CEG 2400 FALL 2012 Chapter 6 Network Hardware


- Slides: 53
CEG 2400 FALL 2012 Chapter 6 Network Hardware, Switching, and Routing 1
NICs (Network Interface Cards) • Connectivity device (Common to every networking device) – Transceiver • Transmits and receives data • Enable device transmission • Operates at the Physical and Data Link layer – Issue data signals – Assemble and disassemble data frames – Interpret physical addressing information • Determines if client can transmit data • Do not analyze information – Added by Layers 3 through 7 OSI model protocols 2
NICs (Network Interface Cards) • NIC dependencies – – Access method (EX. Ethernet) Network transmission speed (1 Gbps) Connector interfaces (RJ-45) Method of connecting to the computers motherboard 3
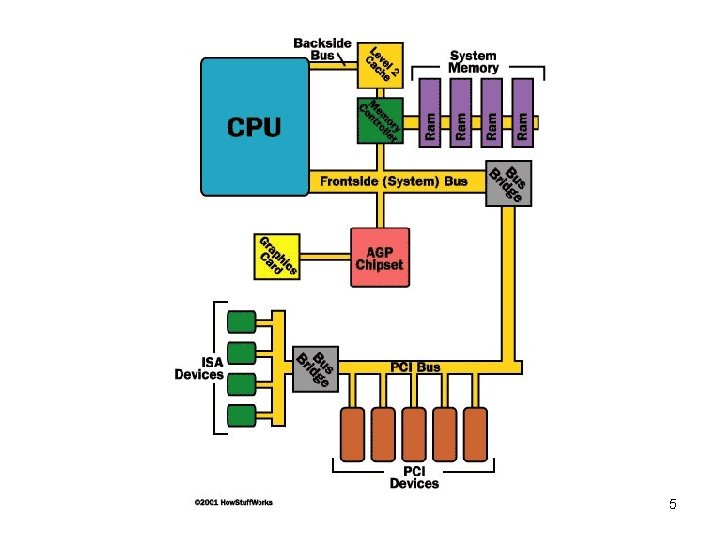
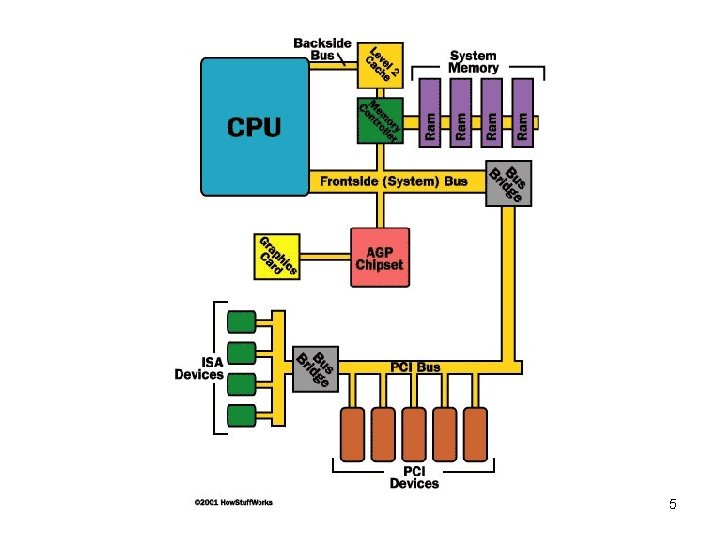
How NICs connect • Bus - signaling pathway in computer – Motherboard uses bus to transmit data to computer’s components • Memory, processor, hard disk, NIC – Differ according to capacity • Defined by data path width and clock speed – Data path size • Parallel bits transmitting at any given time • Proportional to attached device’s speed 4
5
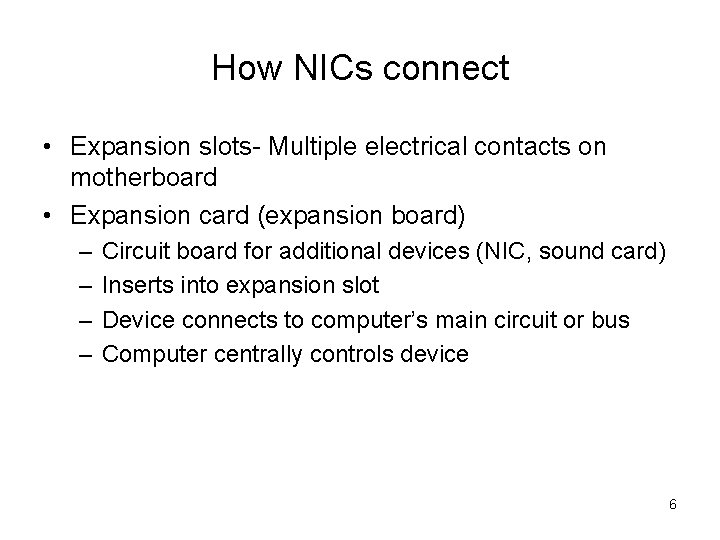
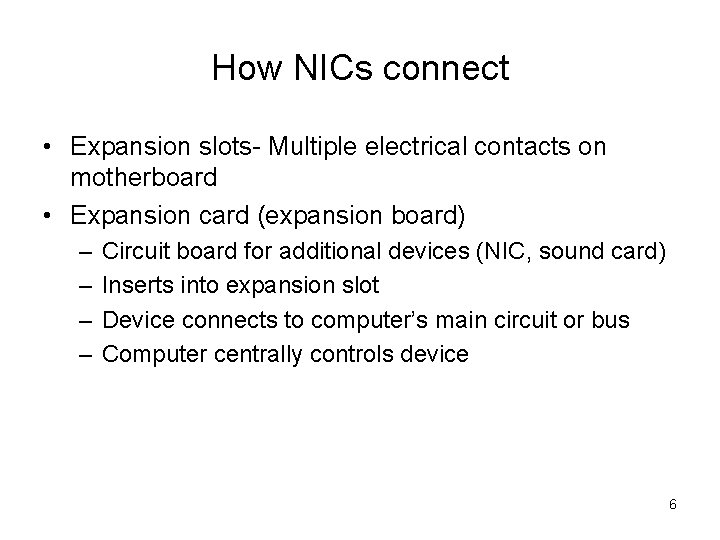
How NICs connect • Expansion slots- Multiple electrical contacts on motherboard • Expansion card (expansion board) – – Circuit board for additional devices (NIC, sound card) Inserts into expansion slot Device connects to computer’s main circuit or bus Computer centrally controls device 6
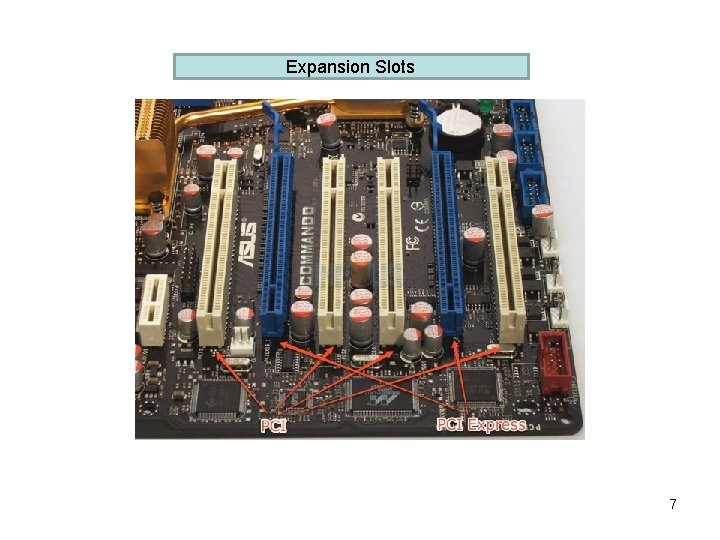
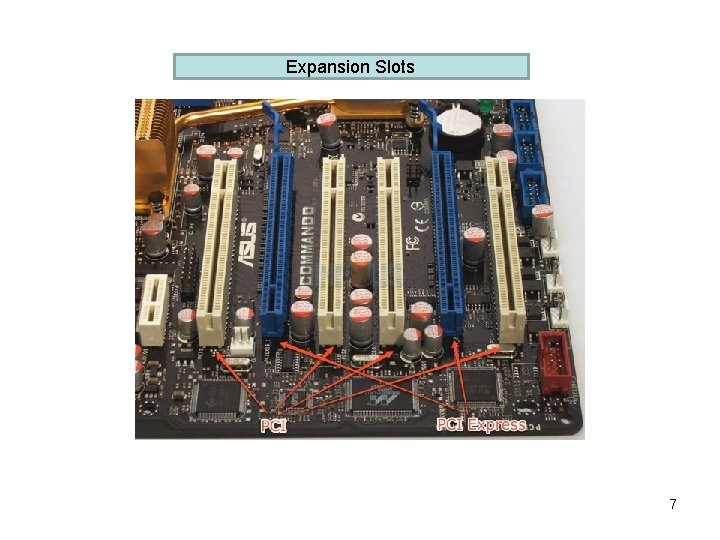
Expansion Slots 7
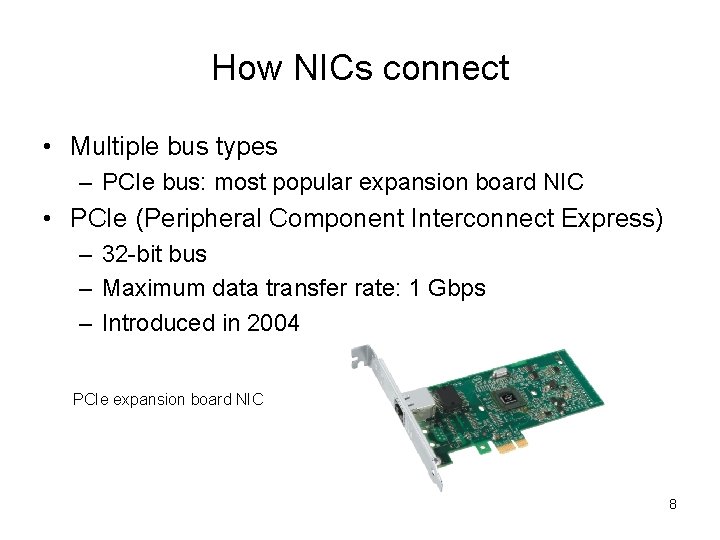
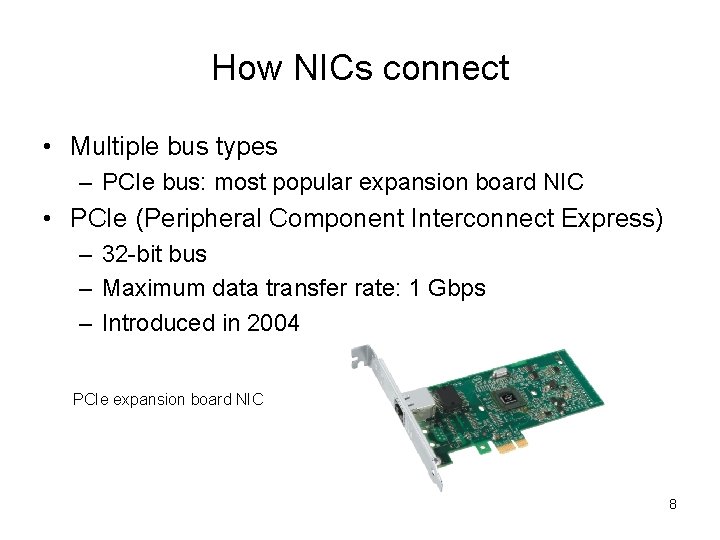
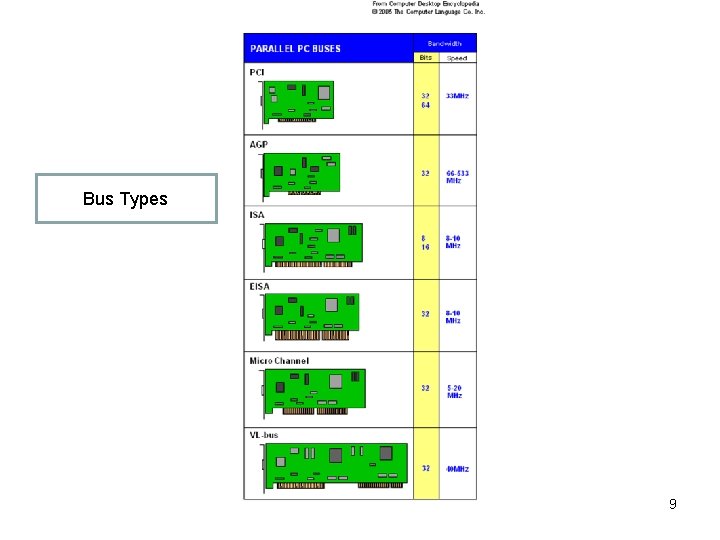
How NICs connect • Multiple bus types – PCIe bus: most popular expansion board NIC • PCIe (Peripheral Component Interconnect Express) – 32 -bit bus – Maximum data transfer rate: 1 Gbps – Introduced in 2004 PCIe expansion board NIC 8
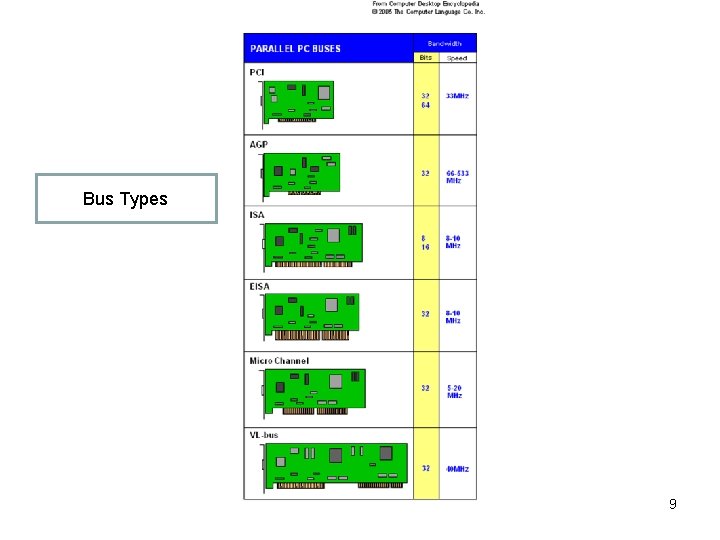
Bus Types 9
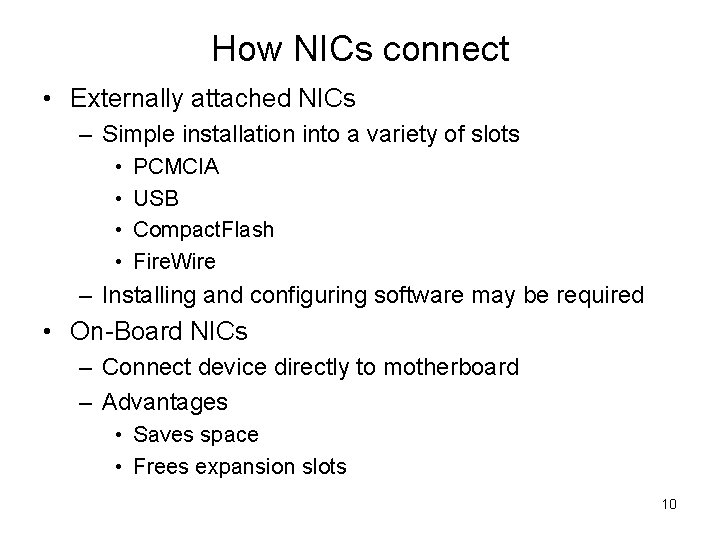
How NICs connect • Externally attached NICs – Simple installation into a variety of slots • • PCMCIA USB Compact. Flash Fire. Wire – Installing and configuring software may be required • On-Board NICs – Connect device directly to motherboard – Advantages • Saves space • Frees expansion slots 10
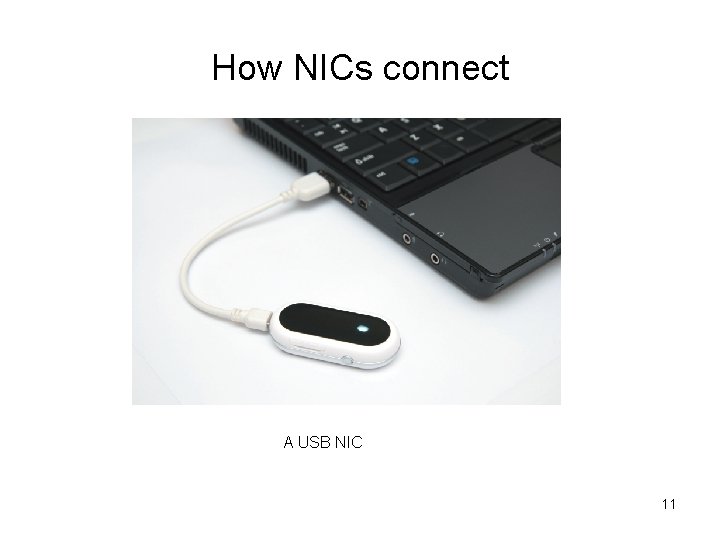
How NICs connect A USB NIC 11

How NICs connect Motherboard with on-board NICs 12
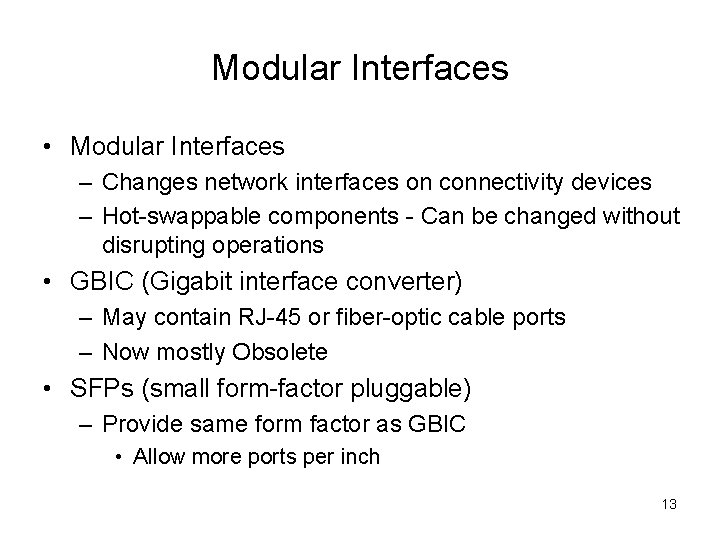
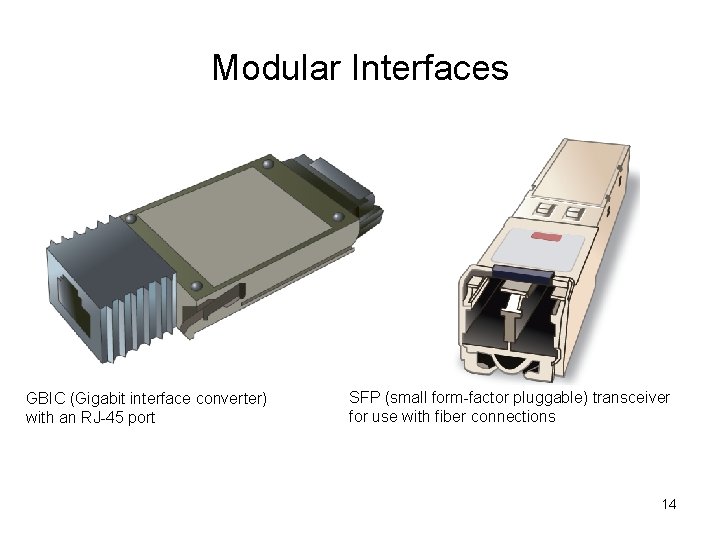
Modular Interfaces • Modular Interfaces – Changes network interfaces on connectivity devices – Hot-swappable components - Can be changed without disrupting operations • GBIC (Gigabit interface converter) – May contain RJ-45 or fiber-optic cable ports – Now mostly Obsolete • SFPs (small form-factor pluggable) – Provide same form factor as GBIC • Allow more ports per inch 13
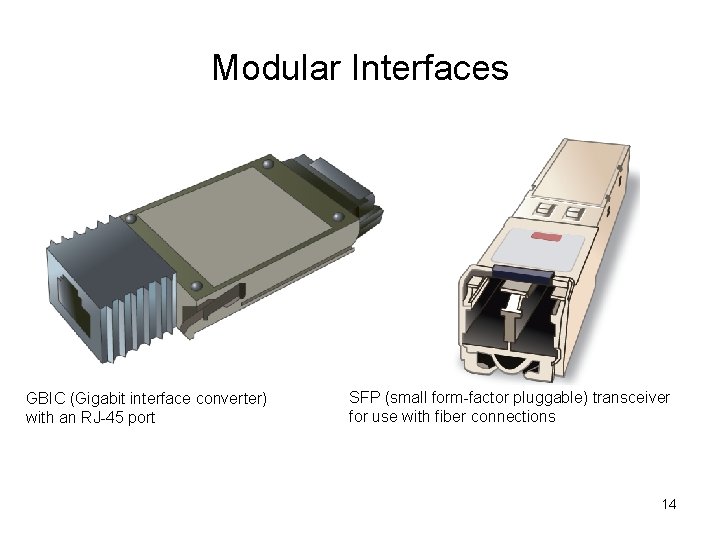
Modular Interfaces GBIC (Gigabit interface converter) with an RJ-45 port SFP (small form-factor pluggable) transceiver for use with fiber connections 14
Repeaters and Hubs • Repeaters – Operate in Physical OSI model layer – No means to interpret data – Just regenerates signal • Hub – Repeater with more than one output port – Typically contains multiple data ports • Patch cables connect printers, servers, and workstations – Most contain uplink port 15
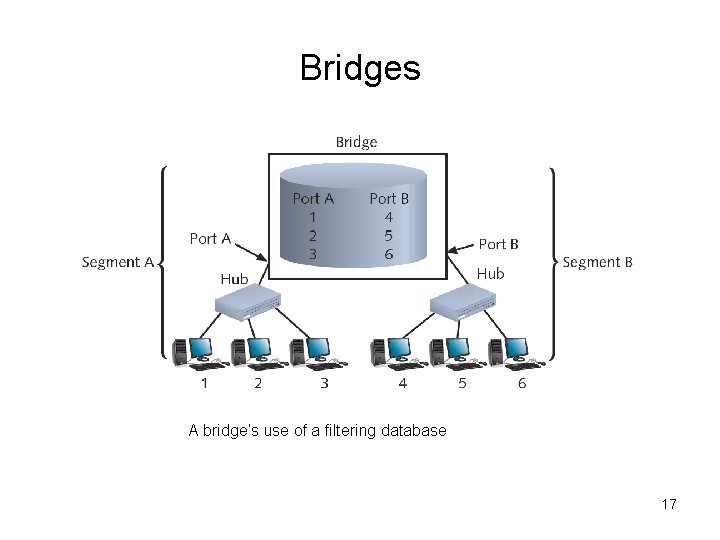
Bridges • • • Device that connect two network segments Operate at Data Link OSI model layer Single input and single output ports Protocol independent Analyze incoming frames and makes decisions on where to direct them by MAC address • Filtering database – Contains known MAC addresses and network locations • Not common anymore 16
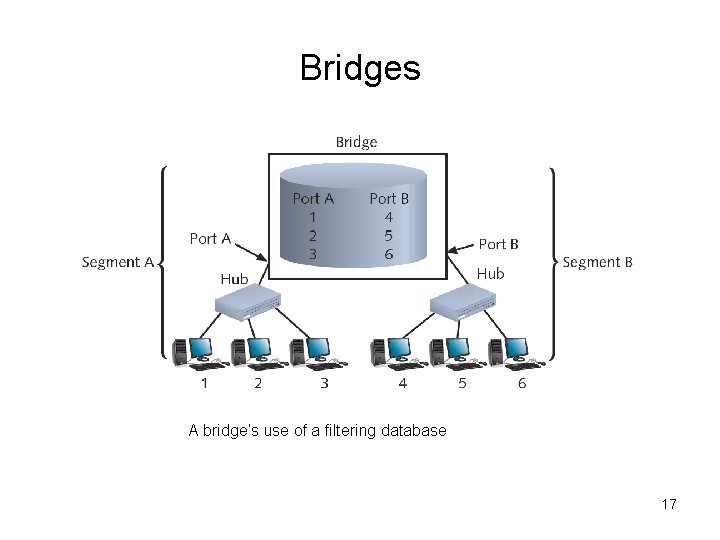
Bridges A bridge’s use of a filtering database 17
Switches • Connectivity devices that subdivide a network into segments • Traditional switches – Operate at Data Link OSI model layer • Modern switches – Can operate at Layer 3 or Layer 4 (blurs line between switches and routers) • Switches interpret MAC address information (just like bridge) • Common switch components – Internal processor, operating system, memory, ports 18
PC connecting to a Switch 19
Switches • Advantages – Better performance and security • Disadvantages – Can be overwhelmed by heavy traffic • Four switching methods exist – Two basic methods discussed 1. Cut-through mode 2. Store-and-forward mode 20
Switching Methods • Cut-through mode – Switch reads frame’s header only – Forwarding decision made before receiving entire packet • Uses frame header: first 14 bytes which contains destination MAC address – Cannot verify data integrity using frame check sequence • Cannot detect corrupt packets 21
Switching Methods • Cut-through mode (cont’d. ) – Advantage: speed – Disadvantage • Data buffering (switch flooded with traffic) – Best use • Small workgroups needing speed • Low number of devices 22
Switching Methods • Store-and-forward mode – Switch reads entire data frame into memory – Checks for accuracy before transmitting information (frame check) – Transmit data more accurately than cut-through mode – Slower than cut-through mode because reads entire frame – Best uses • Larger LAN environments – Can transfer data between segments running different transmission speeds 23
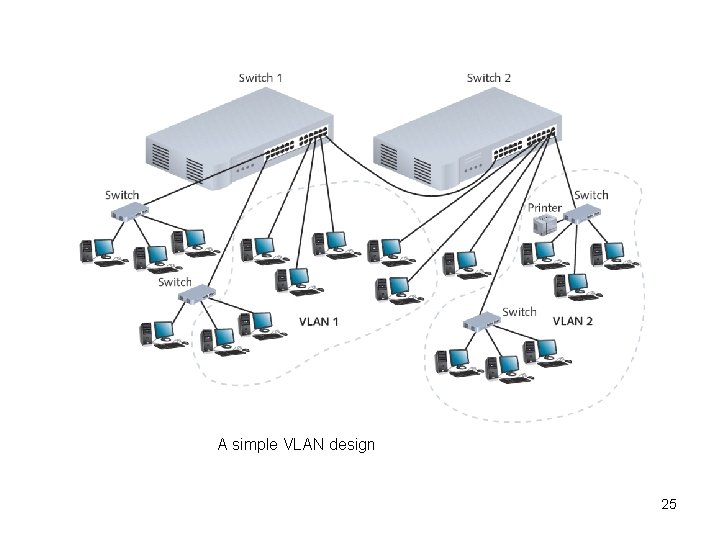
VLANs • VLANs (virtual local area networks) – Concept of partitioning a physical network – Logically separate networks not physical • Groups ports into broadcast domain • Broadcast domain – All nodes can reached each other by a broadcast message • Collision domain – Data packets can collide with one another when being sent on a shared medium 24
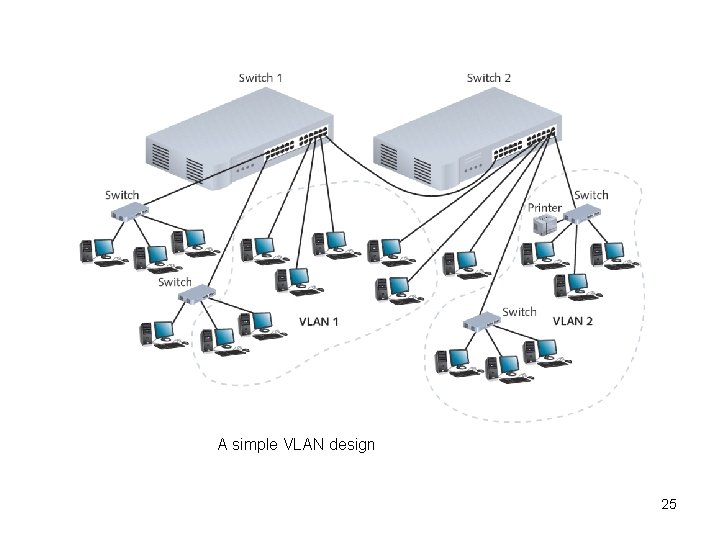
A simple VLAN design 25
VLANs • Advantage of VLANs – Flexible • Ports from multiple switches or segments grouped • Any end node type (PCs, printers) can belong to VLAN – Reasons for using VLAN • • • Separating user groups Isolating connections Identifying priority device groups Grouping legacy protocol devices Separating large network into smaller subnets 26
VLANs • Switch typically preconfigured – One default VLAN – Cannot be deleted or renamed • Create additional VLANs – Indicate to which VLAN each port belongs • Maintain VLAN using switch software • Potential problem – Cutting off group from rest of network 27
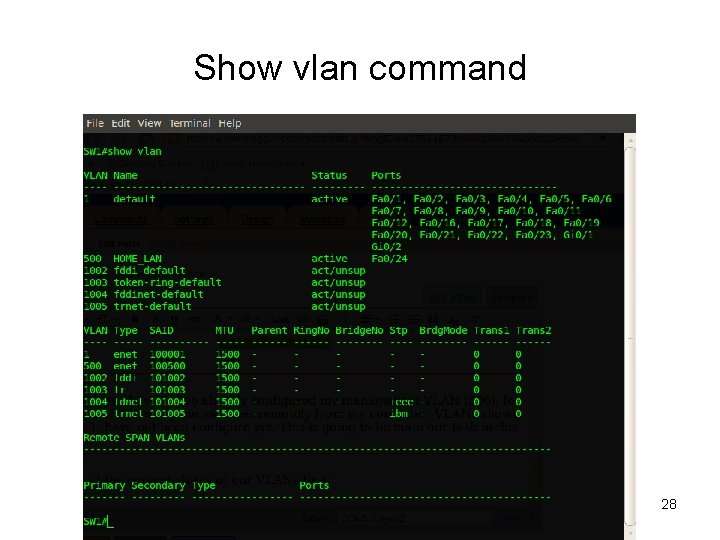
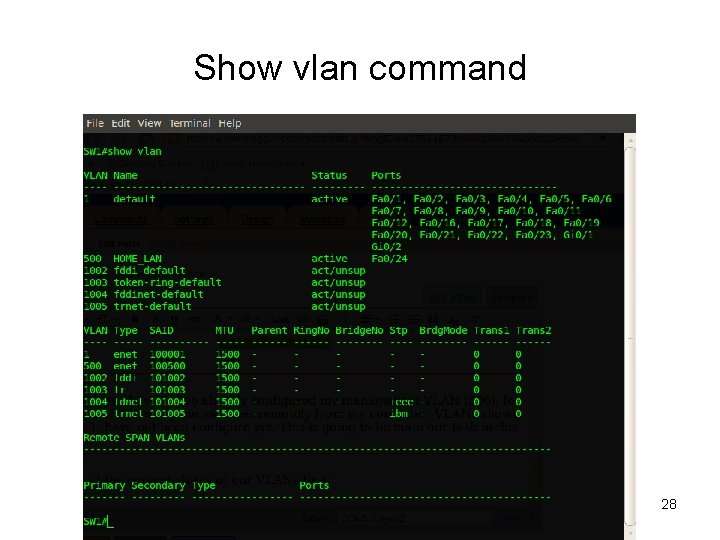
Show vlan command 28
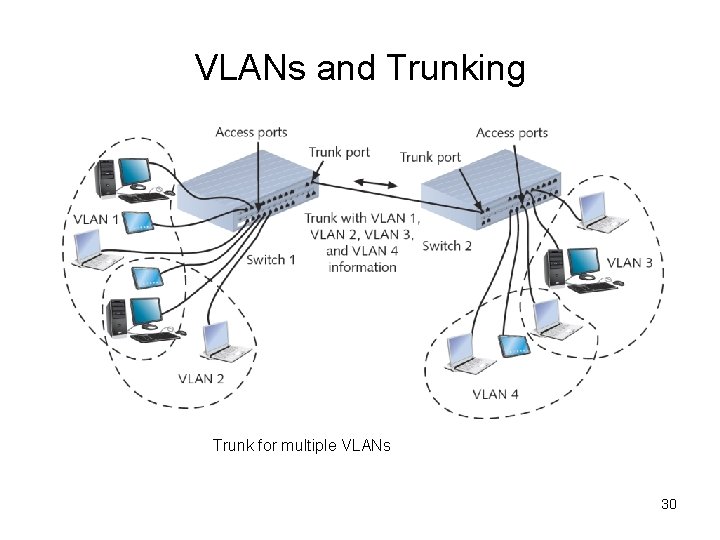
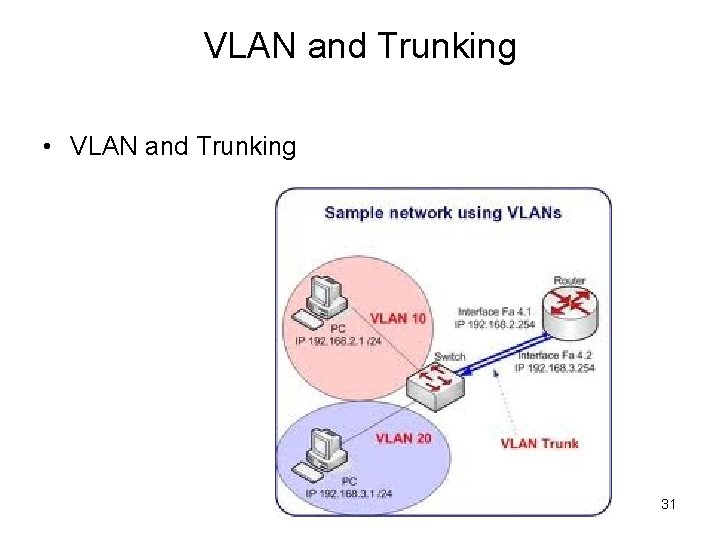
Trunking • Trunking – Switch’s interface carries traffic of multiple VLANs • Trunk – Single physical connection between • VLAN data separation (tag) – Frame contains VLAN identifier in header 29
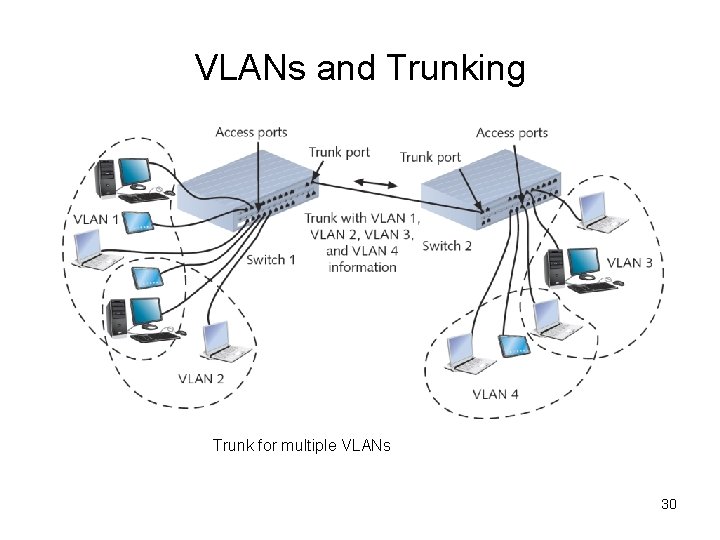
VLANs and Trunking Trunk for multiple VLANs 30
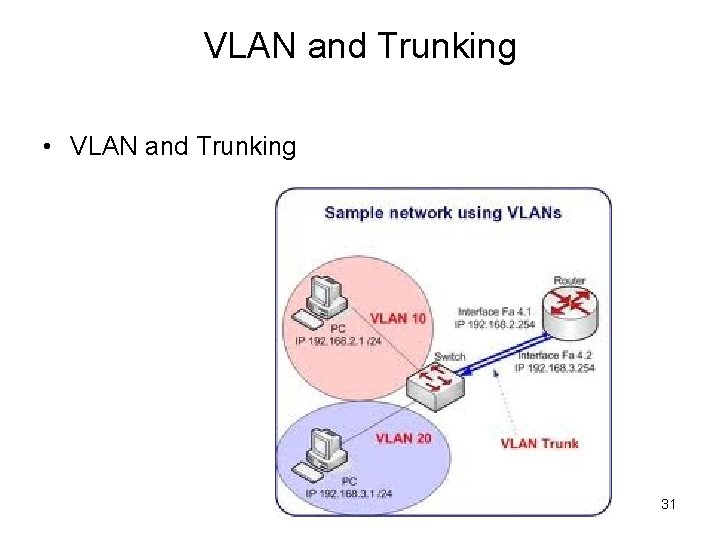
VLAN and Trunking • VLAN and Trunking 31
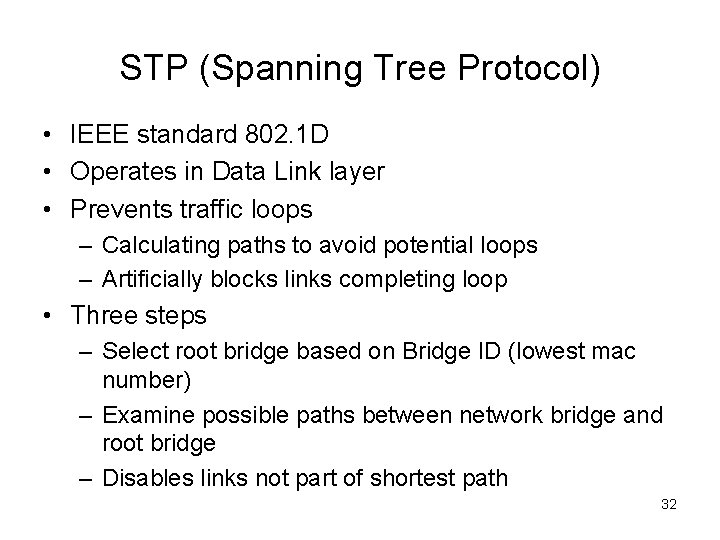
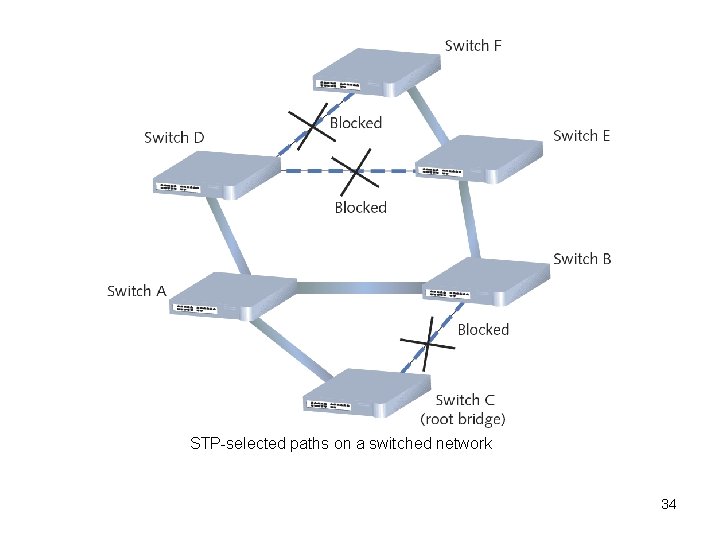
STP (Spanning Tree Protocol) • IEEE standard 802. 1 D • Operates in Data Link layer • Prevents traffic loops – Calculating paths to avoid potential loops – Artificially blocks links completing loop • Three steps – Select root bridge based on Bridge ID (lowest mac number) – Examine possible paths between network bridge and root bridge – Disables links not part of shortest path 32
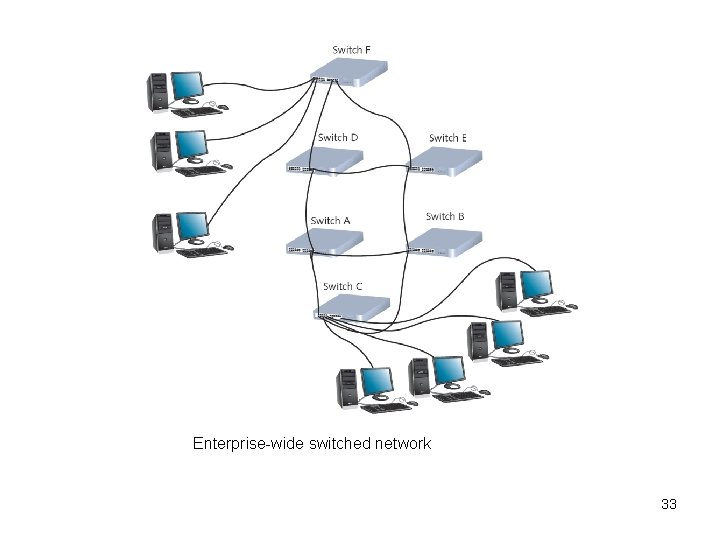
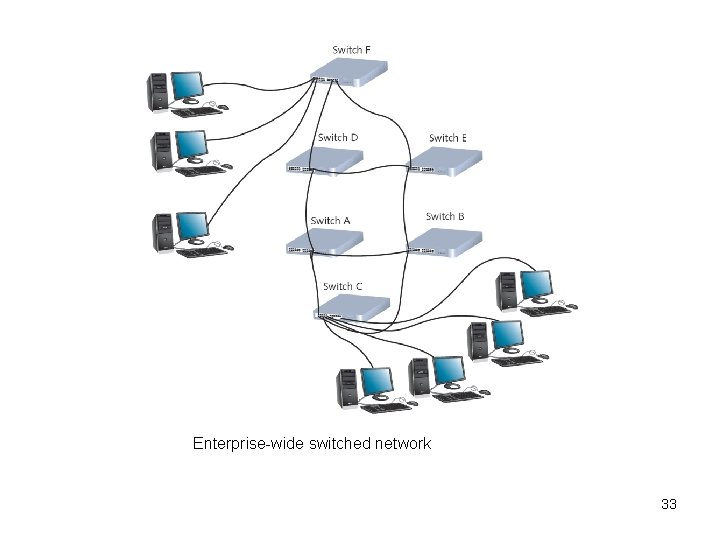
Enterprise-wide switched network 33
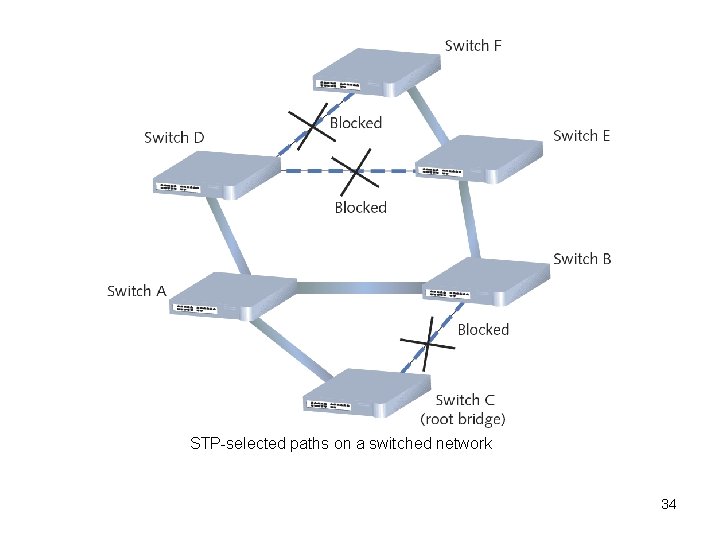
STP-selected paths on a switched network 34
STP (Spanning Tree Protocol) • History – Introduced in 1980 s • Original STP too slow responding to changes – RSTP (Rapid Spanning Tree Protocol) • Newer version • IEEE’s 802. 1 w standard • Cisco and Extreme Networks – Have proprietary versions • No enabling or configuration needed – Included in switch operating software 35
Content and Multilayer Switches • Blurring lines between switches and routers • Layer 3 switch (routing switch) - Interprets Layer 3 data • Layer 4 switch - Interprets Layer 4 data • Content switch (application switch) – Interprets Layer 4 through Layer 7 data • Advantages of interpreting higher layers – Advanced filtering – Keeping statistics – Security functions • Disadvantage – Cost, standards 36
Routers • Multiport connectivity device – Integrates LANs and WANs • Operate at Network layer (Layer 3) – Directs data between network nodes and from one segment or network to another – Uses logical addressing, Protocol dependent • Slower than switches and bridges – Need to interpret Layers 3 and higher information • Traditional stand-alone LAN routers – Being replaced by Layer 3 routing switches 37
Router Characteristics and Functions • Intelligence – Determine shortest, fastest path between two nodes – Connects dissimilar network types • Large LANs and WANs – Routers indispensable • Router components – Internal processor, operating system, memory, input and output jacks, management control interface 38
Router Characteristics and Functions • Multiprotocol routers – Multiple slots – Accommodate multiple network interfaces • Inexpensive routers – Home, small office use • Router capabilities – Interpret Layer 3 addressing – Determine best data path – Reroute traffic 39

Routers 40
Router Types and Terms • Interior router – Directs data between nodes on a LAN • Exterior router – Directs data between nodes external to a LAN • Border routers – Connect autonomous LAN with a WAN • Routing tables (database) – Maintain information where hosts are and how to reach them • Static routing – Router configured to use specific path between nodes • Dynamic routing – Automatically calculates best path between nodes 41
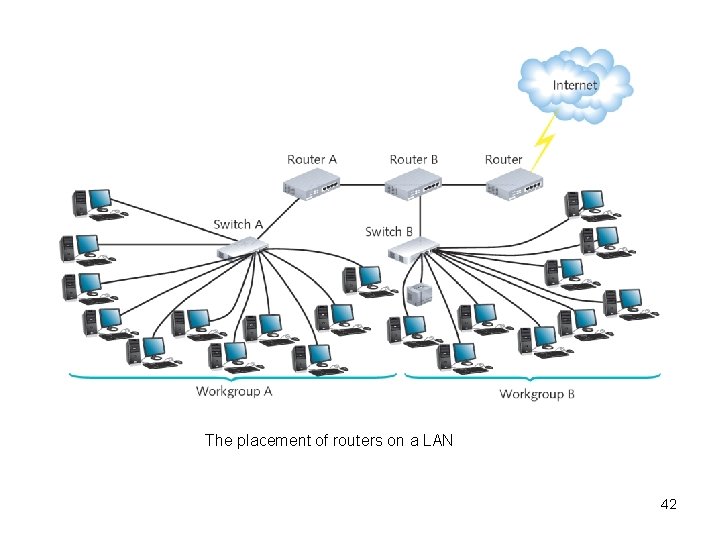
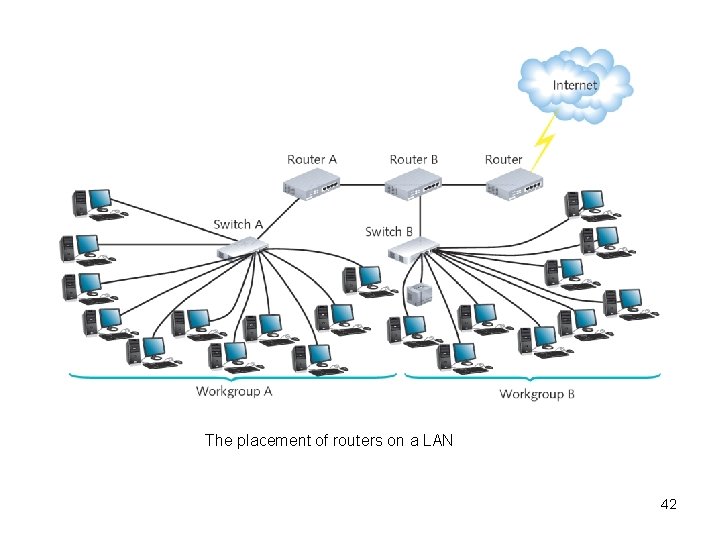
The placement of routers on a LAN 42
Routing Protocols • How to decide on best path – Path is decided by routing protocol • Routing metric factors – – – – Number of hops Throughput on potential path - Transmission speed Delay on a potential path - Current network activity Load (traffic) Maximum transmission unit (MTU) Reliability of potential path - Unavailable link Cost (assigned by administrator) 43
Routing Protocols • Router Convergence Time (con’t) – The time the router takes to recognize best path after change or network outage event 44
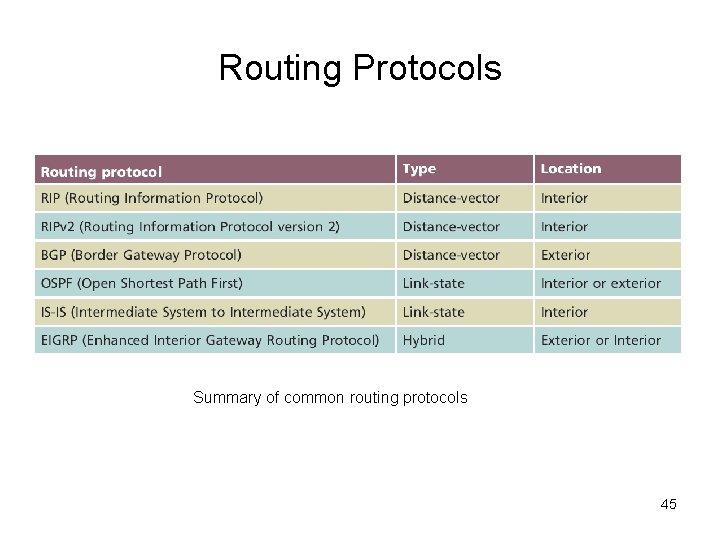
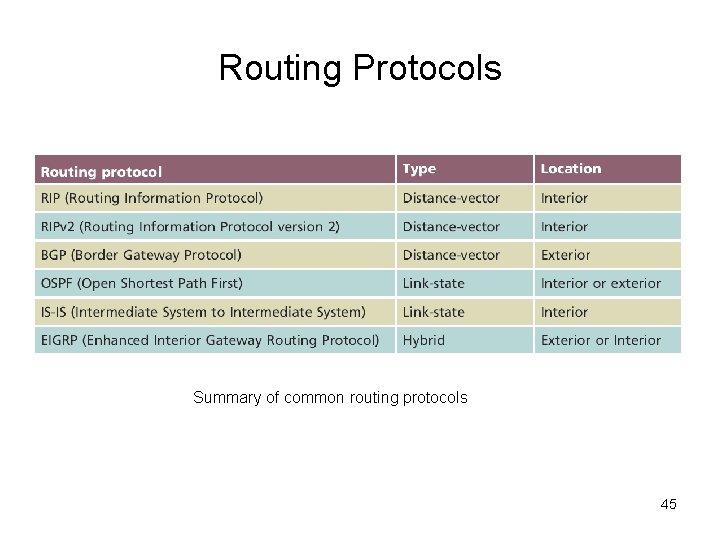
Routing Protocols Summary of common routing protocols 45
Routing Protocols • Distance-vector type routing protocols - RIP, RIPv 2, BGP – Determine best route based on distance to destination – Factors • Hops, latency, network traffic conditions • RIP (Routing Information Protocol) – Only factor is number of hops between nodes • Limits 15 hops – Type of IGP (Interior Gateway Protocol) • Can only route within internal network – Slower and less secure than other routing protocols 46
Routing Protocols • RIPv 2 (Routing Information Protocol Version 2) – Generates less broadcast traffic, more secure than RIP – Cannot exceed 15 hops – Less commonly used • BGP (Border Gateway Protocol) – – – Type of EGP (Exterior Gateway Protocol) Most complex (choice for Internet traffic) Communicates using BGP-specific messages Many factors determine best paths Configurable to follow policies 47
Routing Protocols • Link-state type routing protocol – OSPF and IS-IS – Routers share information • Each router independently maps network, determines best path • OSPF (Open Shortest Path First) – – Interior or border router use No hop limit Complex algorithm for determining best paths Each OSPF router • Maintains database containing other routers’ links 48
Routing Protocols • IS-IS (Intermediate System to Intermediate System) – Codified by ISO – Interior routers only! – Supports two Layer 3 protocols • IP • ISO-specific protocol – Much less common than OSPF 49
Routing Protocols • Hybrid type routing protocol - EIGRP – Link-state and distance-vector characteristics – EIGRP (Enhanced Interior Gateway Routing Protocol) • Most popular • Cisco network routers only! – EIGRP benefits • • Fast convergence time, low network overhead Easier to configure and less CPU-intensive than OSPF Supports multiple protocols Accommodates very large, heterogeneous networks 50
Gateways and Other Multifunction Devices • Gateway – Combination of networking hardware and software – Connects two systems that use different formatting, communications protocols, architecture – They repackages information – Can reside on servers, microcomputers, connectivity devices, mainframes • Popular gateways – Firewall, E-mail gateway, Internet gateway, voice/data gateway, LAN gateway 51
Summary • • • Network adapter types vary (NIC) Repeaters - Regenerate digital signal Hubs Bridges can interpret the data they retransmit Switches subdivide a network – Create VLANs – Trunking • Routers – Various routing protocols • Gateways 52
End of Chapter 6 Questions 53