Cerner Medical Billing HIPAA and PHI Training Revenue
Cerner Medical Billing HIPAA and PHI Training Revenue Cycle Compliance 2017 1303521959_Cerner Medical Billing HIPAA and PHI Training_Rev 004
HIPAA and PHI Training Objectives • This training is designed to help Medical Billing Associates understand the basics of the HIPAA law and how it affects you. • This session will give you a general overview of privacy requirements and the processes that are in place to reduce the risk of unauthorized disclosures of protected information. • This session will provide an overview of proper safeguards to use when releasing patient information during the course of performing your day-to-day duties. BRNDEXP 3. 0 © Cerner Corporation. All rights reserved. This document contains Cerner confidential and/or proprietary information belonging to Cerner Corporation and/or its related affiliates which may not be reproduced or transmitted in any form or by any means without the express written consent of Cerner. 1
Cerner Medical Billing HIPAA and PHI Training • What Is HIPAA? • The Health Insurance Portability and Accountability Act (HIPAA) is a federal law that governs the use, transfer, and disclosure of identifiable health information: • To establish basic privacy and security protection of health information; • To guarantee individuals the right to access their health information and learn how it is used and disclosed; and • To simplify payment for health care. • Why is it important? • Healthcare providers and those using the data for healthcare operations have access to highly confidential information. • The law provides rights for patients, regulations for use and penalties for misuse of private information. BRNDEXP 3. 0 © Cerner Corporation. All rights reserved. This document contains Cerner confidential and/or proprietary information belonging to Cerner Corporation and/or its related affiliates which may not be reproduced or transmitted in any form or by any means without the express written consent of Cerner. 2
Cerner Medical Billing HIPAA and PHI Training • What communication is impacted? • Any information transmitted electronically, recorded, written on paper, or shared in verbal communications. • Why do I have to keep information confidential? • The HIPAA Privacy Rule requires that we keep valuable and sensitive information safe; • We trust our Associates with a wide spectrum of information, and we all share a responsibility for confidentiality; • We want to keep our clients’ patient data safe, and we want to comply with the HIPAA rules and regulations; and • Misusing PHI can result in discipline, legal penalties and loss of trust. BRNDEXP 3. 0 © Cerner Corporation. All rights reserved. This document contains Cerner confidential and/or proprietary information belonging to Cerner Corporation and/or its related affiliates which may not be reproduced or transmitted in any form or by any means without the express written consent of Cerner. 3
Cerner Medical Billing HIPAA and PHI Training • What information is protected? • Generally, any information about a patient’s health condition, demographics, treatment, billing and payment is considered Protected Health Information (PHI). • Unique identifiers for PHI include: • Name; • Address; • Dates of Birth, Admission or Discharge and Death; • Telephone and Fax Numbers; • Email addresses; • Medical Record Numbers; • Health Insurance ID Numbers; • Social Security Numbers; BRNDEXP 3. 0 © Cerner Corporation. All rights reserved. This document contains Cerner confidential and/or proprietary information belonging to Cerner Corporation and/or its related affiliates which may not be reproduced or transmitted in any form or by any means without the express written consent of Cerner. 4
Cerner Medical Billing HIPAA and PHI Training • Unique Identifiers for PHI Continued: • • • Account Numbers; Certificate/License Numbers; Vehicle or Other Device Serial Numbers; Web URL (and email addresses with practice names when coupled with other identifiers); Internet Protocol (IP) Address; Finger or Voice Prints; Photographic Images; Medical History and Treatment; and Financial Information (Insurance and Credit Card Numbers). • The elements in the list, when taken together and in context with a patient’s record, are considered protected health information that must be properly handled and safeguarded. BRNDEXP 3. 0 © Cerner Corporation. All rights reserved. This document contains Cerner confidential and/or proprietary information belonging to Cerner Corporation and/or its related affiliates which may not be reproduced or transmitted in any form or by any means without the express written consent of Cerner. 5
Cerner Medical Billing HIPAA and PHI Training • Personally Identifiable Information (PII) is also protected. This includes information about patients, clients, Cerner, and Cerner Associates. • Driver’s License Number; • Social Security Number; • Bank Account Numbers; • User ID and Passwords (Cerner access, Payer Website access, Client System access); • Financial and operational information; and • Trade secrets. BRNDEXP 3. 0 © Cerner Corporation. All rights reserved. This document contains Cerner confidential and/or proprietary information belonging to Cerner Corporation and/or its related affiliates which may not be reproduced or transmitted in any form or by any means without the express written consent of Cerner. 6
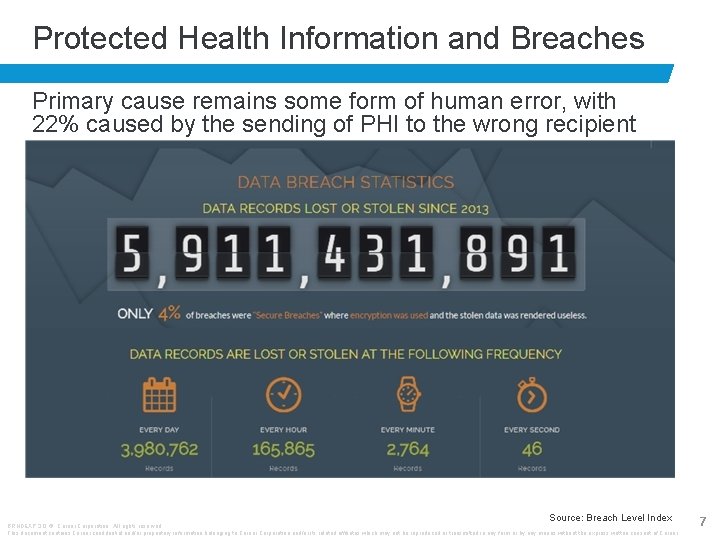
Protected Health Information and Breaches Primary cause remains some form of human error, with 22% caused by the sending of PHI to the wrong recipient Source: Breach Level Index BRNDEXP 3. 0 © Cerner Corporation. All rights reserved. This document contains Cerner confidential and/or proprietary information belonging to Cerner Corporation and/or its related affiliates which may not be reproduced or transmitted in any form or by any means without the express written consent of Cerner. 7
What is Minimum Necessary Usage? • The concept of minimum necessary must be reasonably applied to all situations involving PHI. • Associates must take reasonable measures to protect the privacy of individual patient health information by limiting the amount of information disclosed to the minimum amount necessary to perform a job or complete a function. • You must consider: • What is the minimum amount of information necessary to perform this task? • Does anyone (including you) need to access this information in order to complete a job? BRNDEXP 3. 0 © Cerner Corporation. All rights reserved. This document contains Cerner confidential and/or proprietary information belonging to Cerner Corporation and/or its related affiliates which may not be reproduced or transmitted in any form or by any means without the express written consent of Cerner. 8
Safeguards YOU Can Employ • People consider health information their most confidential information, and we must protect it accordingly • Do not share access credentials; • Do not access PHI that you do not need; • Do not discuss PHI with individuals who do not need to know it; • Do not provide PHI to anyone not authorized to receive it; and • NEVER post any work-related information on Social Media (including u. Cern) unless you have specific permission to do so. BRNDEXP 3. 0 © Cerner Corporation. All rights reserved. This document contains Cerner confidential and/or proprietary information belonging to Cerner Corporation and/or its related affiliates which may not be reproduced or transmitted in any form or by any means without the express written consent of Cerner. 9
Workplace Safeguards – LOCK IT UP! • During after-work hours, weekends, holidays: • All Protected Information must be locked up; • Includes Work-In-Process at desks, mail, file cabinets; and • All faxes and print-outs must be removed from printers. • Breaks and Lunch: • At minimum, turn over PHI on desks; but • Best practice – lock it up! • Do not leave devices unlocked • Ctrl+Alt+Delete, Lock or Windows+L. • Close out sessions when finished or gone for long periods of time. BRNDEXP 3. 0 © Cerner Corporation. All rights reserved. This document contains Cerner confidential and/or proprietary information belonging to Cerner Corporation and/or its related affiliates which may not be reproduced or transmitted in any form or by any means without the express written consent of Cerner. 10
Workplace Safeguards – LOCK IT UP! • Electronic information: • If it is necessary to store confidential information in • • a file, that file must be encrypted and/or password protected; Store on a secure network site, not on devices or portable media (e. g. , flash drive); Do not store on the hard drive of your personal computing device; Delete file when not longer needed for purpose for which it was obtained; and Double delete – delete the file from the Recycle Bin as well. BRNDEXP 3. 0 © Cerner Corporation. All rights reserved. This document contains Cerner confidential and/or proprietary information belonging to Cerner Corporation and/or its related affiliates which may not be reproduced or transmitted in any form or by any means without the express written consent of Cerner. 11
Workplace Safeguards – Transmission • Always use secure means when transmitting confidential information. Examples of secure means are: • A secure file transfer protocol (SFTP) encrypted transmission (ensure that a named account is used for traceability rather than using a generic account); • An encrypted, compressed file using 7 -Zip or Win. Zip can be emailed if the password is emailed separately or communicated by phone; • By mail; • By Fax* with a Cerner standard fax cover sheet; and • By phone. *Outlook fax should not be used, only actual machines BRNDEXP 3. 0 © Cerner Corporation. All rights reserved. This document contains Cerner confidential and/or proprietary information belonging to Cerner Corporation and/or its related affiliates which may not be reproduced or transmitted in any form or by any means without the express written consent of Cerner. 12
Workplace Safeguards – Email • All electronic transmission safeguards apply when transmitting PHI/PII either outside of or within Cerner’s network; • Send encrypted email using Move. IT or Office 365 Message Encryption (if available for use). • As long as email does not include any direct identifiers, email may be sent unencrypted. • Indirect identifiers are: • Medical record numbers, encounter numbers or accession, without any other direct identifiers. • Other internal identifiers not likely to have meaning to external parties. BRNDEXP 3. 0 © Cerner Corporation. All rights reserved. This document contains Cerner confidential and/or proprietary information belonging to Cerner Corporation and/or its related affiliates which may not be reproduced or transmitted in any form or by any means without the express written consent of Cerner. 13
Workplace Safeguards – Mailing • Includes mail, courier, or other commercial delivery system. • Include full first and last name of recipient and their department within the institution or company on the mailing label; • Write “Confidential Information – To be opened by Addressee only” on outside of envelope; • Ensure that PHI cannot be viewed through window of envelope; and • Include the “Protected Health Information Confidential Notice for U. S. Mail and Transport” form in the mailed envelope to inform the recipient that what they have received contains PHI or other confidential information. BRNDEXP 3. 0 © Cerner Corporation. All rights reserved. This document contains Cerner confidential and/or proprietary information belonging to Cerner Corporation and/or its related affiliates which may not be reproduced or transmitted in any form or by any means without the express written consent of Cerner. 14
Workplace Safeguards – Safe Disposal • Printed PHI should only be disposed of in locked • • • shred bins. If bin is full (one can stick hand in slot and pull out papers), use another bin. Never put PHI in desk trash can, break room trash can or any other disposal area outside of work area. Ensure that “trashed” emails are permanently deleted. Ensure that device Recycle Bin is emptied daily. Contact CTS Enterprise Security for assistance in destruction and disposal of data on CD, thumb drive or other portable media. BRNDEXP 3. 0 © Cerner Corporation. All rights reserved. This document contains Cerner confidential and/or proprietary information belonging to Cerner Corporation and/or its related affiliates which may not be reproduced or transmitted in any form or by any means without the express written consent of Cerner. 15
Client Sends PHI via Email • Obtain information needed for completion of duties, then permanently delete the email. • If a reply or forward is necessary, delete the PHI from the reply/forward message. • Do not store email in Outlook. If the message must be retained, scan into proper repository. • Do not refuse to accept the information, but remind clients of the need to keep their patient information secure. BRNDEXP 3. 0 © Cerner Corporation. All rights reserved. This document contains Cerner confidential and/or proprietary information belonging to Cerner Corporation and/or its related affiliates which may not be reproduced or transmitted in any form or by any means without the express written consent of Cerner. 16
OOPS! I Sent That Email/Fax/Claim to the Wrong Person • What to do in the event of any inadvertent disclosure (not just email) or suspected breach. • Escalate upon discovery to: • Direct Manager; and • Revenue Cycle Compliance. • Compliance will provide guidance on notification toc clients and other Cerner teams, which may include: • Community. Works (when the disclosure or breach involves a Community. Works client); • Regulatory Affairs; • Cerner Legal; • Director of GRID Security/Cerner. Works Security; or • Public Relations. BRNDEXP 3. 0 © Cerner Corporation. All rights reserved. This document contains Cerner confidential and/or proprietary information belonging to Cerner Corporation and/or its related affiliates which may not be reproduced or transmitted in any form or by any means without the express written consent of Cerner. 17
Handling a Disclosure or Suspected Breach • Provide as much information on the issue as you can • • Date of disclosure or breach; Time of disclosure or breach; Description of incident; Associate(s) involved; Type of PHI involved; Specific records/data breached; and If the situation that created the issue is still occurring. • If an inadvertent disclosure or breach results from an Associate failing to securely transmit PHI or from inappropriate handling or disposal of PHI, that disclosure will be reported. Corrective action may be warranted. This should never deter you from reporting. Compliance with the law is always the ethical and most appropriate action to take. BRNDEXP 3. 0 © Cerner Corporation. All rights reserved. This document contains Cerner confidential and/or proprietary information belonging to Cerner Corporation and/or its related affiliates which may not be reproduced or transmitted in any form or by any means without the express written consent of Cerner. 18
Thoughts on Social Media • Cerner has embraced social media tools in communicating with clients and consumers, but the following should be kept in mind: • Do not publish “official” opinions unless authorized to do so; • Do not publish confidential or proprietary information; • Activity on Cerner social media accounts is monitored; • Think before you post about Cerner or Cerner clients and • • • partners; Do not position yourself as an official Cerner representative Use your best judgment – you are held responsible for the content you post – forever; Lurk and listen; Engage responsibly; and Be professional BRNDEXP 3. 0 © Cerner Corporation. All rights reserved. This document contains Cerner confidential and/or proprietary information belonging to Cerner Corporation and/or its related affiliates which may not be reproduced or transmitted in any form or by any means without the express written consent of Cerner. 19
Cerner Medical Billing HIPAA and PHI Training • Compliance Team Contacts • Courtney Muehe Courtney. Muehe@cerner. com • Leslie Lapsley llapsley@cerner. com BRNDEXP 3. 0 © Cerner Corporation. All rights reserved. This document contains Cerner confidential and/or proprietary information belonging to Cerner Corporation and/or its related affiliates which may not be reproduced or transmitted in any form or by any means without the express written consent of Cerner. 20
- Slides: 21