Chapter 10 Http netwk hannam ac kr HANNAM
![[그림 10. 1] 보안 목표와 관련된 공격의 분류 Http: //netwk. hannam. ac. kr HANNAM [그림 10. 1] 보안 목표와 관련된 공격의 분류 Http: //netwk. hannam. ac. kr HANNAM](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-7.jpg)
![[그림 10. 2] 모듈로 26에서 평문과 암호문의 표현 Http: //netwk. hannam. ac. kr HANNAM [그림 10. 2] 모듈로 26에서 평문과 암호문의 표현 Http: //netwk. hannam. ac. kr HANNAM](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-19.jpg)
![[그림 10. 6] 전치 암호 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 26 [그림 10. 6] 전치 암호 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 26](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-26.jpg)
![[그림 10. 8] 현대 블록 암호의 구성 요소 Http: //netwk. hannam. ac. kr HANNAM [그림 10. 8] 현대 블록 암호의 구성 요소 Http: //netwk. hannam. ac. kr HANNAM](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-30.jpg)
![[그림 10. 9] DES의 일반 구조 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 32 [그림 10. 9] DES의 일반 구조 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 32](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-32.jpg)
![[그림 10. 10] DES 함수 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 33 [그림 10. 10] DES 함수 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 33](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-33.jpg)
![[그림 10. 11] 키 생성 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 34 [그림 10. 11] 키 생성 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 34](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-34.jpg)
![[그림 10. 12] One-time pad Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 38 [그림 10. 12] One-time pad Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 38](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-38.jpg)
![[그림 10. 13] 비대칭-키 암호시스템에서의 잠금과 잠금해제 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY [그림 10. 13] 비대칭-키 암호시스템에서의 잠금과 잠금해제 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-41.jpg)
![[그림 10. 16] 메시지와 다이제스트 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 55 [그림 10. 16] 메시지와 다이제스트 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 55](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-55.jpg)
![[그림 10. 17] 메시지 인증 코드 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 58 [그림 10. 17] 메시지 인증 코드 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 58](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-58.jpg)
![[그림 10. 18] 디지털 서명 처리 과정 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY [그림 10. 18] 디지털 서명 처리 과정 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-62.jpg)
![[그림 10. 19] 다이제스트에 서명하기 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 63 [그림 10. 19] 다이제스트에 서명하기 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 63](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-63.jpg)
![[그림 10. 20] 부인봉쇄를 위해 신뢰할 수 있는 센터 이용 Http: //netwk. hannam. ac. [그림 10. 20] 부인봉쇄를 위해 신뢰할 수 있는 센터 이용 Http: //netwk. hannam. ac.](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-65.jpg)
![[그림 10. 21] 메시지 다이제스트에서 RSA 서명 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY [그림 10. 21] 메시지 다이제스트에서 RSA 서명 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-67.jpg)
![[그림 10. 25] 다중 KDC Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 76 [그림 10. 25] 다중 KDC Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 76](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-76.jpg)
![[그림 10. 26] KDC를 이용한 세션 키 생성 Http: //netwk. hannam. ac. kr HANNAM [그림 10. 26] KDC를 이용한 세션 키 생성 Http: //netwk. hannam. ac. kr HANNAM](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-78.jpg)
![[그림 10. 28] 인증 관리 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 83 [그림 10. 28] 인증 관리 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 83](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-83.jpg)
![[그림 10. 2] 평문 메시지 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 88 [그림 10. 2] 평문 메시지 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 88](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-88.jpg)
![[그림 10. 30] 인증된 메시지 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 89 [그림 10. 30] 인증된 메시지 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 89](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-89.jpg)
![[그림 10. 31] 압축된 메시지 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 90 [그림 10. 31] 압축된 메시지 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 90](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-90.jpg)
![[그림 10. 32] 기밀성을 갖는 메시지 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 92 [그림 10. 32] 기밀성을 갖는 메시지 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 92](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-92.jpg)
![[그림 10. 33] PGP에서 키 킹 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 93 [그림 10. 33] PGP에서 키 킹 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 93](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-93.jpg)
![[그림 10. 34] 신뢰 모델 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 96 [그림 10. 34] 신뢰 모델 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 96](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-96.jpg)
![[그림 10. 35] 서명된 데이터 콘텐츠 유형 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY [그림 10. 35] 서명된 데이터 콘텐츠 유형 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-98.jpg)
![[그림 10. 36] 봉합된 데이터 콘텐츠 유형 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY [그림 10. 36] 봉합된 데이터 콘텐츠 유형 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-99.jpg)
![[그림 10. 37] 다이제스트된 데이터 콘텐츠 유형 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY [그림 10. 37] 다이제스트된 데이터 콘텐츠 유형 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-100.jpg)
![[그림 10. 38] 인증된 데이터 콘텐츠 유형 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY [그림 10. 38] 인증된 데이터 콘텐츠 유형 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-101.jpg)
![[그림 10. 39] 인터넷 모델에서 SSL과 TLS의 위치 Http: //netwk. hannam. ac. kr HANNAM [그림 10. 39] 인터넷 모델에서 SSL과 TLS의 위치 Http: //netwk. hannam. ac. kr HANNAM](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-105.jpg)
![[그림 10. 40] 사전-마스터 비밀로부터 마스터 비밀의 계산 Http: //netwk. hannam. ac. kr HANNAM [그림 10. 40] 사전-마스터 비밀로부터 마스터 비밀의 계산 Http: //netwk. hannam. ac. kr HANNAM](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-109.jpg)
![[그림 10. 41] 마스터 비밀로부터 키 재료의 인증 관리 Http: //netwk. hannam. ac. kr [그림 10. 41] 마스터 비밀로부터 키 재료의 인증 관리 Http: //netwk. hannam. ac. kr](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-110.jpg)
![[그림 10. 42] 키 재료로부터 암호학적 비밀의 추출 Http: //netwk. hannam. ac. kr HANNAM [그림 10. 42] 키 재료로부터 암호학적 비밀의 추출 Http: //netwk. hannam. ac. kr HANNAM](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-111.jpg)
![[그림 10. 43] 4개의 SSL 프로토콜 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 113 [그림 10. 43] 4개의 SSL 프로토콜 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 113](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-113.jpg)
![[그림 10. 44] 핸드셰이크 프로토콜 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 114 [그림 10. 44] 핸드셰이크 프로토콜 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 114](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-114.jpg)
![[그림 10. 45] 레코드 프로토콜에 의해 행해지는 처리 과정 Http: //netwk. hannam. ac. kr [그림 10. 45] 레코드 프로토콜에 의해 행해지는 처리 과정 Http: //netwk. hannam. ac. kr](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-116.jpg)
![[그림 10. 46] IPSec 전송 모드 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 119 [그림 10. 46] IPSec 전송 모드 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 119](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-119.jpg)
![[그림 10. 47] 전송 모드 동작 과정 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY [그림 10. 47] 전송 모드 동작 과정 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-120.jpg)
![[그림 10. 48] IPSec 터널 모드 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 122 [그림 10. 48] IPSec 터널 모드 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 122](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-122.jpg)
![[그림 10. 49] 터널 모드 실제 동작 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY [그림 10. 49] 터널 모드 실제 동작 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-123.jpg)
![[그림 10. 51] 인증 헤더 프로토콜 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 126 [그림 10. 51] 인증 헤더 프로토콜 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 126](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-126.jpg)
![[그림 10. 52] ESP Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 128 [그림 10. 52] ESP Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 128](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-128.jpg)
![[표 10. 1] IPSec 서비스 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 131 [표 10. 1] IPSec 서비스 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 131](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-131.jpg)
![[그림 10. 53] 간단한 SA Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 133 [그림 10. 53] 간단한 SA Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 133](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-133.jpg)
![[그림 10. 54] SAD Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 134 [그림 10. 54] SAD Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 134](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-134.jpg)
![[그림 10. 55] SPD Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 135 [그림 10. 55] SPD Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 135](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-135.jpg)
![[그림 10. 56] 외부적 처리 절차 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 137 [그림 10. 56] 외부적 처리 절차 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 137](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-137.jpg)
![[그림 10. 57] 내부적 처리 절차 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 138 [그림 10. 57] 내부적 처리 절차 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 138](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-138.jpg)
![[그림 10. 58] IKE 구성 요소 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 140 [그림 10. 58] IKE 구성 요소 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 140](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-140.jpg)
![[그림 10. 59] 가상 사설 네트워크 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 142 [그림 10. 59] 가상 사설 네트워크 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 142](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-142.jpg)
![[그림 10. 60] 방화벽 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 144 [그림 10. 60] 방화벽 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 144](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-144.jpg)
![[그림 10. 61] 패킷 필터 방화벽 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 146 [그림 10. 61] 패킷 필터 방화벽 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 146](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-146.jpg)
![[그림 10. 62] 프록시 방화벽 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 148 [그림 10. 62] 프록시 방화벽 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 148](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-148.jpg)
- Slides: 151
Chapter 10 네트워크 보안 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 1
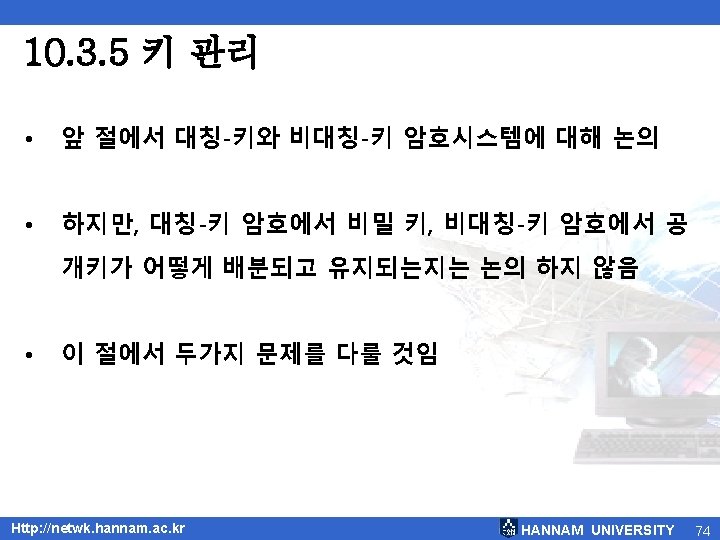
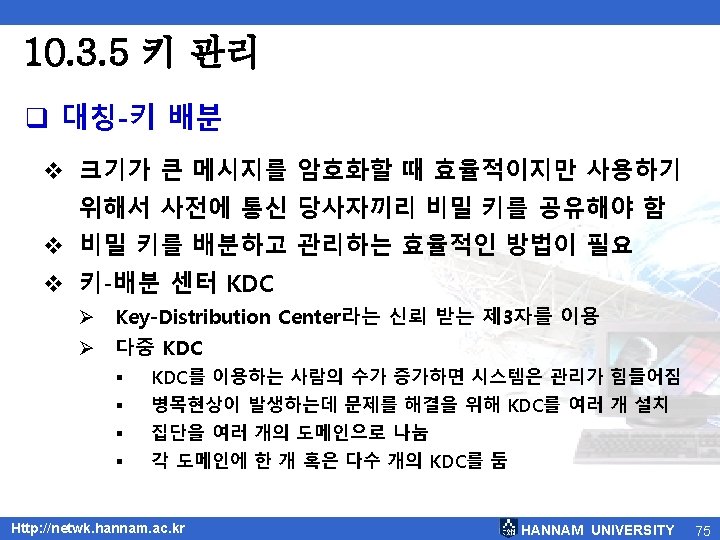
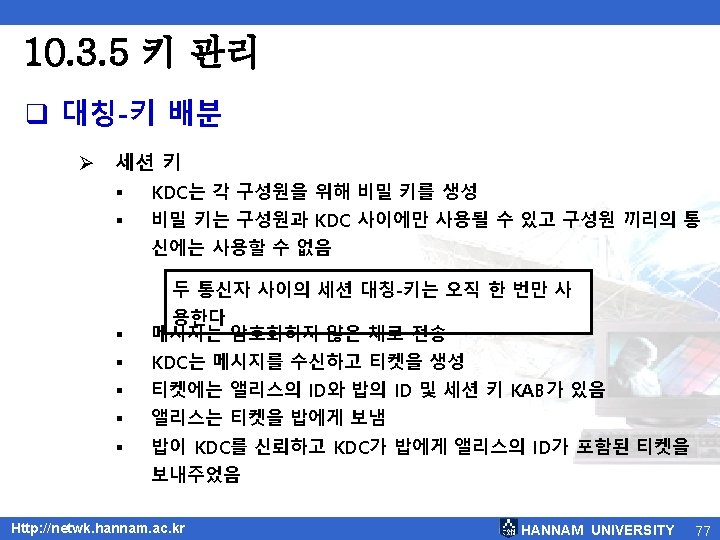
Chapter 10 : 목차 10. 1 개요 10. 2 기밀성 10. 3 보안의 또 다른 중요한 것들 10. 4 인터넷 보안 10. 5 방화벽 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 2
![그림 10 1 보안 목표와 관련된 공격의 분류 Http netwk hannam ac kr HANNAM [그림 10. 1] 보안 목표와 관련된 공격의 분류 Http: //netwk. hannam. ac. kr HANNAM](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-7.jpg)
[그림 10. 1] 보안 목표와 관련된 공격의 분류 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 7
![그림 10 2 모듈로 26에서 평문과 암호문의 표현 Http netwk hannam ac kr HANNAM [그림 10. 2] 모듈로 26에서 평문과 암호문의 표현 Http: //netwk. hannam. ac. kr HANNAM](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-19.jpg)
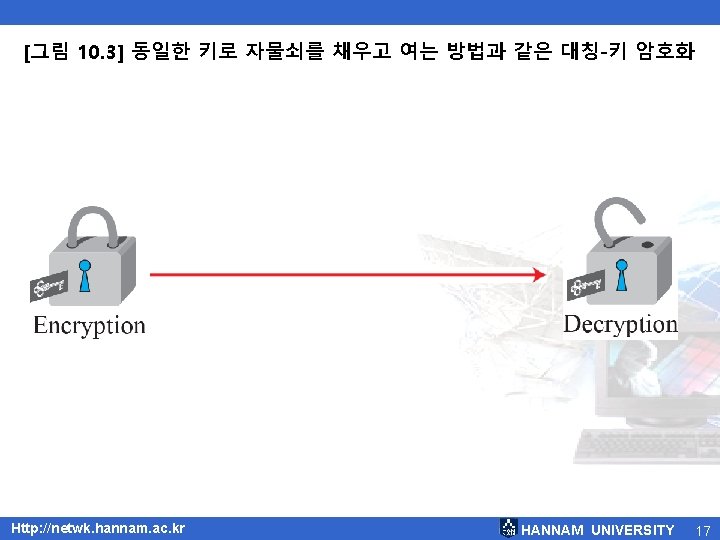
[그림 10. 2] 모듈로 26에서 평문과 암호문의 표현 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 19
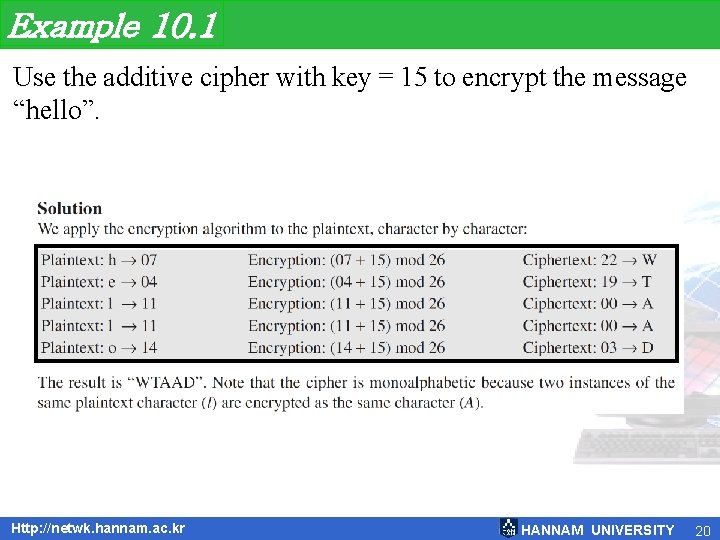
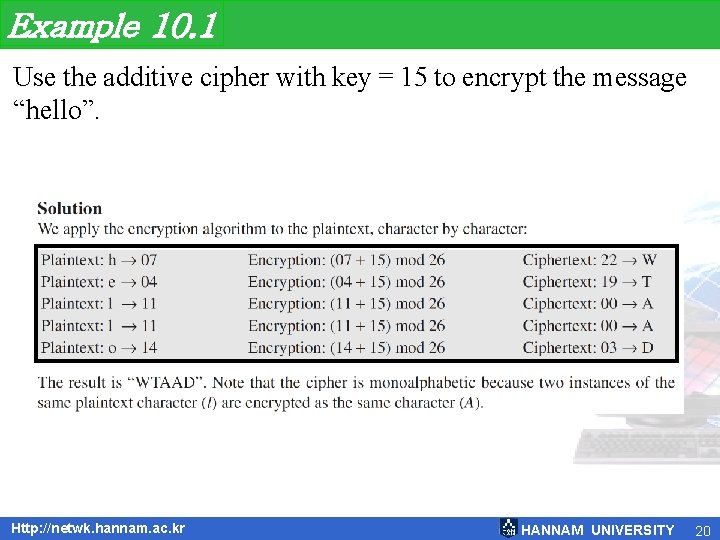
Example 10. 1 Use the additive cipher with key = 15 to encrypt the message “hello”. Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 20
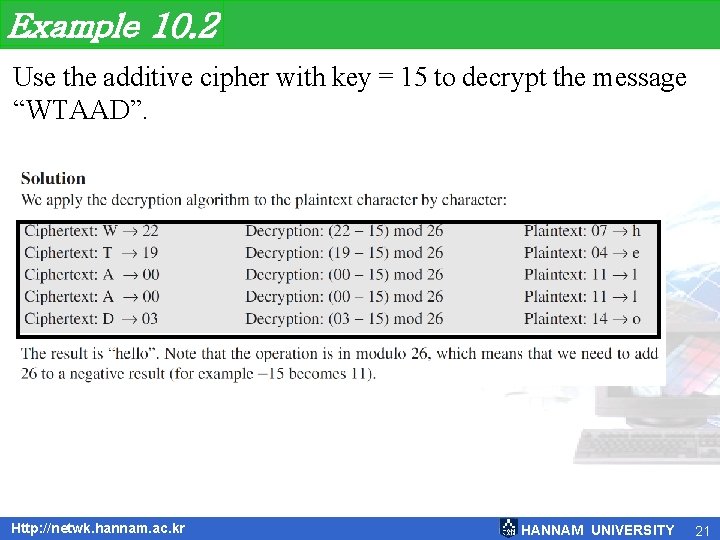
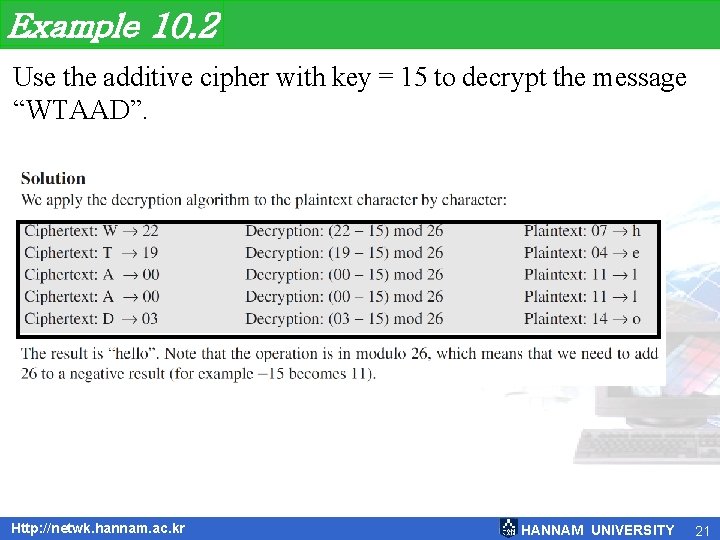
Example 10. 2 Use the additive cipher with key = 15 to decrypt the message “WTAAD”. Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 21
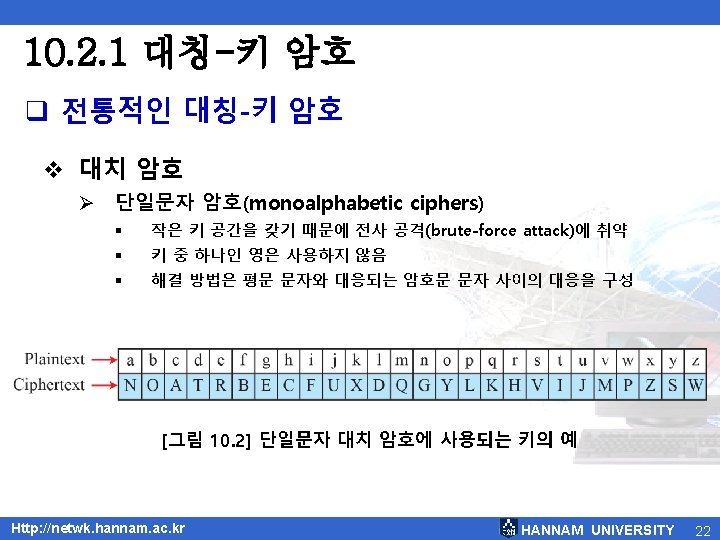
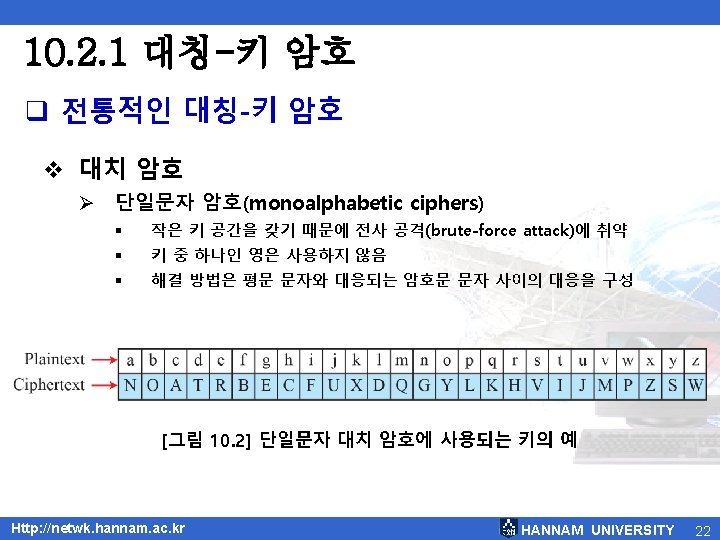
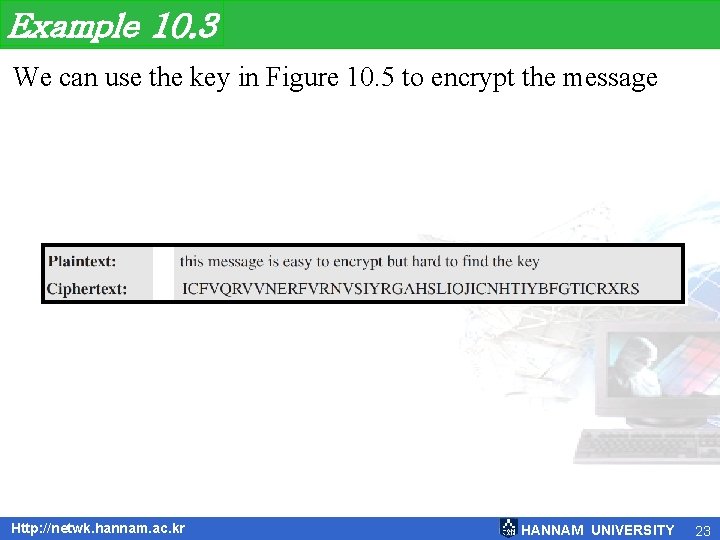
Example 10. 3 We can use the key in Figure 10. 5 to encrypt the message Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 23
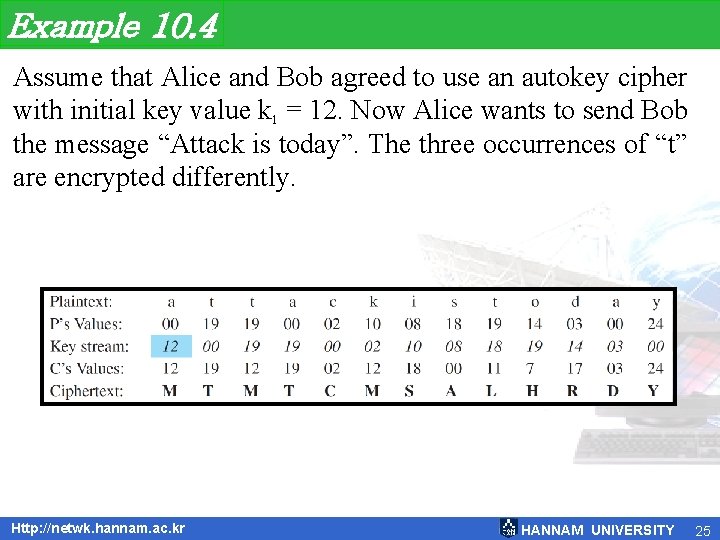
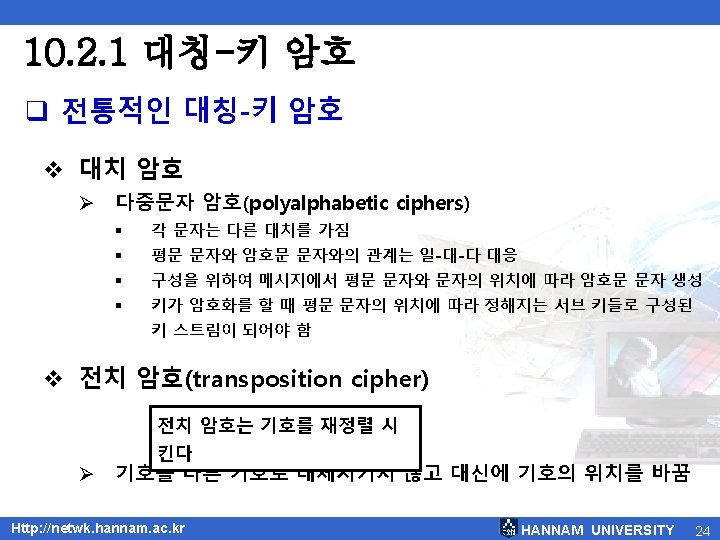
Example 10. 4 Assume that Alice and Bob agreed to use an autokey cipher with initial key value k 1 = 12. Now Alice wants to send Bob the message “Attack is today”. The three occurrences of “t” are encrypted differently. Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 25
![그림 10 6 전치 암호 Http netwk hannam ac kr HANNAM UNIVERSITY 26 [그림 10. 6] 전치 암호 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 26](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-26.jpg)
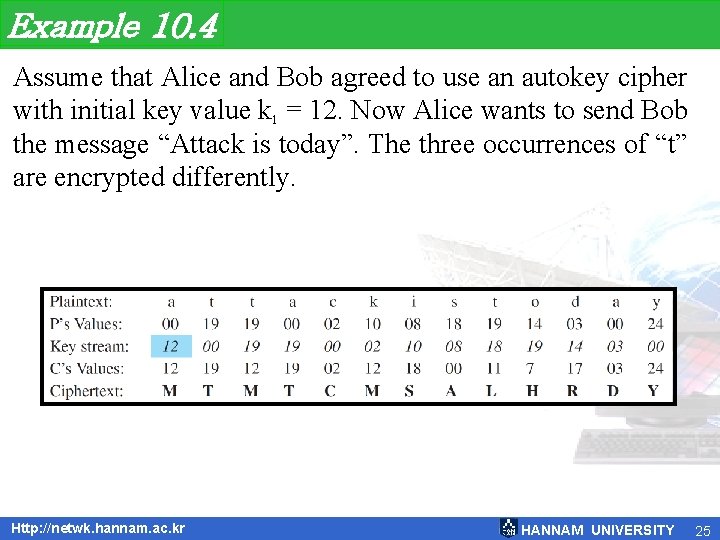
[그림 10. 6] 전치 암호 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 26
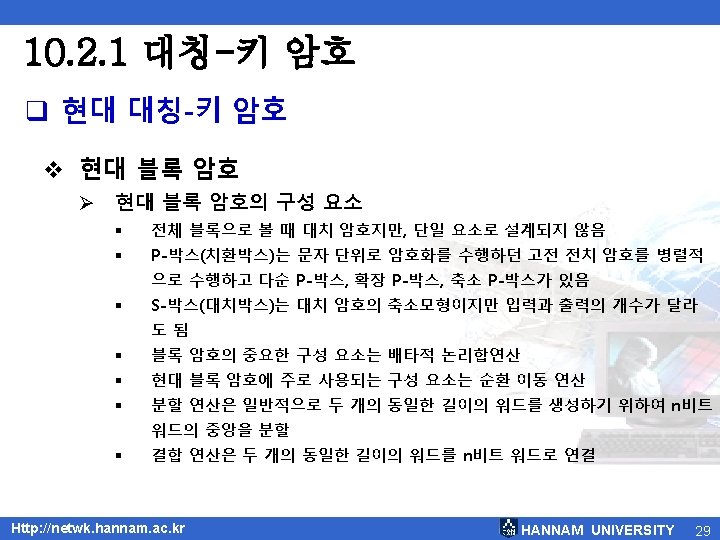
![그림 10 8 현대 블록 암호의 구성 요소 Http netwk hannam ac kr HANNAM [그림 10. 8] 현대 블록 암호의 구성 요소 Http: //netwk. hannam. ac. kr HANNAM](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-30.jpg)
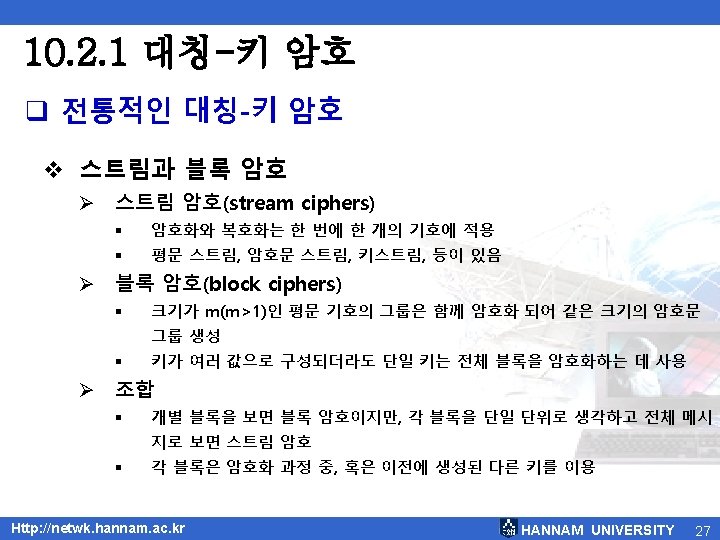
[그림 10. 8] 현대 블록 암호의 구성 요소 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 30
![그림 10 9 DES의 일반 구조 Http netwk hannam ac kr HANNAM UNIVERSITY 32 [그림 10. 9] DES의 일반 구조 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 32](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-32.jpg)
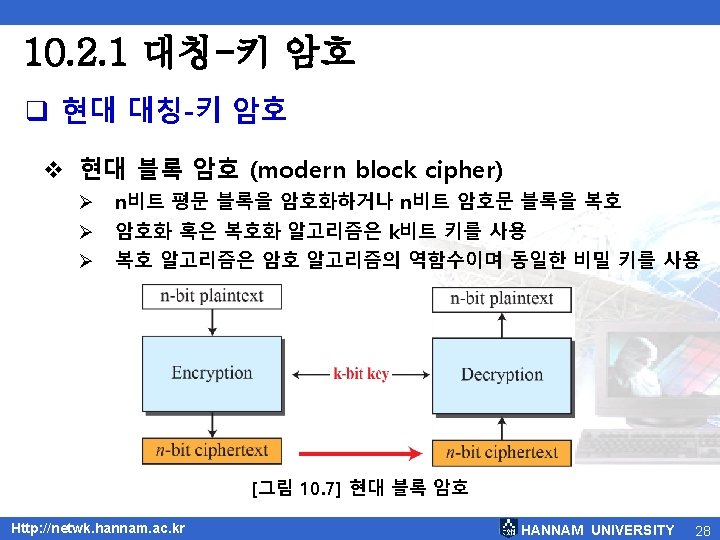
[그림 10. 9] DES의 일반 구조 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 32
![그림 10 10 DES 함수 Http netwk hannam ac kr HANNAM UNIVERSITY 33 [그림 10. 10] DES 함수 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 33](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-33.jpg)
[그림 10. 10] DES 함수 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 33
![그림 10 11 키 생성 Http netwk hannam ac kr HANNAM UNIVERSITY 34 [그림 10. 11] 키 생성 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 34](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-34.jpg)
[그림 10. 11] 키 생성 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 34
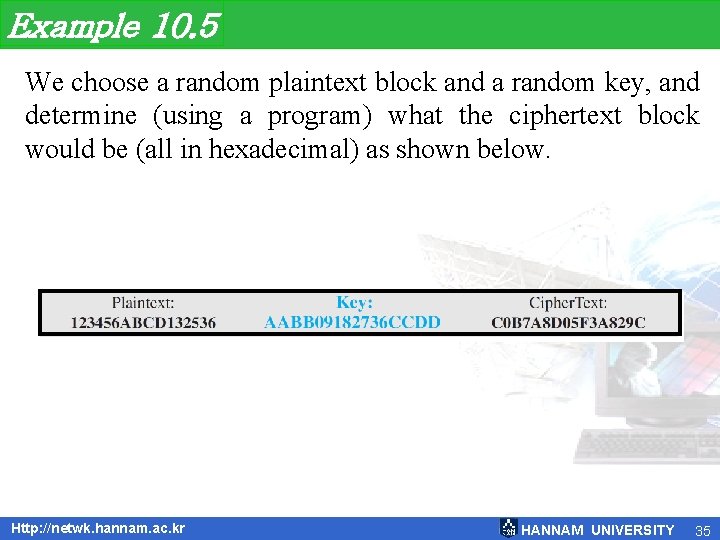
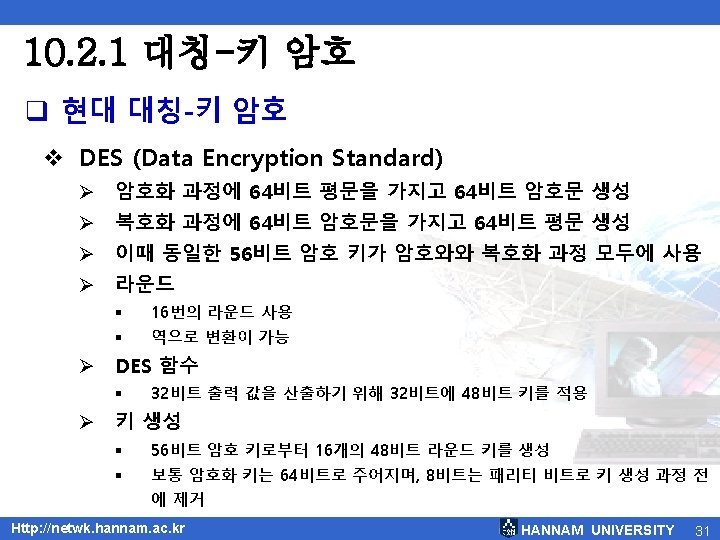
Example 10. 5 We choose a random plaintext block and a random key, and determine (using a program) what the ciphertext block would be (all in hexadecimal) as shown below. Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 35
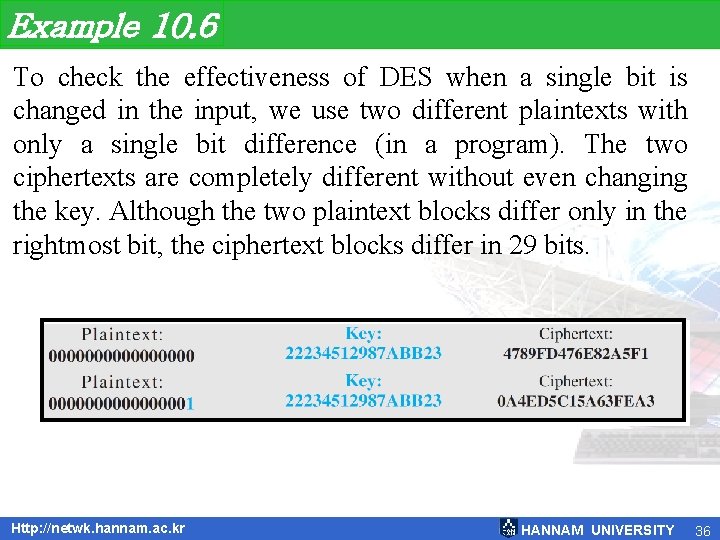
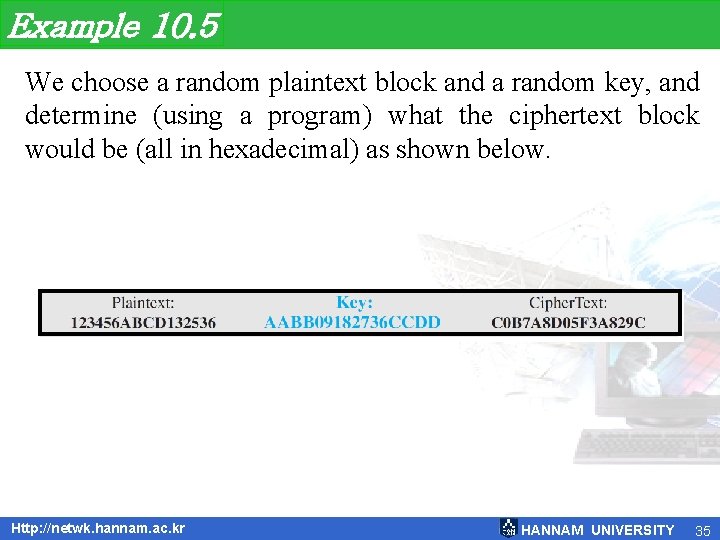
Example 10. 6 To check the effectiveness of DES when a single bit is changed in the input, we use two different plaintexts with only a single bit difference (in a program). The two ciphertexts are completely different without even changing the key. Although the two plaintext blocks differ only in the rightmost bit, the ciphertext blocks differ in 29 bits. Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 36
![그림 10 12 Onetime pad Http netwk hannam ac kr HANNAM UNIVERSITY 38 [그림 10. 12] One-time pad Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 38](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-38.jpg)
[그림 10. 12] One-time pad Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 38
![그림 10 13 비대칭키 암호시스템에서의 잠금과 잠금해제 Http netwk hannam ac kr HANNAM UNIVERSITY [그림 10. 13] 비대칭-키 암호시스템에서의 잠금과 잠금해제 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-41.jpg)
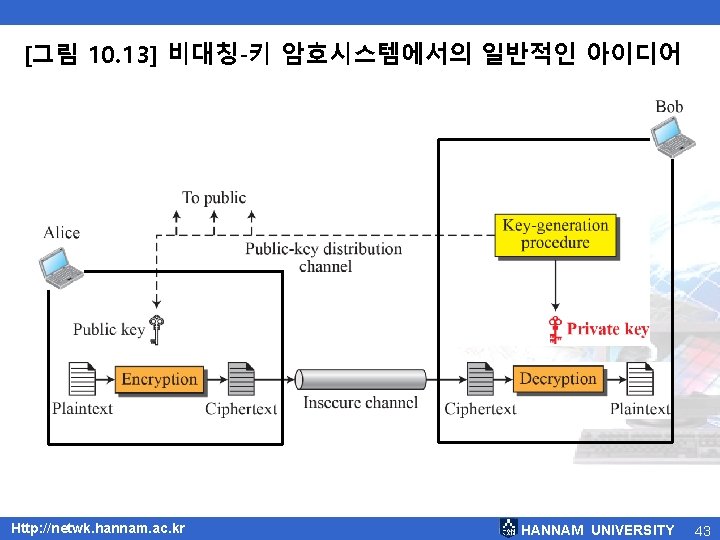
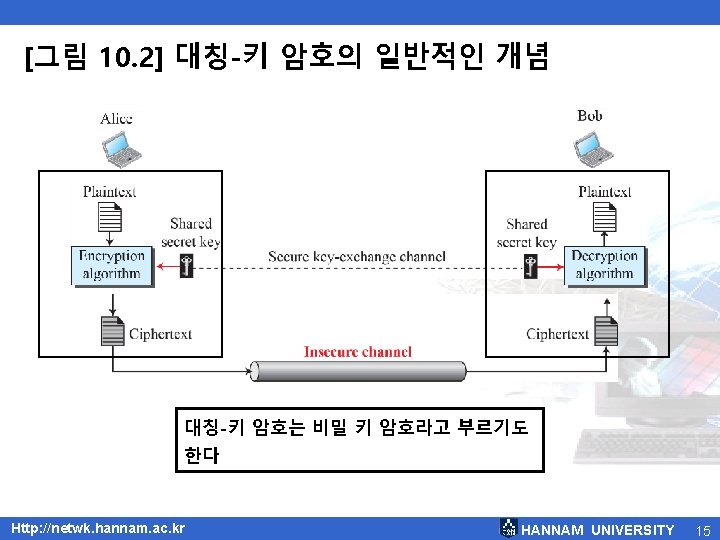
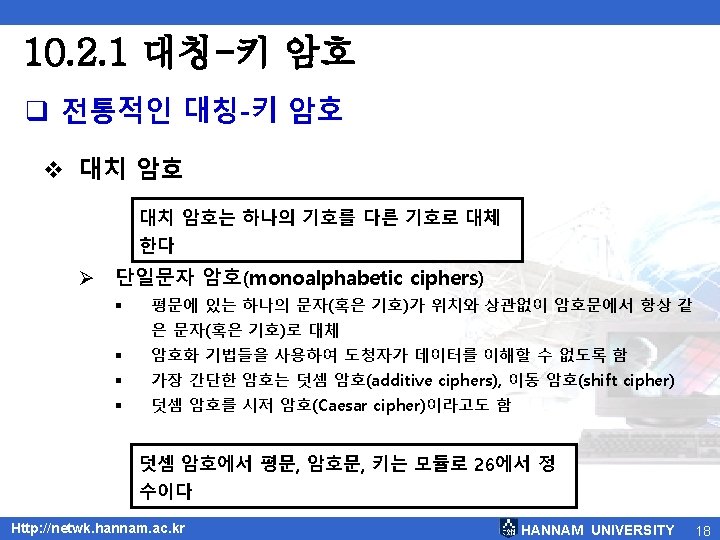
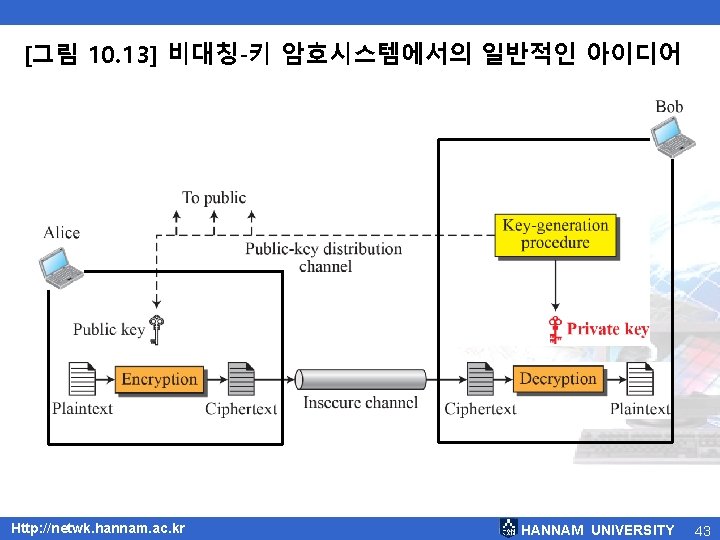
[그림 10. 13] 비대칭-키 암호시스템에서의 잠금과 잠금해제 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 41
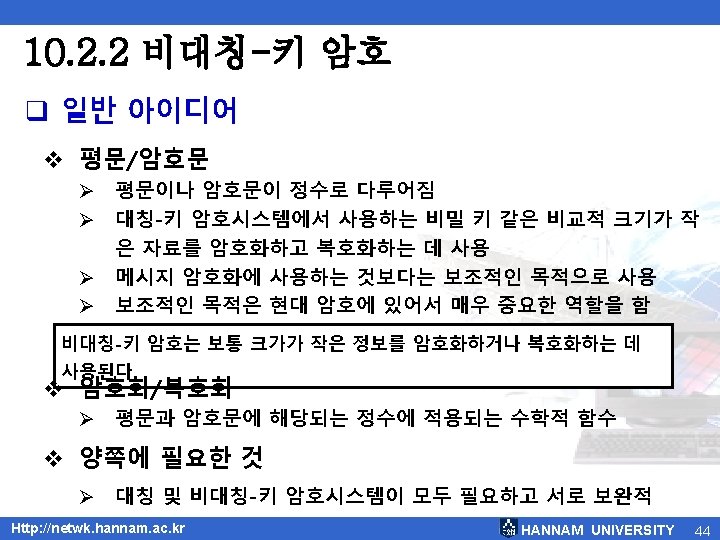
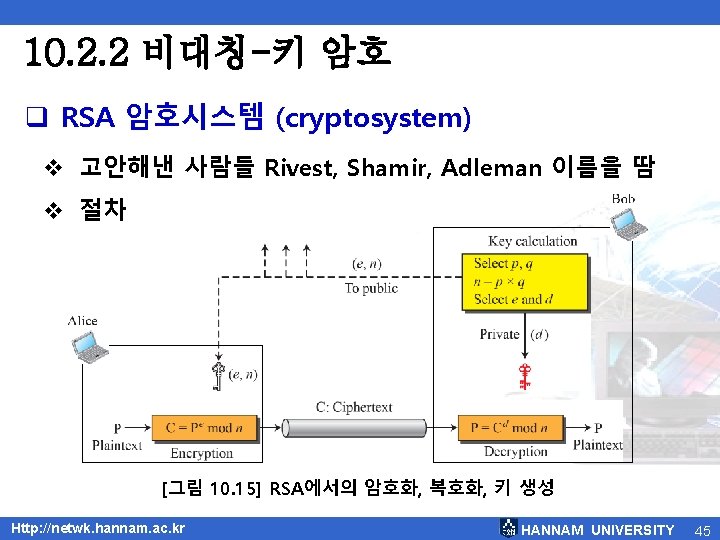
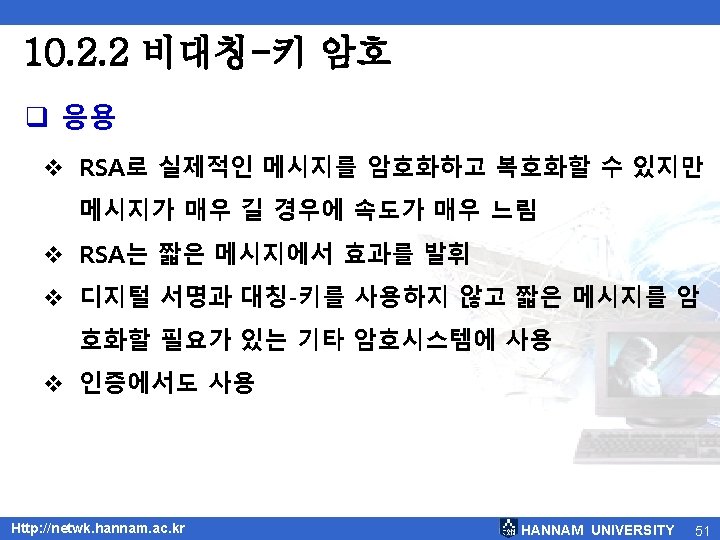
10. 2. 2 비대칭-키 암호 q RSA 암호시스템 (cryptosystem) v 고안해낸 사람들 Rivest, Shamir, Adleman 이름을 땀 v 절차 [그림 10. 15] RSA에서의 암호화, 복호화, 키 생성 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 45
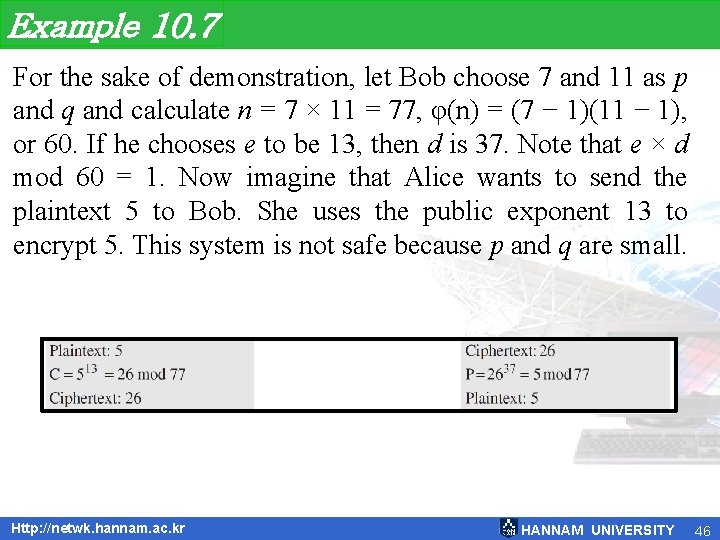
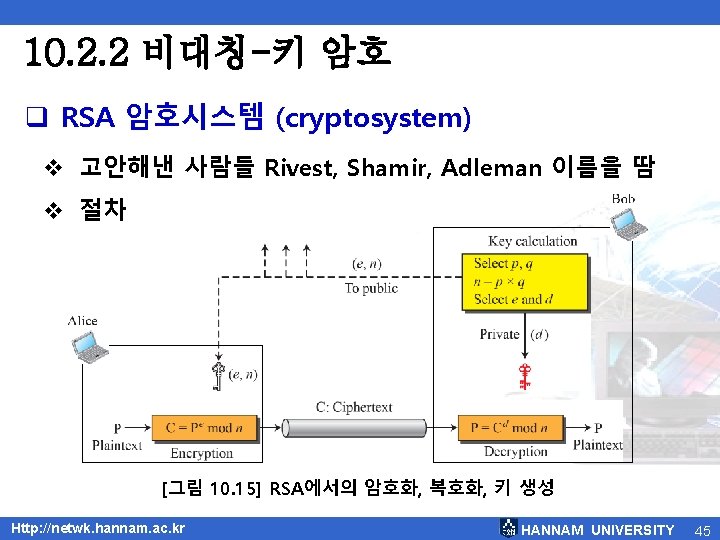
Example 10. 7 For the sake of demonstration, let Bob choose 7 and 11 as p and q and calculate n = 7 × 11 = 77, φ(n) = (7 − 1)(11 − 1), or 60. If he chooses e to be 13, then d is 37. Note that e × d mod 60 = 1. Now imagine that Alice wants to send the plaintext 5 to Bob. She uses the public exponent 13 to encrypt 5. This system is not safe because p and q are small. Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 46
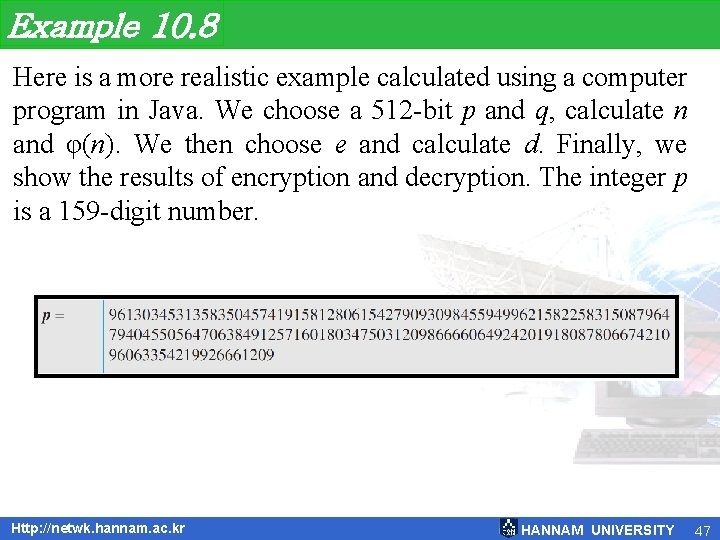
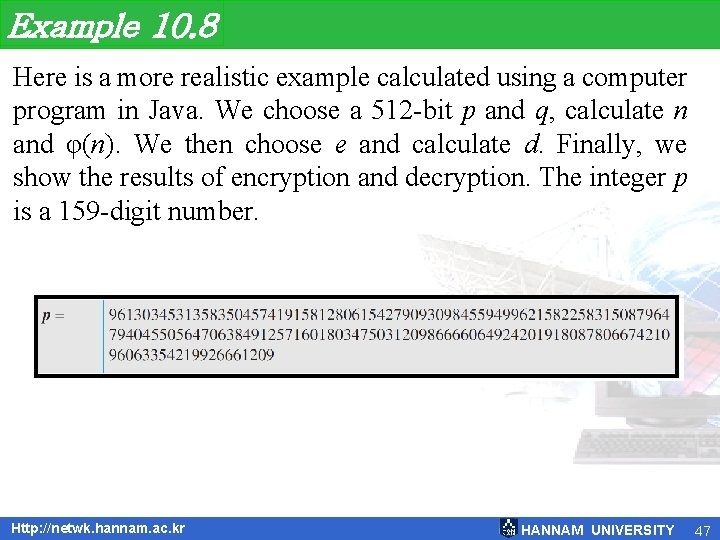
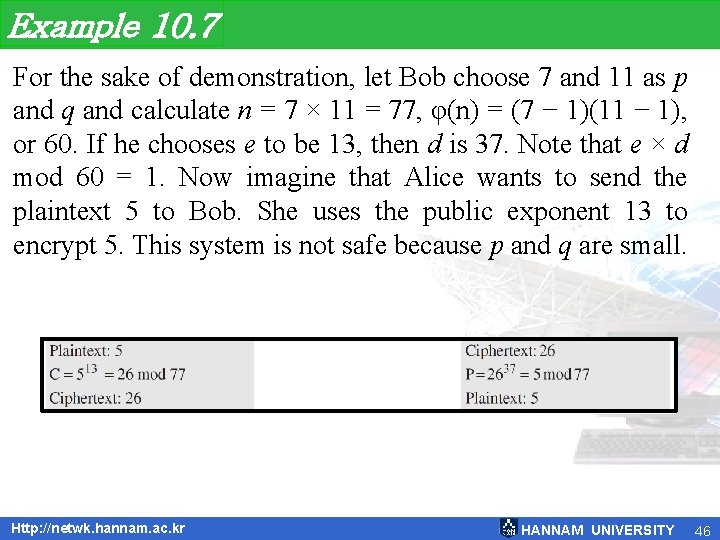
Example 10. 8 Here is a more realistic example calculated using a computer program in Java. We choose a 512 -bit p and q, calculate n and φ(n). We then choose e and calculate d. Finally, we show the results of encryption and decryption. The integer p is a 159 -digit number. Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 47
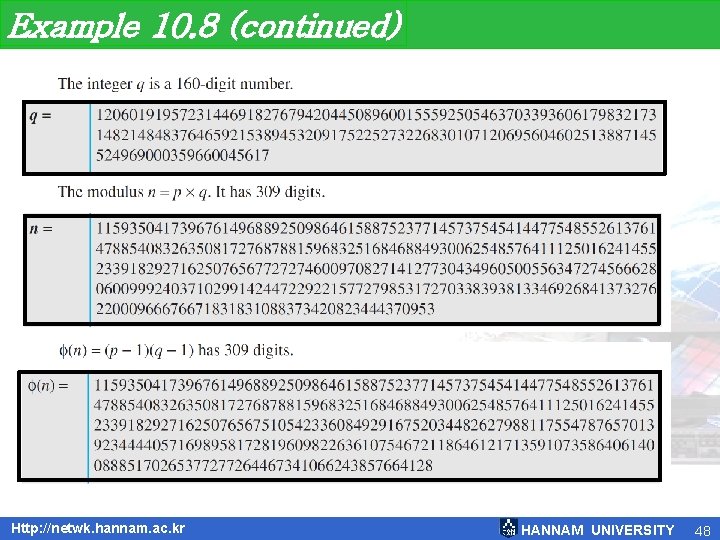
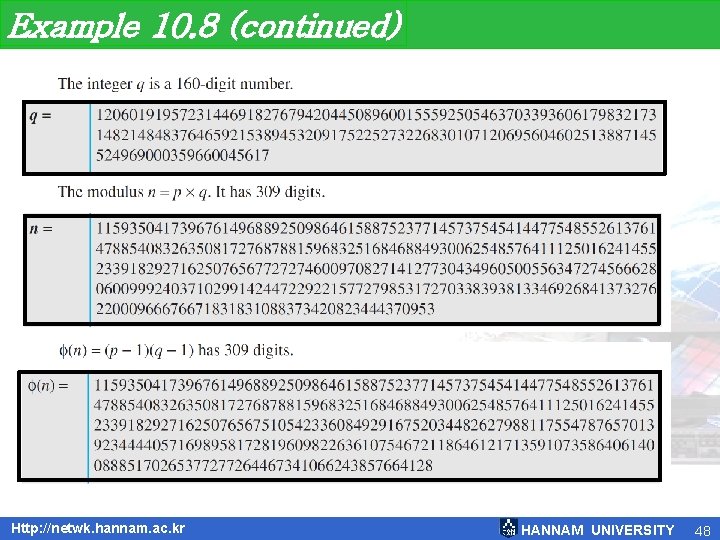
Example 10. 8 (continued) Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 48
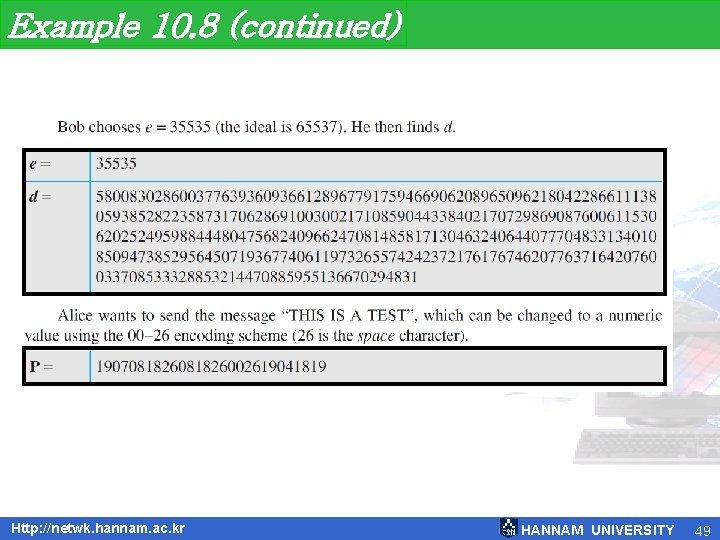
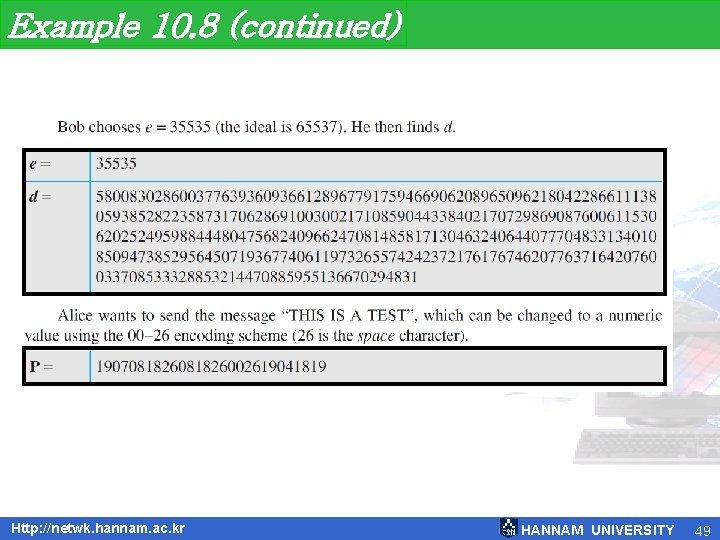
Example 10. 8 (continued) Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 49
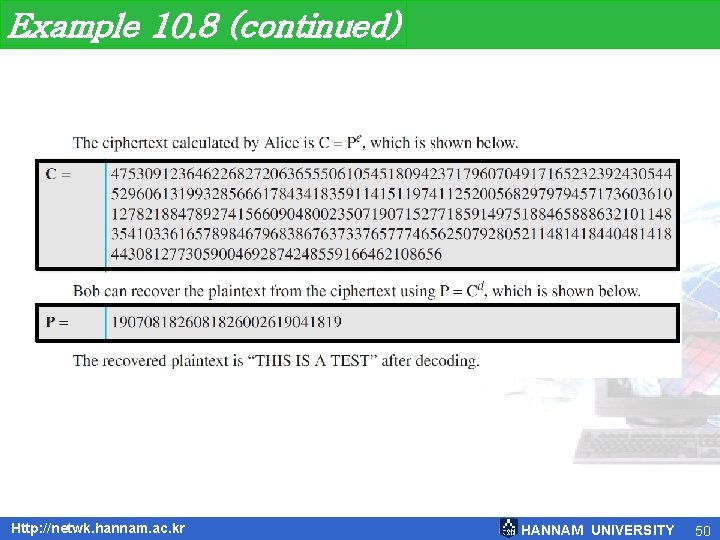
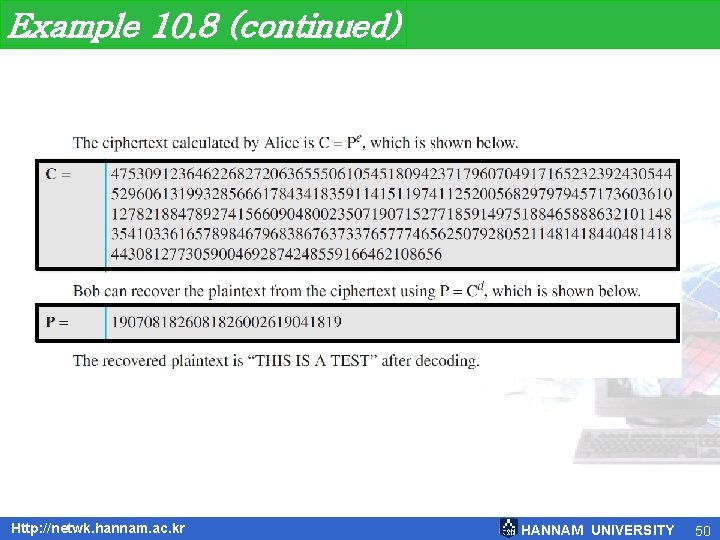
Example 10. 8 (continued) Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 50
![그림 10 16 메시지와 다이제스트 Http netwk hannam ac kr HANNAM UNIVERSITY 55 [그림 10. 16] 메시지와 다이제스트 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 55](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-55.jpg)
[그림 10. 16] 메시지와 다이제스트 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 55
![그림 10 17 메시지 인증 코드 Http netwk hannam ac kr HANNAM UNIVERSITY 58 [그림 10. 17] 메시지 인증 코드 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 58](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-58.jpg)
[그림 10. 17] 메시지 인증 코드 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 58
![그림 10 18 디지털 서명 처리 과정 Http netwk hannam ac kr HANNAM UNIVERSITY [그림 10. 18] 디지털 서명 처리 과정 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-62.jpg)
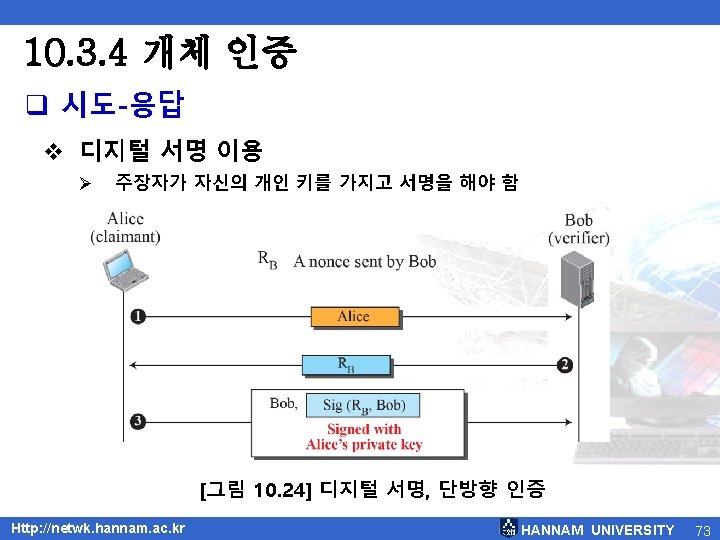
[그림 10. 18] 디지털 서명 처리 과정 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 62
![그림 10 19 다이제스트에 서명하기 Http netwk hannam ac kr HANNAM UNIVERSITY 63 [그림 10. 19] 다이제스트에 서명하기 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 63](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-63.jpg)
[그림 10. 19] 다이제스트에 서명하기 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 63
![그림 10 20 부인봉쇄를 위해 신뢰할 수 있는 센터 이용 Http netwk hannam ac [그림 10. 20] 부인봉쇄를 위해 신뢰할 수 있는 센터 이용 Http: //netwk. hannam. ac.](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-65.jpg)
[그림 10. 20] 부인봉쇄를 위해 신뢰할 수 있는 센터 이용 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 65
![그림 10 21 메시지 다이제스트에서 RSA 서명 Http netwk hannam ac kr HANNAM UNIVERSITY [그림 10. 21] 메시지 다이제스트에서 RSA 서명 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-67.jpg)
[그림 10. 21] 메시지 다이제스트에서 RSA 서명 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 67
![그림 10 25 다중 KDC Http netwk hannam ac kr HANNAM UNIVERSITY 76 [그림 10. 25] 다중 KDC Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 76](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-76.jpg)
[그림 10. 25] 다중 KDC Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 76
![그림 10 26 KDC를 이용한 세션 키 생성 Http netwk hannam ac kr HANNAM [그림 10. 26] KDC를 이용한 세션 키 생성 Http: //netwk. hannam. ac. kr HANNAM](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-78.jpg)
[그림 10. 26] KDC를 이용한 세션 키 생성 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 78
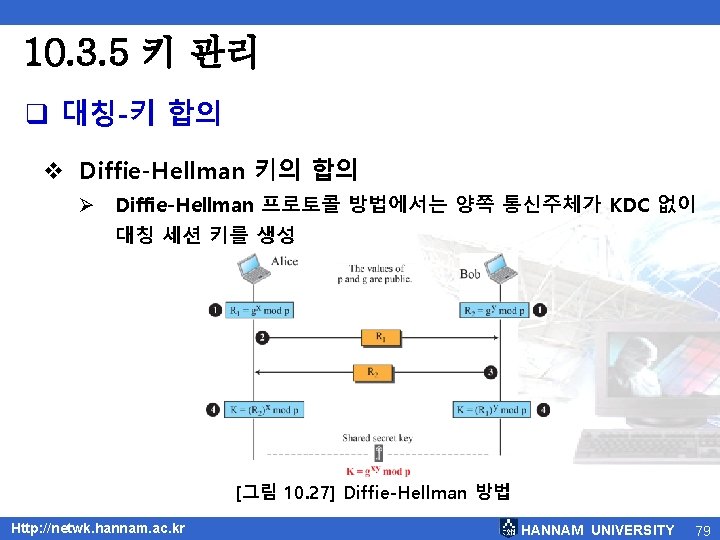
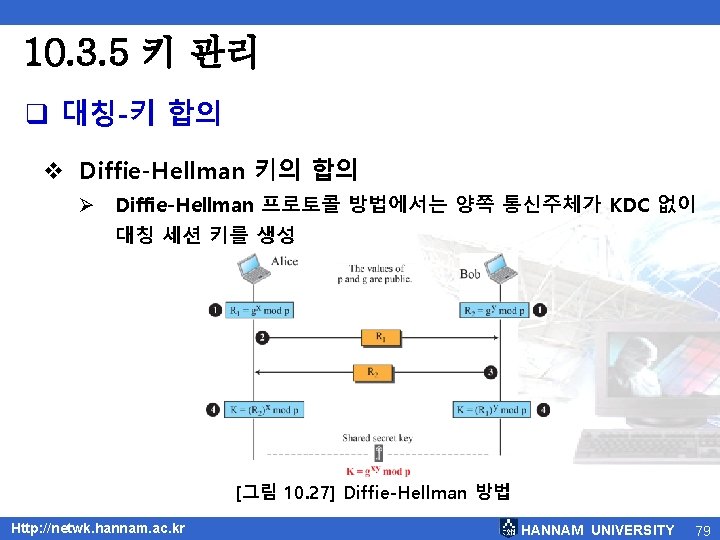
10. 3. 5 키 관리 q 대칭-키 합의 v Diffie-Hellman 키의 합의 Ø Diffie-Hellman 프로토콜 방법에서는 양쪽 통신주체가 KDC 없이 대칭 세션 키를 생성 [그림 10. 27] Diffie-Hellman 방법 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 79
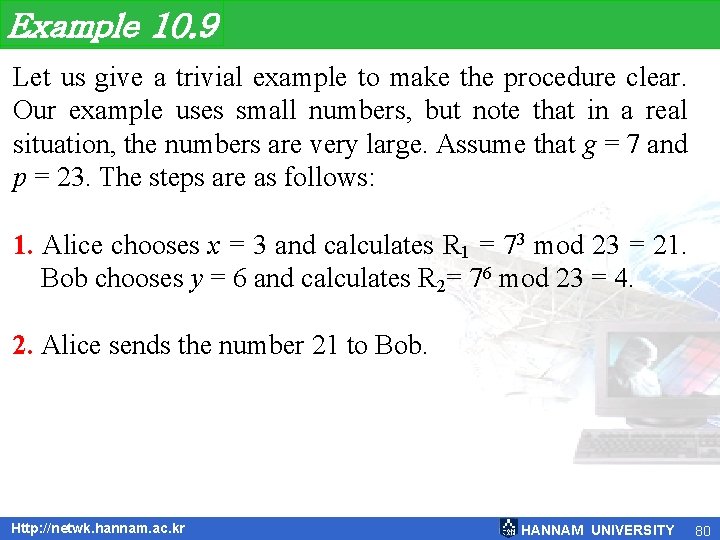
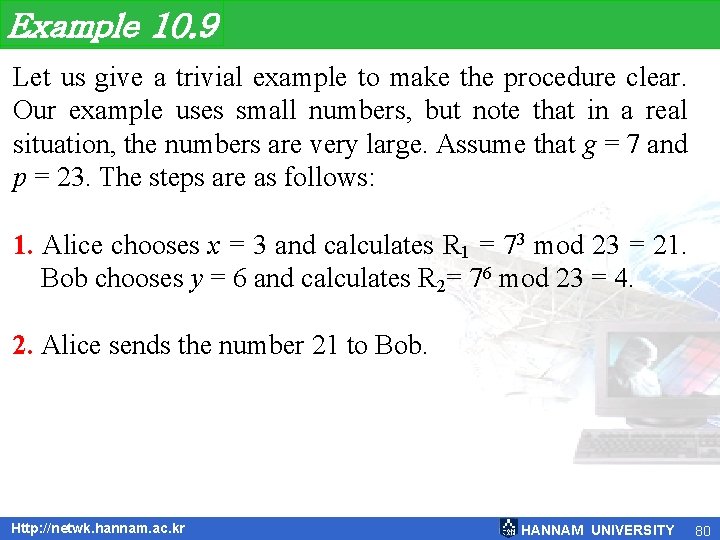
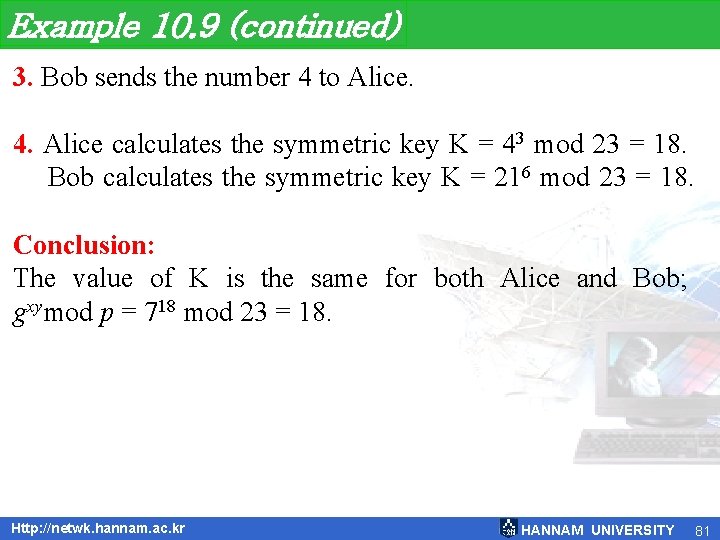
Example 10. 9 Let us give a trivial example to make the procedure clear. Our example uses small numbers, but note that in a real situation, the numbers are very large. Assume that g = 7 and p = 23. The steps are as follows: 1. Alice chooses x = 3 and calculates R 1 = 73 mod 23 = 21. Bob chooses y = 6 and calculates R 2= 76 mod 23 = 4. 2. Alice sends the number 21 to Bob. Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 80
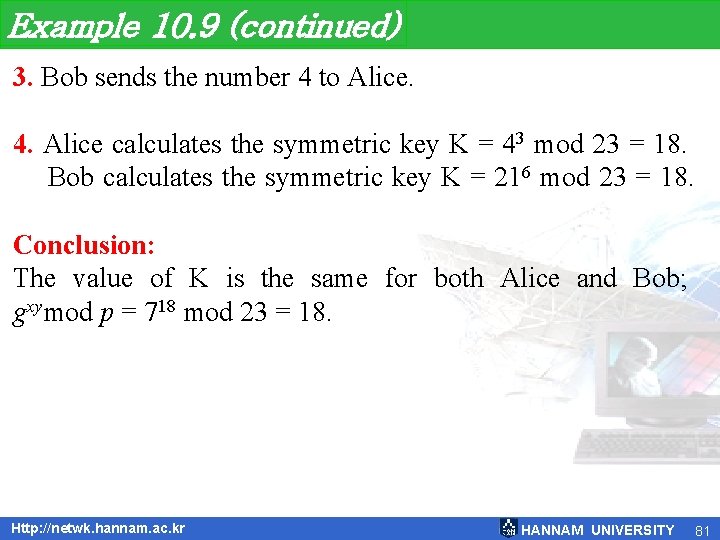
Example 10. 9 (continued) 3. Bob sends the number 4 to Alice. 4. Alice calculates the symmetric key K = 43 mod 23 = 18. Bob calculates the symmetric key K = 216 mod 23 = 18. Conclusion: The value of K is the same for both Alice and Bob; gxymod p = 718 mod 23 = 18. Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 81
![그림 10 28 인증 관리 Http netwk hannam ac kr HANNAM UNIVERSITY 83 [그림 10. 28] 인증 관리 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 83](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-83.jpg)
[그림 10. 28] 인증 관리 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 83
10. 4. 1 응용 계층 보안 • 이 절은 전자우편에서 보안을 제공하는 두 가지 프로토콜 을 설명 • PGP (Pretty Good Privacy) • S/MIME(Secure/Multiputpose Internet Mail Extension) Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 85
![그림 10 2 평문 메시지 Http netwk hannam ac kr HANNAM UNIVERSITY 88 [그림 10. 2] 평문 메시지 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 88](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-88.jpg)
[그림 10. 2] 평문 메시지 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 88
![그림 10 30 인증된 메시지 Http netwk hannam ac kr HANNAM UNIVERSITY 89 [그림 10. 30] 인증된 메시지 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 89](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-89.jpg)
[그림 10. 30] 인증된 메시지 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 89
![그림 10 31 압축된 메시지 Http netwk hannam ac kr HANNAM UNIVERSITY 90 [그림 10. 31] 압축된 메시지 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 90](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-90.jpg)
[그림 10. 31] 압축된 메시지 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 90
![그림 10 32 기밀성을 갖는 메시지 Http netwk hannam ac kr HANNAM UNIVERSITY 92 [그림 10. 32] 기밀성을 갖는 메시지 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 92](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-92.jpg)
[그림 10. 32] 기밀성을 갖는 메시지 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 92
![그림 10 33 PGP에서 키 킹 Http netwk hannam ac kr HANNAM UNIVERSITY 93 [그림 10. 33] PGP에서 키 킹 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 93](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-93.jpg)
[그림 10. 33] PGP에서 키 킹 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 93
![그림 10 34 신뢰 모델 Http netwk hannam ac kr HANNAM UNIVERSITY 96 [그림 10. 34] 신뢰 모델 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 96](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-96.jpg)
[그림 10. 34] 신뢰 모델 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 96
![그림 10 35 서명된 데이터 콘텐츠 유형 Http netwk hannam ac kr HANNAM UNIVERSITY [그림 10. 35] 서명된 데이터 콘텐츠 유형 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-98.jpg)
[그림 10. 35] 서명된 데이터 콘텐츠 유형 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 98
![그림 10 36 봉합된 데이터 콘텐츠 유형 Http netwk hannam ac kr HANNAM UNIVERSITY [그림 10. 36] 봉합된 데이터 콘텐츠 유형 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-99.jpg)
[그림 10. 36] 봉합된 데이터 콘텐츠 유형 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 99
![그림 10 37 다이제스트된 데이터 콘텐츠 유형 Http netwk hannam ac kr HANNAM UNIVERSITY [그림 10. 37] 다이제스트된 데이터 콘텐츠 유형 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-100.jpg)
[그림 10. 37] 다이제스트된 데이터 콘텐츠 유형 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 100
![그림 10 38 인증된 데이터 콘텐츠 유형 Http netwk hannam ac kr HANNAM UNIVERSITY [그림 10. 38] 인증된 데이터 콘텐츠 유형 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-101.jpg)
[그림 10. 38] 인증된 데이터 콘텐츠 유형 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 101
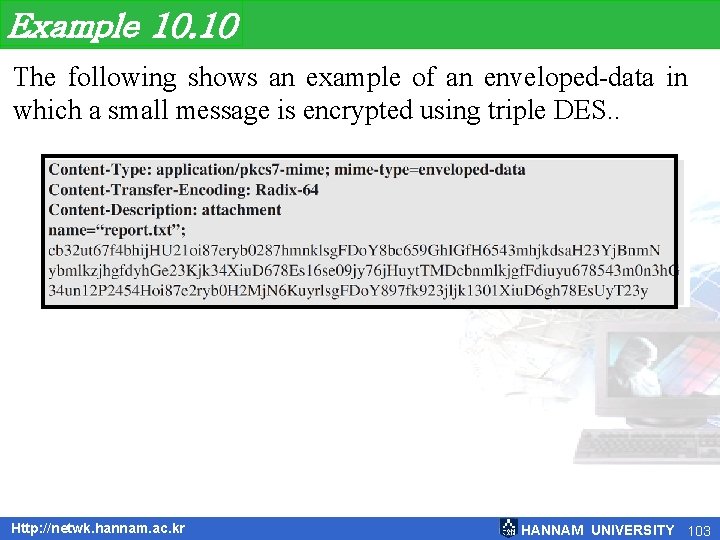
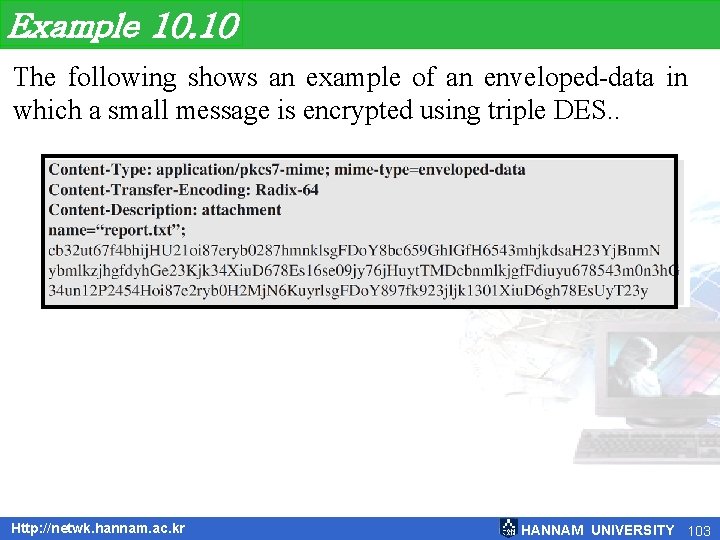
Example 10. 10 The following shows an example of an enveloped-data in which a small message is encrypted using triple DES. . Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 103
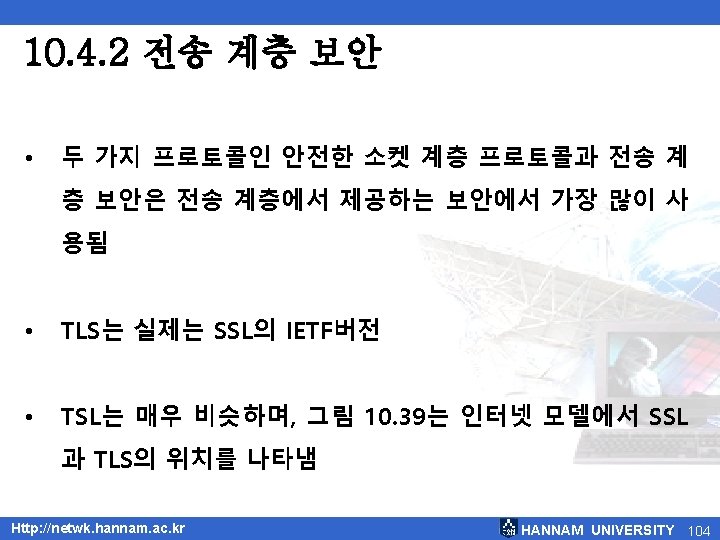
![그림 10 39 인터넷 모델에서 SSL과 TLS의 위치 Http netwk hannam ac kr HANNAM [그림 10. 39] 인터넷 모델에서 SSL과 TLS의 위치 Http: //netwk. hannam. ac. kr HANNAM](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-105.jpg)
[그림 10. 39] 인터넷 모델에서 SSL과 TLS의 위치 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 105
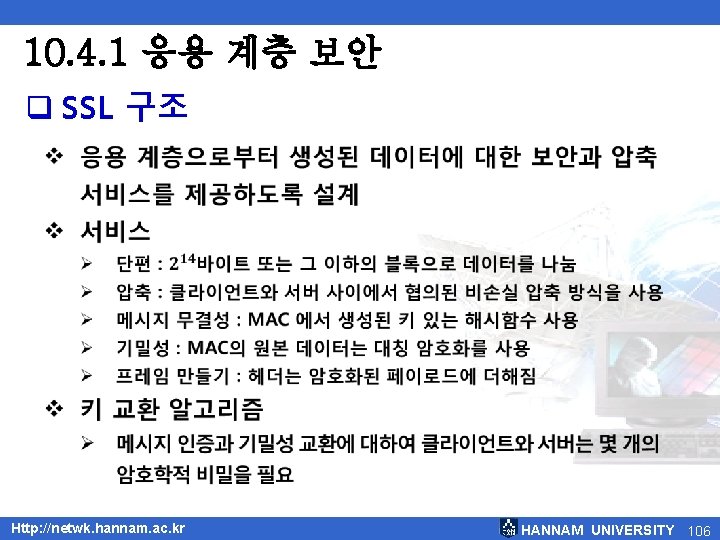
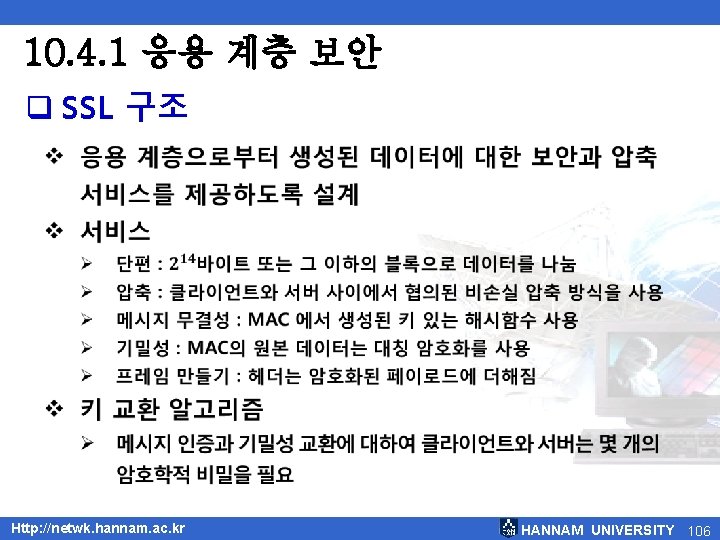
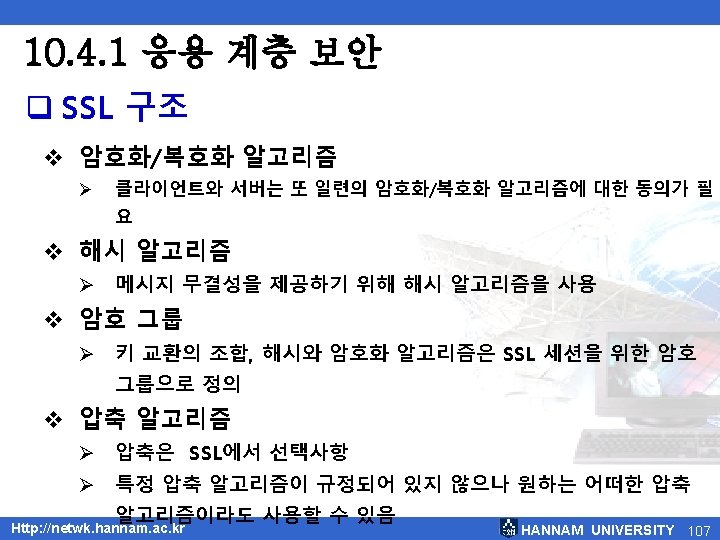
10. 4. 1 응용 계층 보안 q SSL 구조 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 106
![그림 10 40 사전마스터 비밀로부터 마스터 비밀의 계산 Http netwk hannam ac kr HANNAM [그림 10. 40] 사전-마스터 비밀로부터 마스터 비밀의 계산 Http: //netwk. hannam. ac. kr HANNAM](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-109.jpg)
[그림 10. 40] 사전-마스터 비밀로부터 마스터 비밀의 계산 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 109
![그림 10 41 마스터 비밀로부터 키 재료의 인증 관리 Http netwk hannam ac kr [그림 10. 41] 마스터 비밀로부터 키 재료의 인증 관리 Http: //netwk. hannam. ac. kr](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-110.jpg)
[그림 10. 41] 마스터 비밀로부터 키 재료의 인증 관리 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 110
![그림 10 42 키 재료로부터 암호학적 비밀의 추출 Http netwk hannam ac kr HANNAM [그림 10. 42] 키 재료로부터 암호학적 비밀의 추출 Http: //netwk. hannam. ac. kr HANNAM](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-111.jpg)
[그림 10. 42] 키 재료로부터 암호학적 비밀의 추출 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 111
![그림 10 43 4개의 SSL 프로토콜 Http netwk hannam ac kr HANNAM UNIVERSITY 113 [그림 10. 43] 4개의 SSL 프로토콜 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 113](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-113.jpg)
[그림 10. 43] 4개의 SSL 프로토콜 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 113
![그림 10 44 핸드셰이크 프로토콜 Http netwk hannam ac kr HANNAM UNIVERSITY 114 [그림 10. 44] 핸드셰이크 프로토콜 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 114](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-114.jpg)
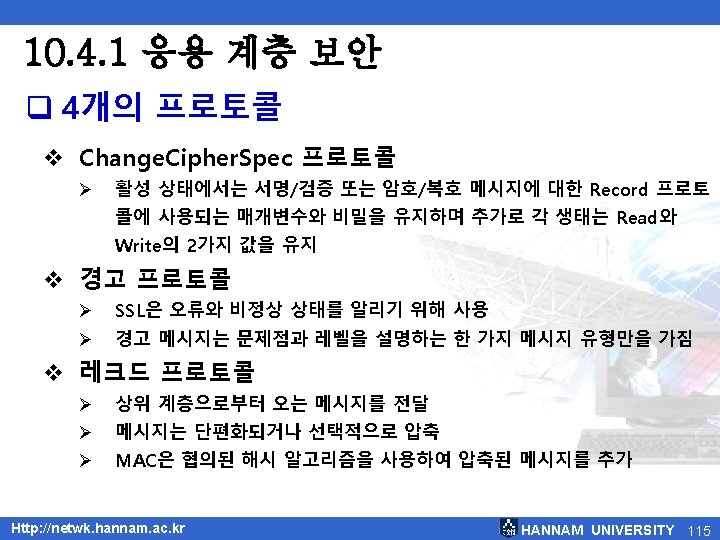
[그림 10. 44] 핸드셰이크 프로토콜 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 114
![그림 10 45 레코드 프로토콜에 의해 행해지는 처리 과정 Http netwk hannam ac kr [그림 10. 45] 레코드 프로토콜에 의해 행해지는 처리 과정 Http: //netwk. hannam. ac. kr](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-116.jpg)
[그림 10. 45] 레코드 프로토콜에 의해 행해지는 처리 과정 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 116
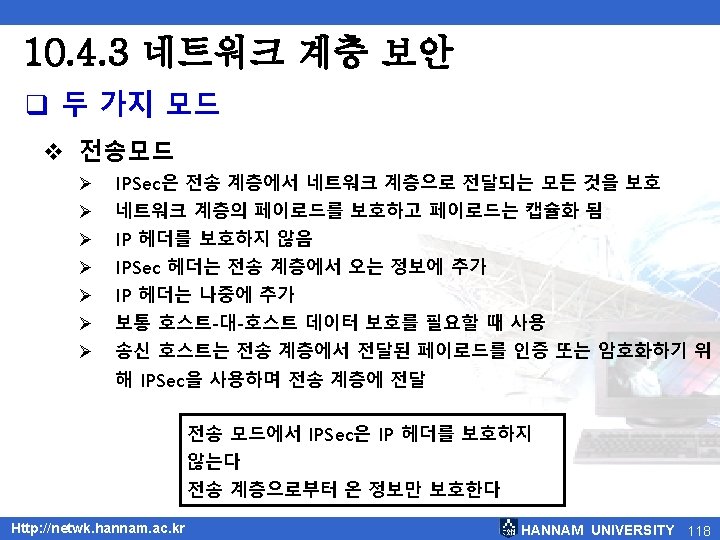
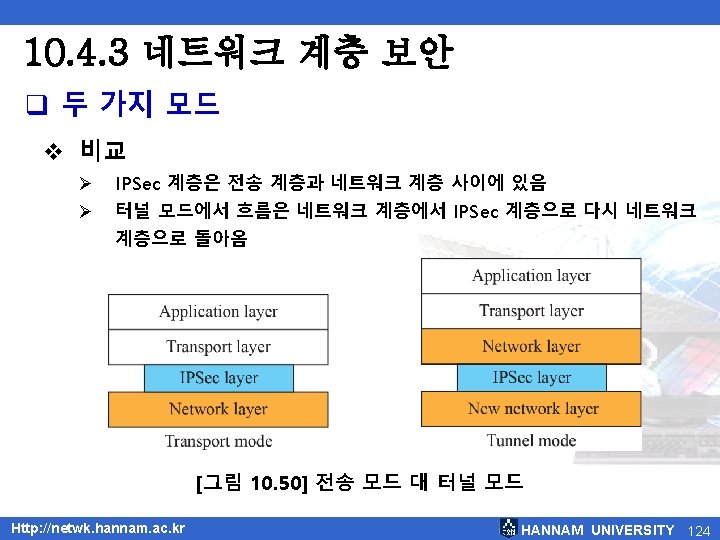
![그림 10 46 IPSec 전송 모드 Http netwk hannam ac kr HANNAM UNIVERSITY 119 [그림 10. 46] IPSec 전송 모드 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 119](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-119.jpg)
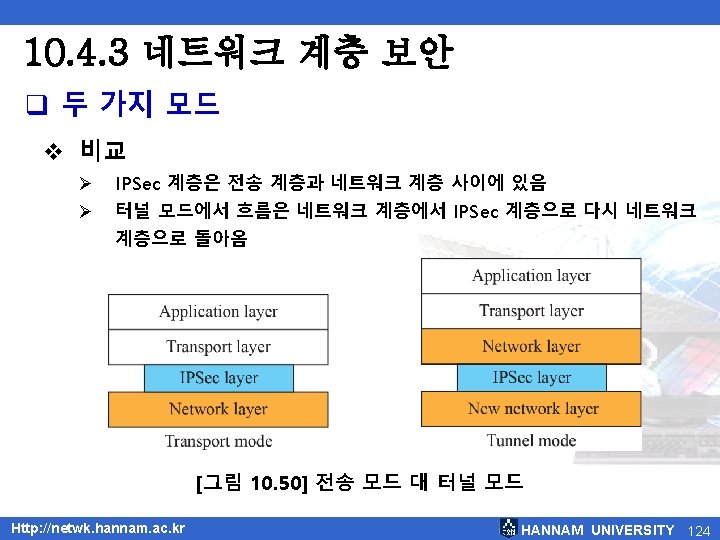
[그림 10. 46] IPSec 전송 모드 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 119
![그림 10 47 전송 모드 동작 과정 Http netwk hannam ac kr HANNAM UNIVERSITY [그림 10. 47] 전송 모드 동작 과정 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-120.jpg)
[그림 10. 47] 전송 모드 동작 과정 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 120
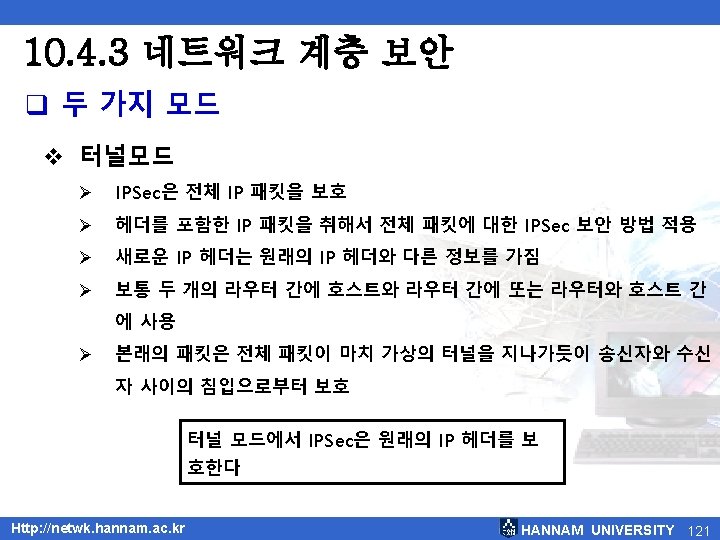
![그림 10 48 IPSec 터널 모드 Http netwk hannam ac kr HANNAM UNIVERSITY 122 [그림 10. 48] IPSec 터널 모드 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 122](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-122.jpg)
[그림 10. 48] IPSec 터널 모드 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 122
![그림 10 49 터널 모드 실제 동작 Http netwk hannam ac kr HANNAM UNIVERSITY [그림 10. 49] 터널 모드 실제 동작 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-123.jpg)
[그림 10. 49] 터널 모드 실제 동작 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 123
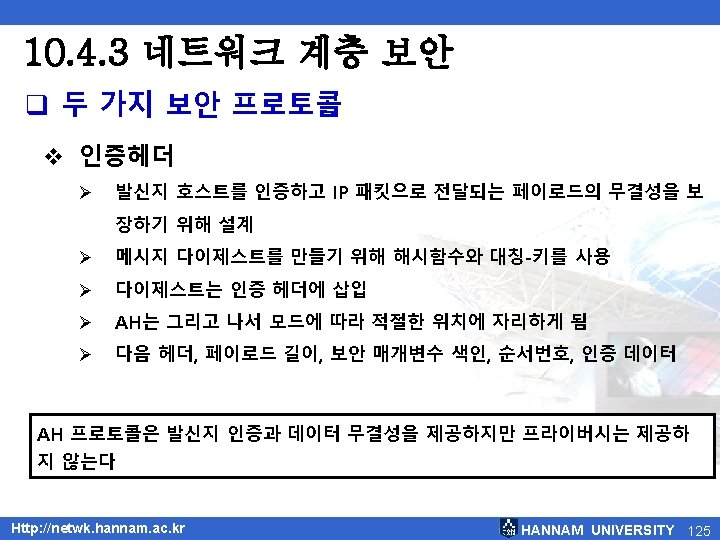
![그림 10 51 인증 헤더 프로토콜 Http netwk hannam ac kr HANNAM UNIVERSITY 126 [그림 10. 51] 인증 헤더 프로토콜 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 126](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-126.jpg)
[그림 10. 51] 인증 헤더 프로토콜 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 126
![그림 10 52 ESP Http netwk hannam ac kr HANNAM UNIVERSITY 128 [그림 10. 52] ESP Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 128](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-128.jpg)
[그림 10. 52] ESP Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 128
![표 10 1 IPSec 서비스 Http netwk hannam ac kr HANNAM UNIVERSITY 131 [표 10. 1] IPSec 서비스 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 131](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-131.jpg)
[표 10. 1] IPSec 서비스 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 131
![그림 10 53 간단한 SA Http netwk hannam ac kr HANNAM UNIVERSITY 133 [그림 10. 53] 간단한 SA Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 133](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-133.jpg)
[그림 10. 53] 간단한 SA Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 133
![그림 10 54 SAD Http netwk hannam ac kr HANNAM UNIVERSITY 134 [그림 10. 54] SAD Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 134](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-134.jpg)
[그림 10. 54] SAD Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 134
![그림 10 55 SPD Http netwk hannam ac kr HANNAM UNIVERSITY 135 [그림 10. 55] SPD Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 135](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-135.jpg)
[그림 10. 55] SPD Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 135
![그림 10 56 외부적 처리 절차 Http netwk hannam ac kr HANNAM UNIVERSITY 137 [그림 10. 56] 외부적 처리 절차 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 137](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-137.jpg)
[그림 10. 56] 외부적 처리 절차 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 137
![그림 10 57 내부적 처리 절차 Http netwk hannam ac kr HANNAM UNIVERSITY 138 [그림 10. 57] 내부적 처리 절차 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 138](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-138.jpg)
[그림 10. 57] 내부적 처리 절차 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 138
![그림 10 58 IKE 구성 요소 Http netwk hannam ac kr HANNAM UNIVERSITY 140 [그림 10. 58] IKE 구성 요소 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 140](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-140.jpg)
[그림 10. 58] IKE 구성 요소 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 140
![그림 10 59 가상 사설 네트워크 Http netwk hannam ac kr HANNAM UNIVERSITY 142 [그림 10. 59] 가상 사설 네트워크 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 142](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-142.jpg)
[그림 10. 59] 가상 사설 네트워크 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 142
![그림 10 60 방화벽 Http netwk hannam ac kr HANNAM UNIVERSITY 144 [그림 10. 60] 방화벽 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 144](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-144.jpg)
[그림 10. 60] 방화벽 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 144
![그림 10 61 패킷 필터 방화벽 Http netwk hannam ac kr HANNAM UNIVERSITY 146 [그림 10. 61] 패킷 필터 방화벽 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 146](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-146.jpg)
[그림 10. 61] 패킷 필터 방화벽 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 146
![그림 10 62 프록시 방화벽 Http netwk hannam ac kr HANNAM UNIVERSITY 148 [그림 10. 62] 프록시 방화벽 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 148](https://slidetodoc.com/presentation_image/1f87f9ee53c96747a741b0b9fd9c9ace/image-148.jpg)
[그림 10. 62] 프록시 방화벽 Http: //netwk. hannam. ac. kr HANNAM UNIVERSITY 148