Challenges of Practical Civil GNSS Security Todd Humphreys

- Slides: 9

Challenges of Practical Civil GNSS Security Todd Humphreys, UT Austin Civil Navigation and Timing Security Splinter Meeting |Portland, Oregon | September 23, 2010
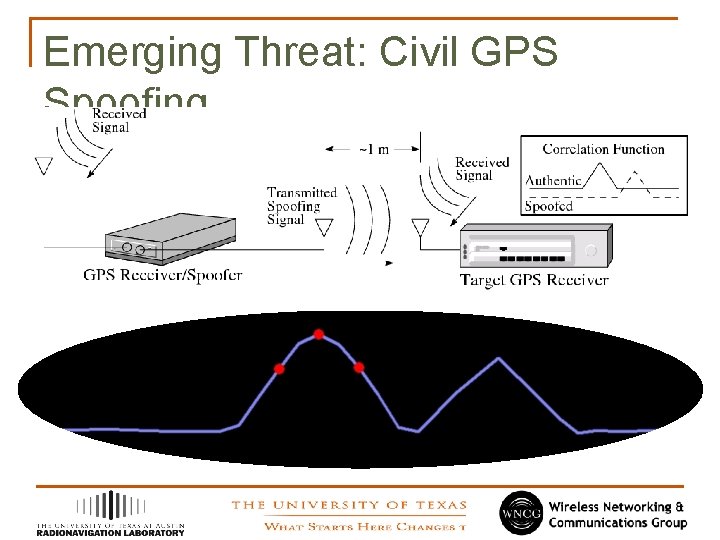
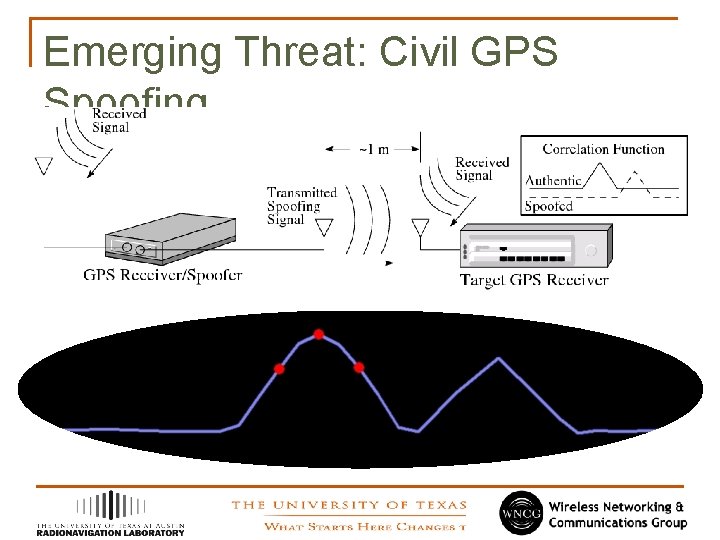
Emerging Threat: Civil GPS Spoofing
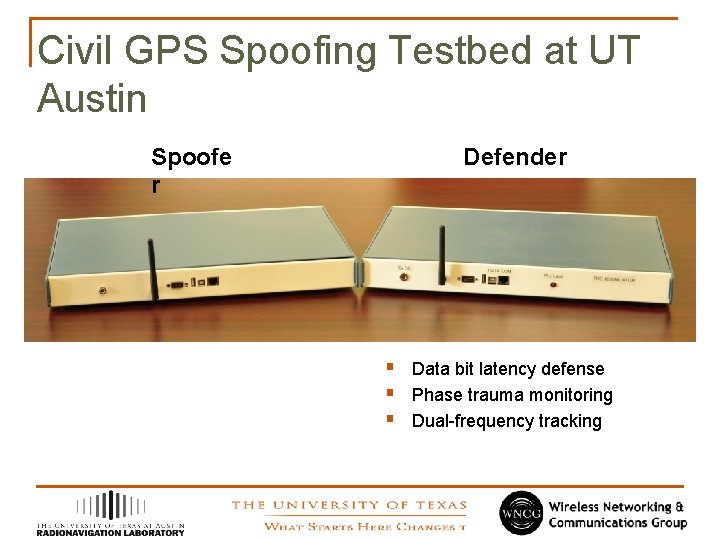
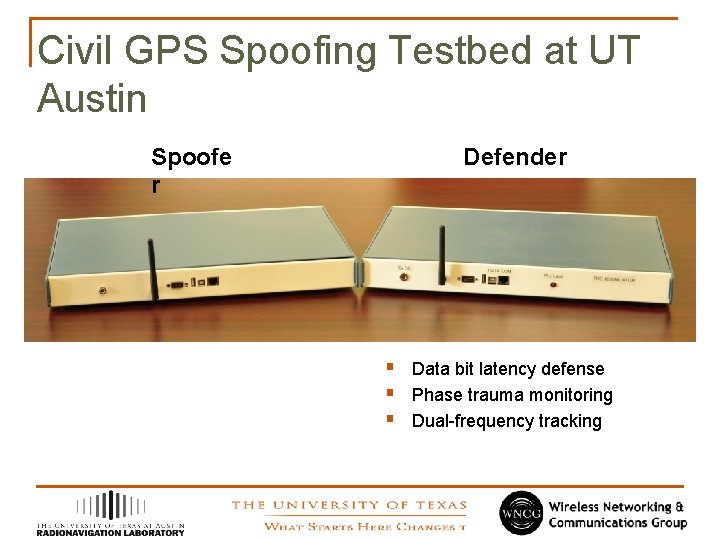
Civil GPS Spoofing Testbed at UT Austin Spoofe r Defender § Data bit latency defense § Phase trauma monitoring § Dual-frequency tracking
Video Demonstration of Spoofing Attack (not embedded; see posted video)
Thoughts on the Way Forward for Civil GNSS Authentication § § § § More signals means more inherent security, but probably insufficient Some civil cryptographic authentication scheme is likely required “Signal definition inertia is enormous” – Tom Stansell Navigation message authentication (NMA) appears to be best, practical option (advocated by Logan Scott in 2003, others since) Goal of cryptographic authentication: force adversary to use directional antennas in a replay attack Preliminary evaluation of NMA for L 2 C suggests optimism, but strategy is not water-tight Cryptography is the easy part
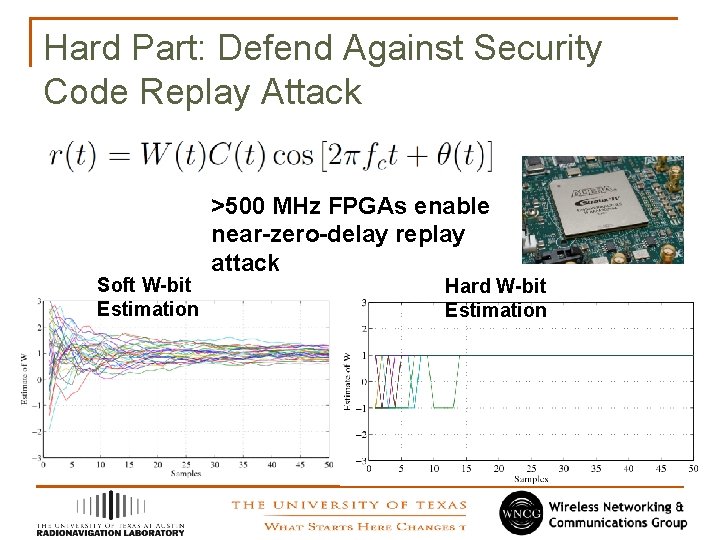
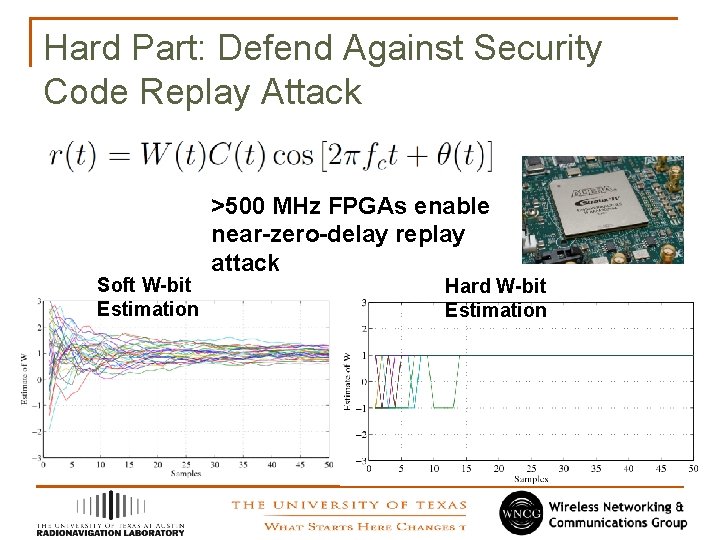
Hard Part: Defend Against Security Code Replay Attack Soft W-bit Estimation >500 MHz FPGAs enable near-zero-delay replay attack Hard W-bit Estimation
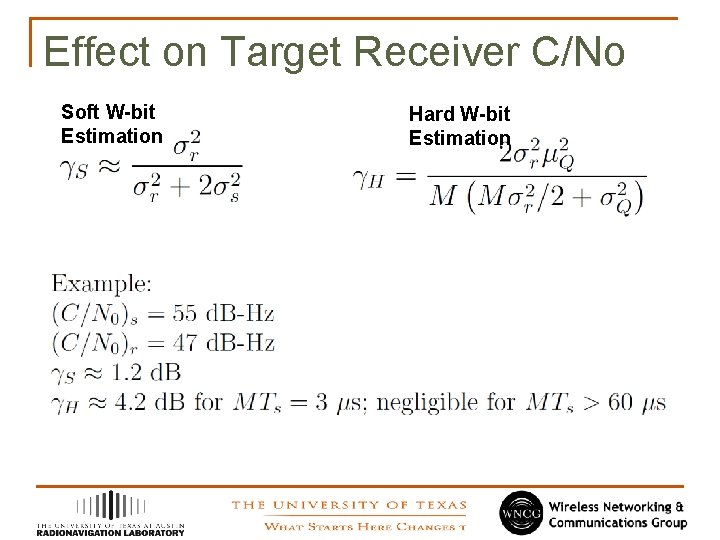
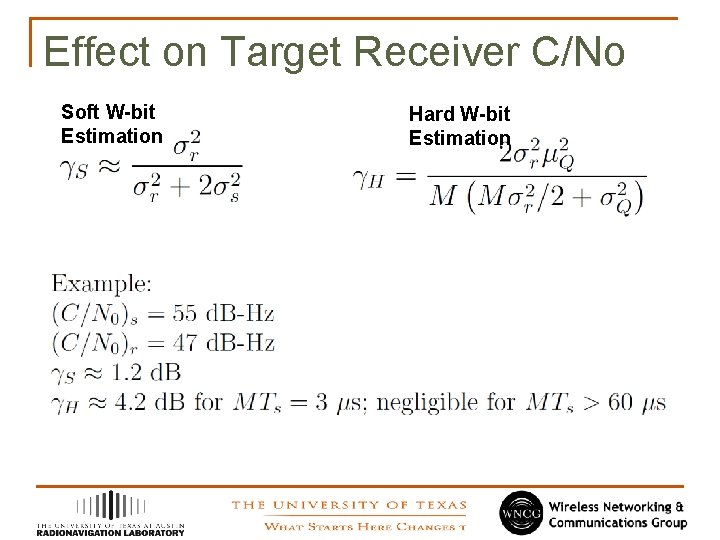
Effect on Target Receiver C/No Soft W-bit Estimation Hard W-bit Estimation
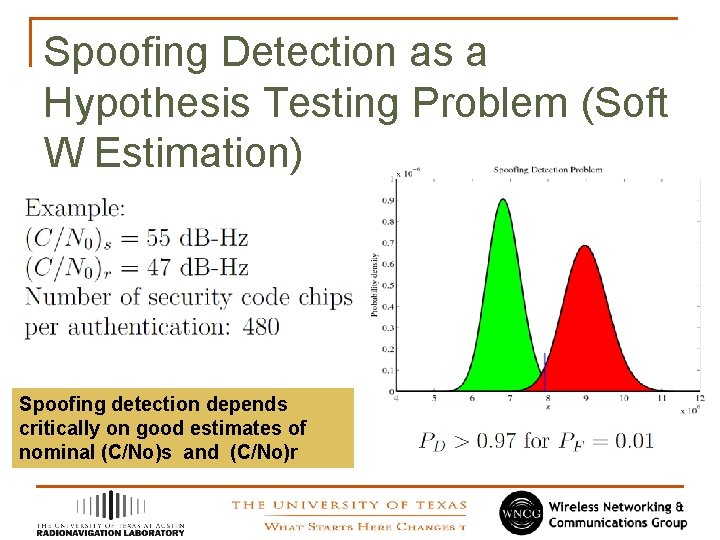
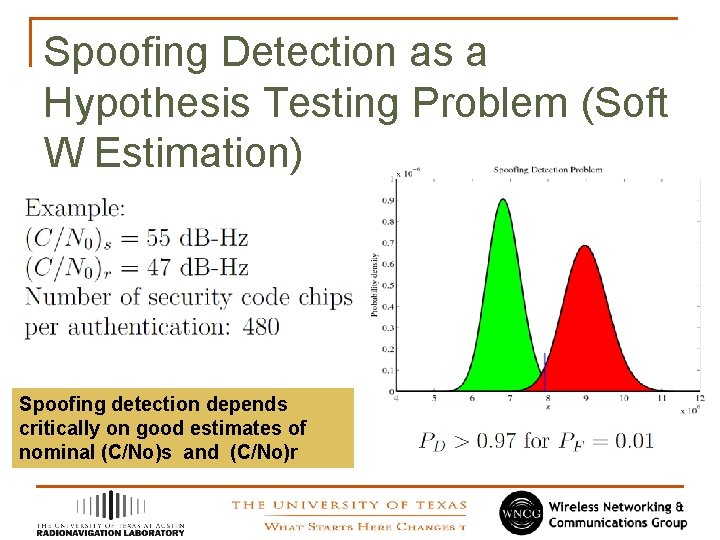
Spoofing Detection as a Hypothesis Testing Problem (Soft W Estimation) Spoofing detection depends critically on good estimates of nominal (C/No)s and (C/No)r
Final Observations § Must defend against following spoofing strategy: (1) § § § soften up target with low-grade jamming, (2) begin softestimate replay attack, (3) transition to hard-estimate replay attack A J/N meter is indispensable in spoofing detection to eliminate the possibility that the receiver’s estimate of its own nominal C/No (in the absence of spoofing) has been altered Solar radio bursts, unintentional/intentional jamming will tend to trigger spoofing alarms Spoofing detection is challenging for dynamic platforms because of the volatility in the nominal C/No