CERTIFIED PROTECTION PROFESSIONAL CPP Certification Examination Review October
CERTIFIED PROTECTION PROFESSIONAL (CPP) Certification Examination Review October 2017 Dennis Shepp, CPP
SUBJECTS (DOMAINS) Business Security Principles Information Crisis Personnel Security – Investigations. Principles & Physical Security & Practices Management Security Practices CERTIFIED PROTECTION PROFESSIONAL (CPP) Certification Examination Review DOMAIN 1 – Security Principles & Practices (21%) DOMAIN 2 – Business Principles & Practices (13%) DOMAIN 3 – Investigations (10%) DOMAIN 4 – Personnel Security (12%) DOMAIN 5 – Physical Security (25%) DOMAIN 6 – Information Security (9%) DOMAIN 7 – Crisis Management (10%)
CERTIFIED PROTECTION PROFESSIONAL (CPP) Certification Examination Review 4 DOMAIN 4 – PERSONNEL SECURITY (12%) October 2017 Dennis Shepp, CPP
CERTIFIED PROTECTION PROFESSIONAL (CPP) Certification Examination Review Task 04/01 Develop, implement, and manage background investigations for hiring, promotion, or retention of individuals Task 04/02 Develop, implement, manage, and evaluate policies, procedures, programs and methods to protect individuals in the workplace against human threats (for example, harassment, violence) Task 04/03 Develop, implement, and manage executive protection programs October 2017 Dennis Shepp, CPP
CERTIFIED PROTECTION PROFESSIONAL (CPP) Certification Examination Review Task 04/01 Develop, implement, and manage background investigations for hiring, promotion, or retention of individuals October 2017 Dennis Shepp, CPP
CERTIFIED PROTECTION PROFESSIONAL (CPP) Certification Examination Review Knowledge of: 04/01/01 Background investigations and personnel screening techniques 04/01/02 Quality and types of information sources 04/01/03 Screening policies and guidelines 04/01/04 Laws and regulations pertaining to personnel screening October 2017 Dennis Shepp, CPP
Task 4. 1. 1 Develop, implement, and manage background investigations for hiring, promotion, or retention of individuals explaining background investigations and personnel screening techniques. Chapter 4. 5 DATA COLLECTION POA: Investigations, (Kindle Locations 19075 -19076) • initially focuses on information provided by the applicant. • Typically found in the employment application, personal history questionnaire, résumé, and other biographical documents. • No single tool should be used to screen applicant. • Detailed application process • Application review – examine red flags (4. 6. 1) • Applicant interviews (initial – reviews supplied data in application &resume)
• At final selection stage: o Screening: § Drug § Psychological 4. 8 INVESTIGATION PROCEDURES, POA: Investigations (Kindle Locations 19231 -19233) • Most common resources: security or assets protection department - human resources department - outside consumer reporting and investigative agency. 4. 8. 4 DATA ANALYSIS, POA: Investigations • Adverse information verified – investigated REVIEW ASIS Pre-employment & Background Screening Guideline (ASIS GDL PBS-2009)
Task 4. 1. 2 Develop, implement, and manage background investigations for hiring, promotion, or retention of individuals explaining the quality and types of information sources. 3. 5 INFORMATION SOURCES, POA: Investigations, (Kindle Locations 18469 -18474). • Primary sources: o Interviews with individuals o Direct observations of people, places, or events • Secondary sources include these: o Government-maintained public records o Commercial record sources o Annual reports and other company records. o News and other media sources
CHAPTER 9 APPLICANT SCREENING PROCESS Preemployment Screening Guideline (ASIS)
Task 4. 1. 4 Develop, implement, and manage background investigations for hiring, promotion, or retention of individuals explaining the laws and regulations pertaining to personnel screening. 4. 4. 5 SEVEN EASY STEPS TO A COMPREHENSIVE PREEMPLOYMENT SCREENING POLICY, POA: Investigation page 165 4. 4. 3 LIABILITY ISSUES, POA: Investigations o Protect organization from issues relating to vicarious liability 4. 4. 4 INDUSTRY REGULATIONS POA: Investigations • Generally, the higher the level of responsibility, the more involved the screening should be. • Consider the ramifications of incomplete or incompetent performance of particular jobs.
• Laws vary, but accidents and injuries that result from employee error or incompetence often become the employer’s responsibility. • Related lawsuits and settlements cost a substantial amount of money and may actually put a company out of business. POA Investigation 4. 4. 5 Page 165 4. 4. 4 INDUSTRY REGULATIONS • Proper data collection • Effective background screening and investigation • Data analysis and sound hiring practices • Requires corporate policy and ethical compliance outlined to guide IU
• USA laws and regulations do not impact foreign investigations outside of USA/Canada/UK – HOWEVER – policies & procedures for investigations should follow ethical standards which meet western legal requirements. • Corporate legal counsel should be consulted
Task 4. 1. 3 Develop, implement, and manage background investigations for hiring, promotion, or retention of individuals explaining the screening policies and guidelines. 4. 4. 5 SEVEN EASY STEPS TO A COMPREHENSIVE PREEMPLOYMENT SCREENING POLICY, POA: Investigation (Kindle Location 19032). pge 165 • Seven steps for pre-employment screening o Create clearly written, well-defined job descriptions for all positions. o Assess the risk of each job classification in terms of reasonable (or foreseeable) potential for problems o Based on the preceding risk assessment, determine the scope of preemployment screening for each job classification.
o Work with human resources and legal personnel to develop an appropriate hiring packet. o Establish criteria for evaluating information. o Communicate the policy o Periodically review POA; LEGAL ISSUES CHAPTER 4. 4 ADMINISTRATIVE LAW, (Kindle Locations 11400 -11406). • In some parts of the world, databases containing criminal records are not digitized, are not centralized, or are nonexistent. • Fraudulent criminal records, employment history, credentialing, and education complicates. • Privacy laws may tightly control the dissemination and use of records.
• The security practitioner should work closely with human resources personnel to understand what data is available, how reliable it may be, and how it can be employed in the hiring process.
CERTIFIED PROTECTION PROFESSIONAL (CPP) Certification Examination Review Task 04/02 Develop, implement, manage, and evaluate policies, procedures, programs and methods to protect individuals in the workplace against human threats (for example, harassment, violence) October 2017 Dennis Shepp, CPP
CERTIFIED PROTECTION PROFESSIONAL (CPP) Certification Examination Review Knowledge of: 04/02/01 Protection techniques and methods 04/02/02 Threat assessment 04/02/03 Prevention, intervention and response tactics 04/02/04 Educational and awareness program design and implementation 04/02/05 Travel security program 04/02/06 Laws, government, and labor regulations regarding organizational efforts to reduce employee substance abuse October 2017 Dennis Shepp, CPP
Task 4. 2. 1 Develop, implement, manage, and evaluate policies, procedures, programs and methods to protect individuals in the workplace against human threats (for example, harassment, violence) explaining protection techniques and methods ASIS/SHRM WVPI. 1 -2011 Workplace Violence Standard, page 11 -15 • The ASIS General Security Risk Assessment Guideline, describes the risk assessment process. • Evaluate current policy & procedures (PDCA Cycle) • Evaluate existing physical security (PDCA Cycle) • Pre-employment screening • Needs assessment – threat assessment • Prevention is key - Policy and procedures (harassment & workplace violence) as outlined in ANSI/ASIS OSM. 1 -2017 (9. 5. 3 OHS) page 32
• Establish policy & procedures (recognition, reporting, action) • Employee awareness programs • Appropriate physical security • Contract SME’s.
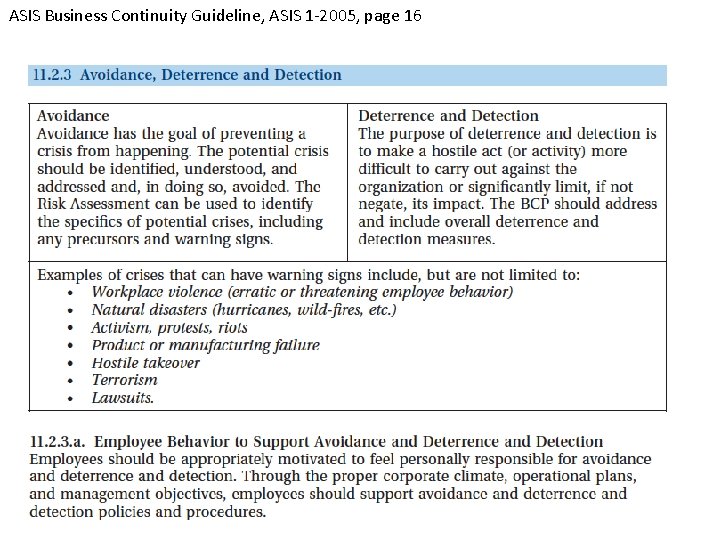
ASIS Business Continuity Guideline, ASIS 1 -2005, page 16
Task 4. 2. 2 Develop, implement, manage, and evaluate policies, procedures, programs and methods to protect individuals in the workplace against human threats (for example, harassment, violence) explaining threat assessments. ASIS/SHRM WPVI. 1 -2011 Workplace Violence Standard page 29 • Early actions by the threat management team – consult with an internal or external threat assessment professional for comprehensive assessment of violence risk – mitigates to manage the risks. • Engage internal or external threat assessment professional to address and mitigate issues. • Conduct a Violence Risk Assessment – refer to methodology in ASIS General Risk Assessment Guideline (next slide)

Task 4. 2. 3 Develop, implement, manage, and evaluate policies, procedures, programs and methods to protect individuals in the workplace against human threats (for example, harassment, violence) explaining prevention, intervention and response tactics. ASIS/SHRM WPVI. 1 -2011 Workplace Violence Standard, 6. 2. 8 page 19 -20 (Prevention strategies) • Physical security measures • Effective employment screening measures. • Policies and procedures • Conflict resolution and mediation process • Awareness program ANSI/ASIS ORM. 1 -2017 CHAPTER 8 THREAT RESPONSE & INCIDENT MANAGEMENT; (A. 9. 1. 2. and 9. 5. 3. ) • Policies & procedures with guidelines to identify & address workplace harassment and violence. (OHS requirement)
• Contained in an organization’s Code of Conduct to establish organizational norms 8. 2 ENCOURAGING THE REPORTING OF PROBLEMATIC BEHAVIOR • Awareness programs explaining warning signs and encouraging reporting 8. 3 INCIDENT MANAGEMENT PROCESS • Outlines the response tactics • Review Figure 1: Overview of the Incident Management Process in Non-Emergency Situations.
Task 4. 2. 4 Develop, implement, manage, and evaluate policies, procedures, programs and methods to protect individuals in the workplace against human threats (for example, harassment, violence) explaining the educational and awareness program design and implementation. 5. 5 GENDER DISCRIMINATION AND SEXUAL HARASSMENT, POA: Legal Issues (Kindle Location 12076). • US LAWS QUOTED – ETHICS & BEST PRACTICE DICTATE THE PRINICPLES ARE INTERNATIONAL GUIDELINES • Employers need to be aware of the risks associated with gender bias in the workplace appropriate measures to remove it. • Establishing policies that treat men and women as equally as possible is the first step in a solution.
5. 4 THE SECURITY ROLE IN EQUAL EMPLOYMENT OPPORTUNITY AND AFFIRMATIVE ACTION, POA: Legal Issues, (Kindle Locations 12035 -12036). • Strong commitment to the equal employment opportunity/ affirmative action program = recognizing the importance of reducing financial risk to the company. POA Security Management & ASIS Workplace Violence Standard, 2011 • US LAWS QUOTED – ETHICS & BEST PRACTICE DICTATE THE PRINICPLES ARE INTERNATIONAL GUIDELINES • Employee awareness programs lie at the heart of a successful program to ensure adequate prevention and management • Must have senior management support
Task 4. 2. 6 Develop, implement, manage, and evaluate policies, procedures, programs and methods to protect individuals in the workplace against human threats (for example, harassment, violence) explaining the laws, government, and labor regulations regarding organizational efforts to reduce employee substance abuse. LAWS CONCERNING SUBSTANCE ABUSE VARY INTERNATIONALLY – FOCUS ON LIABILITY ISSUES WHICH ARE A BEST PRACTICE & GLOBAL POA: Security Management; Chapter 11. 5 • Liability - substance abusers are more likely to have accidents and get injured. • Vicarious liability – employee “agent” of employer. 11. 8. 1 • Drug-free workplace policy POA: Legal Issues, 11. 8. 1. • Criminal laws governing the use of abused substances.
• Recent high-profile cases have brought more attention to business ethics. • The reason may be that the unethical behavior has caused widespread harm. • One ill effect is the vicarious liability employers bear for the negligent action of employees. • Another is the damage that such cases can cause to corporate reputations and to the image of business in general. 9. 5. 4 ANSI/ASIS ORM. 1 -2017 Incident Monitoring, Reporting and Investigations – policies and procedures for Substance Abuse Testing
Task 4. 2. 5 Develop, implement, manage, and evaluate policies, procedures, programs and methods to protect individuals in the workplace against human threats (for example, harassment, violence) explaining travel security programs. 4. 2. 2 ASSETS PROTECTION IN VARIOUS SETTINGS, POA: Security Management • Corporate safeguards: Domestic and international travel security. 4. 3. 2 GLOBALIZATION IN BUSINESS, POA: Security Management • Globalization makes it necessary for assets protection managers to consider a wider variety of customs, cultures, laws, business practices, economic factors, language issues, workforce characteristics, and travel requirements.
POA, Security Mgmt, pge; 267; Information Security pges 18, 35) • Travel for local and broader - employee and executive • Local –policies and awareness for driving • Broader – Travel research (customs, register with embassy, assessments by security, travel low profile, provide advice on how to react to incidents, who to call, register travel details with security, Health history, subscribe to travel services etc. )
CERTIFIED PROTECTION PROFESSIONAL (CPP) Certification Examination Review Task 04/03 Develop, implement, and manage executive protection programs October 2017 Dennis Shepp, CPP

CERTIFIED PROTECTION PROFESSIONAL (CPP) Certification Examination Review Knowledge of: 04/03/01 Executive protection techniques and methods 04/03/02 Risk analysis 04/03/03 Liaison and resource management techniques 04/03/04 Selection, costs, and effectiveness of proprietary and contract executive protection personnel October 2017 Dennis Shepp, CPP
Task 4. 3. 1 Develop, implement, and manage executive protection programs, explaining executive protection techniques and methods. 9. 3 BASICS OF EXECUTIVE PROTECTION POA: Security Management; • Best approach is to establish a crisis management team during the preplanning stage. • The person who performs the in-person, up-close service — who walks, rides, and flies with the executive— is usually called the EP specialist.
• Six principles guide EP: o Prevent and avoid danger. o Realize that anyone can protect anyone. o Don’t stop to think. o Keep clients out of trouble. o Understand the security vs. convenience continuum. o Rely on brains, not technology. • Collecting information – the advance assessment (good advance reduces exposure by smoothing logistics) • The choreography (maneuvering) used by the EP specialist to physically move about with the subject is called “working the principal. ” • Avoid the threat – not confront it.
• Integrate people, equipment and PPS systems • Starts with employee selection & screening – key for EPS • Never leave the building with Principal without conducting a risk assessment
Task 4. 3. 2 Develop, implement, and manage executive protection programs, describing the risk analysis. 9. 6 BASICS OF EXECUTIVE PROTECTION POA: Security Management; • Conducting an EP risk assessment, the specialist must consider two factors. o The threats that the executive faces must be analyzed based on multiple considerations such as the executive’s position with the employer, access to and level of exposure among potential adversaries, access to wealth or other lifestyle attributes, publicity, and travel practices. o The specialist must assess the likelihood that threats could be carried out successfully
Task 4. 3. 3 Develop, implement, and manage executive protection programs, describing the liaison and resource management techniques. 9. 11 PROTECTION RESOURCES POA: Security Management • Police resources • Public and subscribed news services • Networking with professional contacts • A key phrase to remember in executive protection is “use your resources. ”
Task 4. 3. 4 Develop, implement, and manage executive protection programs, describing the selection, costs, and effectiveness of proprietary and contract executive protection personnel. POA: SECURITY OFFICER OPERATIONS; CHAPTER 1 UNDERSTANDING SECURITY OFFICER OPERATIONS (Page 19) • Contract security costs can be lower – detailed specifications and competency expectations should be detailed and enforced • Issues – dependability of EP specialists (turnover) • If contracted – does control over quality get compromised? • Analyze the cost between in-house and contract – which is better?
• Consider: o Liability issues o Workers’ Compensation o Labor relations • EP is VERY expertise specific – competencies may NEED to be contracted.
CERTIFIED PROTECTION PROFESSIONAL (CPP) Certification Examination Review PRACTICE EXAM QUESTIONS October 2017 Dennis Shepp, CPP
A general statement of the way an organization implements a policy, BEST describes which of the following? a. A policy b. A procedure c. A practice d. A standard
A general statement of the way an organization implements a policy, BEST describes which of the following? a. A policy b. A procedure c. A practice d. A standard ASIS GDL PBS-2009, “Pre-employment and Background Screening Guideline, page 9
Which of the following BEST describes the personnel who are often described as the “first line of defense” in the selection of quality and risk-free applicants for the organization? a. Background Investigator b. HR personnel c. Security Manager d. Contracted Recruiter
Which of the following BEST describes the personnel who are often described as the “first line of defense” in the selection of quality and risk-free applicants for the organization? a. Background Investigators b. HR personnel c. Security Manager d. Contracted Recruiter ASIS GDL PBS-2009, “Pre-employment and Background Screening Guideline, page 10
The Sarbanes-Oxley Act of 2002, requires, which of the following: . a. Prohibits discrimination in employment on the basis of bankruptcy history. b. Recommends publicly traded companies conduct background checks on certain positions of trust. c. Prohibits the use of the polygraph for preemployment screening of employees. d. Recommends the use of credit checks for preemployment screening of employees.
The Sarbanes-Oxley Act of 2002, requires, which of the following: . a. Prohibits discrimination in employment on the basis of bankruptcy history. b. Recommends publicly traded companies conduct background checks on certain positions of trust. c. Prohibits the use of the polygraph for preemployment screening of employees. d. Recommends the use of credit checks for preemployment screening of employees. ASIS GDL PBS-2009, “Preemployment and Background Screening Guideline, page 15
When using a third-party to conduct preemployment background investigations, which of the following statements is correct? a. The third party’s judgment of the background investigation results should be considered final. b. The accountability for the final evaluation of the background investigation remains with the employer. c. Person’s with any form of criminal history should never be recommended for hiring. d. The age of any adverse information and the age of the applicant at the time of the adverse incident is not relevant.
When using a third-party to conduct preemployment background investigations, which of the following statements is correct? a. The third party’s judgment of the background investigation results should be considered final. b. The accountability for the final evaluation of the background investigation remains with the employer. c. Person’s with any form of criminal history should never be recommended for hiring. d. The age of any adverse information and the age of the applicant at the time of the adverse incident is not relevant. ASIS GDL PBS-2009, “Preemployment and Background Screening Guideline, page 42

When establishing internal and external complaint and grievance procedures, which of the following procedures should to be included? a. Identification of the root causes b. Levels of the organization excluded from the procedures. c. Details on the required experience and training of the investigators. d. Identification of the penalties for breach of policy.
When establishing internal and external complaint and grievance procedures, which of the following procedures should to be included? a. Identification of the root causes b. Levels of the organization excluded from the procedures. c. Details on the required experience and training of the investigators. d. Identification of the penalties for breach of policy. ANSI/ASIS ORM. 1 -2017, “Security and Resilience in Organizations and their Supply Chains” (2017) , page 26
Organizations are required by standards (ANSI/ASIS ORM. 12017) to report and investigate incidents. Which of the following types of incidents are stipulated? a. Incidents involving casualties, allegations of abuse or substance abuse. b. Incidents involving missing property and subordination to a supervisor. c. HR reporting employees arriving late for work and abusing sick time. d. Incidents with allegations of personal relationships between employees.
Organizations are required by standards (ANSI/ASIS ORM. 1 -2017) to report and investigate incidents. Which of the following types of incidents are stipulated? a. Incidents involving casualties, allegations of abuse or substance abuse. b. Incidents involving missing property and subordination to a supervisor. c. HR reporting employees arriving late for work and abusing sick time. d. Incidents with allegations of personal relationships between employees. ANSI/ASIS ORM. 1 -2017, “Security and Resilience in Organizations and their Supply Chains” (2017) , page 26
In an armed workplace violence incident, the program assumes that an effective response by properly trained personnel will occur if the perpetrator is not diverted. This means that one of the BEST planned responses should be which of the following? a. The quickest responding security force, closest to the incident. b. Company security personnel from all posts respond to the scene as soon as possible. c. Assigned supervisors who are trained to deal with conflict. d. Response by correctly trained, armed personnel who will handle the situation.
In an armed workplace violence incident, the program assumes that an effective response by properly trained personnel will occur if the perpetrator is not diverted. This means that one of the BEST planned responses should be which of the following? a. The quickest responding security force, closest to the incident. b. Company security personnel from all posts respond to the scene as soon as possible. c. Assigned supervisors who are trained to deal with conflict. d. Response by correctly trained, armed personnel who will handle the situation. POA: Security Management; (Kindle Location 8228). ASIS International. Kindle Edition.
Like a typical security program, a violence risk assessment program employs which of the following tactics as a countermeasure to a workplace violence incident? a. Delay, detection and response b. Diversion, delay and response c. Deterrence, delay, and detection d. Diversion, detection, Response
Like a typical security program, a violence risk assessment program employs which of the following tactics as a countermeasure to a workplace violence incident? a. Delay, detection and response b. Diversion, delay and response c. Deterrence, delay, and detection d. Diversion, detection, Response POA: Security Management; (Kindle Location 8232). ASIS International. Kindle Edition.
The most important elements of a violence risk assessment program are which of the following? a. Behavioral recognition, diversion, delay and adequate response. b. Behavioral recognition, notification, assessment, and adequate response. c. Detection, diversion, delay, and response. d. Detection, deterrence, delay and response.
The most important elements of a violence risk assessment program are which of the following? a. Behavioral recognition, diversion, delay and adequate response. b. Behavioral recognition, notification, assessment, and adequate response. c. Detection, diversion, delay, and response. d. Detection, deterrence, delay and response. ASIS. POA: Security Management; (Kindle Locations 8233 -8234). ASIS International. Kindle Edition.
For security practitioners. the most effective means of preventing workplace violence is which of the following? a. Having a well trained and adequately armed response force available for rapid response. b. Early detection of this behavioral, emotional, and psychological dynamic. c. Providing stronger physical security protection surrounding the facility’s inner, middle and outer perimeters. d. Providing a well trained and adequately armed response force as part of the proprietary security force.
For security practitioners. the most effective means of preventing workplace violence is which of the following? a. Having a well trained and adequately armed response force available for rapid response. b. Early detection of this behavioral, emotional, and psychological dynamic. c. Providing stronger physical security protection surrounding the facility’s inner, middle and outer perimeters. d. Providing a well trained and adequately armed response force as part of the proprietary security force. POA: Security Management; (Kindle Location 8310). ASIS International. Kindle Edition.
“In a workplace violence assessment, the more one knows about the aggressor’s emotional history, violence history, recent behavior, reactions to stress, and current stressors, the better one can assess the aggressor’s current level of violence risk to the company or its employees. ” This can also be referred to as: a. “The best reaction to workplace violence is management support. ” b. “The best predictor of workplace violence is investigating threats. ” c. “The best predictor of future behavior is past behavior” d. “Workplace violence is predicable when investigated properly. ”
“In a workplace violence assessment, the more one knows about the aggressor’s emotional history, violence history, recent behavior, reactions to stress, and current stressors, the better one can assess the aggressor’s current level of violence risk to the company or its employees. ” This can also be referred to as: a. “The best reaction to workplace violence is management support. ” b. “The best predictor of workplace violence is investigating threats. ” c. “The best predictor of future behavior is past behavior” d. “Workplace violence is predicable when investigated properly. ” POA: Security Management; (Kindle Location 8331). ASIS International. Kindle Edition.
If an executive from the organization is kidnapped and made incapable of running the company, the organization can expect three types of financial losses, one of these is: a. The costly loss of corporate revenue due to lost sales. b. The executive’s services will be lost either temporarily or permanently, which can be costly. c. The subsequent lawsuit from the executive’s family for the loss of the executive. d. The government fining the organization for failing to provide adequate security.
If an executive from the organization is kidnapped and made incapable of running the company, the organization can expect three types of financial losses, one of these is: a. The costly loss of corporate revenue due to lost sales. b. The executive’s services will be lost either temporarily or permanently, which can be costly. c. The subsequent lawsuit from the executive’s family for the loss of the executive. d. The government fining the organization for failing to provide adequate security. POA: Security Management; (Kindle Location 6360). ASIS International. Kindle Edition.
The following statement defines a stage in the PDCA Cycle, “One looks at the planning analysis, devises a solution, prioritizes next steps, and develops a detailed action plan. The key word is action. The goal is to develop a plan that will be used actively to engage the organization and address problems and their causes and then to implement that plan. ” The BEST defines which of the following in the PDCA? a. Plan b. Do c. Check d. Act

The following statement defines a stage in the PDCA Cycle, “One looks at the planning analysis, devises a solution, prioritizes next steps, and develops a detailed action plan. The key word is action. The goal is to develop a plan that will be used actively to engage the organization and address problems and their causes and then to implement that plan. ” The BEST defines which of the following in the PDCA? a. Plan b. Do c. Check d. Act POA: Security Management (Kindle Locations 2025 -2028).
When an organization is looking to create a model theft and fraud prevention program, which of the following approaches should they adopt? a. Proactive b. Reactive c. Controlled d. Collaborative
When an organization is looking to create a model theft and fraud prevention program, which of the following approaches should they adopt? a. Proactive b. Reactive c. Controlled d. Collaborative 6. 4. 1 ESTABLISHING A MODEL PREVENTION PROGRAM, POA: Investigations (Kindle Location 4113)

According to Joseph Wells, “Occupational Fraud and Abuse” three (3) factors are present in every fraud. They are: a. Criminal experience; opportunity and needs. b. Financial pressure; opportunity and justification. c. Criminal experience; rationalization and needs d. Financial pressure; needs and rationalization.
According to Joseph Wells, “Occupational Fraud and Abuse” three (3) factors are present in every fraud. They are: a. Criminal experience; opportunity and needs. b. Financial pressure; opportunity and justification. c. Criminal experience; rationalization and needs d. Financial pressure; needs and rationalization. ASIS. POA: Security Management; (Kindle Location 4035).
Which of the following statements is TRUE concerning employee dishonesty? a. Most employees who steal from their employers consider themselves dishonest. b. Employees involved in theft have usually been involved in other prior misconduct at the company. c. Most employees would steal from their employer if given the opportunity. d. Employers have no control over factors which contribute toward employee theft and fraud.
Which of the following statements is TRUE concerning employee dishonesty? a. Most employees who steal from their employers consider themselves dishonest. b. Employees involved in theft have usually been involved in other prior misconduct at the company. c. Most employees would steal from their employer if given the opportunity. d. Employers have no control over factors which contribute toward employee theft and fraud. ASIS. POA: Security Management; (Kindle Locations 42424243). APPENDIX B
A company is interested in purchasing property overseas. They decide to conduct an investigation to evaluate the current property owners, the location, finances and operations of the target property. Which of the following statements is BEST describes this type of investigation? a. Compliance b. Financial c. Background d. Due diligence
A company is interested in purchasing property overseas. They decide to conduct an investigation to evaluate the current property owners, the location, finances and operations of the target property. Which of the following statements is BEST describes this type of investigation? a. Compliance b. Financial c. Background d. Due diligence Chapter 3 Due Diligence; ASIS. POA: Investigations; (Kindle Locations 4242 -4243).
What is the term used to describe when a member of law enforcement or designated agent arrests a perpetrator at the moment they are caught either buying or selling stolen property? a. Sting operation b. Buy-Bust operation c. Undercover investigation d. Incident investigation
What is the term used to describe when a member of law enforcement or designated agent arrests a perpetrator at the moment they are caught either buying or selling stolen property? a. Sting operation b. Buy-Bust operation c. Undercover investigation d. Incident investigation 2. 8. 2 Theft Investigations POA: Investigation (Kindle Locations 18107 -18108)
Which of the following BEST describes “Entrapment”? a. Considered a crime when done by a designated agent. b. Does not require preexisting evidence of similar acts. c. The agent is encouraged to use entrapment to catch employees stealing. d. The agent encourages a person to commit a crime.
Which of the following BEST describes “Entrapment”? a. Considered a crime when done by a designated agent. b. Does not require preexisting evidence of similar acts. c. The agent is encouraged to use entrapment to catch employees stealing. d. The agent encourages a person to commit a crime. 2. 8. 1 Drug Investigations POA: Investigation Entrapment. POA: Investigation (Kindle Location 18047).
A company’s IU is conducting an internal theft investigation in its warehouse. The company investigator has contract external investigators to assist in the project by providing project management, undercover operations, an anonymous caller “Tip Line” and covert CCV monitoring the area. These efforts can be BEST described as: a. Covert surveillance b. Overt surveillance c. Force multipliers d. Undercover operation
A company’s IU is conducting an internal theft investigation in its warehouse. The company investigator has contract external investigators to assist in the project by providing project management, undercover operations, an anonymous caller “Tip Line” and covert CCV monitoring the area. These efforts can be BEST described as: a. Covert surveillance b. Overt surveillance c. Force multipliers d. Undercover operation 1. 6 Investigative Force Multipliers, POA: Investigation (Kindle Location 17190).

Which of the following types of investigations is considered the “the most common type of investigation in many business and organizational settings” ? a. Incident b. Misconduct c. Compliance d. Undercover
Which of the following types of investigations is considered the “the most common type of investigation in many business and organizational settings” ? a. Incident b. Misconduct c. Compliance d. Undercover 1. 4. 1 Incident Investigations. POA: Investigation (Kindle Locations 16914 -16915).
CERTIFIED PROTECTION PROFESSIONAL (CPP) Certification Examination Review 4 DOMAIN October 2017 DOMAIN 4 – PERSONNEL SECURITY (12%) October 2017 Shepp, CPP Dennis Shepp,
- Slides: 84