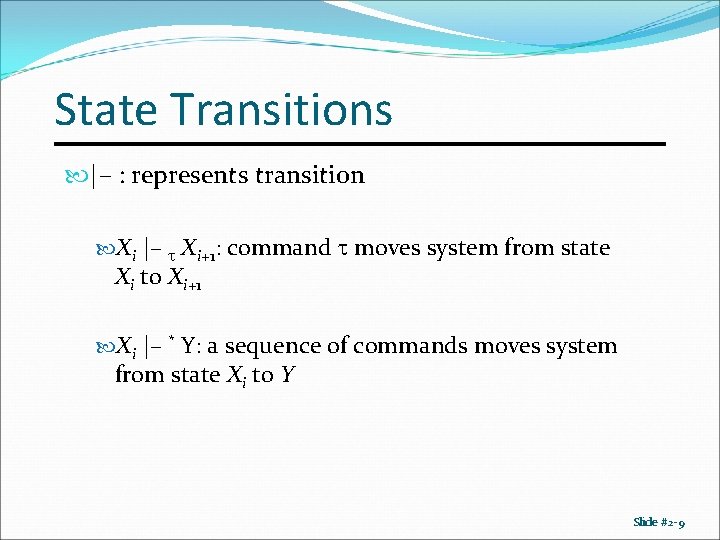
State Transitions |– : represents transition Xi |– Xi+1: command moves system from state Xi to Xi+1 Xi |– * Y: a sequence of commands moves system from state Xi to Y Slide #2 -9
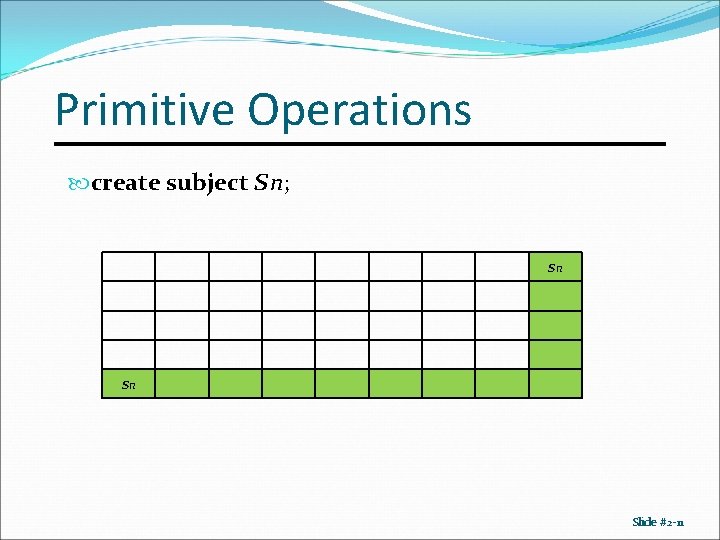
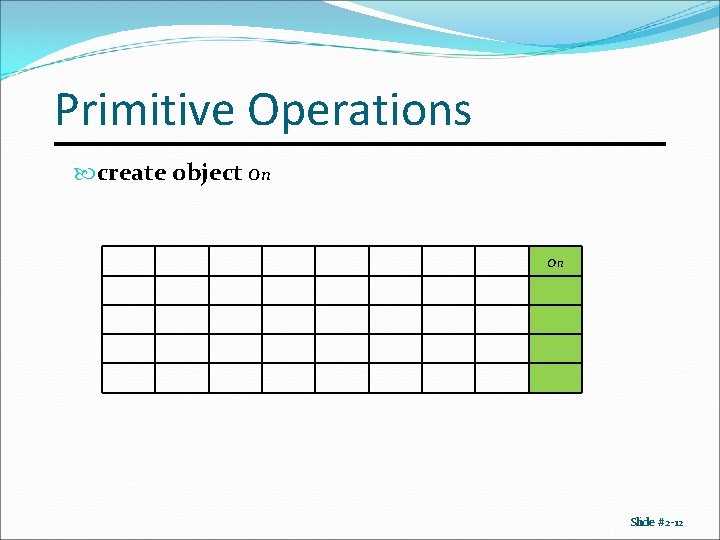
Primitive Operations create subject s; create object o destroy subject s; destroy object o enter r into A[s, o] delete r from A[s, o] Slide #2 -10
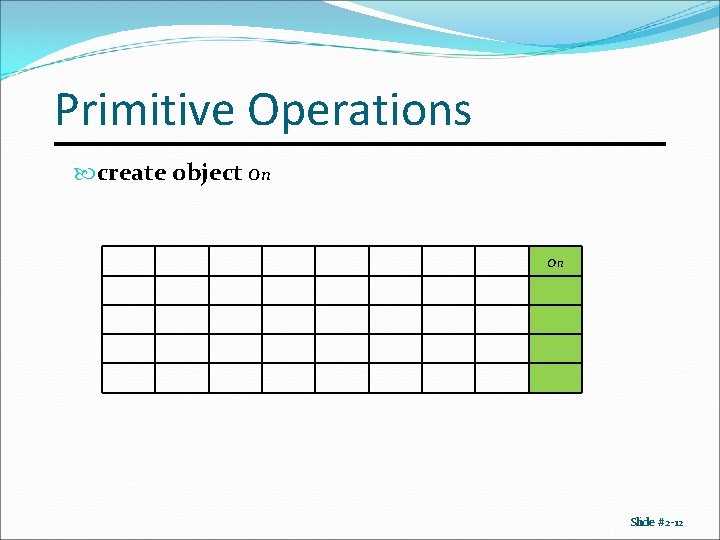
Primitive Operations create subject sn; sn sn Slide #2 -11
Primitive Operations create object on on Slide #2 -12
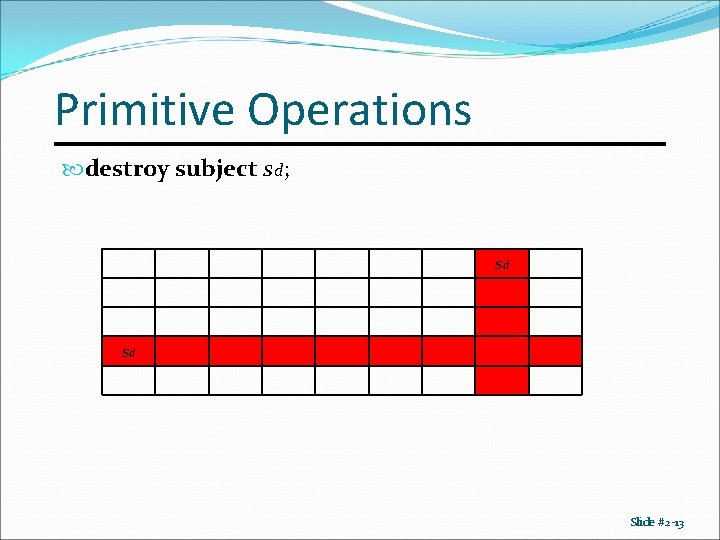
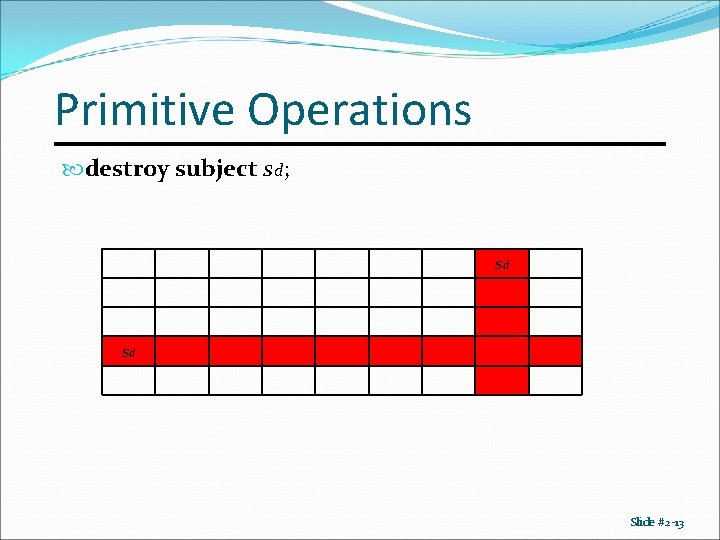
Primitive Operations destroy subject sd; sd sd Slide #2 -13
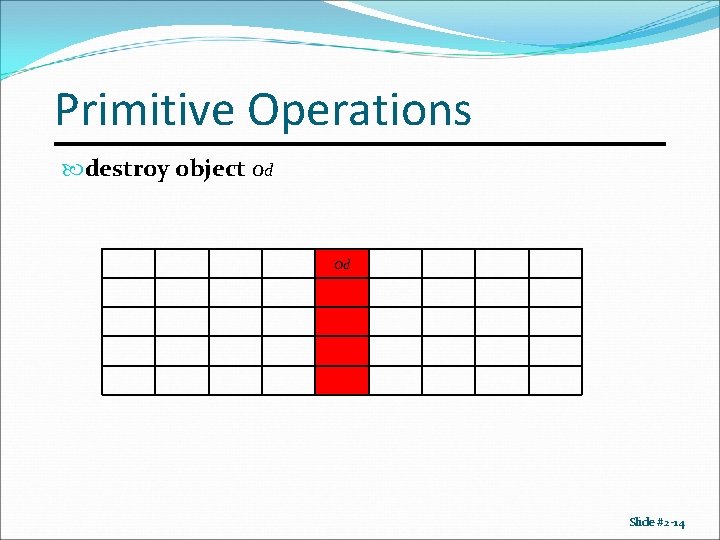
Primitive Operations destroy object od od Slide #2 -14
![Primitive Operations enter r into As o Adds r rights for subject s over Primitive Operations enter r into A[s, o] Adds r rights for subject s over](https://slidetodoc.com/presentation_image/1773964689c371de4d993cc4279bb105/image-15.jpg)
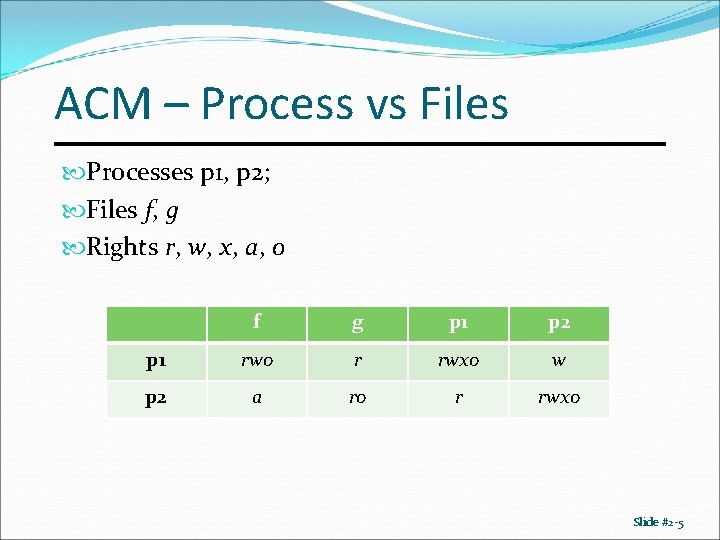
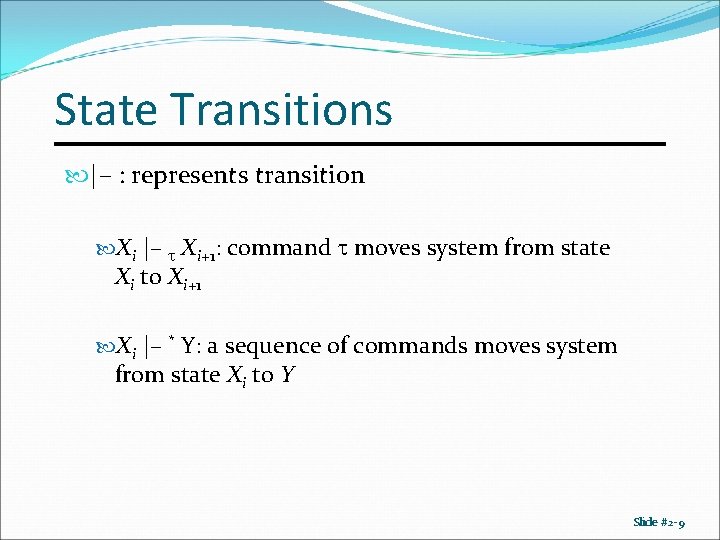
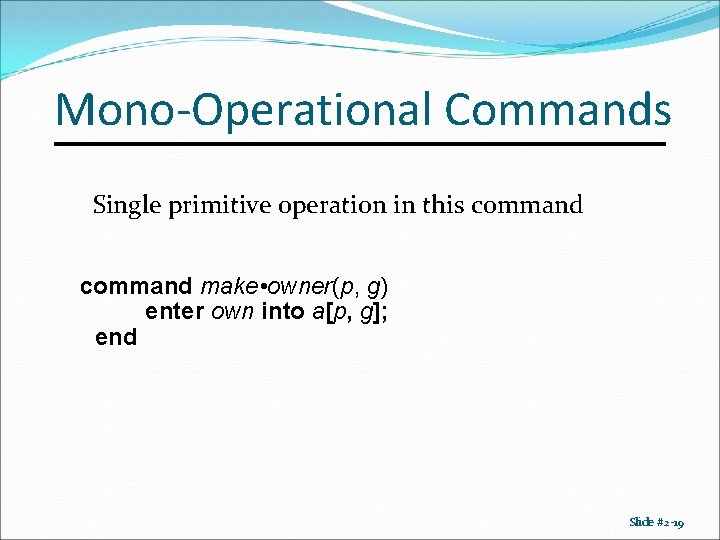
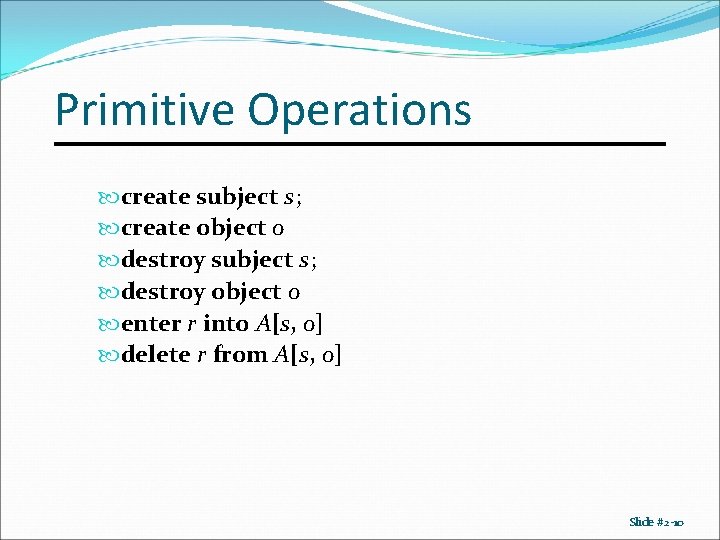
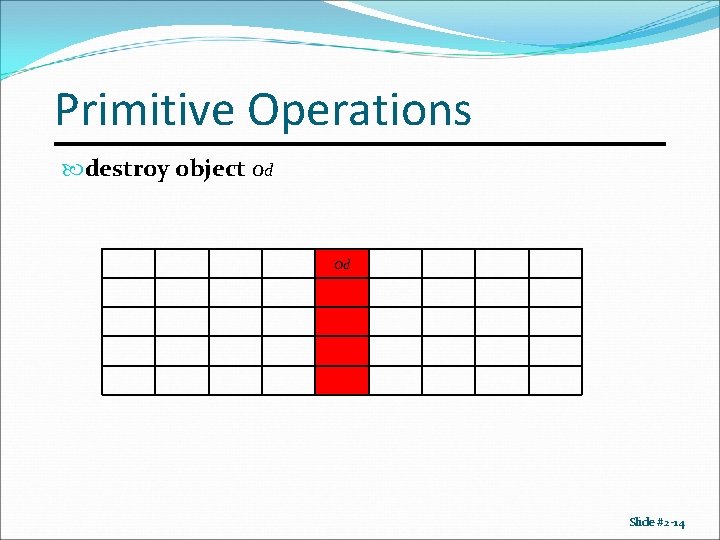
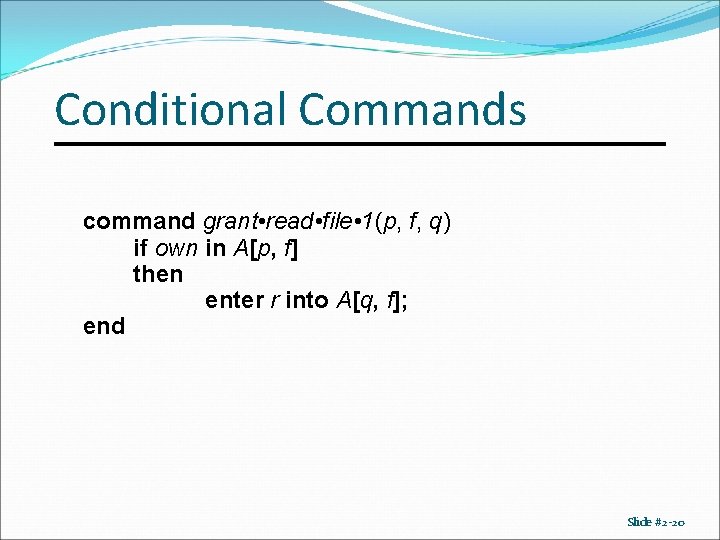
Primitive Operations enter r into A[s, o] Adds r rights for subject s over object o o s r Slide #2 -15
![Primitive Operations delete r from As o Removes r rights from subject s over Primitive Operations delete r from A[s, o] Removes r rights from subject s over](https://slidetodoc.com/presentation_image/1773964689c371de4d993cc4279bb105/image-16.jpg)
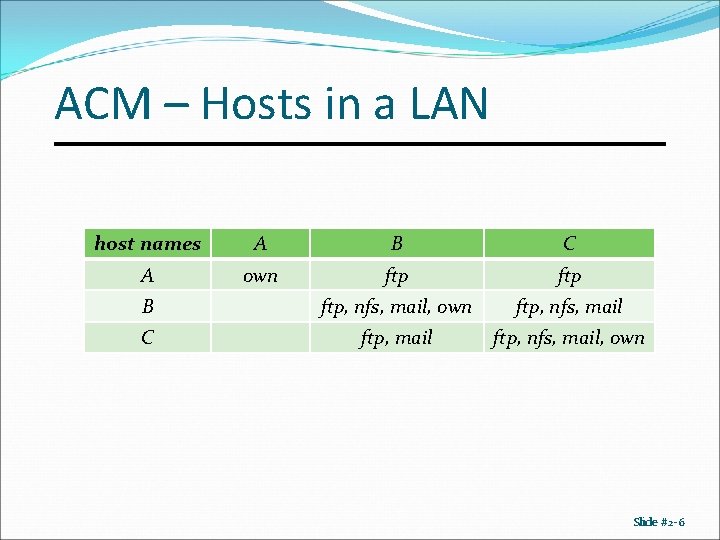
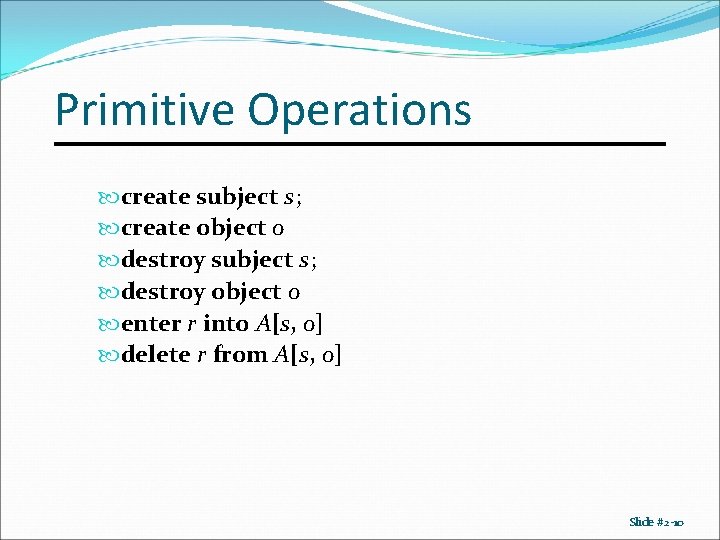
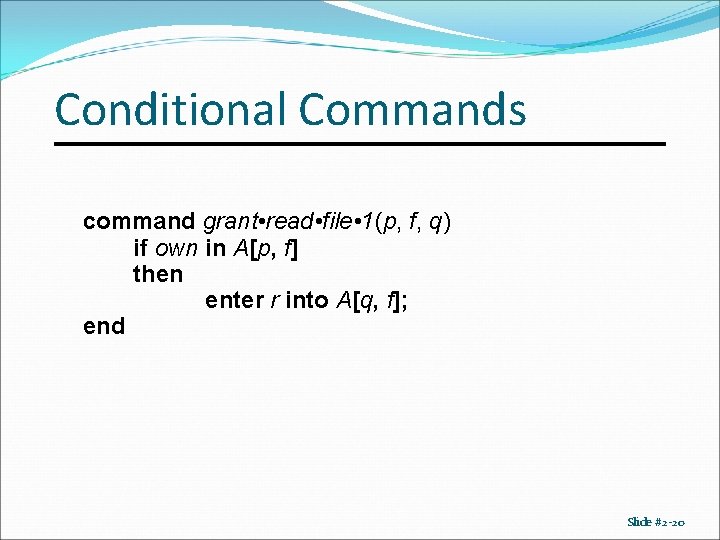
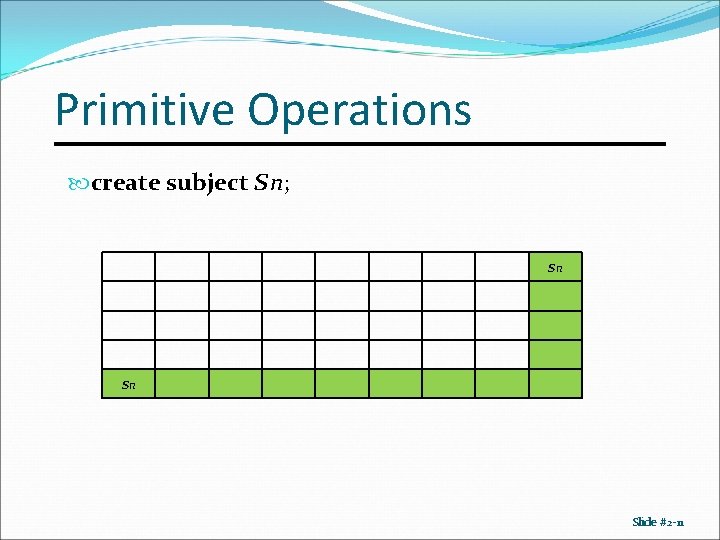
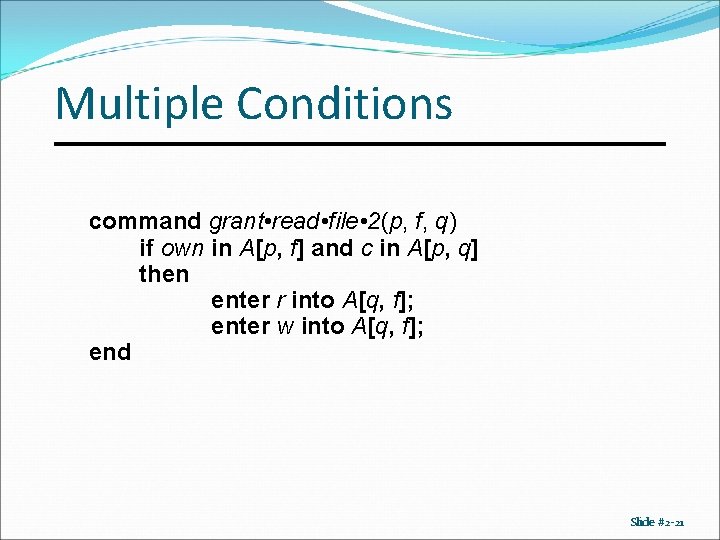
Primitive Operations delete r from A[s, o] Removes r rights from subject s over object o o s r Slide #2 -16
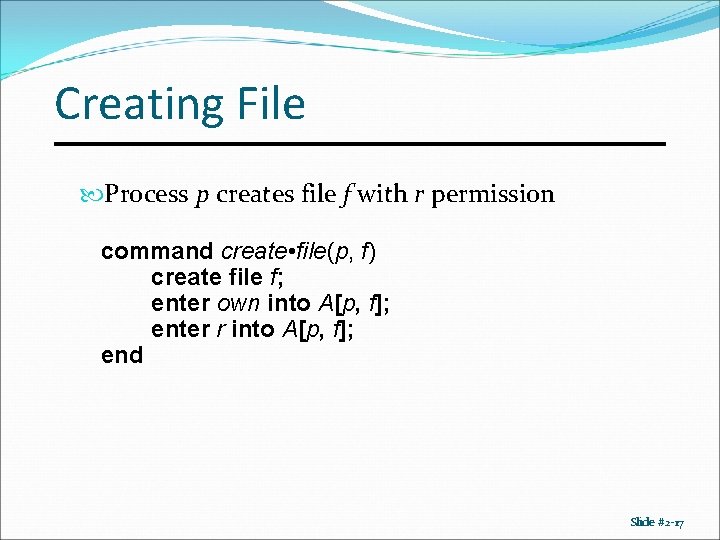
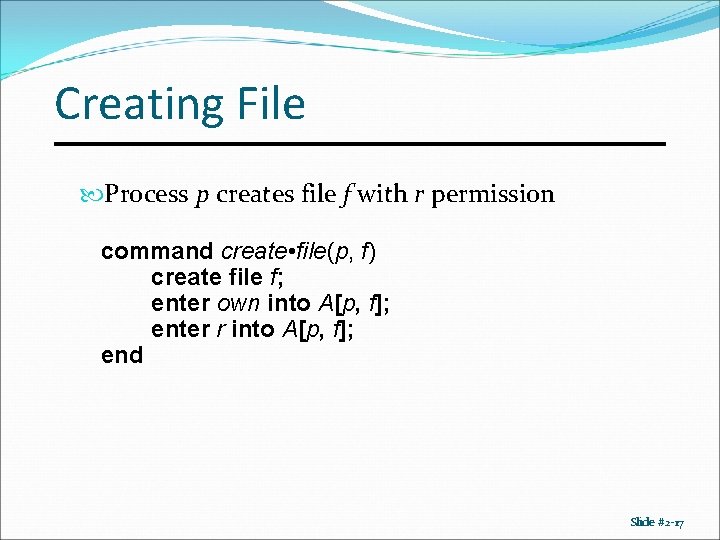
Creating File Process p creates file f with r permission command create • file(p, f) create file f; enter own into A[p, f]; enter r into A[p, f]; end Slide #2 -17
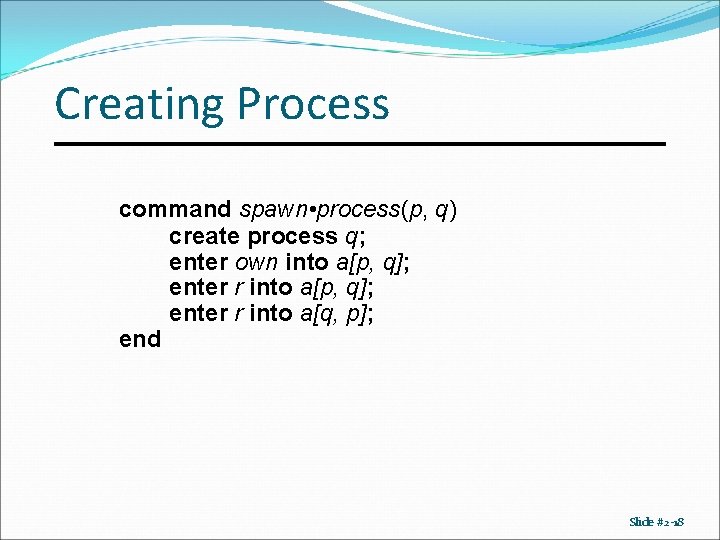
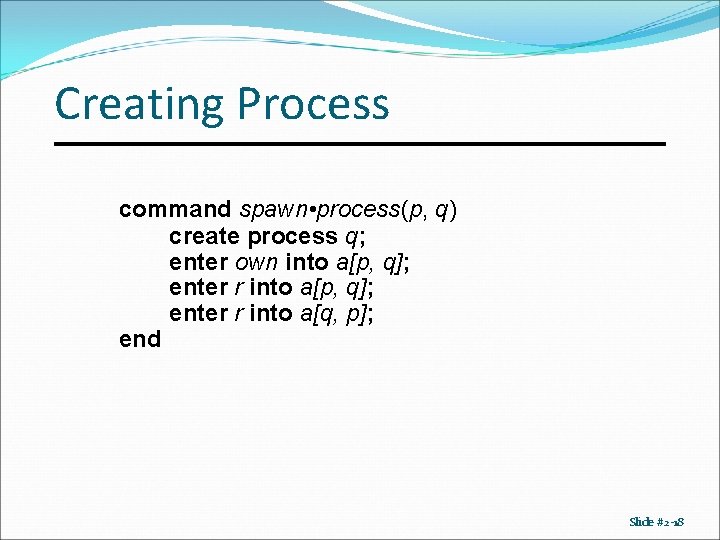
Creating Process command spawn • process(p, q) create process q; enter own into a[p, q]; enter r into a[q, p]; end Slide #2 -18
Mono-Operational Commands Single primitive operation in this command make • owner(p, g) enter own into a[p, g]; end Slide #2 -19
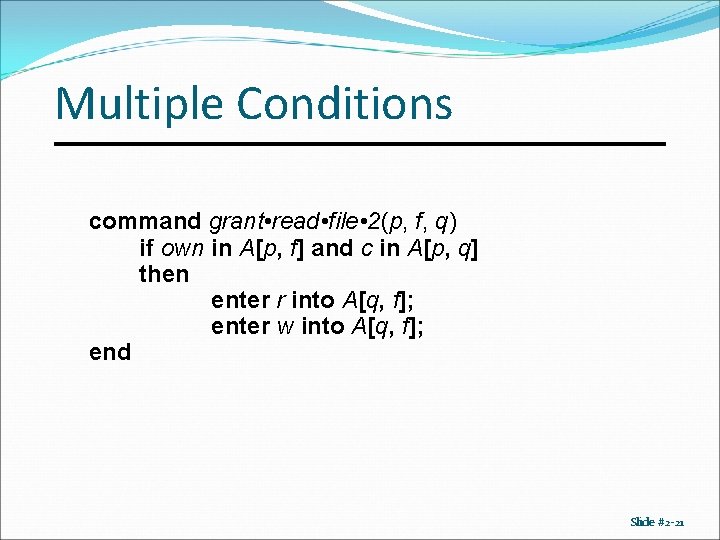
Conditional Commands command grant • read • file • 1(p, f, q) if own in A[p, f] then enter r into A[q, f]; end Slide #2 -20
Multiple Conditions command grant • read • file • 2(p, f, q) if own in A[p, f] and c in A[p, q] then enter r into A[q, f]; enter w into A[q, f]; end Slide #2 -21