Chapter 12 Multiple Access Http netwk hannam ac

- Slides: 72
Chapter 12 다중 접속 (Multiple Access) Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY
12 장 다중접속(Multiple Access) 12. 1 임의접속 12. 2 제어접속 12. 3 채널화 12. 4 요약 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 2
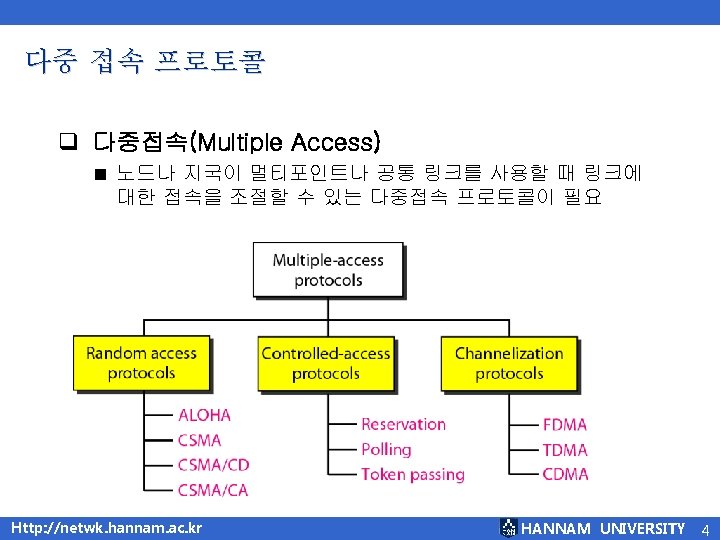
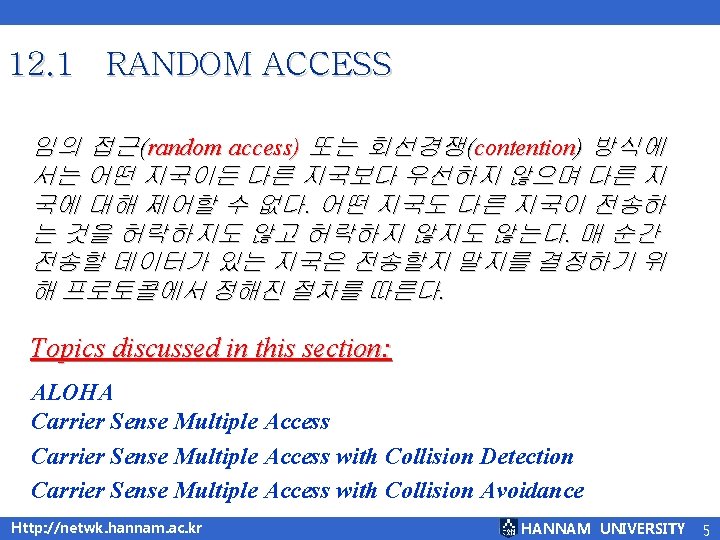
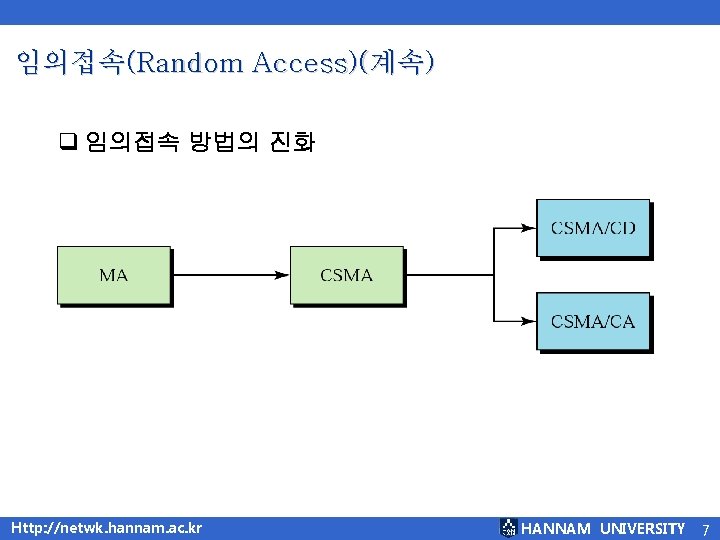
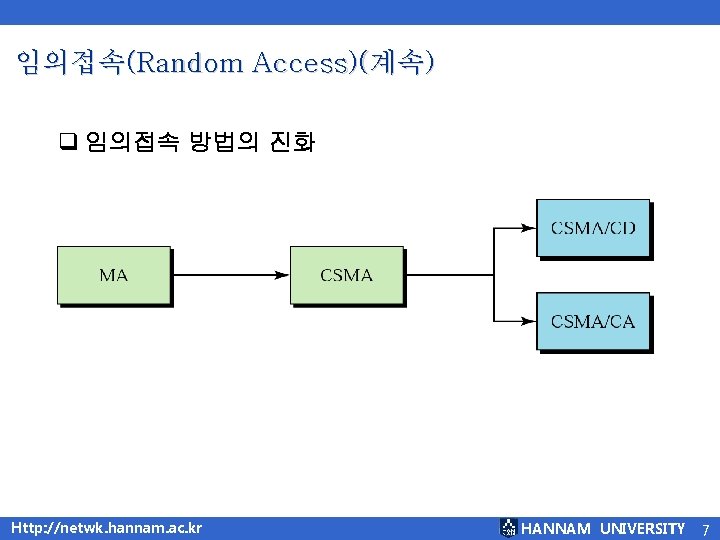
임의접속(Random Access)(계속) q 임의접속 방법의 진화 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 7
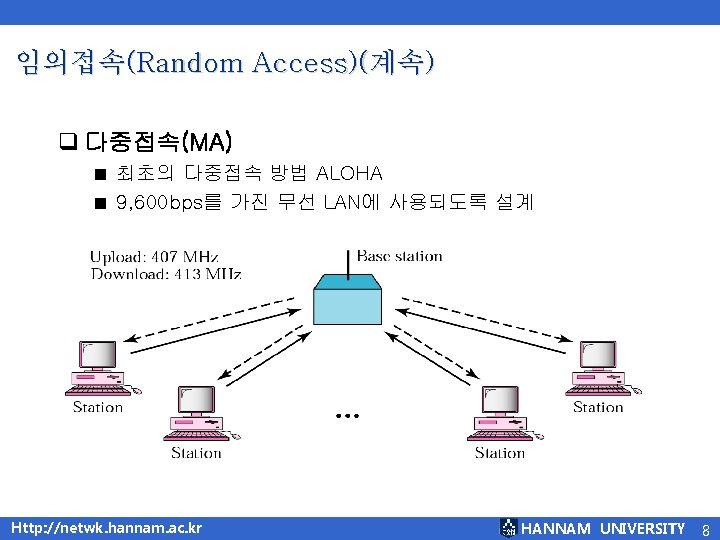
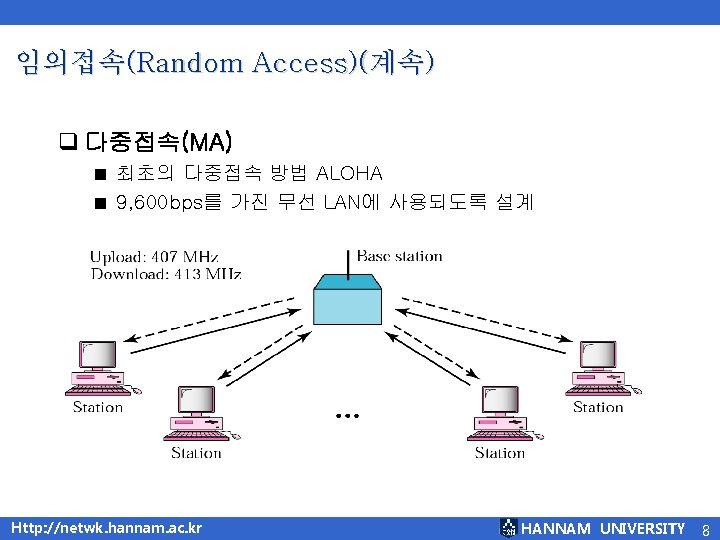
임의접속(Random Access)(계속) q 다중접속(MA) ■ ■ 최초의 다중접속 방법 ALOHA 9, 600 bps를 가진 무선 LAN에 사용되도록 설계 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 8
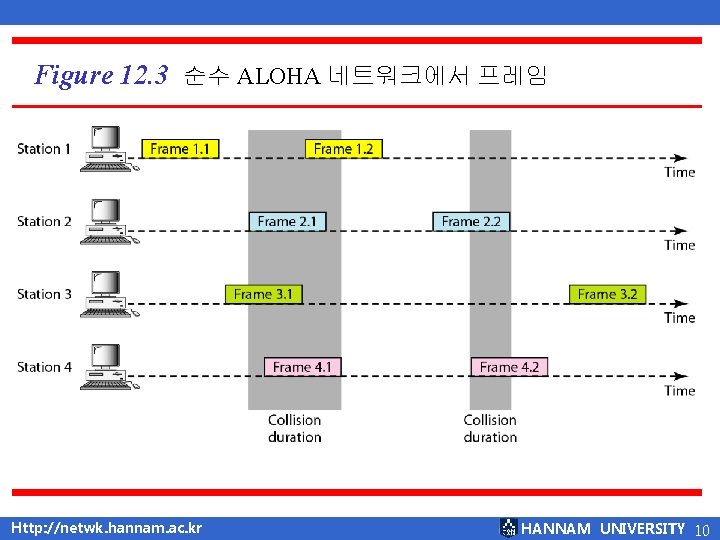
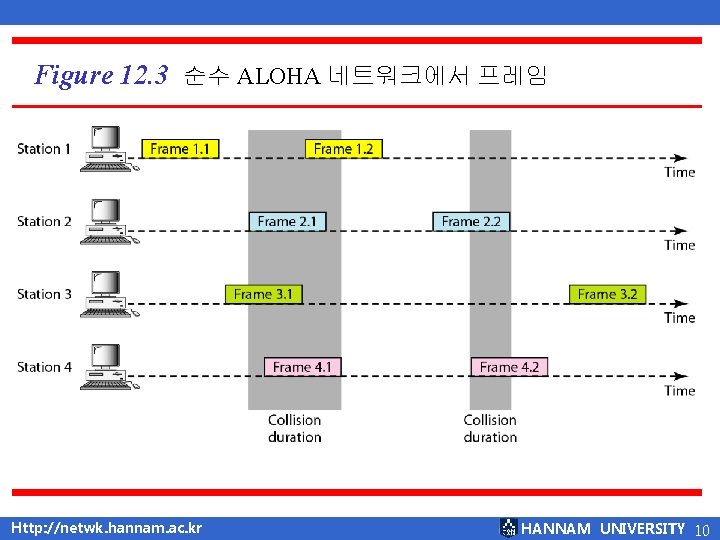
Figure 12. 3 순수 ALOHA 네트워크에서 프레임 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 10
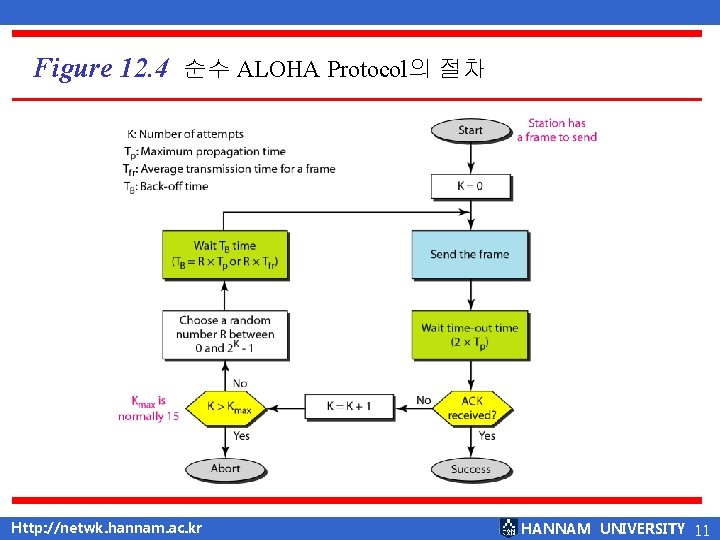
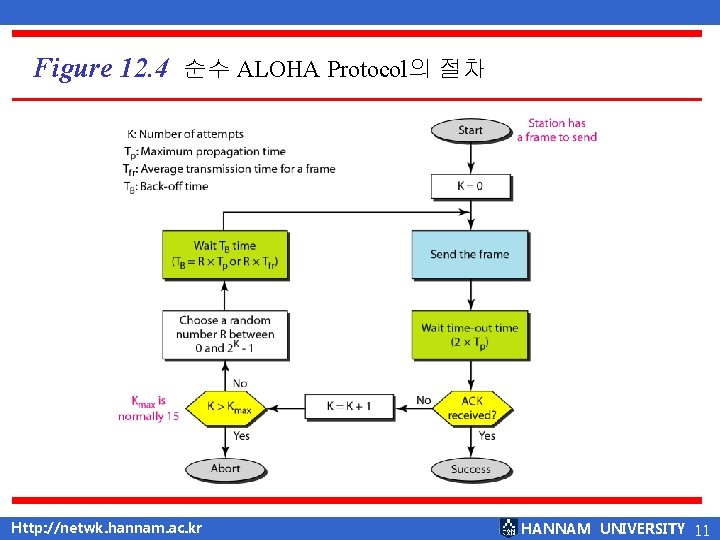
Figure 12. 4 순수 ALOHA Protocol의 절차 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 11
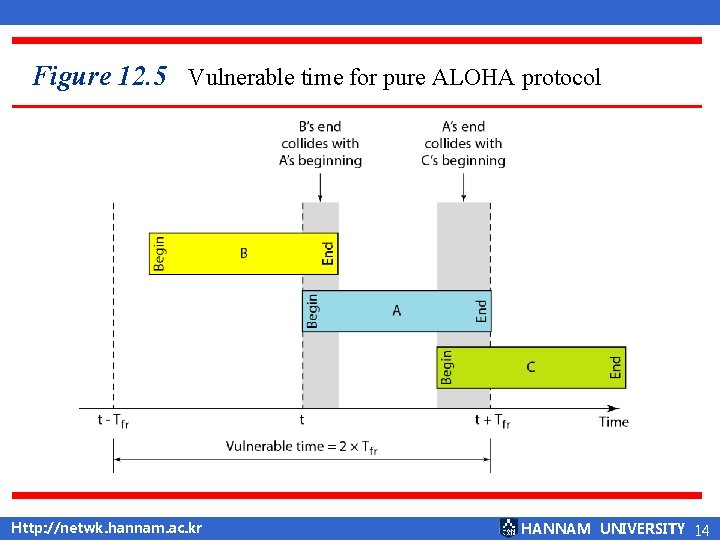
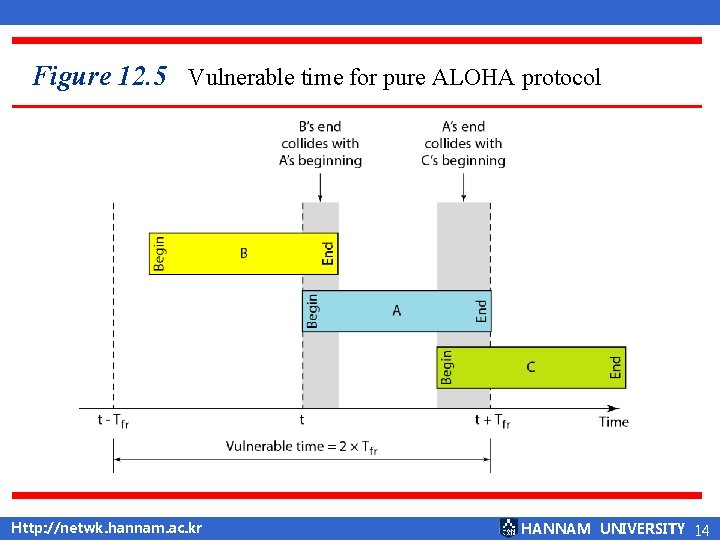
Figure 12. 5 Vulnerable time for pure ALOHA protocol Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 14
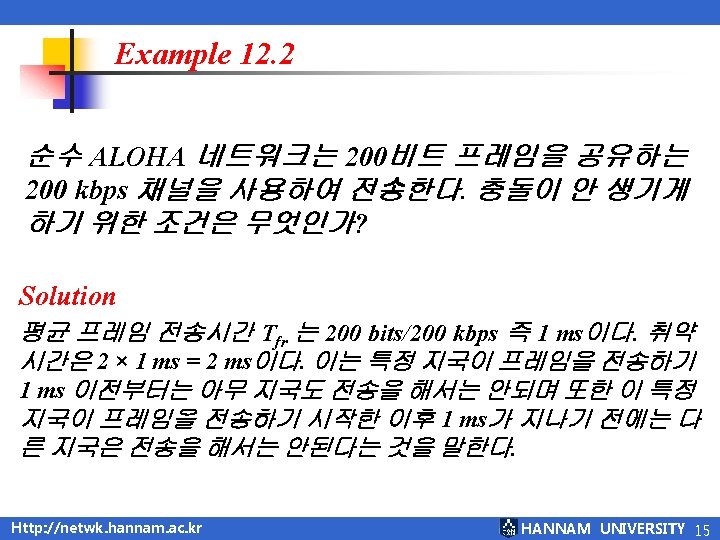
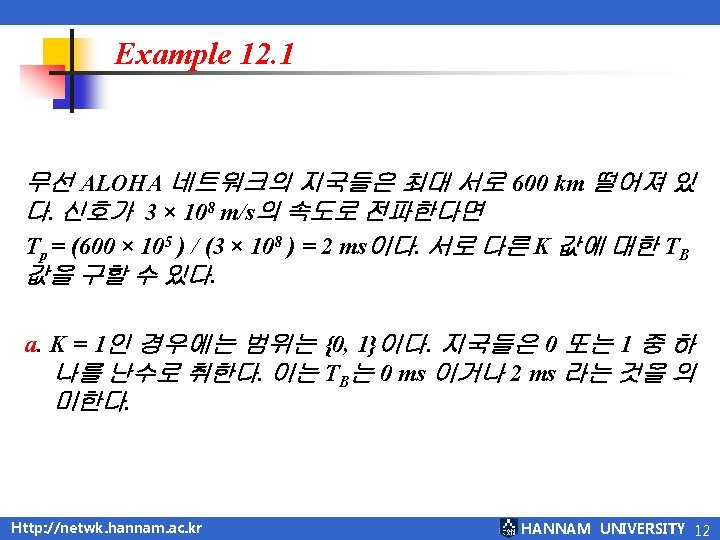
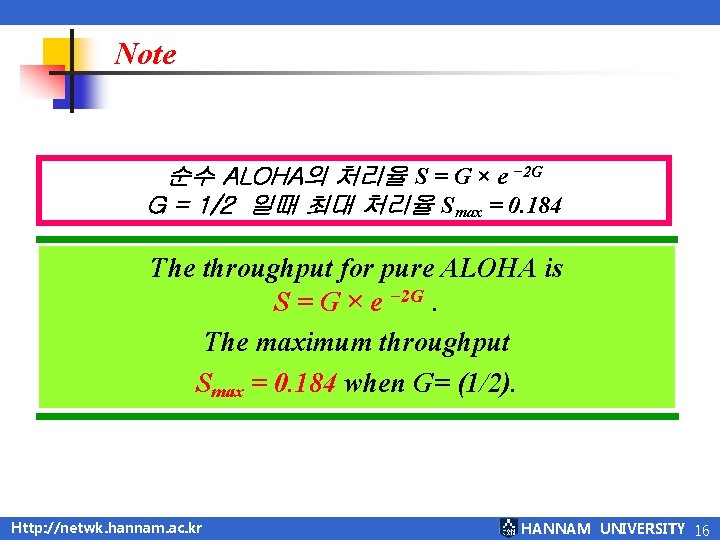
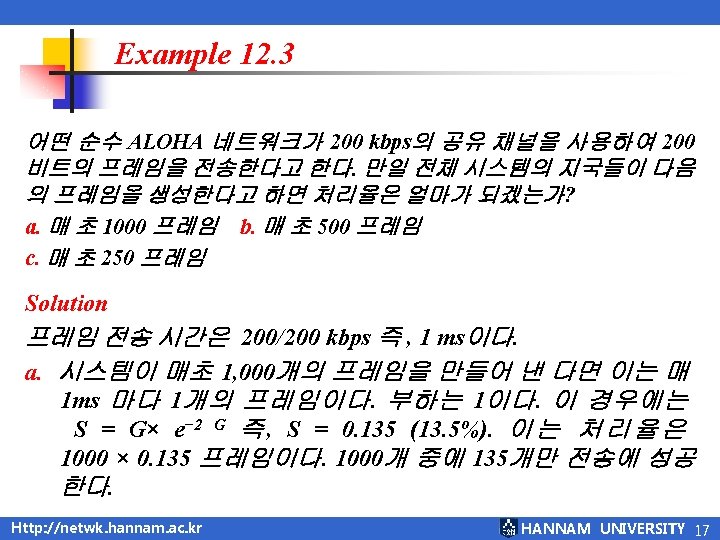
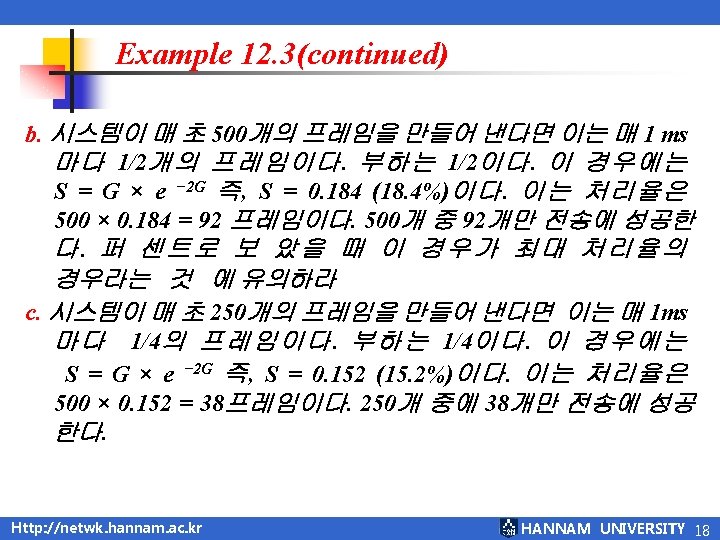
Note 순수 ALOHA의 처리율 S = G × e − 2 G G = 1/2 일때 최대 처리율 Smax = 0. 184 The throughput for pure ALOHA is S = G × e − 2 G. The maximum throughput Smax = 0. 184 when G= (1/2). Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 16
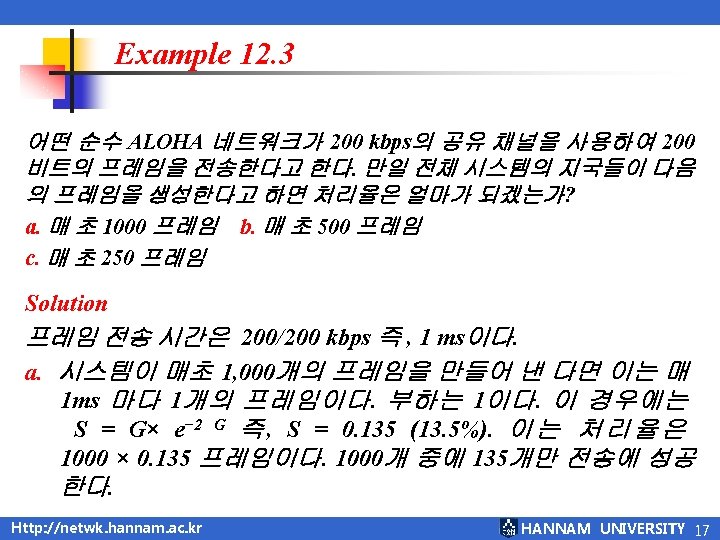
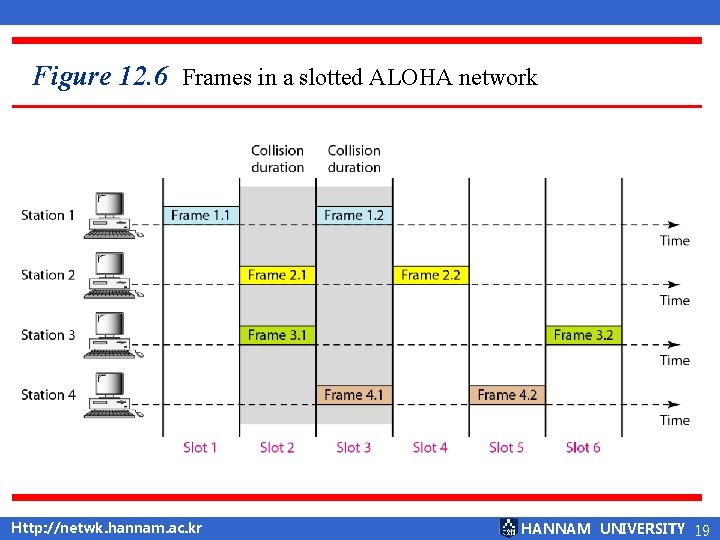
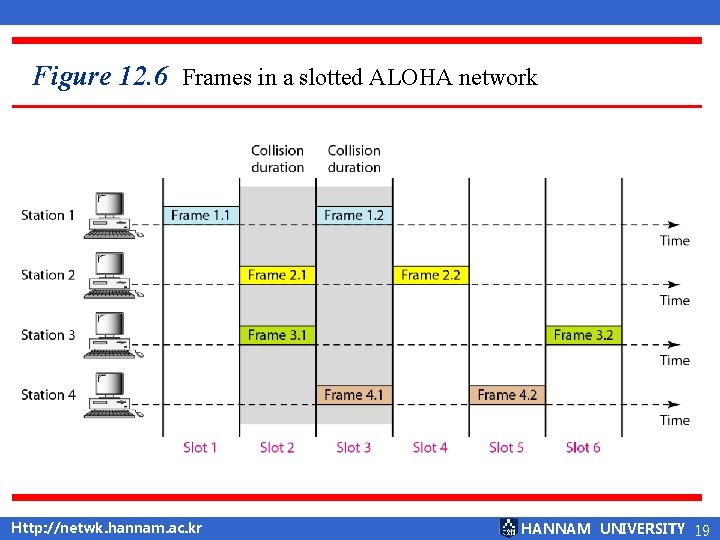
Figure 12. 6 Frames in a slotted ALOHA network Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 19
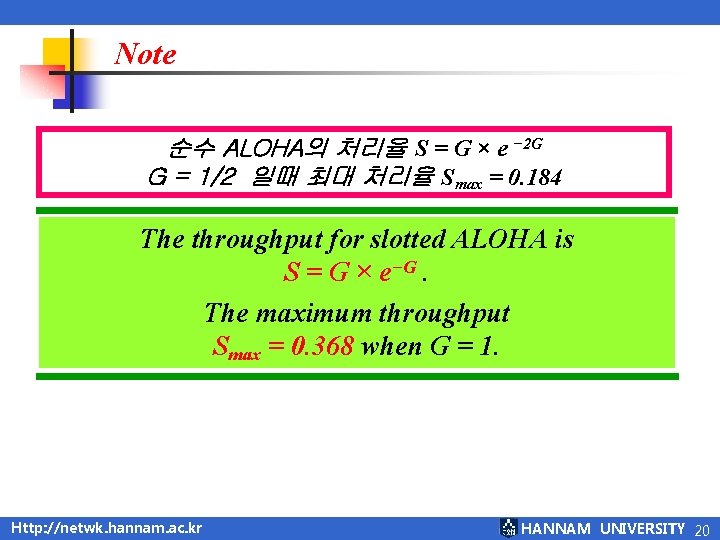
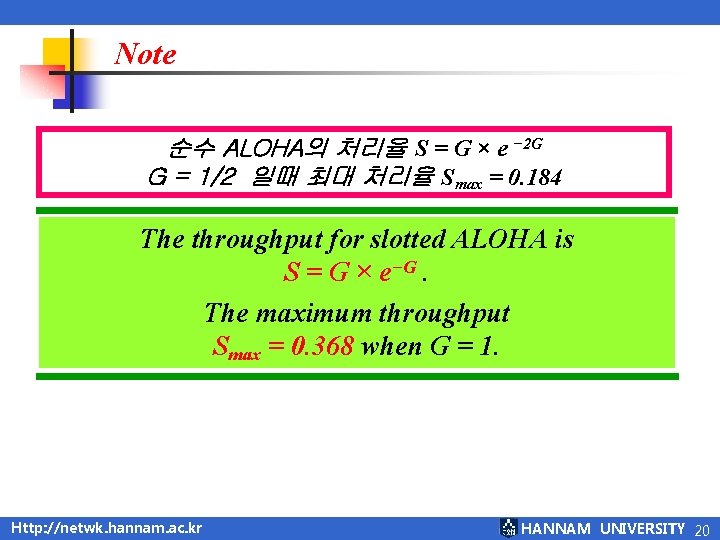
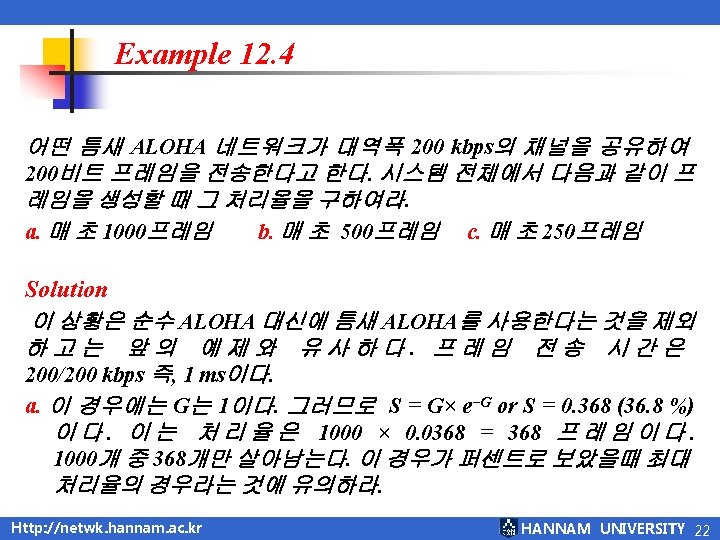
Note 순수 ALOHA의 처리율 S = G × e − 2 G G = 1/2 일때 최대 처리율 Smax = 0. 184 The throughput for slotted ALOHA is S = G × e−G. The maximum throughput Smax = 0. 368 when G = 1. Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 20
Figure 12. 7 Vulnerable time for slotted ALOHA protocol Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 21
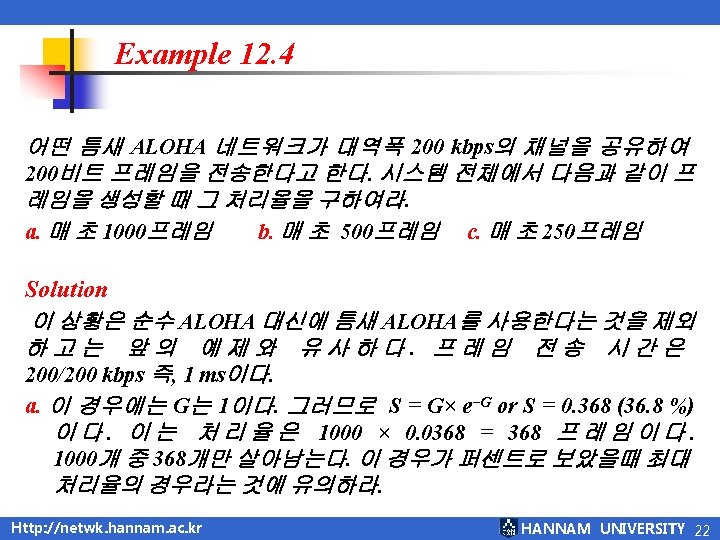
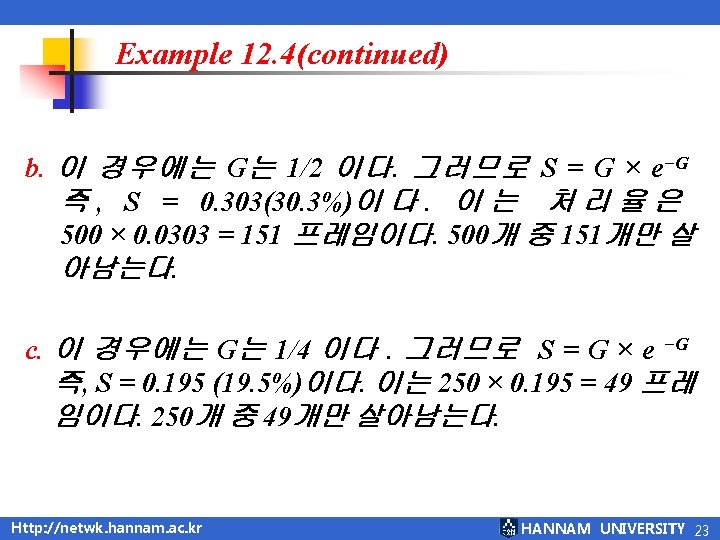

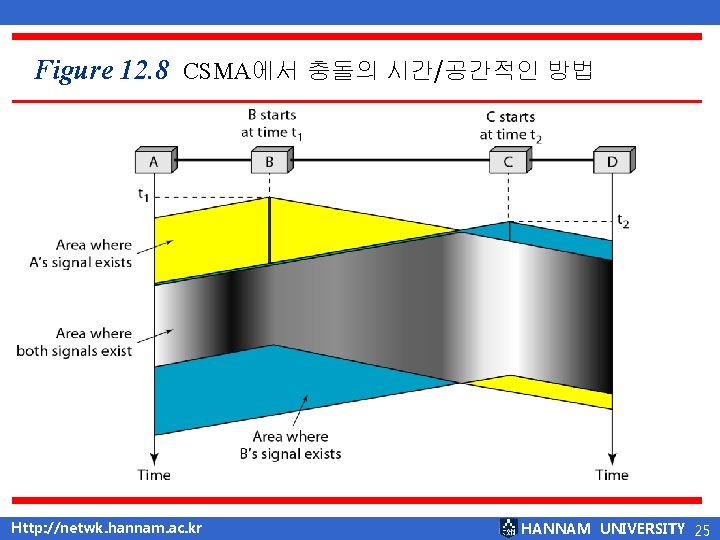
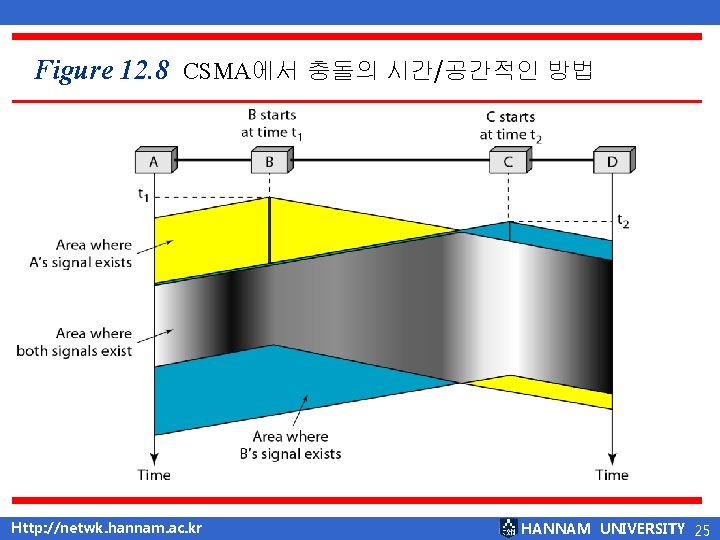
Figure 12. 8 CSMA에서 충돌의 시간/공간적인 방법 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 25
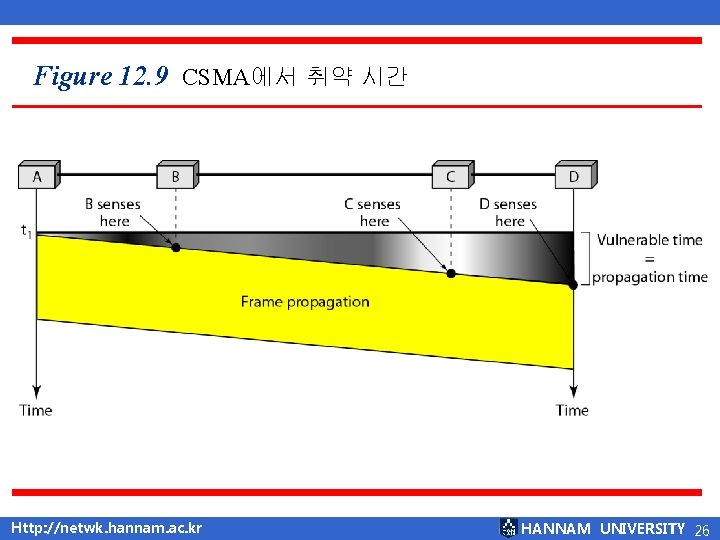
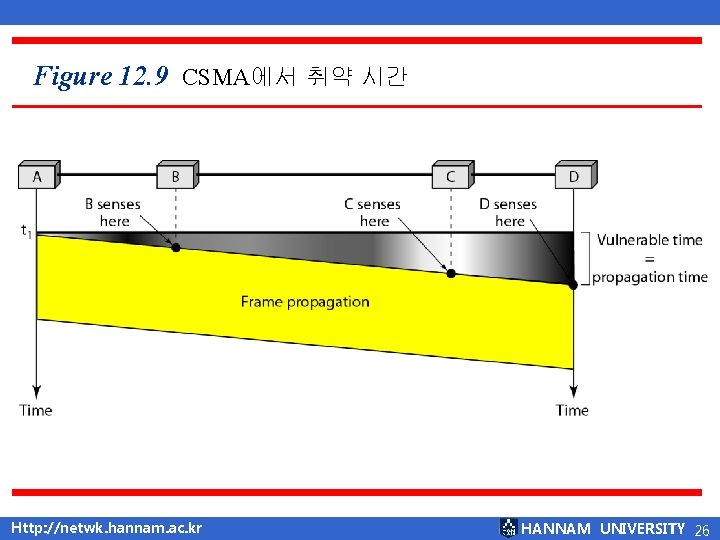
Figure 12. 9 CSMA에서 취약 시간 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 26
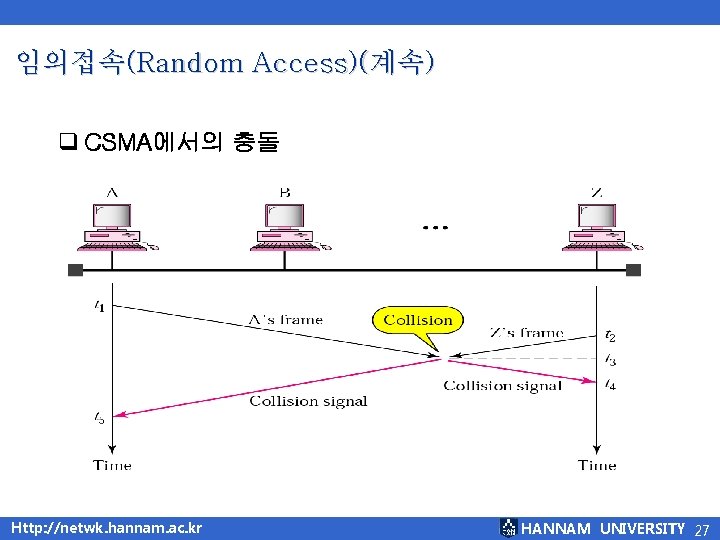
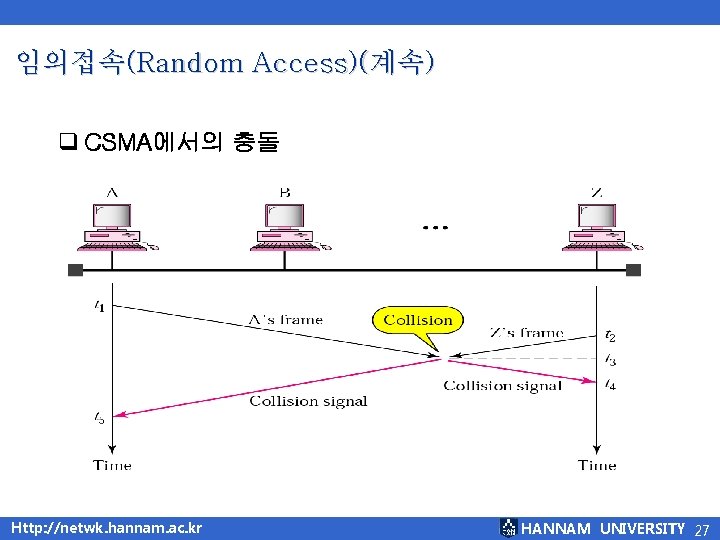
임의접속(Random Access)(계속) q CSMA에서의 충돌 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 27
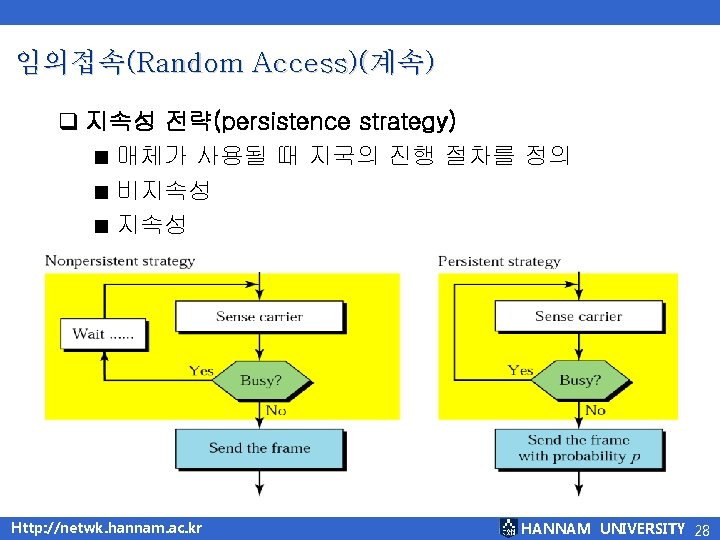
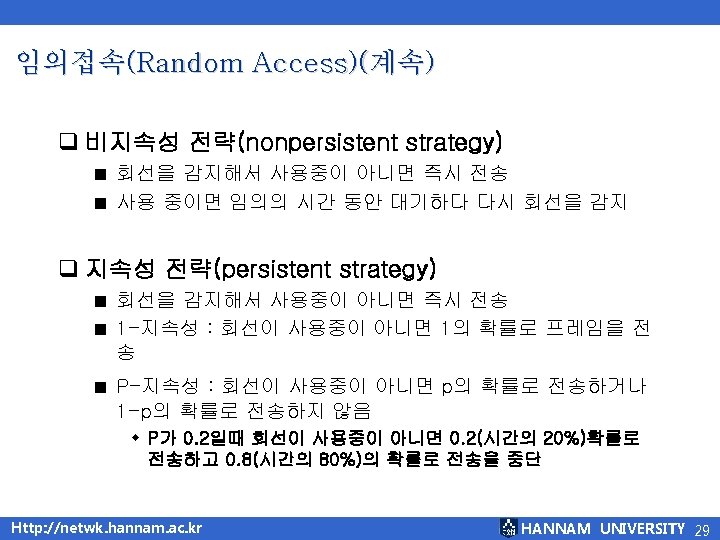
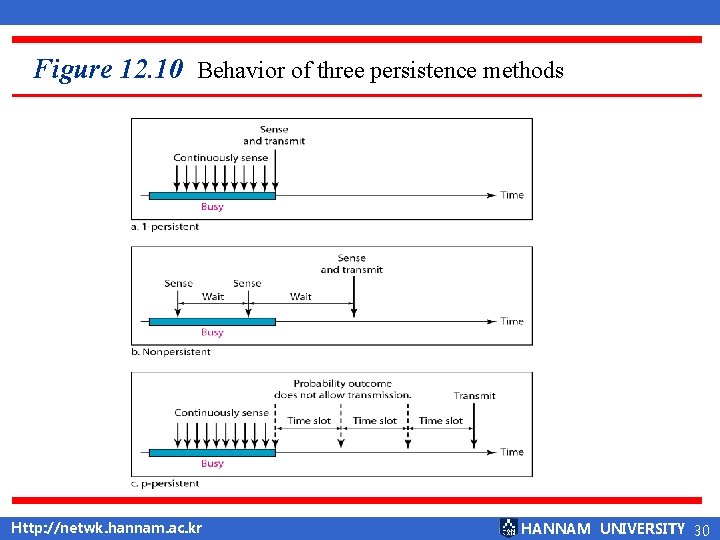
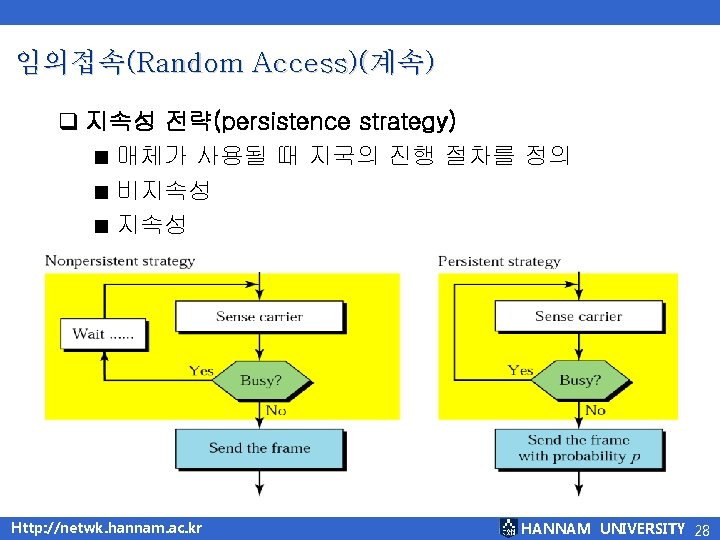
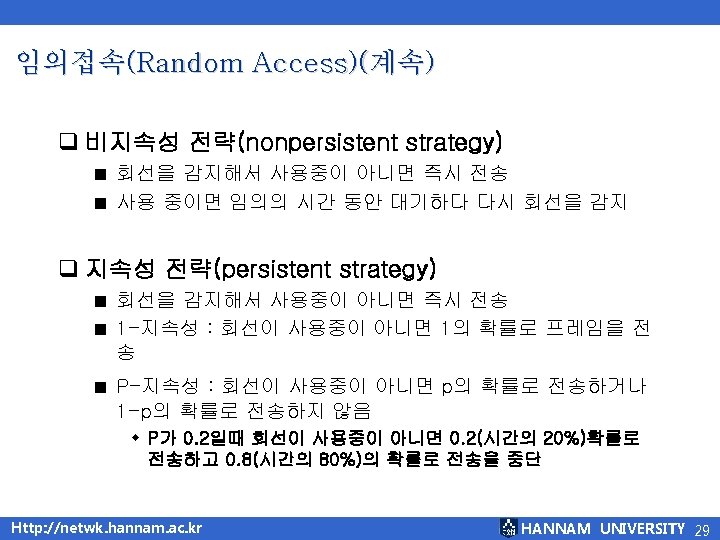
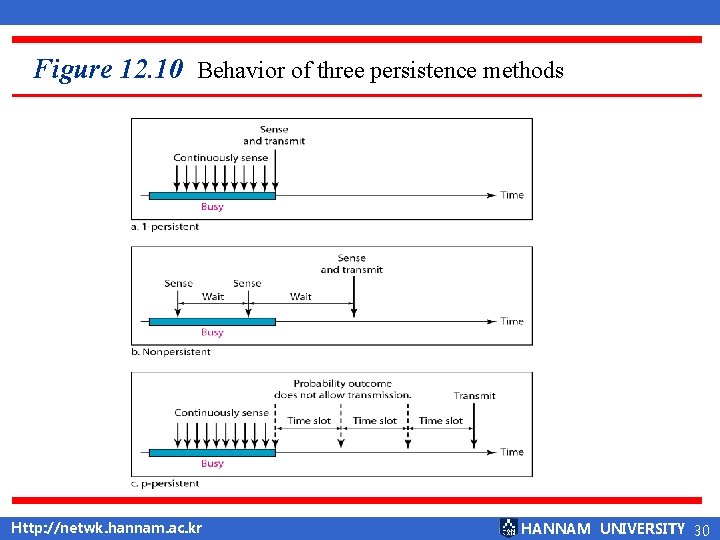
Figure 12. 10 Behavior of three persistence methods Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 30
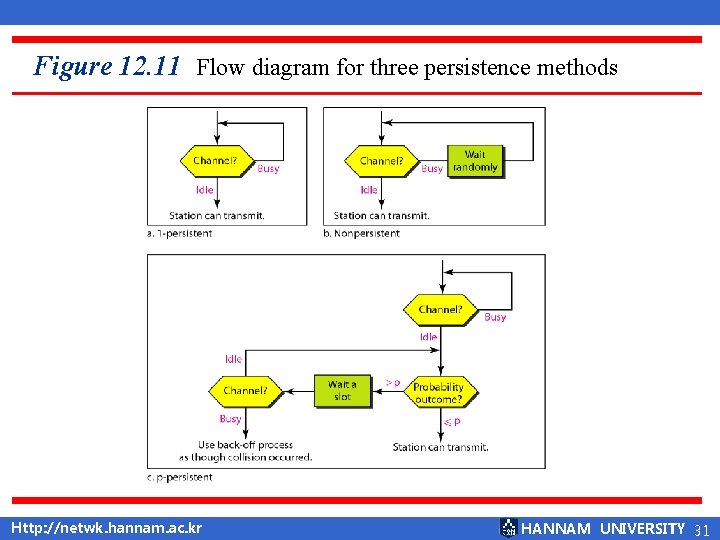
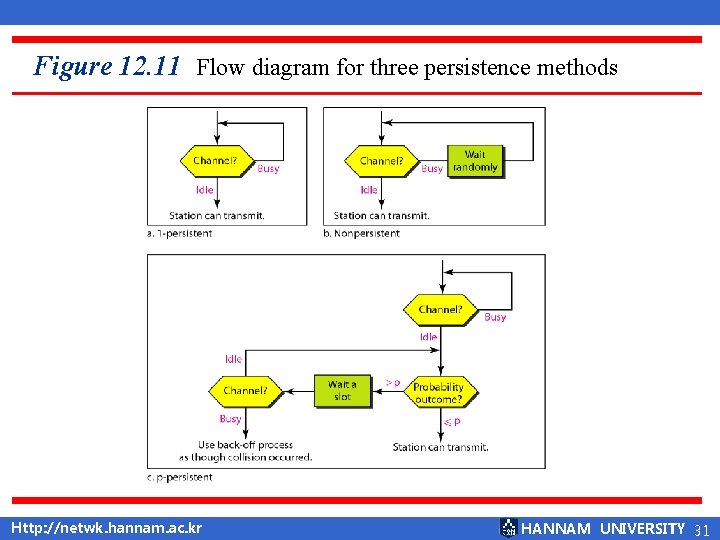
Figure 12. 11 Flow diagram for three persistence methods Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 31
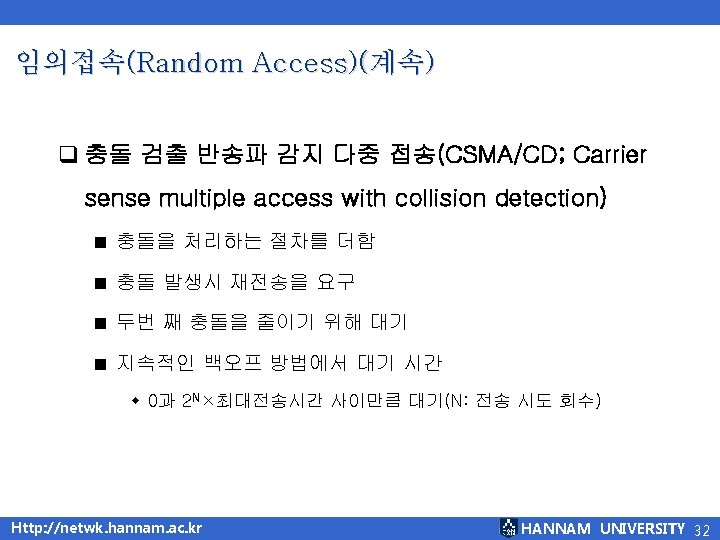
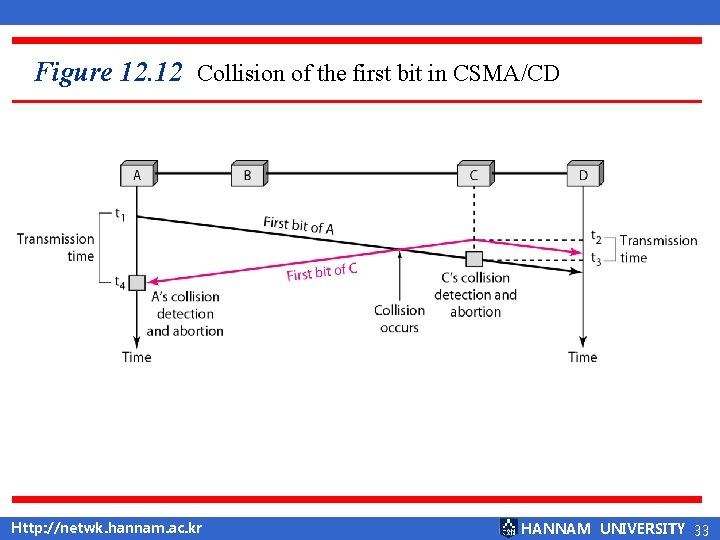
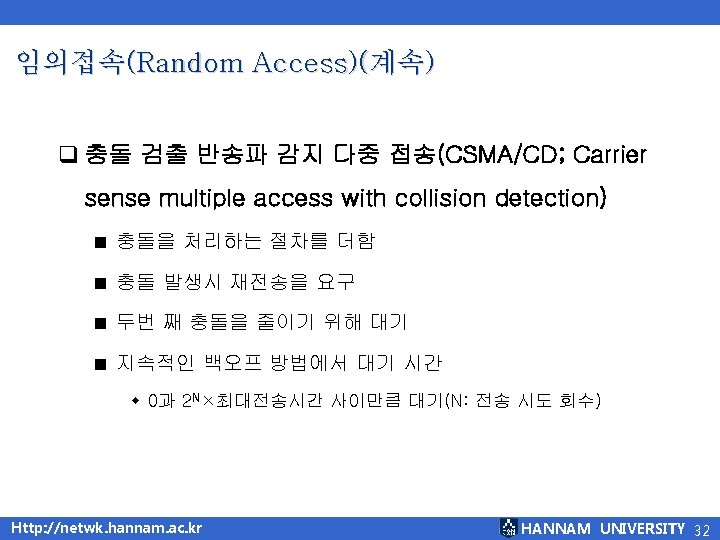
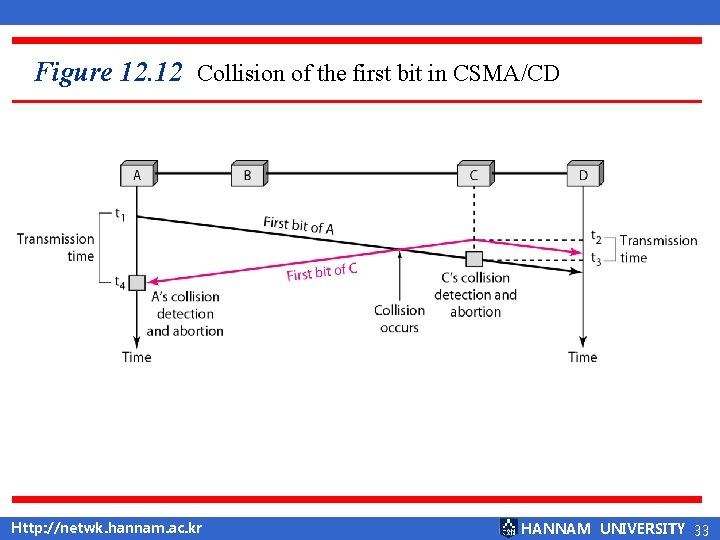
Figure 12. 12 Collision of the first bit in CSMA/CD Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 33
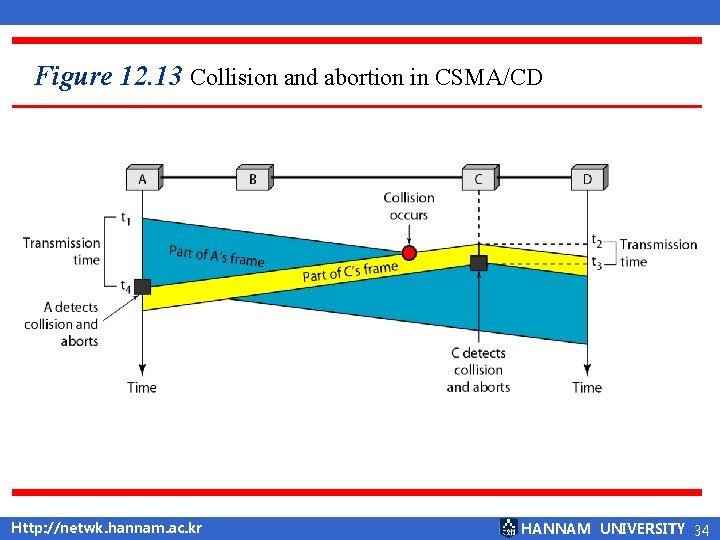
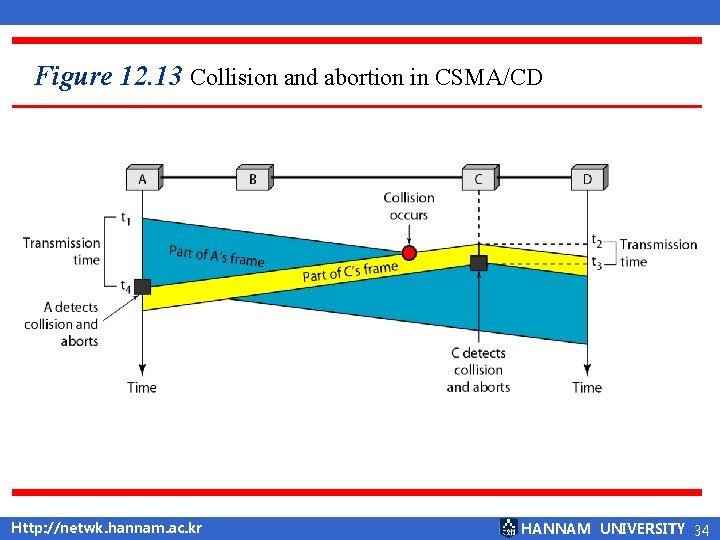
Figure 12. 13 Collision and abortion in CSMA/CD Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 34
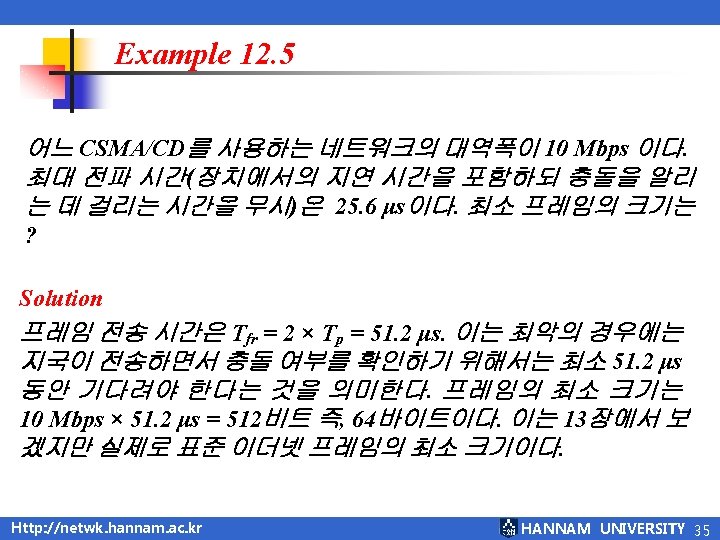
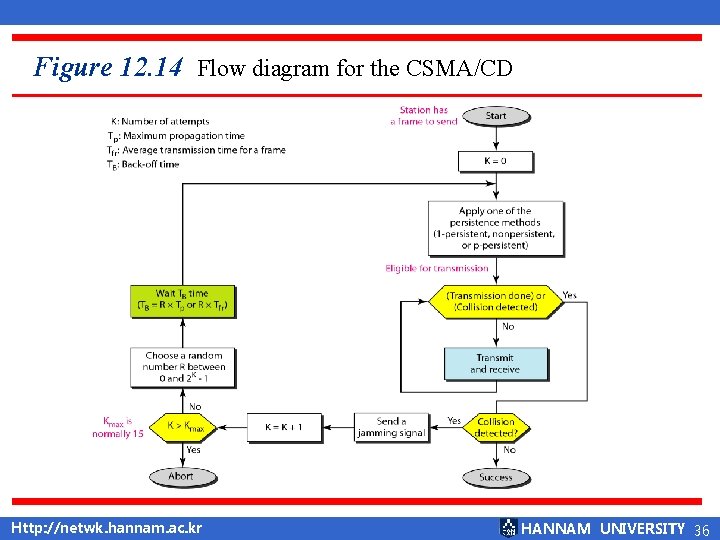
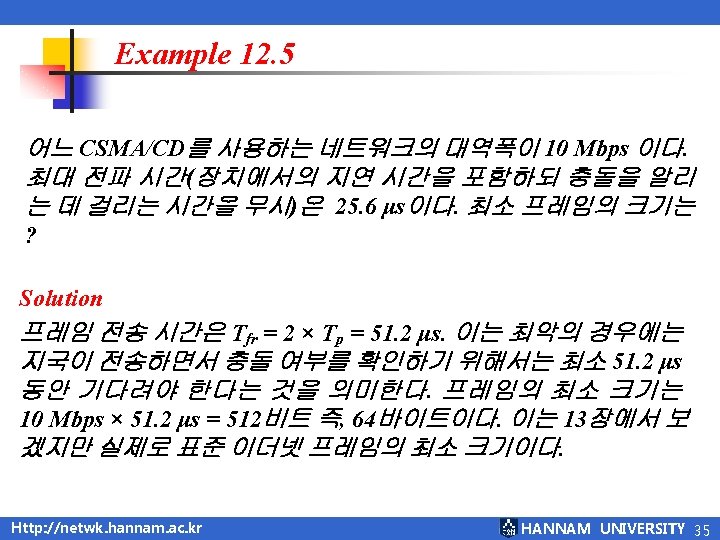
Figure 12. 14 Flow diagram for the CSMA/CD Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 36
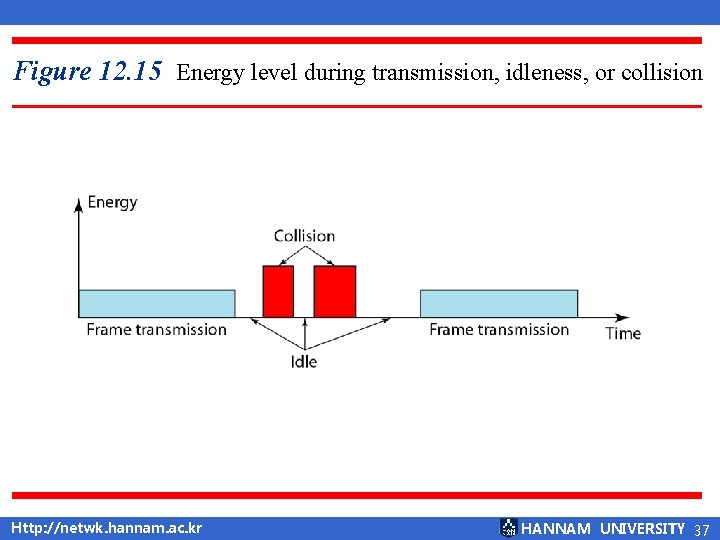
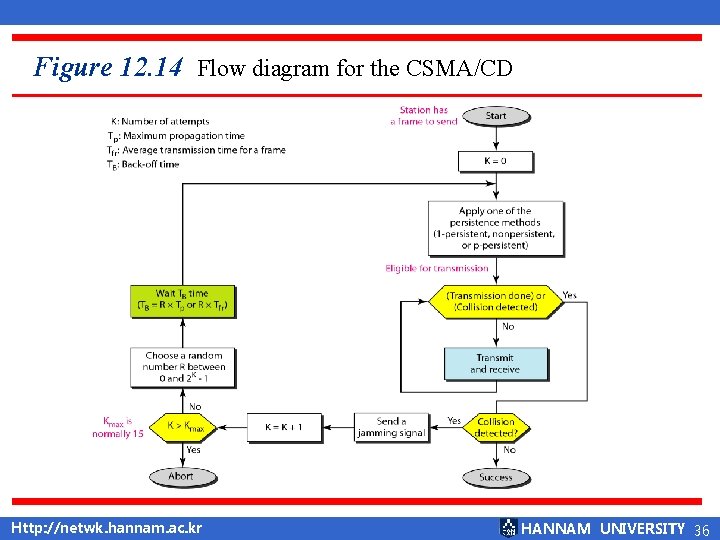
Figure 12. 15 Energy level during transmission, idleness, or collision Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 37
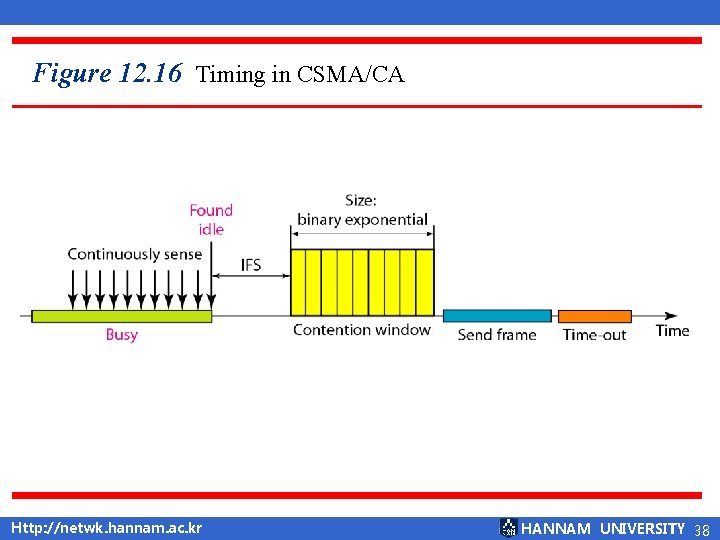
Figure 12. 16 Timing in CSMA/CA Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 38
Note CSMA/CA에서는 IFS는 지국이나 프레임의 우선순위를 규정하는 것에도 사용될 수 있다. In CSMA/CA, the IFS can also be used to define the priority of a station or a frame. Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 39
Note CSMA/CA 에서는 채널이 사용 중인 것을 감지하면 다툼 구 간의 타이머를 다시 시작하지 않고 단지 멈춘 후에 채널이 휴지 상태인 것을 감지하면 다시 작동한다. In CSMA/CA, if the station finds the channel busy, it does not restart the timer of the contention window; it stops the timer and restarts it when the channel becomes idle. Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 40
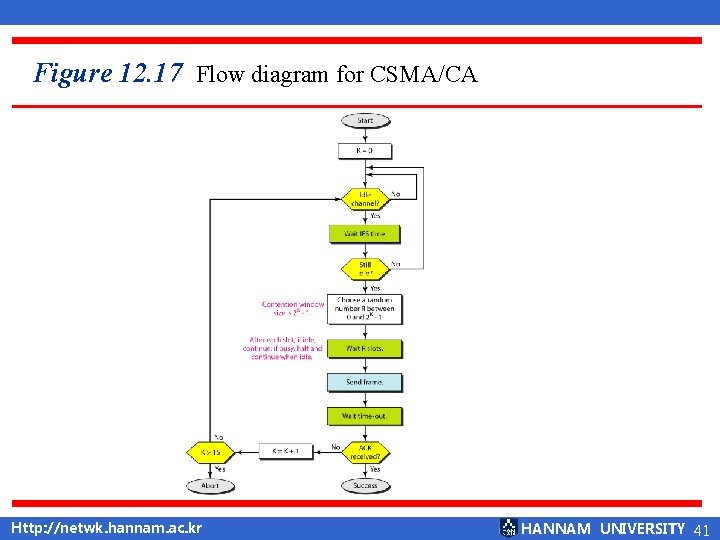
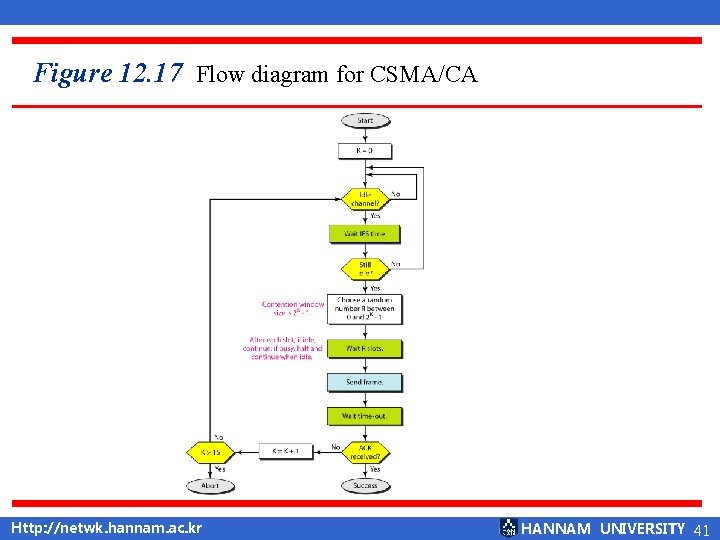
Figure 12. 17 Flow diagram for CSMA/CA Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 41
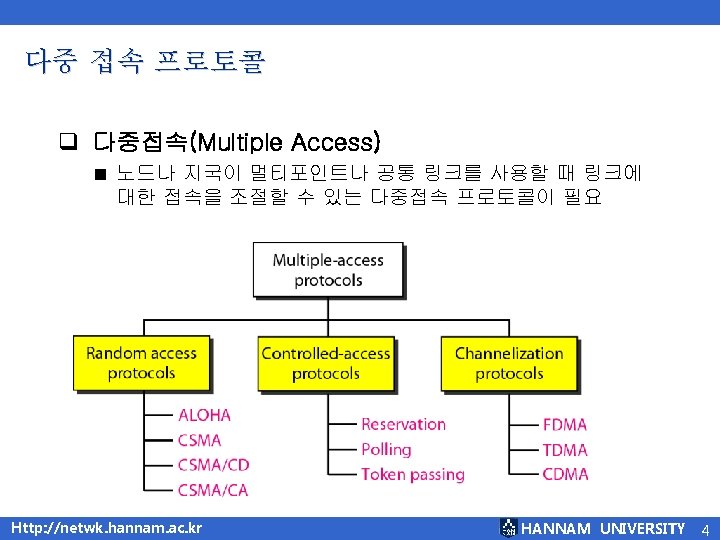
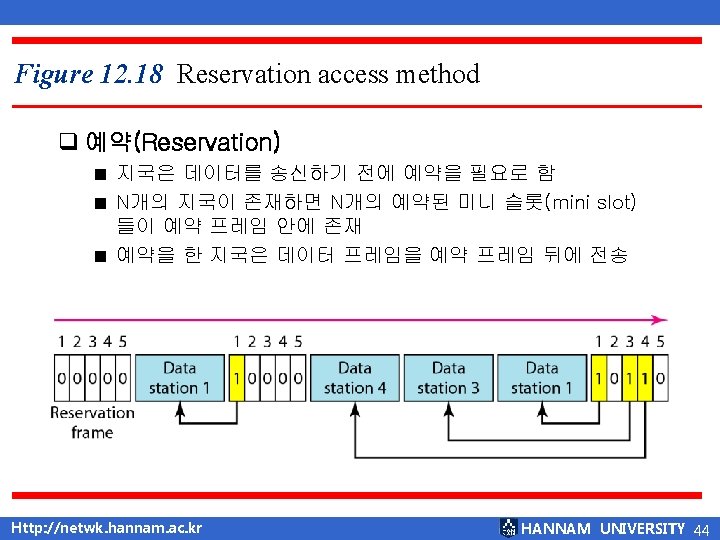
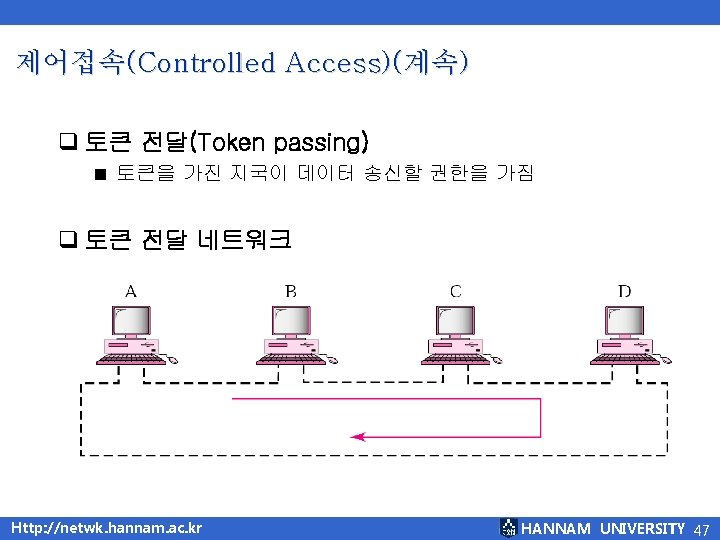
12. 2 제어 접속(Controlled Access) q 제어접속(Controlled Access) ■ 어느 지국이 송신 권한을 가지고 있는지 서로 협력 ■ 예약(Reservation) ■ 폴링(Polling) ■ 토큰전달(Token passing) Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 43
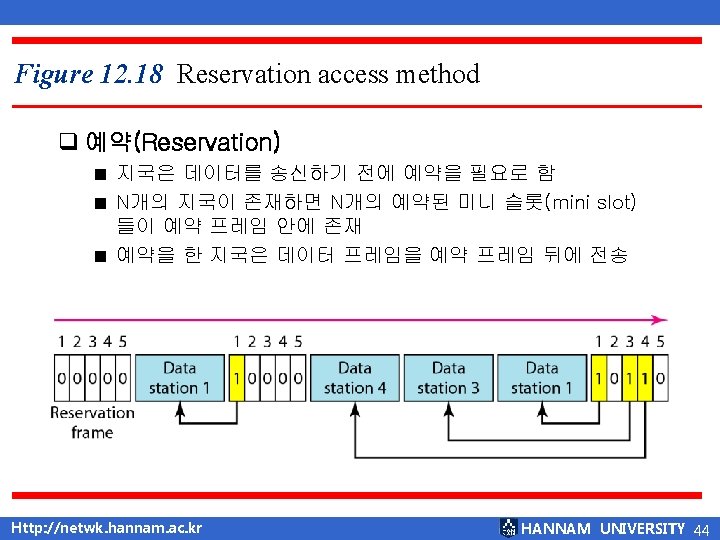
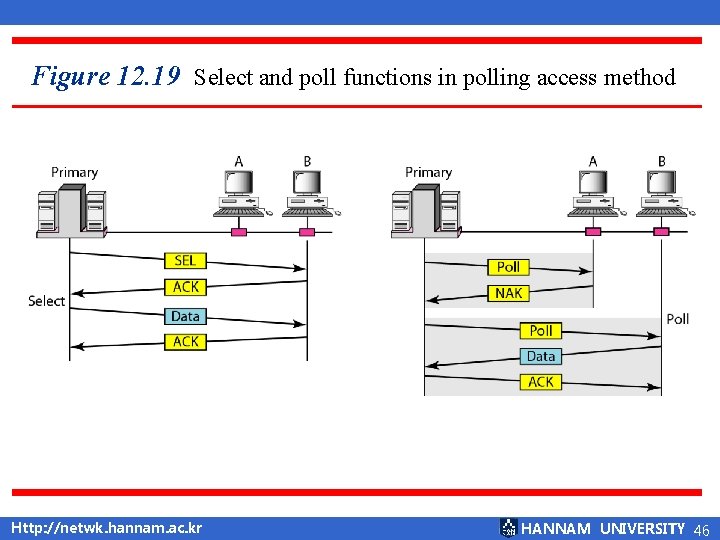
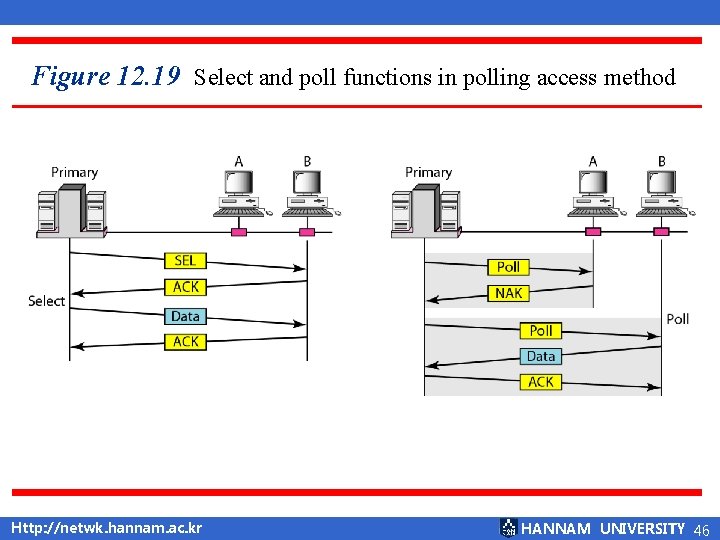
Figure 12. 19 Select and poll functions in polling access method Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 46
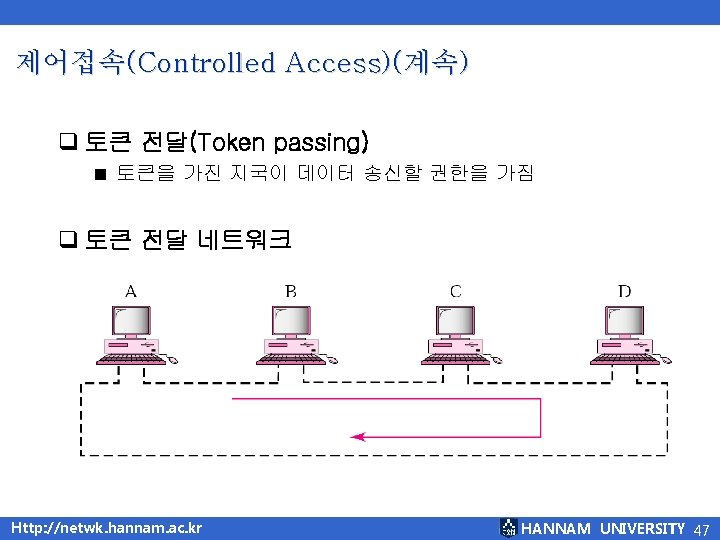
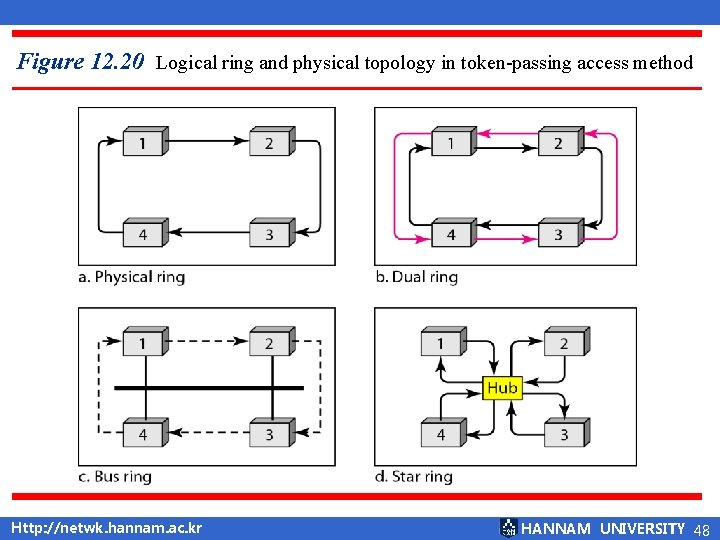
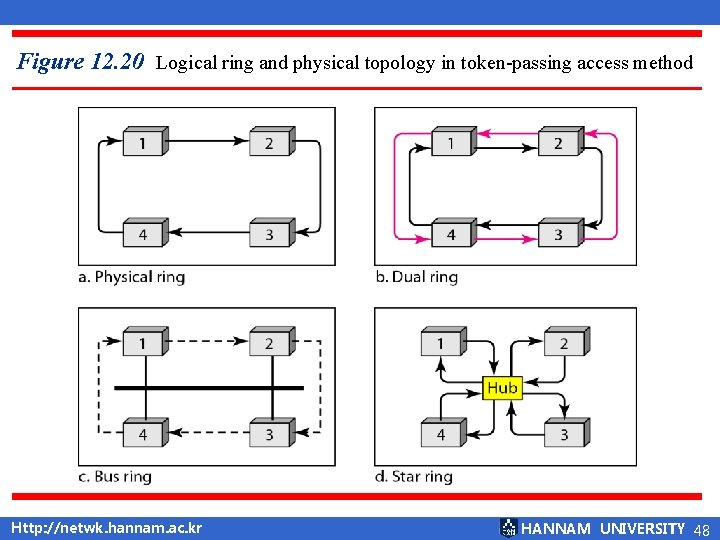
Figure 12. 20 Logical ring and physical topology in token-passing access method Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 48
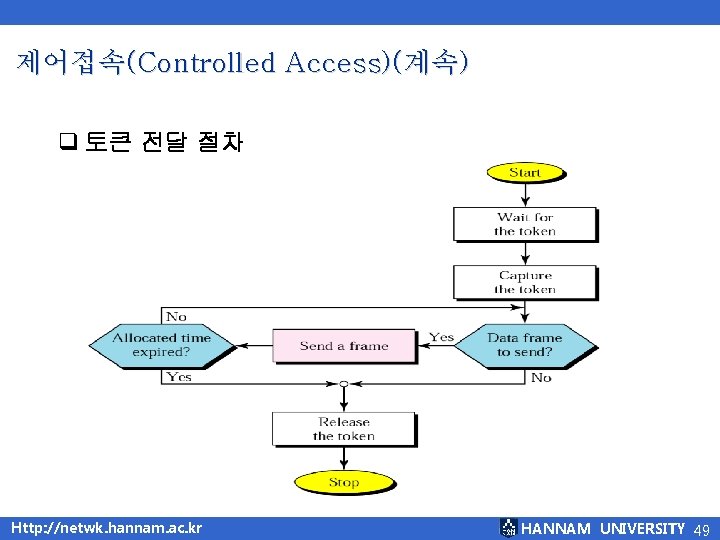
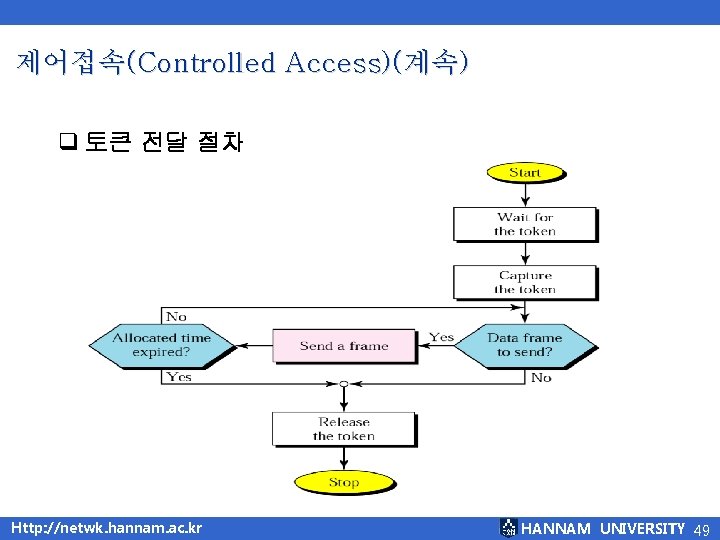
제어접속(Controlled Access)(계속) q 토큰 전달 절차 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 49
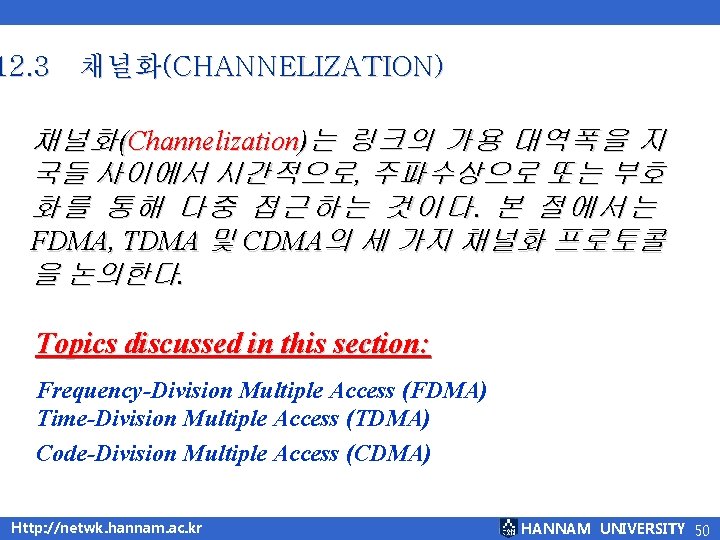
12. 3 채널화(CHANNELIZATION) 채 널 화 (Channelization)는 링 크 의 가 용 대 역 폭 을 지 국들 사이에서 시간적으로, 주파수상으로 또는 부호 화를 통해 다중 접근하는 것이다. 본 절에서는 FDMA, TDMA 및 CDMA의 세 가지 채널화 프로토콜 을 논의한다. Topics discussed in this section: Frequency-Division Multiple Access (FDMA) Time-Division Multiple Access (TDMA) Code-Division Multiple Access (CDMA) Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 50
Note 이 방법들의 응용에 대해서는 휴대 전화를 논의하는 16장 에서 논의한다. We see the application of all these methods in Chapter 16 when we discuss cellular phone systems. Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 51
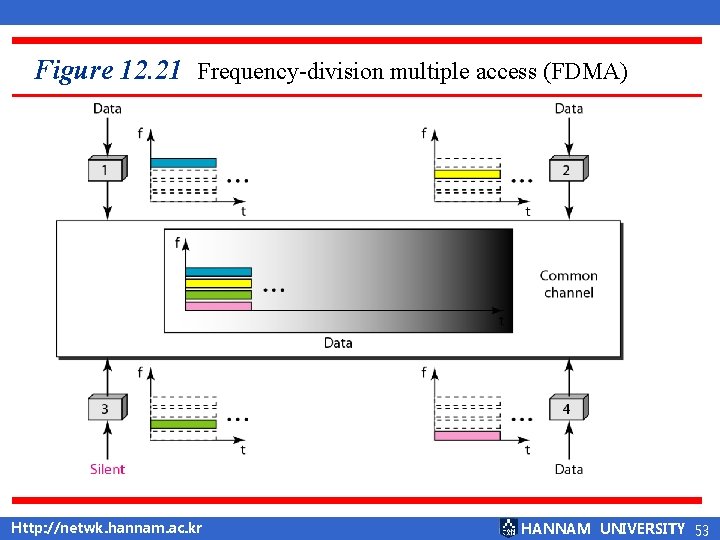
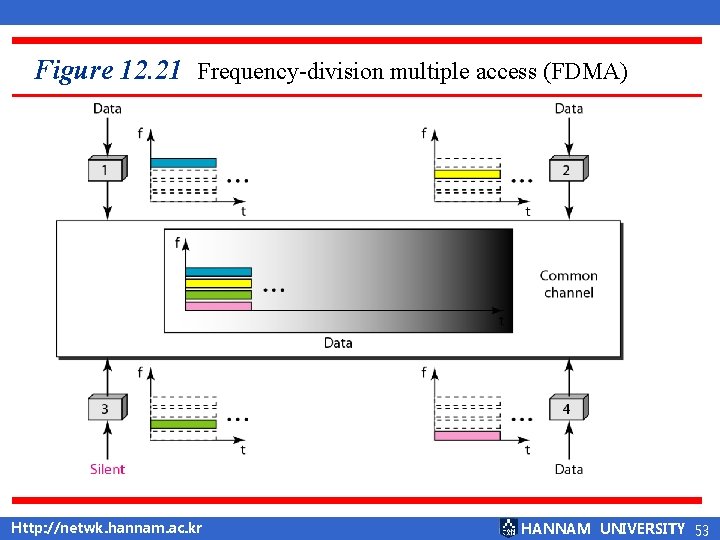
Figure 12. 21 Frequency-division multiple access (FDMA) Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 53
Note FDMA에서는 공유 채널의 가용 대역폭을 보호대역으로 분 리된 대역들로 나누게 된다. In FDMA, the available bandwidth of the common channel is divided into bands that are separated by guard bands. Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 54
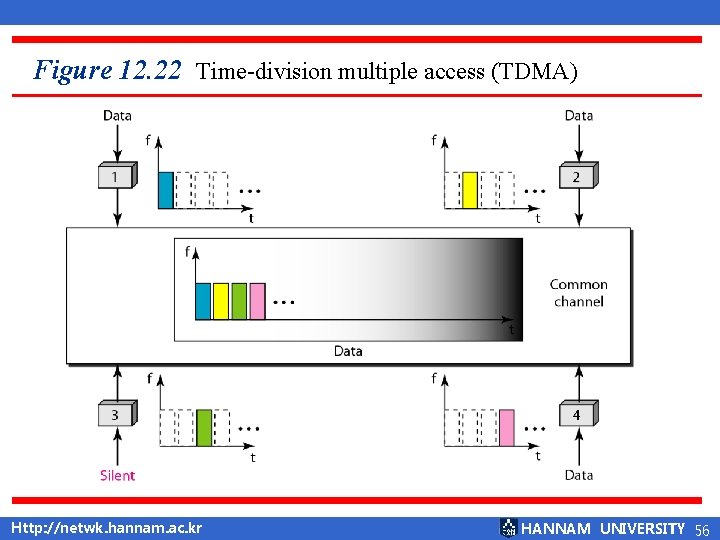
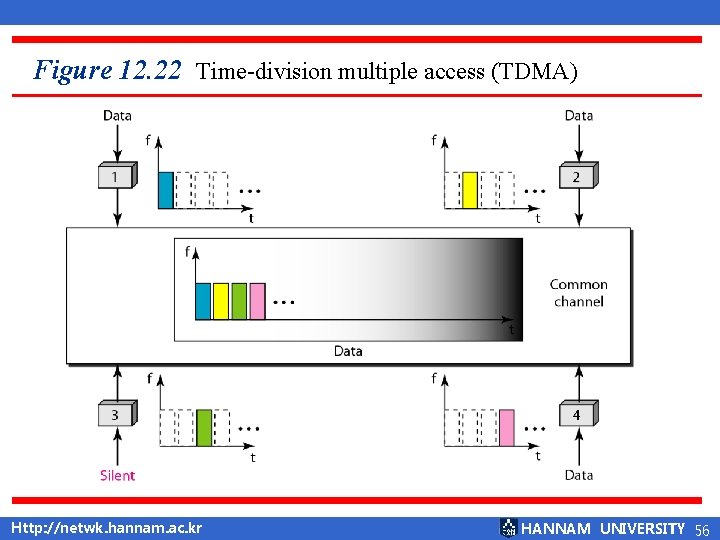
Figure 12. 22 Time-division multiple access (TDMA) Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 56
Note TDMA에서는 대역폭은 여러 지국들이 시간 상에서 공유 하는 단일 채널이다. In TDMA, the bandwidth is just one channel that is timeshared between different stations. Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 57
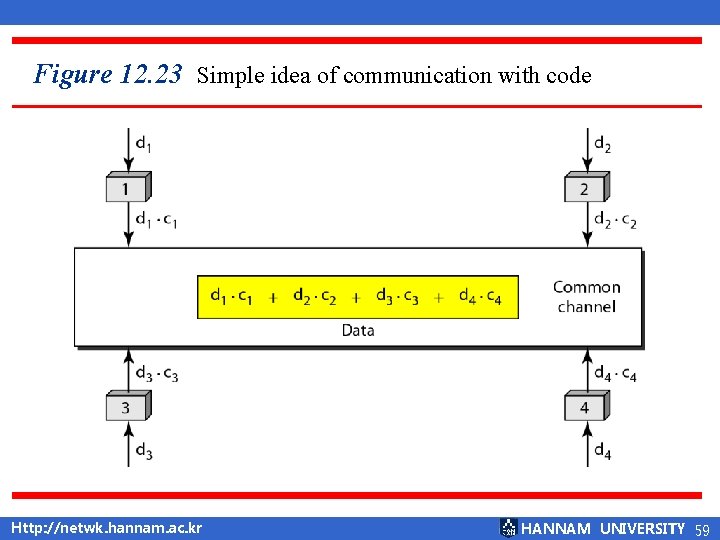
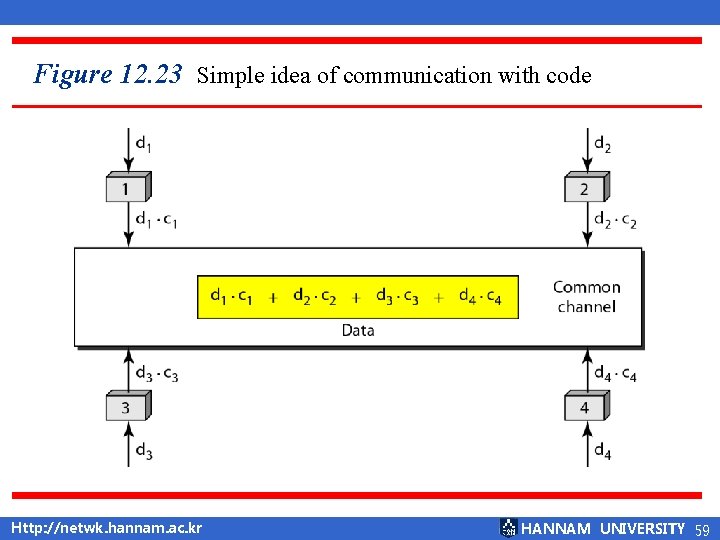
Figure 12. 23 Simple idea of communication with code Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 59
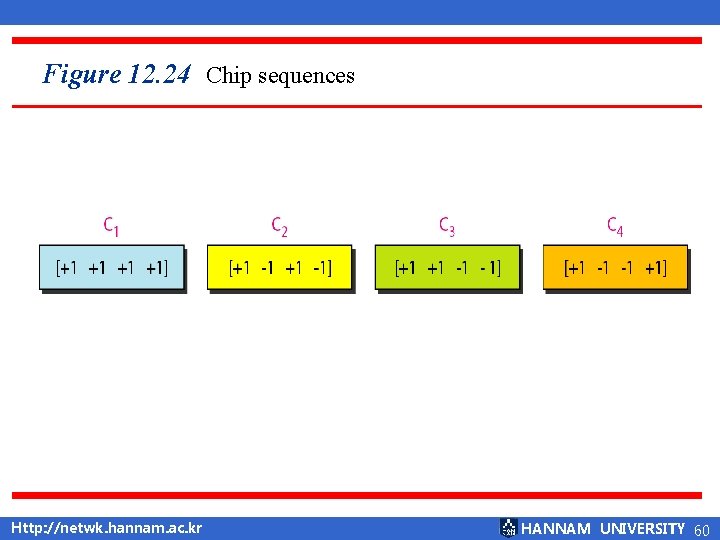
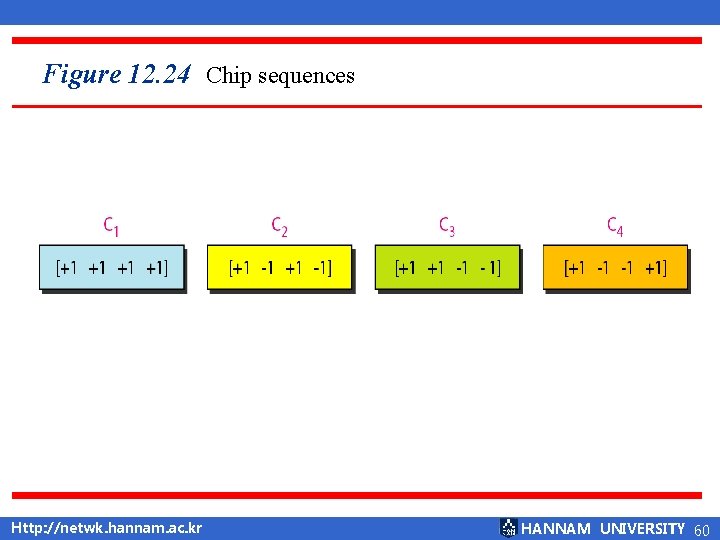
Figure 12. 24 Chip sequences Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 60
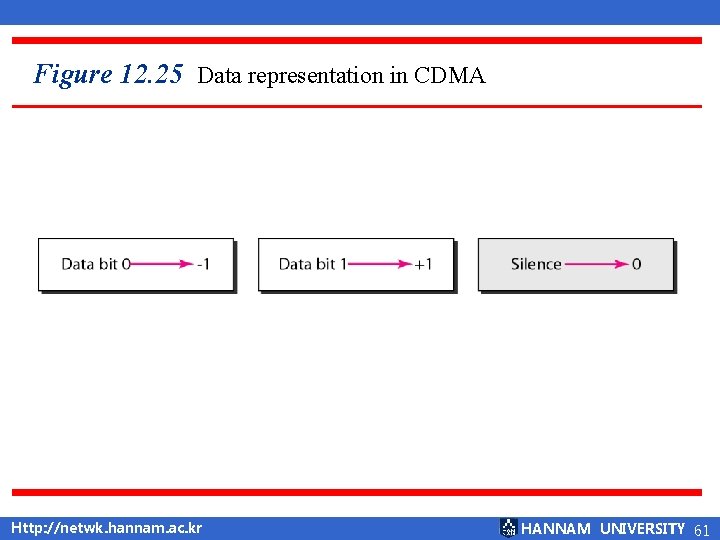
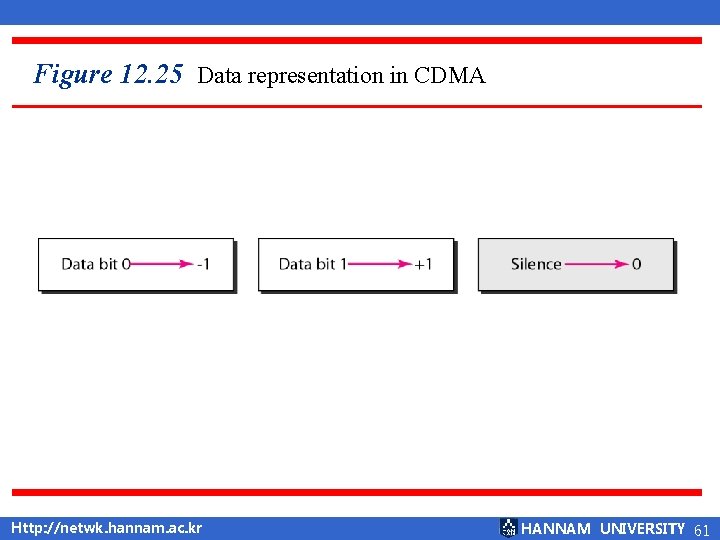
Figure 12. 25 Data representation in CDMA Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 61
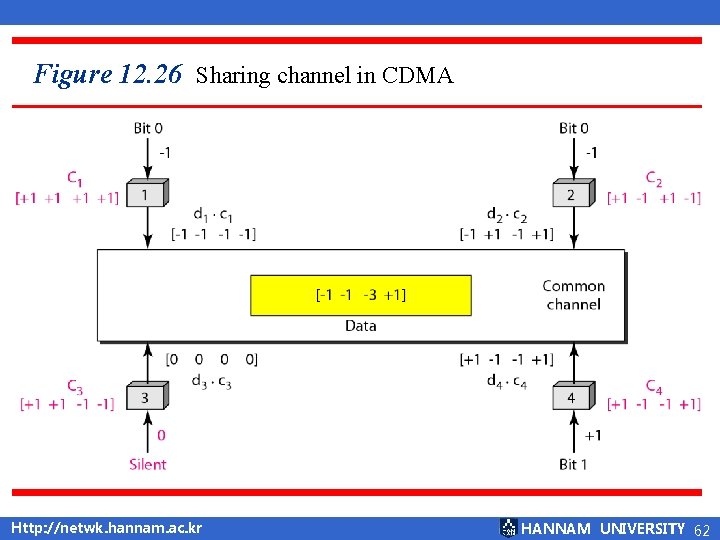
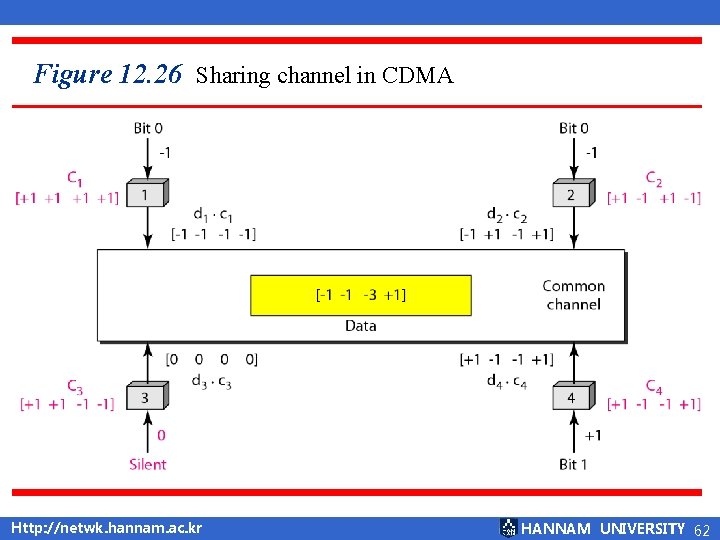
Figure 12. 26 Sharing channel in CDMA Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 62
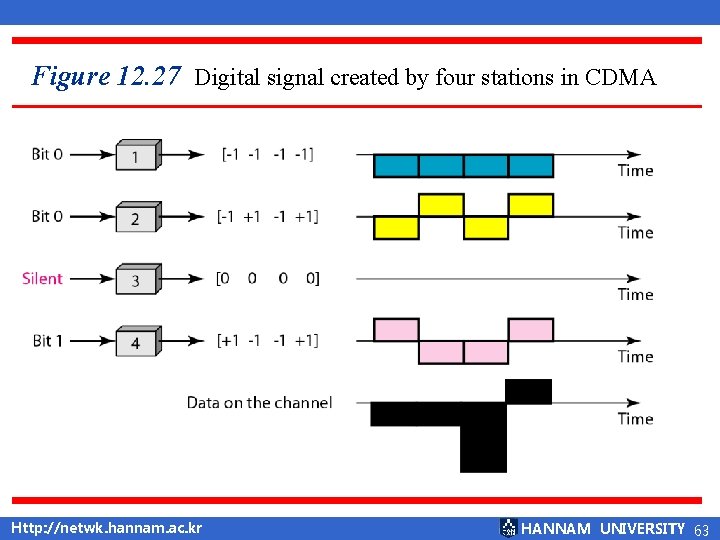
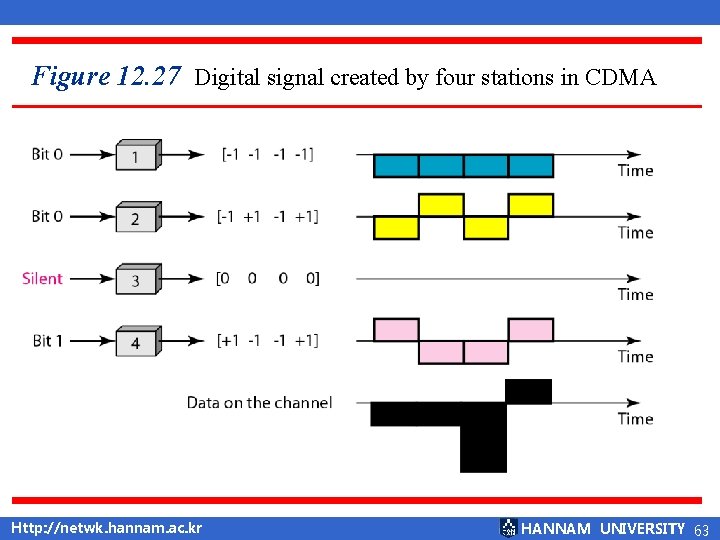
Figure 12. 27 Digital signal created by four stations in CDMA Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 63
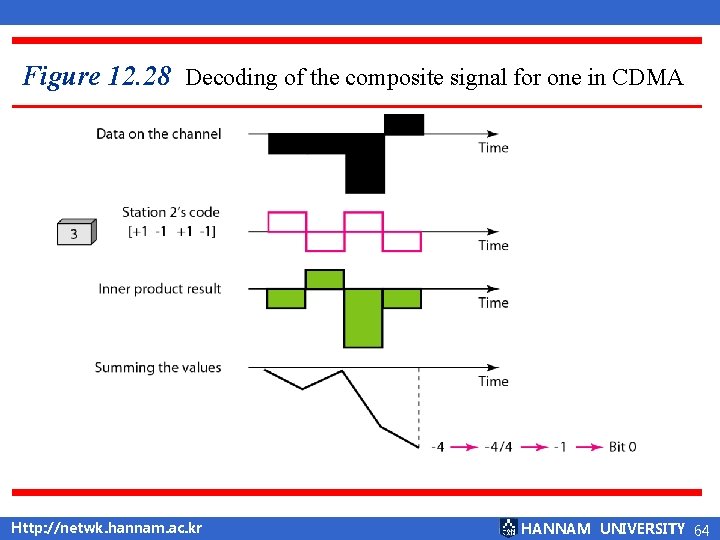
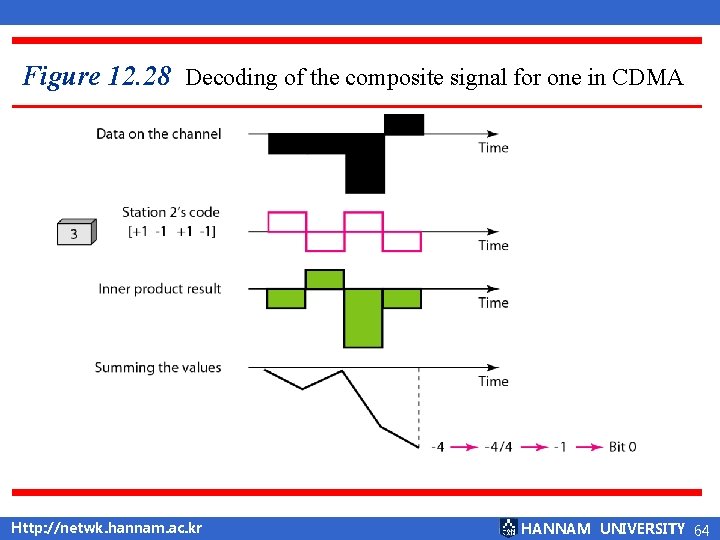
Figure 12. 28 Decoding of the composite signal for one in CDMA Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 64
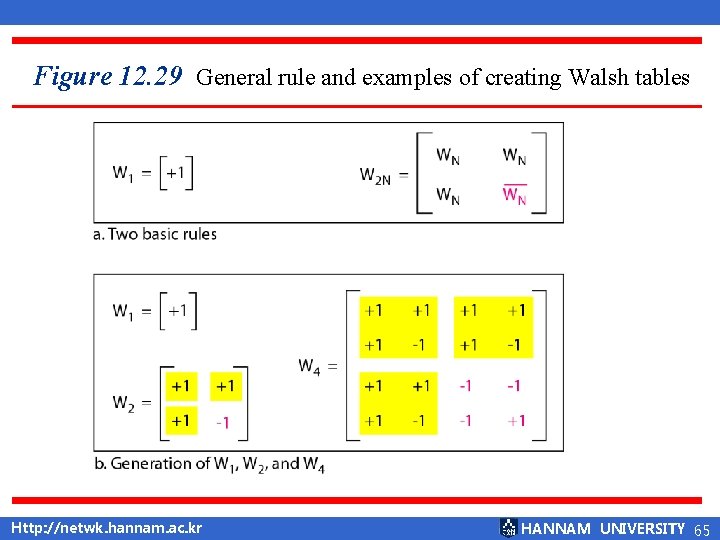
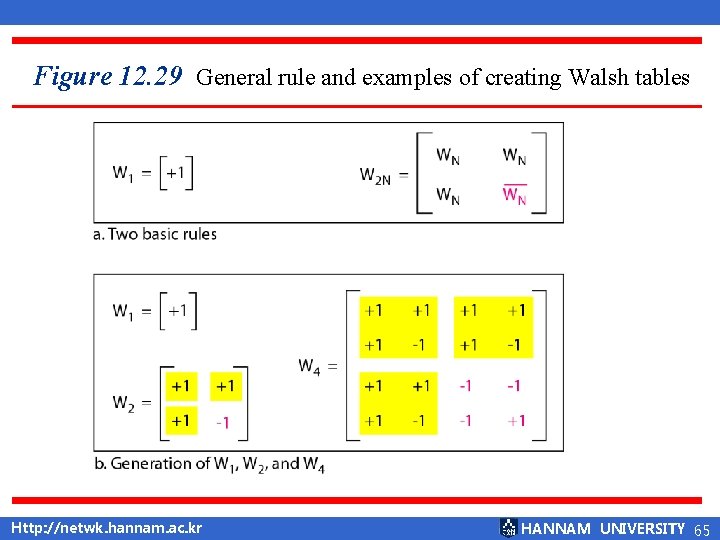
Figure 12. 29 General rule and examples of creating Walsh tables Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 65
Note 월쉬 표의 수열의 개수는 N = 2 m 이어야 한다. The number of sequences in a Walsh table needs to be N = 2 m. Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 66
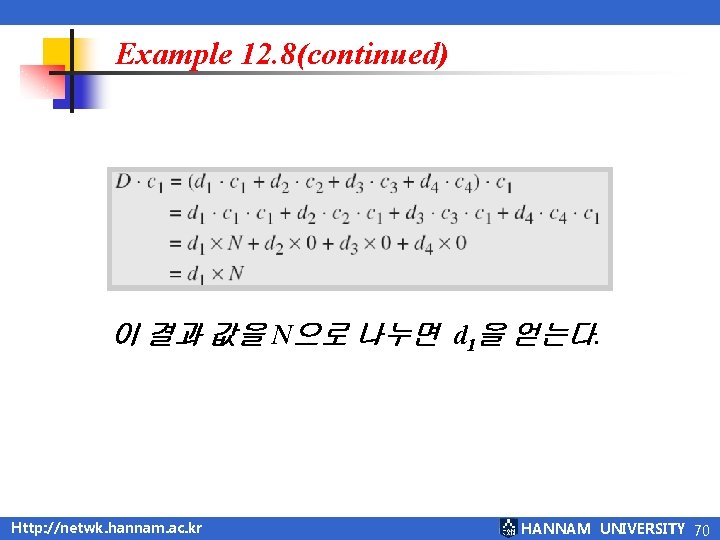
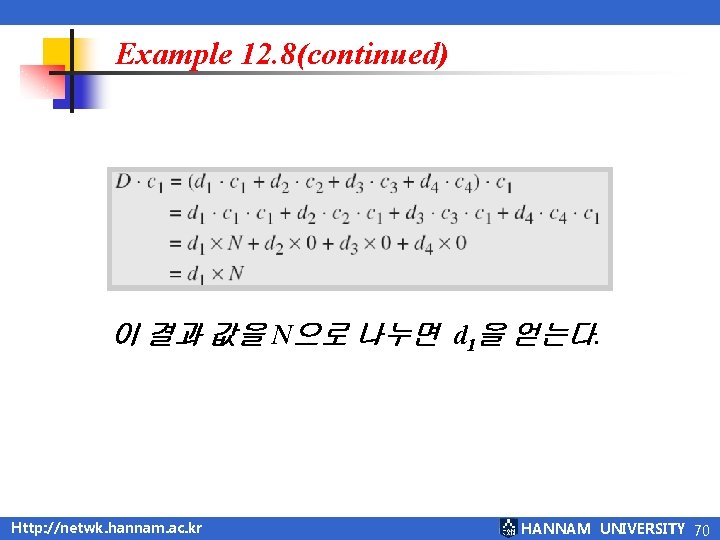
Example 12. 8(continued) 이 결과 값을 N으로 나누면 d 1을 얻는다. Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 70
12. 4 요약 Q & A Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 71
q Report ■ 연습 문제 풀이 ■ 다음주 이 시간까지 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 72