Chapter 13 Security Privacy and Ethics Why and
- Slides: 37
Chapter 13 Security, Privacy, and Ethics Why and what managers need to know about IT risk management, privacy, and information systems ethics. 1
Course Roadmap • • Part I: Foundations Part II: Competing in the Internet Age Part III: The Strategic use of Information Systems Part IV: Getting IT Done – – Chapter 10: Funding Information Systems Chapter 11: Creating Information Systems Chapter 12: Information System Trends Chapter 13: Security, Privacy and Ethics 2
Learning Objectives 1. Learn to make the case that information systems security, privacy, and ethics are issues of interest to general and functional managers, and why it is a grave mistake to delegate them exclusively to IT professionals. 2. Understand the basic IT risk management processes, including risk assessment, risk analysis, and risk mitigation. 3. Understand the principal security threats, both internal and external, and the principal safeguards that have been developed to mitigate these risks. 4. Be able to identify the nature of privacy concerns that modern organizations face, and be able to articulate how general and functional managers can safeguard the privacy of their customers and employees. 5. Define ethics, apply the concept of ethical behavior to information systems decisions, and be able to articulate how general and functional managers can help ensure that their organization behaves ethically. 3
Introduction • Information systems security, privacy, and ethical concerns were born along with the introduction of computer systems and information technology in organizations • The recent widespread adoption of the Internet and the proliferation of information for business use have dramatically amplified these threats • A failure in security, privacy, or ethics can have dramatic repercussions on the organization, both because of its potentially damaging direct effects (e. g. , computer outages, disruptions to operations) and its increasingly negative indirect effects (e. g. , legal recourse, image damage) 4
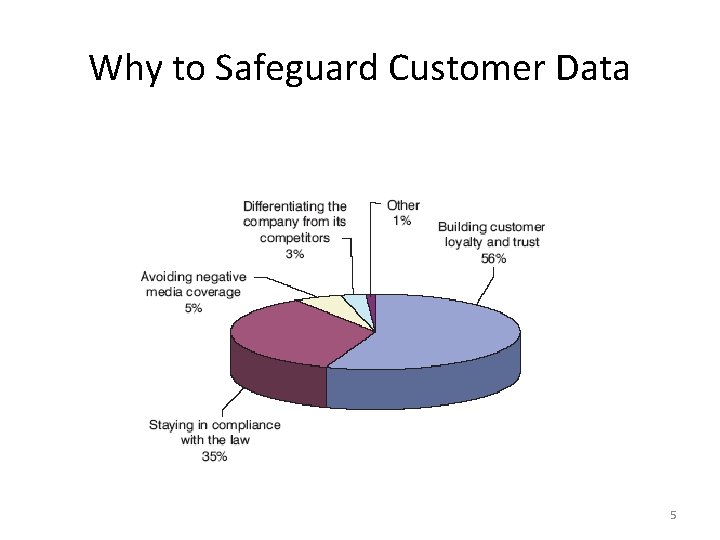
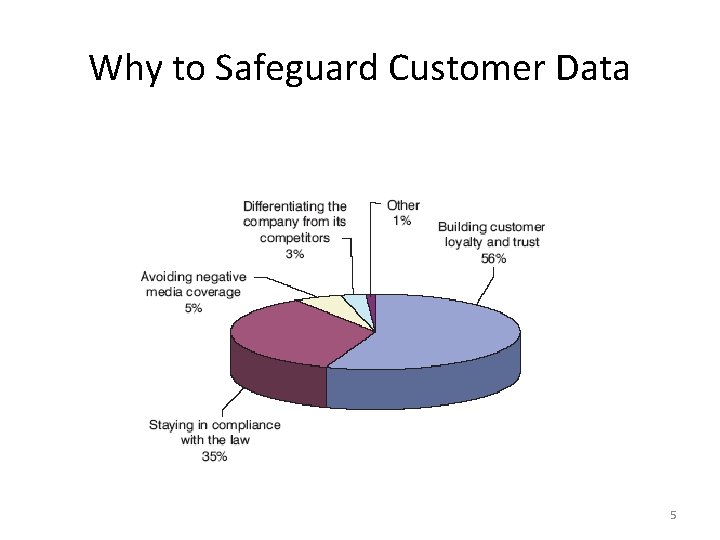
Why to Safeguard Customer Data 5
IT Risk Management and Security • IT Risk Management – The process of identifying and measuring information systems security risks – Objective: To devise the optimal risk mitigation strategy • Security – The set of defenses put in place to mitigate threats to technology infrastructure and data resources 6
Security: Not an IT Problem • Security should be a management priority, not an IT problem • Security is a negative deliverable – Produces no revenues – Creates no efficiencies • Security is difficult to fund – IT departments have limited budgets – They should not be left to fund security measures • The Trade-off: – Purchase more security or accept higher risks? 7
Risk Assessment • Audit the current resources • Map the current state of information systems security in the organization • The audit will: – Expose vulnerabilities – Provide the basis for risk analysis • Risk Analysis: – The process of quantifying the risks identifies in the audit 8
Risk Mitigation • The process of matching the appropriate response to the security threats your firm identified • Designed to help manage the trade-off between the degree of desired security and the investment necessary to achieve it 9
Three Risk Mitigation Strategies • Risk Acceptance – Not investing in countermeasures and not reducing the security risk – Consciously taking the risk of security breach • Risk Reduction – Actively investing in the safeguards designed to mitigate security threats – Consciously paying for security protection • Risk Transference – Passing a potion (or all) of the risks associated with security to a third party – Consciously paying for someone else to assume the risk 10
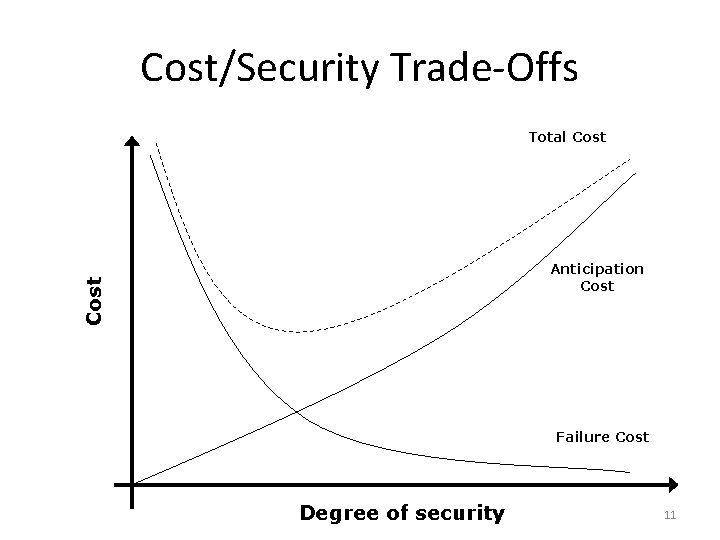
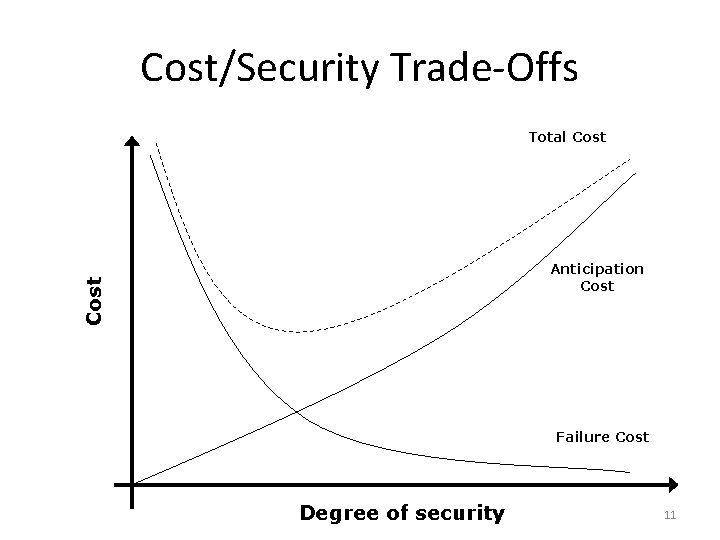
Cost/Security Trade-Offs Total Cost Anticipation Cost Failure Cost Degree of security 11
Internal Threats • Intentional Malicious Behavior – Typically associated with disgruntled or ill-willed employees – Example: A marketing employee selling customers’ e-mail addresses to spammers • Careless Behavior – Associated with ignorance of or disinterest in security problems – Example: Failing to destroy sensitive data according to planned schedules 12
External Threats • Intrusion Threat – An unauthorized attacker gains access to organizational IT resources • Social Engineering – Lying to and deceiving legitimate users so that they divulge restricted or private information • Phishing – Sending official sounding spam from known institutions and asking individuals to confirm private data in an effort to capture the data 13
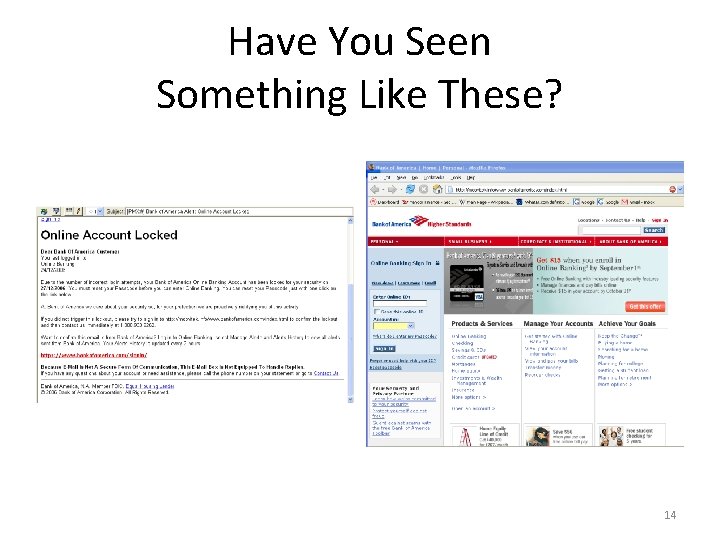
Have You Seen Something Like These? 14
The External Threats • Security Weaknesses – Exploiting weaknesses in the software infrastructure of the organization under attack – Example: Bugs that enable unauthorized access • Backdoors – Code expressly designed into software programs to allow access to the application by circumventing password protection 15
The External Threats • Malicious Code – Any software code expressly designed to cause damage to IT assets. • Viruses – Malicious code that spreads by attaching itself to other, legitimate, executable programs. – After infecting a machine, a harmful set of actions, know as the payload, are performed 16
Malicious Code • Trojan Horses – A computer program that claims to, and sometimes does, deliver useful functionality – Delivers a hidden, malicious payload, after installation • Worms – Malicious code that exploits security holes in network software to self-replicate – Does not deliver a payload – Generates enough network traffic to slow or bring a network down 17
Malicious Code • Spyware – Software that, unbeknownst to the owner of the computer: • • Monitors behavior Collects information Either transfers this information to a third party or Performs unwanted operations – Diverts resources and often slow down a user’s legitimate work 18
The External Threats • Denial-of-Service Attack – A digital assault carried out over a computer network with the objective of overwhelming an online service so as to force it offline. – Can be used to divert attention allowing the intruder to create a backdoor to be exploited later 19
Responding to Internal Security Threats • Security Policies – Spell out what the organization believes are the behaviors that individual employees within the firm should follow in order to minimize security risks – They should specify: – Password standards – User right – Legitimate uses of portable devices – The firm should audit the policies to ensure compliance 20
Responding to External Security Threats • Intrusion – The cornerstone of securing against intrusion is the use of passwords – Firewalls can be used to screen and manage traffic in and out of a computer network • Only as strong as the weakest link – The Encryption process scrambles content so that it is rendered unreadable 21
Responding to External Security Threats • Malware – Safeguarding against malware requires that the firm’s IT professionals install detection software – Training and Policies are also necessary • Denial-of-Service Attacks – Preventing a denial-of-service attack is very difficult – It is difficult to identify the location of the attack 22
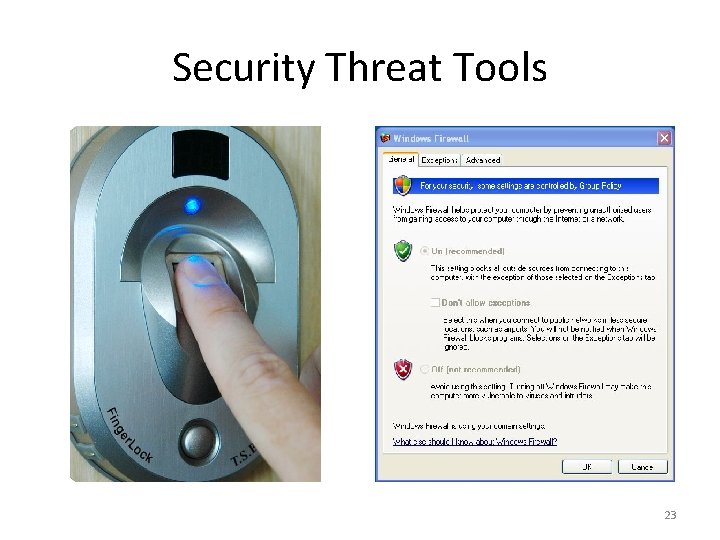
Security Threat Tools 23
Managing Security: Overall Guidelines • Have a plan and specify responsibilities – Who should be contacted in an emergency? – What should the first reaction measures be? • Revisit often – New technologies should be proactively addressed • Develop a mitigation plan – Determine how the attack took place – Assess the damage • Waiting for a crisis to take these decisions and develop policy is too late! 24
Privacy • The ability of individuals to control the terms and conditions under which their personal information is collected, managed, and utilized. • Private information can be traced back to the individual • Privacy subsumes security 25
Privacy Risks • Function Creep – Occurs when data collected for a stated or implied purpose are then reused for other, unrelated objectives. • Proliferating Data Sources – New technological advances and devices generate more data than ever – This proliferation creates opportunities but also many risks 26
Privacy Risks • Data Management Risks – It is increasingly simple, and cost effective, to merge data repositories – IT creates pressure for, and the risk of, function creep if not managed carefully • The Legal Landscape – Currently, technology evolution outpaces legal development – The internet has all but destroyed traditional geographical boundaries • Privacy management is not an IT job 27
Safeguarding Privacy • Fair Information Practice Principles – Notice • The right of individuals to be informed when their personal data is being collected • The right of individuals to be informed about how their data is or will be used. – Choice • The ability of individuals to be informed of, and object to, function creep whether within one firm or across firms who share information. 28
Safeguarding Privacy • Fair Information Practice Principles (cont) – Access • The right of individuals to be able to access their information and correct any errors that may have occurred in their records – Security • Organizations that house individuals’ private information must ensure its safekeeping and to protect it from unauthorized access. – Enforcement • Organizations that collect and use private information must develop enforceable procedures to ensure that the above principles are upheld. 29
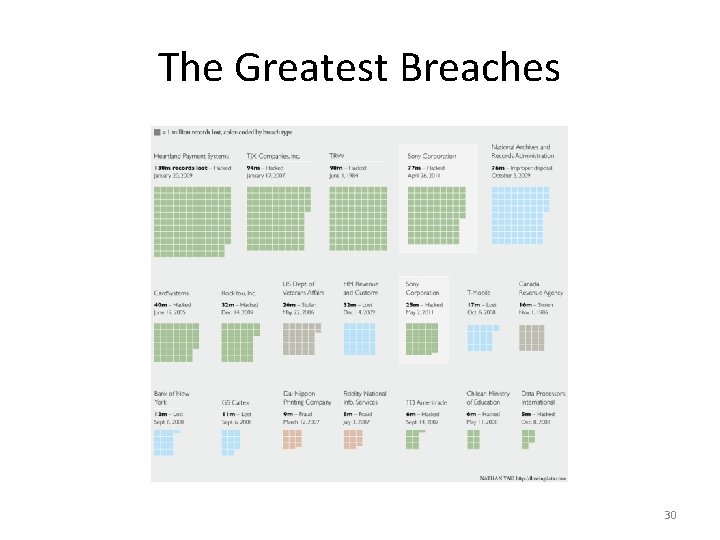
The Greatest Breaches 30
Fair Information Practice Principles • Fair Information Practice Principles – Access • The right of individuals to be able to access their information • The right of individuals to correct any errors that may have occurred in their records. – Security • The responsibility of the firm that houses private information to ensure its safekeeping and to protect it from unauthorized access. – Enforcement • The responsibility of the organizations that collect and use private information to develop enforceable procedure to ensure that the above principals are upheld. 31
Protecting Privacy • Say What You Do – The firm develop a codified set of policies and procedures for safeguarding privacy and communicates these policies to affected individuals (e. g. , customers, employees) • Do What You Say – Those who represent the firm know, understand, and can enact the policies the firm has developed • Be Able to Prove It – The firm document its policies and the processes it has developed to ensure privacy 32
Ethics • The discipline dealing with what is good and bad and with moral duty and obligation • The problem: – Ethical choices are rarely straightforward – Ethical choices typically engender multiple suboptimal options 33
Enabling IS Ethics • Developing a culture of ethical decision making is critical • Establish an information systems ethics code of conduct that: – Identifies the principles of ethical information system use for your organization – Identifies the firm’s formal stance on ethics • Apply the principle of harm minimization 34
The Recap • Information systems must be secured against both internal and external threats • Information systems security and risk management are not “IT issues” • Privacy concerns, like security threats, need general and functional managers’ full attention. 35
The Recap • In order for the firm to safeguard the privacy of its employees and customers, it must subscribe to fair information practices – – – Notice Choice Access Security Enforcement. • The recent flurry of corporate scandals has ignited interest in business ethics • When it comes to information systems, ethics becomes a crucial guiding light for management behavior as legislation often lags behind technology improvements 36
What did we Learned 1. Learn to make the case that information systems security, privacy, and ethics are issues of interest to general and functional managers, and why it is a grave mistake to delegate them exclusively to IT professionals. 2. Understand the basic IT risk management processes, including risk assessment, risk analysis, and risk mitigation. 3. Understand the principal security threats, both internal and external, and the principal safeguards that have been developed to mitigate these risks. 4. Be able to identify the nature of privacy concerns that modern organizations face, and be able to articulate how general and functional managers can safeguard the privacy of their customers and employees. 5. Define ethics, apply the concept of ethical behavior to information systems decisions, and be able to articulate how general and functional managers can help ensure that their organization behaves ethically. 37