Ch 5 Access Points Overview Rick Graziani grazianicabrillo
Ch. 5 – Access Points
Overview Rick Graziani graziani@cabrillo. edu 2
Access Point Connection
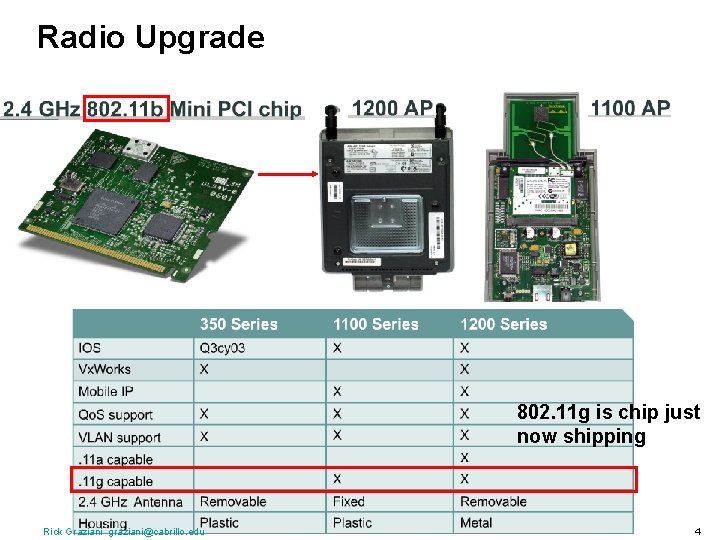
Radio Upgrade 802. 11 g is chip just now shipping Rick Graziani graziani@cabrillo. edu 4
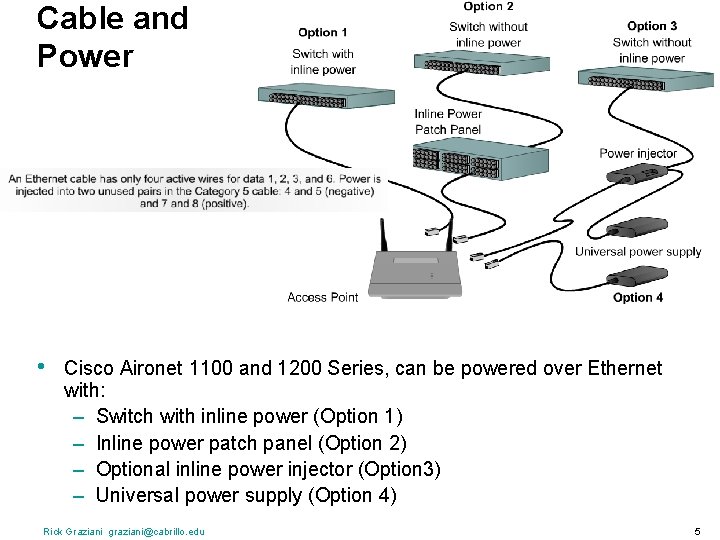
Cable and Power • Cisco Aironet 1100 and 1200 Series, can be powered over Ethernet with: – Switch with inline power (Option 1) – Inline power patch panel (Option 2) – Optional inline power injector (Option 3) – Universal power supply (Option 4) Rick Graziani graziani@cabrillo. edu 5
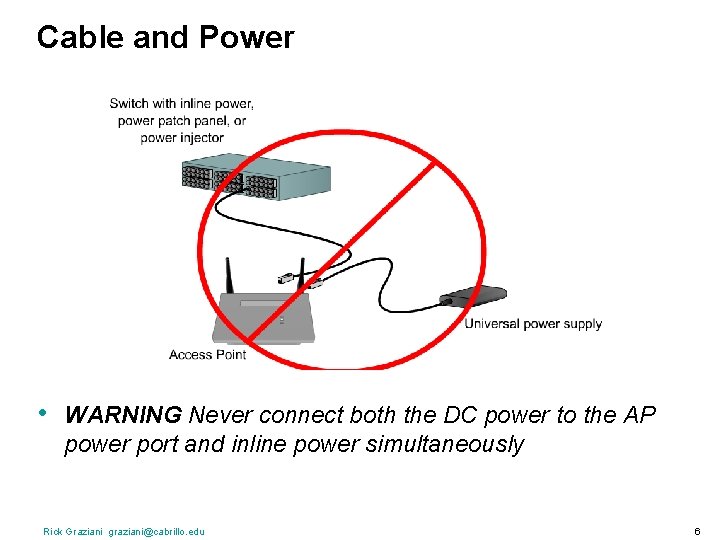
Cable and Power • WARNING Never connect both the DC power to the AP power port and inline power simultaneously Rick Graziani graziani@cabrillo. edu 6
AP Installation
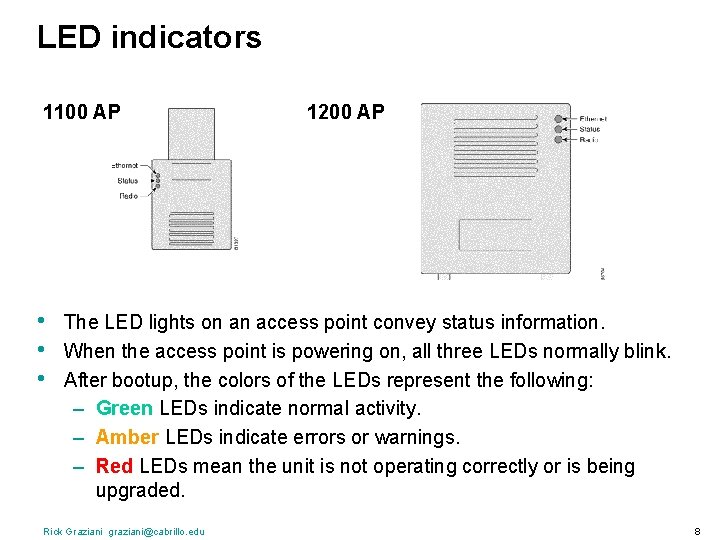
LED indicators 1100 AP • • • 1200 AP The LED lights on an access point convey status information. When the access point is powering on, all three LEDs normally blink. After bootup, the colors of the LEDs represent the following: – Green LEDs indicate normal activity. – Amber LEDs indicate errors or warnings. – Red LEDs mean the unit is not operating correctly or is being upgraded. Rick Graziani graziani@cabrillo. edu 8
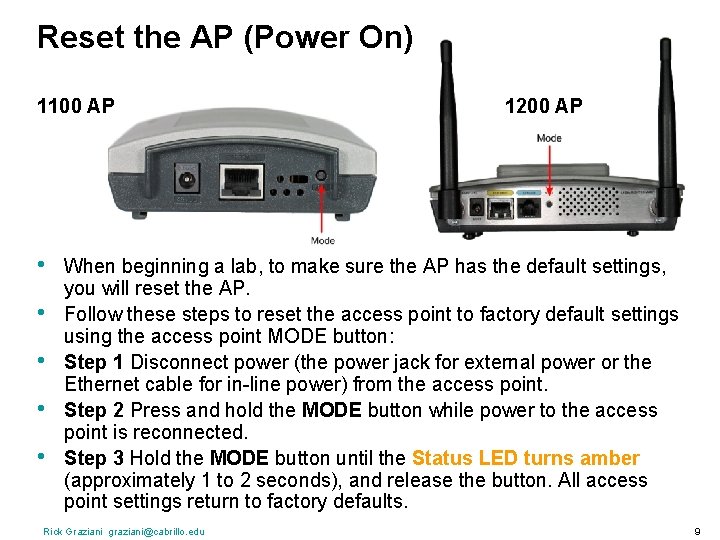
Reset the AP (Power On) 1100 AP • • • 1200 AP When beginning a lab, to make sure the AP has the default settings, you will reset the AP. Follow these steps to reset the access point to factory default settings using the access point MODE button: Step 1 Disconnect power (the power jack for external power or the Ethernet cable for in-line power) from the access point. Step 2 Press and hold the MODE button while power to the access point is reconnected. Step 3 Hold the MODE button until the Status LED turns amber (approximately 1 to 2 seconds), and release the button. All access point settings return to factory defaults. Rick Graziani graziani@cabrillo. edu 9

Connecting to the AP (Configuration) Wired Rick Graziani graziani@cabrillo. edu Wireless: Requires Association 10
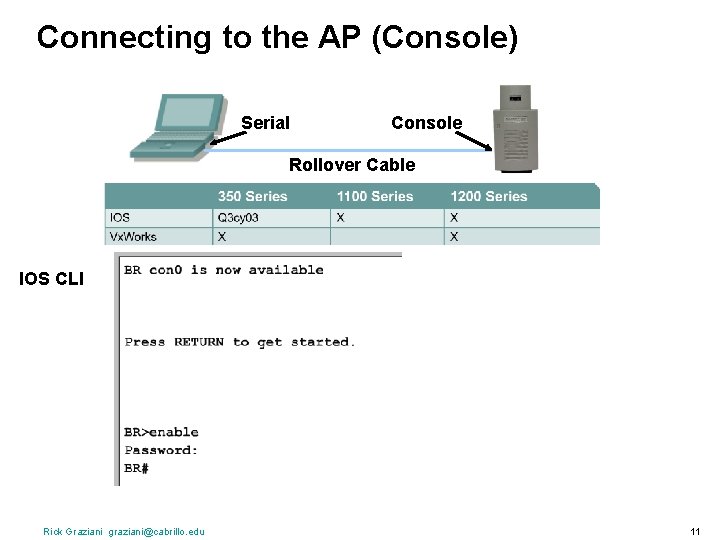
Connecting to the AP (Console) Serial Console Rollover Cable IOS CLI Rick Graziani graziani@cabrillo. edu 11
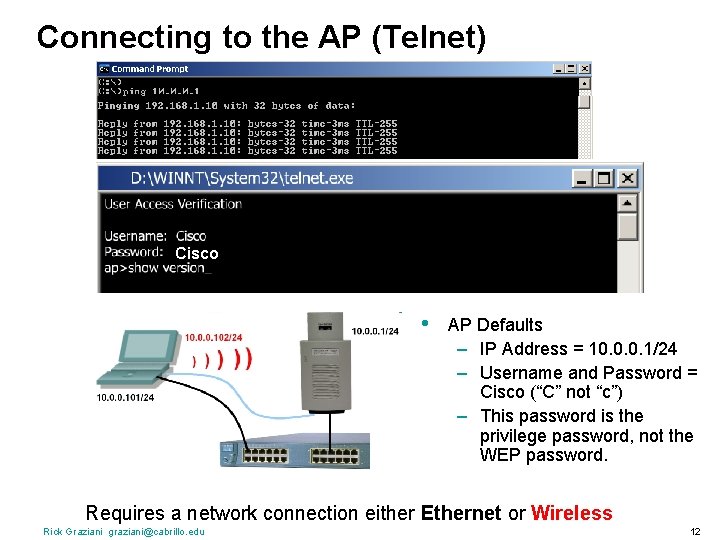
Connecting to the AP (Telnet) Cisco • AP Defaults – IP Address = 10. 0. 0. 1/24 – Username and Password = Cisco (“C” not “c”) – This password is the privilege password, not the WEP password. Requires a network connection either Ethernet or Wireless Rick Graziani graziani@cabrillo. edu 12
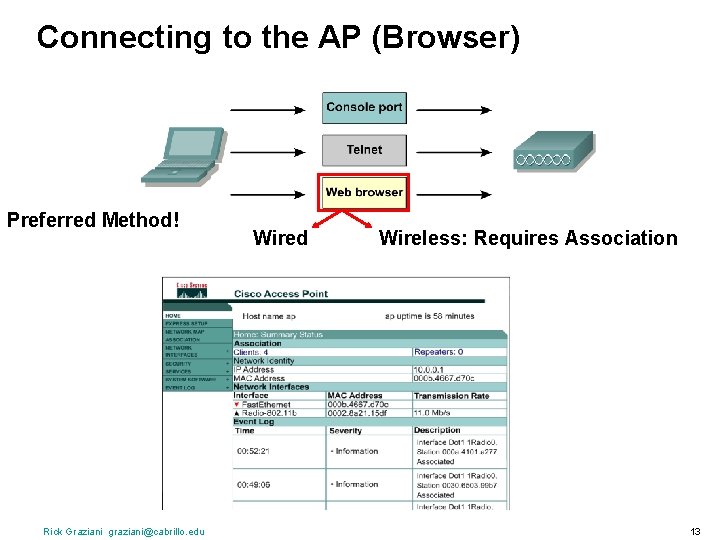
Connecting to the AP (Browser) Preferred Method! Rick Graziani graziani@cabrillo. edu Wired Wireless: Requires Association 13
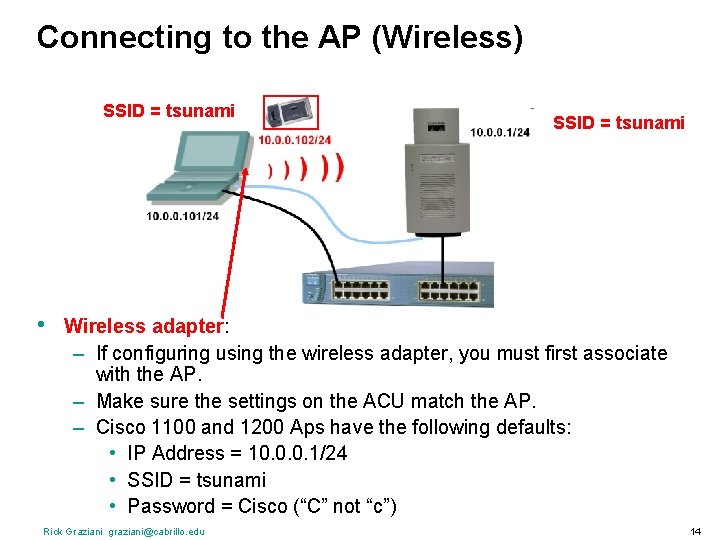
Connecting to the AP (Wireless) SSID = tsunami • SSID = tsunami Wireless adapter: – If configuring using the wireless adapter, you must first associate with the AP. – Make sure the settings on the ACU match the AP. – Cisco 1100 and 1200 Aps have the following defaults: • IP Address = 10. 0. 0. 1/24 • SSID = tsunami • Password = Cisco (“C” not “c”) Rick Graziani graziani@cabrillo. edu 14
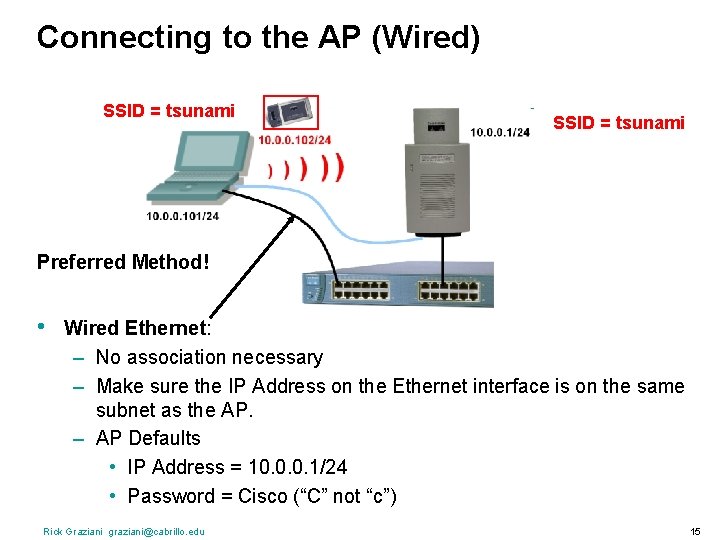
Connecting to the AP (Wired) SSID = tsunami Preferred Method! • Wired Ethernet: – No association necessary – Make sure the IP Address on the Ethernet interface is on the same subnet as the AP. – AP Defaults • IP Address = 10. 0. 0. 1/24 • Password = Cisco (“C” not “c”) Rick Graziani graziani@cabrillo. edu 15
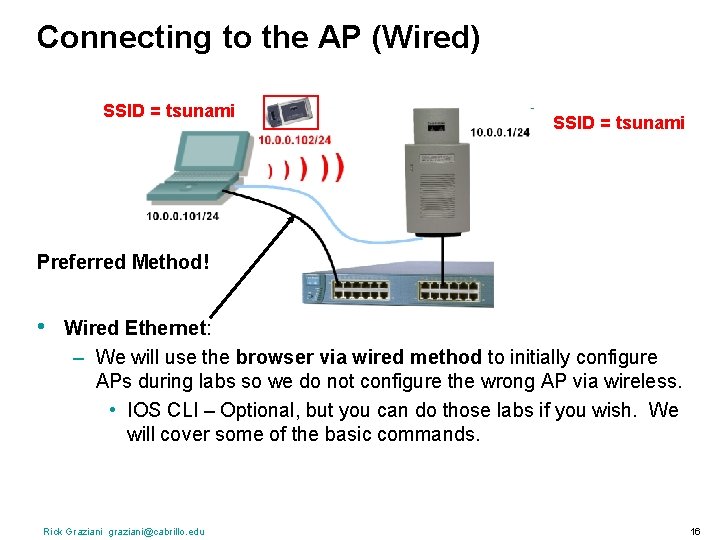
Connecting to the AP (Wired) SSID = tsunami Preferred Method! • Wired Ethernet: – We will use the browser via wired method to initially configure APs during labs so we do not configure the wrong AP via wireless. • IOS CLI – Optional, but you can do those labs if you wish. We will cover some of the basic commands. Rick Graziani graziani@cabrillo. edu 16
Basic Configuration The labs will really help you understand this. Lab 5. 4. 4: Configuring Radio Interfaces Through the GUI Skip step # 4 Refer to the next few slides to complete the lab
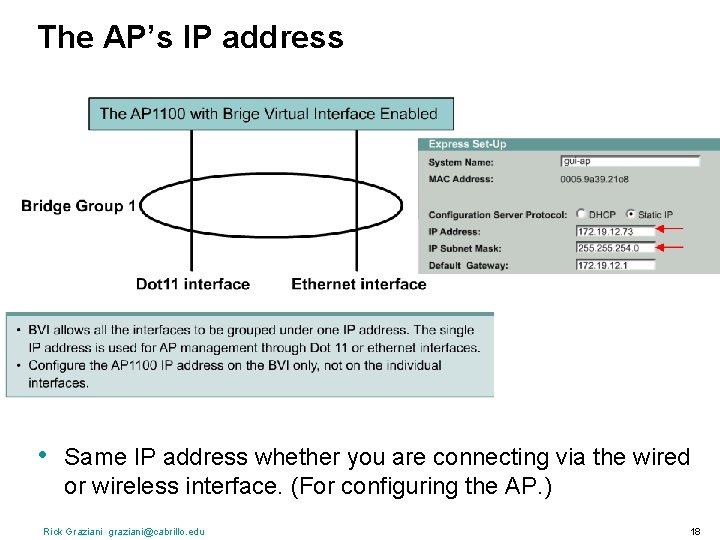
The AP’s IP address • Same IP address whether you are connecting via the wired or wireless interface. (For configuring the AP. ) Rick Graziani graziani@cabrillo. edu 18

ACU - Verifying Right click Rick Graziani graziani@cabrillo. edu 19
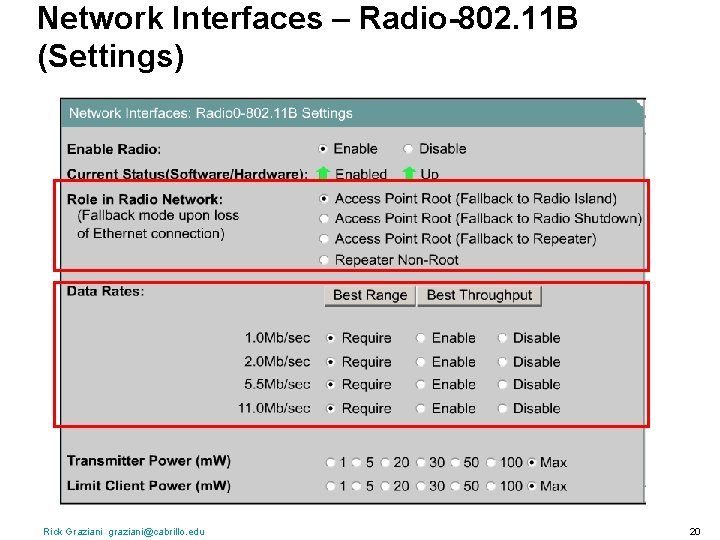
Network Interfaces – Radio-802. 11 B (Settings) Rick Graziani graziani@cabrillo. edu 20
Network Interfaces – Radio-802. 11 B (Settings) Rick Graziani graziani@cabrillo. edu 21
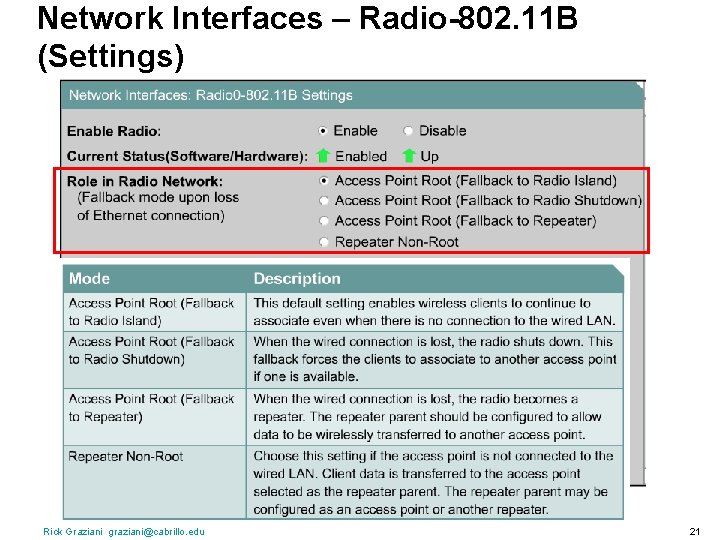
Network Interfaces – Radio-802. 11 B (Settings) Rick Graziani graziani@cabrillo. edu 22
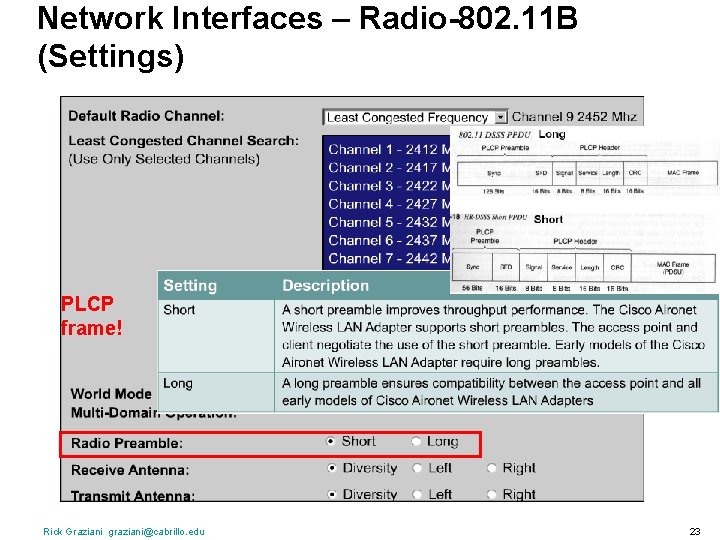
Network Interfaces – Radio-802. 11 B (Settings) PLCP frame! Rick Graziani graziani@cabrillo. edu 23
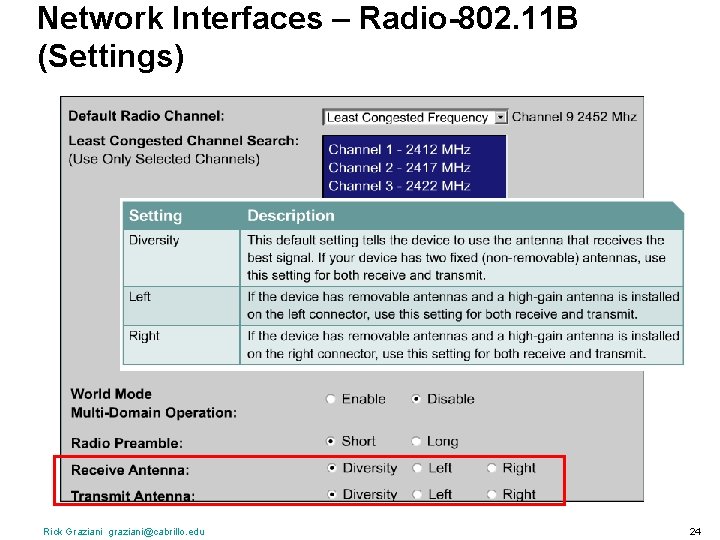
Network Interfaces – Radio-802. 11 B (Settings) Rick Graziani graziani@cabrillo. edu 24
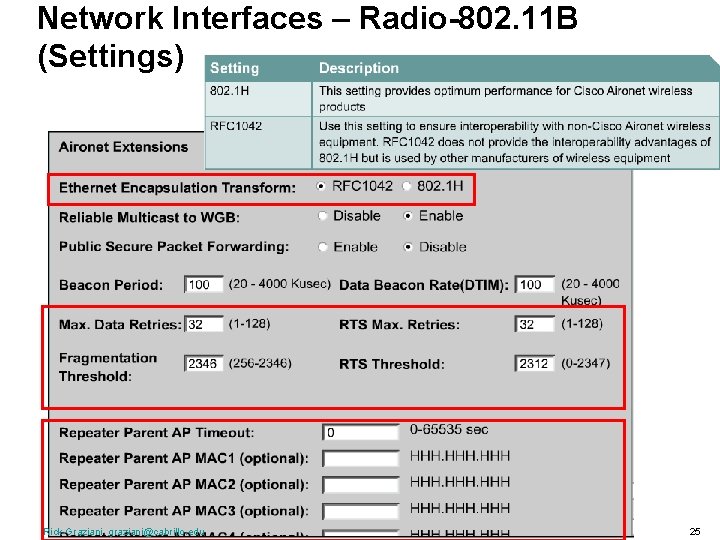
Network Interfaces – Radio-802. 11 B (Settings) Rick Graziani graziani@cabrillo. edu 25
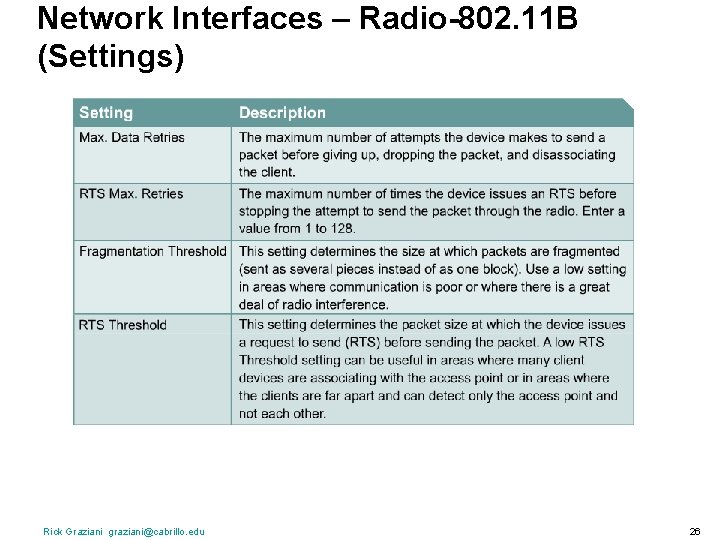
Network Interfaces – Radio-802. 11 B (Settings) Rick Graziani graziani@cabrillo. edu 26
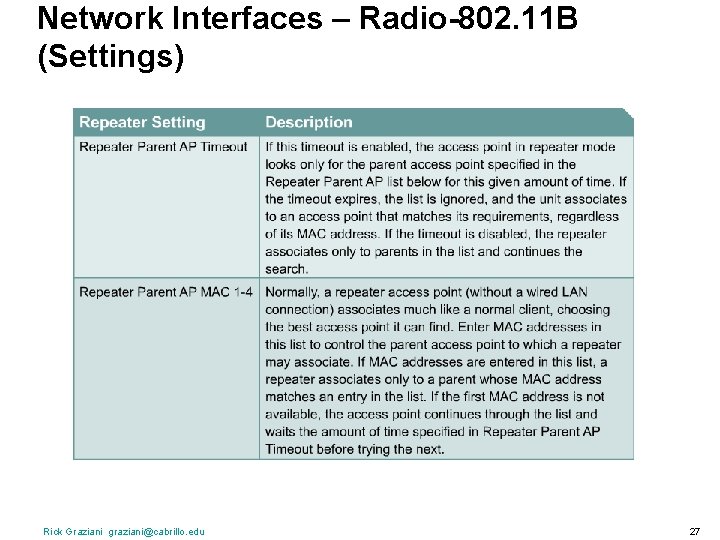
Network Interfaces – Radio-802. 11 B (Settings) Rick Graziani graziani@cabrillo. edu 27

Using the CLI Rick Graziani graziani@cabrillo. edu 28
Lab 5. 4. 5 Page 118 • • Configuring Radio Interfaces through the IOS CLI Stop at step # 10 Rick Graziani graziani@cabrillo. edu 29
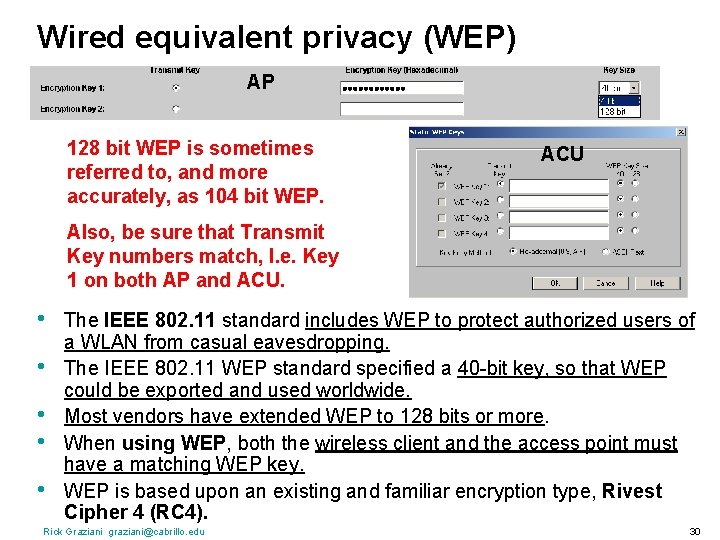
Wired equivalent privacy (WEP) AP 128 bit WEP is sometimes referred to, and more accurately, as 104 bit WEP. ACU Also, be sure that Transmit Key numbers match, I. e. Key 1 on both AP and ACU. • • • The IEEE 802. 11 standard includes WEP to protect authorized users of a WLAN from casual eavesdropping. The IEEE 802. 11 WEP standard specified a 40 -bit key, so that WEP could be exported and used worldwide. Most vendors have extended WEP to 128 bits or more. When using WEP, both the wireless client and the access point must have a matching WEP key. WEP is based upon an existing and familiar encryption type, Rivest Cipher 4 (RC 4). Rick Graziani graziani@cabrillo. edu 30
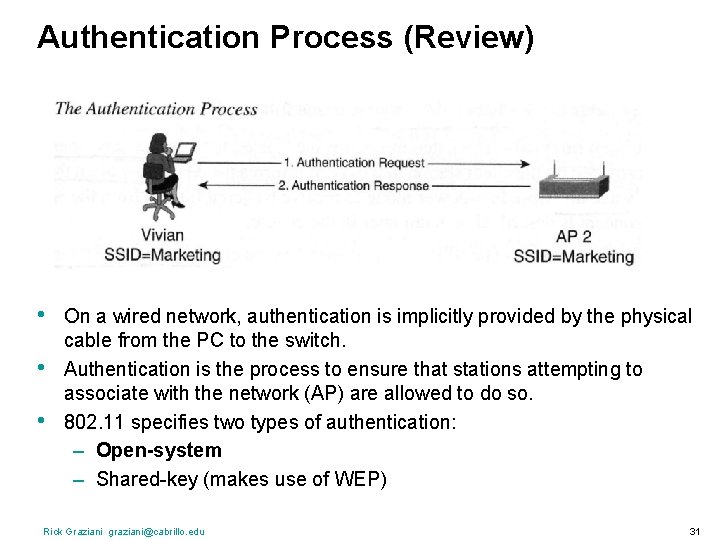
Authentication Process (Review) • • • On a wired network, authentication is implicitly provided by the physical cable from the PC to the switch. Authentication is the process to ensure that stations attempting to associate with the network (AP) are allowed to do so. 802. 11 specifies two types of authentication: – Open-system – Shared-key (makes use of WEP) Rick Graziani graziani@cabrillo. edu 31
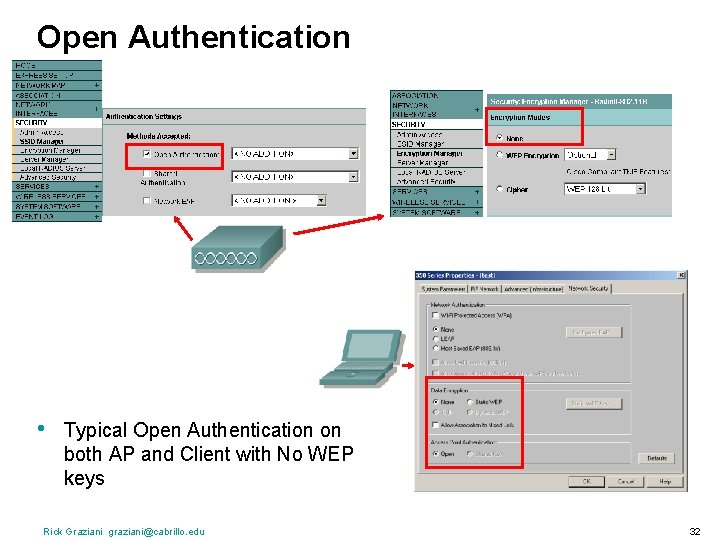
Open Authentication • Typical Open Authentication on both AP and Client with No WEP keys Rick Graziani graziani@cabrillo. edu 32
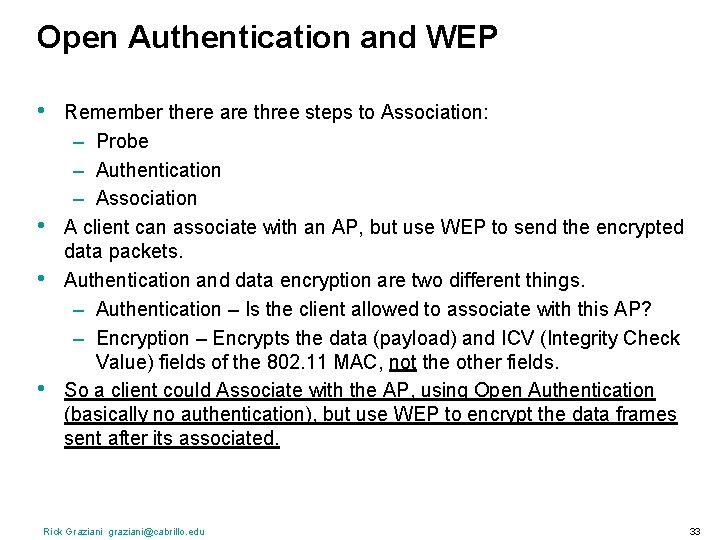
Open Authentication and WEP • • Remember there are three steps to Association: – Probe – Authentication – Association A client can associate with an AP, but use WEP to send the encrypted data packets. Authentication and data encryption are two different things. – Authentication – Is the client allowed to associate with this AP? – Encryption – Encrypts the data (payload) and ICV (Integrity Check Value) fields of the 802. 11 MAC, not the other fields. So a client could Associate with the AP, using Open Authentication (basically no authentication), but use WEP to encrypt the data frames sent after its associated. Rick Graziani graziani@cabrillo. edu 33
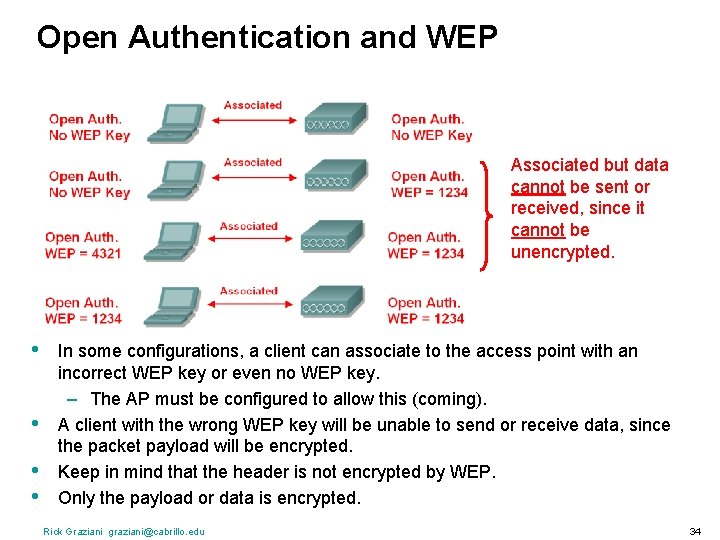
Open Authentication and WEP Associated but data cannot be sent or received, since it cannot be unencrypted. • • In some configurations, a client can associate to the access point with an incorrect WEP key or even no WEP key. – The AP must be configured to allow this (coming). A client with the wrong WEP key will be unable to send or receive data, since the packet payload will be encrypted. Keep in mind that the header is not encrypted by WEP. Only the payload or data is encrypted. Rick Graziani graziani@cabrillo. edu 34
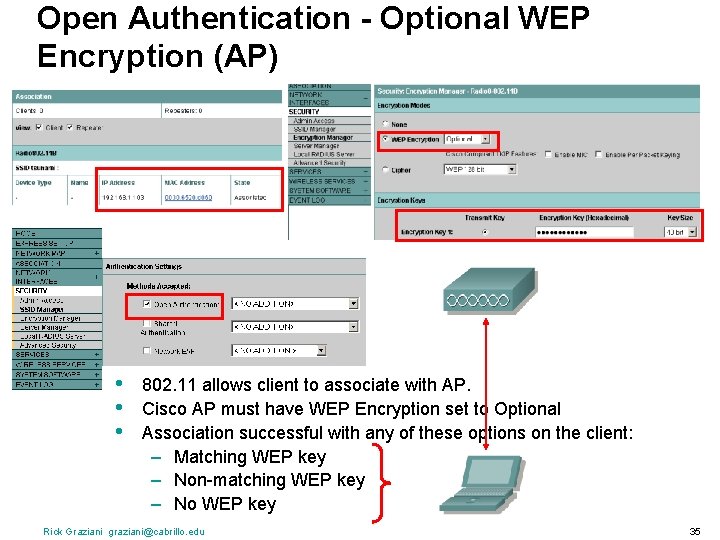
Open Authentication - Optional WEP Encryption (AP) • • • 802. 11 allows client to associate with AP. Cisco AP must have WEP Encryption set to Optional Association successful with any of these options on the client: – Matching WEP key – Non-matching WEP key – No WEP key Rick Graziani graziani@cabrillo. edu 35
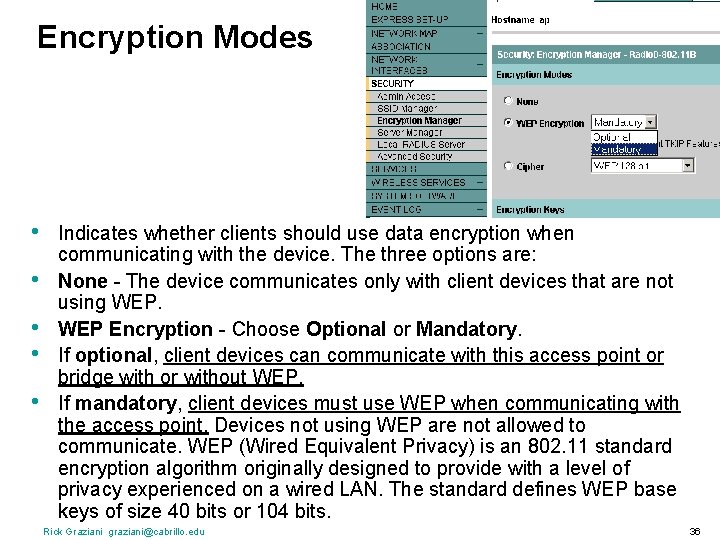
Encryption Modes • • • Indicates whether clients should use data encryption when communicating with the device. The three options are: None - The device communicates only with client devices that are not using WEP Encryption - Choose Optional or Mandatory. If optional, client devices can communicate with this access point or bridge with or without WEP. If mandatory, client devices must use WEP when communicating with the access point. Devices not using WEP are not allowed to communicate. WEP (Wired Equivalent Privacy) is an 802. 11 standard encryption algorithm originally designed to provide with a level of privacy experienced on a wired LAN. The standard defines WEP base keys of size 40 bits or 104 bits. Rick Graziani graziani@cabrillo. edu 36

In Summary • • Client – Use Open Authentication on the client (does not use WEP, challenge transaction, during authentication). – Use WEP for Data Encryption. AP – Use Open Authentication – Use Mandatory WEP Encryption, Devices not using WEP are not allowed to communicate. Rick Graziani graziani@cabrillo. edu 37
Lab 8. 3. 3. 1: Page 225 Configuring WEP on AP and client Rick Graziani graziani@cabrillo. edu 38
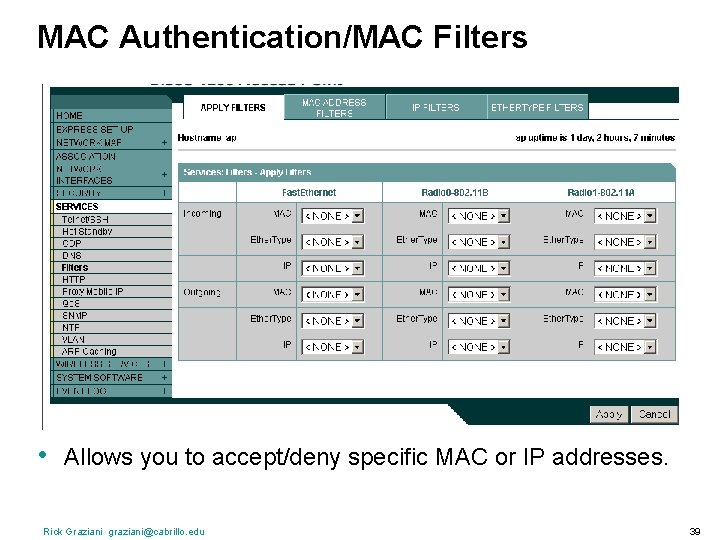
MAC Authentication/MAC Filters • Allows you to accept/deny specific MAC or IP addresses. Rick Graziani graziani@cabrillo. edu 39
Lab 8. 3. 2: Page 218 Configuring Filters on AP Rick Graziani graziani@cabrillo. edu 40
Services We will not configure all of these options or use all of the features.
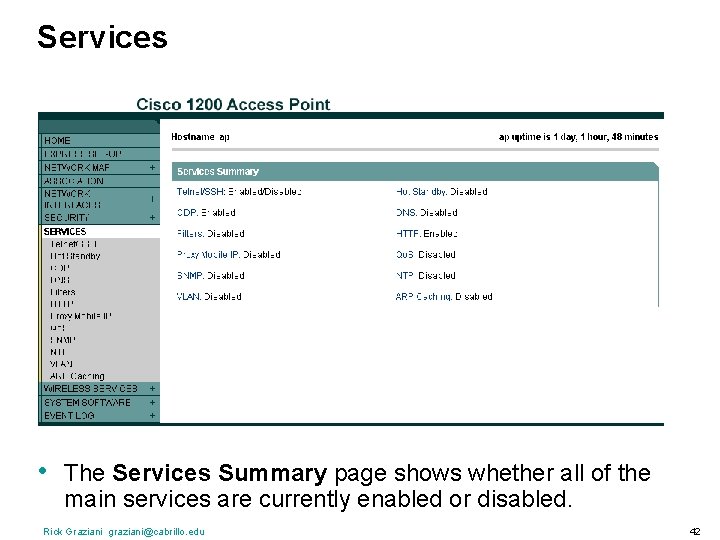
Services • The Services Summary page shows whether all of the main services are currently enabled or disabled. Rick Graziani graziani@cabrillo. edu 42
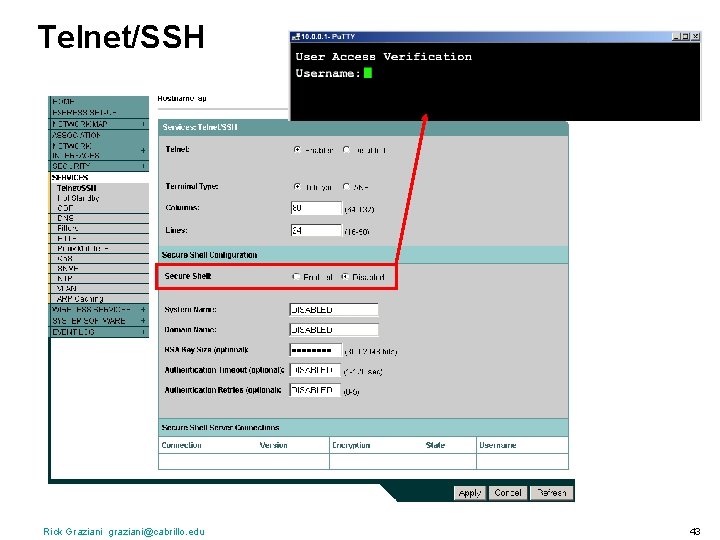
Telnet/SSH Rick Graziani graziani@cabrillo. edu 43
Lab 8. 3. 1. 1 Page 198 Configuring Basic AP Security Via GUI Rick Graziani graziani@cabrillo. edu 44
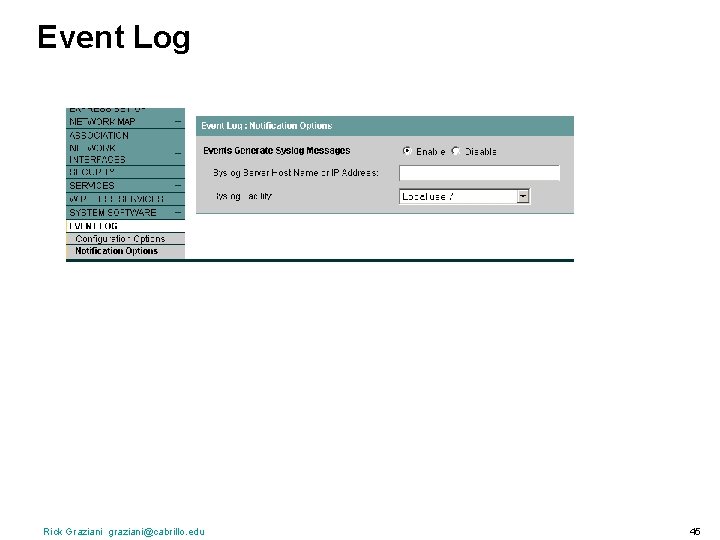
Event Log Rick Graziani graziani@cabrillo. edu 45

Lab 11. 5. 6. 1: page 335 Configuring Syslog on AP Rick Graziani graziani@cabrillo. edu 46
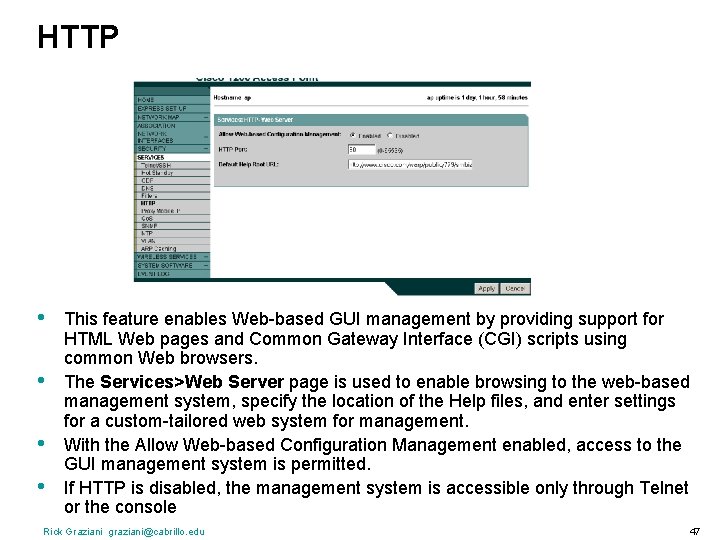
HTTP • • This feature enables Web-based GUI management by providing support for HTML Web pages and Common Gateway Interface (CGI) scripts using common Web browsers. The Services>Web Server page is used to enable browsing to the web-based management system, specify the location of the Help files, and enter settings for a custom-tailored web system for management. With the Allow Web-based Configuration Management enabled, access to the GUI management system is permitted. If HTTP is disabled, the management system is accessible only through Telnet or the console Rick Graziani graziani@cabrillo. edu 47
Configure an AP as a repeater Lab 5. 4. 8: Configure an AP as a repeater through the GUI – Page 127 Lab 8. 3. 3. 2: Configure an AP as a repeater using WEP through the GUI – page 230 Rick Graziani graziani@cabrillo. edu 48
Ch. 5 – Access Points
- Slides: 49