Chapter 11 Physical Database Design Transparencies Chapter 11
Chapter 11 Physical Database Design Transparencies
Chapter 11 - Objectives �Purpose of physical database design. �How to map the logical database design to a physical database design. �How to design base tables for target DBMS. �How to design representation of derived data. �How to design integrity constraints for the target DBMS. �How to analyze the users’ transactions to identify characteristics that may impact on performance. ©Pearson Education 2009 2
Chapter 11 - Objectives �That a database represents an essential corporate resources that must be made secure. �The meaning of denormalization. �About the importance of monitoring and tuning the operational system. �How to measure efficiency. ©Pearson Education 2009 3
Logical vs Physical Database Design �Logical db design independent of implementation details, such as functionality of target DBMS. �Logical db design concerned with the what, physical database design is concerned with the how. �Sources of information for physical design includes logical data model and data dictionary. ©Pearson Education 2009 4
Physical Database Design Process of producing a description of implementation of the database on secondary storage. It describes base tables, file organizations, and indexes used to achieve efficient access to the data, and any associated integrity constraints and security restrictions. ©Pearson Education 2009 5
Overview of Physical Database Design Methodology �Step 3 Translate logical database design for target DBMS �Step 4 Choose file organizations and indexes �Step 5 Design user views �Step 6 Design security mechanisms �Step 7 Consider introduction of controlled redundancy �Step 8 Monitor and tune operational system ©Pearson Education 2009 6
Step 3 Translate logical database design for target DBMS To produce a basic working relational database from the logical data model. �Consists of the following steps: �Step 3. 1 Design base tables �Step 3. 2 Design representation of derived data �Step 3. 3 Design remaining integrity constraints ©Pearson Education 2009 7
Step 3 Translate logical database design for target DBMS �Need to know functionality of target DBMS such as how to create base tables and whether DBMS supports the definition of: �PKs, FKs, and AKs; �required data – i. e. whether system supports NOT NULL; �domains; �relational integrity rules; �other integrity constraints. ©Pearson Education 2009 8
Step 3. 1 Design base tables To decide how to represent base tables identified in logical model in target DBMS. �Need to collate and assimilate the information about tables produced during logical database design (from data dictionary and tables defined in DBDL). ©Pearson Education 2009 9
Step 3. 1 Design base tables �For each table, need to define: �name of the table; �list of simple columns in brackets; �PK and, where appropriate, AKs and FKs. �referential integrity constraints for any FKs identified. �For each column, need to define: �its domain, consisting of a data type, length, and any constraints on the domain; �optional default value for the column; �whether column can hold nulls; �whether column is derived. ©Pearson Education 2009 10
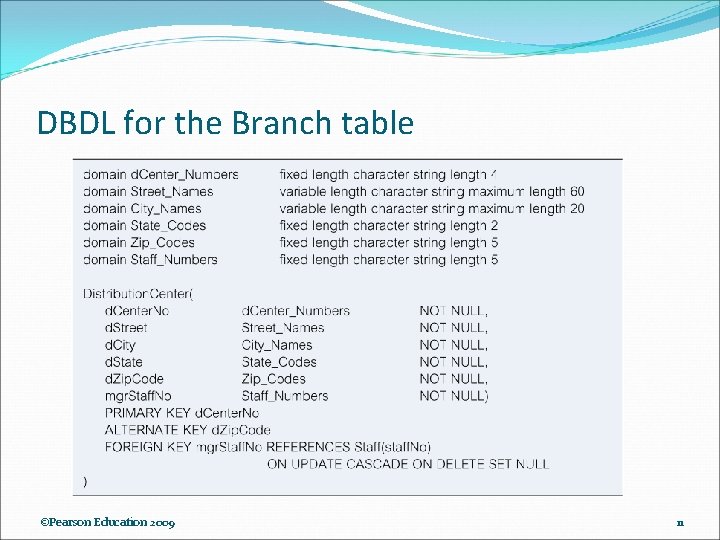
DBDL for the Branch table ©Pearson Education 2009 11
Step 3. 2 Design representation of derived data To design the representation of derived data in the database. �Produce list of all derived columns from logical data model and data dictionary. �Derived column can be stored in database or calculated every time it is needed. ©Pearson Education 2009 12
Step 3. 2 Design representation of derived data �Option selected is based on: �additional cost to store the derived data and keep it consistent with data from which it is derived; �cost to calculate it each time it’s required. �Less expensive option is chosen subject to performance constraints. ©Pearson Education 2009 13
Step 3. 3 Design remaining integrity constraints To design the remaining integrity constraints for the target DBMS. �Some DBMS provide more facilities than others for defining integrity constraints. Example: CONSTRAINT member_not_renting_too_many CHECK (NOT EXISTS (SELECT member. No FROM Rental. Delivery r. DVDRental d WHERE r. delivery. No=d. delivery. No AND date. Return IS NULL GROUP BY member. No HAVING COUNT(*) > 5)) ©Pearson Education 2009 14
Step 4 Choose file organizations/indexes Determine optimal file organizations to store the base tables, and the indexes required to achieve acceptable performance. n Consists of the following steps: n n n Step 4. 1 Analyze transactions Step 4. 2 Choose file organizations Step 4. 3 Choose indexes Chapter Name 15
Step 4. 1 Analyze transactions To analyze the functionality of the transactions that will run on the database to identify those that may impact performance. n Identify performance criteria, such as: n n n transactions that run frequently and will have a significant impact on performance; transactions that are critical to the business; Name times during the Chapter day/week when there will 16
Step 4. 1 Analyze transactions n n Use this information to identify the parts of the database that may cause performance problems. To select appropriate file organizations and indexes, also need to know highlevel functionality of the transactions, such as: n n columns that are updated in an update transaction; criteria used to Chapter restrict records that are Name 17
Step 4. 1 Analyze transactions n To focus on areas that may be problematic: (1) Map all transaction paths to tables. (2) Determine which tables are most frequently accessed by transactions. (3) Analyze the data usage of selected transactions that involve these tables. Chapter Name 18
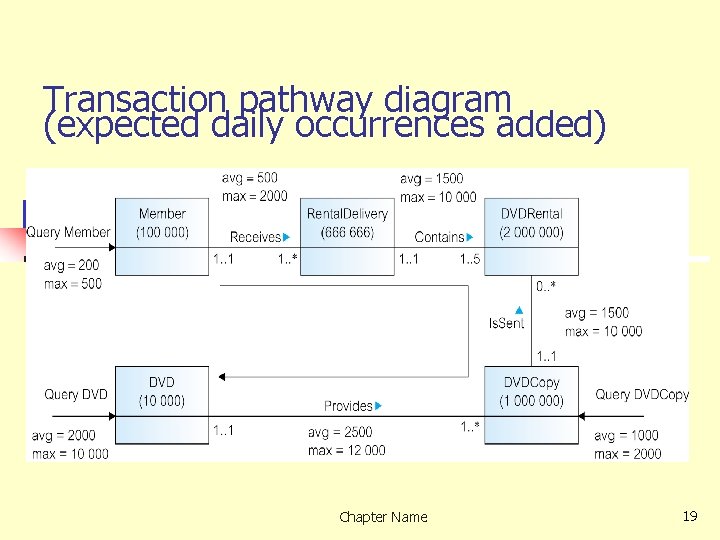
Transaction pathway diagram (expected daily occurrences added) Chapter Name 19
Step 4. 1 Analyze transactions n For each transaction determine: (a) Tables and columns accessed and type of access. (b) Columns used in any search conditions. (c) For query, columns involved in joins. (d) Expected frequency of transaction. (e) Performance goals of transaction. Chapter Name 20
Step 4. 2 Choose file organizations To determine an efficient file organization for each base table. n n File organizations include Heap, Hash, Indexed Sequential Access Method (ISAM), B+-Tree, and Clusters. Some DBMSs (particularly PC-based DBMS) have fixed file organization that you cannot alter. Chapter Name 21
Step 4. 3 Choose indexes Determine whether adding indexes will improve the performance of the system. n n n One approach is to keep records unordered and create as many secondary indexes as necessary. Have to balance overhead in maintenance and use of secondary indexes against performance improvement gained when retrieving data. This includes: n n adding an index record to every secondary index whenever record is inserted; updating a secondary index when corresponding record is updated; increase in disk space needed to store the secondary index; possible performance degradation during query optimization to consider all secondary indexes. Chapter Name 22
Step 4. 3 Choose indexes – Guidelines for choosing ‘wish-list’ (1) Do not index small tables. (2) Index PK of a table if it is not a key of the file organization. (3) Add secondary index to any column that is heavily used as a secondary key. (4) Add secondary index to a FK if it is frequently accessed. (5) Add secondary index on columns that are involved in: selection or join criteria; ORDER BY; GROUP BY; and other operations involving sorting (such as UNION or DISTINCT). Chapter Name 23
Step 4. 3 Choose indexes – Guidelines for choosing ‘wish-list’ (6) Add secondary index on columns involved in builtin functions. (7) Add secondary index on columns that could result in an index-only plan. (8) Avoid indexing an column or table that is frequently updated. (9) Avoid indexing an column if the query will retrieve a significant proportion of the records in the table. (10) Avoid indexing columns that consist of long character strings. Chapter Name 24
Step 5 Design User Views Design user views identified during Requirements Collection and Analysis stage of the database system development lifecycle. n Normally views created using SQL or a QBE-like facility. For example: CREATE VIEW Staff 1 View AS SELECT staff. No, name, position, e. Mail FROM Staff WHERE d. Center. No = ‘D 001’; Chapter Name 25
Step 6 Design Security Measures Design security measures for the database as specified by the users. n RDBMSs generally provide two types of database security: n n system security: access and use of database at system level (such as username/password); data security: access and use of database objects (such as tables and views). Chapter Name 26
Step 6 Design Security Measures - SQL n n Each database user assigned an authorization identifier by DBA (usually has an associated password). Each object created has an owner. Privileges are the actions that a user is permitted to carry out on a given base table or view (such as SELECT, UPDATE). GRANT statement allows owner to give Name privileges to other. Chapter users. 27
Step 7 Consider Introduction of Controlled Redundancy n n n Determine whether introducing redundancy in a controlled manner by relaxing the normalization rules will improve system performance. Normalization results in a logical database design that is structurally consistent and has minimal redundancy. However, sometimes a normalized database design does not provide maximum processing efficiency. May be necessary to accept loss of some of the benefits of a fully normalized design in favor of performance. Chapter Name 28
Denormalization �Refinement to relational schema such that the degree of normalization for a modified table is less than the degree of at least one of the original tables. �Also use term more loosely to refer to situations where two tables are combined into one new table, which is still normalized but contains more nulls than original tables. ©Pearson Education 2009 29
Step 7 Consider Introduction of Controlled Redundancy n Also consider that denormalization: n n n makes implementation more complex; often sacrifices flexibility; may speed up retrievals but it slows down updates. Chapter Name 30
Step 8 Monitor and tune the operational system To monitor operational system and improve performance of system to correct inappropriate design decisions or reflect changing requirements. Chapter Name 31
Step 8 Monitor and tune the operational system n Number of factors that may be used to measure efficiency: - Transaction throughput: number of transactions processed in given time interval. - Response time: elapsed time for completion of a single transaction. - Disk storage: amount of disk space required to store database files. n No one factor is always correct. Typically, have to trade one factor off against 32 Chapter Name
Step 8 Monitor and tune the operational system n Must be aware how 4 main hardware components interact and affect performance: n n n main memory CPU disk I/O network. Note that an improvement in one resource may effect an improvement in 33 other resources. Chapter Name
Step 8 Monitor and tune the operational system n Main memory: n n Significantly faster than secondary storage. More main memory, faster applications will run. Should always have between 5%-10% main memory available. Need to understand how target DBMS uses main memory. Chapter Name 34
Step 8 Monitor and tune the operational system n CPU: n n Controls tasks of other system resources and executes user processes. Most costly resource, so needs to be correctly utilized. Want to prevent CPU contention (processes waiting for CPU). Need to understand typical 24 -hour workload and ensure sufficient resources available for both normal and peak workload. Chapter Name 35
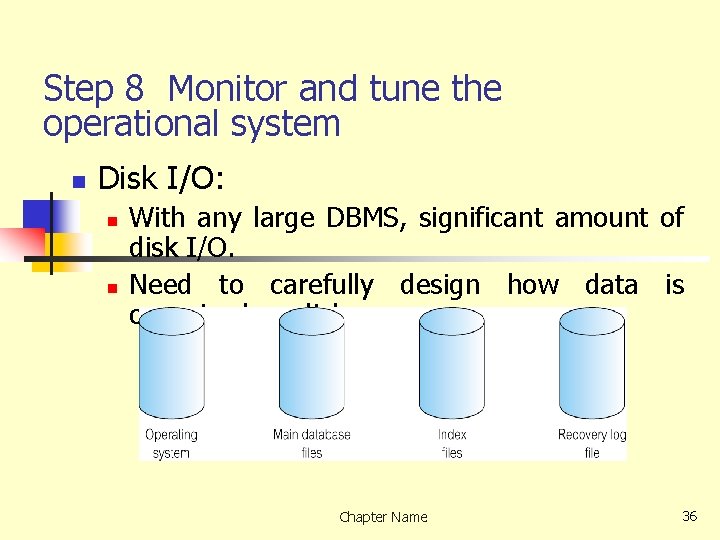
Step 8 Monitor and tune the operational system n Disk I/O: n n With any large DBMS, significant amount of disk I/O. Need to carefully design how data is organized on disk. Chapter Name 36
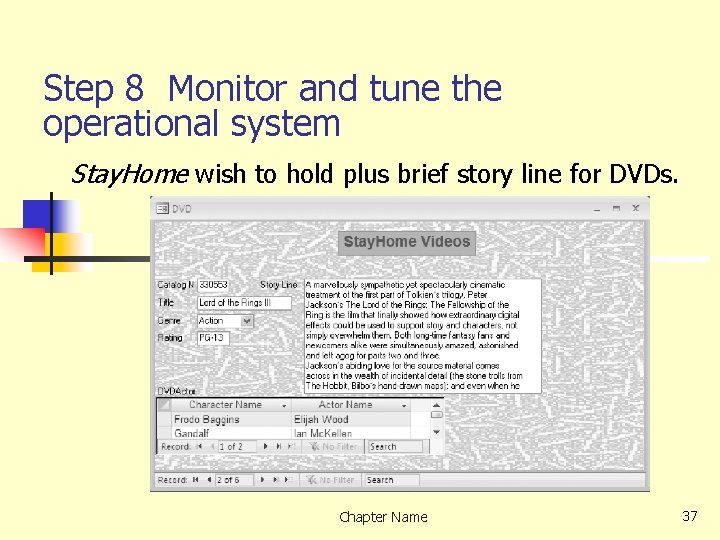
Step 8 Monitor and tune the operational system Stay. Home wish to hold plus brief story line for DVDs. Chapter Name 37
- Slides: 37