Chapter 15 SNMPV 3 Architecture and Applications Prof

- Slides: 36
Chapter 15 SNMPV 3 Architecture and Applications Prof. Choong Seon HONG Kyung Hee University 1
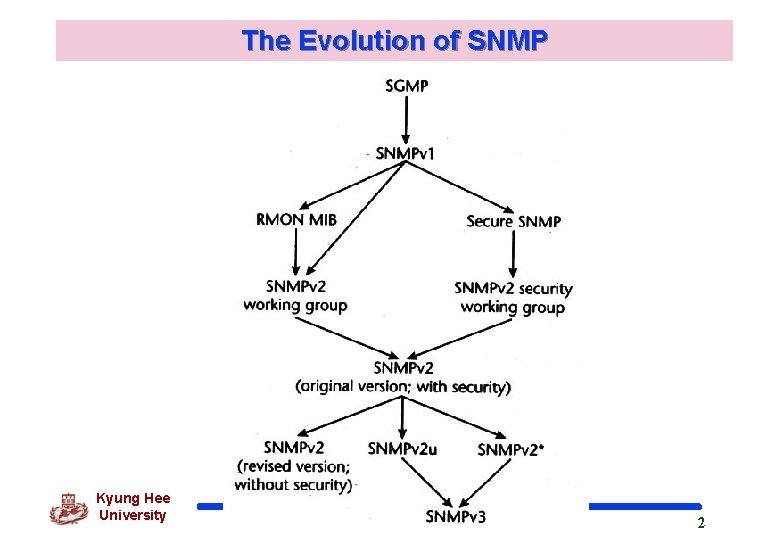
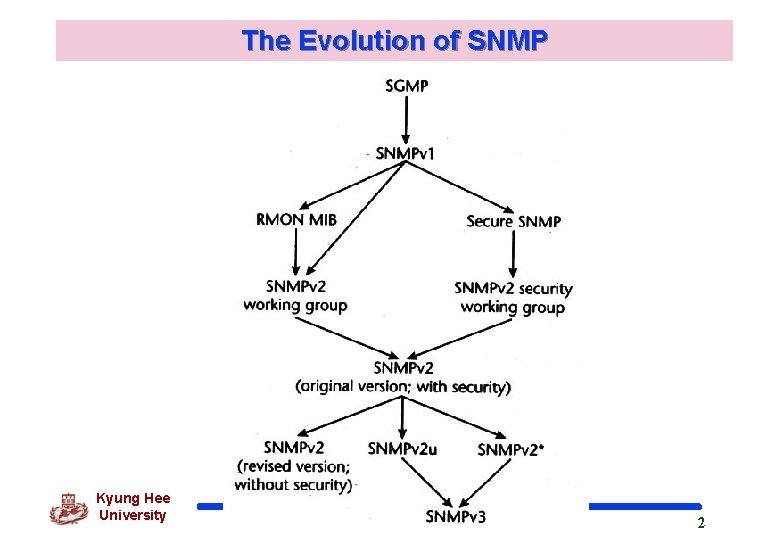
The Evolution of SNMP Kyung Hee University 2
SNMPv 3 Overview q Design Requirements SNMPv 3 security features rely heavily on SNMPv 2 u and SNMPv 2* Address the need for secure Set request messages over realworld networks, which is the most important deficiency of SNMPv 1 and SNMPv 2 Kyung Hee University 3
SNMPv 3 Overview - Design Requirements q ADDRESS THE NEED FOR SECURY SUPPORT q DEFINE AN ARCHITECTURE THAT ALLOWS FOR LONGEVITY OF SNMP q ALLOW THAT DIFFERENT PORTIONS OF THE ARCHITECTURE MOVE AT DIFFERENT SPEEDS TOWARDS STANDARD STATUS q ALLOW FOR FUTURE EXTENSIONS q KEEP SNMP AS SIMPLE AS POSSIBLE q ALLOW FOR MINIMAL IMPLEMENTATIONS q SUPPORT ALSO THE MORE COMPLEX FEATURES, WHICH ARE REQUIRED IN LARGE NETWORKS q RE-USE EXISTING SPECIFICATIONS, WHENEVER POSSIBLE Kyung Hee University 4
SNMP Entities Kyung Hee University 5
SNMPv 3 ARCHITECTURE: MANAGER UDP, Kyung. IPX Hee, Others University 6
SNMPv 3 ARCHITECTURE: Agent Kyung Hee University 7
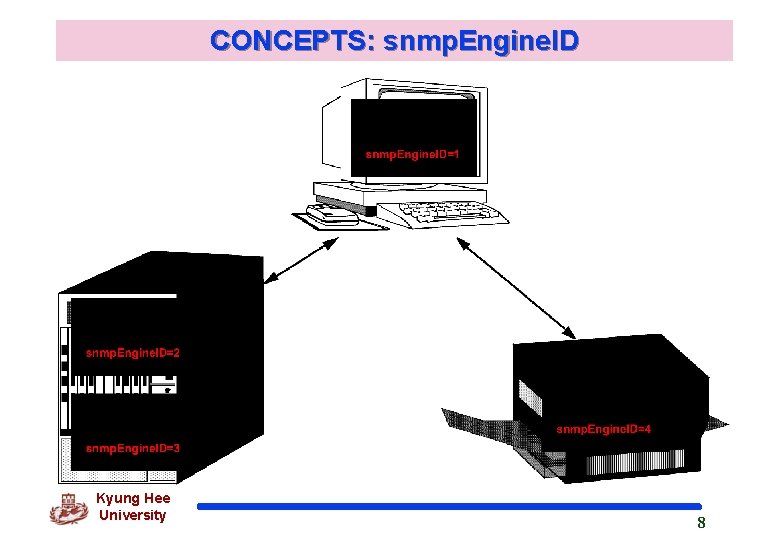
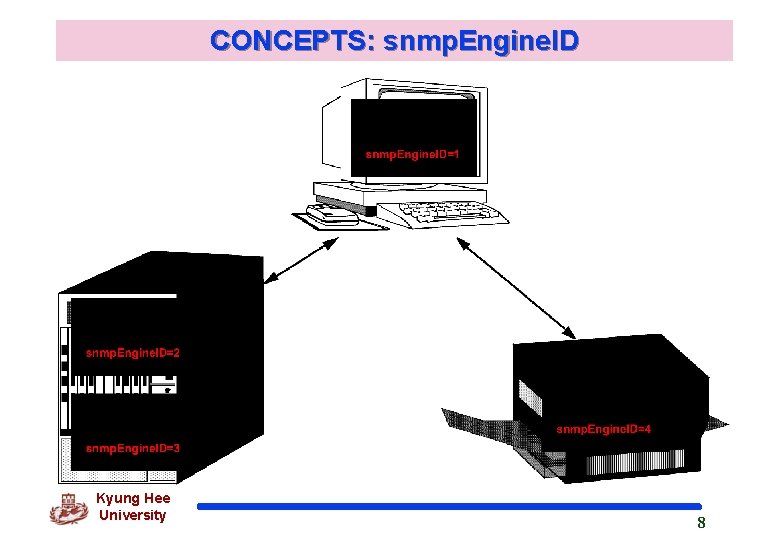
CONCEPTS: snmp. Engine. ID Kyung Hee University 8
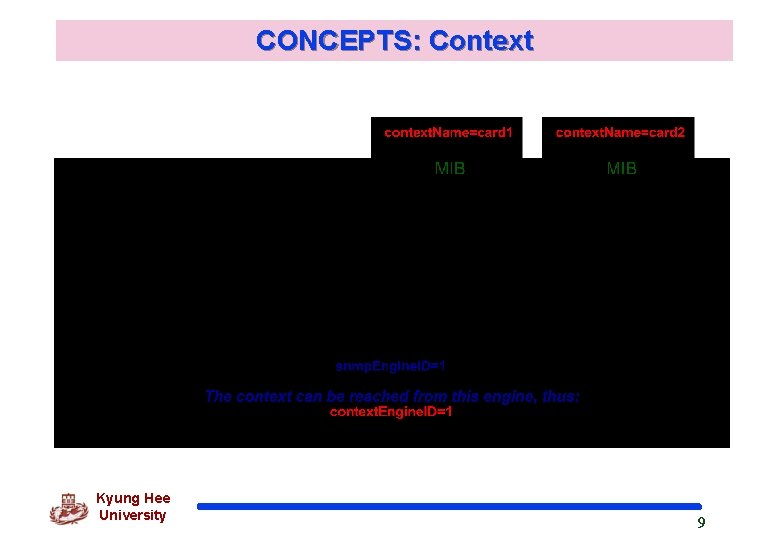
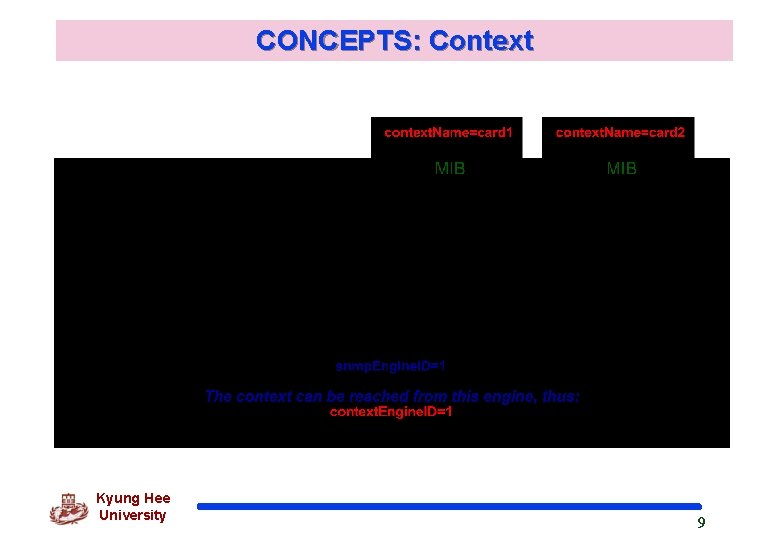
CONCEPTS: Context Kyung Hee University 9
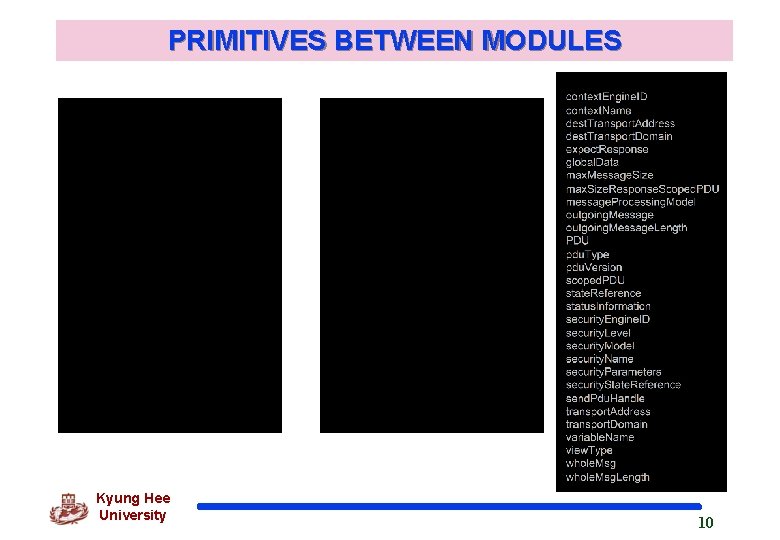
PRIMITIVES BETWEEN MODULES Kyung Hee University 10
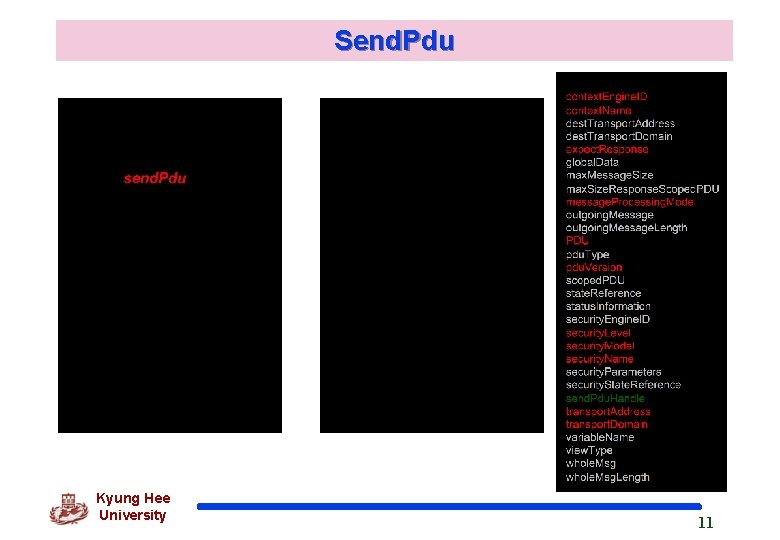
Send. Pdu Kyung Hee University 11
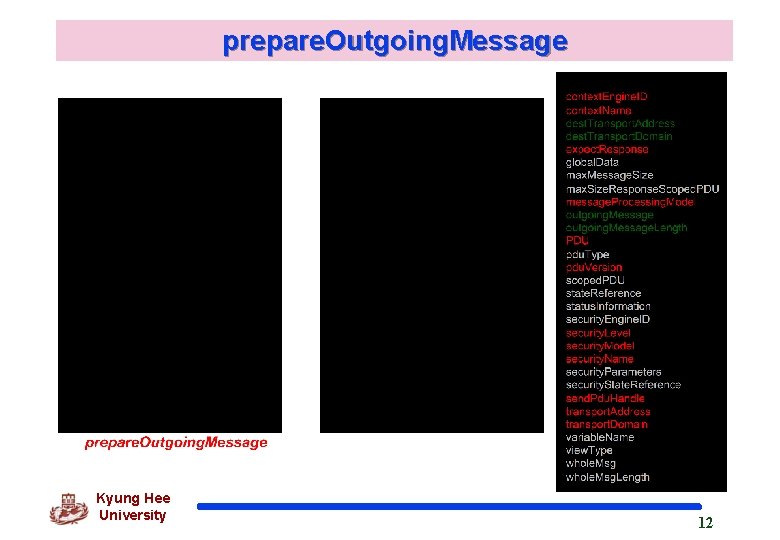
prepare. Outgoing. Message Kyung Hee University 12
generate. Request. Msg Kyung Hee University 13
send / receive Kyung Hee University 14
prepare. Data. Elements Kyung Hee University 15
process. Incoming. Msg Kyung Hee University 16
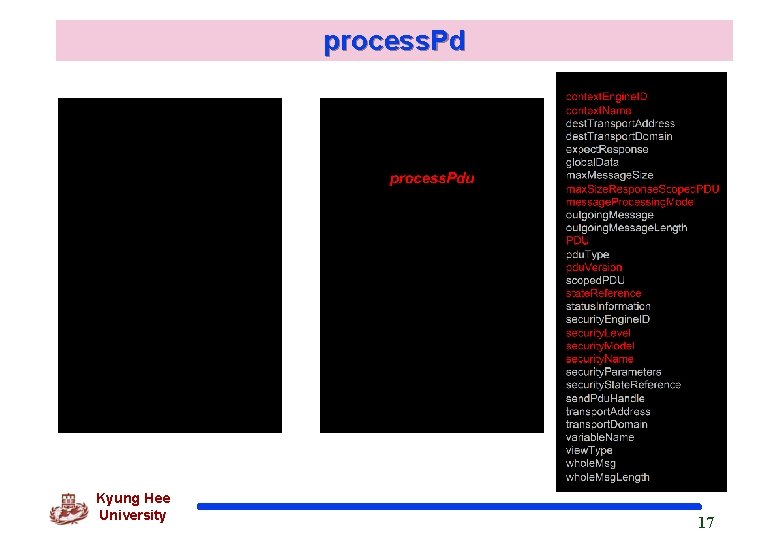
process. Pd Kyung Hee University 17
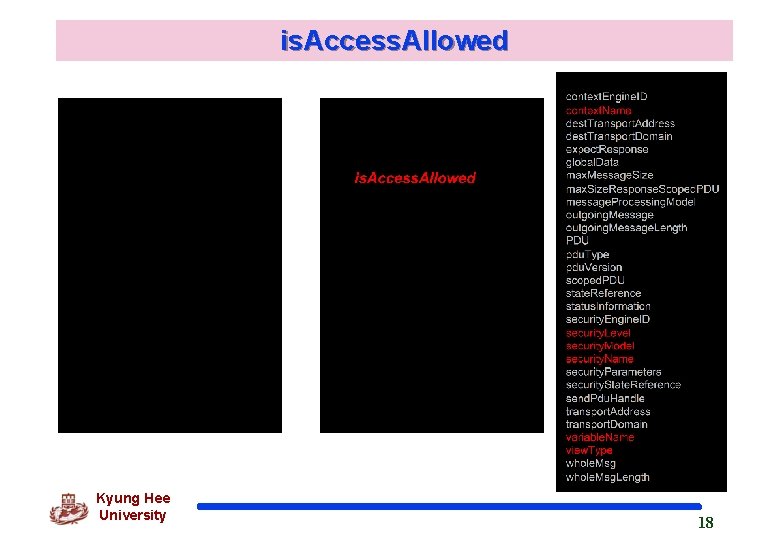
is. Access. Allowed Kyung Hee University 18
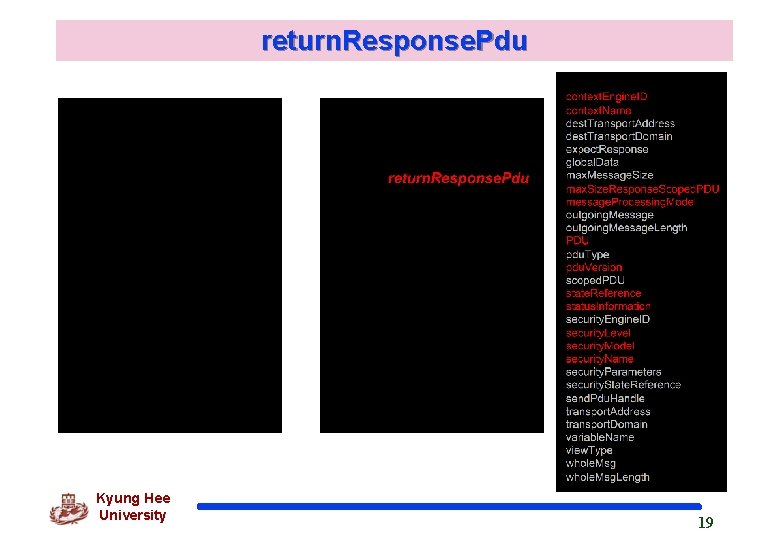
return. Response. Pdu Kyung Hee University 19
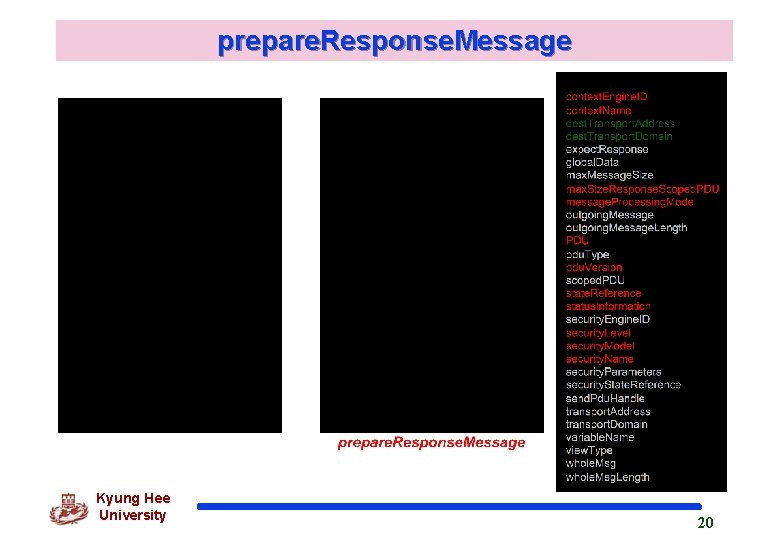
prepare. Response. Message Kyung Hee University 20

generate. Response. Msg Kyung Hee University 21
send / receive Kyung Hee University 22
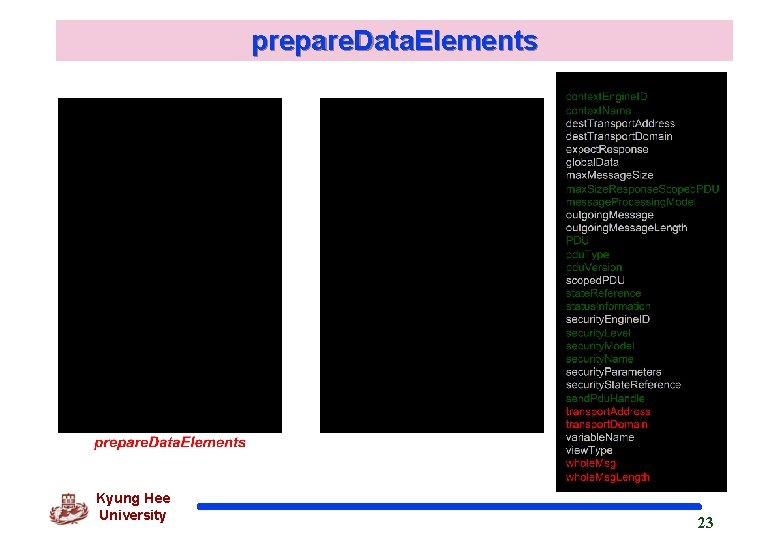
prepare. Data. Elements Kyung Hee University 23
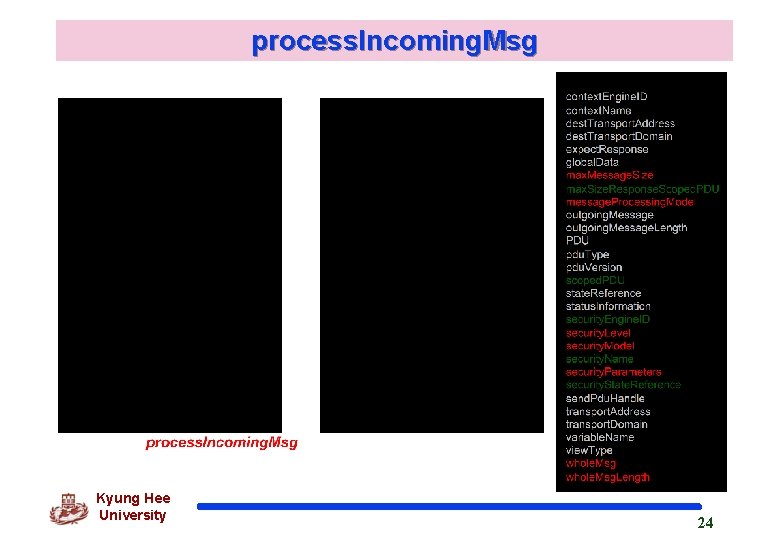
process. Incoming. Msg Kyung Hee University 24
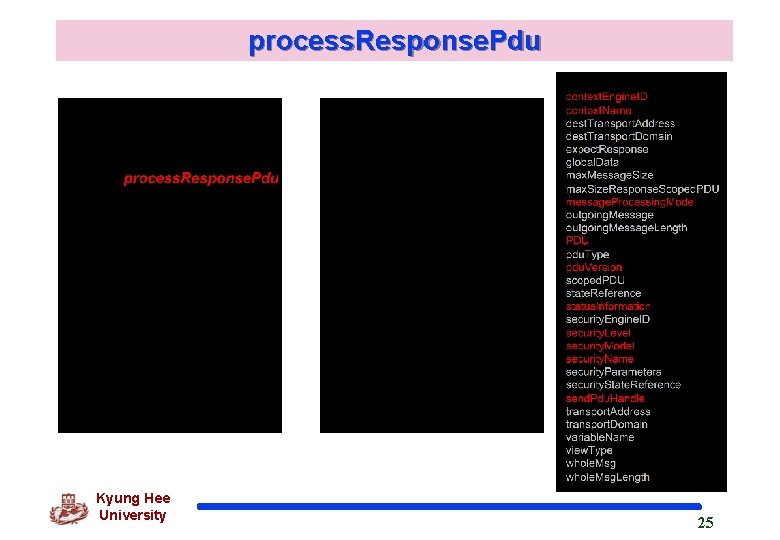
process. Response. Pdu Kyung Hee University 25
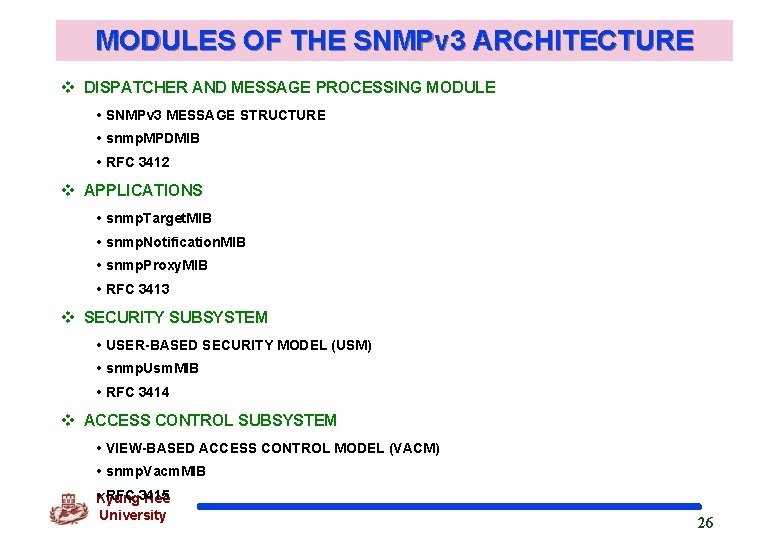
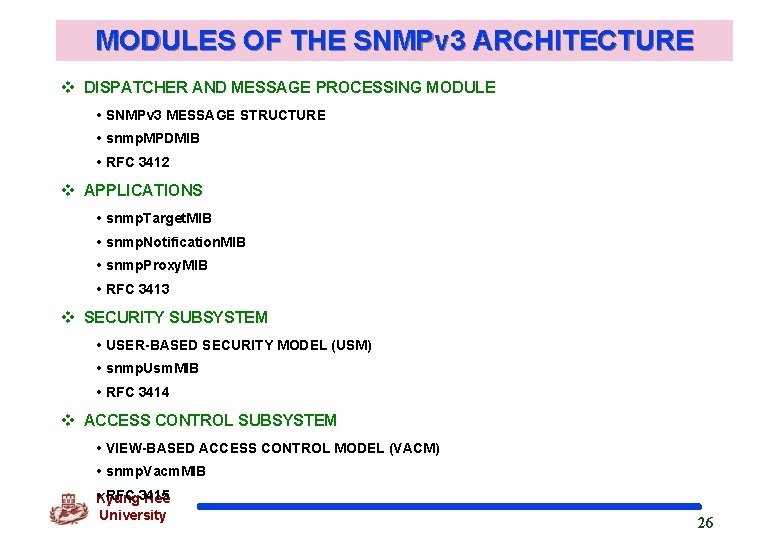
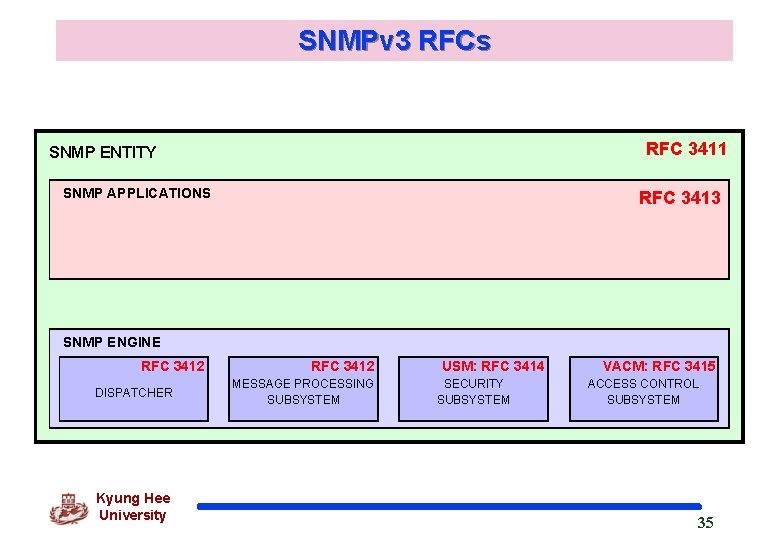
MODULES OF THE SNMPv 3 ARCHITECTURE v DISPATCHER AND MESSAGE PROCESSING MODULE • SNMPv 3 MESSAGE STRUCTURE • snmp. MPDMIB • RFC 3412 v APPLICATIONS • snmp. Target. MIB • snmp. Notification. MIB • snmp. Proxy. MIB • RFC 3413 v SECURITY SUBSYSTEM • USER-BASED SECURITY MODEL (USM) • snmp. Usm. MIB • RFC 3414 v ACCESS CONTROL SUBSYSTEM • VIEW-BASED ACCESS CONTROL MODEL (VACM) • snmp. Vacm. MIB • RFC 3415 Kyung Hee University 26
SNMPv 3 MESSAGE STRUCTURE Kyung Hee University 27
SNMPv 3 PROCESSING MODULE PARAMETERS Kyung Hee University 28
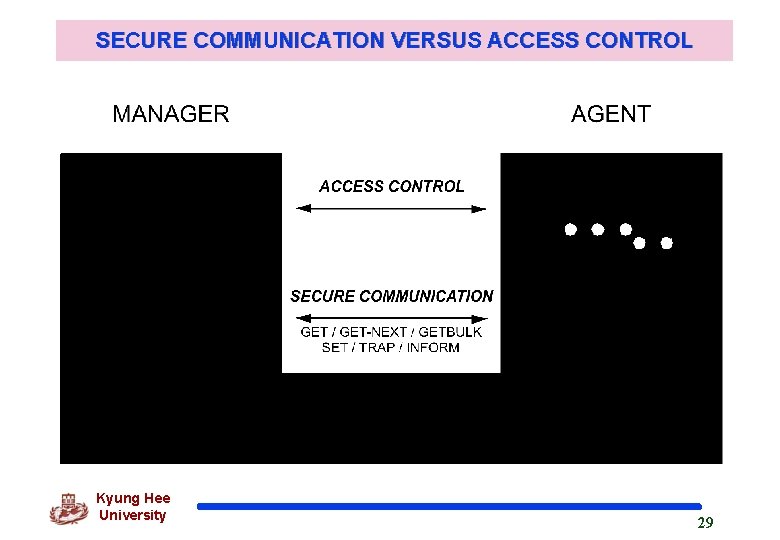
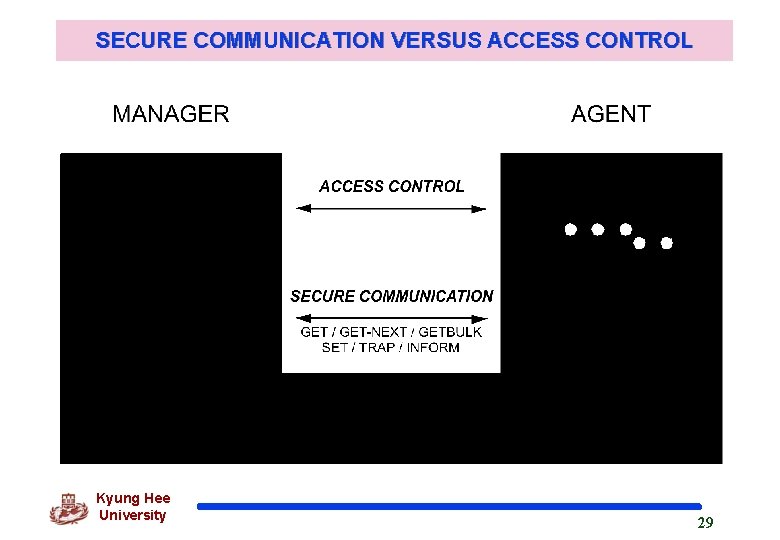
SECURE COMMUNICATION VERSUS ACCESS CONTROL Kyung Hee University 29
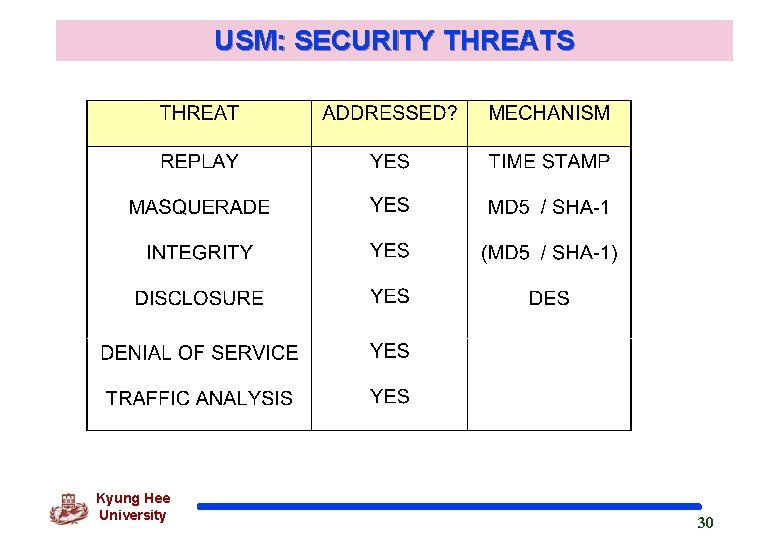
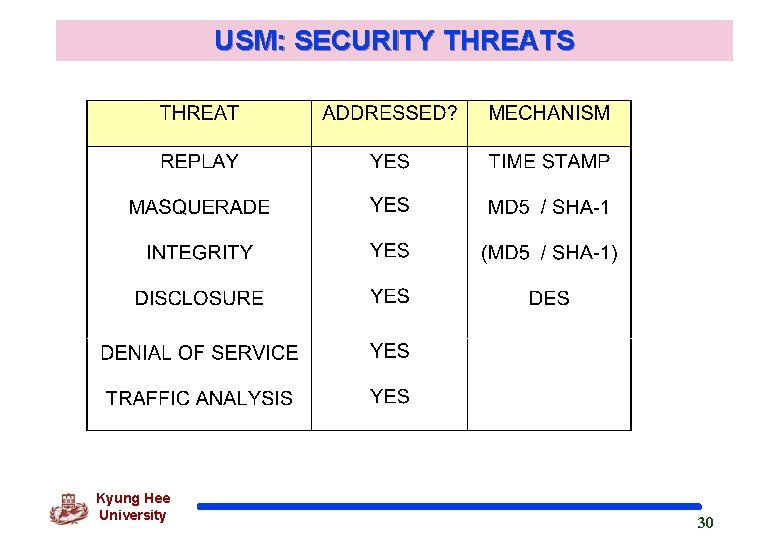
USM: SECURITY THREATS Kyung Hee University 30
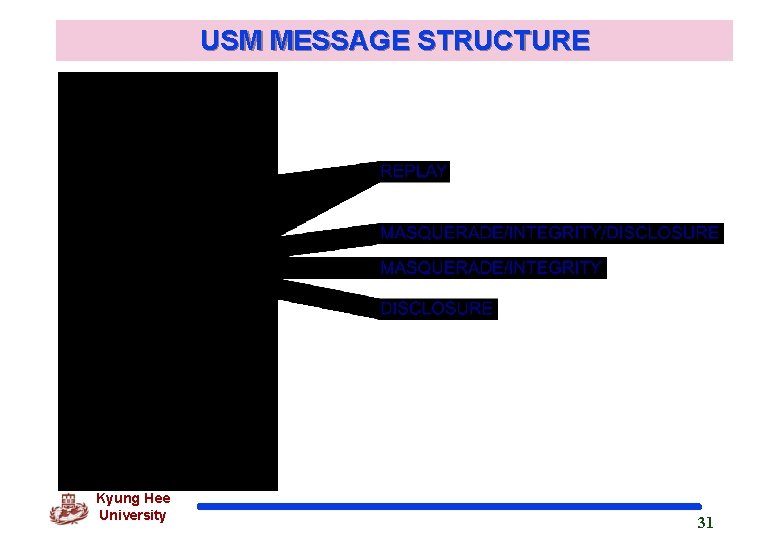
USM MESSAGE STRUCTURE Kyung Hee University 31
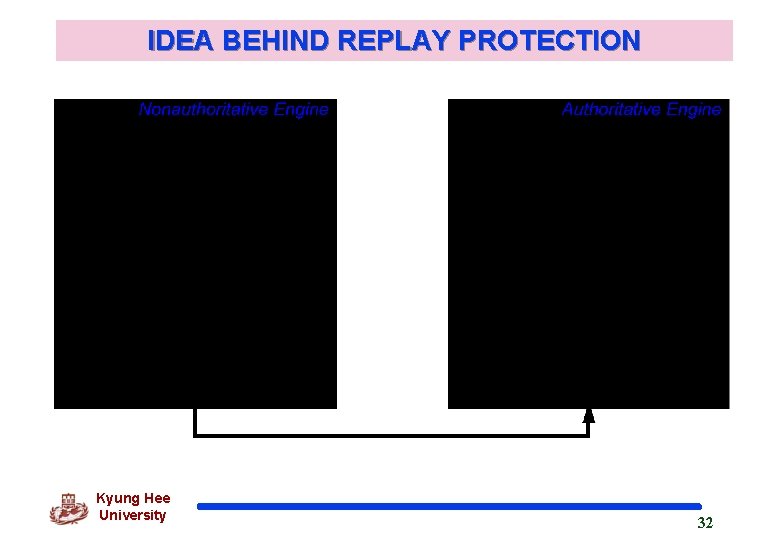
IDEA BEHIND REPLAY PROTECTION Kyung Hee University 32
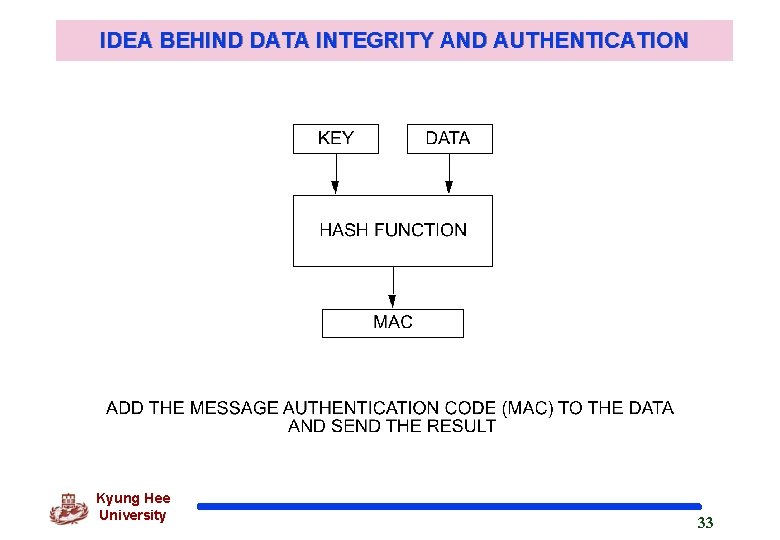
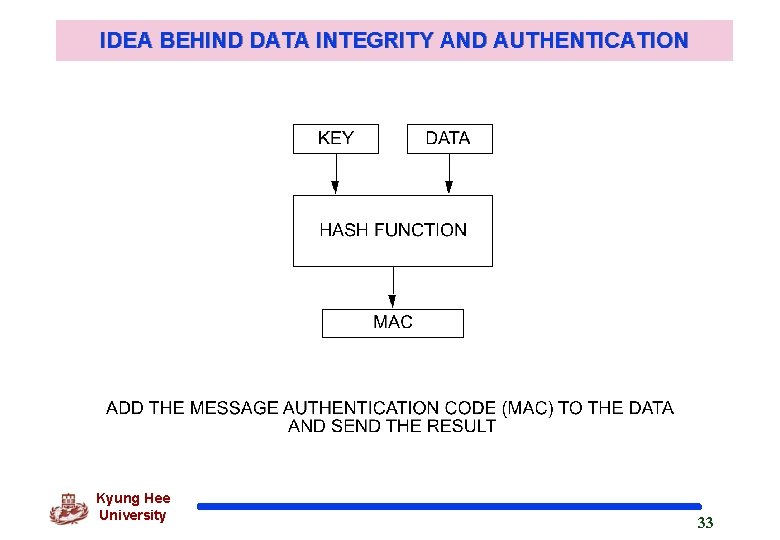
IDEA BEHIND DATA INTEGRITY AND AUTHENTICATION Kyung Hee University 33
SNMPv 3 IMPLEMENTATIONS q ACE*COMM q Advent. Net q BMC Software q Cisco q Epilogue q Gambit Communications q Halcyon q IBM q ISI q IWL q MG-SOFT q Multi. Port Corporation q Simple. Soft q SNMP Research q SNMP++ q TU of Braunschweig q UCD q University of Quebec Kyung Hee University 34
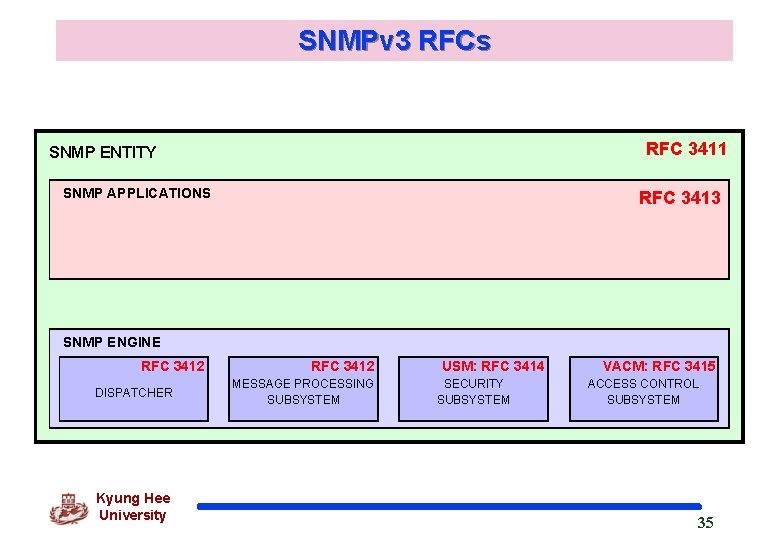
SNMPv 3 RFCs RFC 3411 SNMP ENTITY SNMP APPLICATIONS RFC 3413 OTHER SNMP ENGINE RFC 3412 DISPATCHER Kyung Hee University RFC 3412 MESSAGE PROCESSING SUBSYSTEM USM: RFC 3414 SECURITY SUBSYSTEM VACM: RFC 3415 ACCESS CONTROL SUBSYSTEM 35
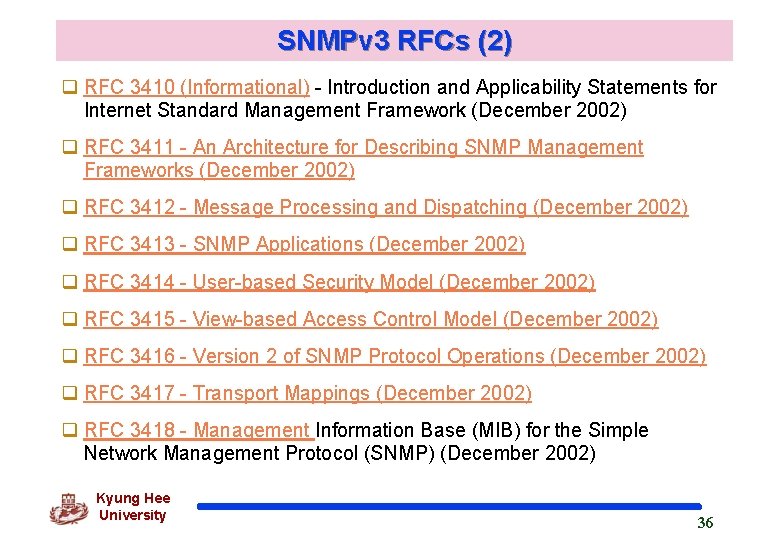
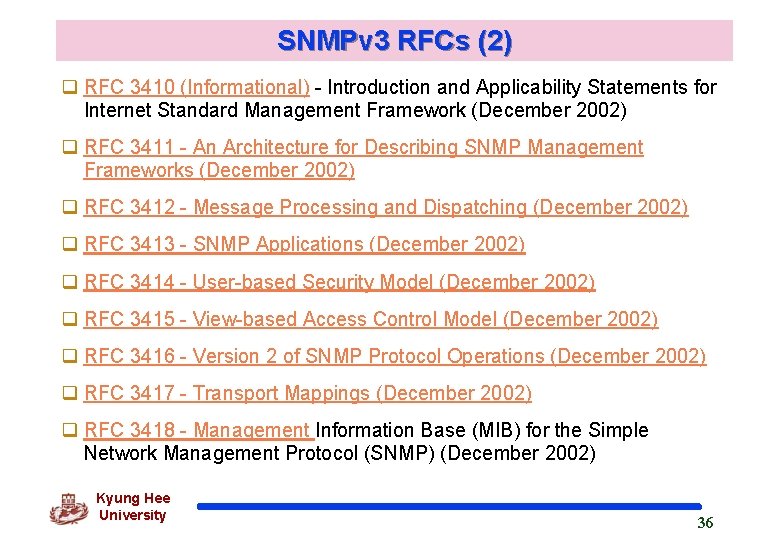
SNMPv 3 RFCs (2) q RFC 3410 (Informational) - Introduction and Applicability Statements for Internet Standard Management Framework (December 2002) q RFC 3411 - An Architecture for Describing SNMP Management Frameworks (December 2002) q RFC 3412 - Message Processing and Dispatching (December 2002) q RFC 3413 - SNMP Applications (December 2002) q RFC 3414 - User-based Security Model (December 2002) q RFC 3415 - View-based Access Control Model (December 2002) q RFC 3416 - Version 2 of SNMP Protocol Operations (December 2002) q RFC 3417 - Transport Mappings (December 2002) q RFC 3418 - Management Information Base (MIB) for the Simple Network Management Protocol (SNMP) (December 2002) Kyung Hee University 36