Chapter 17 Controls and Security Measures Learning Objectives
Chapter 17 Controls and Security Measures
Learning Objectives ü When you finish this chapter, you will w Be able to identify the main types of risks to information systems. w Recognize how a system is vulnerable from development, through construction, implementation, and operation. w Know the types of controls required to ensure the integrity of data entry and processing. 2
Learning Objectives w Recognize the importance of integrating security measures into systems development. w Know the principles of how organizations develop recovery plans. w Be able to explain the economic aspects of pursuing information security. 3

Goals of Information Security ü Reduce the risk of systems and organizations ceasing operations ü Maintain information confidentiality (機密) ü Ensure the integrity and reliability of data resources ü Ensure compliance with national security laws and privacy policies and laws 4
Risks to Information Systems ü Risks to Hardware w Natural disasters total loss w Blackouts and brownouts – voltage regulator (穩壓器); UPS (uninterruptible power supply) w Vandalism (故意破壞) 5
Risks to Information Systems ü Risks to Applications and Data w Theft of information w Data alteration(篡改) and data destruction w Computer viruses – logic bomb w Unauthorized remote control programs – Back Orifice w Nonmalicious mishaps(非惡意的破壞) –Human error, poor training 6
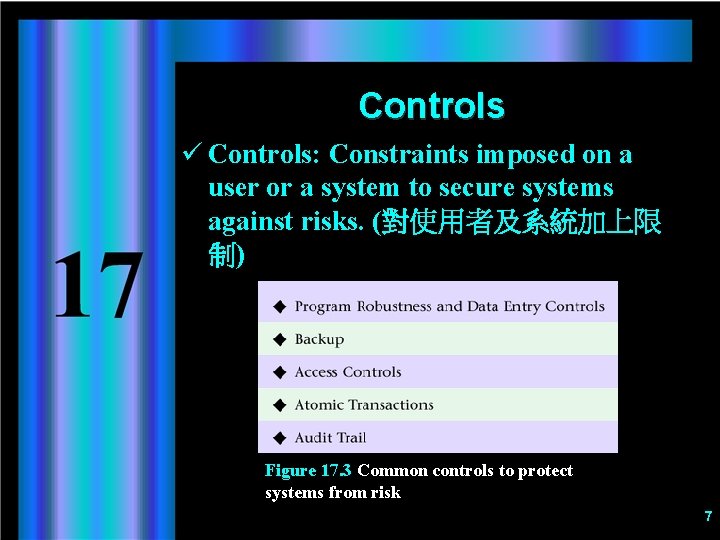
Controls ü Controls: Constraints imposed on a user or a system to secure systems against risks. (對使用者及系統加上限 制) Figure 17. 3 Common controls to protect systems from risk 7
Controls ü Program Robustness and Data Entry Controls w Provide a clear and sound interface with the user w Menus and limits – different menu options depending upon a user’s access authorization ü Backup w Periodic duplication of all data redundant arrays of independent disks (RAID) disk backup -> network backup ü Access Controls w Ensure that only authorized people can gain access to systems and files w Access codes and passwords w biometric (指紋, 耾膜) 8
Controls ü Atomic Transactions w Ensures that transaction data are recorded properly in all the pertinent files to ensure integrity ü Audit Trails w Built into an IS so that transactions can be traced to people, times, and authorization information 9
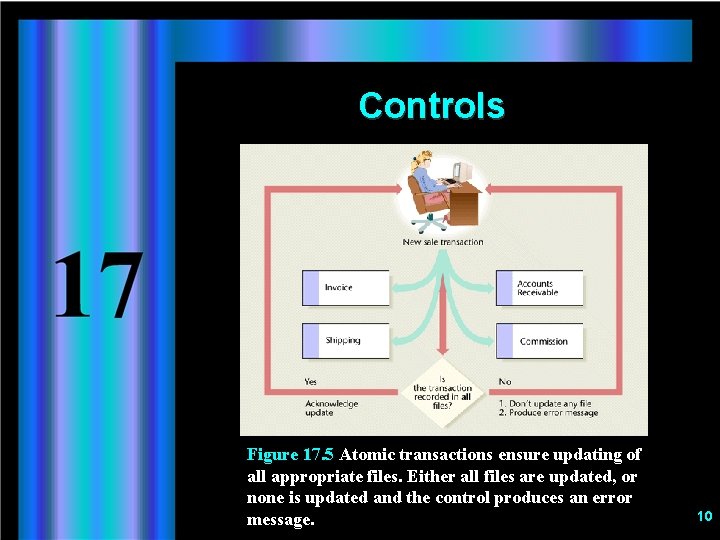
Controls Figure 17. 5 Atomic transactions ensure updating of all appropriate files. Either all files are updated, or none is updated and the control produces an error message. 10
Controls ü Integrating Security Measures into Systems Development w It is much less expensive to incorporate security measures during development than to impose them on an existing system. 11
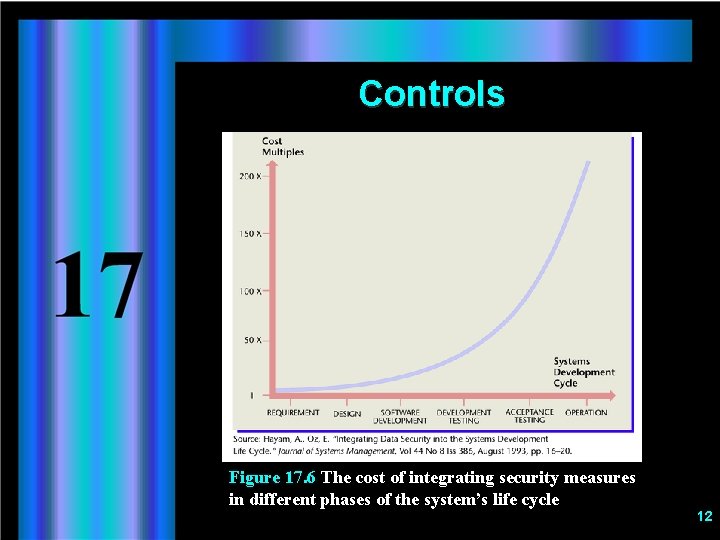
Controls Figure 17. 6 The cost of integrating security measures in different phases of the system’s life cycle 12

Controls Figure 17. 7 Activities required to integrate data security in the system development life cycle (SDLC) 13
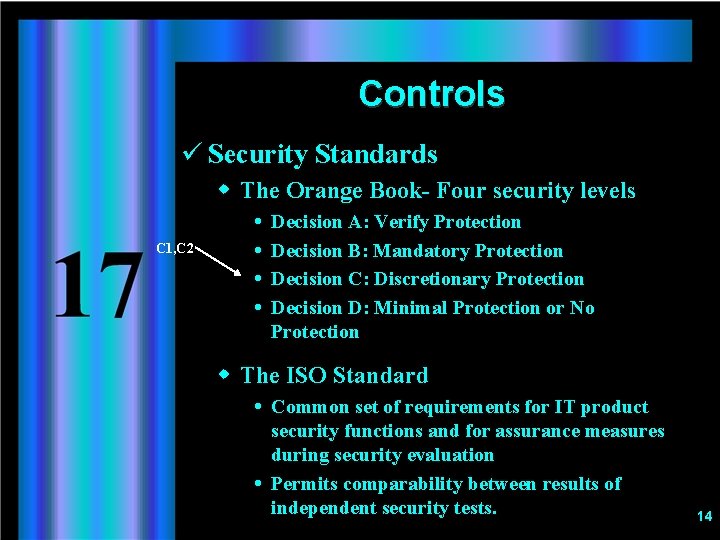
Controls ü Security Standards w The Orange Book- Four security levels C 1, C 2 Decision A: Verify Protection Decision B: Mandatory Protection Decision C: Discretionary Protection Decision D: Minimal Protection or No Protection w The ISO Standard Common set of requirements for IT product security functions and for assurance measures during security evaluation Permits comparability between results of independent security tests. 14
Controls w Separation of Duties Different people in charge of different activities, allowing checks and balances and minimizing possibility of criminal behavior. Separation of duties during systems development prevents installation of trapdoors (破解密碼). Separation of duties while using the system minimizes abuse, especially in electronic fund transfer. 15
Controls ü Network Controls w Callback Remote user’s telephone number verified before access allowed w Encryption Messages scrambled on sending end; descramble to plain text on receiving end Symmetric(對稱): Both users use a private, secret key Asymmetric: Parties use a combination of a public and a private key 16
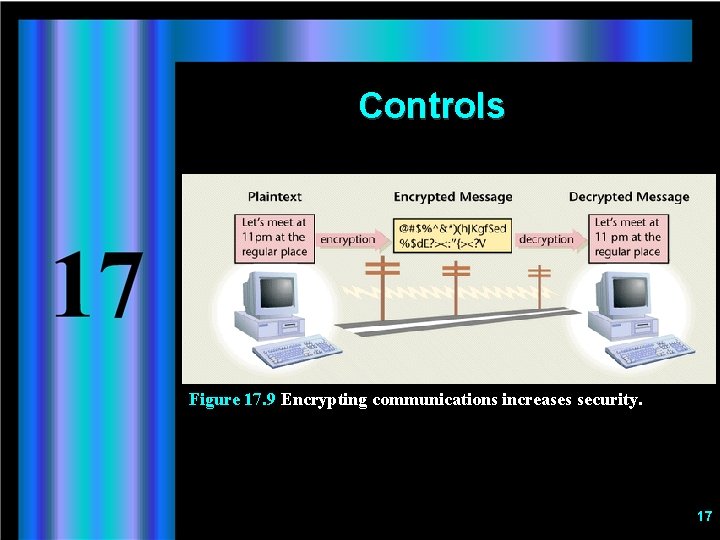
Controls Figure 17. 9 Encrypting communications increases security. 17
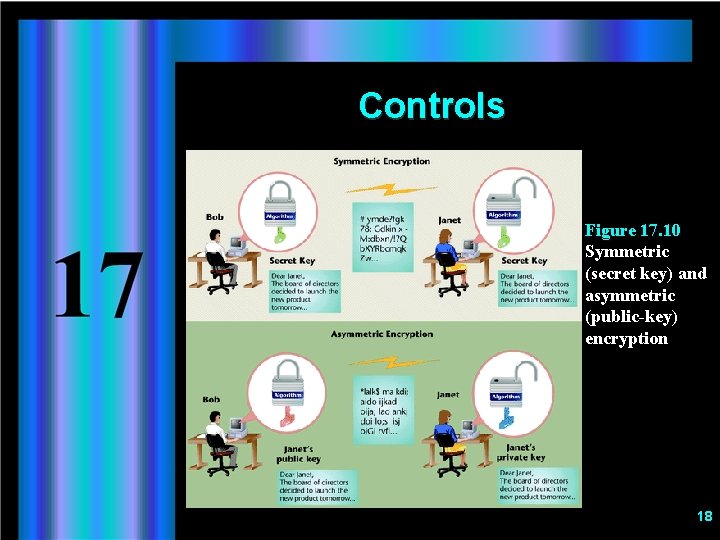
Controls Figure 17. 10 Symmetric (secret key) and asymmetric (public-key) encryption 18
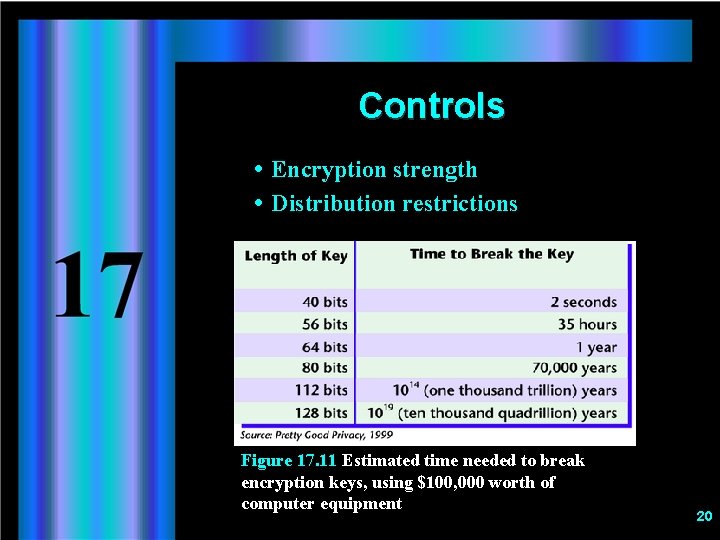
Controls Encryption strength Distribution restrictions Figure 17. 11 Estimated time needed to break encryption keys, using $100, 000 worth of computer equipment 20
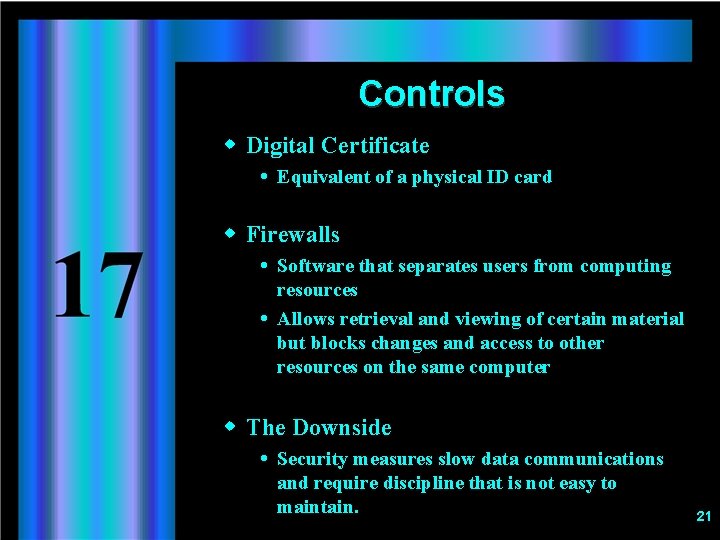
Controls w Digital Certificate Equivalent of a physical ID card w Firewalls Software that separates users from computing resources Allows retrieval and viewing of certain material but blocks changes and access to other resources on the same computer w The Downside Security measures slow data communications and require discipline that is not easy to maintain. 21
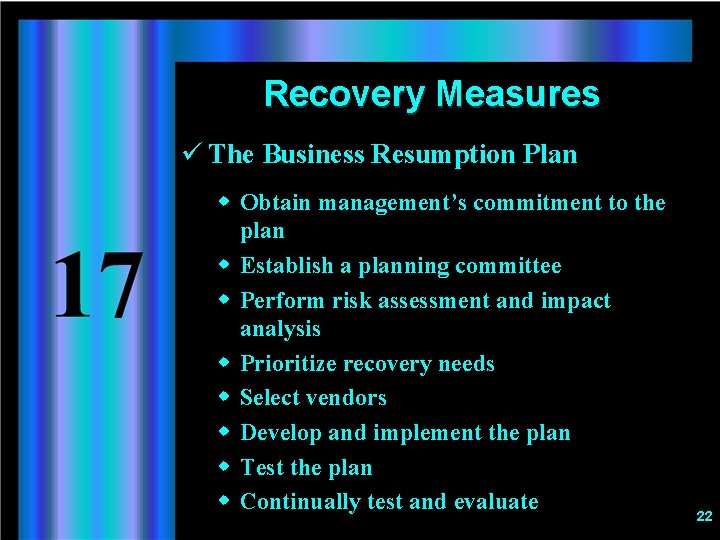
Recovery Measures ü The Business Resumption Plan w Obtain management’s commitment to the plan w Establish a planning committee w Perform risk assessment and impact analysis w Prioritize recovery needs w Select vendors w Develop and implement the plan w Test the plan w Continually test and evaluate 22
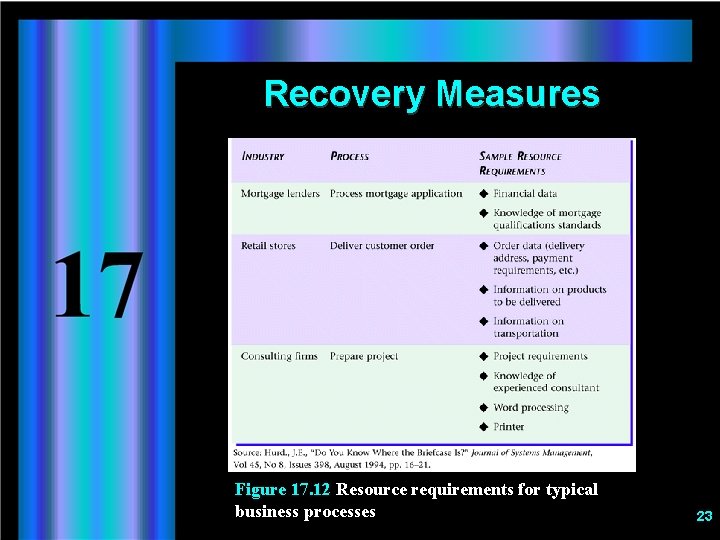
Recovery Measures Figure 17. 12 Resource requirements for typical business processes 23
The Economic Aspect of Security Measures ü Two types of costs to consider when determining how much to spend on data security: w The cost of potential damage w The cost of implementing a preventive measure 24
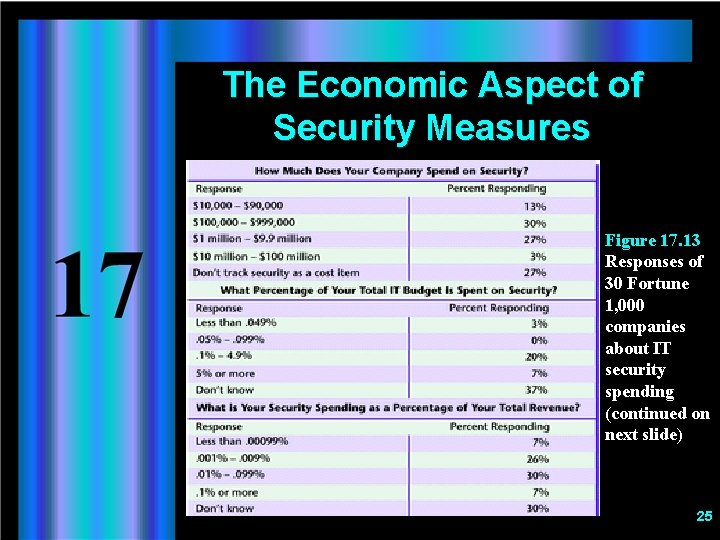
The Economic Aspect of Security Measures Figure 17. 13 Responses of 30 Fortune 1, 000 companies about IT security spending (continued on next slide) 25
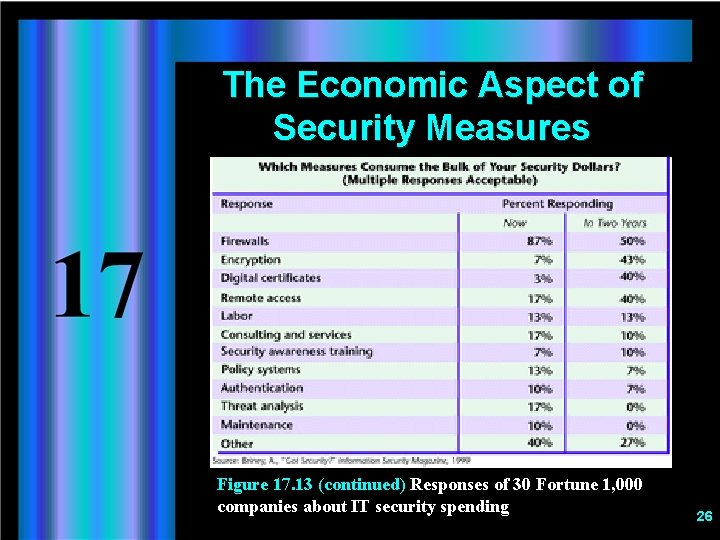
The Economic Aspect of Security Measures Figure 17. 13 (continued) Responses of 30 Fortune 1, 000 companies about IT security spending 26
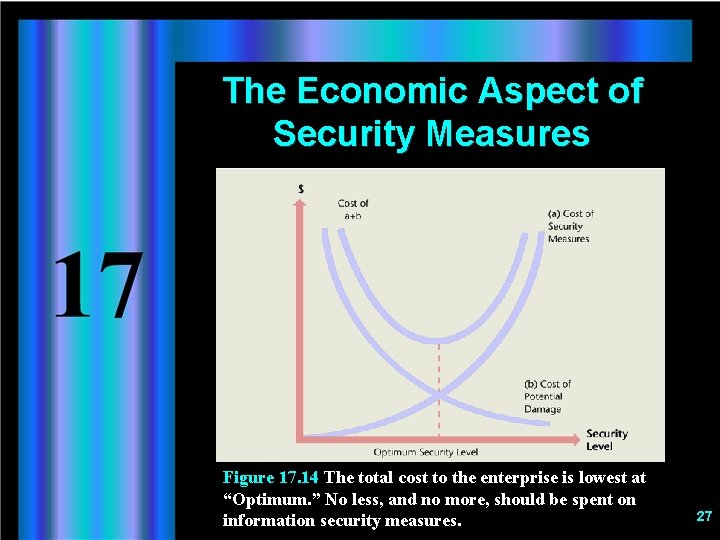
The Economic Aspect of Security Measures Figure 17. 14 The total cost to the enterprise is lowest at “Optimum. ” No less, and no more, should be spent on information security measures. 27
Ethical and Societal Issues No Smooth Sailing for the Clipper ü Clipper: a microprocessor that holds a complex encryption formula ü Government wanted U. S. computer manufacturers to include a chip in every microprocessor w Enables law enforcement agencies to decipher encrypted communication w Prevent criminals from concealing illegal activities, including terrorism and espionage 28
Ethical and Societal Issues No Smooth Sailing for the Clipper ü Privacy advocates were afraid of potential misuses of the method by unscrupulous law enforcement officers. ü Computer industry has strongly lobbied against Clipper for fear of losing both foreign and domestic markets. ü Democratic nations must decide how to balance w Government’s ability to protect citizens. w Citizens ability to protect their privacy. 29
- Slides: 29