Channel Spoofer Defeating Channel Variability and Unpredictability Yue
Channel Spoofer: Defeating Channel Variability and Unpredictability Yue Qiao, Kannan Srinivasan, and Anish Arora Presenter: Jiaqi Xu Computer Science and Engineering December 15 th, 2017 1
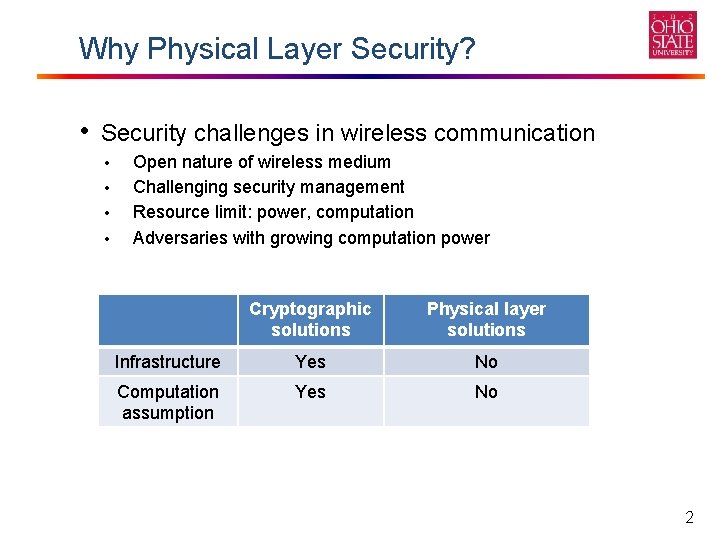
Why Physical Layer Security? • Security challenges in wireless communication • • Open nature of wireless medium Challenging security management Resource limit: power, computation Adversaries with growing computation power Cryptographic solutions Physical layer solutions Infrastructure Yes No Computation assumption Yes No 2
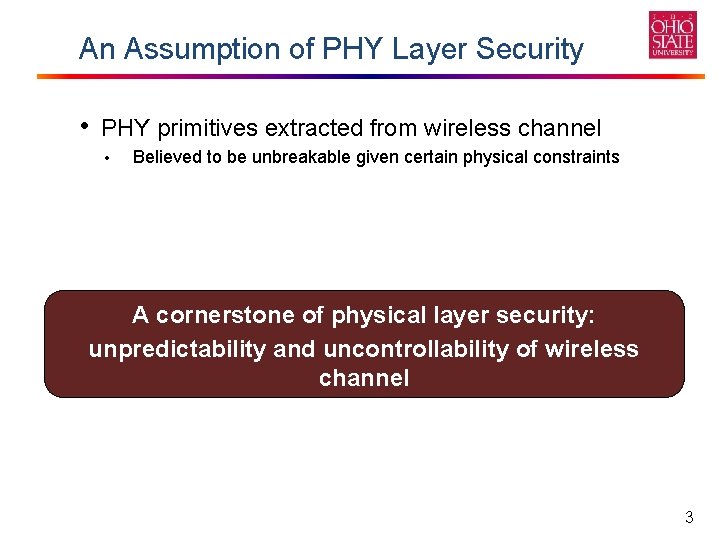
An Assumption of PHY Layer Security • PHY primitives extracted from wireless channel • Believed to be unbreakable given certain physical constraints A cornerstone of physical layer security: unpredictability and uncontrollability of wireless channel 3
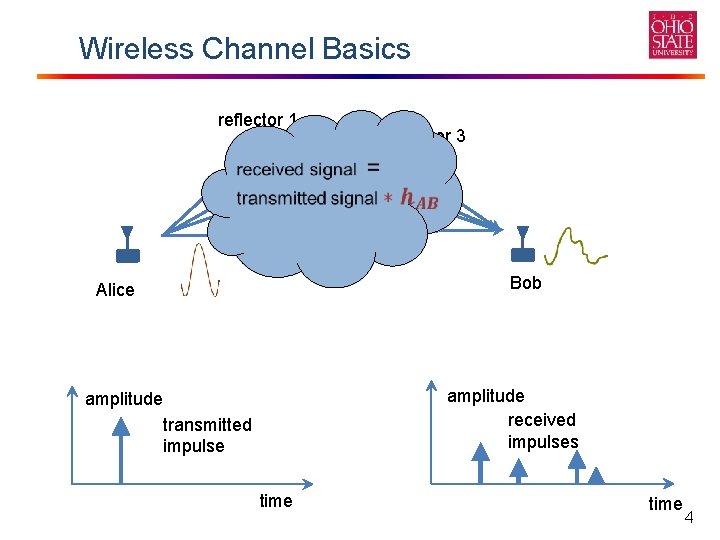
Wireless Channel Basics reflector 1 reflector 2 reflector 3 Bob Alice amplitude received impulses amplitude transmitted impulse time 4
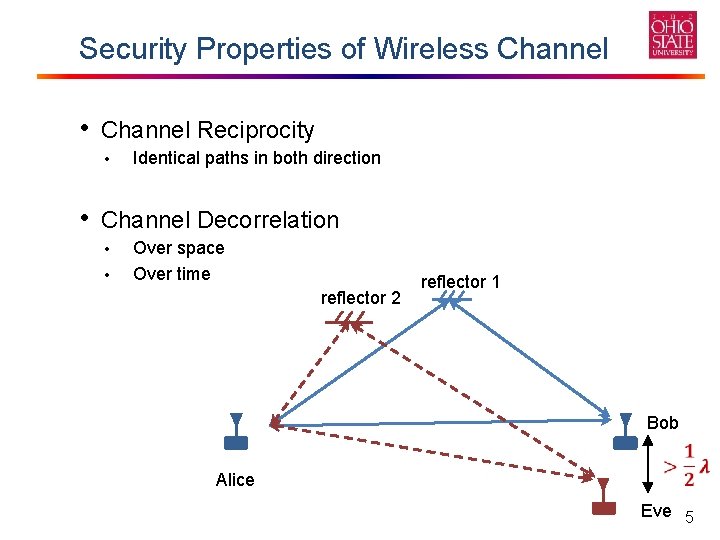
Security Properties of Wireless Channel • Channel Reciprocity • Identical paths in both direction • Channel Decorrelation • • Over space Over time reflector 2 reflector 1 Bob Alice Eve 5
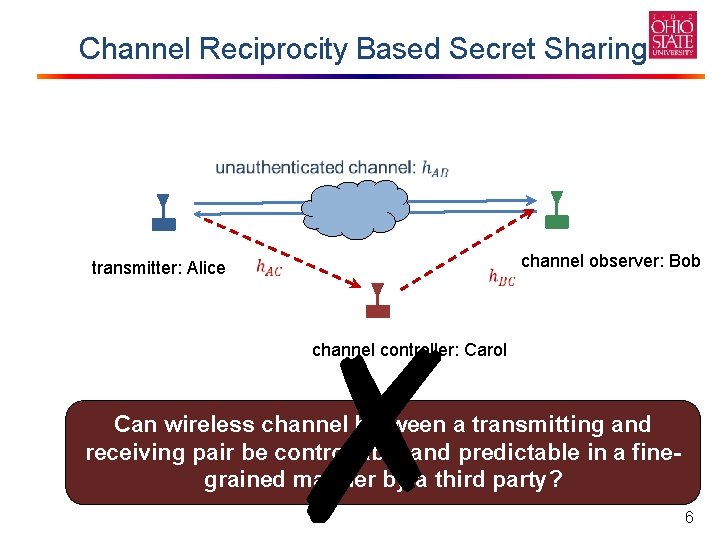
Channel Reciprocity Based Secret Sharing transmitter: Alice ✗ channel observer: Bob channel controller: Carol Can wireless between paths a transmitting Is knowing allchannel the propagation the only and way receiving pair betocontrollable and predictable in a fineperform prediction? grained manner by a third party? 6
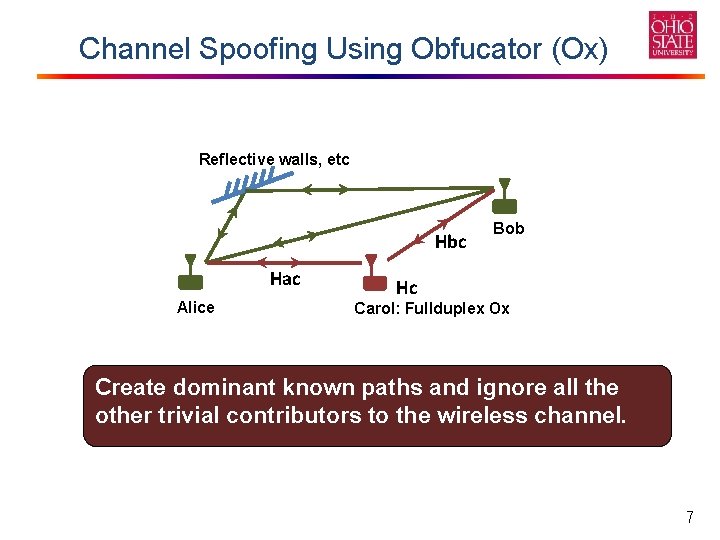
Channel Spoofing Using Obfucator (Ox) Reflective walls, etc Hbc Hac Alice Bob Hc Carol: Fullduplex Ox Create dominant known paths and ignore all the other trivial contributors to the wireless channel. Conventional 7
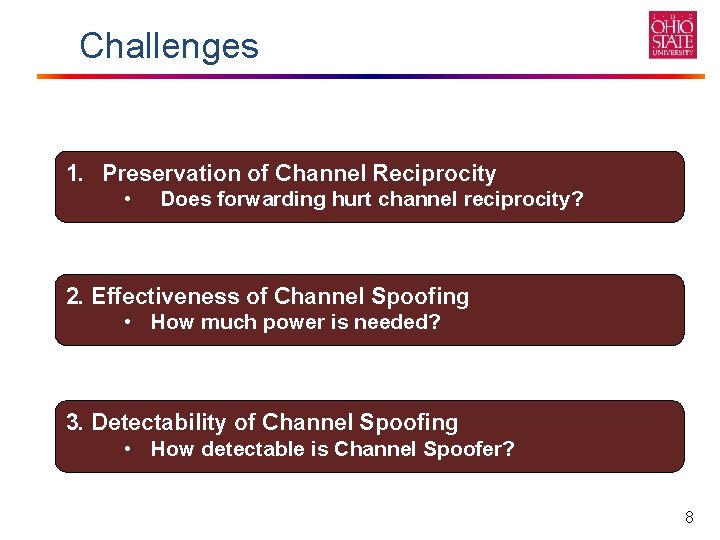
Challenges 1. Preservation of Channel Reciprocity • Does forwarding hurt channel reciprocity? 2. Effectiveness of Channel Spoofing • How much power is needed? 3. Detectability of Channel Spoofing • How detectable is Channel Spoofer? 8
Problem statement 1. Soundness: Alice’s and Bob’s success rate in continually extracting shared secrets is preserved. 2. Disclosure: Alice’s and Bob’s extracted secrets are Alice Bob predicted by Channel Spoofer with non-trivial probability (≫ 50%). Carol: Channel Spoofer 3. Undetectability: Alice and Bob do not detect the presence of Channel Spoofer by physical layer approaches that can be implemented with their system resources. 9
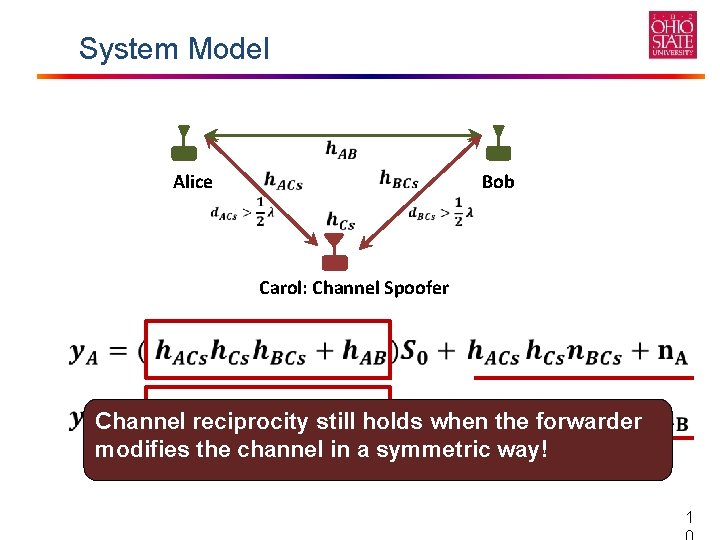
System Model Alice Bob Carol: Channel Spoofer Channel reciprocity still holds when the forwarder modifies the channel in a symmetric way! 1
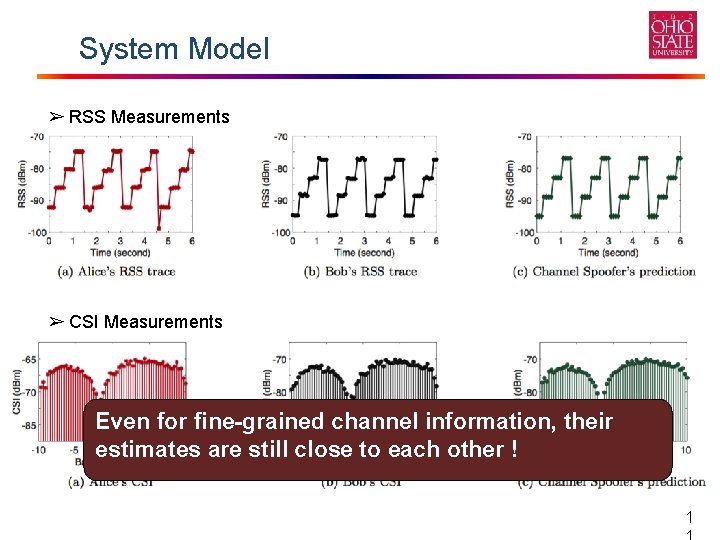
System Model ➢ RSS Measurements ➢ CSI Measurements Even for fine-grained channel information, their estimates are still close to each other ! 1

Preservation of Channel Reciprocity Channel Spoofer Alice Bob • RSS approaches • CSI approaches Channel reciprocity holds regardless of whether or not the channel gain from Alice to Channel Spoofer is comparable to that from Bob to Channel Spoofer. 1
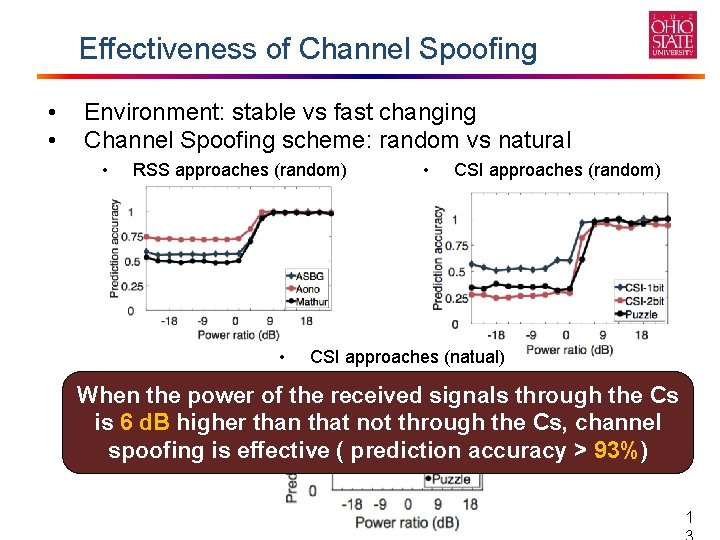
Effectiveness of Channel Spoofing • • Environment: stable vs fast changing Channel Spoofing scheme: random vs natural • RSS approaches (random) • • CSI approaches (random) CSI approaches (natual) When the power of the received signals through the Cs is 6 d. B higher than that not through the Cs, channel spoofing is effective ( prediction accuracy > 93%) 1
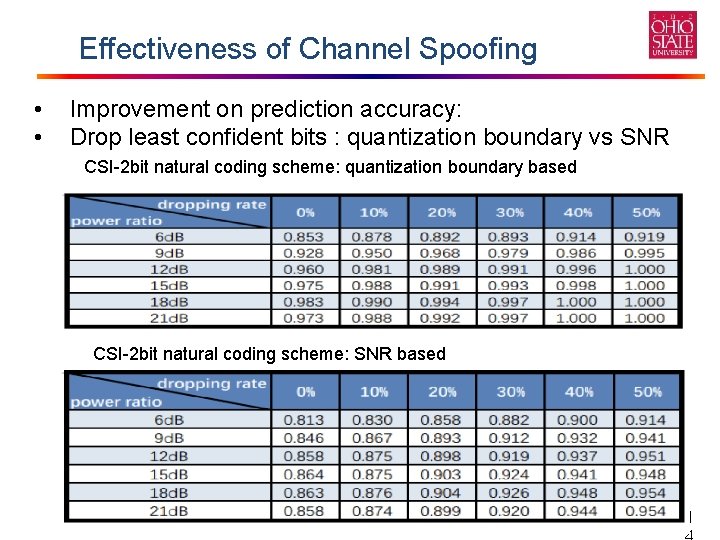
Effectiveness of Channel Spoofing • • Improvement on prediction accuracy: Drop least confident bits : quantization boundary vs SNR CSI-2 bit natural coding scheme: quantization boundary based CSI-2 bit natural coding scheme: SNR based 1
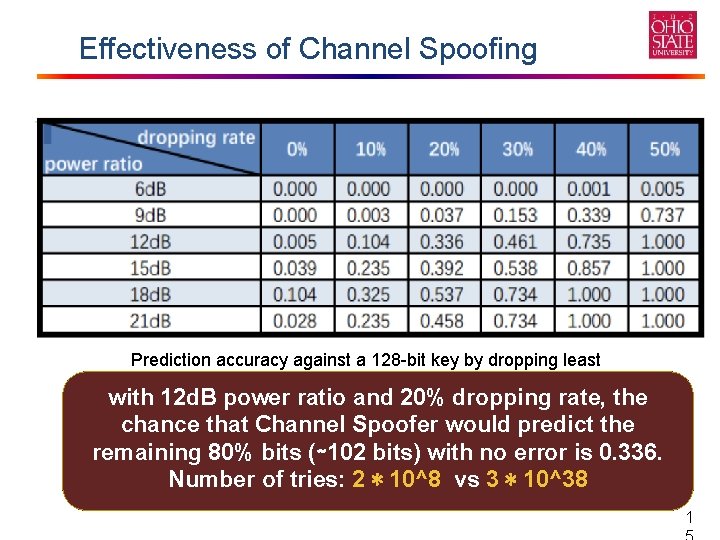
Effectiveness of Channel Spoofing Prediction accuracy against a 128 -bit key by dropping least confident bits based on quantization boundaries (natural coding) with 12 d. B power ratio and 20% dropping rate, the chance that Channel Spoofer would predict the remaining 80% bits (∼ 102 bits) with no error is 0. 336. Number of tries: 2 ∗ 10^8 vs 3 ∗ 10^38 1
Preempt Countermeasures • Countermeasures against Channel Spoofing • Analyses of Power and Channel Statistics - Monitor abrupt power changes. - Tell the artificial channel generated by channel spoofer. • Using a Protector • Transient and non-transient PHY Signatures 1
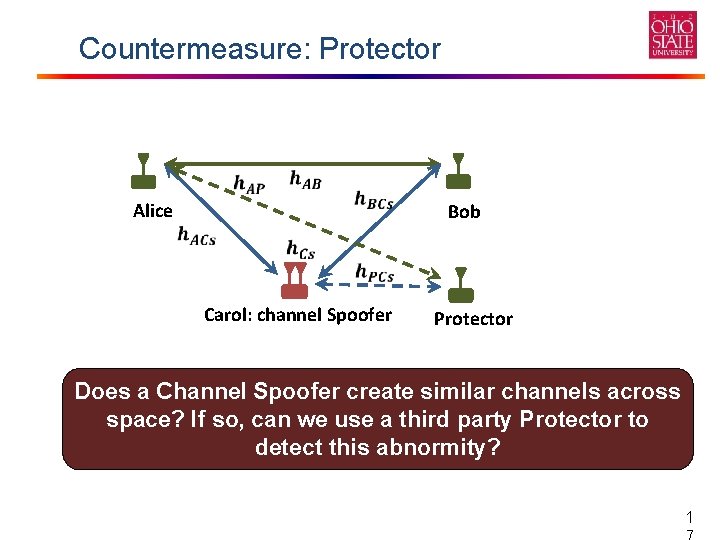
Countermeasure: Protector Alice Bob Carol: channel Spoofer Protector Does a Channel Spoofer create similar channels across space? If so, can we use a third party Protector to detect this abnormity? 1
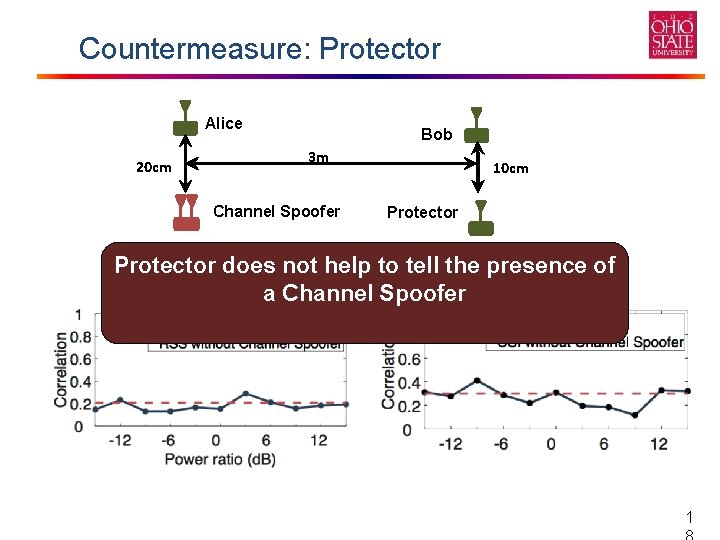
Countermeasure: Protector Alice 20 cm Bob 3 m Channel Spoofer 10 cm Protector does not help to tell the presence of a Channel Spoofer 1
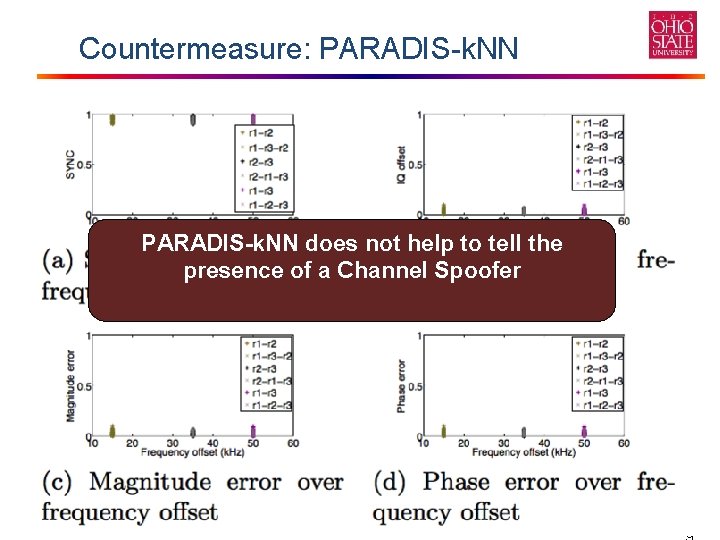
Countermeasure: PARADIS-k. NN does not help to tell the presence of a Channel Spoofer 1
Conclusion • This work demonstrates fined-grained channel information can be easily controlled and predicted • Channel reciprocity based secret sharing are vulnerable to our proposed attack 2
Q&A Thanks 2
- Slides: 21