Chapter 10 Internet Group Management Protocol Objectives Upon
Chapter 10 Internet Group Management Protocol Objectives Upon completion you will be able to: • Know the purpose of IGMP • Know the types of IGMP messages • Understand how a member joins a group and leaves a group • Understand membership monitoring • Understand how an IGMP message is encapsulated • Understand the interactions of the modules of an IGMP package TCP/IP Protocol Suite 1
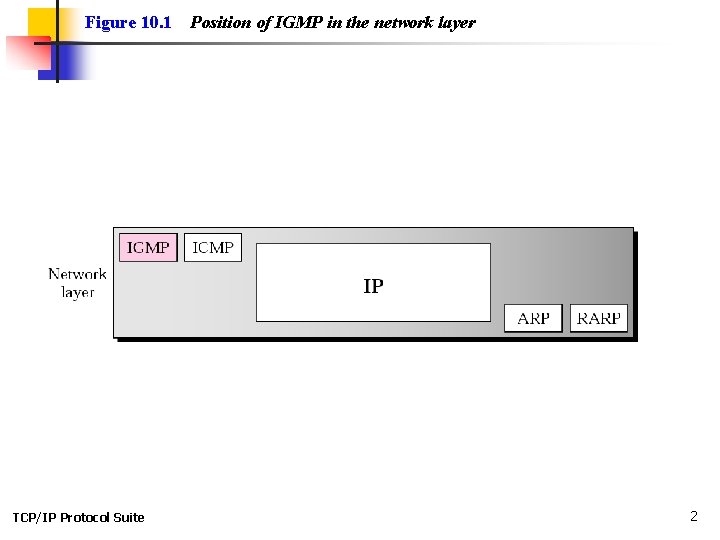
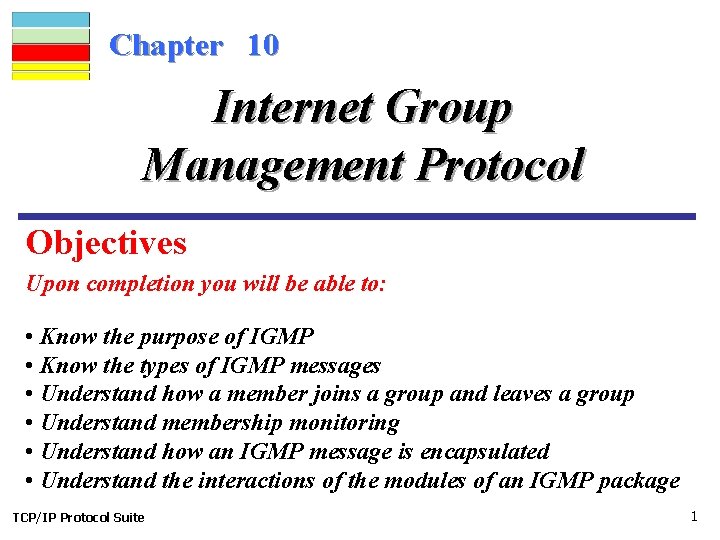
Figure 10. 1 TCP/IP Protocol Suite Position of IGMP in the network layer 2
Unicast Traffic • Unicast applications send one copy of each packet to every client unicast address TCP/IP Protocol Suite 3
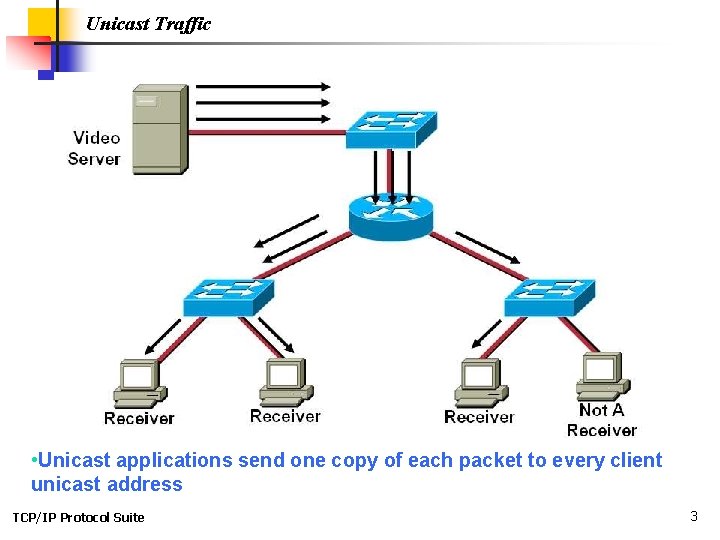
Unicast Traffic TCP/IP Protocol Suite 4
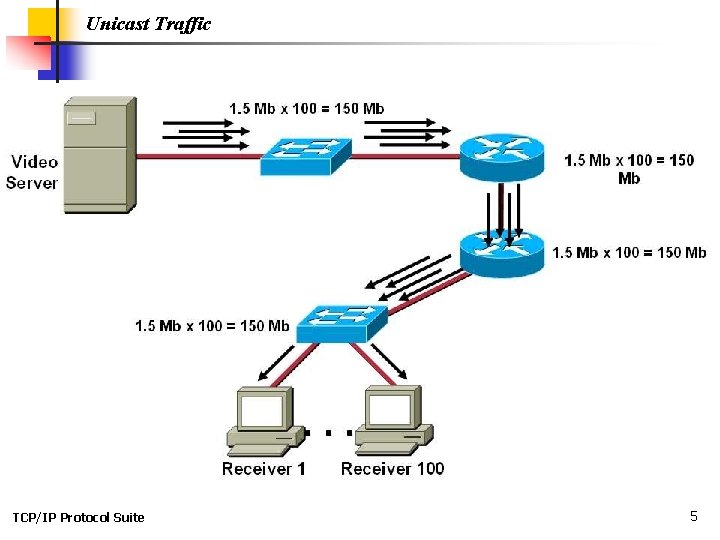
Unicast Traffic TCP/IP Protocol Suite 5
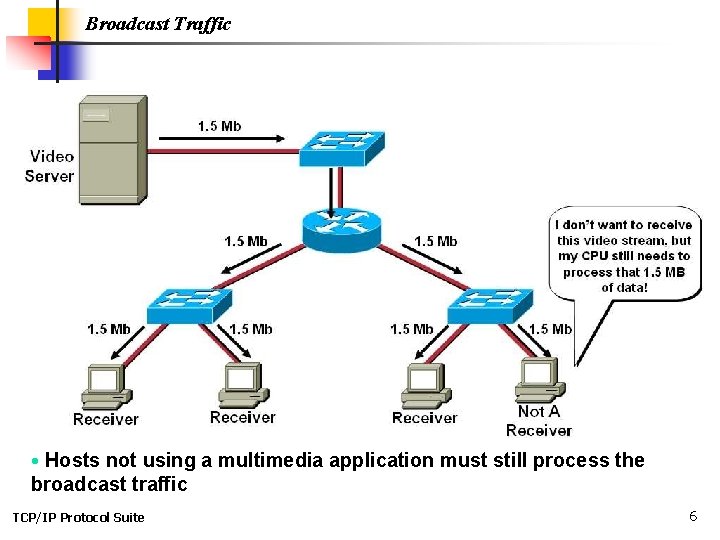
Broadcast Traffic • Hosts not using a multimedia application must still process the broadcast traffic TCP/IP Protocol Suite 6
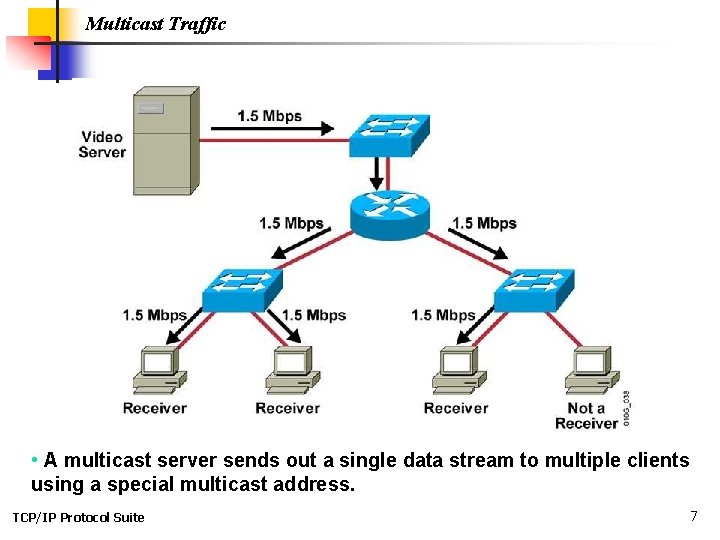
Multicast Traffic • A multicast server sends out a single data stream to multiple clients using a special multicast address. TCP/IP Protocol Suite 7
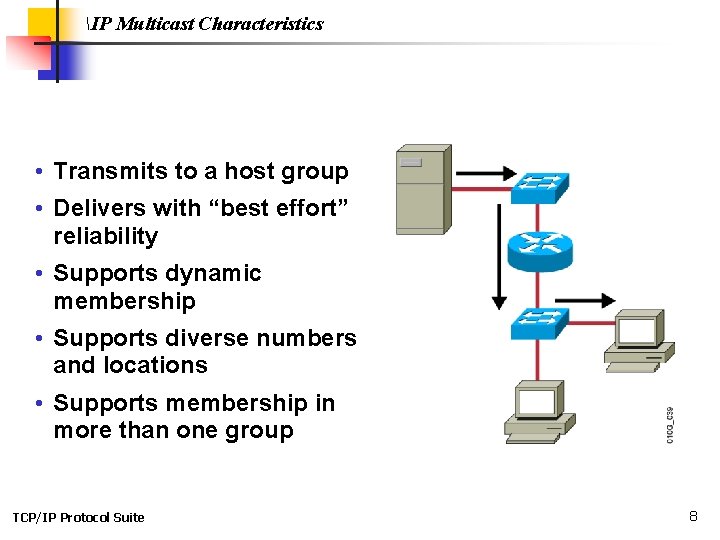
IP Multicast Characteristics • Transmits to a host group • Delivers with “best effort” reliability • Supports dynamic membership • Supports diverse numbers and locations • Supports membership in more than one group TCP/IP Protocol Suite 8
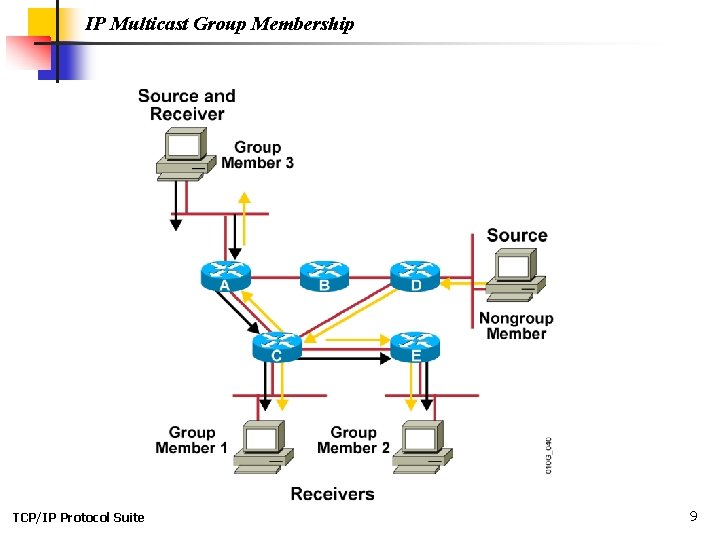
IP Multicast Group Membership TCP/IP Protocol Suite 9
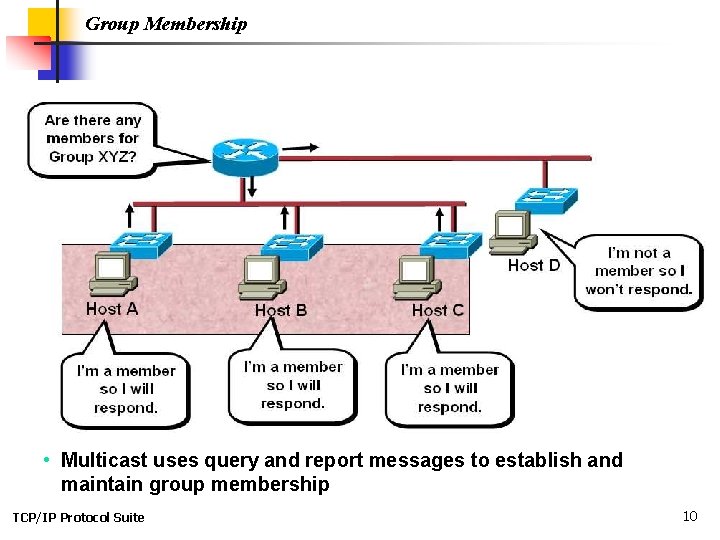
Group Membership • Multicast uses query and report messages to establish and maintain group membership TCP/IP Protocol Suite 10
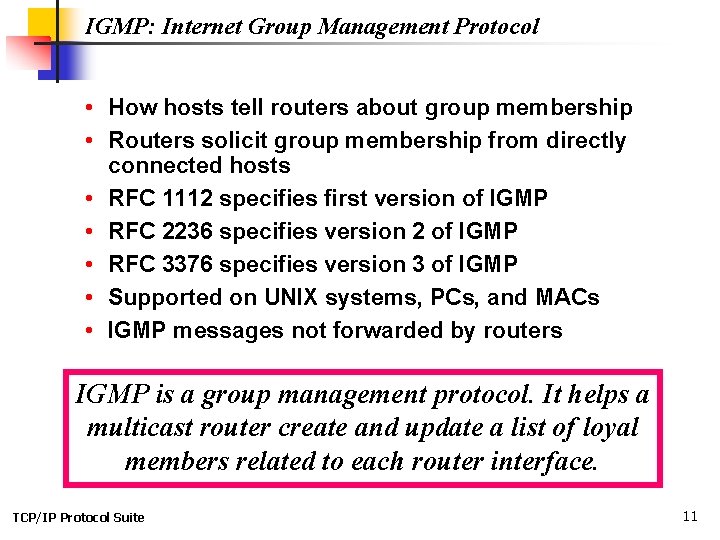
IGMP: Internet Group Management Protocol • How hosts tell routers about group membership • Routers solicit group membership from directly connected hosts • RFC 1112 specifies first version of IGMP • RFC 2236 specifies version 2 of IGMP • RFC 3376 specifies version 3 of IGMP • Supported on UNIX systems, PCs, and MACs • IGMP messages not forwarded by routers IGMP is a group management protocol. It helps a multicast router create and update a list of loyal members related to each router interface. TCP/IP Protocol Suite 11
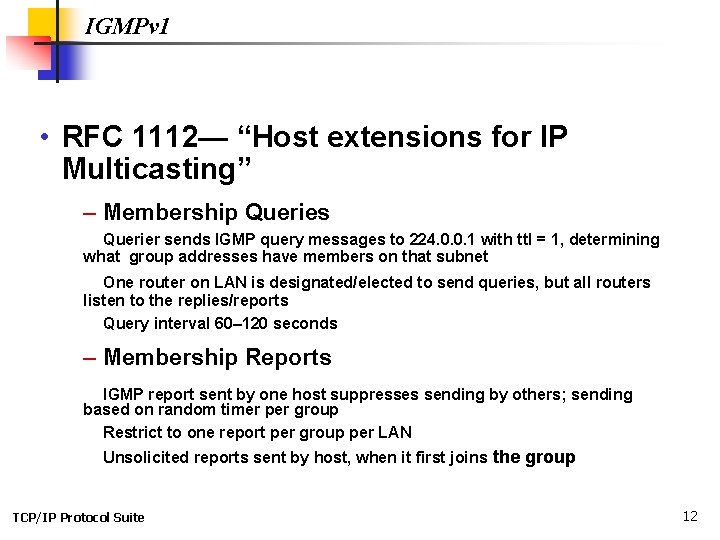
IGMPv 1 • RFC 1112— “Host extensions for IP Multicasting” – Membership Queries Querier sends IGMP query messages to 224. 0. 0. 1 with ttl = 1, determining what group addresses have members on that subnet One router on LAN is designated/elected to send queries, but all routers listen to the replies/reports Query interval 60– 120 seconds – Membership Reports IGMP report sent by one host suppresses sending by others; sending based on random timer per group Restrict to one report per group per LAN Unsolicited reports sent by host, when it first joins the group TCP/IP Protocol Suite 12
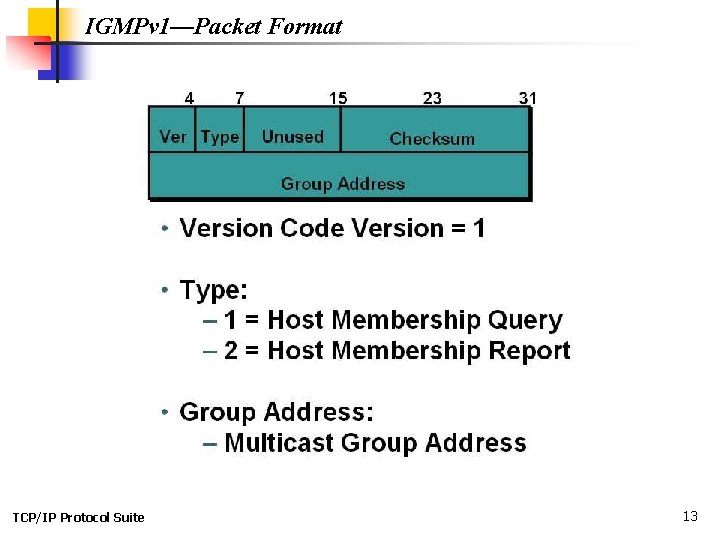
IGMPv 1—Packet Format TCP/IP Protocol Suite 13
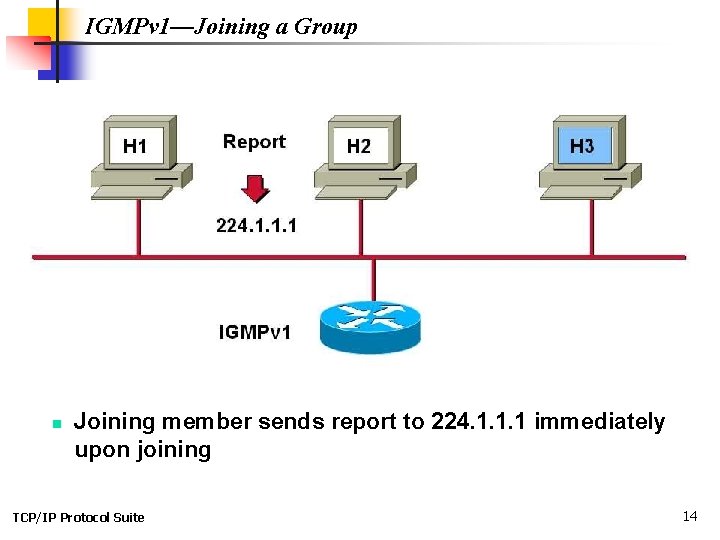
IGMPv 1—Joining a Group n Joining member sends report to 224. 1. 1. 1 immediately upon joining TCP/IP Protocol Suite 14
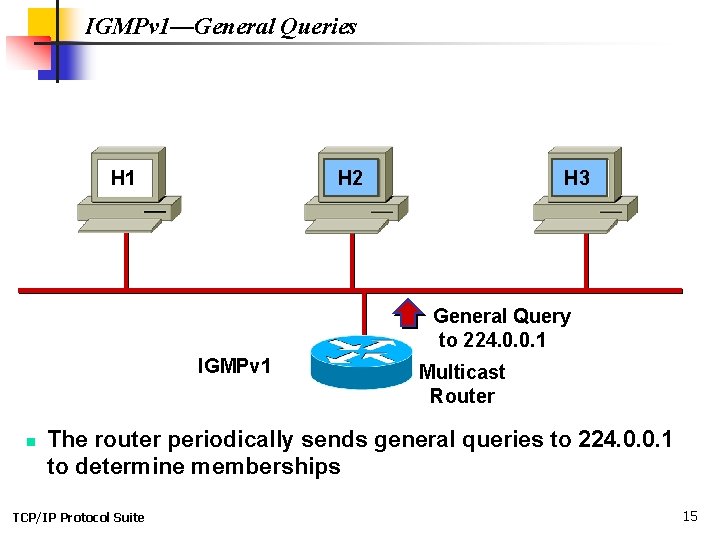
IGMPv 1—General Queries H 1 H 2 H 3 General Query to 224. 0. 0. 1 IGMPv 1 n Multicast Router The router periodically sends general queries to 224. 0. 0. 1 to determine memberships TCP/IP Protocol Suite 15
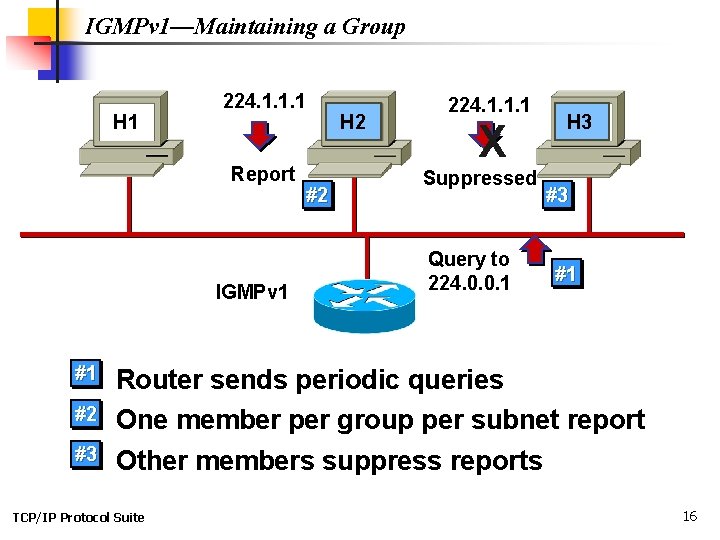
IGMPv 1—Maintaining a Group H 1 224. 1. 1. 1 Report IGMPv 1 H 2 #2 224. 1. 1. 1 X Suppressed Query to 224. 0. 0. 1 H 3 #3 #1 #1 Router sends periodic queries #2 One member per group per subnet report Other members suppress reports #3 TCP/IP Protocol Suite 16
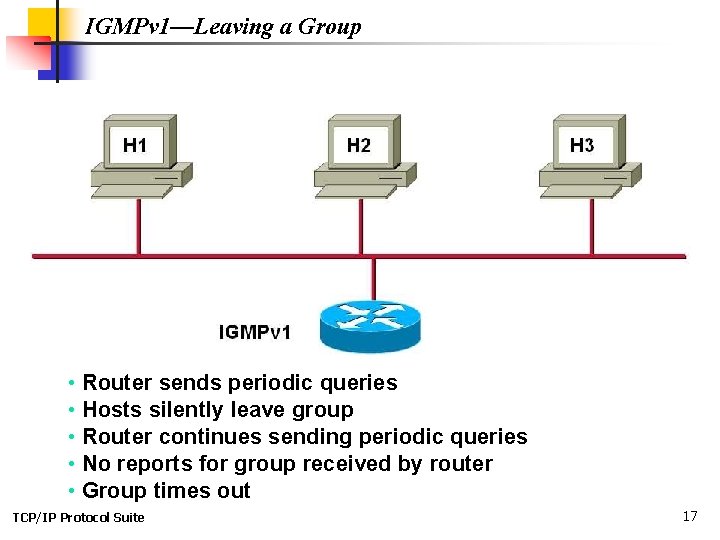
IGMPv 1—Leaving a Group • Router sends periodic queries • Hosts silently leave group • Router continues sending periodic queries • No reports for group received by router • Group times out TCP/IP Protocol Suite 17
IGMPv 2 RFC 2236 –Leave Group message –Host sends leave message if it leaves the group and is the last member (reduces leave latency in comparison to v 1); sent to 224. 0. 0. 2 (all routers) – Group-specific query –After Host sends Leave Group message, Router sends Group-specific queries to make sure there are no members present before stopping to forward data for the group for that subnet TCP/IP Protocol Suite 18
IGMPv 2 – Querier election mechanism On multiaccess networks, an IGMP Querier router is elected based on lowest IP address. Only the Querier router sends Querys. – Query-Interval Response Time General Queries specify “Max. Response Time” which inform hosts of the maximum time within which a host must respond to General Query. (Improves burstiness of the responses. ) – Backward compatible with IGMPv 1 TCP/IP Protocol Suite 19
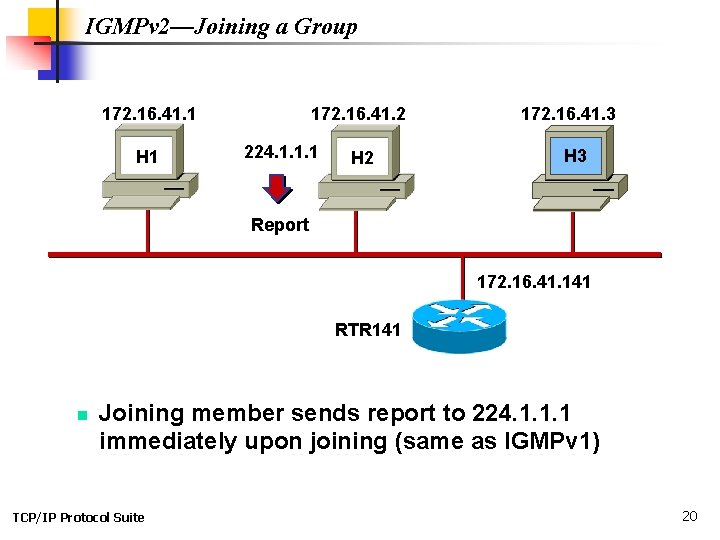
IGMPv 2—Joining a Group 172. 16. 41. 1 H 1 172. 16. 41. 2 224. 1. 1. 1 H 2 172. 16. 41. 3 H 3 Report 172. 16. 41. 141 RTR 141 n Joining member sends report to 224. 1. 1. 1 immediately upon joining (same as IGMPv 1) TCP/IP Protocol Suite 20
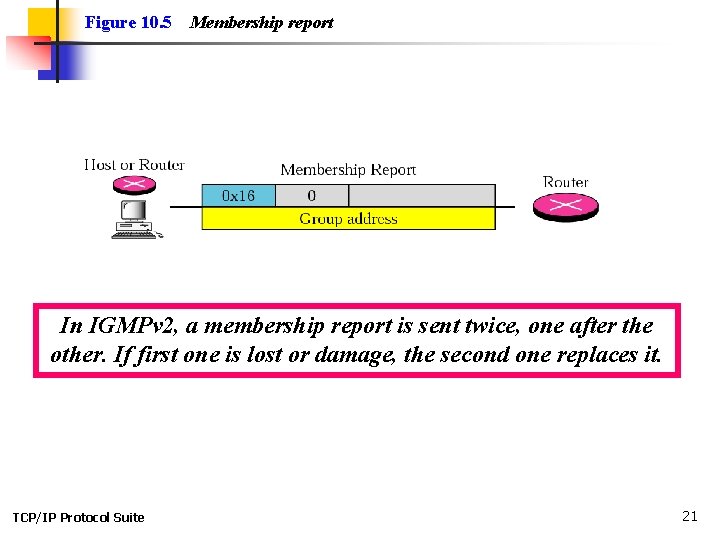
Figure 10. 5 Membership report In IGMPv 2, a membership report is sent twice, one after the other. If first one is lost or damage, the second one replaces it. TCP/IP Protocol Suite 21
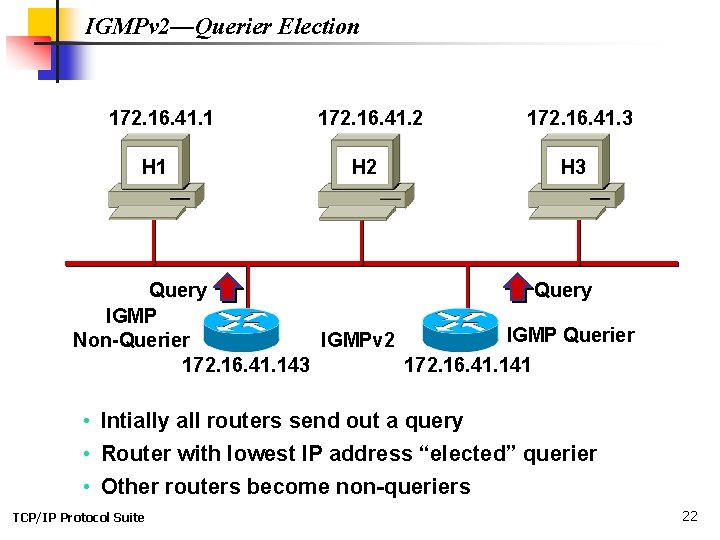
IGMPv 2—Querier Election 172. 16. 41. 1 H 1 172. 16. 41. 2 H 2 172. 16. 41. 3 H 3 Query IGMP Querier Non-Querier IGMPv 2 172. 16. 41. 143 172. 16. 41. 141 • Intially all routers send out a query • Router with lowest IP address “elected” querier • Other routers become non-queriers TCP/IP Protocol Suite 22
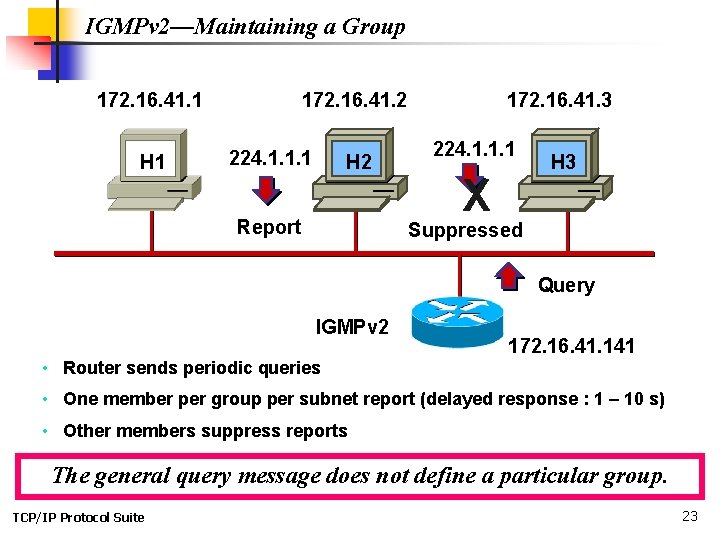
IGMPv 2—Maintaining a Group 172. 16. 41. 1 H 1 172. 16. 41. 2 224. 1. 1. 1 H 2 Report 172. 16. 41. 3 224. 1. 1. 1 X H 3 Suppressed Query IGMPv 2 • Router sends periodic queries 172. 16. 41. 141 • One member per group per subnet report (delayed response : 1 – 10 s) • Other members suppress reports The general query message does not define a particular group. TCP/IP Protocol Suite 23
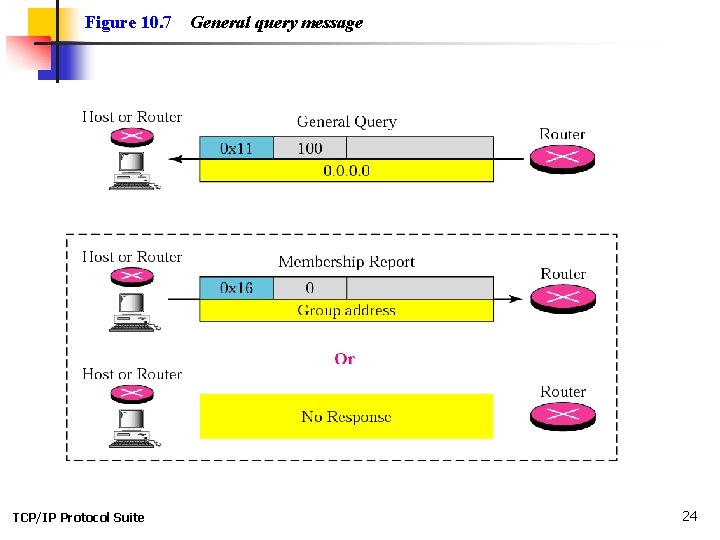
Figure 10. 7 TCP/IP Protocol Suite General query message 24
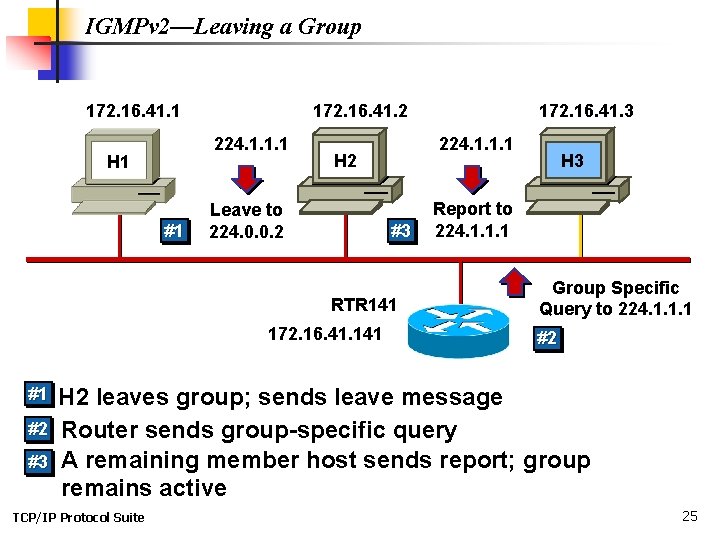
IGMPv 2—Leaving a Group 172. 16. 41. 1 172. 16. 41. 2 224. 1. 1. 1 H 1 #1 224. 1. 1. 1 H 2 Leave to 224. 0. 0. 2 #3 RTR 141 172. 16. 41. 3 H 3 Report to 224. 1. 1. 1 Group Specific Query to 224. 1. 1. 1 #2 H 2 leaves group; sends leave message #2 • Router sends group-specific query • A remaining member host sends report; group #3 remains active #1 n TCP/IP Protocol Suite 25
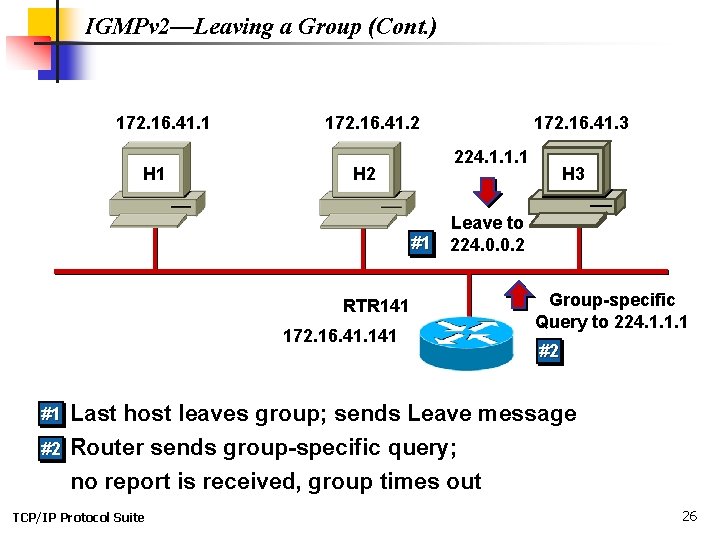
IGMPv 2—Leaving a Group (Cont. ) 172. 16. 41. 1 H 1 172. 16. 41. 2 224. 1. 1. 1 H 2 #1 RTR 141 172. 16. 41. 3 H 3 Leave to 224. 0. 0. 2 Group-specific Query to 224. 1. 1. 1 #2 #1 • Last host leaves group; sends Leave message #2 • Router sends group-specific query; no report is received, group times out TCP/IP Protocol Suite 26
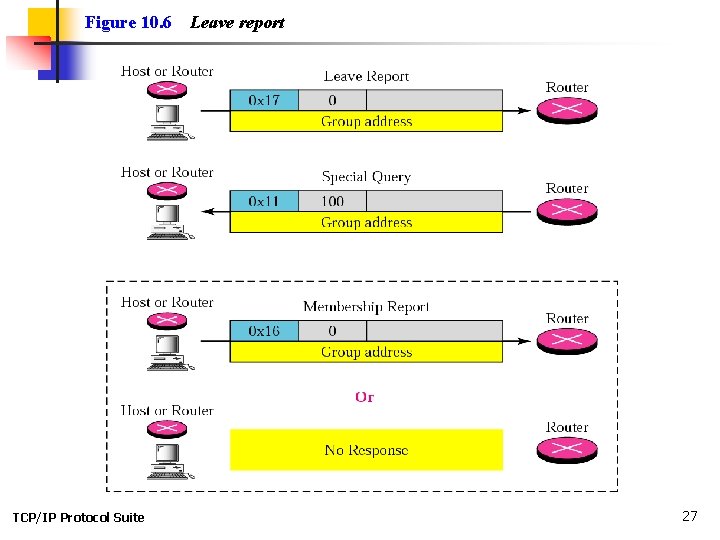
Figure 10. 6 TCP/IP Protocol Suite Leave report 27
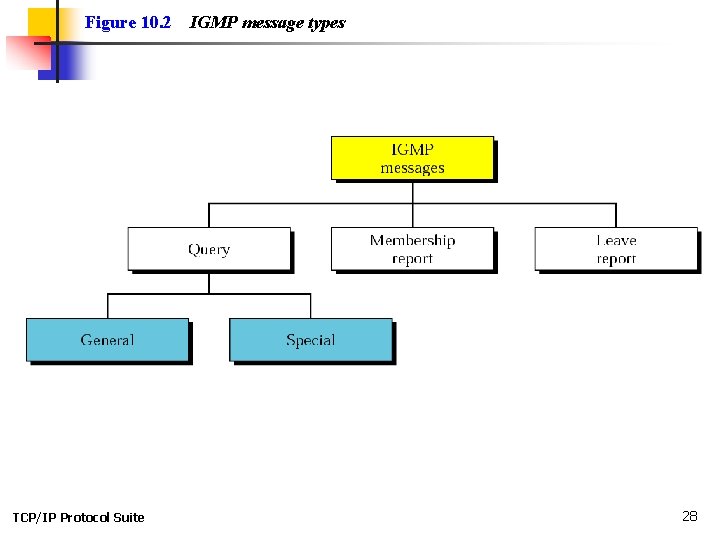
Figure 10. 2 TCP/IP Protocol Suite IGMP message types 28
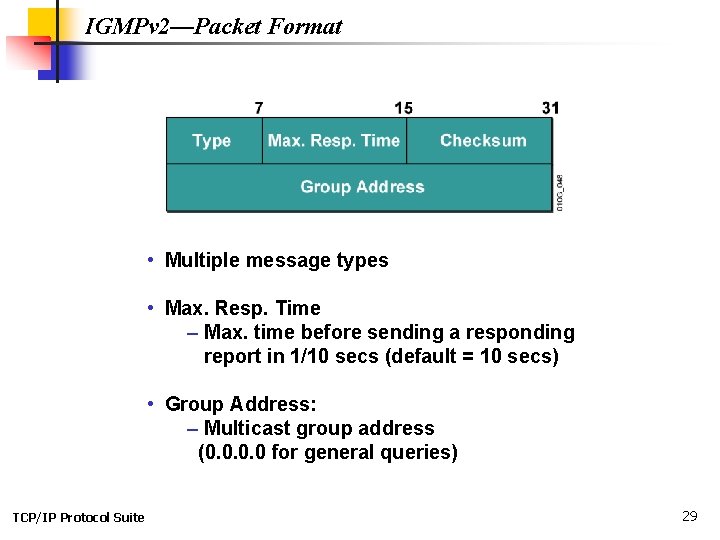
IGMPv 2—Packet Format • Multiple message types • Max. Resp. Time – Max. time before sending a responding report in 1/10 secs (default = 10 secs) • Group Address: – Multicast group address (0. 0 for general queries) TCP/IP Protocol Suite 29
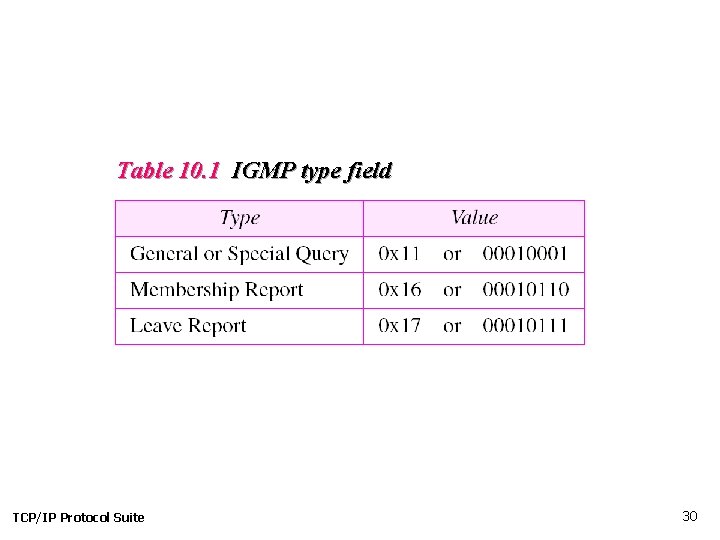
Table 10. 1 IGMP type field TCP/IP Protocol Suite 30
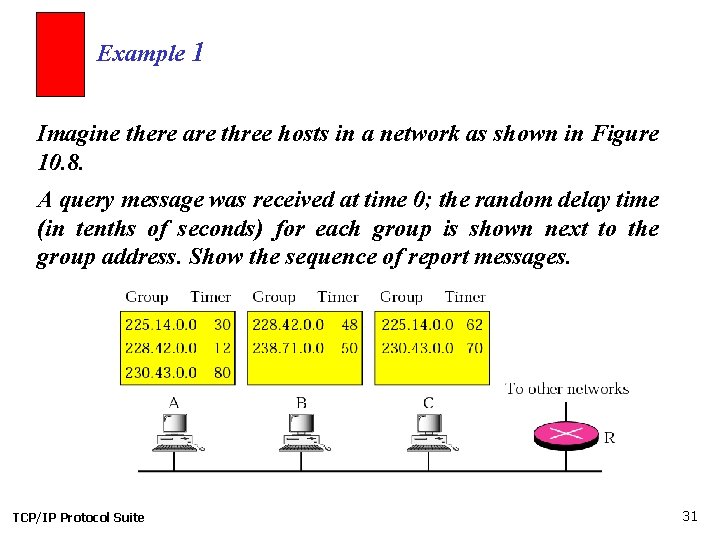
Example 1 Imagine there are three hosts in a network as shown in Figure 10. 8. A query message was received at time 0; the random delay time (in tenths of seconds) for each group is shown next to the group address. Show the sequence of report messages. TCP/IP Protocol Suite 31
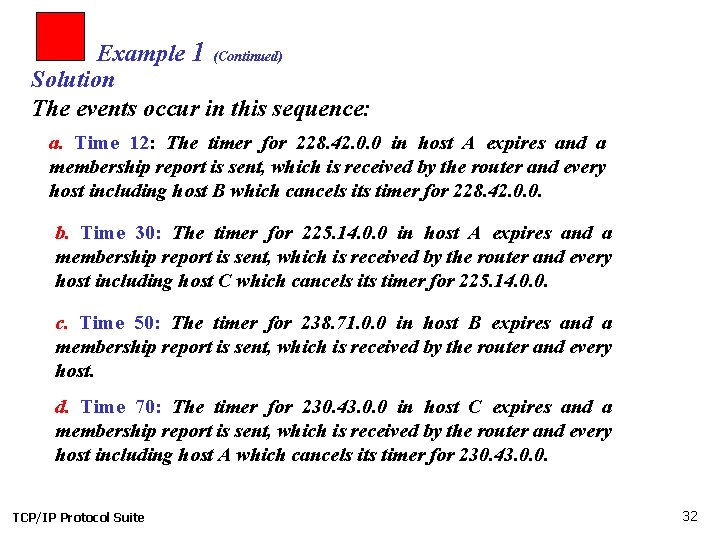
Example 1 (Continued) Solution The events occur in this sequence: a. Time 12: The timer for 228. 42. 0. 0 in host A expires and a membership report is sent, which is received by the router and every host including host B which cancels its timer for 228. 42. 0. 0. b. Time 30: The timer for 225. 14. 0. 0 in host A expires and a membership report is sent, which is received by the router and every host including host C which cancels its timer for 225. 14. 0. 0. c. Time 50: The timer for 238. 71. 0. 0 in host B expires and a membership report is sent, which is received by the router and every host. d. Time 70: The timer for 230. 43. 0. 0 in host C expires and a membership report is sent, which is received by the router and every host including host A which cancels its timer for 230. 43. 0. 0. TCP/IP Protocol Suite 32
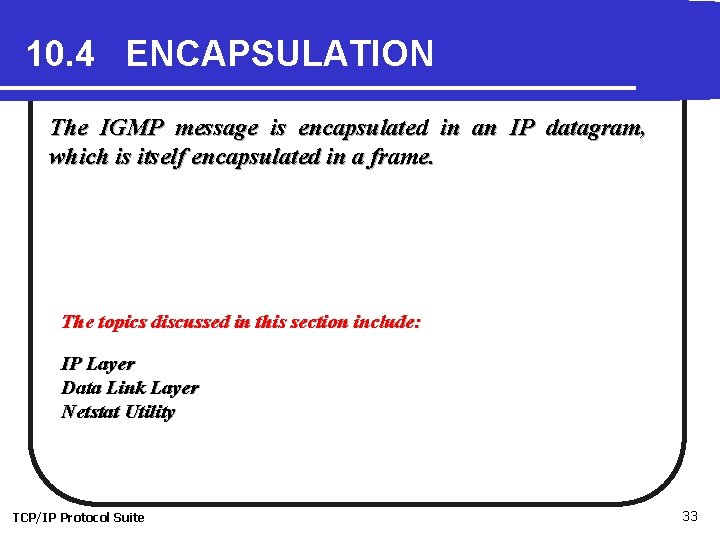
10. 4 ENCAPSULATION The IGMP message is encapsulated in an IP datagram, which is itself encapsulated in a frame. The topics discussed in this section include: IP Layer Data Link Layer Netstat Utility TCP/IP Protocol Suite 33
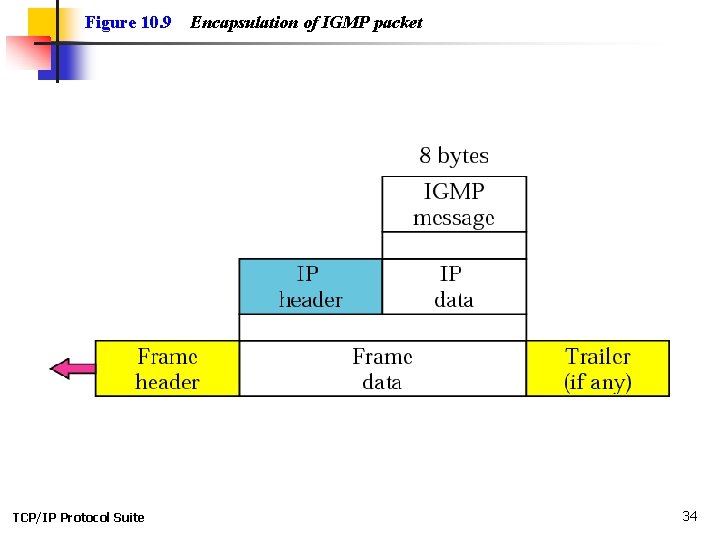
Figure 10. 9 TCP/IP Protocol Suite Encapsulation of IGMP packet 34
Note: The IP packet that carries an IGMP packet has a value of 2 in its protocol field. The IP packet that carries an IGMP packet has a value of 1 in its TTL field. TCP/IP Protocol Suite 35
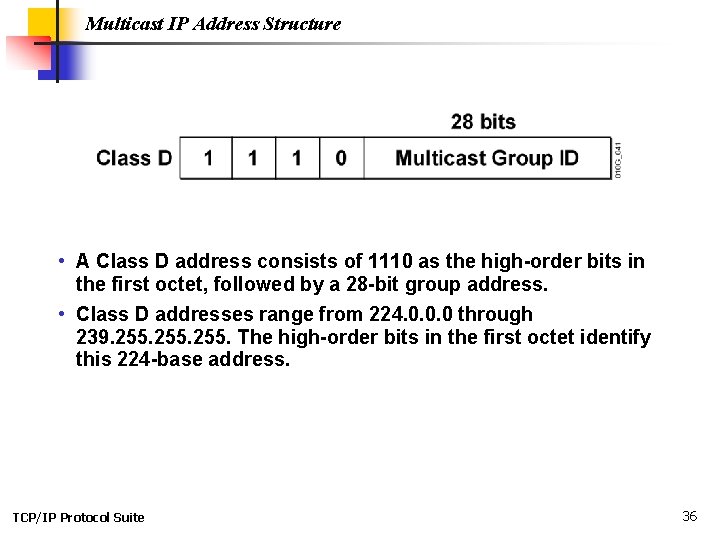
Multicast IP Address Structure • A Class D address consists of 1110 as the high-order bits in the first octet, followed by a 28 -bit group address. • Class D addresses range from 224. 0. 0. 0 through 239. 255. The high-order bits in the first octet identify this 224 -base address. TCP/IP Protocol Suite 36
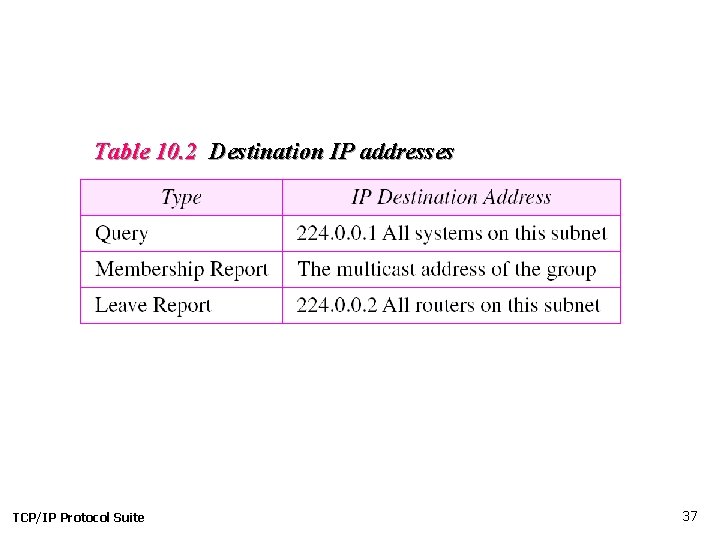
Table 10. 2 Destination IP addresses TCP/IP Protocol Suite 37
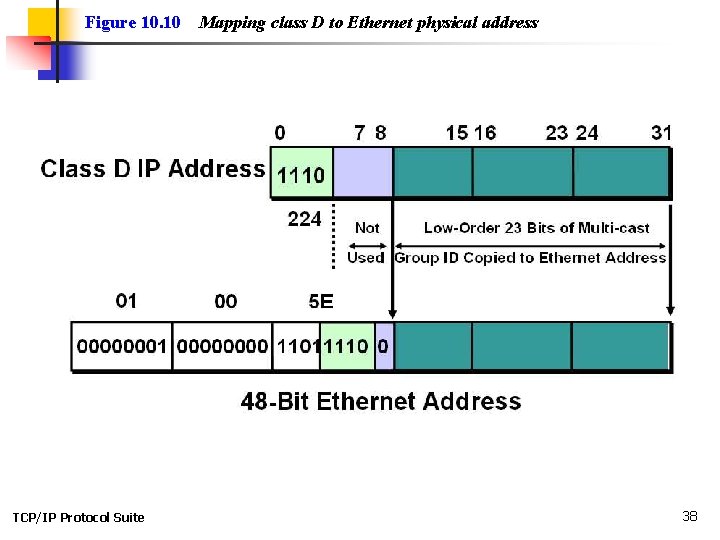
Figure 10. 10 TCP/IP Protocol Suite Mapping class D to Ethernet physical address 38
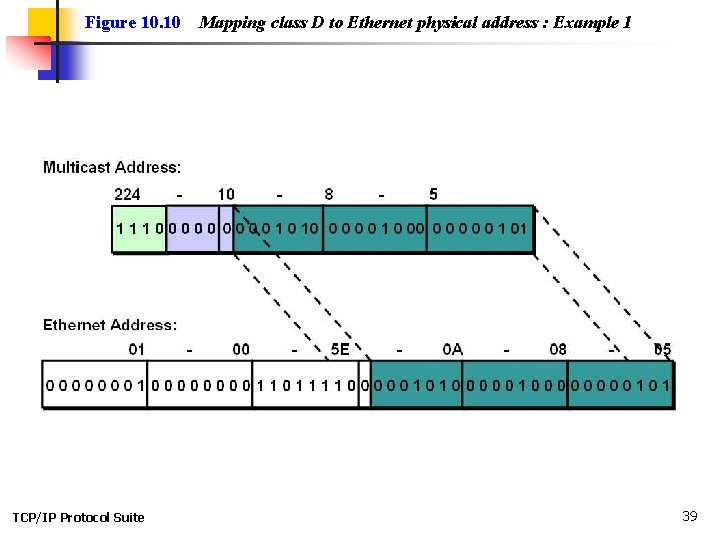
Figure 10. 10 TCP/IP Protocol Suite Mapping class D to Ethernet physical address : Example 1 39
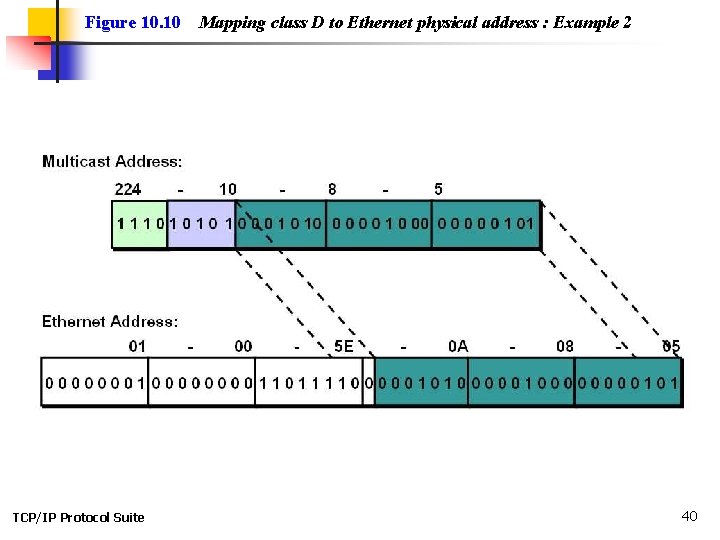
Figure 10. 10 TCP/IP Protocol Suite Mapping class D to Ethernet physical address : Example 2 40
Note: An Ethernet multicast physical address is in the range 01: 00: 5 E: 00: 00 to 01: 00: 5 E: 7 F: FF. TCP/IP Protocol Suite 41
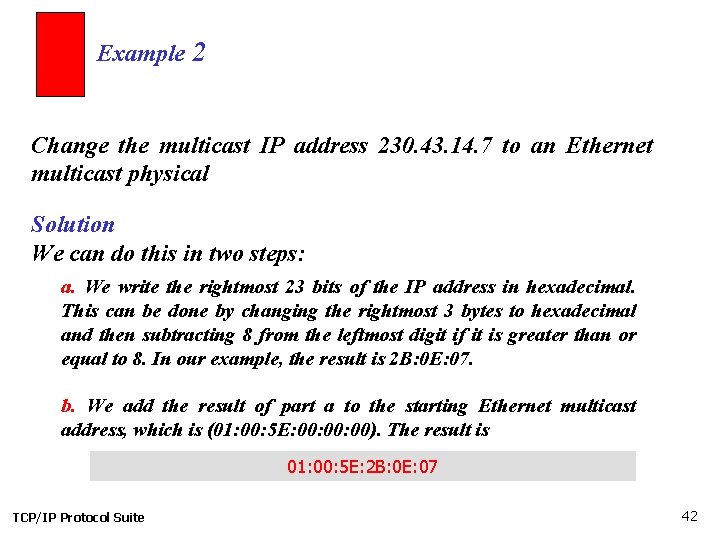
Example 2 Change the multicast IP address 230. 43. 14. 7 to an Ethernet multicast physical Solution We can do this in two steps: a. We write the rightmost 23 bits of the IP address in hexadecimal. This can be done by changing the rightmost 3 bytes to hexadecimal and then subtracting 8 from the leftmost digit if it is greater than or equal to 8. In our example, the result is 2 B: 0 E: 07. b. We add the result of part a to the starting Ethernet multicast address, which is (01: 00: 5 E: 00: 00). The result is 01: 00: 5 E: 2 B: 0 E: 07 TCP/IP Protocol Suite 42
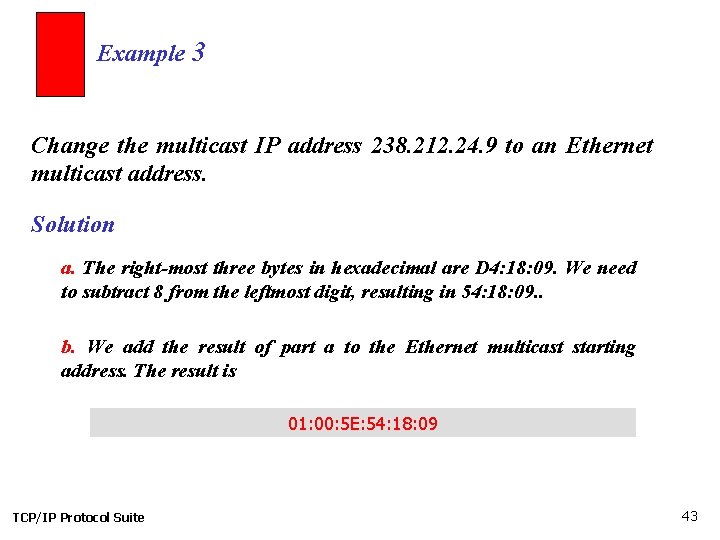
Example 3 Change the multicast IP address 238. 212. 24. 9 to an Ethernet multicast address. Solution a. The right-most three bytes in hexadecimal are D 4: 18: 09. We need to subtract 8 from the leftmost digit, resulting in 54: 18: 09. . b. We add the result of part a to the Ethernet multicast starting address. The result is 01: 00: 5 E: 54: 18: 09 TCP/IP Protocol Suite 43
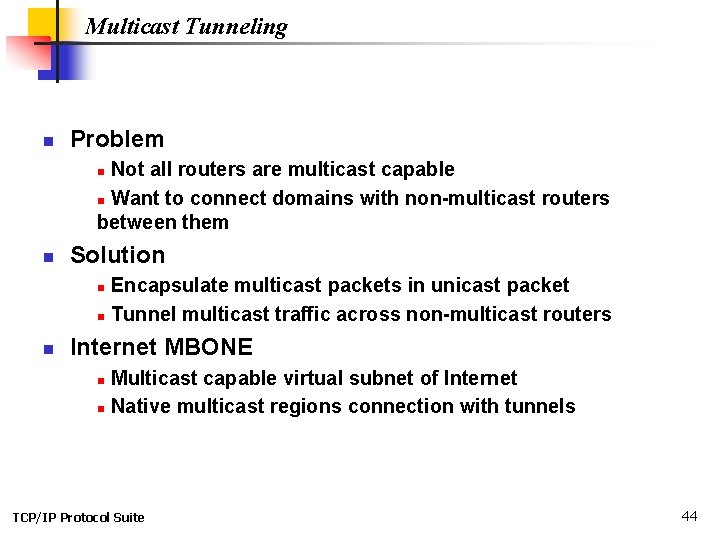
Multicast Tunneling n Problem Not all routers are multicast capable n Want to connect domains with non-multicast routers between them n n Solution Encapsulate multicast packets in unicast packet n Tunnel multicast traffic across non-multicast routers n n Internet MBONE Multicast capable virtual subnet of Internet n Native multicast regions connection with tunnels n TCP/IP Protocol Suite 44
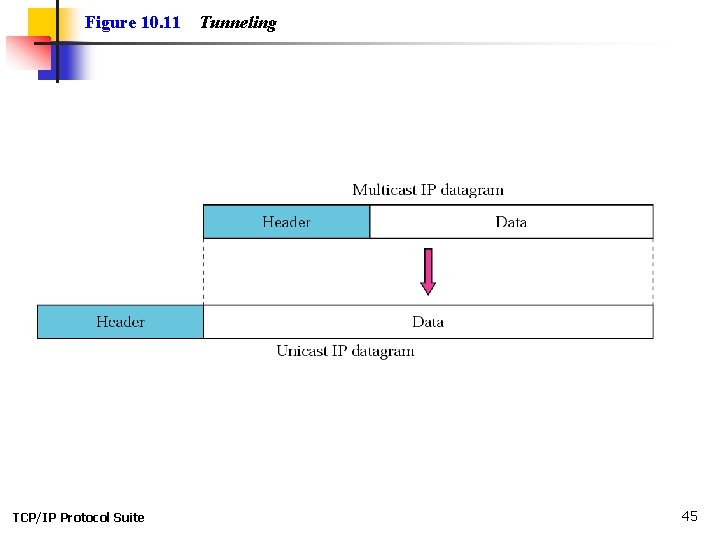
Figure 10. 11 TCP/IP Protocol Suite Tunneling 45
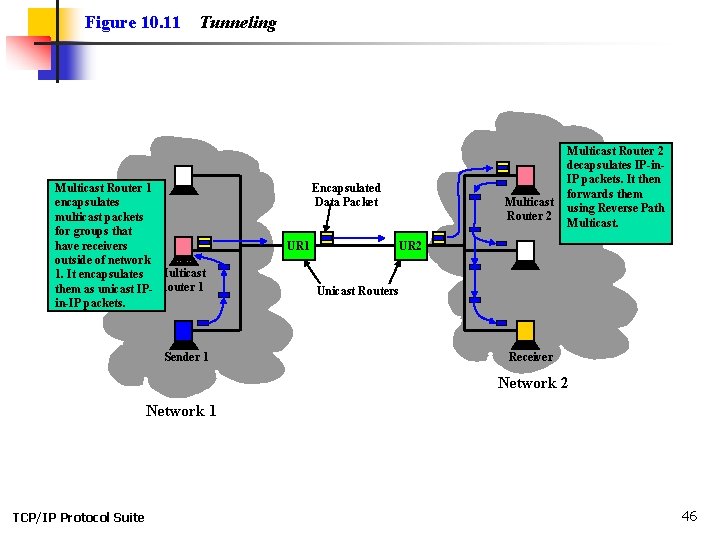
Figure 10. 11 Tunneling Multicast Router 1 encapsulates multicast packets for groups that have receivers outside of network 1. It encapsulates Multicast them as unicast IP- Router 1 in-IP packets. Sender 1 Encapsulated Data Packet UR 1 Multicast Router 2 decapsulates IP-in. IP packets. It then forwards them using Reverse Path Multicast. UR 2 Unicast Routers Receiver Network 2 Network 1 TCP/IP Protocol Suite 46
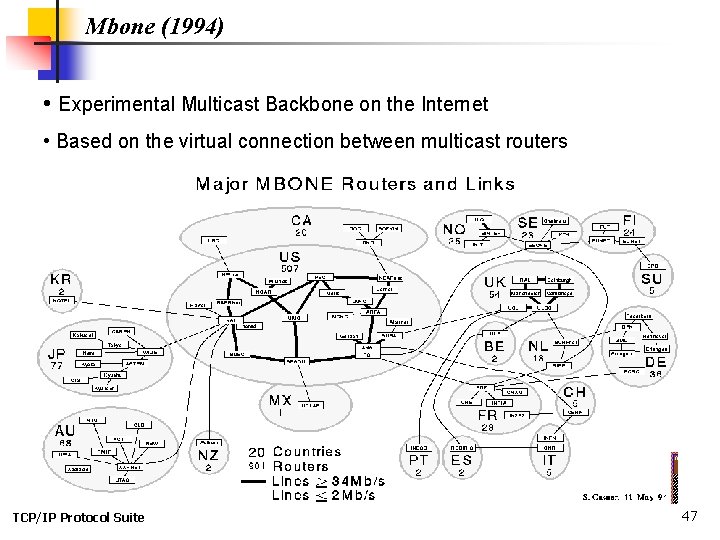
Mbone (1994) • Experimental Multicast Backbone on the Internet • Based on the virtual connection between multicast routers TCP/IP Protocol Suite 47
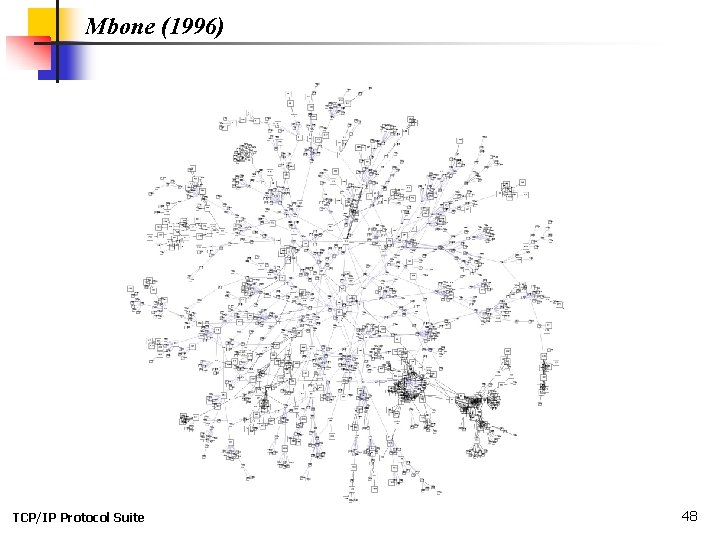
Mbone (1996) TCP/IP Protocol Suite 48
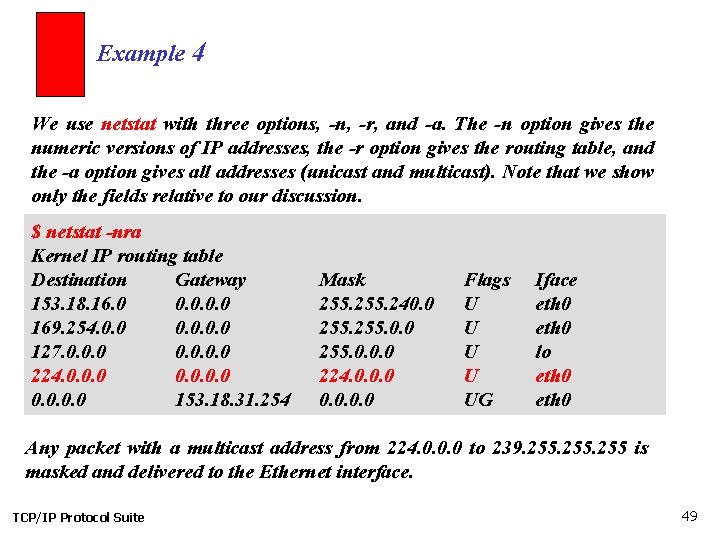
Example 4 We use netstat with three options, -n, -r, and -a. The -n option gives the numeric versions of IP addresses, the -r option gives the routing table, and the -a option gives all addresses (unicast and multicast). Note that we show only the fields relative to our discussion. $ netstat -nra Kernel IP routing table Destination Gateway 153. 18. 16. 0 0. 0 169. 254. 0. 0 127. 0. 0 224. 0. 0. 0 153. 18. 31. 254 Mask 255. 240. 0 255. 0. 0. 0 224. 0. 0 Flags U U UG Iface eth 0 lo eth 0 Any packet with a multicast address from 224. 0. 0. 0 to 239. 255 is masked and delivered to the Ethernet interface. TCP/IP Protocol Suite 49
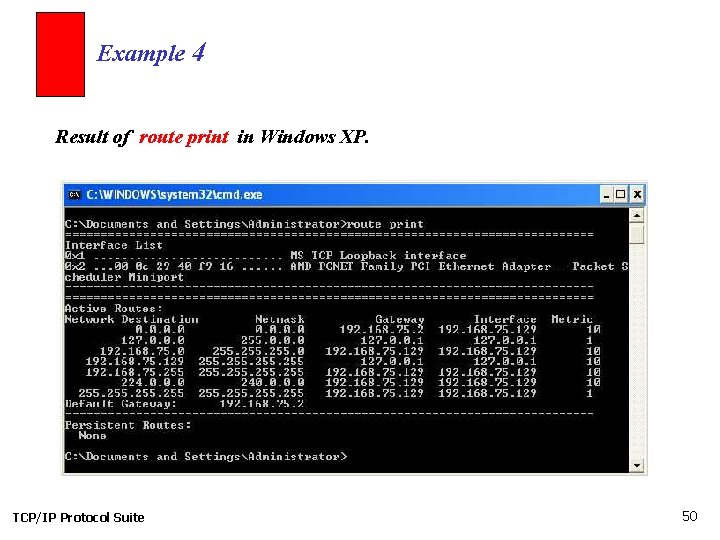
Example 4 Result of route print in Windows XP. TCP/IP Protocol Suite 50
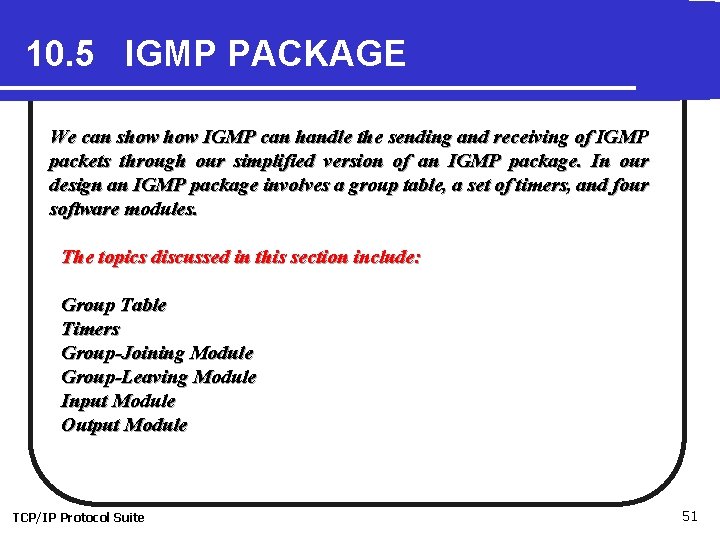
10. 5 IGMP PACKAGE We can show IGMP can handle the sending and receiving of IGMP packets through our simplified version of an IGMP package. In our design an IGMP package involves a group table, a set of timers, and four software modules. The topics discussed in this section include: Group Table Timers Group-Joining Module Group-Leaving Module Input Module Output Module TCP/IP Protocol Suite 51
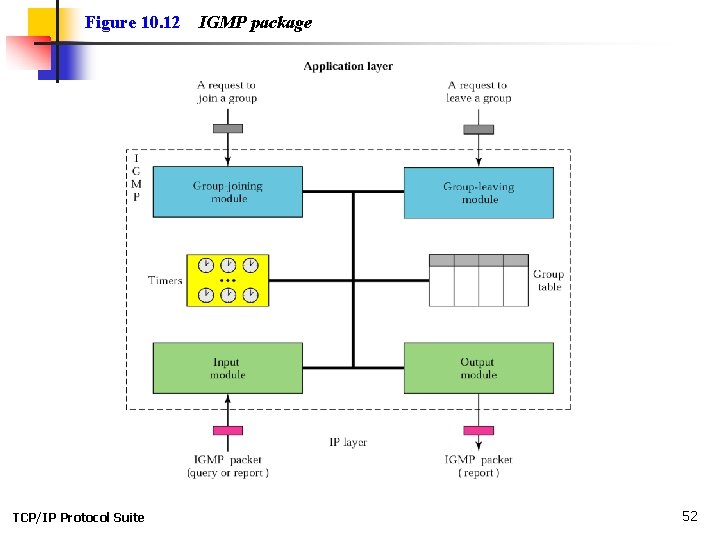
Figure 10. 12 TCP/IP Protocol Suite IGMP package 52
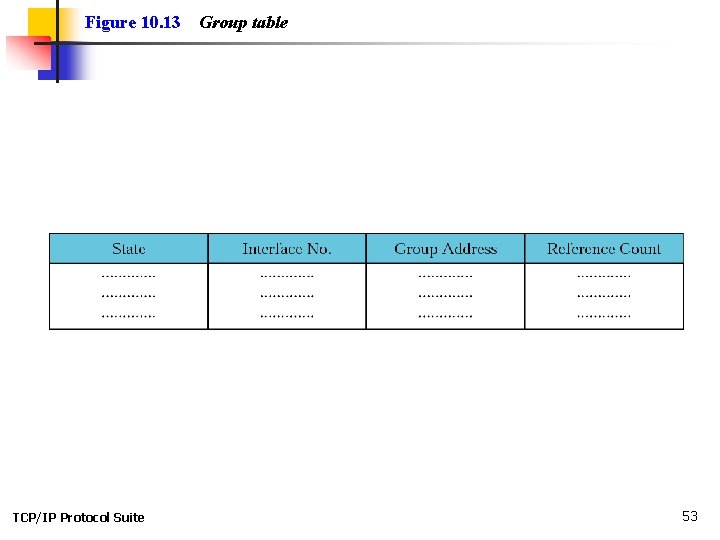
Figure 10. 13 TCP/IP Protocol Suite Group table 53
Chapter 11 User Datagram Protocol Objectives Upon completion you will be able to: • Be able to explain process-to-process communication • Know the format of a UDP user datagram • Be able to calculate a UDP checksum • Understand the operation of UDP • Know when it is appropriate to use UDP • Understand the modules in a UDP package TCP/IP Protocol Suite 54
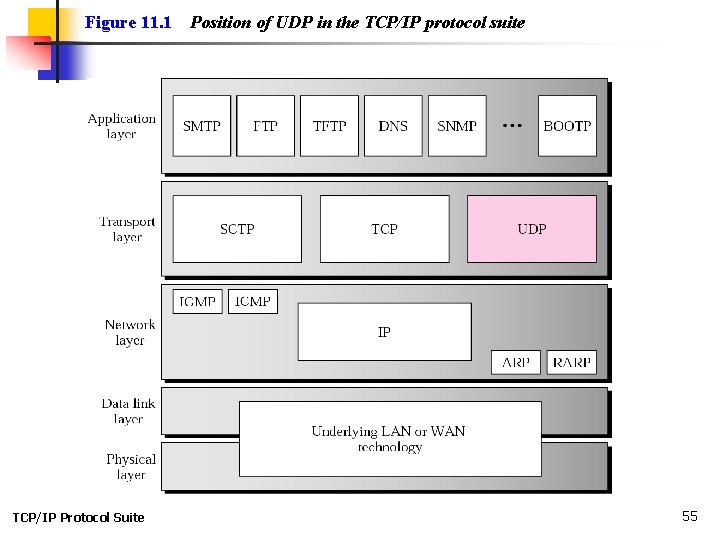
Figure 11. 1 TCP/IP Protocol Suite Position of UDP in the TCP/IP protocol suite 55
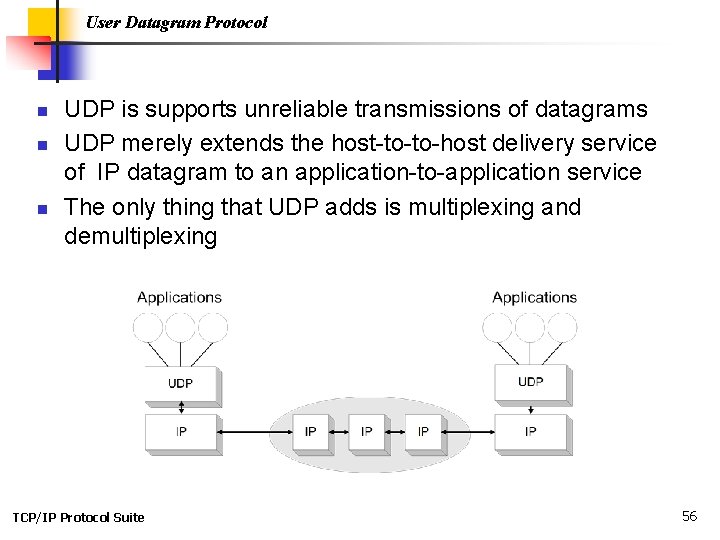
User Datagram Protocol n n n UDP is supports unreliable transmissions of datagrams UDP merely extends the host-to-to-host delivery service of IP datagram to an application-to-application service The only thing that UDP adds is multiplexing and demultiplexing TCP/IP Protocol Suite 56
11. 1 PROCESS-TO-PROCESS COMMUNICATION Before we examine UDP, we must first understand host-to-host communication and process-to-process communication and the difference between them. The topics discussed in this section include: Port Numbers Socket Addresses TCP/IP Protocol Suite 57
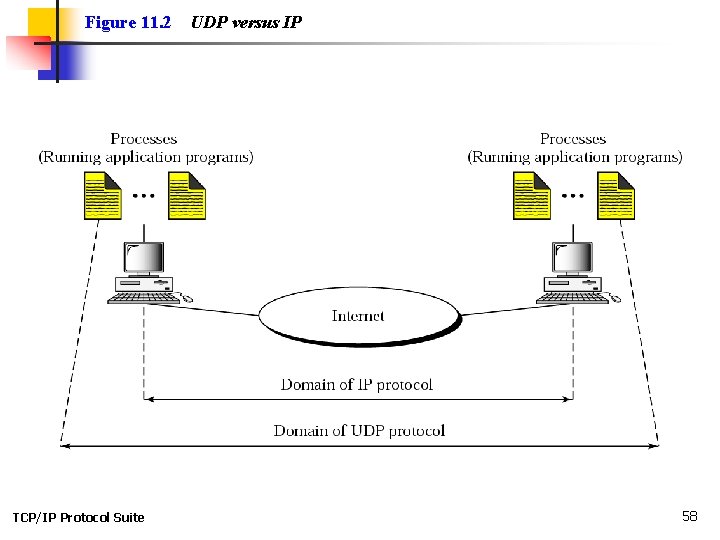
Figure 11. 2 TCP/IP Protocol Suite UDP versus IP 58
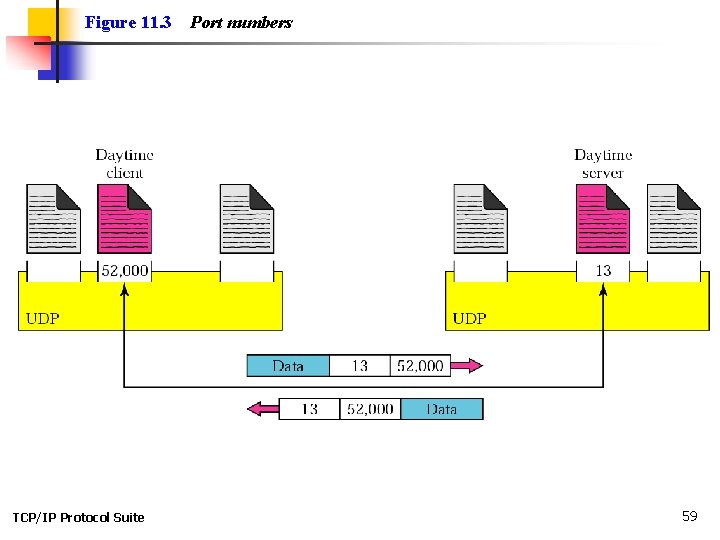
Figure 11. 3 TCP/IP Protocol Suite Port numbers 59
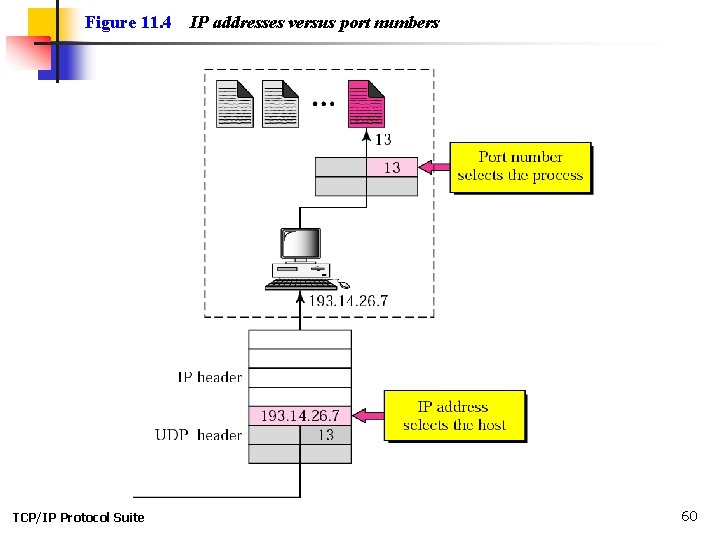
Figure 11. 4 TCP/IP Protocol Suite IP addresses versus port numbers 60
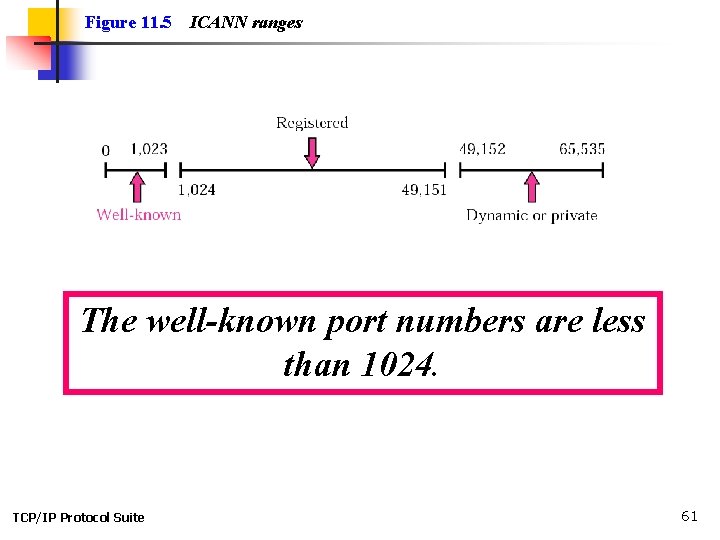
Figure 11. 5 ICANN ranges The well-known port numbers are less than 1024. TCP/IP Protocol Suite 61
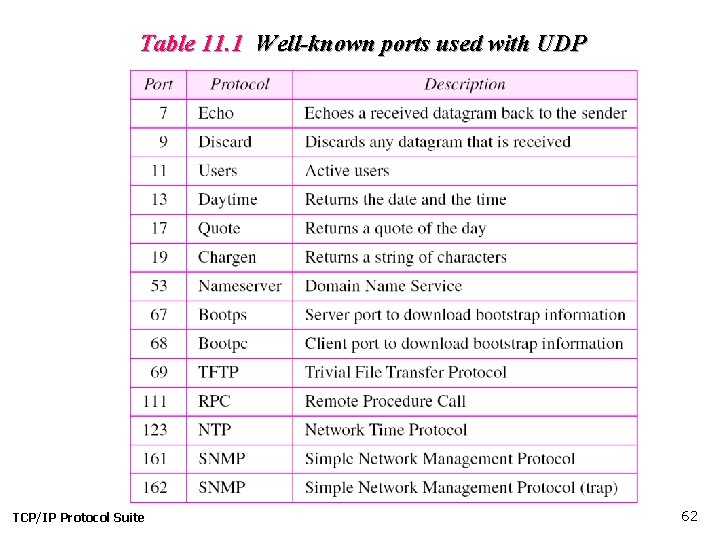
Table 11. 1 Well-known ports used with UDP TCP/IP Protocol Suite 62
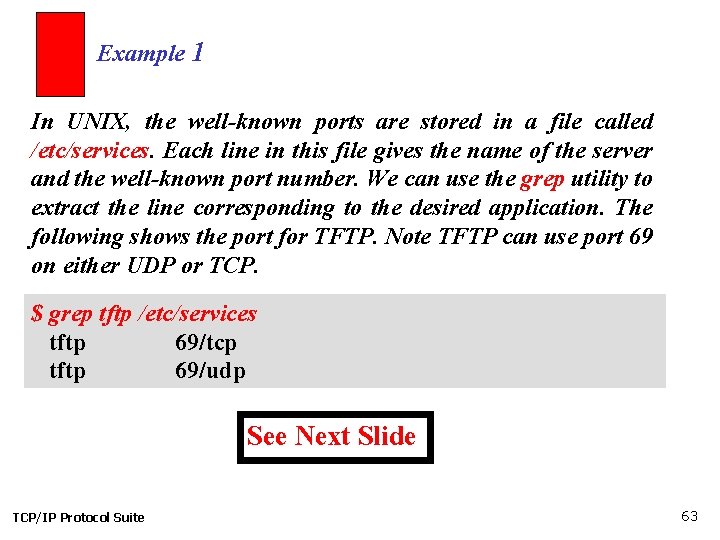
Example 1 In UNIX, the well-known ports are stored in a file called /etc/services. Each line in this file gives the name of the server and the well-known port number. We can use the grep utility to extract the line corresponding to the desired application. The following shows the port for TFTP. Note TFTP can use port 69 on either UDP or TCP. $ grep tftp /etc/services tftp 69/tcp tftp 69/udp See Next Slide TCP/IP Protocol Suite 63
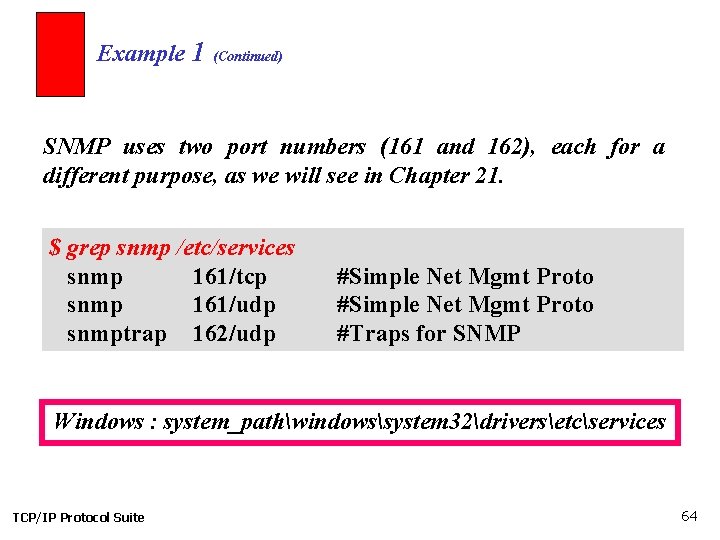
Example 1 (Continued) SNMP uses two port numbers (161 and 162), each for a different purpose, as we will see in Chapter 21. $ grep snmp /etc/services snmp 161/tcp snmp 161/udp snmptrap 162/udp #Simple Net Mgmt Proto #Traps for SNMP Windows : system_pathwindowssystem 32driversetcservices TCP/IP Protocol Suite 64
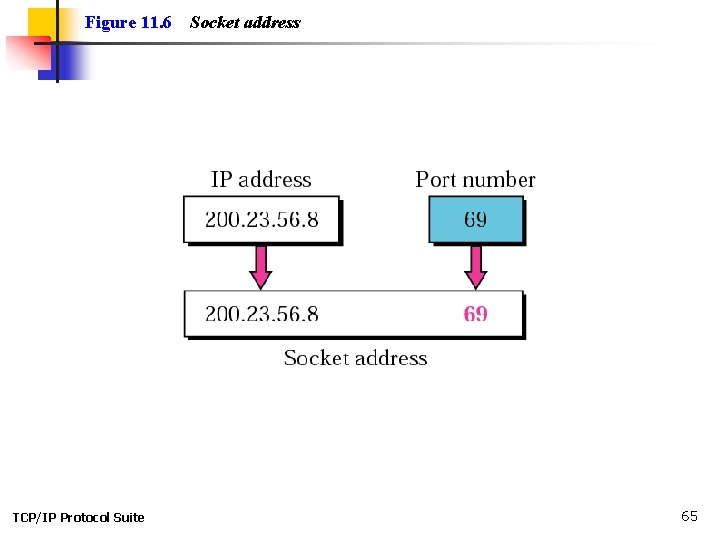
Figure 11. 6 TCP/IP Protocol Suite Socket address 65
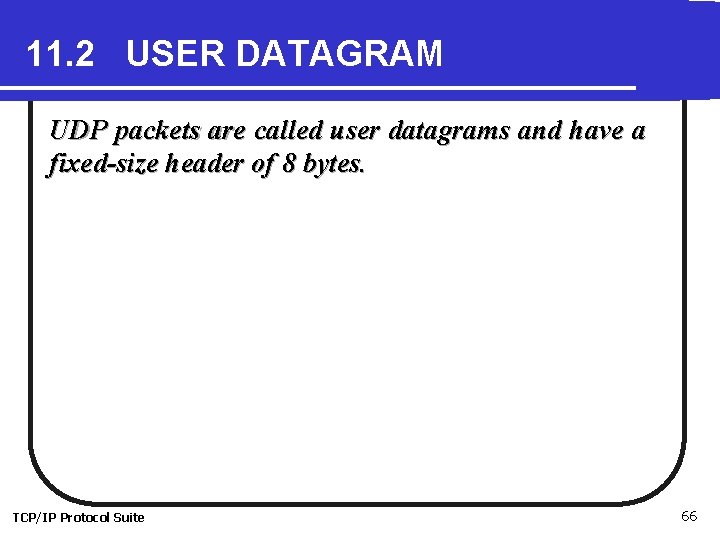
11. 2 USER DATAGRAM UDP packets are called user datagrams and have a fixed-size header of 8 bytes. TCP/IP Protocol Suite 66
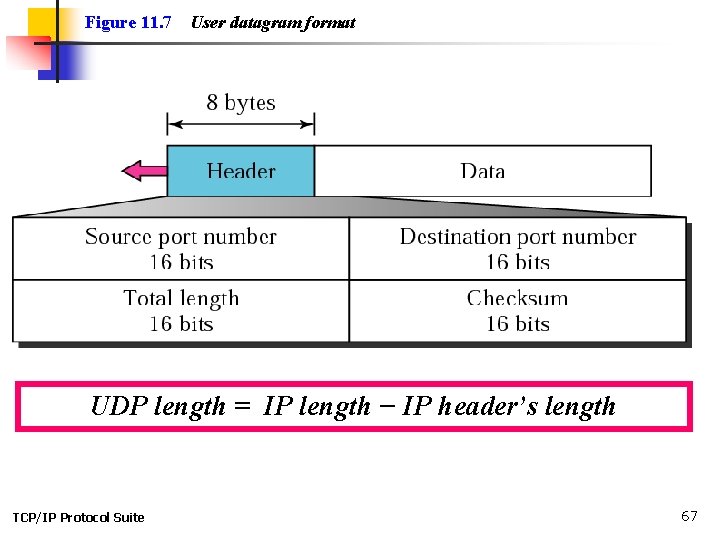
Figure 11. 7 User datagram format UDP length = IP length − IP header’s length TCP/IP Protocol Suite 67
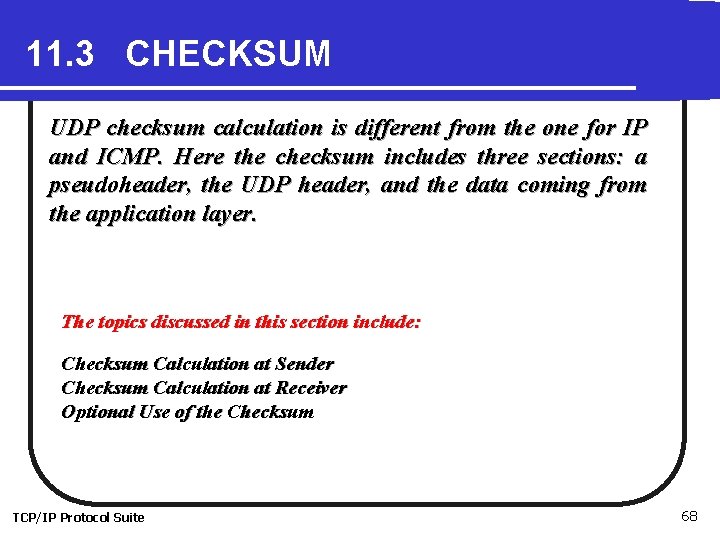
11. 3 CHECKSUM UDP checksum calculation is different from the one for IP and ICMP. Here the checksum includes three sections: a pseudoheader, the UDP header, and the data coming from the application layer. The topics discussed in this section include: Checksum Calculation at Sender Checksum Calculation at Receiver Optional Use of the Checksum TCP/IP Protocol Suite 68
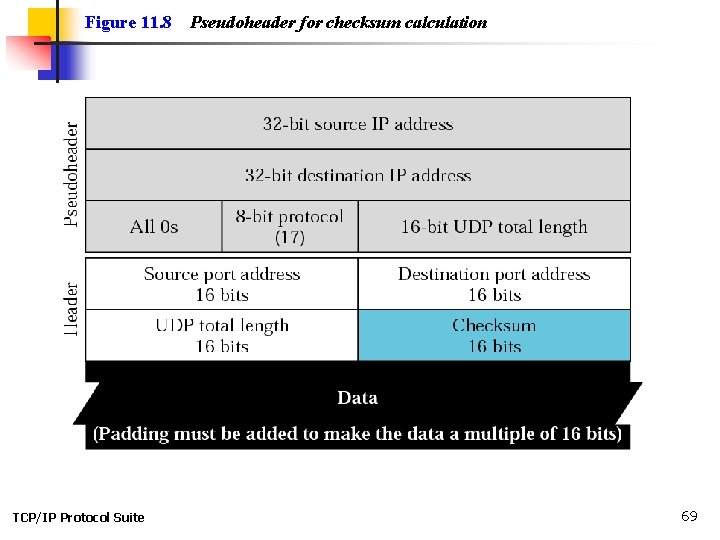
Figure 11. 8 TCP/IP Protocol Suite Pseudoheader for checksum calculation 69
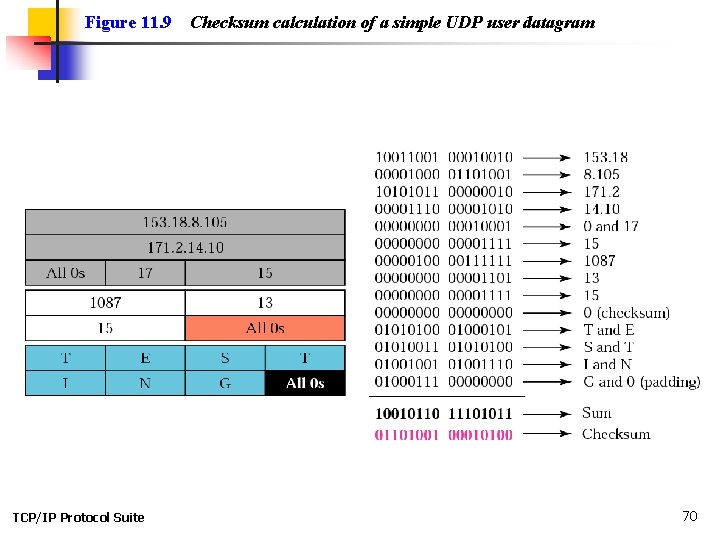
Figure 11. 9 TCP/IP Protocol Suite Checksum calculation of a simple UDP user datagram 70
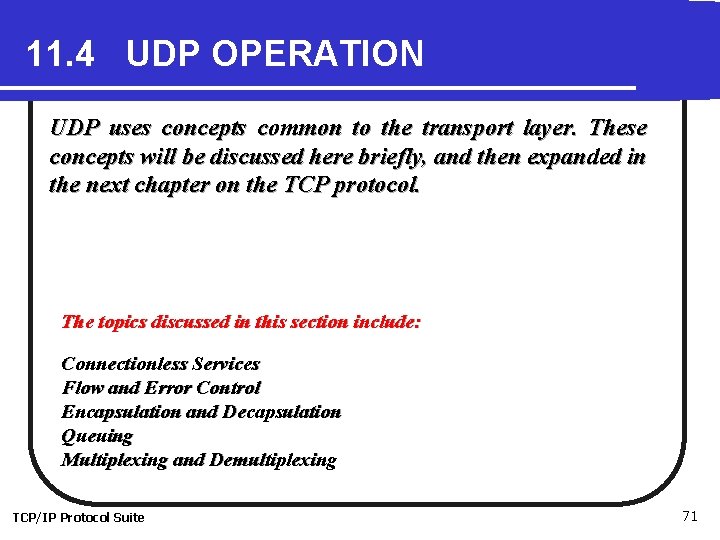
11. 4 UDP OPERATION UDP uses concepts common to the transport layer. These concepts will be discussed here briefly, and then expanded in the next chapter on the TCP protocol. The topics discussed in this section include: Connectionless Services Flow and Error Control Encapsulation and Decapsulation Queuing Multiplexing and Demultiplexing TCP/IP Protocol Suite 71
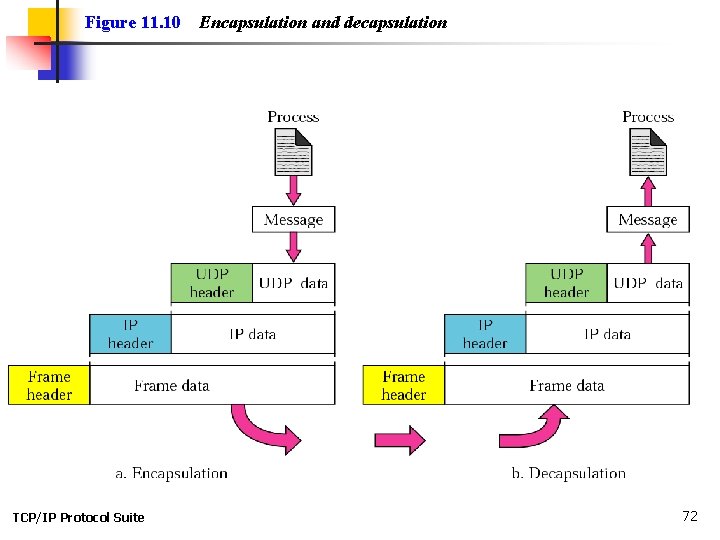
Figure 11. 10 TCP/IP Protocol Suite Encapsulation and decapsulation 72
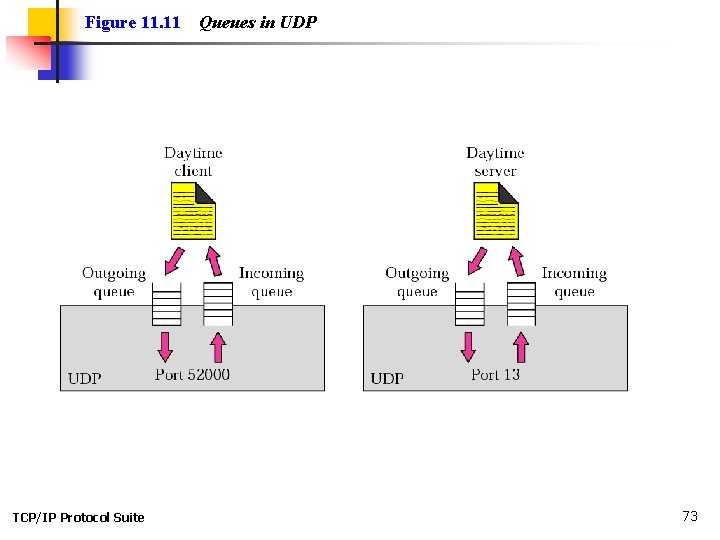
Figure 11. 11 TCP/IP Protocol Suite Queues in UDP 73
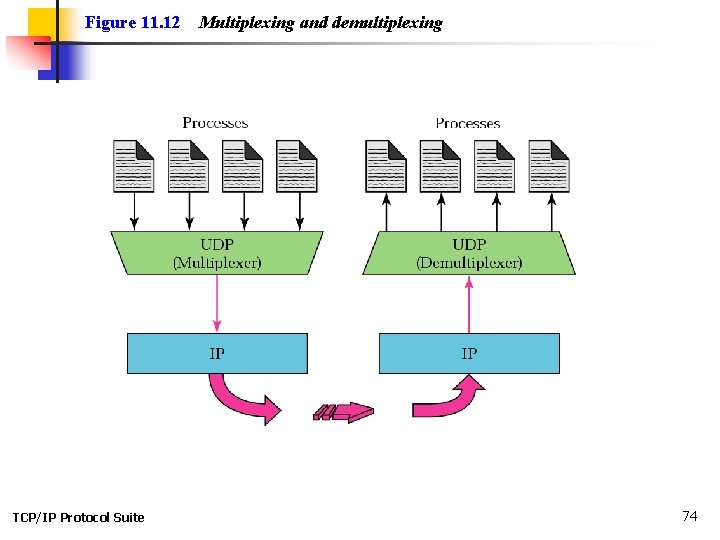
Figure 11. 12 TCP/IP Protocol Suite Multiplexing and demultiplexing 74
11. 5 USE OF UDP We discuss some uses of the UDP protocol in this section. TCP/IP Protocol Suite 75
11. 6 UDP PACKAGE To show UDP handles the sending and receiving of UDP packets, we present a simple version of the UDP package. The UDP package involves five components: a control-block table, input queues, a control-block module, an input module, and an output module. The topics discussed in this section include: Control-Block Table Input Queues Control-Block Module Input Module Output Module TCP/IP Protocol Suite 76
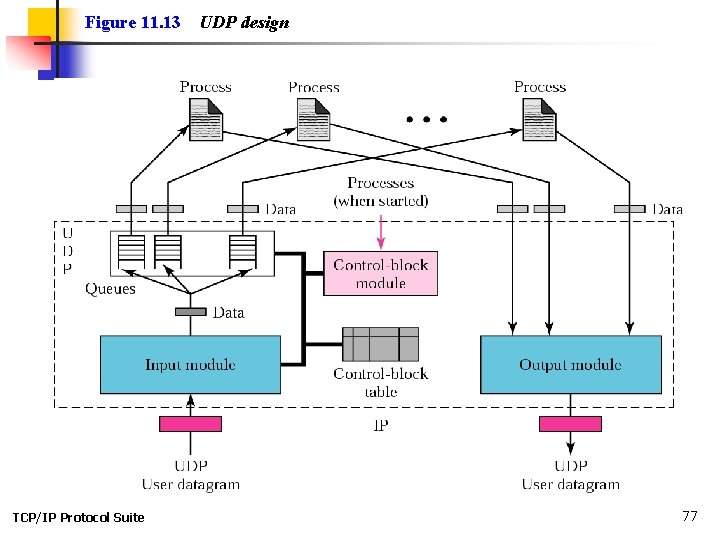
Figure 11. 13 TCP/IP Protocol Suite UDP design 77
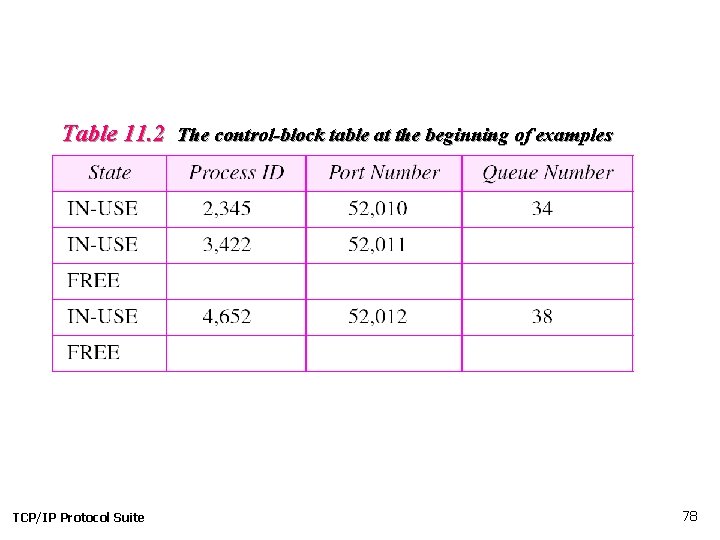
Table 11. 2 The control-block table at the beginning of examples TCP/IP Protocol Suite 78
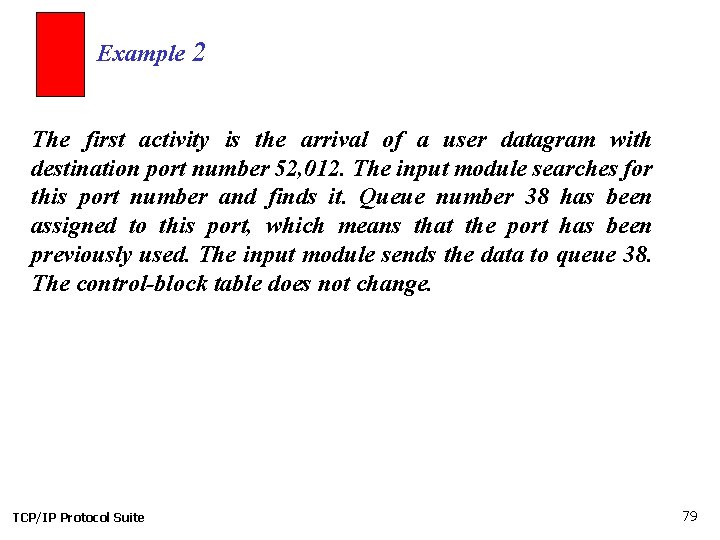
Example 2 The first activity is the arrival of a user datagram with destination port number 52, 012. The input module searches for this port number and finds it. Queue number 38 has been assigned to this port, which means that the port has been previously used. The input module sends the data to queue 38. The control-block table does not change. TCP/IP Protocol Suite 79
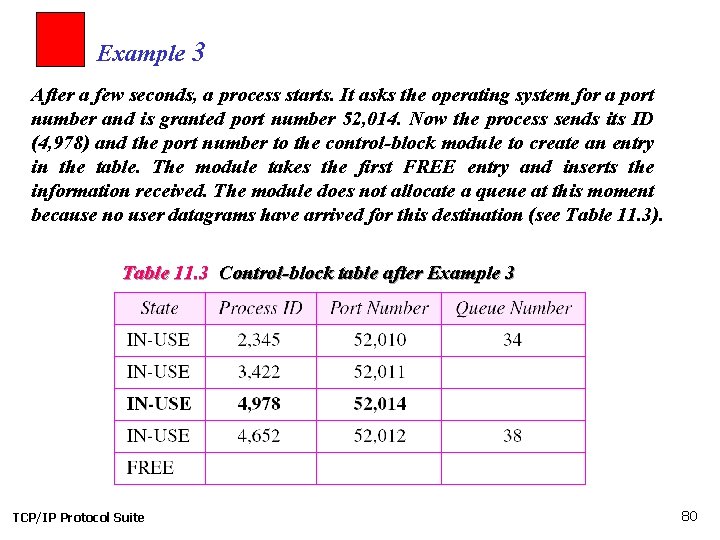
Example 3 After a few seconds, a process starts. It asks the operating system for a port number and is granted port number 52, 014. Now the process sends its ID (4, 978) and the port number to the control-block module to create an entry in the table. The module takes the first FREE entry and inserts the information received. The module does not allocate a queue at this moment because no user datagrams have arrived for this destination (see Table 11. 3). Table 11. 3 Control-block table after Example 3 TCP/IP Protocol Suite 80
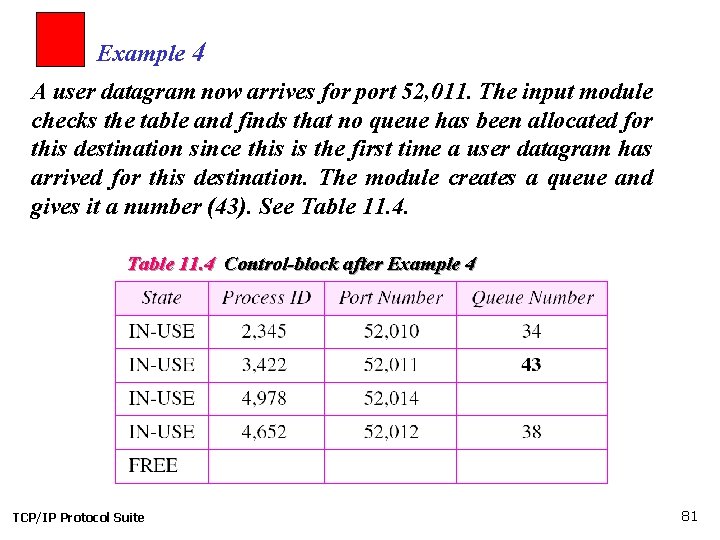
Example 4 A user datagram now arrives for port 52, 011. The input module checks the table and finds that no queue has been allocated for this destination since this is the first time a user datagram has arrived for this destination. The module creates a queue and gives it a number (43). See Table 11. 4 Control-block after Example 4 TCP/IP Protocol Suite 81
Example 5 After a few seconds, a user datagram arrives for port 52, 222. The input module checks the table and cannot find an entry for this destination. The user datagram is dropped and a request is made to ICMP to send an “unreachable port” message to the source. TCP/IP Protocol Suite 82
- Slides: 82