Chapter 14 System Administration Chapter 14 System Administration
- Slides: 40
Chapter 14 System Administration
Chapter 14 System Administration Chapter Outline System Administration Focus - A Standard Hardware Platform? The Acquisition Process Determining Requirements and Evaluating Performance Focus - Windows XP and Server Performance Monitoring Security Physical Environment
Chapter Goals Describe system administration responsibilities and tasks Explain the process of acquiring computer hardware and system software Describe tools and processes for evaluating application resource requirements and computer system performance Define a system security model and describe how it can be implemented Understand issues related to installing and protecting computer hardware
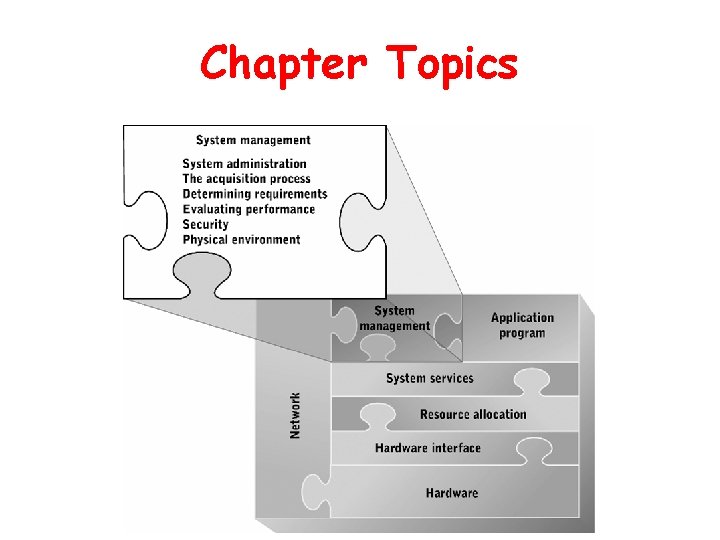
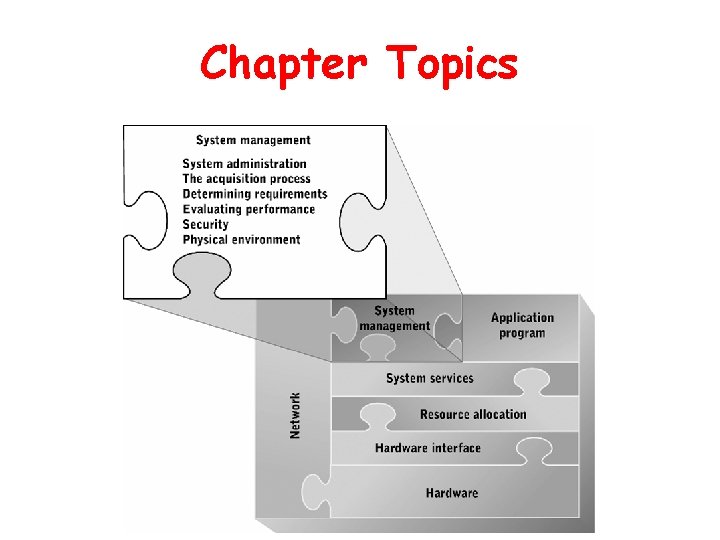
Chapter Topics
System Administration • Primary responsibility – Ensure efficient and reliable delivery of IS services • Broad categories of tasks – Acquiring new IS resources – Maintaining existing IS resources – Designing and implementing an IS security policy • Varies among organizations
Strategic Planning • Goal-Plan Paradigm – Set long-range goals – Develop a plan to attain those goals • Tends to follow rather than lead strategic plans of other organizational units – IS serves business needs
Strategic Goals and Plans • Goals – Identify services to be provided and the resources needed to provide those services • Plan – Strategies for developing services and markets for them – Strategies for acquiring sufficient resources for operations and growth – Organizational structure and control
Hardware and Software as Infrastructure • Strategic issues relevant to IS – Services to be provided – Charging for services – Infrastructure composition – Infrastructure improvement and maintenance
Standards • Required when providing infrastructure-based services to a wide variety of users • Potential issues – – Tends to stifle innovation May fail to meet needs of some users Incompatibility Problems for users who need services at or near the leading edge of technology
Competitive Advantage • Technology can be applied to: – Provide services that competitors are unable to provide – Provide services of unusually high quality – Provide services at unusually low price – Generate services at unusually low cost • Restricted useful life due to: – Rapid technology changes – High cost for developers and early adopters
The Acquisition Process • Determine applications that will be supported • Specify hardware and software capability and capacity requirements • Draft and circulate a request for proposals (RFP) • Evaluate RFP responses • Negotiate purchase, installation, and/or maintenance contract
Request for Proposals (RFP) • Formal document sent to vendors • States requirements • Solicits proposals to meet requirements
Evaluating Proposals • Determine acceptability of each proposal • Rank acceptable proposals • Validate high-ranking proposals – Benchmarking
Determining Requirements and Evaluating Performance • Hardware requirements depend on hardware and system software resources required • Is application software going to be developed? – Yes: hardware and system software resource consumption can be measured – No: determining resource requirements is complex • use benchmark testing
Determining Requirements and Evaluating Performance • Mathematical models for estimating computer requirements – Application demand model – Resource availability model
Benchmarks • Measure of computer system performance while executing specific processing tasks • Organizations that develop widely used benchmarks and perform computer system testing – SPEC (Standard Performance Evaluation Corporation) – TPC (Transaction Processing Performance Council)
Measuring Resource Demand Utilization • Hardware and software monitors – Detect and report processing or I/O activity – Operate continuously or intermittently – Help identify performance bottlenecks • Program profilers – Describe resource or service utilization of an application program during execution
Windows XP and Server Performance Monitoring • System Monitor (SM) – Monitors hardware and software resource use in real time – Captures performance and utilization data for defined objects • Each object has a set of counters – Has many display options
Security • Well-integrated approach protects hardware, software, and data resources against accidental loss or damage, malicious tampering, unauthorized access, and accidental disclosure • First line of defense: – Authentication and authorization • Other defensive measures: – Password control – Auditing – Virus protection – Regular software updates – Firewalls
Physical Security • Restrict access to prevent theft, tampering, and unauthorized access – Lock doors – Limit distribution of keys, key cards, etc. – Reinforce doors and walls – Lock equipment to desks
Access Controls • Based on two key processes – Authentication (verifies identity) • Password-based most common • Biometric – Authorization (verifies rights) • Based on security tickets • Access control list
Password Controls and Security • Ways to enhance password-based authentication – Restrictions on length and composition of valid passwords – Requirements that passwords periodically be changed – Analysis of password content to identify passwords that are easily guessed – Encryption of passwords in files and during transmission over a network
Auditing • Process of creating and managing records of user activity or resource access • Useful tool for examining security policy and analyzing security breaches
Limitations of Auditing • Size of logs – Auditing log files can grow very large • Reduction in system performance – Auditing uses lots of system resources • Poor tool for prevention – Auditing is backward-looking • Difficult to use – Automated search tools required to extract useful information
Viruses • Programs or program fragments that: – Infect computer by permanently installing themselves in a hard-to-find location – Perform malicious acts on infected computer – Replicate and spread using services of infected computer • Types: boot virus, macro virus, worm
Virus Protection • Common features of antivirus software – Scans e-mail messages and attachments for known viruses; disables or deletes them – Monitors access to important system files and data structures and logs or denies access as appropriate – Scans removable media for known viruses when they are inserted – Periodically scans file system and important data structures for viruses
Software Updates • Fix bugs, errors, and security holes as they are discovered • Used to be a manual process; now typically automated
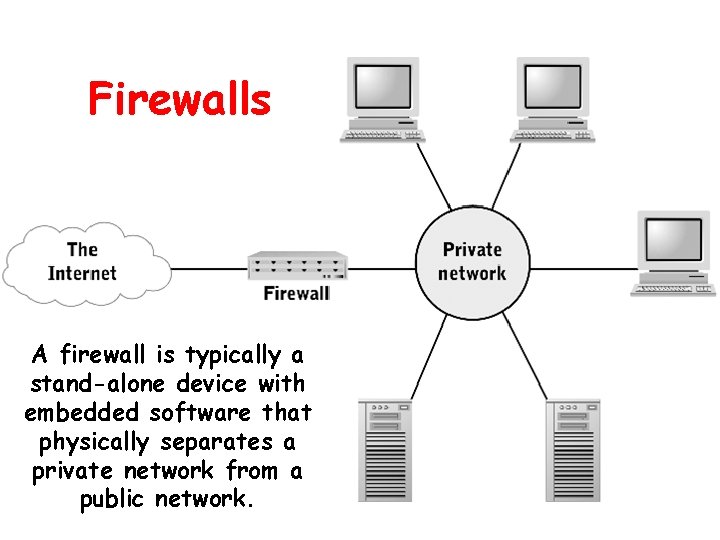
Firewalls • Hardware devices, software, or a combination that prevents unauthorized users in one network from accessing resources on another network • A firewall is typically a stand-alone device with embedded software that physically separates a private network from a public network.
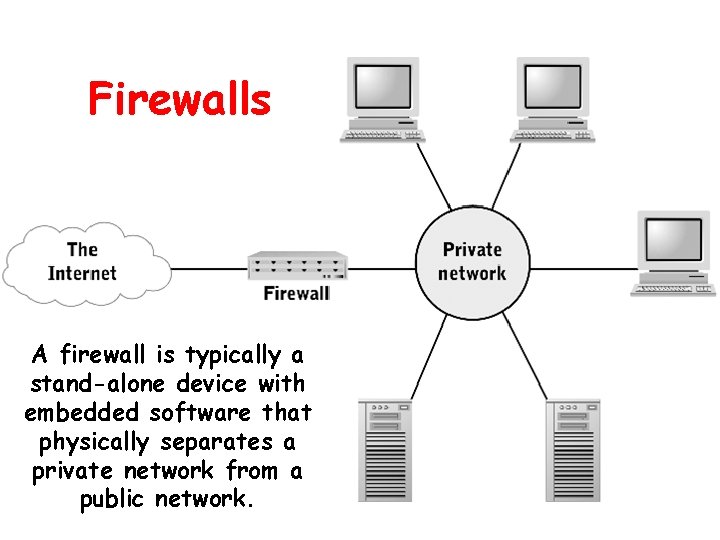
Firewalls A firewall is typically a stand-alone device with embedded software that physically separates a private network from a public network.
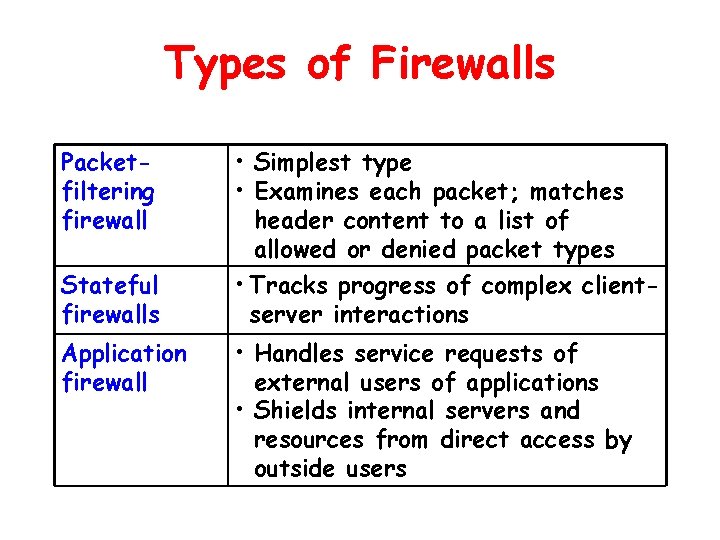
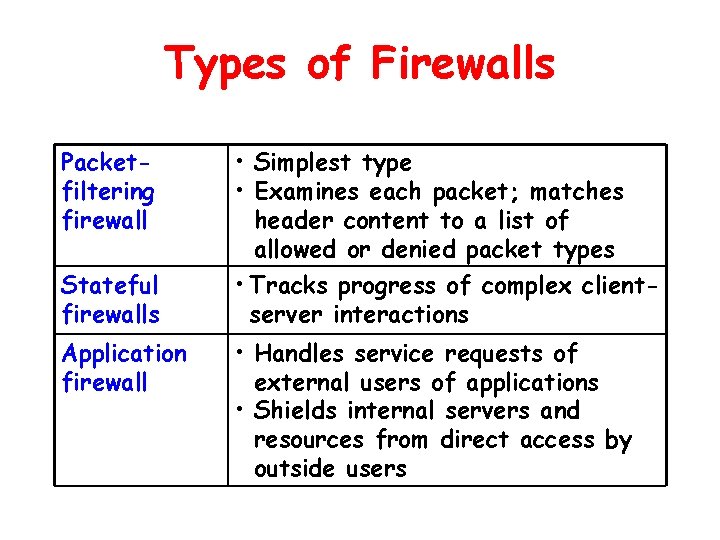
Types of Firewalls Packetfiltering firewall Stateful firewalls Application firewall • Simplest type • Examines each packet; matches header content to a list of allowed or denied packet types • Tracks progress of complex clientserver interactions • Handles service requests of external users of applications • Shields internal servers and resources from direct access by outside users
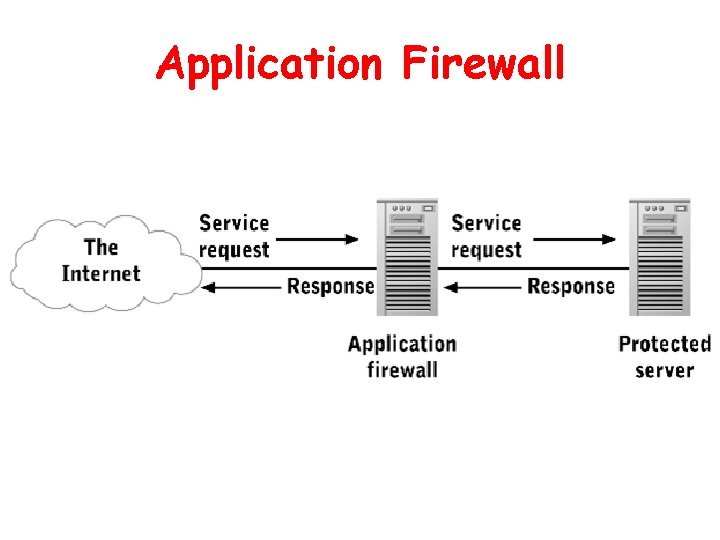
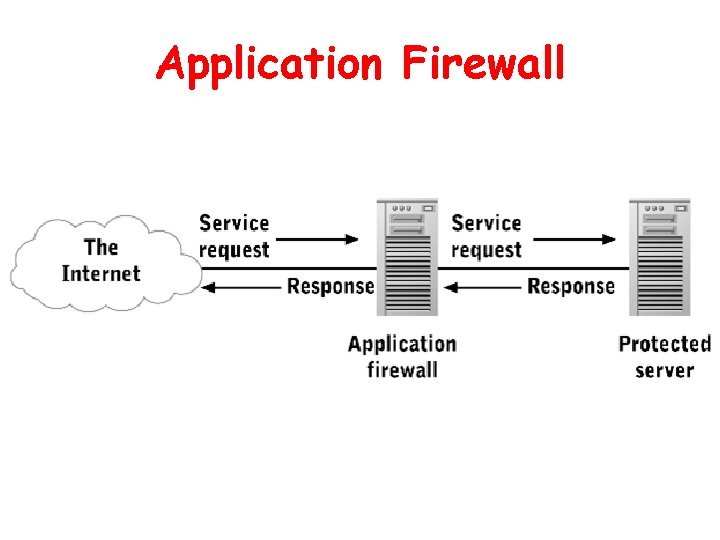
Application Firewall
Physical Environment • Considerations when choosing or preparing a location for computer hardware – Electrical power – Heat dissipation – Moisture – Cable routing – Fire protection
Electrical Power • Fluctuations can cause momentary loss of operation or damage to electrical circuits • Types of fluctuations – Momentary power surges • surge protector – Momentary power sags – Long-term voltage sags – Total loss of power • auxiliary power source, such as USP
Heat Dissipation • Excessive heat can cause intermittent or total failure of electrical circuits • Means of heat dissipation – Vents or fans on the computer itself – Cooling the room – Auxiliary cooling of cabinet
Moisture • Excessive moisture – Danger of short circuits • Low humidity – Buildup of static electricity • Protective measures – Well-designed cabinets protect against spills and leaks – Mount hardware above floor level – Control humidity with optional components of heating, ventilation, and air conditioning systems
Cable Routing • Provide protection and ease of access with: – Raised floors – Dedicated cable conduits
Fire Protection • Protection – Carbon dioxide – Fire retardant foams and powders – Gaseous compounds • Supplemental detection equipment within computer room
Disaster Planning and Recovery • Periodic data backup and storage of backups at alternate sites • Backup and storage of critical software at alternate sites • Installing duplicate or supplementary equipment at alternate sites • Arrangements for leasing existing equipment at alternate sites
Summary • System administration • The acquisition process • Determining requirements • Evaluating performance • Security • Physical environment
Chapter Goals Describe system administration responsibilities and tasks Explain the process of acquiring computer hardware and system software Describe tools and processes for evaluating application resource requirements and computer system performance Define a system security model and describe how it can be implemented Understand issues related to installing and protecting computer hardware