Certifying Authorities Liability under PKI A Global Perspective
Certifying Authorities Liability under PKI: A Global Perspective Seema Sharma Senior Partner Vakul Corporate Advisory © All rights reserved, 2010
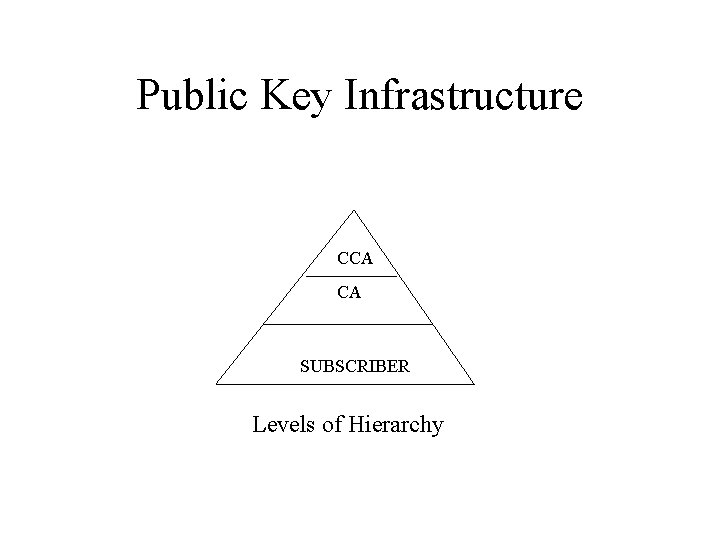
Public Key Infrastructure CCA CA SUBSCRIBER Levels of Hierarchy
A PKI system is much more than the ‘subordinatesuperior’ relationship existing between the Certifying Authorities and the Controller. It is a set of policies, processes, server platforms, software and workstations used for the purpose of administering Electronic Signature and publicprivate key pairs, including the ability to generate, issue, maintain, and revoke public key certificates.
PKI represents a brand new system of creating and authenticating digital ‘binding’ relationships.
This multiple party system of creating and authenticating digital ‘binding’ relationships is based on trust. Basically it involves: (a) an individual or entity identified by the certificate (Subscriber); (b) the issuer of the certificate, which includes identification and authentication of subject (subscriber) information contained in the certificate (Certifying Authority); and (c) the company, agency or individual relying on the certificate (Relying Party).
Creating Binding Linkages In order to create ‘binding linkage’ between the subscriber and the CA one needs ‘binding policies’. These policies in turn define the level of trust a relying party shall put forth in the Certifying Authority’s overall certificate issuance and management process.
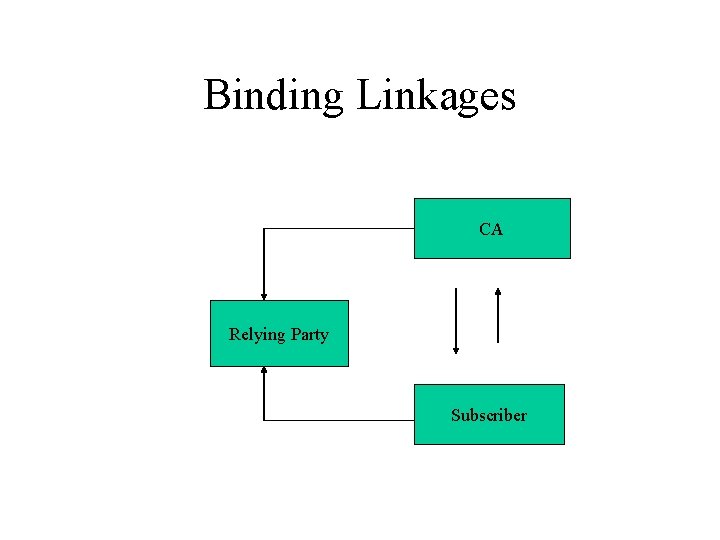
Binding Linkages CA Relying Party Subscriber
It is the Controller, who provides a template for such binding linkages in the form of Certification Policy Statement* (CPS) It is prudent that CPS must define the obligations and liabilities of the parties involved in issuing, managing, and processing certificates. *The IETF Framework [Internet Engineering Task Force] defines the Certification Practice Statement (CPS) as the “statement of practices which a certification authority employs in issuing certificates”.
The CPS takes a life cycle, or “cradle-to-grave, ” approach to describing certification processes. It not only describes the CA’s establishment, start-up procedures, but also information about issuing, managing, using, suspending, activating, revoking and expiration of Certificates.
The CPS is intended to legally bind all parties that create, use, and validate Signature Certificates within the context of the Certification practices of the Certifying Authority.
In the nut shell, CA being a trusted third party has a set of obligations towards the subscribers and the relying party. It is for the CA’s to create and maintain this bond of trust by adhering to the CPS template created by the Controller.

PKI: Bond of Trust CCA CA S R CPS template S = subscribers R= relying party
Difficulty arises when CPS remains a piece of paper, and is not internalised by CAs. CPS is not a static policy document, it is a dynamic policy document. It needs to be reviewed and updated frequently for the maintenance of that bond of trust.
Indian Perspective to CA Liability
Functions of Controller • • • Supervision over activities of CAs Standards to be maintained by CAs Duties of CAs Certifies public keys of CAs Resolves conflict of interest between CAs and the subscribers
CCA-----CA • • • Suspension of Licence CA to follow procedures CA to ensure compliance of the IT Act Display of Licence Surrender of Licence Disclosure
CA-----Subscriber • CA to issue Electronic Signature Certificate (ESC) • Representations upon issuance of DSC • Suspension of DSC • Revocation of DSC • Notice of suspension or revocation
Globalization of PKI
The beauty of PKI lies in the fact that across the world the basic law related to electronic signatures (including digital signatures) talk in one legal language. In other words, across the world there is harmonization of laws on PKI.
Surveyed laws related to PKI of more than 45 countries and found that the basic law on PKI remains static – whether it is across Asia-Pacific, U. S (including its various States)- Canada or Europe.
PKI harmonization has made the proverb: “East is East and West is West, twain shall never meet” turn on its head. One of the benefits: to facilitate seamless ecommerce across the countries and continents.
Why seamless e-commerce is not happening?
One of the basic reasons is lack of cross-certification among CAs across the countries. In fact, more and more subscribers want cross certification to happen as e-commerce is now moving towards ‘age of maturity’, i. e. , realization of borderless and seamless e-commerce.
Cross certification in India • The IT Act permits cross certification by recognition of foreign CA • Recognition by Controller, previous approval of Central Government, notification in official gazette • The ESC issued by such foreign CA is valid for IT Act
Cross certification practices among CAs of different countries would create a ‘Global PKI Platform’. A beginning can be made at this Asia PKI Forum. Yes, from the liability perspective – CAs obligations towards the subscribers and the relying parties (in the event of cross-certification) will increase. But one cannot ignore the tangible benefits to CA’s business model.
It is strange that at one level we talk about PKI harmonization across the world and at the other we are reluctant in granting global acceptability to locally issued signature certificates by the licensed CAs.
Legal relevance of time stamping
Under Regulation 3 of the Information Technology (Certifying Authorities) Regulations, 2001, articulates that CA shall use methods, which are approved by the Controller to provide time stamping service for its subscribers;
Illustration 1: In the case of death of a subscriber, how will it be proved that the ‘deceased subscriber’ had digitally signed an electronic document during his lifetime? The use of ‘Time Stamping Service’ of electronic document will be quite effective in creating the digital evidence and ascertaining whether the said electronic document was created or signed at (or before) a particular point of time. When a digitally signed document must live beyond the expiration date of its certificate, a secure time stamp can prove that the record was signed during the valid period of the certificate.
Illustration 2: From the point of preservation and retention of electronic records, time stamping is quite crucial.
Illustration 3: From the point of audit of documents and records or information processed and maintained in electronic form, a practice of time stamping could be quite useful.
Illustration 4: Validity of contracts formed through electronic means will carry an ‘extra evidentiary edge’ when supported by time stamping.
“ It's not enough to be up to date; you have to be up to tomorrow. ” -David Ben-Gurion
Thanks Seema Sharma, Senior Partner Vakul Corporate Advisory Email: seekat@gmail. com © All rights reserved, 2010
- Slides: 34