Chapter 11 Unicast Routing Protocols RIP OSPF BGP
Chapter 11 Unicast Routing Protocols (RIP, OSPF, BGP) (How the routers’ tables are filled in) Dr. Clincy 1
MULTICAST ROUTING Now we understand what multicasting is Now let’s understand how packets are routed in the multicast case Some Objectives of multicast routing (very complex) • Each Rx of the group must get only one copy of the packet • Rx’s not belonging to the group DO NOT get a copy of the packet • The packet can not visit the same router more than once (no loops) • The route from Tx to various Rx’s must be optimal (shortest path) Dr. Clincy Lecture 2
MULTICAST TREES • Recall in the RIP/OSPF unicast World, we converted networks to graphs in finding the optimal routes • For graphs, nodes can have both successors and predecessors • In the multicast World, networks are converted to trees • Tree has a hierarchical structure • Each node on a tree has (1) a single parent and (2) zero to multiple off-springs (children) • The root (source or Tx) of the tree is the initial node (has no parent) • A leaf (group members) of a tree has no child • Called Spanning Tree provided all nodes are connected • NOTE: show students difference between graph & tree Lecture Dr. Clincy 3
Two Types of Trees are used for multicasting by protocols: • Source-Based Trees – a single tree is created for each Source-to-Group combination. For example, given M sources and N groups, there would be a maximum of Mx. N trees • Group-Shared Trees – each group has it’s own tree. Given N groups, there would be a maximum of N trees. Dr. Clincy Lecture 4
Source-Based Tree • Given a source needs to send a packet to group-1, a certain tree is used • Given the same source needs to send a packet to group-5, a different tree is used • Challenge: (1) determining all source-to-group combinations, (2) each tree needs to be optimal Two approaches used to create optimal source-based trees: • (1 st) An extension to the unicast distance vector routing we covered in regards to RIP – used by DVMRP (Distance Vector Multicasting Routing Protocol) • (2 nd) An extension to the unicast link state routing we covered in regards to OSPF – used by MOSPF (Multicast Open Shortest Path First) • Another protocol called PIM-DM (Protocol Independent Multicast – Dense Mode) uses either RIP or OSPF depending on need Dr. Clincy Lecture 5
Group-Shared Tree • Given a source (source x) needs to send a packet to group-1, a certain tree is used • Given a different source (source y) needs to send a packet to the same group, group-1, the same tree is used • If either source-x or source-y need to send to a different group, the tree would change • Note: the tree changes when the group changes – the tree remains the same for a group regardless if the source changes – the group determines the tree Two approaches used to create optimal group-shared trees: • (1 st) Steiner Tree – the optimal tree has the minimum cost routes like Dijkstra’ algorithm however, instead of it being based around a source node, it is not based around any particular source (very complex and has to re-run every time the topology changes) – not really used by the Internet • (2 nd) Rendezvous-Point Tree – a tree is created for each group and a single router is selected as the core or rendezvous point or root of the tree. The CBT (Core-Based Tree Protocol) and PIM-SM (Protocol Independent Multicast – Sparse Mode) use the rendezvous-point tree approach. Dr. Clincy Lecture 6
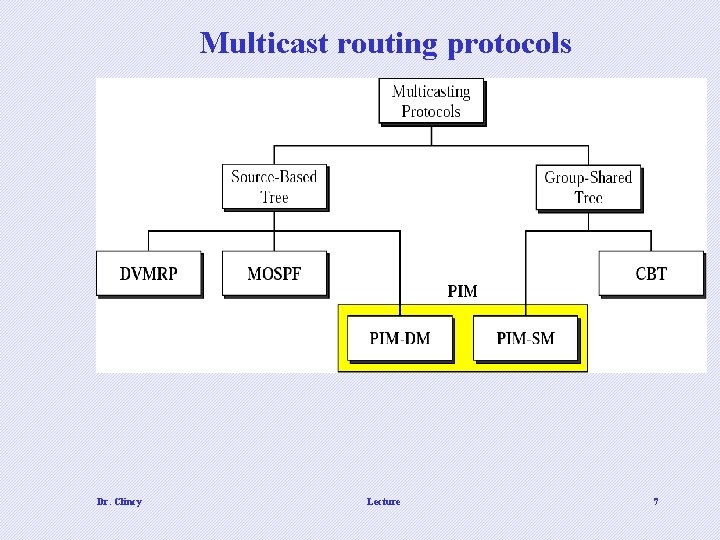
Multicast routing protocols Dr. Clincy Lecture 7
DVMRP • Distance Vector Multicast Routing Protocol –similar to the distance vector routing protocol we covered for the unicast case – next hop scenario. • For DVMRP, the optimal tree is not pre-defined – only the next hop How do we build a tree using the DVMRP approach ? • Use a modified “flooding” approach • Recall what flooding is: a router sends a copy of a packet out of all of it’s interfaces – all interfaces except the interface the packet came in on • Flooding will cause looping problems (ie. the same packet copy that left the router will re-visit the router) • The flooding is modified to stop the looping problem How is the flooding modified ? ? ? Dr. Clincy Lecture 8
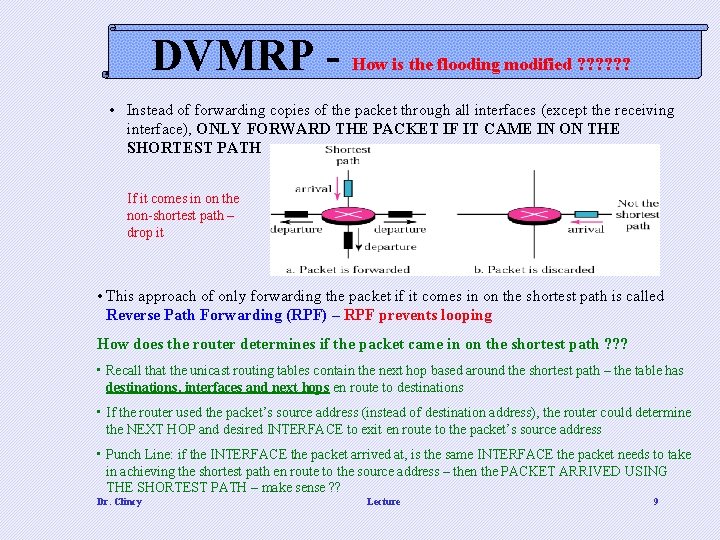
DVMRP - How is the flooding modified ? ? ? • Instead of forwarding copies of the packet through all interfaces (except the receiving interface), ONLY FORWARD THE PACKET IF IT CAME IN ON THE SHORTEST PATH If it comes in on the non-shortest path – drop it • This approach of only forwarding the packet if it comes in on the shortest path is called Reverse Path Forwarding (RPF) – RPF prevents looping How does the router determines if the packet came in on the shortest path ? ? ? • Recall that the unicast routing tables contain the next hop based around the shortest path – the table has destinations, interfaces and next hops en route to destinations • If the router used the packet’s source address (instead of destination address), the router could determine the NEXT HOP and desired INTERFACE to exit en route to the packet’s source address • Punch Line: if the INTERFACE the packet arrived at, is the same INTERFACE the packet needs to take in achieving the shortest path en route to the source address – then the PACKET ARRIVED USING THE SHORTEST PATH – make sense ? ? Dr. Clincy Lecture 9
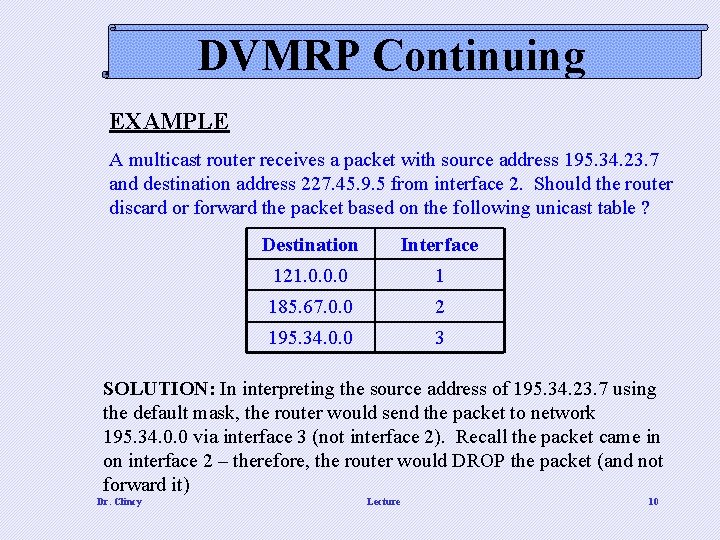
DVMRP Continuing EXAMPLE A multicast router receives a packet with source address 195. 34. 23. 7 and destination address 227. 45. 9. 5 from interface 2. Should the router discard or forward the packet based on the following unicast table ? Destination Interface 121. 0. 0. 0 1 185. 67. 0. 0 2 195. 34. 0. 0 3 SOLUTION: In interpreting the source address of 195. 34. 23. 7 using the default mask, the router would send the packet to network 195. 34. 0. 0 via interface 3 (not interface 2). Recall the packet came in on interface 2 – therefore, the router would DROP the packet (and not forward it) Dr. Clincy Lecture 10
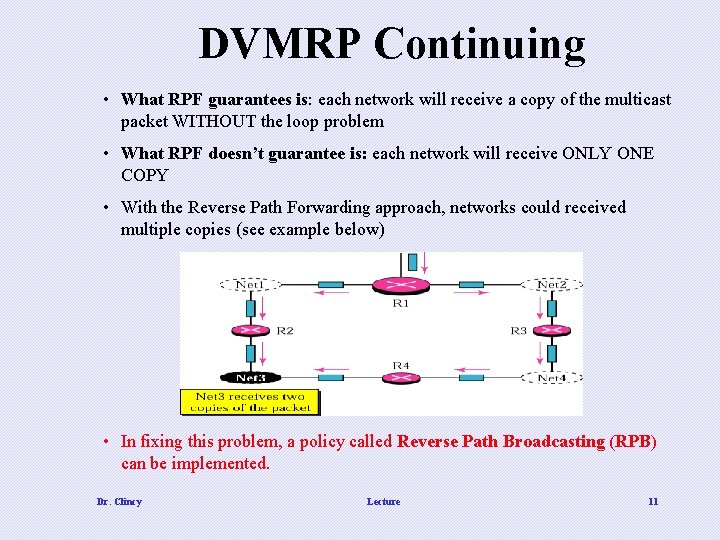
DVMRP Continuing • What RPF guarantees is: each network will receive a copy of the multicast packet WITHOUT the loop problem • What RPF doesn’t guarantee is: each network will receive ONLY ONE COPY • With the Reverse Path Forwarding approach, networks could received multiple copies (see example below) • In fixing this problem, a policy called Reverse Path Broadcasting (RPB) can be implemented. Dr. Clincy Lecture 11
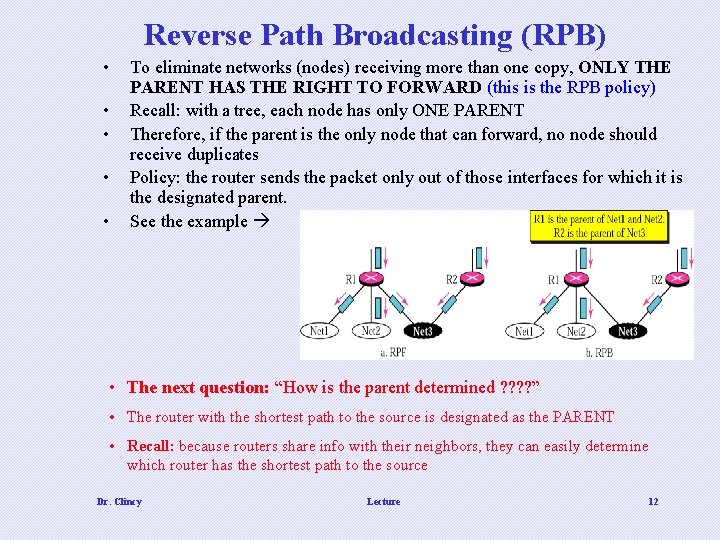
Reverse Path Broadcasting (RPB) • • • To eliminate networks (nodes) receiving more than one copy, ONLY THE PARENT HAS THE RIGHT TO FORWARD (this is the RPB policy) Recall: with a tree, each node has only ONE PARENT Therefore, if the parent is the only node that can forward, no node should receive duplicates Policy: the router sends the packet only out of those interfaces for which it is the designated parent. See the example • The next question: “How is the parent determined ? ? ” • The router with the shortest path to the source is designated as the PARENT • Recall: because routers share info with their neighbors, they can easily determine which router has the shortest path to the source Dr. Clincy Lecture 12
RPB creates a shortest path broadcast tree (not multicast tree) from the source to each destination. It guarantees that each destination receives one and only one copy of the packet. Dr. Clincy Lecture 13
Reverse Path Multicasting (RPM) • Recall RPB broadcast a packet versus multicast • How is multicasting achieved ? (1) the first packet is broadcasted no matter what, (2) the remaining packets are multicasted based on pruning and grafting • Another name for pruning and grafting is Reverse Path Multicasting (RPM) Based on pruning • Based on grafting • • Suppose a “leaf” router (a router with NO children) had previously sent a prune message and suddenly realize it NOW INTERESTED in receiving the multicast packet The leaf router will issue a grafting message upstream and as a result, multicasting will resume • • • Using the IGMP (Internet Group Management Protocol), each PARENT ROUTER holds a membership and knows which groups it is not responsible for. The PARENT ROUTER sends a “prune message” to it’s upstream router letting the upstream router know NOT to send any packets belonging to certain no-interest groups through that corresponding interface. That upstream router will do the same to it’s upstream router This creates a “pruning” effect in that only the packets belonging to a group are forwarded through a particular interface Dr. Clincy • Lecture 14
RPM adds pruning and grafting to RPB to create a multicast shortest path tree that supports dynamic membership changes. Dr. Clincy Lecture 15
MOSPF • MOSPF stands for Multicast Open Shortest Path First • Extension of the OSPF protocol • Instead of the tree being generated gradually – it’s generated all at once – by using the link state database (recall) • With the link state database, the router can see the entire topology • Each router could then use Dijikstra’s algorithm and obtain a least cost tree for each router (or node) • For multicasting routing, we need a tree for each source/group pair • For the source/group trees, the only hosts with the particular group address are included • We do the previous by associating the unicast address with the group address – with this approach, we do the calculation the same way using the unicast address however, the associated group address dictates if the host is added to the tree or not • MOSPF is a data-driven protocol – the first time a MOSPF router sees a datagram with a given source and group address, the router calculates Dijkstra Dr. Clincy Lecture 16
Core-Based Tree (CBT) Protocol • Is a group-shared protocol • Autonomous systems are divided into regions and a core router or rendezvous point is used for each region • In forming a tree: • 1 st: the core router or rendezvous router is selected (very complex - will not cover this process – not covered in your book as well) • 2 nd: all other routers are informed of the unicast address of rendezvous router • 3 rd: all routers wanting to join group sends a “join message” to the rendezvous router • 4 th: the intermediate routers between the rendezvous router and Tx router record the address of the source and the interface in which the packet came into the router on • 5 th: after the rendezvous has received all joined messages – the tree is formed Dr. Clincy Lecture 17
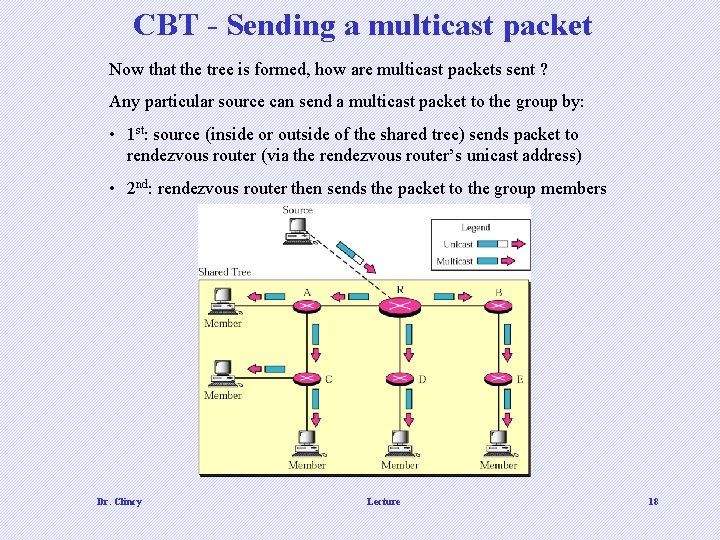
CBT - Sending a multicast packet Now that the tree is formed, how are multicast packets sent ? Any particular source can send a multicast packet to the group by: • 1 st: source (inside or outside of the shared tree) sends packet to rendezvous router (via the rendezvous router’s unicast address) • 2 nd: rendezvous router then sends the packet to the group members Dr. Clincy Lecture 18
DVMRP & MOSPF Versus CBT • For DVMRP and MOSPF, the tree is created from the root • For CBT, the tree is created starting from the leaves • For DVMRP, the tree is first made via broadcast and then pruned into a multicast tree • For CBT, initially there is no tree and then a tree is created gradually via grafting (ie. announcing to the core you want to be apart of the group) Dr. Clincy Lecture 19
Protocol Independent Multicast – Dense Mode (PIM-DM) • PIM-DM is used in a dense multicast environment, such as a LAN environment. • PIM-DM is justifiably used when each router is involved in multicasting – therefore broadcasting is justified • PIM-DM uses reverse path forwarding, pruning and grafting techniques for multicasting Dr. Clincy Lecture 20
Protocol Independent Multicast – Sparse Mode (PIM-SM) • PIM-SM is used in a sparse multicast environment, such as a WAN environment. • PIM-SM is used when there is a slight possibility each router is involved in multicasting – therefore NOT justifying broadcasting • PIM-SM operates more like CBT • PIM-SM allows the ability to switch between source-based tree and groupshared tree strategies Dr. Clincy Lecture 21
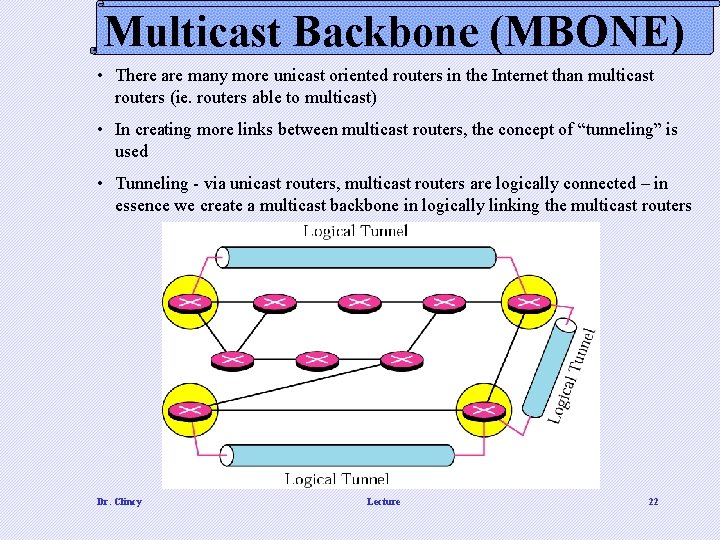
Multicast Backbone (MBONE) • There are many more unicast oriented routers in the Internet than multicast routers (ie. routers able to multicast) • In creating more links between multicast routers, the concept of “tunneling” is used • Tunneling - via unicast routers, multicast routers are logically connected – in essence we create a multicast backbone in logically linking the multicast routers Dr. Clincy Lecture 22
MBONE – How are tunnels created ? How to create a tunnel • 1 st: encapsulate multicast packet inside a unicast packet (in the data field) • 2 nd: the unicast intermediate routers route the packet to the next multicast router Dr. Clincy Lecture 23
Transport Layer- Chapter 14 - UDP Transport Layer- Chapter 15 - TCP Dr. Clincy Lecture 24
Question 1 to Students • What is the Transport Layer’s function/job/objective ? ? ? • What are some of the tasks in implementing the “objective” Dr. Clincy Lecture 25
Question 2 to Students What’s their understanding, if any, between UDP and TCP. In simple terms prior to the lecture, explain the difference between UDP and TCP Dr. Clincy Lecture 26
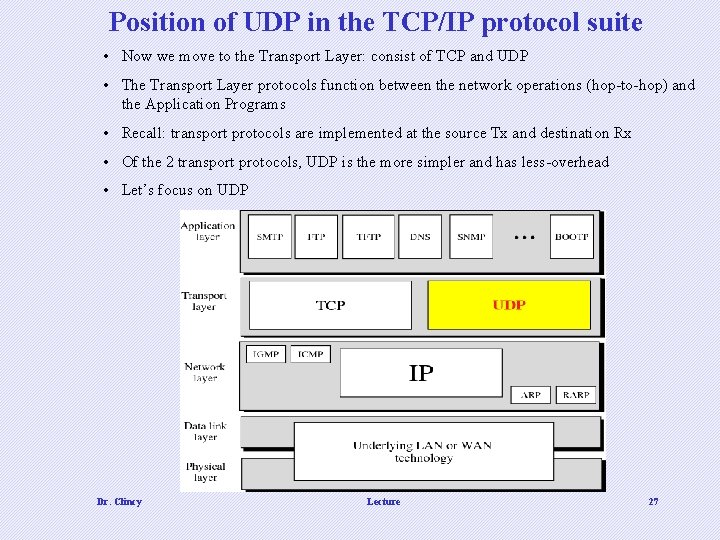
Position of UDP in the TCP/IP protocol suite • Now we move to the Transport Layer: consist of TCP and UDP • The Transport Layer protocols function between the network operations (hop-to-hop) and the Application Programs • Recall: transport protocols are implemented at the source Tx and destination Rx • Of the 2 transport protocols, UDP is the more simpler and has less-overhead • Let’s focus on UDP Dr. Clincy Lecture 27
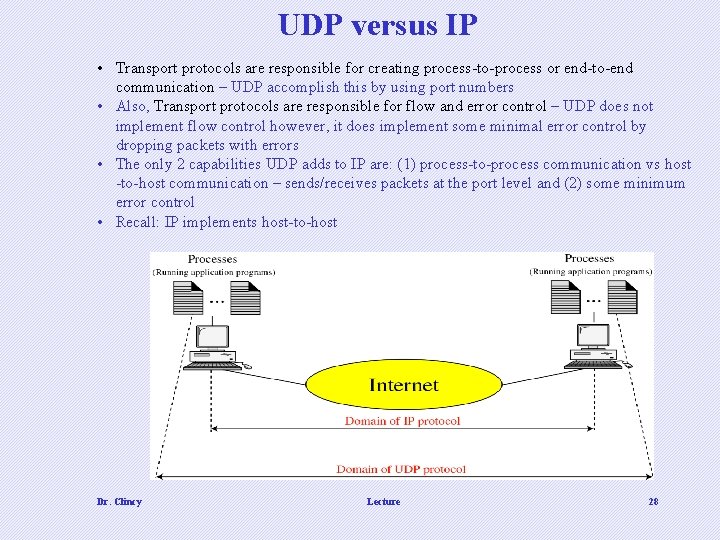
UDP versus IP • Transport protocols are responsible for creating process-to-process or end-to-end communication – UDP accomplish this by using port numbers • Also, Transport protocols are responsible for flow and error control – UDP does not implement flow control however, it does implement some minimal error control by dropping packets with errors • The only 2 capabilities UDP adds to IP are: (1) process-to-process communication vs host -to-host communication – sends/receives packets at the port level and (2) some minimum error control • Recall: IP implements host-to-host Dr. Clincy Lecture 28
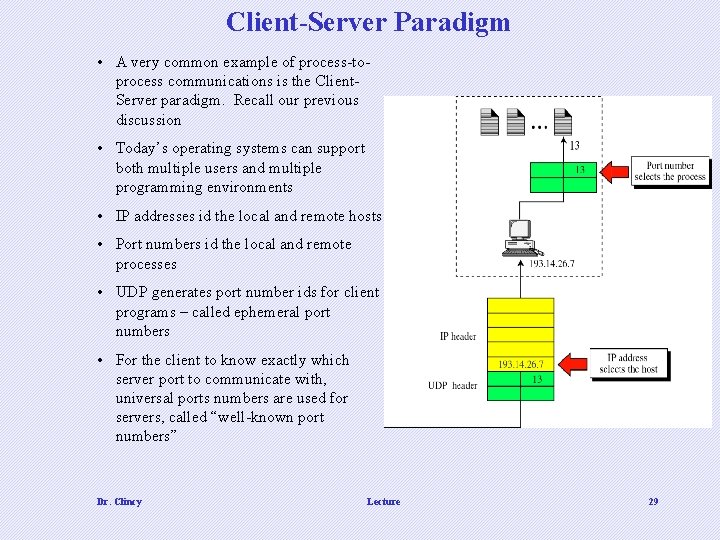
Client-Server Paradigm • A very common example of process-toprocess communications is the Client. Server paradigm. Recall our previous discussion • Today’s operating systems can support both multiple users and multiple programming environments • IP addresses id the local and remote hosts • Port numbers id the local and remote processes • UDP generates port number ids for client programs – called ephemeral port numbers • For the client to know exactly which server port to communicate with, universal ports numbers are used for servers, called “well-known port numbers” Dr. Clincy Lecture 29
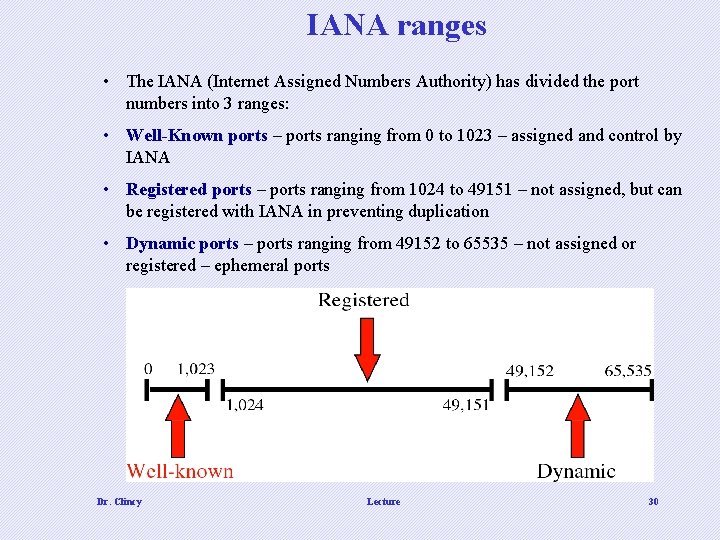
IANA ranges • The IANA (Internet Assigned Numbers Authority) has divided the port numbers into 3 ranges: • Well-Known ports – ports ranging from 0 to 1023 – assigned and control by IANA • Registered ports – ports ranging from 1024 to 49151 – not assigned, but can be registered with IANA in preventing duplication • Dynamic ports – ports ranging from 49152 to 65535 – not assigned or registered – ephemeral ports Dr. Clincy Lecture 30
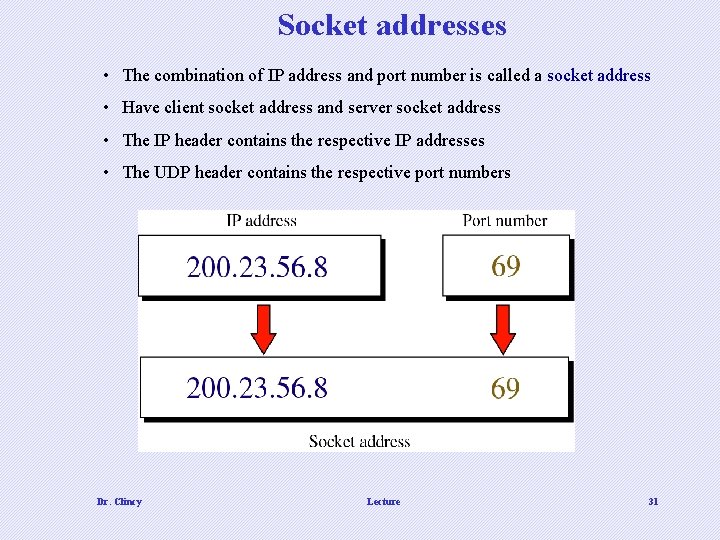
Socket addresses • The combination of IP address and port number is called a socket address • Have client socket address and server socket address • The IP header contains the respective IP addresses • The UDP header contains the respective port numbers Dr. Clincy Lecture 31
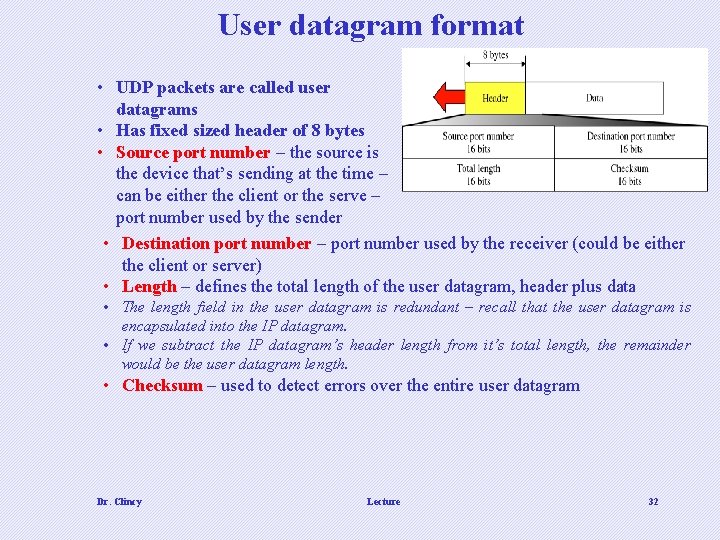
User datagram format • UDP packets are called user datagrams • Has fixed sized header of 8 bytes • Source port number – the source is the device that’s sending at the time – can be either the client or the serve – port number used by the sender • Destination port number – port number used by the receiver (could be either the client or server) • Length – defines the total length of the user datagram, header plus data • The length field in the user datagram is redundant – recall that the user datagram is encapsulated into the IP datagram. • If we subtract the IP datagram’s header length from it’s total length, the remainder would be the user datagram length. • Checksum – used to detect errors over the entire user datagram Dr. Clincy Lecture 32
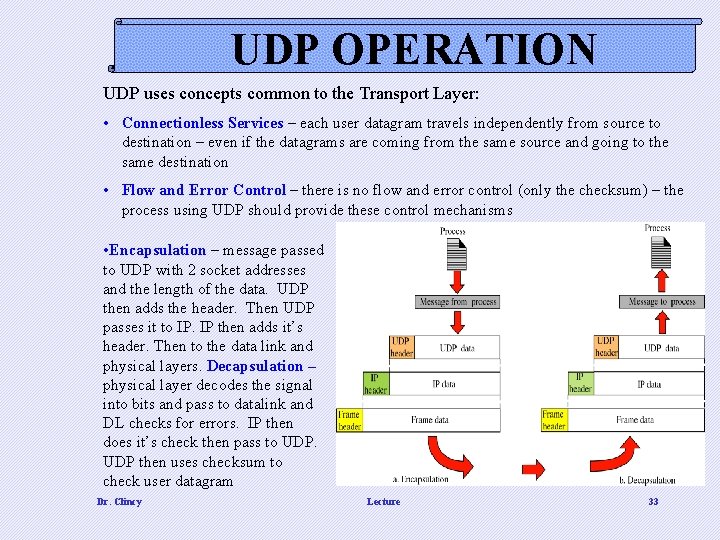
UDP OPERATION UDP uses concepts common to the Transport Layer: • Connectionless Services – each user datagram travels independently from source to destination – even if the datagrams are coming from the same source and going to the same destination • Flow and Error Control – there is no flow and error control (only the checksum) – the process using UDP should provide these control mechanisms • Encapsulation – message passed to UDP with 2 socket addresses and the length of the data. UDP then adds the header. Then UDP passes it to IP. IP then adds it’s header. Then to the data link and physical layers. Decapsulation – physical layer decodes the signal into bits and pass to datalink and DL checks for errors. IP then does it’s check then pass to UDP then uses checksum to check user datagram Dr. Clincy Lecture 33
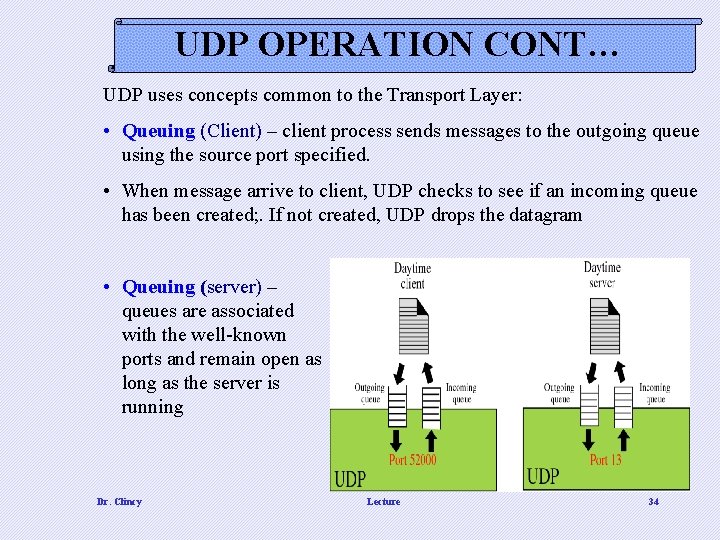
UDP OPERATION CONT… UDP uses concepts common to the Transport Layer: • Queuing (Client) – client process sends messages to the outgoing queue using the source port specified. • When message arrive to client, UDP checks to see if an incoming queue has been created; . If not created, UDP drops the datagram • Queuing (server) – queues are associated with the well-known ports and remain open as long as the server is running Dr. Clincy Lecture 34
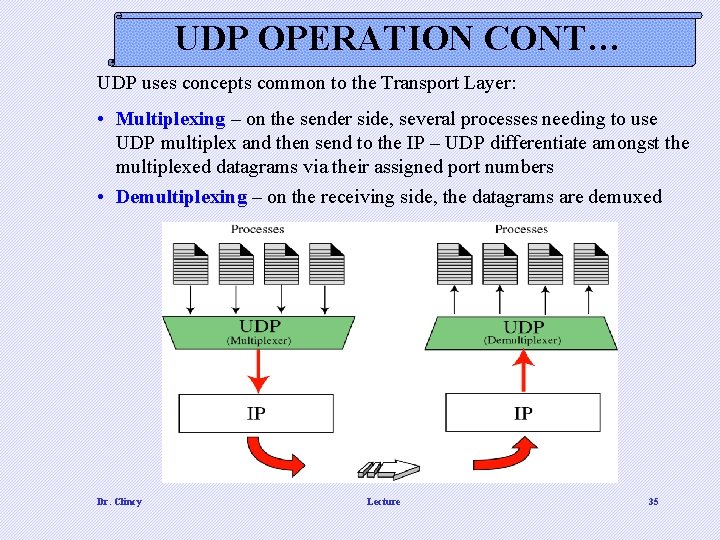
UDP OPERATION CONT… UDP uses concepts common to the Transport Layer: • Multiplexing – on the sender side, several processes needing to use UDP multiplex and then send to the IP – UDP differentiate amongst the multiplexed datagrams via their assigned port numbers • Demultiplexing – on the receiving side, the datagrams are demuxed Dr. Clincy Lecture 35

Transmission Control Protocol (TCP) Dr. Clincy Lecture 36
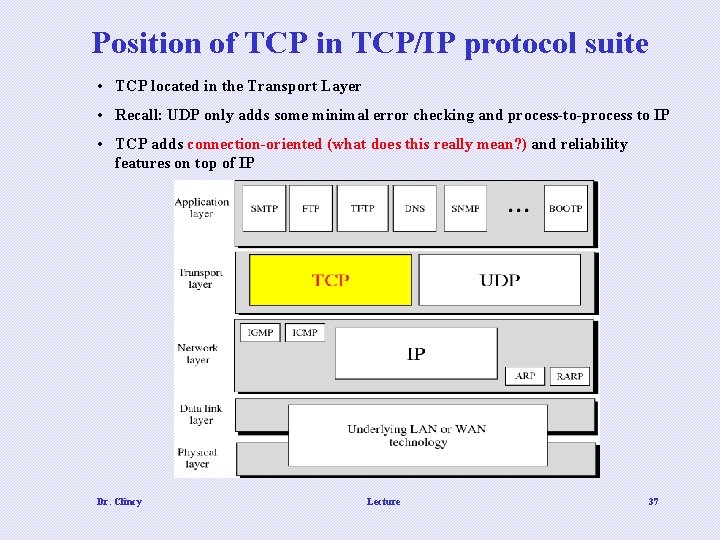
Position of TCP in TCP/IP protocol suite • TCP located in the Transport Layer • Recall: UDP only adds some minimal error checking and process-to-process to IP • TCP adds connection-oriented (what does this really mean? ) and reliability features on top of IP Dr. Clincy Lecture 37
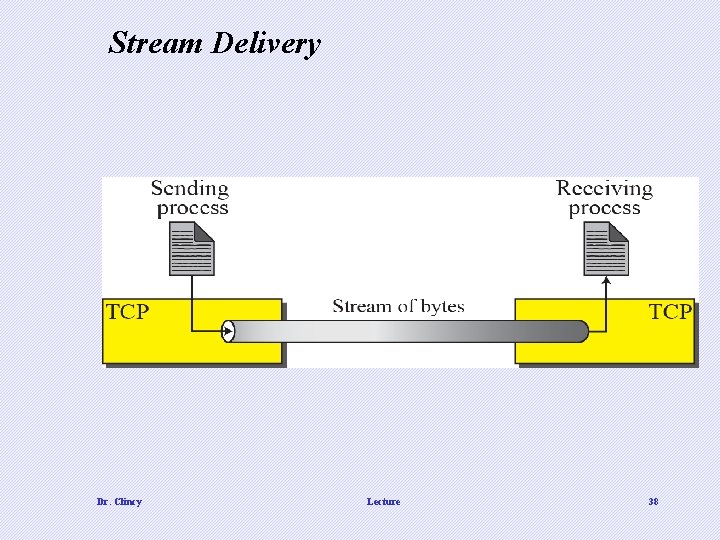
Stream Delivery Dr. Clincy Lecture 38
Transport Layer/TCP Responsibilities • Responsible for process-to-process communications (accomplished via the use of port numbers) • Responsible for flow control – uses a “sliding window” protocol to accomplish this • Responsible for error control – uses the acknowledgment packet, time-out and retransmission to accomplish this • Responsible for providing a connection mechanism • TCP Sender: (1) application send streams to transport layer, (2) Tx makes connection with Rx, (3) breaks up stream, (4) assign overhead and number, (5) send one by one • TCP Receiver: (1) wait for all pieces to arrive, (2) error check each piece, (3) deliver error-free pieces to receiving application as a stream, (4) after entire stream has been sent to receiving application, terminate connection Dr. Clincy Lecture 39
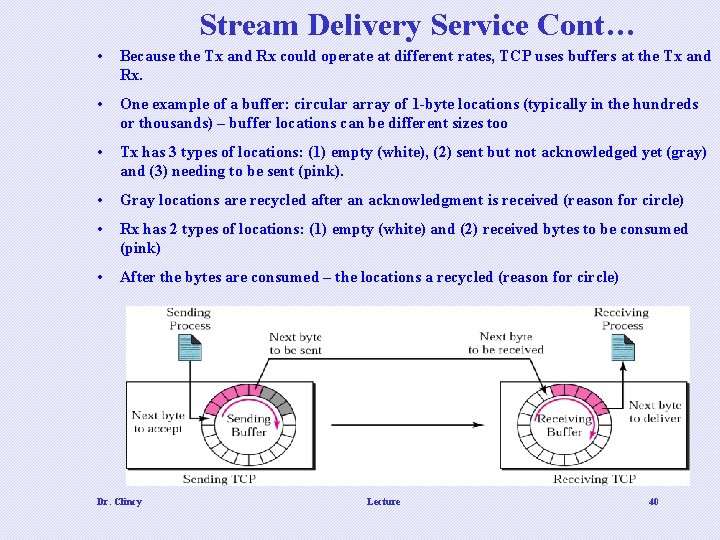
Stream Delivery Service Cont… • Because the Tx and Rx could operate at different rates, TCP uses buffers at the Tx and Rx. • One example of a buffer: circular array of 1 -byte locations (typically in the hundreds or thousands) – buffer locations can be different sizes too • Tx has 3 types of locations: (1) empty (white), (2) sent but not acknowledged yet (gray) and (3) needing to be sent (pink). • Gray locations are recycled after an acknowledgment is received (reason for circle) • Rx has 2 types of locations: (1) empty (white) and (2) received bytes to be consumed (pink) • After the bytes are consumed – the locations a recycled (reason for circle) Dr. Clincy Lecture 40
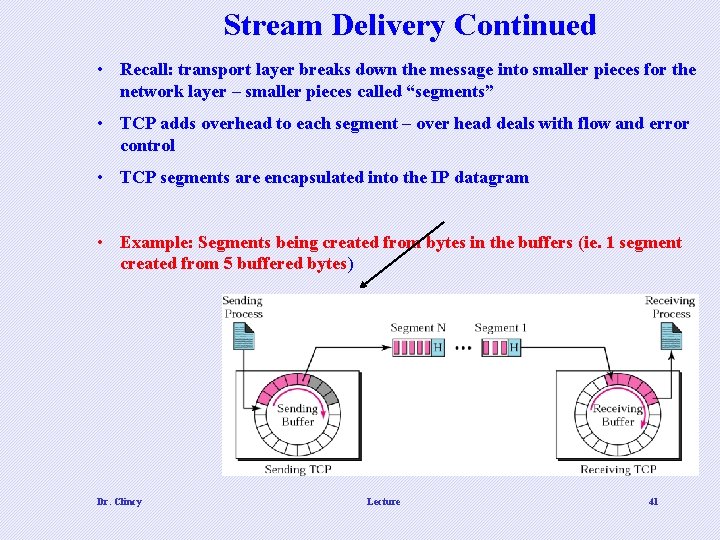
Stream Delivery Continued • Recall: transport layer breaks down the message into smaller pieces for the network layer – smaller pieces called “segments” • TCP adds overhead to each segment – over head deals with flow and error control • TCP segments are encapsulated into the IP datagram • Example: Segments being created from bytes in the buffers (ie. 1 segment created from 5 buffered bytes) Dr. Clincy Lecture 41
NUMBERING BYTES • TCP keeps track of segments using numbers relating to the bytes versus the segments • Sequence number and Acknowledgment Number are used and relate to the byte • The start number is randomly generated (versus always being 0) • For example, suppose 1057 is generated and let’s say 6000 bytes need to be sent – the numbering will range from 1057 to 7056 • Byte numbering is also used for flow and error control • After the bytes are numbered, TCP assigns a sequence # to each segment – the sequence # is the first byte number of the segment • The acknowledgment # is sequence # incremented each time a byte is received (ie. take a 4 -byte segment with starting sequence # 11, when byte 11 received, ack #=12, when byte 12 received, ack # = 13, etc. . ) Dr. Clincy Lecture 42
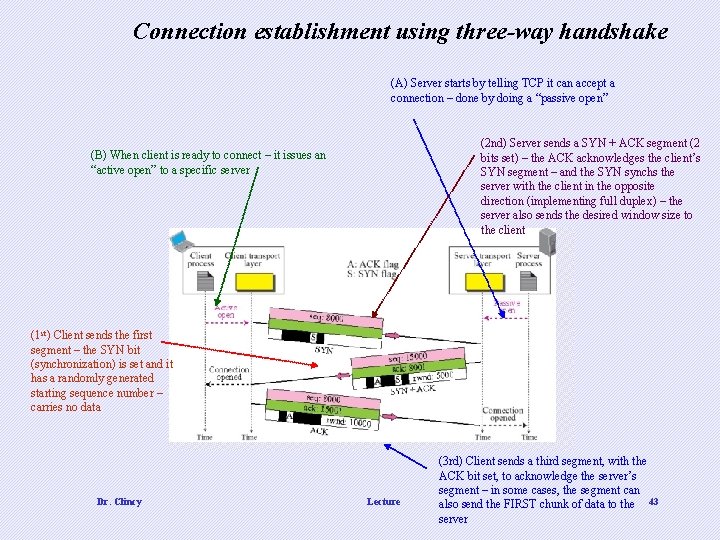
Connection establishment using three-way handshake (A) Server starts by telling TCP it can accept a connection – done by doing a “passive open” (2 nd) Server sends a SYN + ACK segment (2 bits set) – the ACK acknowledges the client’s SYN segment – and the SYN synchs the server with the client in the opposite direction (implementing full duplex) – the server also sends the desired window size to the client (B) When client is ready to connect – it issues an “active open” to a specific server (1 st) Client sends the first segment – the SYN bit (synchronization) is set and it has a randomly generated starting sequence number – carries no data Dr. Clincy Lecture (3 rd) Client sends a third segment, with the ACK bit set, to acknowledge the server’s segment – in some cases, the segment can also send the FIRST chunk of data to the 43 server
TCP - FLOW CONTROL • Flow Control – amount of data a Tx sends before receiving an acknowledgment from the Rx • Can send too much and overwhelm routers and etc. . • Can send too little and Tx stays idle too much waiting for acknowledgments • TCP defines a “window” that’s imposed on the buffer of data delivered • A sliding window is used to make transmission more efficient as well as to control the flow of data so that the destination does not become overwhelmed with data. • TCP’s sliding windows are byte oriented. Dr. Clincy Lecture 44
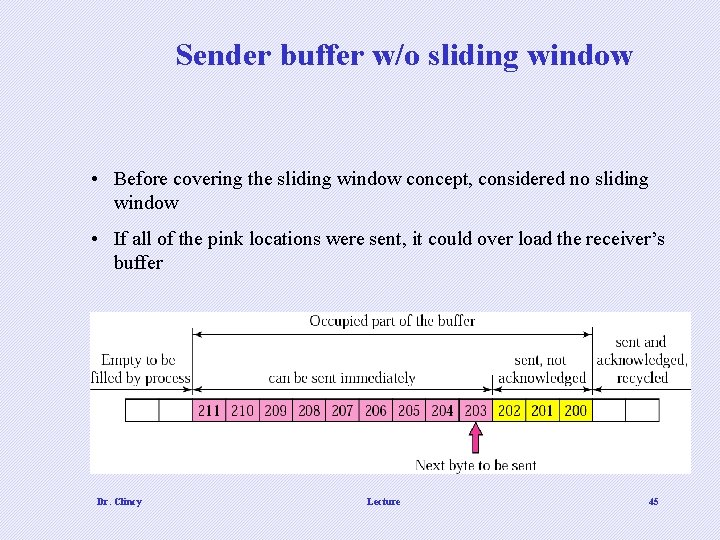
Sender buffer w/o sliding window • Before covering the sliding window concept, considered no sliding window • If all of the pink locations were sent, it could over load the receiver’s buffer Dr. Clincy Lecture 45
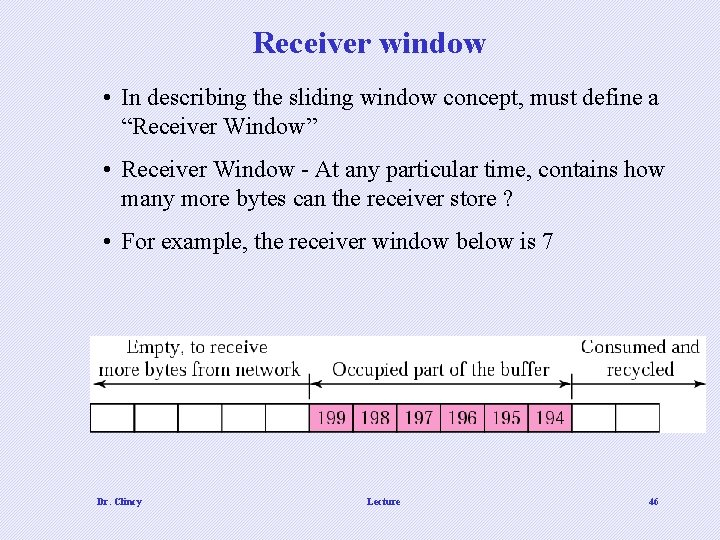
Receiver window • In describing the sliding window concept, must define a “Receiver Window” • Receiver Window - At any particular time, contains how many more bytes can the receiver store ? • For example, the receiver window below is 7 Dr. Clincy Lecture 46
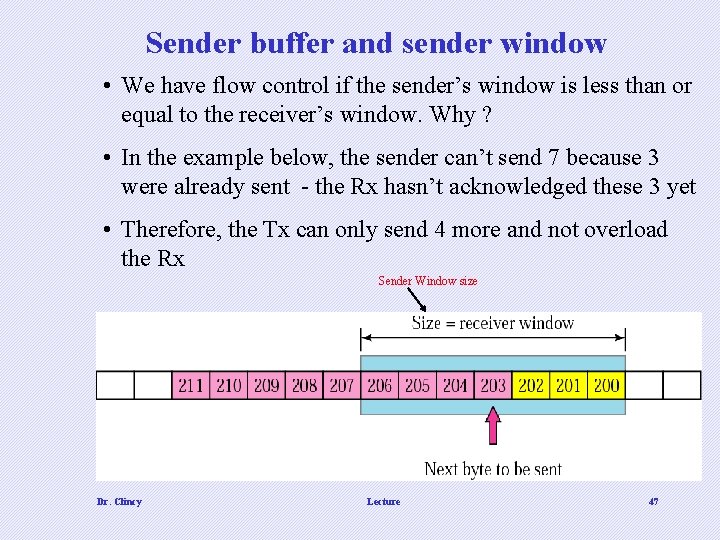
Sender buffer and sender window • We have flow control if the sender’s window is less than or equal to the receiver’s window. Why ? • In the example below, the sender can’t send 7 because 3 were already sent - the Rx hasn’t acknowledged these 3 yet • Therefore, the Tx can only send 4 more and not overload the Rx Sender Window size Dr. Clincy Lecture 47
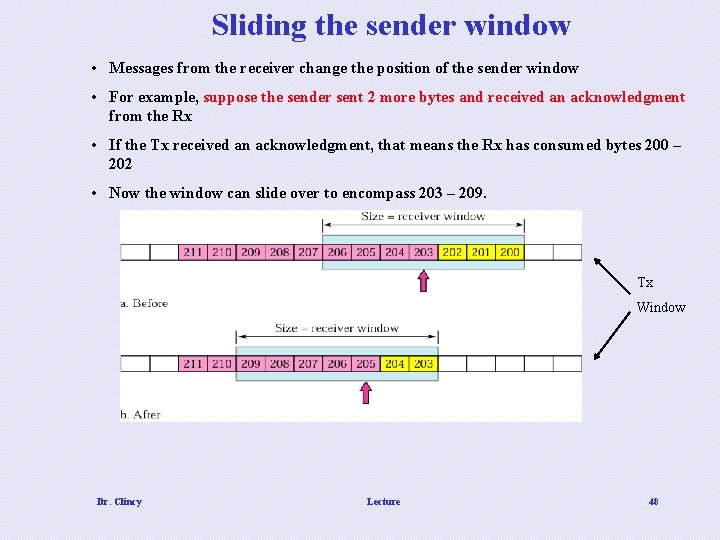
Sliding the sender window • Messages from the receiver change the position of the sender window • For example, suppose the sender sent 2 more bytes and received an acknowledgment from the Rx • If the Tx received an acknowledgment, that means the Rx has consumed bytes 200 – 202 • Now the window can slide over to encompass 203 – 209. Tx Window Dr. Clincy Lecture 48
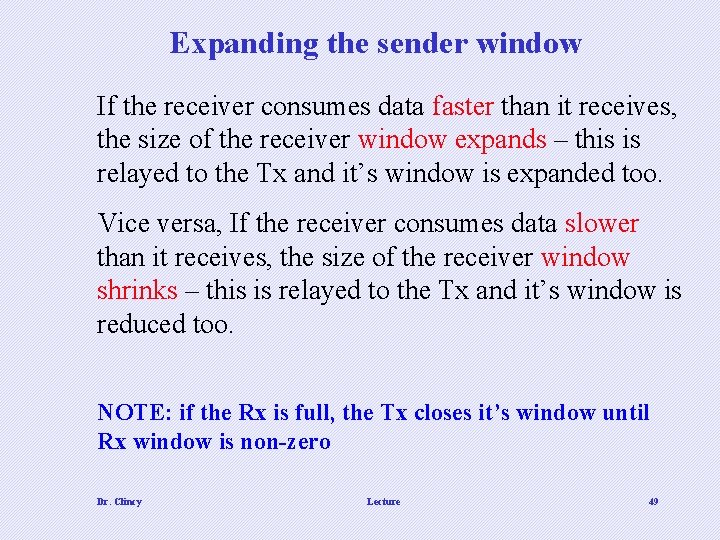
Expanding the sender window If the receiver consumes data faster than it receives, the size of the receiver window expands – this is relayed to the Tx and it’s window is expanded too. Vice versa, If the receiver consumes data slower than it receives, the size of the receiver window shrinks – this is relayed to the Tx and it’s window is reduced too. NOTE: if the Rx is full, the Tx closes it’s window until Rx window is non-zero Dr. Clincy Lecture 49
In TCP, the sender window size is totally controlled by the receiver window value. However, the sender’s actual window size can be smaller if there is congestion in the network. Dr. Clincy Lecture 50
SILLY WINDOW SYNDROME • If the Tx application created data slowly, data would be sent in smaller segments – not enough data to create larger segments • If the Rx application consumed data slowly, the data would be sent in smaller segments in not overloading the Rx. • In either case, network capacity efficiency would be reduced – poor use of network capacity • This is called “Silly Window Syndrome” – why is it “silly” ? ? Dr. Clincy Lecture 51
Explain the Following How Transport-level flow control works with Data Link-level flow control Dr. Clincy Lecture 52
ERROR CONTROL • TCP provides reliability using error control • TCP can detect corrupted segments, lost segments, out-of-order segments and duplicated segments • TCP also has a mechanism in correcting detected errors Error Detection • Error Detection is achieved through 3 tools: (1) checksum, (2) acknowledgment and (3) time-out • Checksum – checksum is used to determine if a segment is corrupted (recall) – if segment is corrupted, it’s dropped • Acknowledgement – acknowledgement is sent by the Rx when the segment is received • If no acknowledgement is received by the Tx before the time-out timer counts down, then it’s assumed the segment is corrupted or lost Error Correction • Re-transmit if error is detected Dr. Clincy Lecture 53
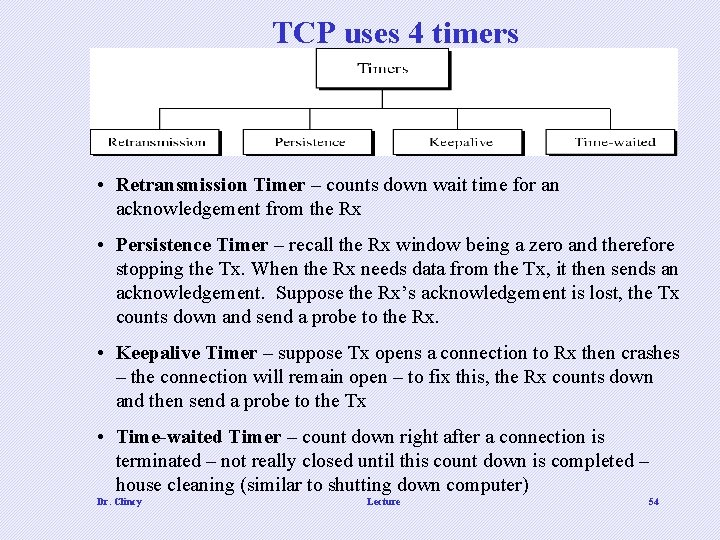
TCP uses 4 timers • Retransmission Timer – counts down wait time for an acknowledgement from the Rx • Persistence Timer – recall the Rx window being a zero and therefore stopping the Tx. When the Rx needs data from the Tx, it then sends an acknowledgement. Suppose the Rx’s acknowledgement is lost, the Tx counts down and send a probe to the Rx. • Keepalive Timer – suppose Tx opens a connection to Rx then crashes – the connection will remain open – to fix this, the Rx counts down and then send a probe to the Tx • Time-waited Timer – count down right after a connection is terminated – not really closed until this count down is completed – house cleaning (similar to shutting down computer) Dr. Clincy Lecture 54
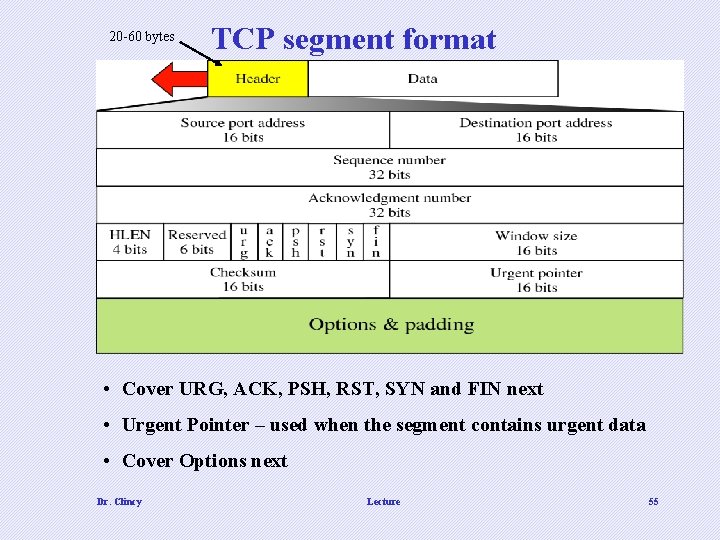
20 -60 bytes TCP segment format • Cover URG, ACK, PSH, RST, SYN and FIN next • Urgent Pointer – used when the segment contains urgent data • Cover Options next Dr. Clincy Lecture 55
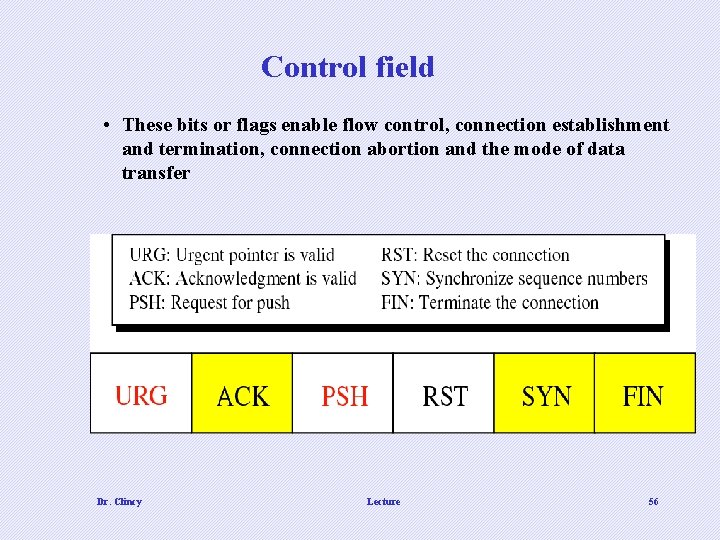
Control field • These bits or flags enable flow control, connection establishment and termination, connection abortion and the mode of data transfer Dr. Clincy Lecture 56
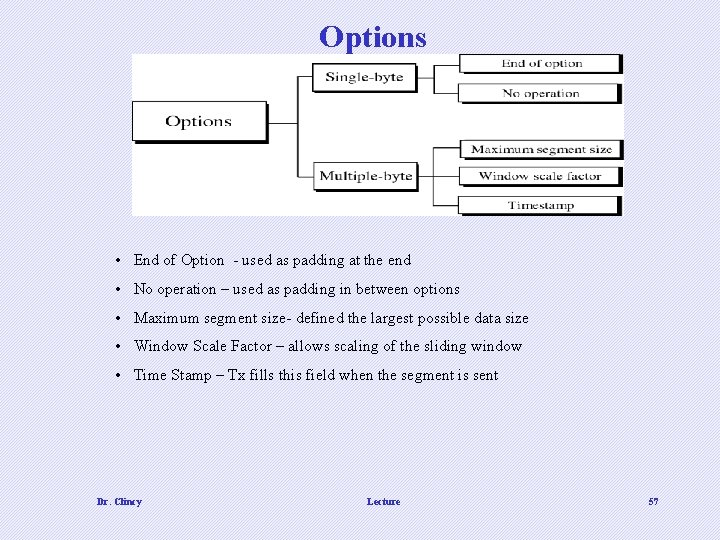
Options • End of Option - used as padding at the end • No operation – used as padding in between options • Maximum segment size- defined the largest possible data size • Window Scale Factor – allows scaling of the sliding window • Time Stamp – Tx fills this field when the segment is sent Dr. Clincy Lecture 57
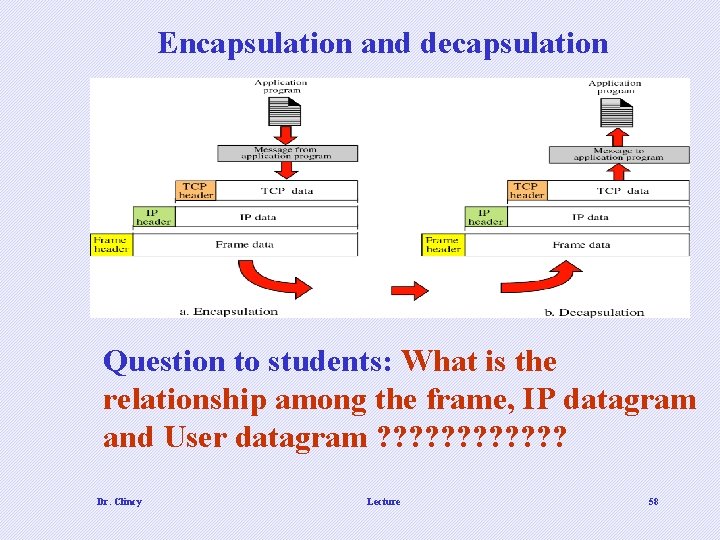
Encapsulation and decapsulation Question to students: What is the relationship among the frame, IP datagram and User datagram ? ? ? Dr. Clincy Lecture 58
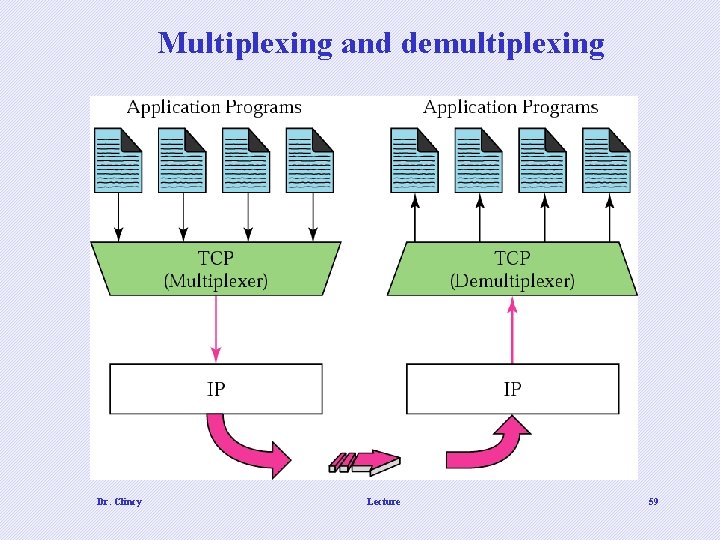
Multiplexing and demultiplexing Dr. Clincy Lecture 59
Also called , IPng – “IP next generation” Next Generation: IPv 6 and ICMPv 6 Recall IPv 4 provides host-to-host or hop-to -hop communication Recall UDP/TCP provide end-to-end or process-to-process communication Dr. Clincy 60
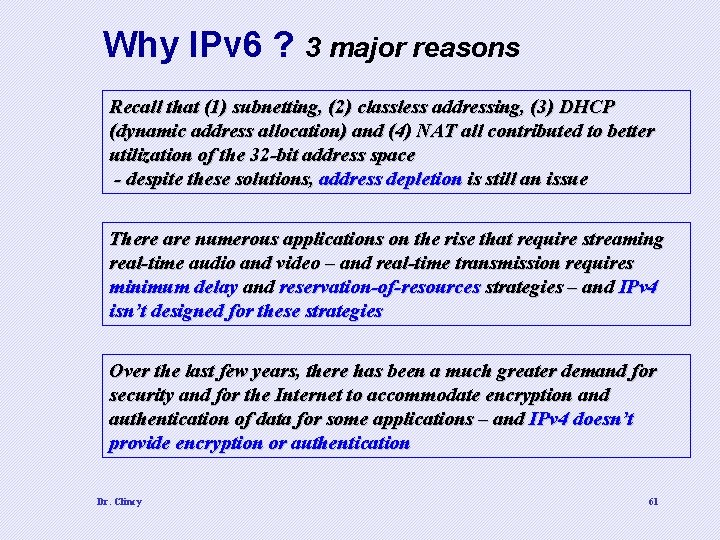
Why IPv 6 ? 3 major reasons Recall that (1) subnetting, (2) classless addressing, (3) DHCP (dynamic address allocation) and (4) NAT all contributed to better utilization of the 32 -bit address space - despite these solutions, address depletion is still an issue There are numerous applications on the rise that require streaming real-time audio and video – and real-time transmission requires minimum delay and reservation-of-resources strategies – and IPv 4 isn’t designed for these strategies Over the last few years, there has been a much greater demand for security and for the Internet to accommodate encryption and authentication of data for some applications – and IPv 4 doesn’t provide encryption or authentication Dr. Clincy 61
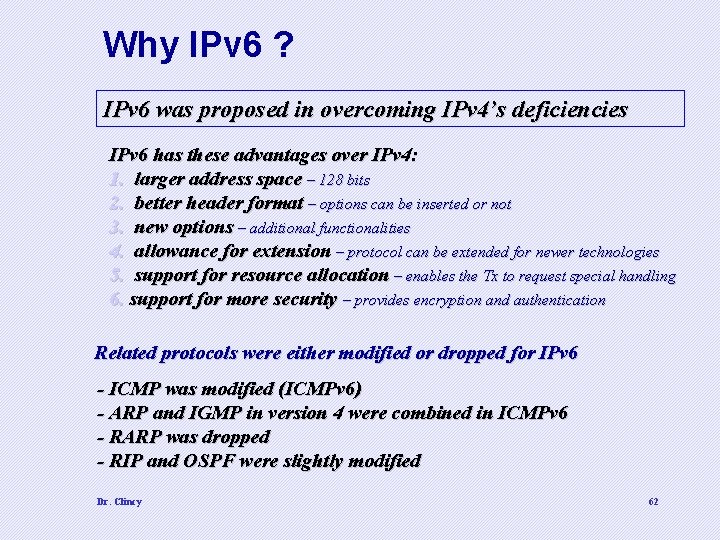
Why IPv 6 ? IPv 6 was proposed in overcoming IPv 4’s deficiencies IPv 6 has these advantages over IPv 4: 1. larger address space – 128 bits 2. better header format – options can be inserted or not 3. new options – additional functionalities 4. allowance for extension – protocol can be extended for newer technologies 5. support for resource allocation – enables the Tx to request special handling 6. support for more security – provides encryption and authentication Related protocols were either modified or dropped for IPv 6 - ICMP was modified (ICMPv 6) - ARP and IGMP in version 4 were combined in ICMPv 6 - RARP was dropped - RIP and OSPF were slightly modified Dr. Clincy 62
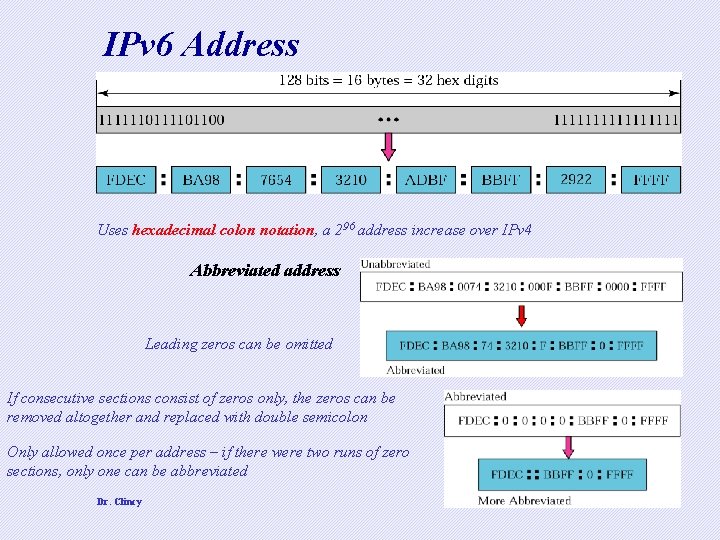
IPv 6 Address Uses hexadecimal colon notation, a 296 address increase over IPv 4 Abbreviated address Leading zeros can be omitted If consecutive sections consist of zeros only, the zeros can be removed altogether and replaced with double semicolon Only allowed once per address – if there were two runs of zero sections, only one can be abbreviated Dr. Clincy 63
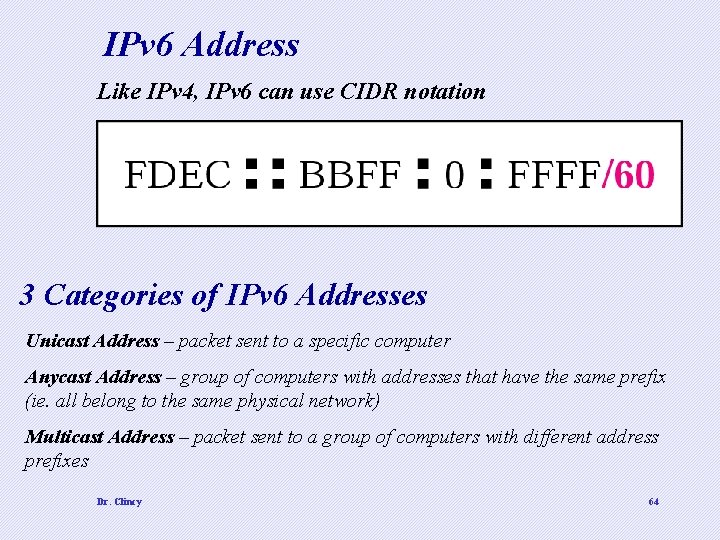
IPv 6 Address Like IPv 4, IPv 6 can use CIDR notation 3 Categories of IPv 6 Addresses Unicast Address – packet sent to a specific computer Anycast Address – group of computers with addresses that have the same prefix (ie. all belong to the same physical network) Multicast Address – packet sent to a group of computers with different address prefixes Dr. Clincy 64
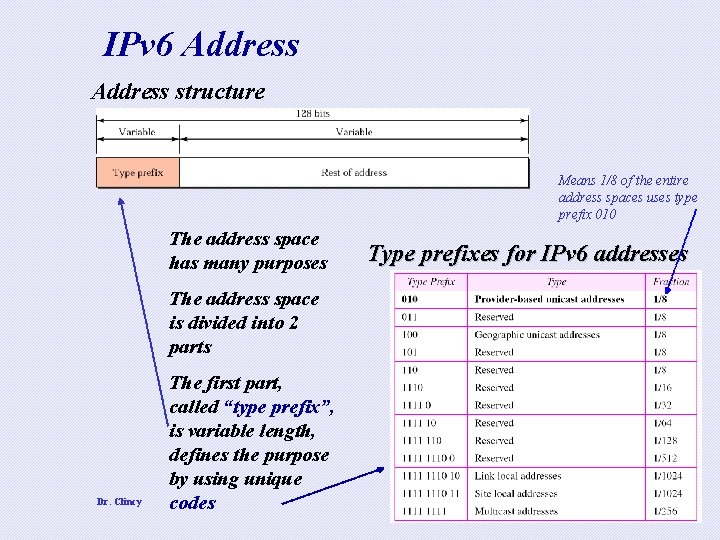
IPv 6 Address structure Means 1/8 of the entire address spaces uses type prefix 010 The address space has many purposes Type prefixes for IPv 6 addresses The address space is divided into 2 parts Dr. Clincy The first part, called “type prefix”, is variable length, defines the purpose by using unique codes 65
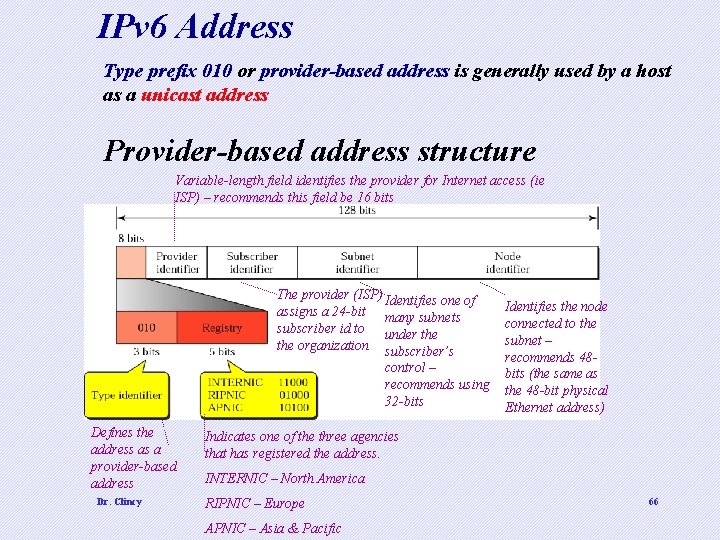
IPv 6 Address Type prefix 010 or provider-based address is generally used by a host as a unicast address Provider-based address structure Variable-length field identifies the provider for Internet access (ie ISP) – recommends this field be 16 bits The provider (ISP) Identifies one of assigns a 24 -bit many subnets subscriber id to under the organization subscriber’s control – recommends using 32 -bits Defines the address as a provider-based address Dr. Clincy Identifies the node connected to the subnet – recommends 48 bits (the same as the 48 -bit physical Ethernet address) Indicates one of the three agencies that has registered the address. INTERNIC – North America RIPNIC – Europe APNIC – Asia & Pacific 66
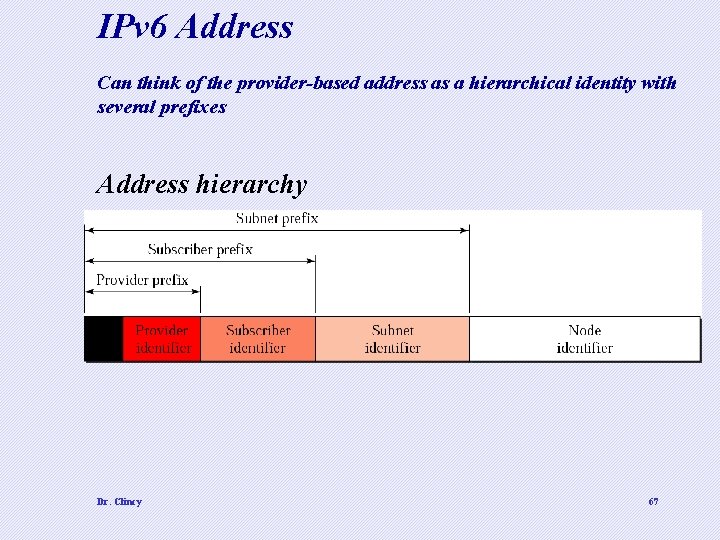
IPv 6 Address Can think of the provider-based address as a hierarchical identity with several prefixes Address hierarchy Dr. Clincy 67
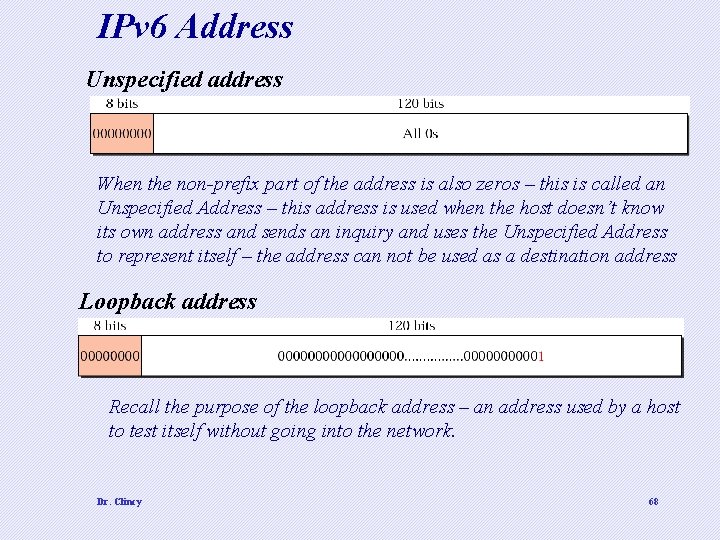
IPv 6 Address Unspecified address When the non-prefix part of the address is also zeros – this is called an Unspecified Address – this address is used when the host doesn’t know its own address and sends an inquiry and uses the Unspecified Address to represent itself – the address can not be used as a destination address Loopback address Recall the purpose of the loopback address – an address used by a host to test itself without going into the network. Dr. Clincy 68
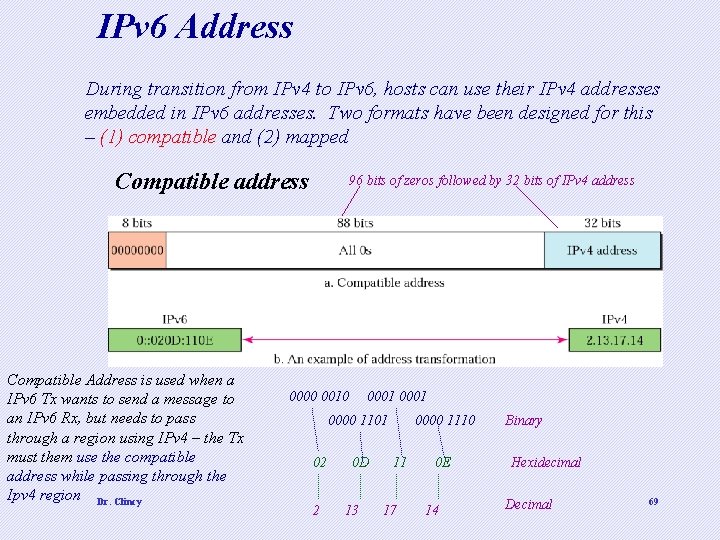
IPv 6 Address During transition from IPv 4 to IPv 6, hosts can use their IPv 4 addresses embedded in IPv 6 addresses. Two formats have been designed for this – (1) compatible and (2) mapped Compatible address Compatible Address is used when a IPv 6 Tx wants to send a message to an IPv 6 Rx, but needs to pass through a region using IPv 4 – the Tx must them use the compatible address while passing through the Ipv 4 region Dr. Clincy 96 bits of zeros followed by 32 bits of IPv 4 address 0000 0010 0001 0000 1101 02 2 0 D 13 0000 1110 11 17 0 E 14 Binary Hexidecimal Decimal 69
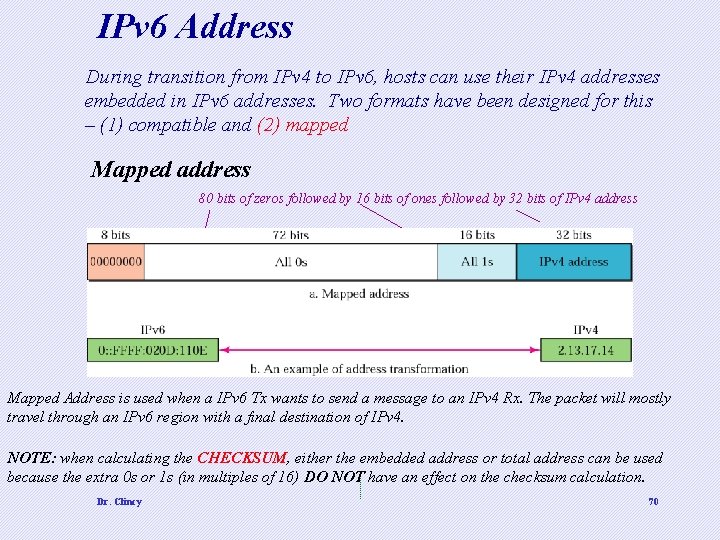
IPv 6 Address During transition from IPv 4 to IPv 6, hosts can use their IPv 4 addresses embedded in IPv 6 addresses. Two formats have been designed for this – (1) compatible and (2) mapped Mapped address 80 bits of zeros followed by 16 bits of ones followed by 32 bits of IPv 4 address Mapped Address is used when a IPv 6 Tx wants to send a message to an IPv 4 Rx. The packet will mostly travel through an IPv 6 region with a final destination of IPv 4. NOTE: when calculating the CHECKSUM, either the embedded address or total address can be used because the extra 0 s or 1 s (in multiples of 16) DO NOT have an effect on the checksum calculation. Dr. Clincy 70
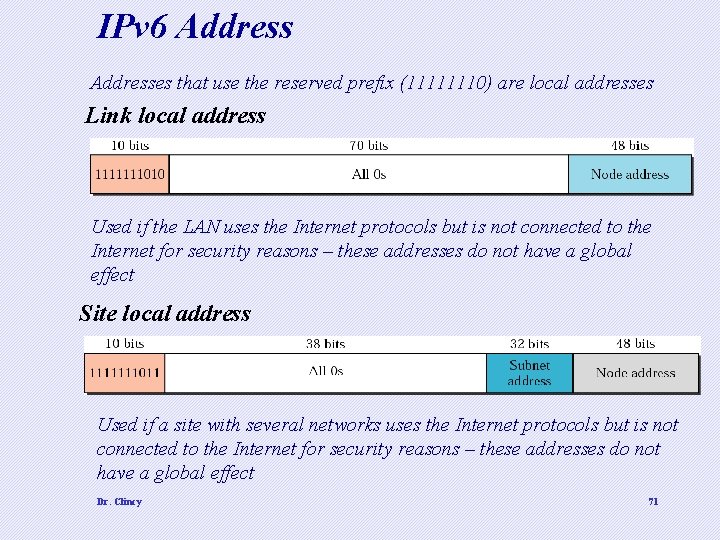
IPv 6 Addresses that use the reserved prefix (11111110) are local addresses Link local address Used if the LAN uses the Internet protocols but is not connected to the Internet for security reasons – these addresses do not have a global effect Site local address Used if a site with several networks uses the Internet protocols but is not connected to the Internet for security reasons – these addresses do not have a global effect Dr. Clincy 71
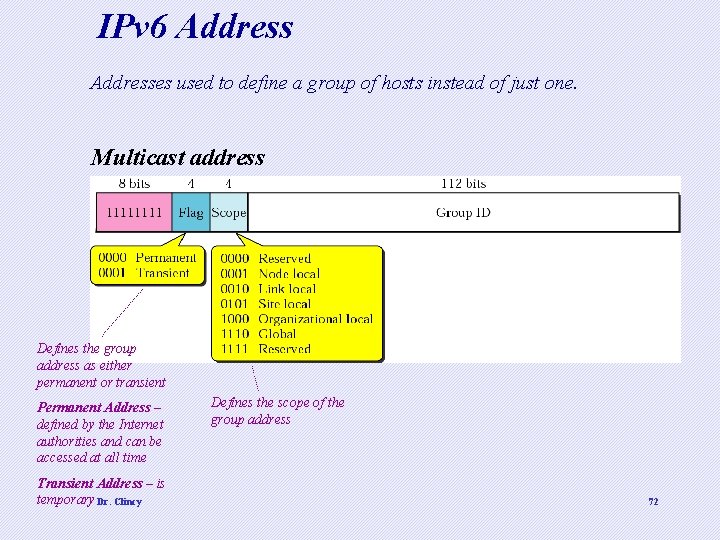
IPv 6 Addresses used to define a group of hosts instead of just one. Multicast address Defines the group address as either permanent or transient Permanent Address – defined by the Internet authorities and can be accessed at all time Transient Address – is temporary Dr. Clincy Defines the scope of the group address 72
Next Generation: IPv 6 and ICMPv 6. . Continuing … Dr. Clincy 73
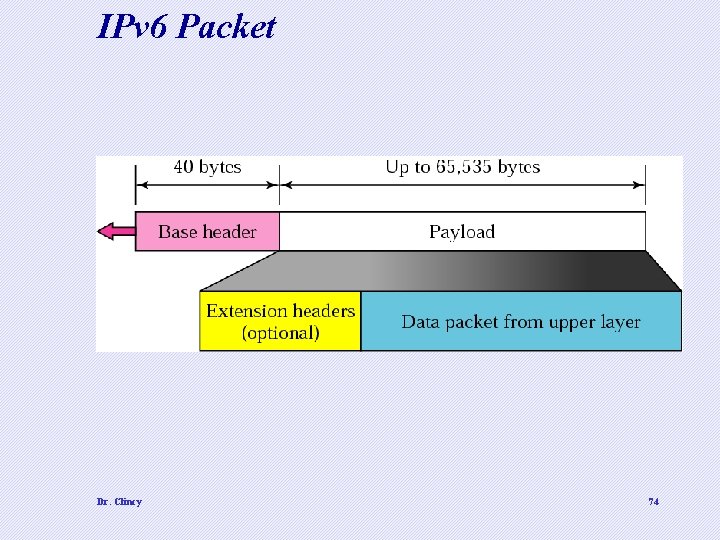
IPv 6 Packet Dr. Clincy 74
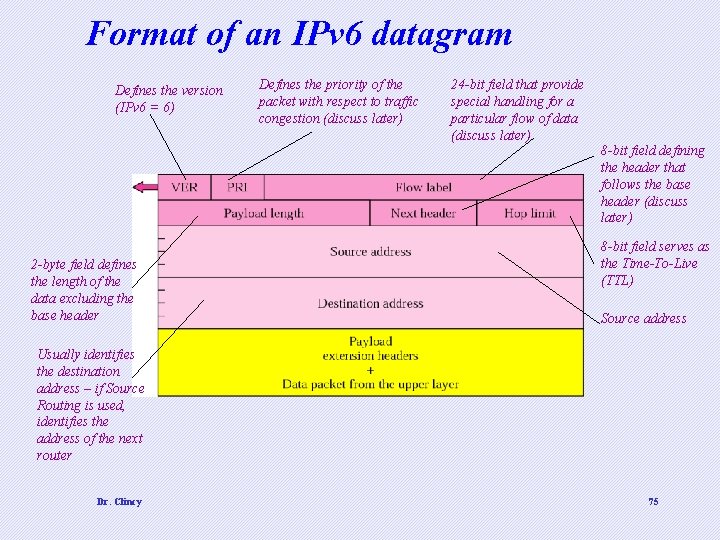
Format of an IPv 6 datagram Defines the version (IPv 6 = 6) Defines the priority of the packet with respect to traffic congestion (discuss later) 24 -bit field that provide special handling for a particular flow of data (discuss later) 8 -bit field defining the header that follows the base header (discuss later) 2 -byte field defines the length of the data excluding the base header 8 -bit field serves as the Time-To-Live (TTL) Source address Usually identifies the destination address – if Source Routing is used, identifies the address of the next router Dr. Clincy 75
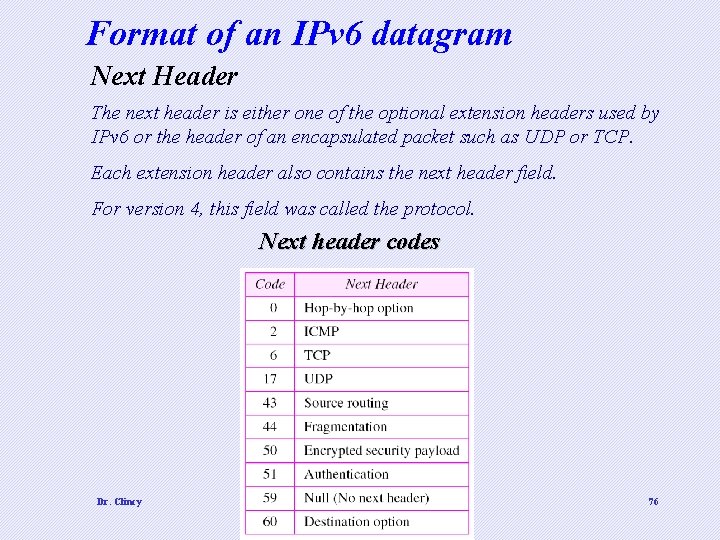
Format of an IPv 6 datagram Next Header The next header is either one of the optional extension headers used by IPv 6 or the header of an encapsulated packet such as UDP or TCP. Each extension header also contains the next header field. For version 4, this field was called the protocol. Next header codes Dr. Clincy 76
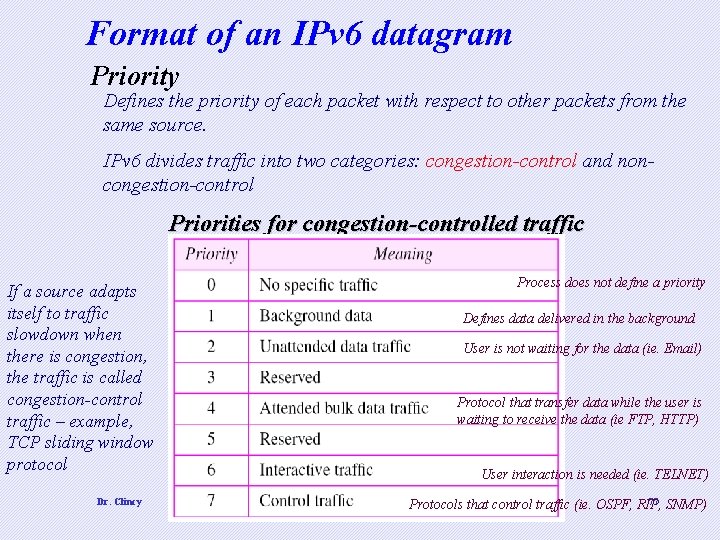
Format of an IPv 6 datagram Priority Defines the priority of each packet with respect to other packets from the same source. IPv 6 divides traffic into two categories: congestion-control and noncongestion-control Priorities for congestion-controlled traffic If a source adapts itself to traffic slowdown when there is congestion, the traffic is called congestion-control traffic – example, TCP sliding window protocol Dr. Clincy Process does not define a priority Defines data delivered in the background User is not waiting for the data (ie. Email) Protocol that transfer data while the user is waiting to receive the data (ie FTP, HTTP) User interaction is needed (ie. TELNET) 77 SNMP) Protocols that control traffic (ie. OSPF, RIP,
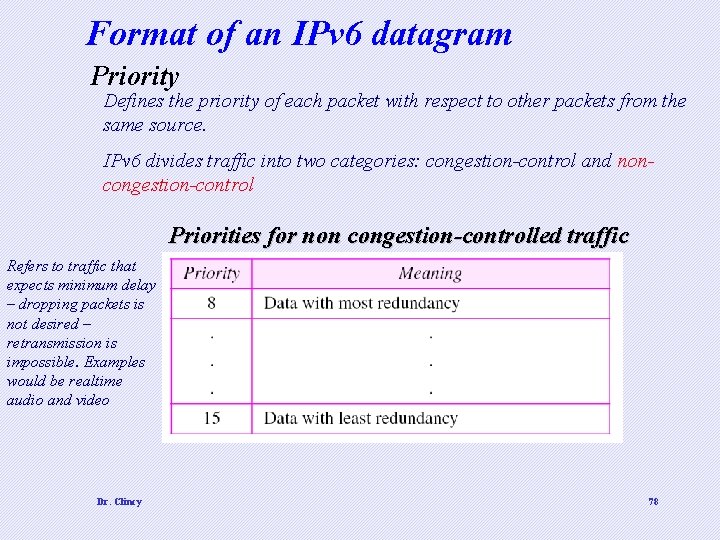
Format of an IPv 6 datagram Priority Defines the priority of each packet with respect to other packets from the same source. IPv 6 divides traffic into two categories: congestion-control and noncongestion-control Priorities for non congestion-controlled traffic Refers to traffic that expects minimum delay – dropping packets is not desired – retransmission is impossible. Examples would be realtime audio and video Dr. Clincy 78
IPv 6 Packet Flow Label • Recall how a routing-algorithm table lookup is performed for a packet using a router. • Sequence of packets sent from a Tx to Rx needing “special handling” is called a flow • Combo of the Tx address and a flow label uniquely identifies a flow of packets • The flow label is assigned to the packet by the Tx – randomly generated number • From a router perspective, a flow is a sequence of packets sharing the characteristics (using same resources, same security, , etc) • If the packet has a flow number, the router consults it flow label table for the next hop • This speeds up the process – much faster than going through the routing algorithm approach • Flow label approach is good for apps needing to reserve bandwidth and buffer space beforehand in minimizing delays (ie. realtime audio and video) Dr. Clincy 79
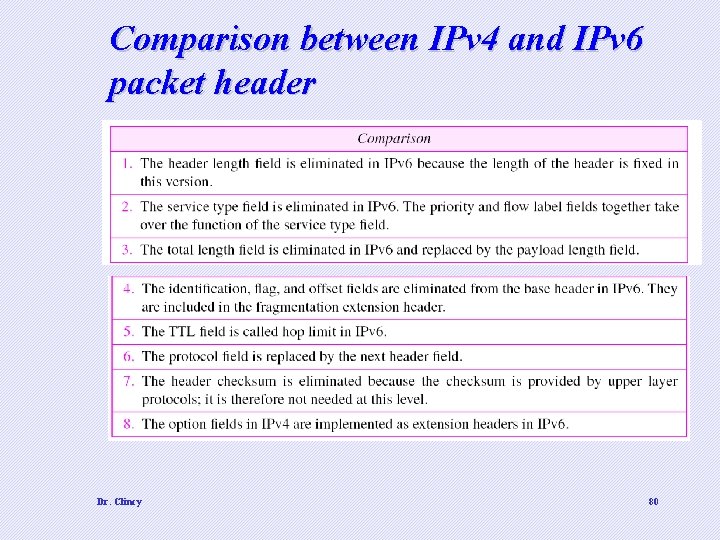
Comparison between IPv 4 and IPv 6 packet header Dr. Clincy 80
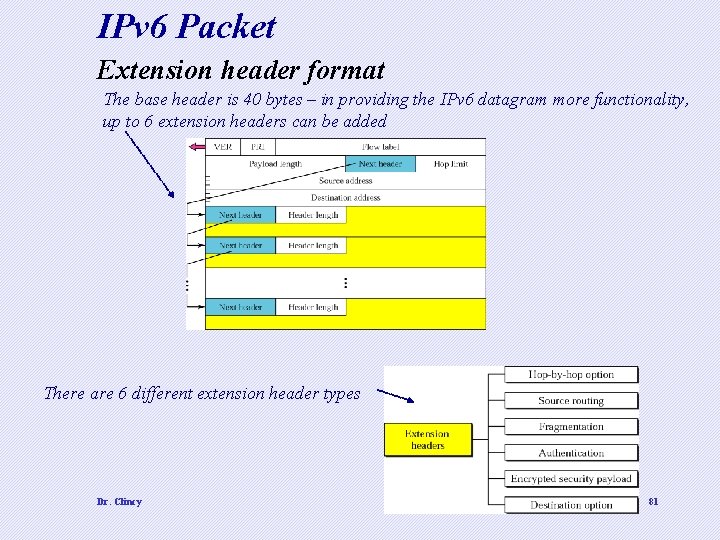
IPv 6 Packet Extension header format The base header is 40 bytes – in providing the IPv 6 datagram more functionality, up to 6 extension headers can be added There are 6 different extension header types Dr. Clincy 81
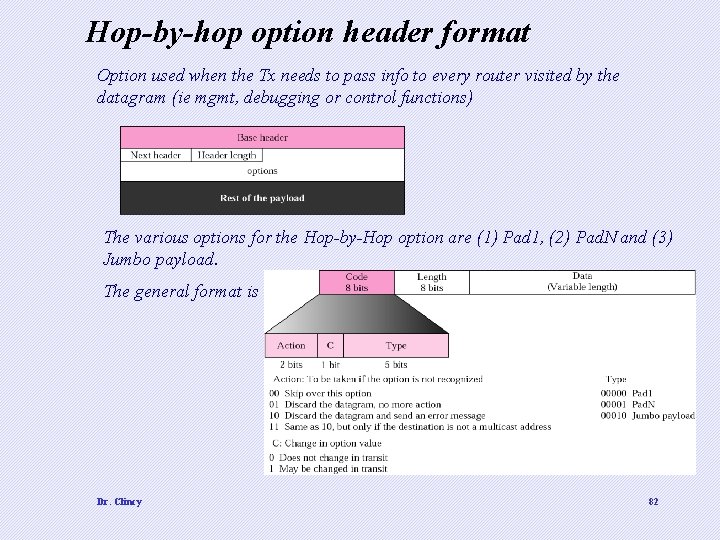
Hop-by-hop option header format Option used when the Tx needs to pass info to every router visited by the datagram (ie mgmt, debugging or control functions) The various options for the Hop-by-Hop option are (1) Pad 1, (2) Pad. N and (3) Jumbo payload. The general format is Dr. Clincy 82
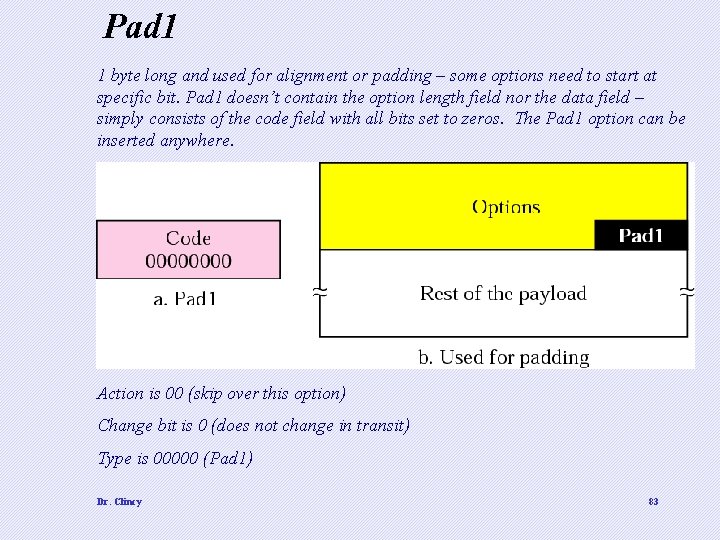
Pad 1 1 byte long and used for alignment or padding – some options need to start at specific bit. Pad 1 doesn’t contain the option length field nor the data field – simply consists of the code field with all bits set to zeros. The Pad 1 option can be inserted anywhere. Action is 00 (skip over this option) Change bit is 0 (does not change in transit) Type is 00000 (Pad 1) Dr. Clincy 83
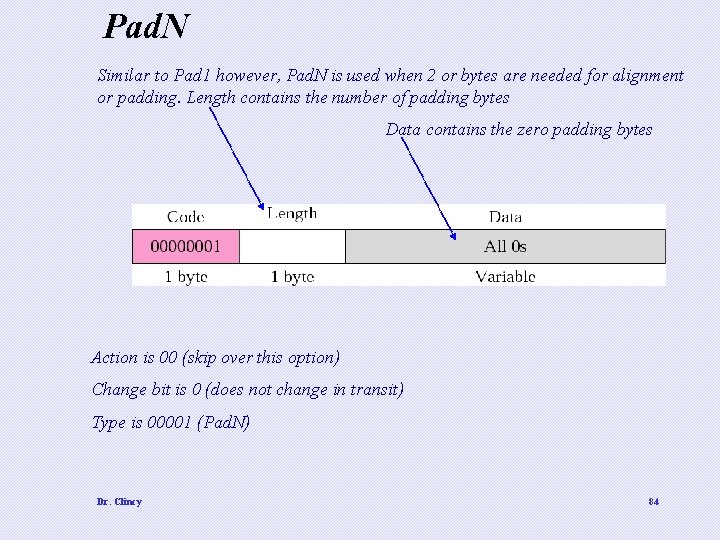
Pad. N Similar to Pad 1 however, Pad. N is used when 2 or bytes are needed for alignment or padding. Length contains the number of padding bytes Data contains the zero padding bytes Action is 00 (skip over this option) Change bit is 0 (does not change in transit) Type is 00001 (Pad. N) Dr. Clincy 84
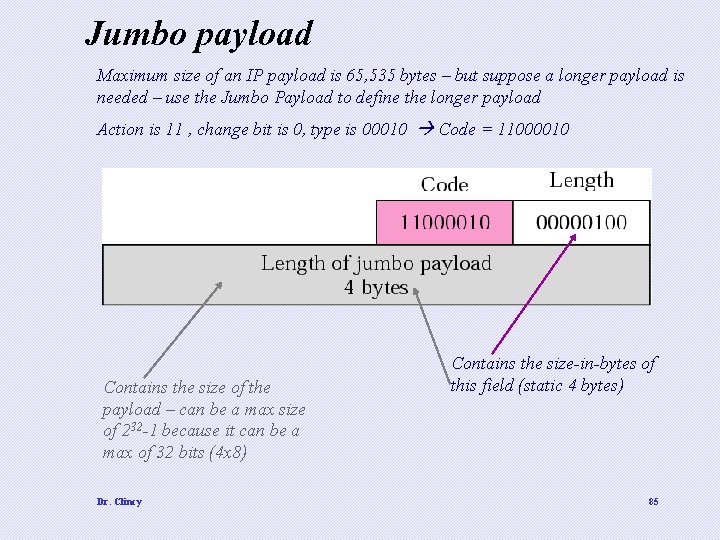
Jumbo payload Maximum size of an IP payload is 65, 535 bytes – but suppose a longer payload is needed – use the Jumbo Payload to define the longer payload Action is 11 , change bit is 0, type is 00010 Code = 11000010 Contains the size of the payload – can be a max size of 232 -1 because it can be a max of 32 bits (4 x 8) Dr. Clincy Contains the size-in-bytes of this field (static 4 bytes) 85
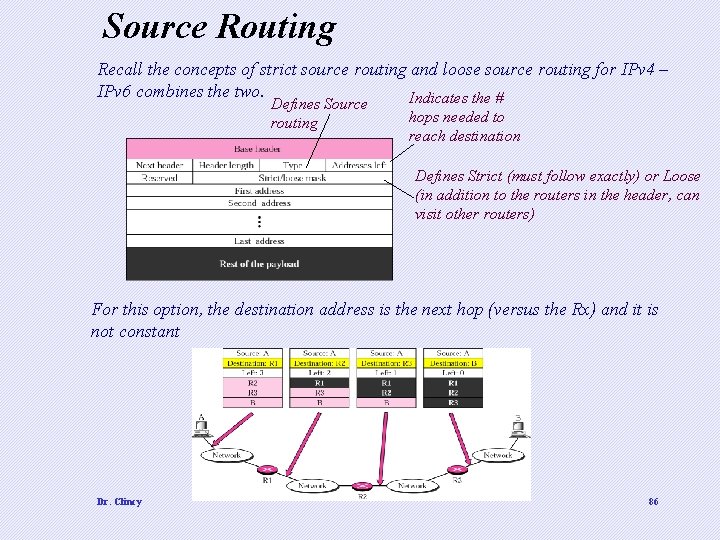
Source Routing Recall the concepts of strict source routing and loose source routing for IPv 4 – IPv 6 combines the two. Indicates the # Defines Source routing hops needed to reach destination Defines Strict (must follow exactly) or Loose (in addition to the routers in the header, can visit other routers) For this option, the destination address is the next hop (versus the Rx) and it is not constant Dr. Clincy 86
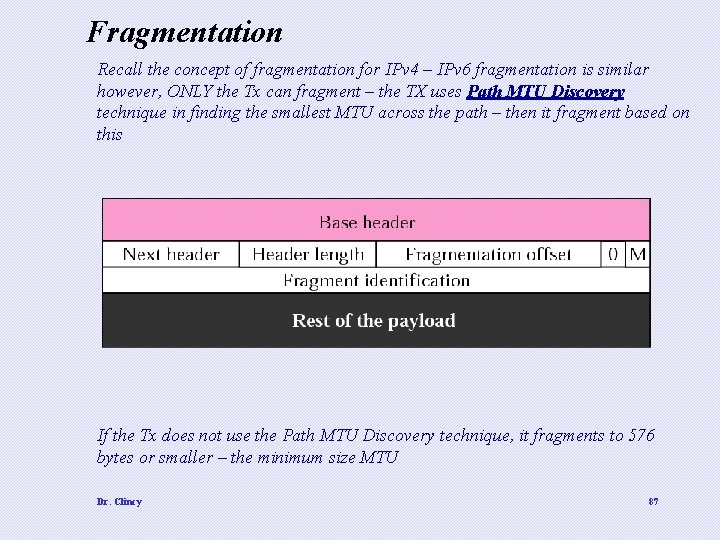
Fragmentation Recall the concept of fragmentation for IPv 4 – IPv 6 fragmentation is similar however, ONLY the Tx can fragment – the TX uses Path MTU Discovery technique in finding the smallest MTU across the path – then it fragment based on this If the Tx does not use the Path MTU Discovery technique, it fragments to 576 bytes or smaller – the minimum size MTU Dr. Clincy 87
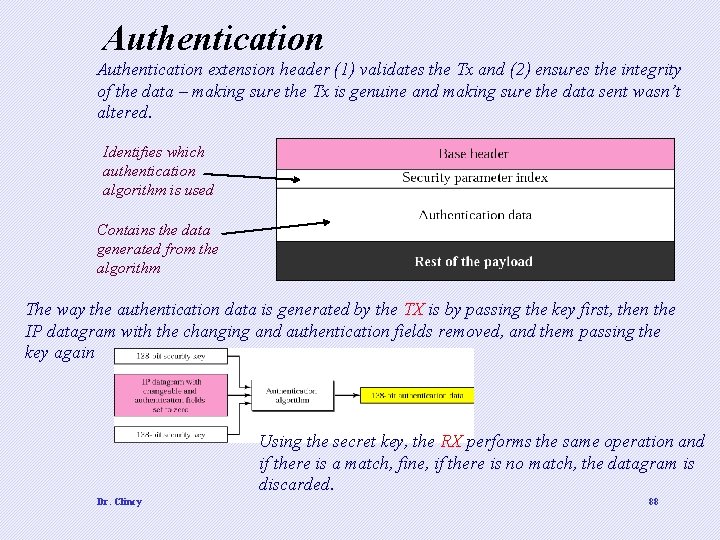
Authentication extension header (1) validates the Tx and (2) ensures the integrity of the data – making sure the Tx is genuine and making sure the data sent wasn’t altered. Identifies which authentication algorithm is used Contains the data generated from the algorithm The way the authentication data is generated by the TX is by passing the key first, then the IP datagram with the changing and authentication fields removed, and them passing the key again Using the secret key, the RX performs the same operation and if there is a match, fine, if there is no match, the datagram is discarded. Dr. Clincy 88
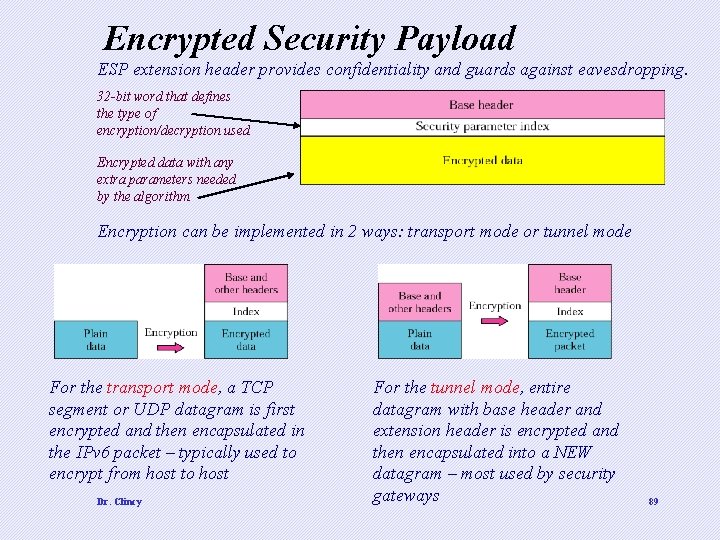
Encrypted Security Payload ESP extension header provides confidentiality and guards against eavesdropping. 32 -bit word that defines the type of encryption/decryption used Encrypted data with any extra parameters needed by the algorithm Encryption can be implemented in 2 ways: transport mode or tunnel mode For the transport mode, a TCP segment or UDP datagram is first encrypted and then encapsulated in the IPv 6 packet – typically used to encrypt from host to host Dr. Clincy For the tunnel mode, entire datagram with base header and extension header is encrypted and then encapsulated into a NEW datagram – most used by security gateways 89
Destination option Option used when the Tx needs to pass info to the Rx only Dr. Clincy 90
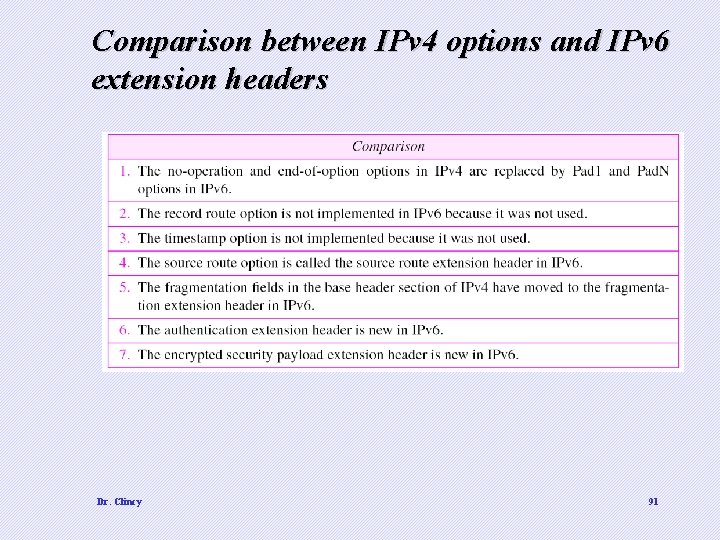
Comparison between IPv 4 options and IPv 6 extension headers Dr. Clincy 91
- Slides: 91