Chapter 11 Unicast Routing Protocols TCPIP Protocol Suite
- Slides: 41
Chapter 11 Unicast Routing Protocols TCP/IP Protocol Suite 1 Copyright © The Mc. Graw-Hill Companies, Inc. Permission required for reproduction or display.
11 -1 INTRODUCTION An internet is a combination of networks connected by routers. When a datagram goes from a source to a destination, it will probably pass through many routers until it reaches the router attached to the destination network. TCP/IP Protocol Suite 2
11 -2 INTER- AND INTRA-DOMAIN ROUTING Today, an internet can be so large that one routing protocol cannot handle the task of updating the routing tables of all routers. For this reason, an internet is divided into autonomous systems. An autonomous system (AS) is a group of networks and routers under the authority of a single administration. Routing inside an autonomous system is called intradomain routing. Routing between autonomous systems is called inter-domain routing TCP/IP Protocol Suite 3
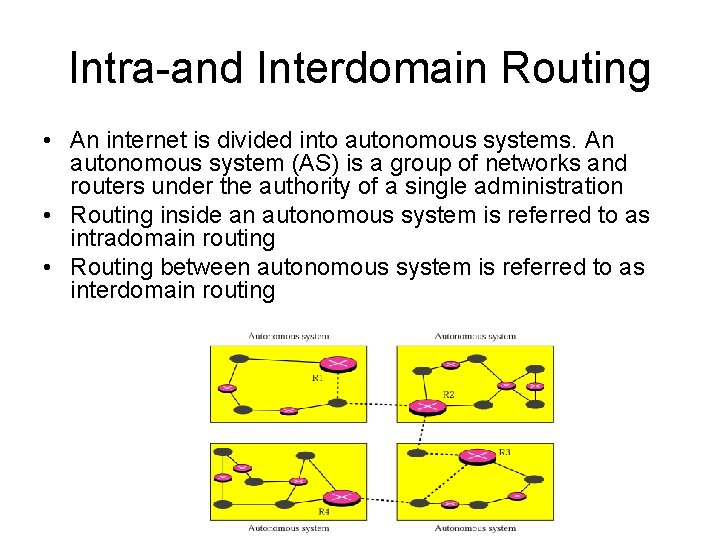
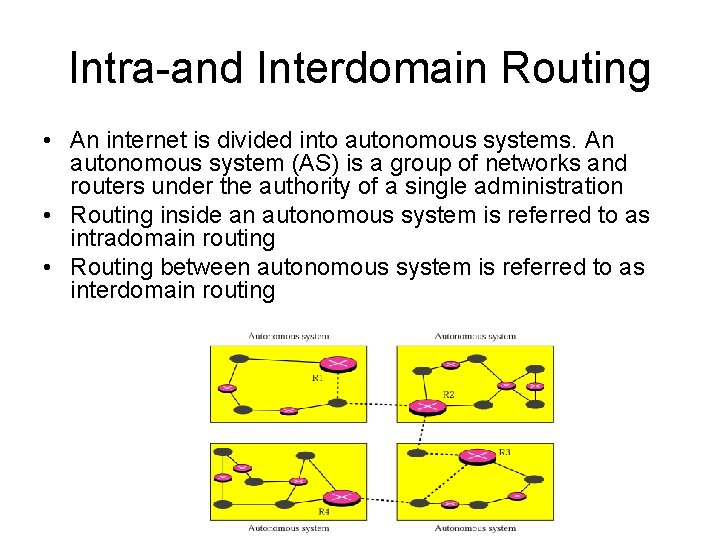
Intra-and Interdomain Routing • An internet is divided into autonomous systems. An autonomous system (AS) is a group of networks and routers under the authority of a single administration • Routing inside an autonomous system is referred to as intradomain routing • Routing between autonomous system is referred to as interdomain routing
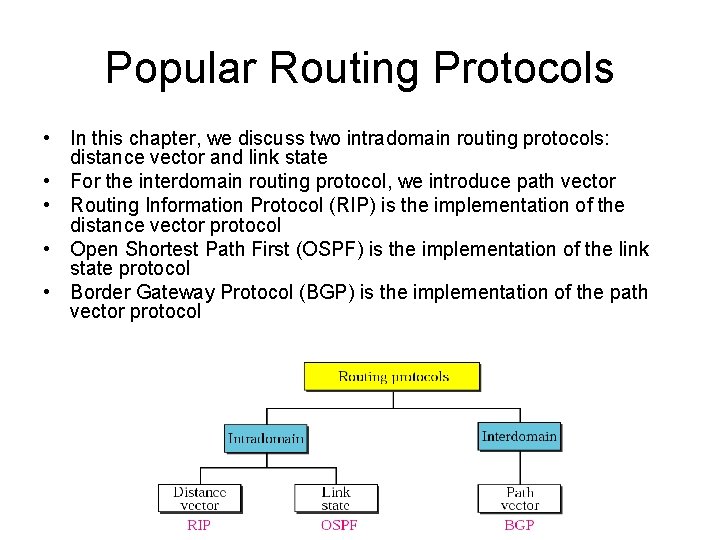
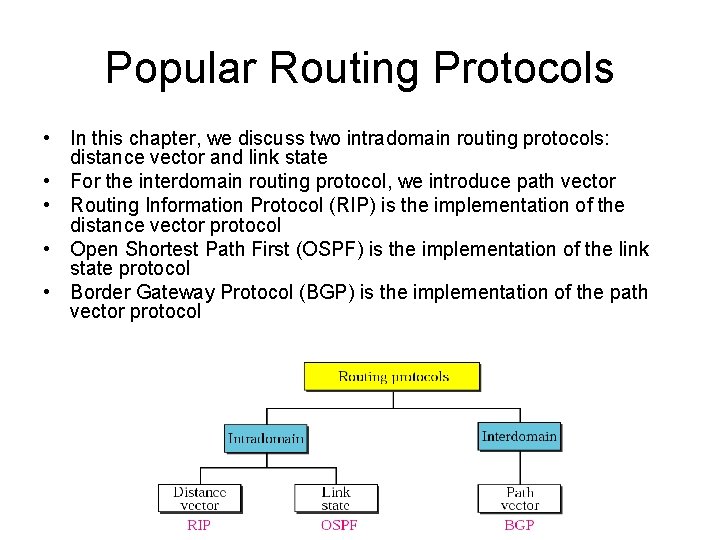
Popular Routing Protocols • In this chapter, we discuss two intradomain routing protocols: distance vector and link state • For the interdomain routing protocol, we introduce path vector • Routing Information Protocol (RIP) is the implementation of the distance vector protocol • Open Shortest Path First (OSPF) is the implementation of the link state protocol • Border Gateway Protocol (BGP) is the implementation of the path vector protocol
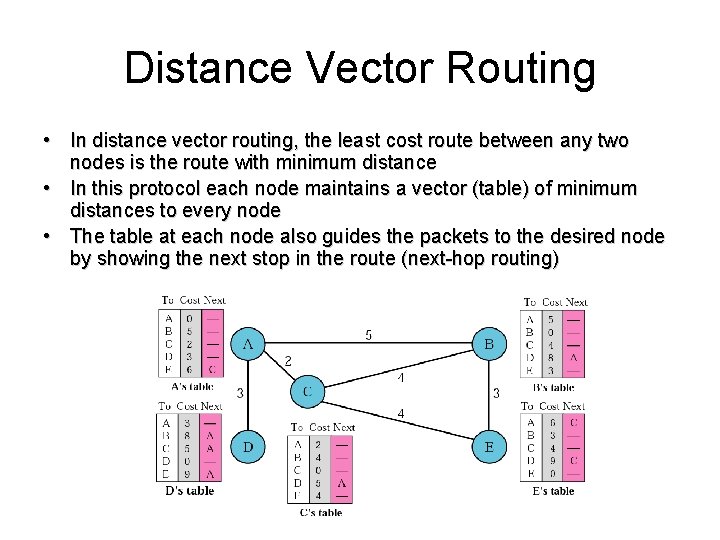
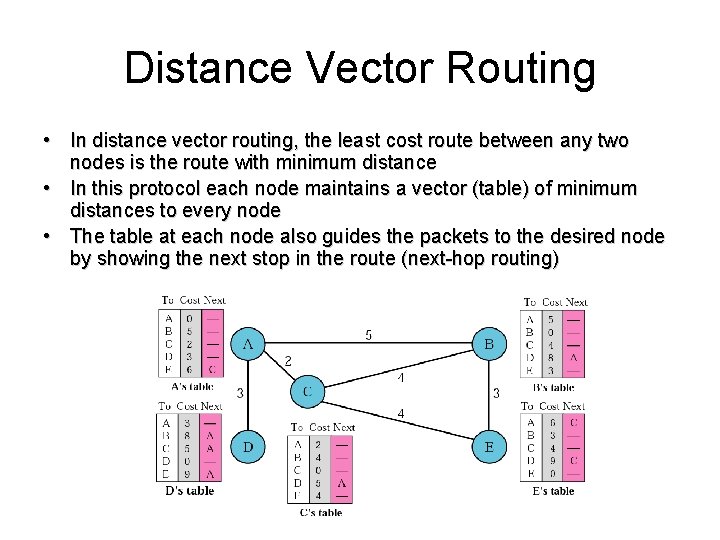
Distance Vector Routing • In distance vector routing, the least cost route between any two nodes is the route with minimum distance • In this protocol each node maintains a vector (table) of minimum distances to every node • The table at each node also guides the packets to the desired node by showing the next stop in the route (next-hop routing)
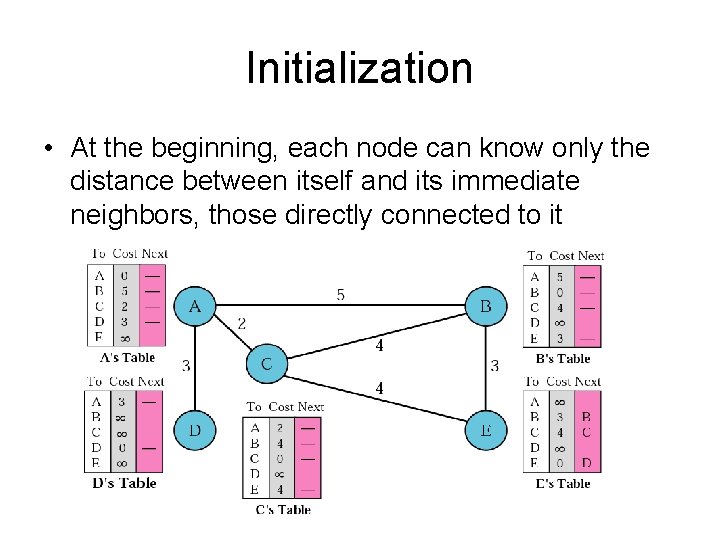
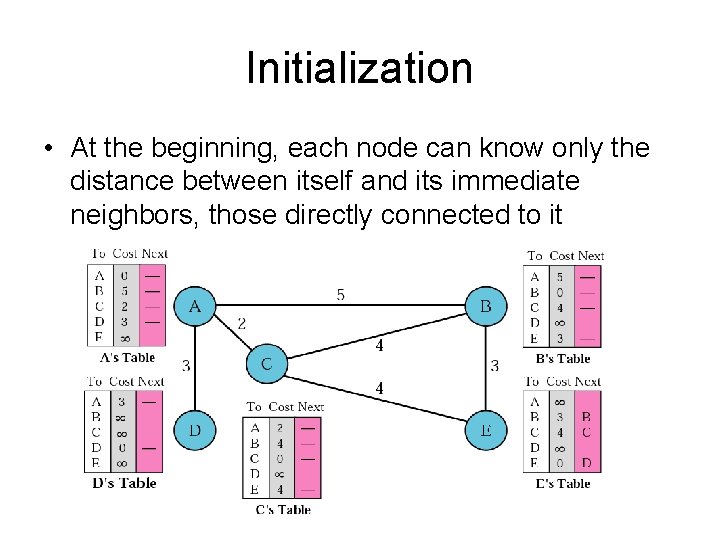
Initialization • At the beginning, each node can know only the distance between itself and its immediate neighbors, those directly connected to it
Sharing • The whole idea of distance vector routing is the sharing of information between neighbors • Although node A does not know about node E, node C does. So if node C shares its routing table with A, node A can also know how to reach node E Note: In distance vector routing, each node shares its routing table with its immediate neighbors periodically and when there is a change.
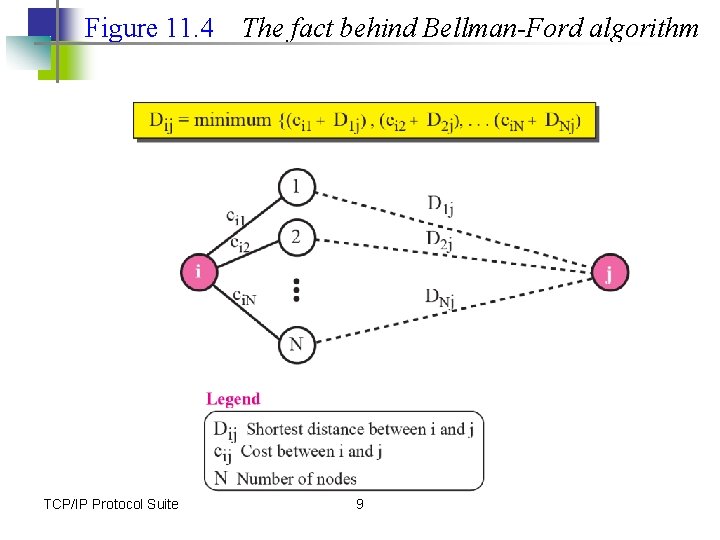
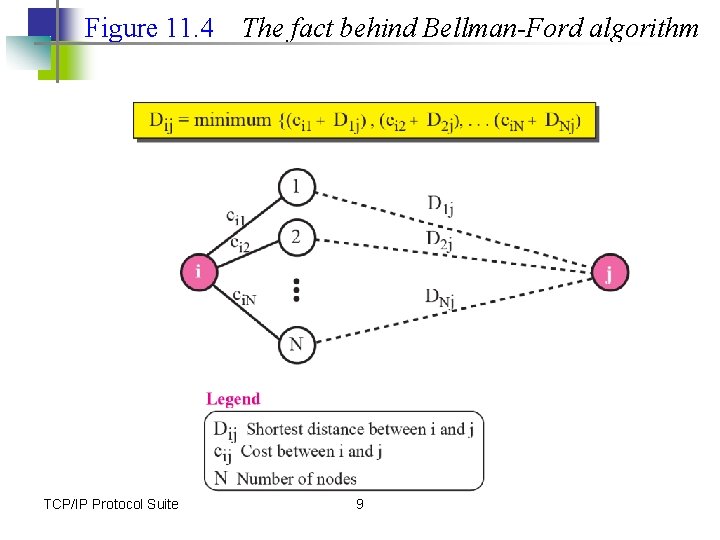
Figure 11. 4 TCP/IP Protocol Suite The fact behind Bellman-Ford algorithm 9
Updating • When a node receives a 2 -column table from a neighbor, it needs to update its routing table. Updating takes 3 steps: 1. The receiving node needs to add the cost between itself and the sending node to each value in the second column 2. The receiving node needs to add the name of the sending node to each row as the 3 rd column if the receiving node uses information from any row. The sending node is the next node in the route
Updating (cont. ) 3. The receiving node needs to compare each row of its old table with the corresponding row of the modified version of the received table. a) If the next-node entry is different, the receiving node chooses the row with the smaller cost. If there is a tie, the old one is kept b) If the next-node entry is the same, the receiving node chooses the new row. For example, if node C has previously advertised a route to node X with distance 3. Suppose that now there is no path between C and X; node C now advertises this route with a distance of infinity. Node A must not ignore this value even though its old entry is smaller.
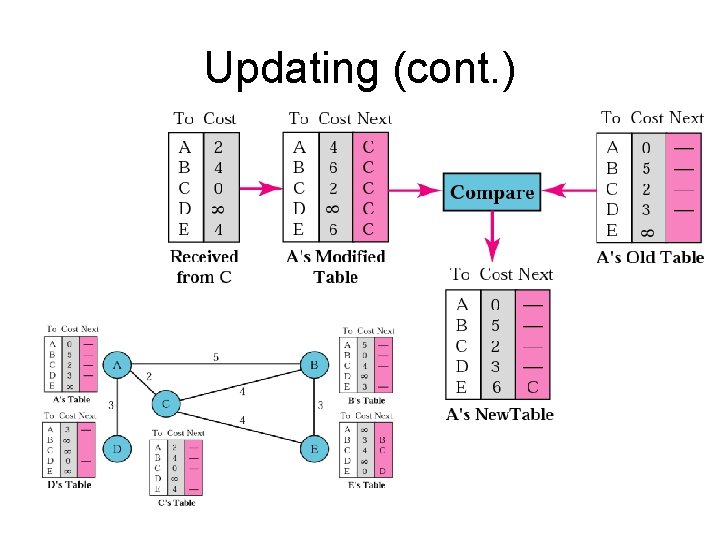
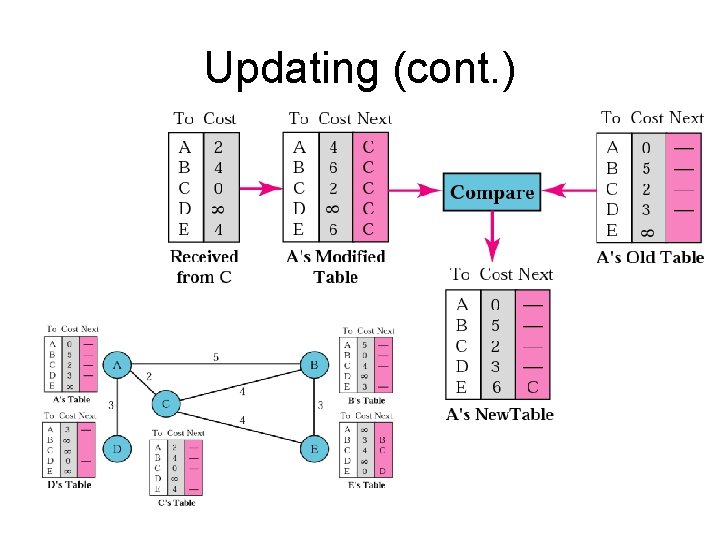
Updating (cont. )
When to Share • • • The table is sent both periodically and when there is a change in the table Periodic Update. A node sends its routing table, normally every 30 seconds, in a periodic update. The period depends on the protocol that is using distance vector routing Triggered Update. A node sends its 2 -column routing table to its neighbors any time there is a change in its routing table. This is called a triggered update. The change can result from the following. 1. A node receive a table from a neighbor resulting in changes in its own table after updating 2. A node detects some failure in the neighboring links which results in a distance change to infinity
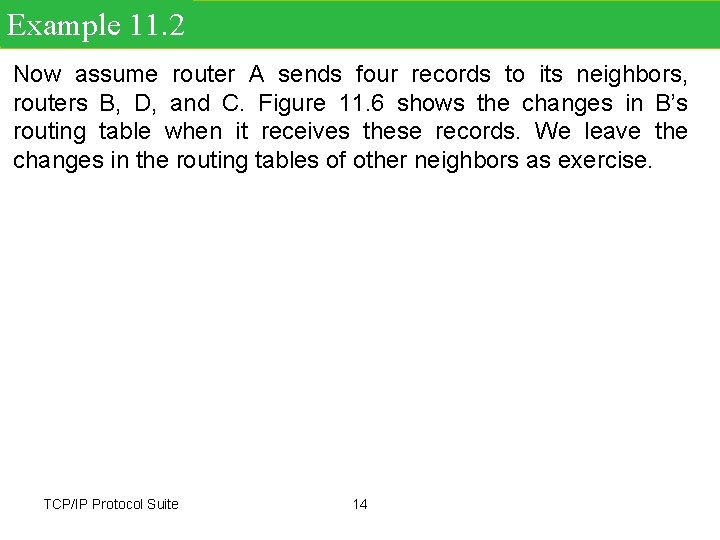
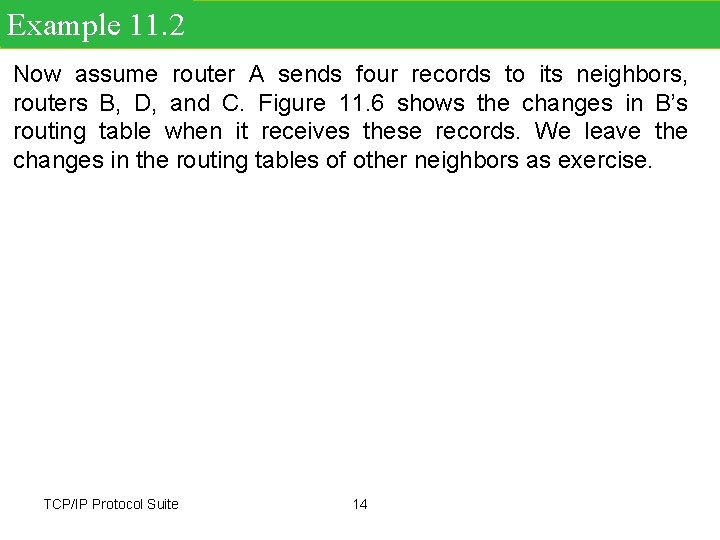
Example 11. 2 Now assume router A sends four records to its neighbors, routers B, D, and C. Figure 11. 6 shows the changes in B’s routing table when it receives these records. We leave the changes in the routing tables of other neighbors as exercise. TCP/IP Protocol Suite 14
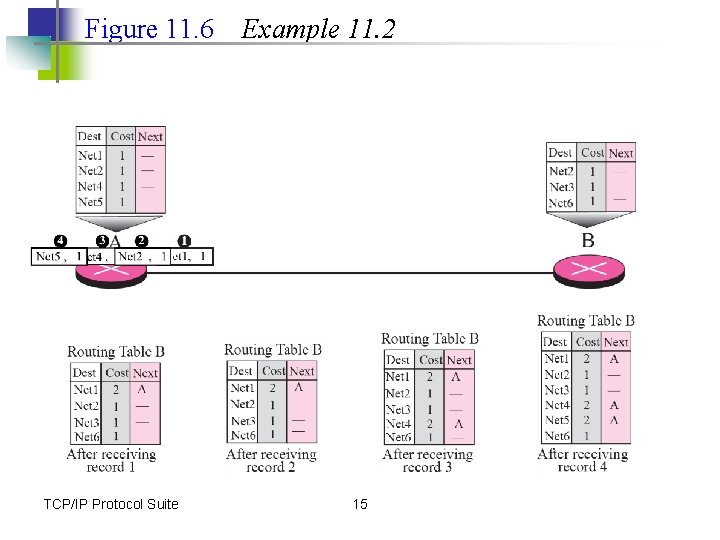
Figure 11. 6 TCP/IP Protocol Suite Example 11. 2 15
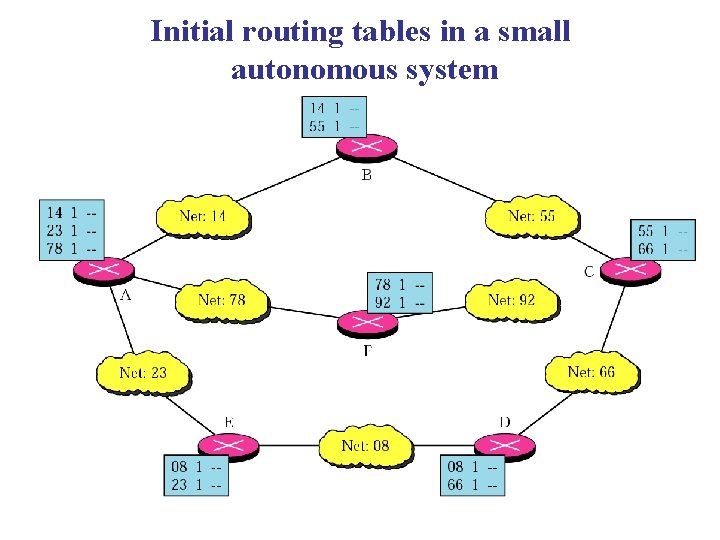
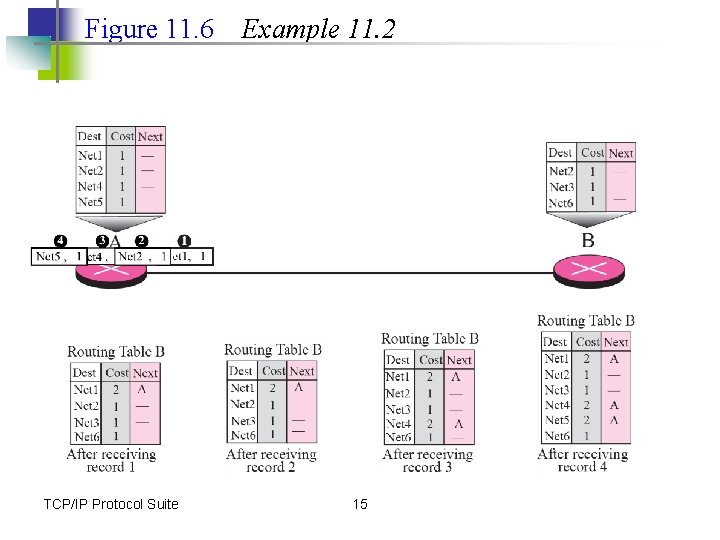
Initial routing tables in a small autonomous system
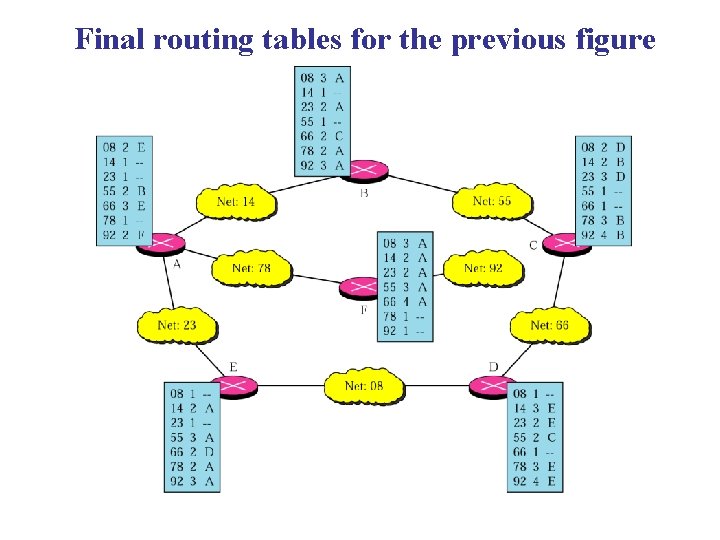
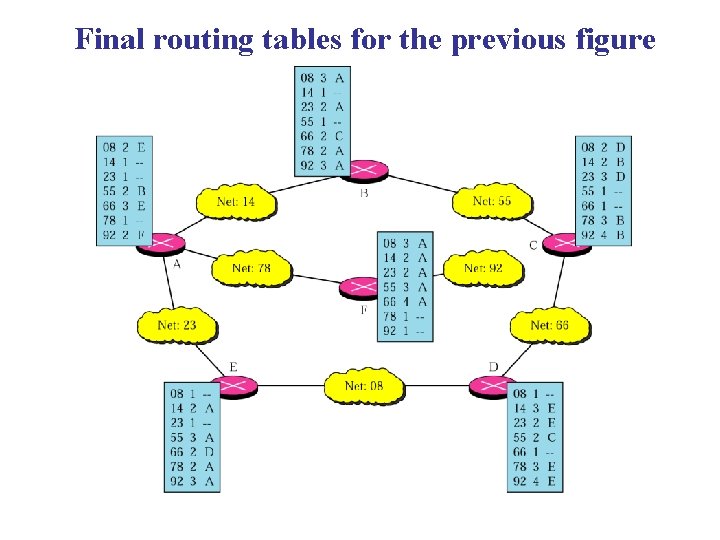
Final routing tables for the previous figure
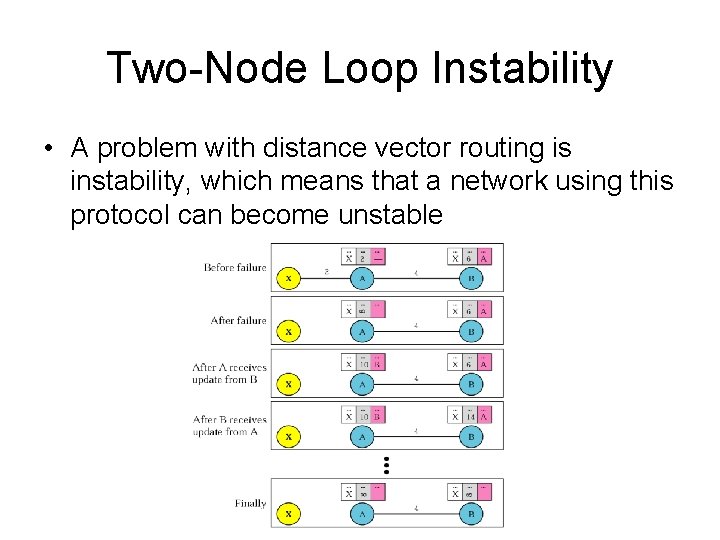
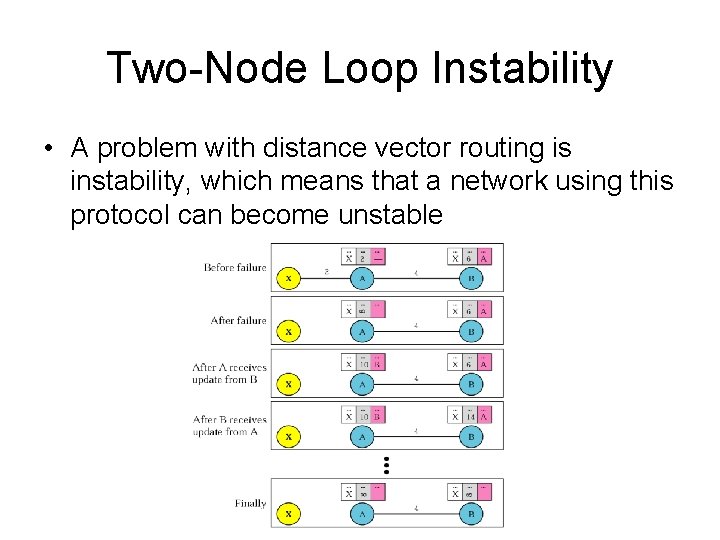
Two-Node Loop Instability • A problem with distance vector routing is instability, which means that a network using this protocol can become unstable
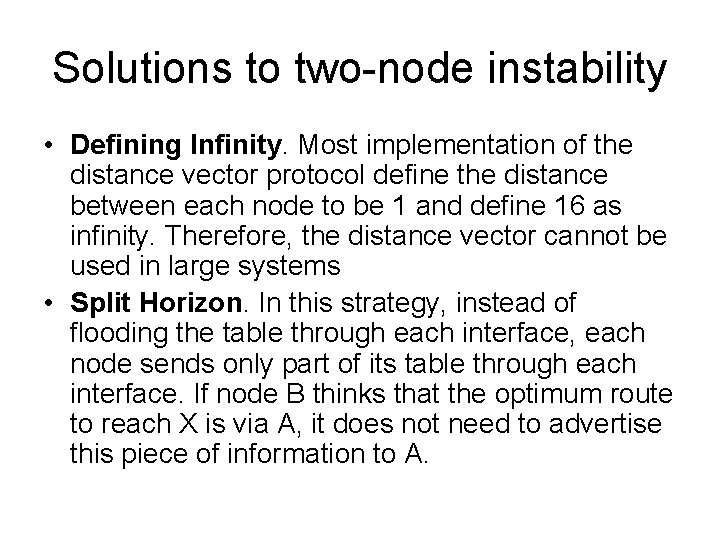
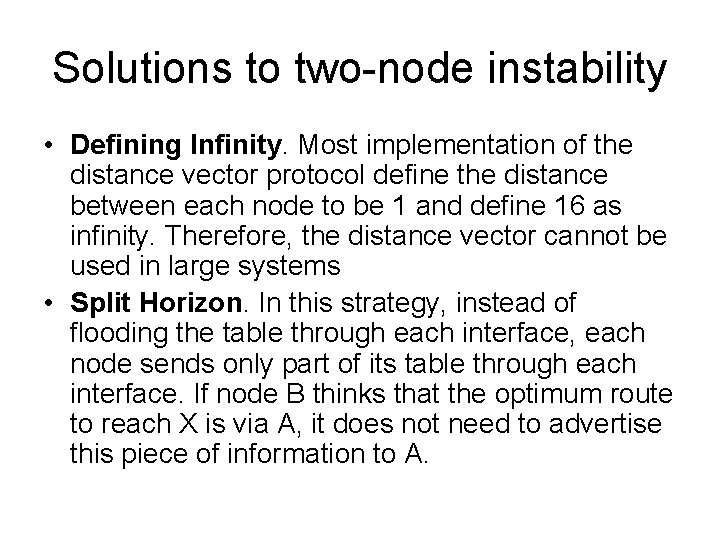
Solutions to two-node instability • Defining Infinity. Most implementation of the distance vector protocol define the distance between each node to be 1 and define 16 as infinity. Therefore, the distance vector cannot be used in large systems • Split Horizon. In this strategy, instead of flooding the table through each interface, each node sends only part of its table through each interface. If node B thinks that the optimum route to reach X is via A, it does not need to advertise this piece of information to A.
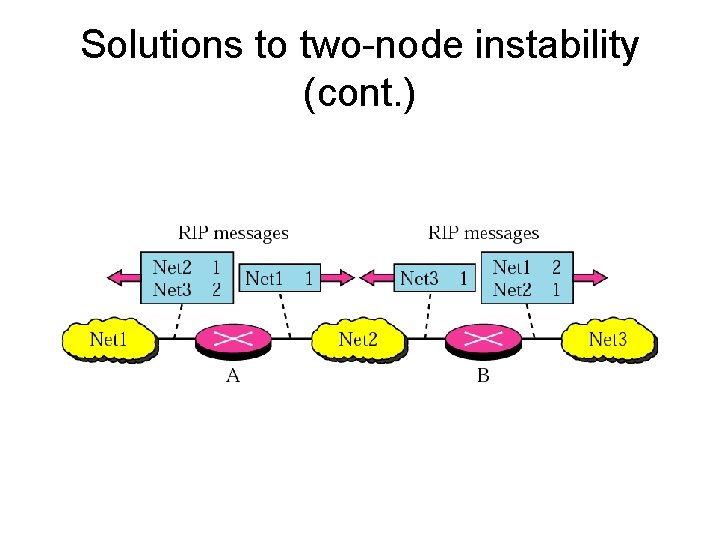
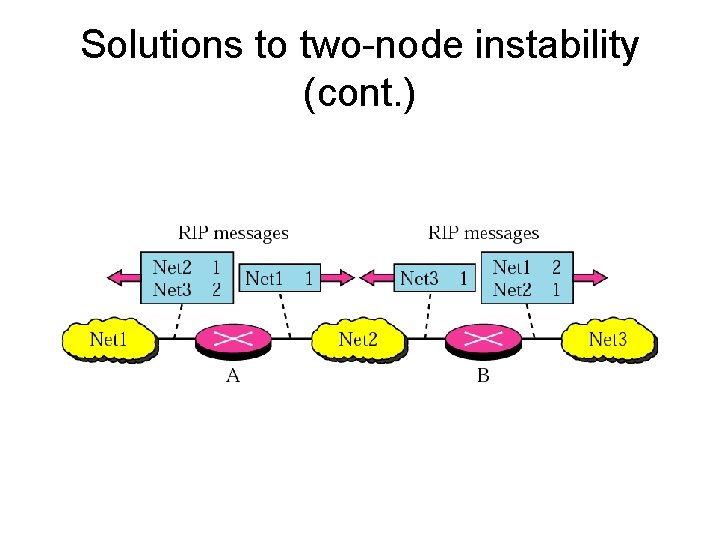
Solutions to two-node instability (cont. )
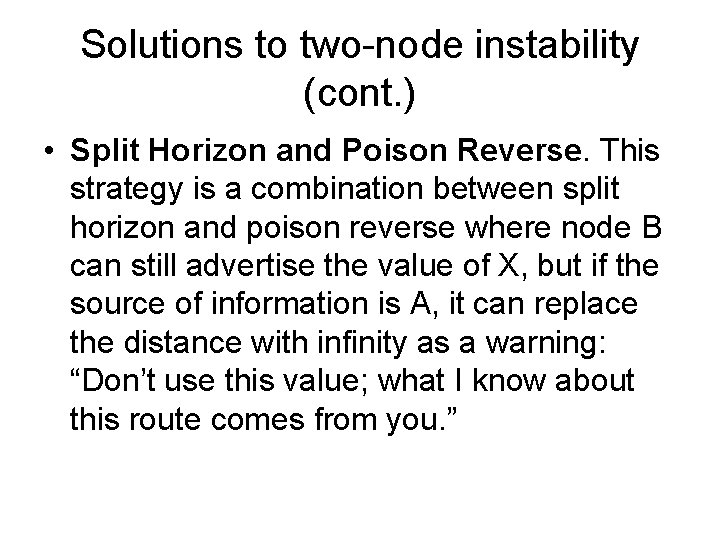
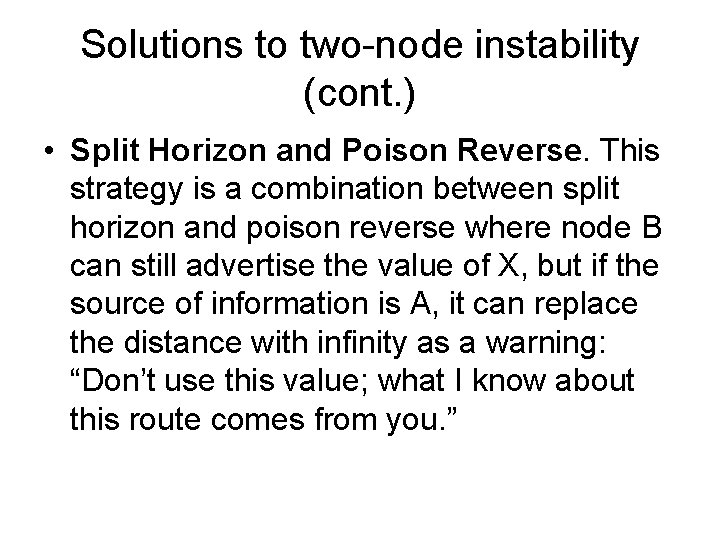
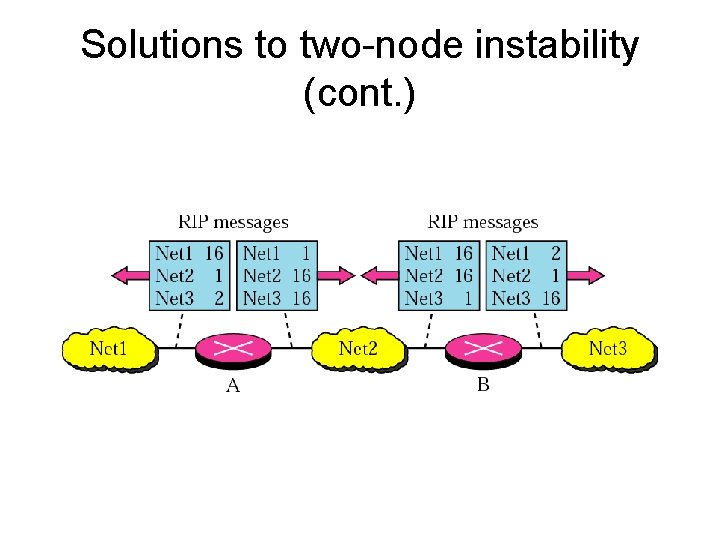
Solutions to two-node instability (cont. ) • Split Horizon and Poison Reverse. This strategy is a combination between split horizon and poison reverse where node B can still advertise the value of X, but if the source of information is A, it can replace the distance with infinity as a warning: “Don’t use this value; what I know about this route comes from you. ”
Solutions to two-node instability (cont. )
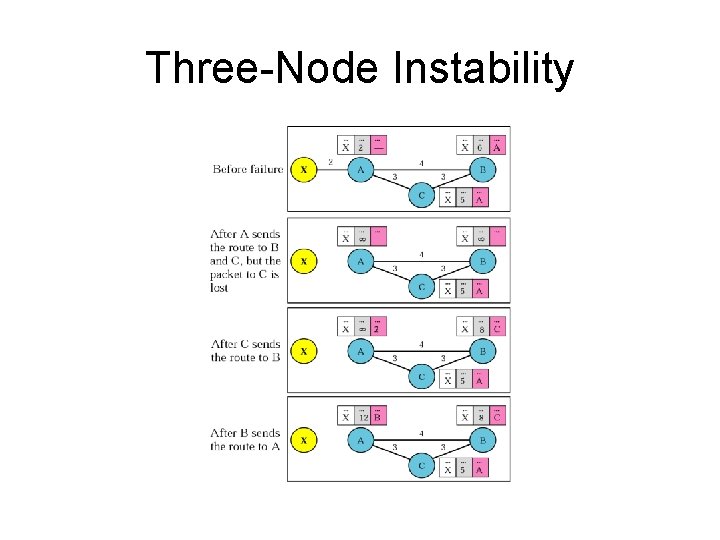
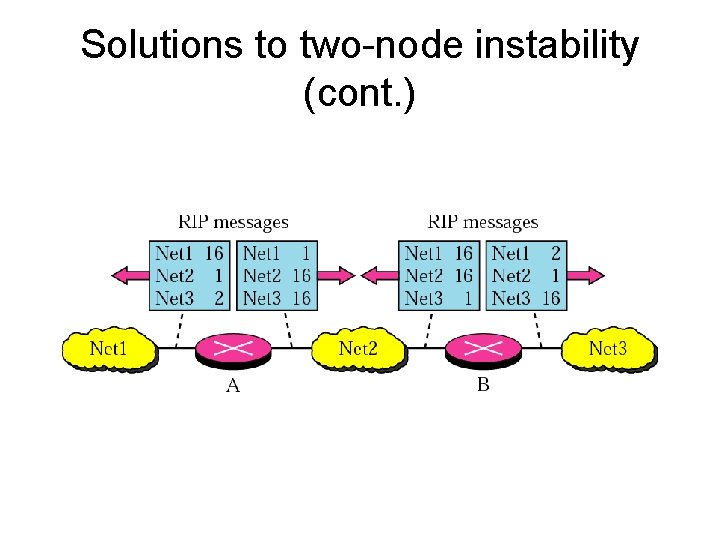
Three-Node Instability
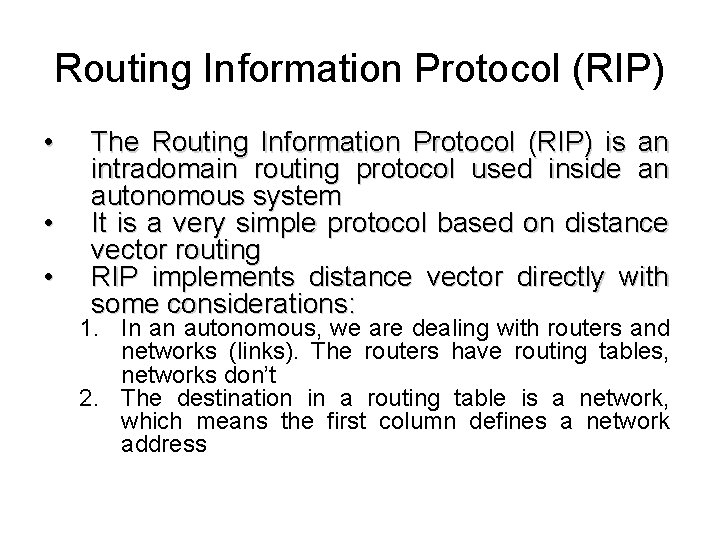
Routing Information Protocol (RIP) • • • The Routing Information Protocol (RIP) is an intradomain routing protocol used inside an autonomous system It is a very simple protocol based on distance vector routing RIP implements distance vector directly with some considerations: 1. In an autonomous, we are dealing with routers and networks (links). The routers have routing tables, networks don’t 2. The destination in a routing table is a network, which means the first column defines a network address
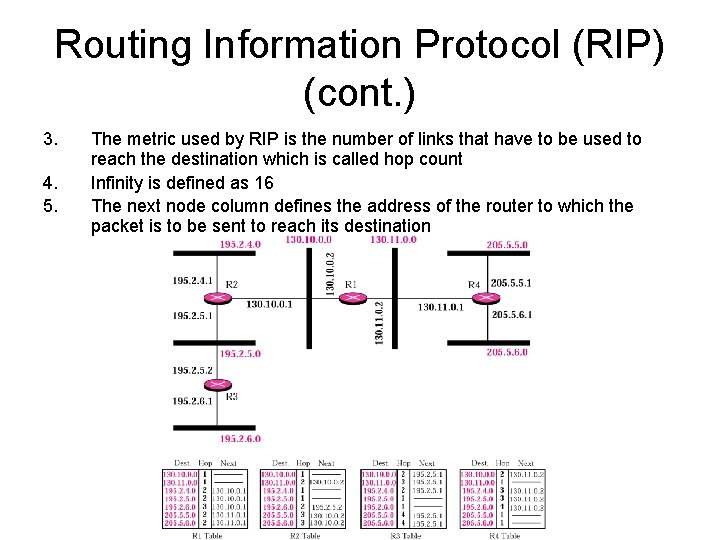
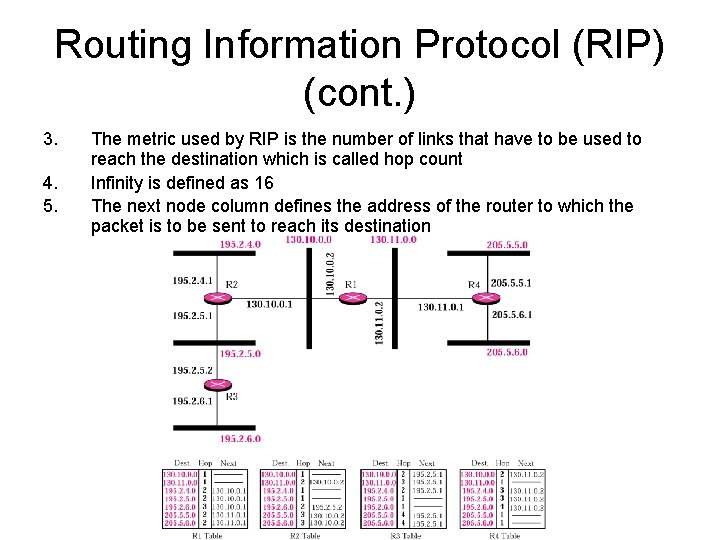
Routing Information Protocol (RIP) (cont. ) 3. 4. 5. The metric used by RIP is the number of links that have to be used to reach the destination which is called hop count Infinity is defined as 16 The next node column defines the address of the router to which the packet is to be sent to reach its destination
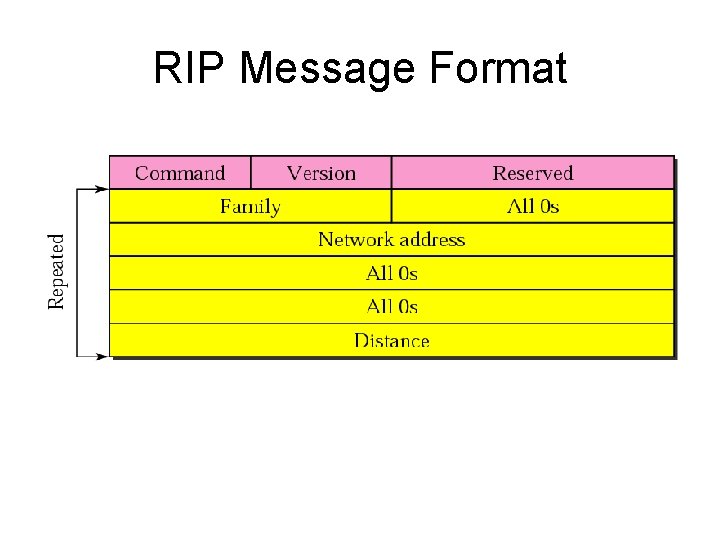
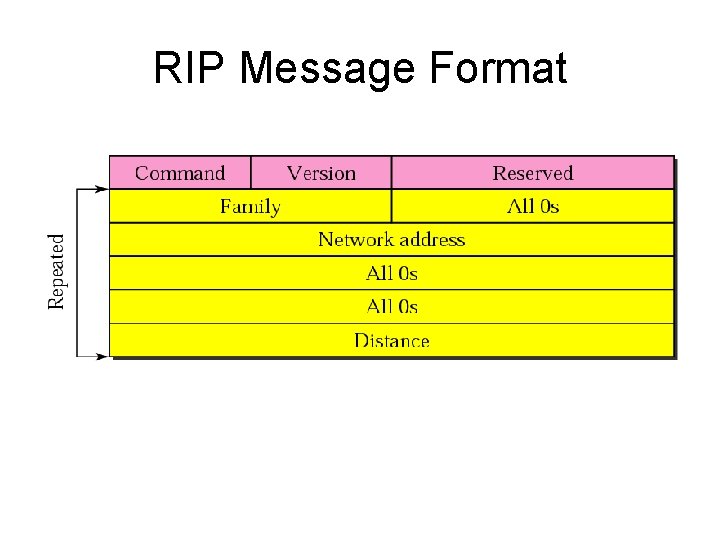
RIP Message Format
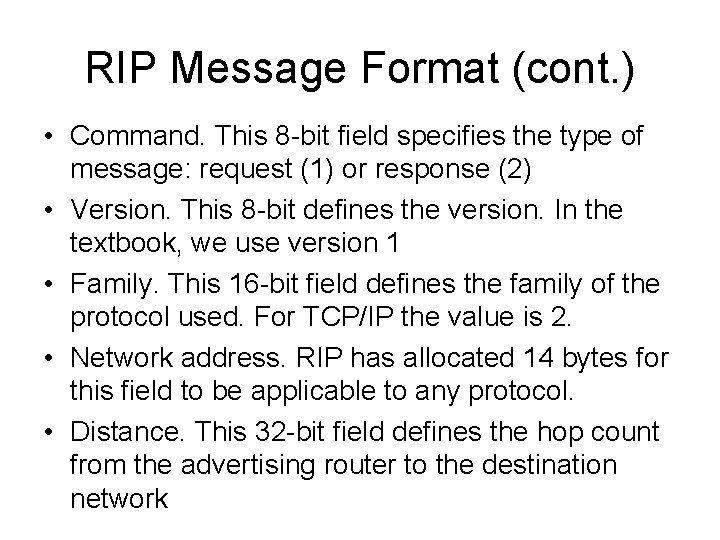
RIP Message Format (cont. ) • Command. This 8 -bit field specifies the type of message: request (1) or response (2) • Version. This 8 -bit defines the version. In the textbook, we use version 1 • Family. This 16 -bit field defines the family of the protocol used. For TCP/IP the value is 2. • Network address. RIP has allocated 14 bytes for this field to be applicable to any protocol. • Distance. This 32 -bit field defines the hop count from the advertising router to the destination network
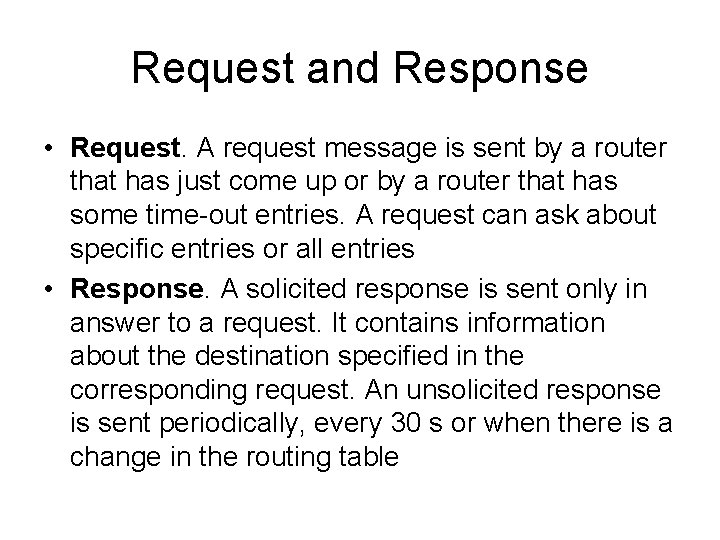
Request and Response • Request. A request message is sent by a router that has just come up or by a router that has some time-out entries. A request can ask about specific entries or all entries • Response. A solicited response is sent only in answer to a request. It contains information about the destination specified in the corresponding request. An unsolicited response is sent periodically, every 30 s or when there is a change in the routing table
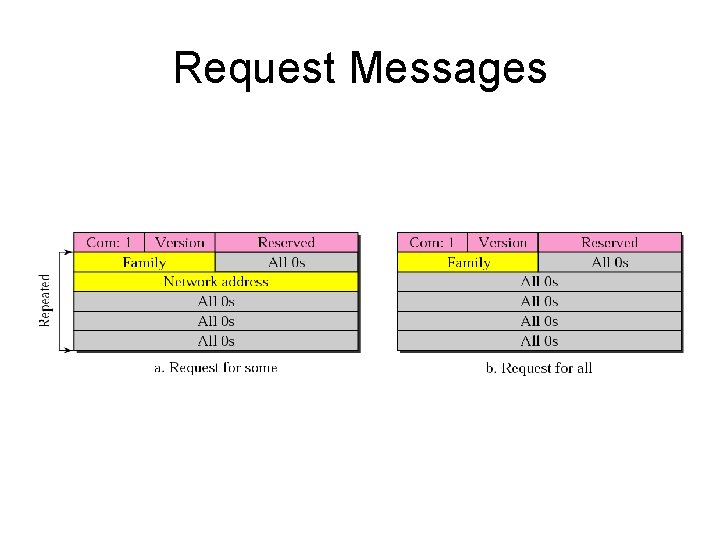
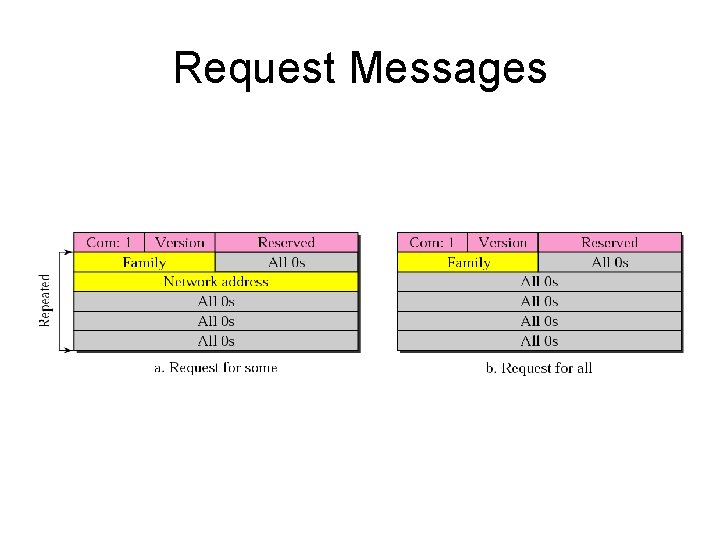
Request Messages
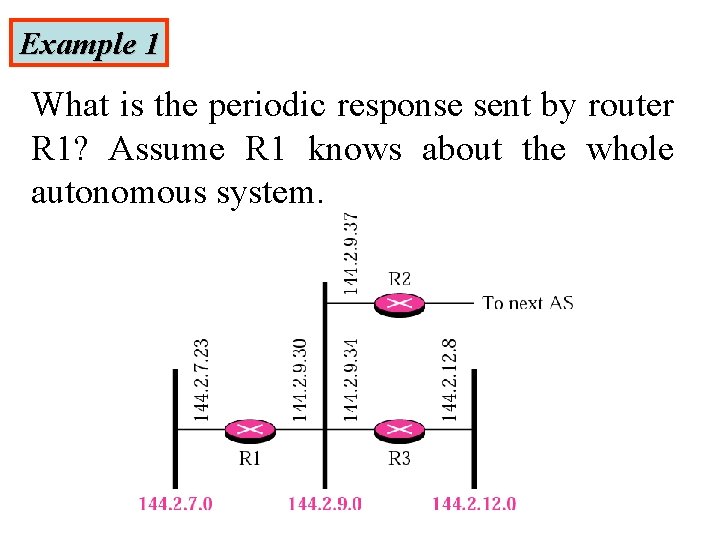
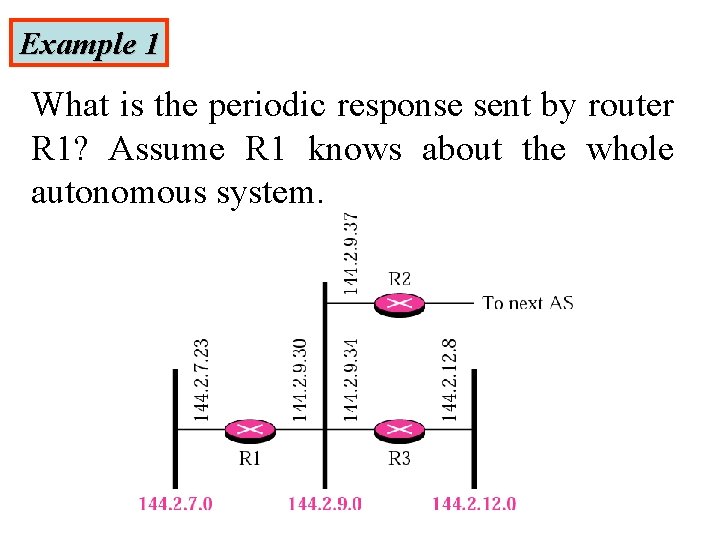
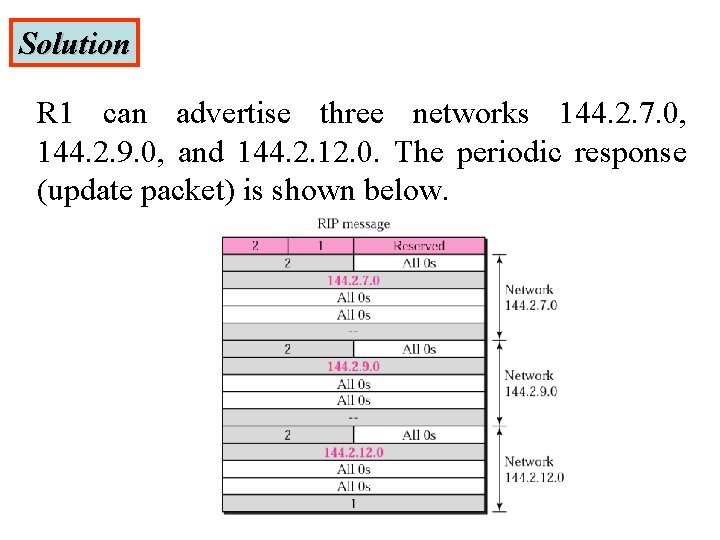
Example 1 What is the periodic response sent by router R 1? Assume R 1 knows about the whole autonomous system.
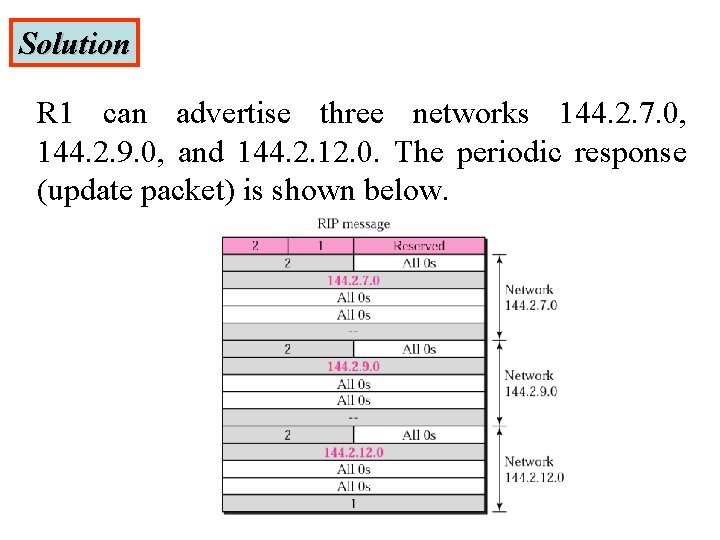
Solution R 1 can advertise three networks 144. 2. 7. 0, 144. 2. 9. 0, and 144. 2. 12. 0. The periodic response (update packet) is shown below.
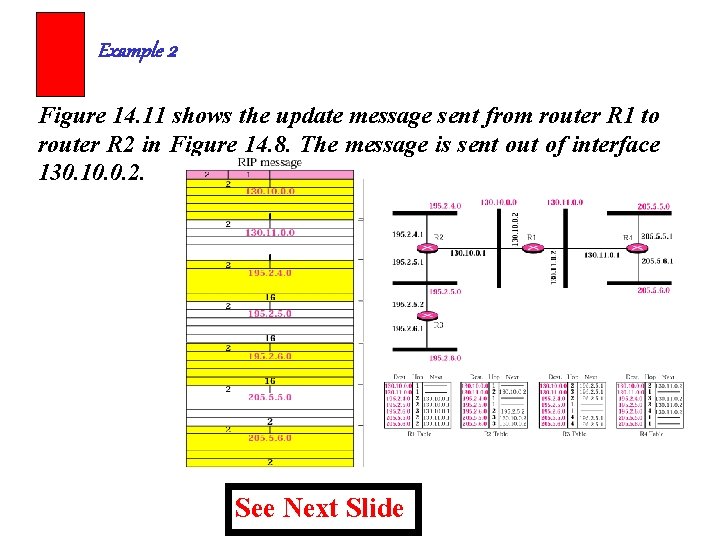
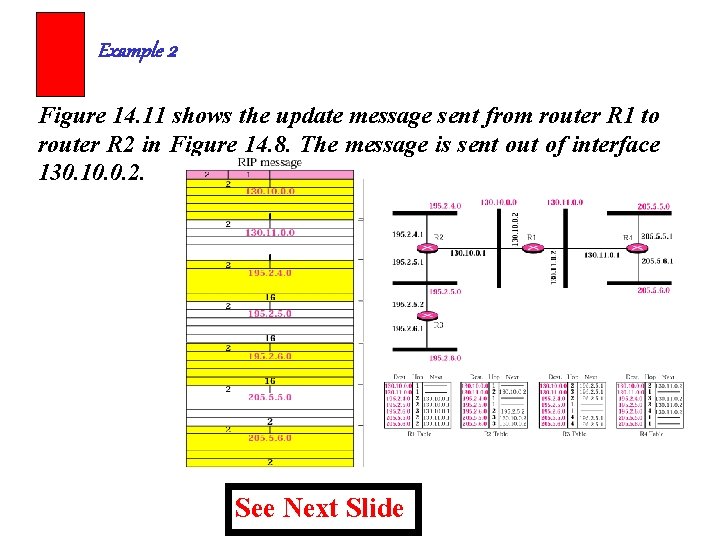
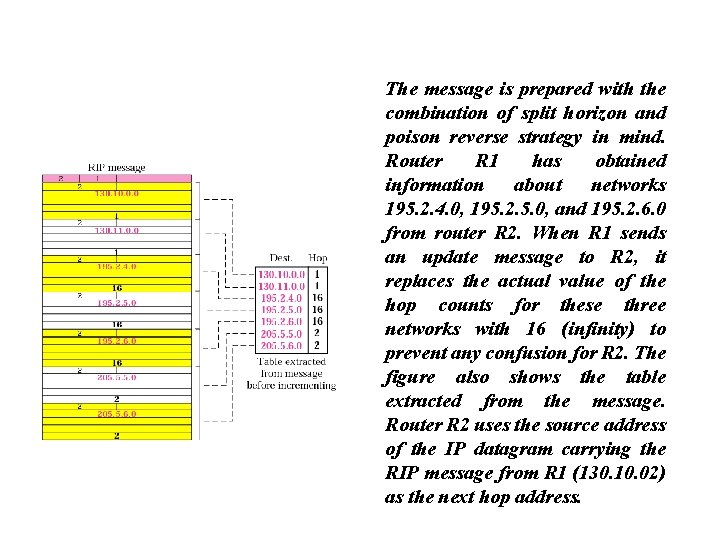
Example 2 Figure 14. 11 shows the update message sent from router R 1 to router R 2 in Figure 14. 8. The message is sent out of interface 130. 10. 0. 2. See Next Slide
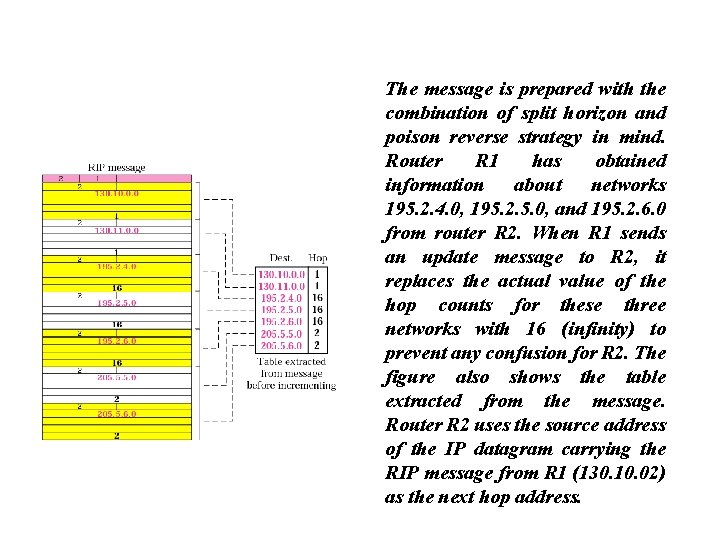
The message is prepared with the combination of split horizon and poison reverse strategy in mind. Router R 1 has obtained information about networks 195. 2. 4. 0, 195. 2. 5. 0, and 195. 2. 6. 0 from router R 2. When R 1 sends an update message to R 2, it replaces the actual value of the hop counts for these three networks with 16 (infinity) to prevent any confusion for R 2. The figure also shows the table extracted from the message. Router R 2 uses the source address of the IP datagram carrying the RIP message from R 1 (130. 10. 02) as the next hop address.
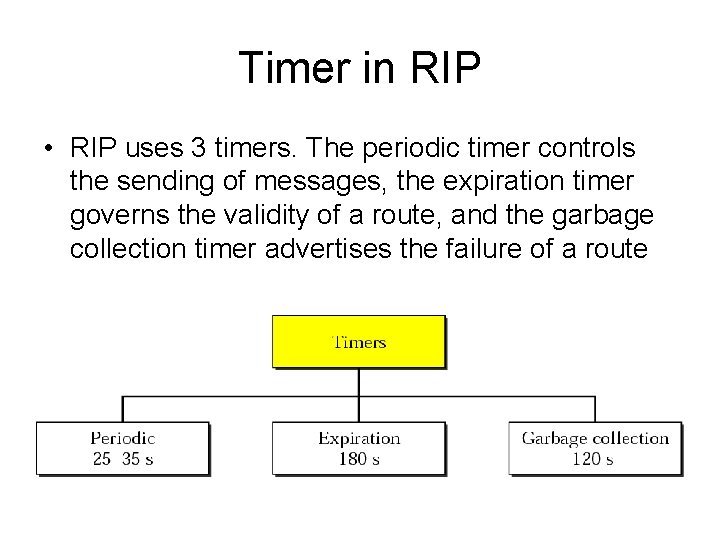
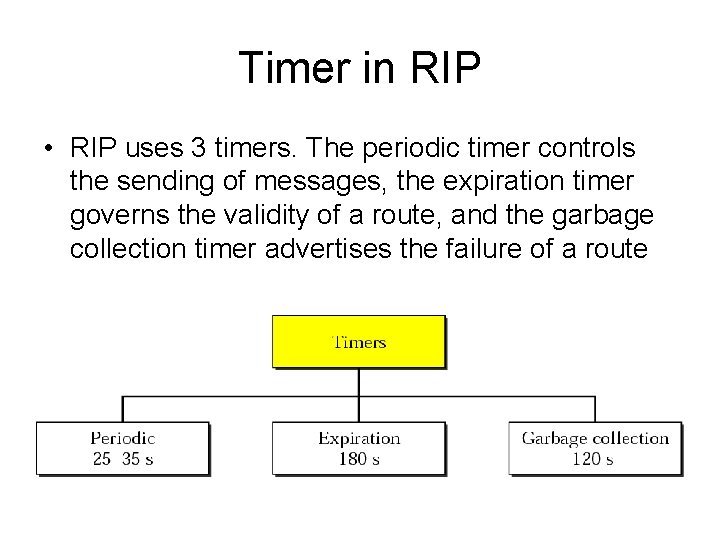
Timer in RIP • RIP uses 3 timers. The periodic timer controls the sending of messages, the expiration timer governs the validity of a route, and the garbage collection timer advertises the failure of a route
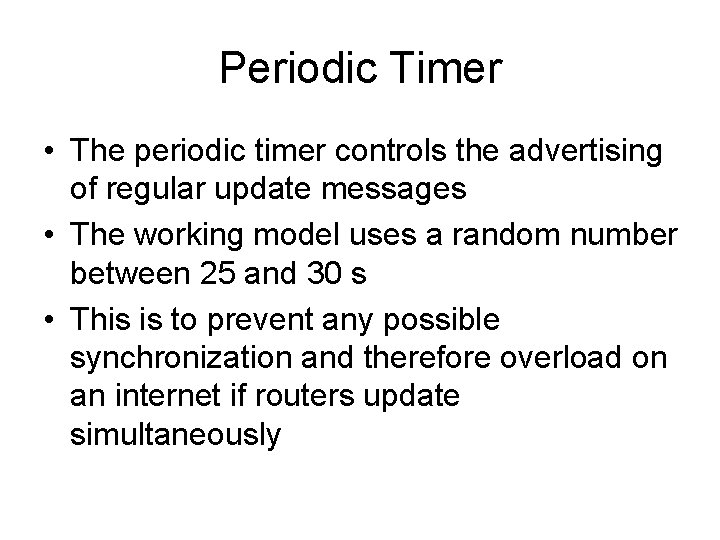
Periodic Timer • The periodic timer controls the advertising of regular update messages • The working model uses a random number between 25 and 30 s • This is to prevent any possible synchronization and therefore overload on an internet if routers update simultaneously
Expiration Timer • The expiration timer governs the validity of a route • When a router receives update information for a route, the expiration timer is set to 180 s for that particular route • Every time a new update for the route is received, the timer is reset • If the timer is expired, the hop count of the route is set to 16, which means the destination is unreachable
Garbage Collection Timer • When the information about a route becomes invalid, the router does not immediately purge that route from its table • Instead, it continues to advertise the route with a metric value of 16 • At the same time, the garbage collection timer is set to 120 s for that route • When the count reaches zero, the route is purged from the table
Example 3 A routing table has 20 entries. It does not receive information about five routes for 200 s. How many timers are running at this time? Solution The 21 timers are listed below: Periodic timer: 1 Expiration timer: 20 − 5 = 15 Garbage collection timer: 5
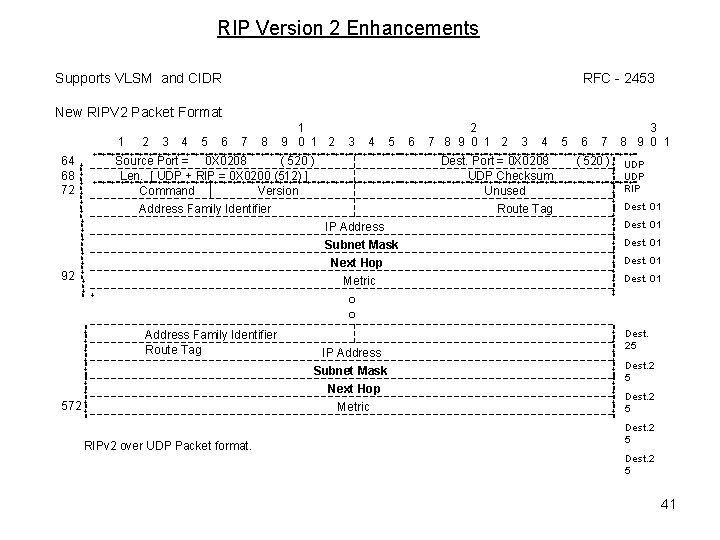
RIP Version 2 • RIP version 2 was designed to overcome some of the shortcomings of version 1 • The designers of version 2 have not augmented the length of the message for each entry • They have only replaced those fields in version 1 that were filled with 0 s for the TCP/IP protocol with some new fields
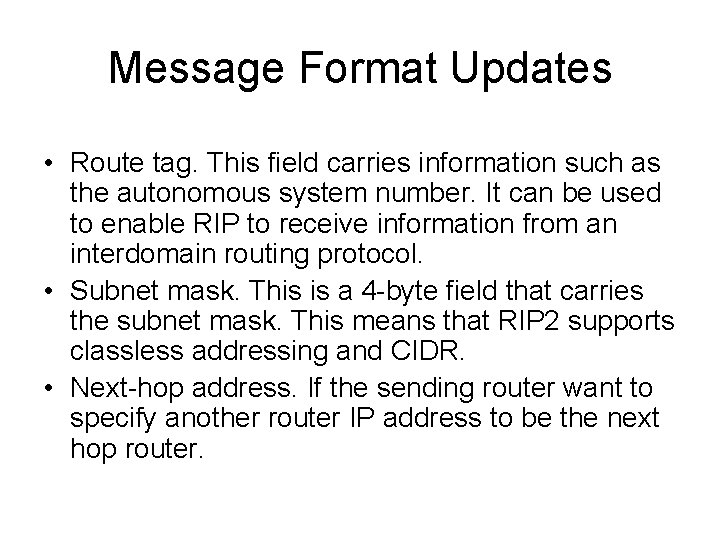
Message Format Updates • Route tag. This field carries information such as the autonomous system number. It can be used to enable RIP to receive information from an interdomain routing protocol. • Subnet mask. This is a 4 -byte field that carries the subnet mask. This means that RIP 2 supports classless addressing and CIDR. • Next-hop address. If the sending router want to specify another router IP address to be the next hop router.
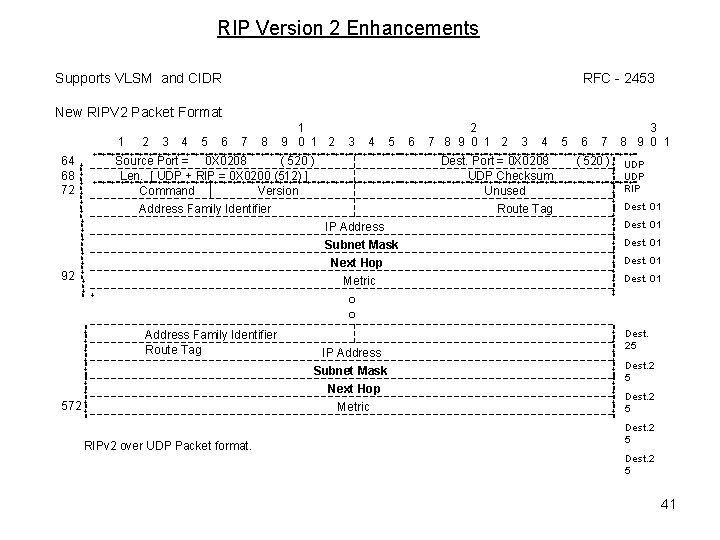
RIP Version 2 Enhancements Supports VLSM and CIDR RFC - 2453 New RIPV 2 Packet Format 1 4 5 6 7 8 3 4 5 6 3 8 9 0 1 7 +=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+==+=+=+=+=+=+=+=+=+=+=+=+=+= Source Port = 0 X 0208 ( 520 ) Dest. Port = 0 X 0208 ( 520 ) UDP Len. [ UDP + RIP = 0 X 0200 (512) ] UDP Checksum +=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+==+=+=+=+=+=+=+=+=+=+=+=+=+= RIP Command Version Unused Dest. 01 Address Family Identifier Route Tag Dest. 01 IP Address Dest. 01 Subnet Mask Dest. 01 Next Hop =+=+=+=+=+=+=+=+=+ + 92 3 2 7 8 9 0 1 2 Address Family Identifier Route Tag RIPv 2 over UDP Packet format. IP Address Subnet Mask Next Hop Metric =+=+=+=+=+==+=+=+=+= 572 Metric =+=+=+=+=+=+=+=+=++ 64 68 72 2 1 9 0 1 2 Dest. 01 Dest. 25 Dest. 2 5 41